Filecoin
Filecoin
PoRep- und PoSt-Protokollskizzen

Context
Figure 4 closes Section 3.4 (Practical PoRep and PoSt) and presents complete, step-by-step algorithm listings for both the Filecoin PoRep and PoSt protocols. It is explicitly referenced from Sections 3.4.3 and 3.4.4 as the definitive protocol sketch for practical implementations. The caption states: 'Proof-of-Replication and Proof-of-Spacetime protocol sketches.'
What This Figure Shows
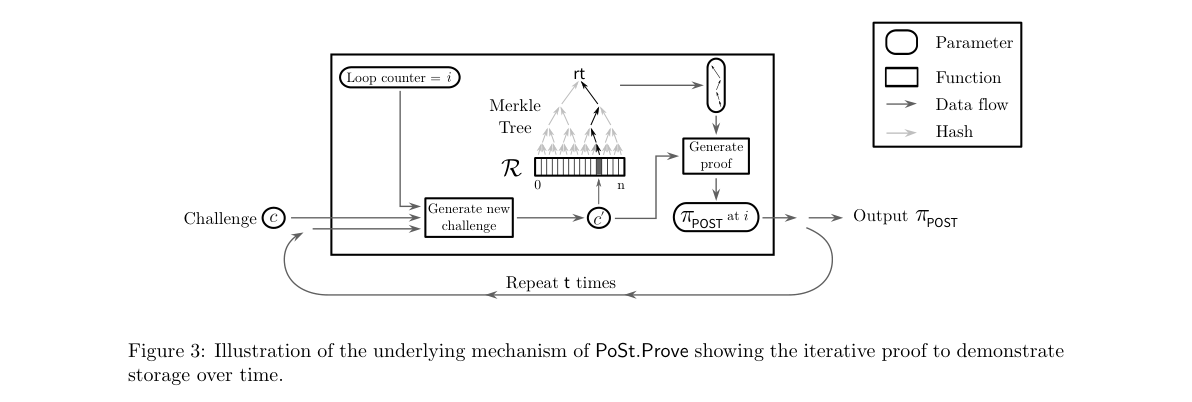
The left half of the figure presents the Filecoin PoRep protocol with three algorithms. Setup takes the prover's key pair and data D, applies the slow Seal operation to produce a unique replica, computes its Merkle root, and generates a zk-SNARK proof proving correct replication. Prove takes a random challenge, computes the Merkle path from root to the challenged leaf, and outputs a proof. Verify checks both the seal proof (confirming correct replica generation) and the storage proof (confirming possession of the challenged leaf). The right half presents the Filecoin PoSt protocol: Setup delegates to PoRep.Setup; Prove iterates t times, deriving new challenges and composing proofs recursively; Verify checks the seal proof and the final PoSt proof against the time parameter t.
Significance
Figure 4 is the formal specification that proves Filecoin's storage proofs are publicly verifiable without trusted verifiers and resistant to sybil, outsourcing, and generation attacks. By combining the slow Seal operation with recursive zk-SNARK composition, the protocol achieves succinct, non-interactive proofs that any network participant can verify from the blockchain, making the system auditable and incentive-compatible.