Solana
Solana
CBC Encryption for Proof of Replication
Context
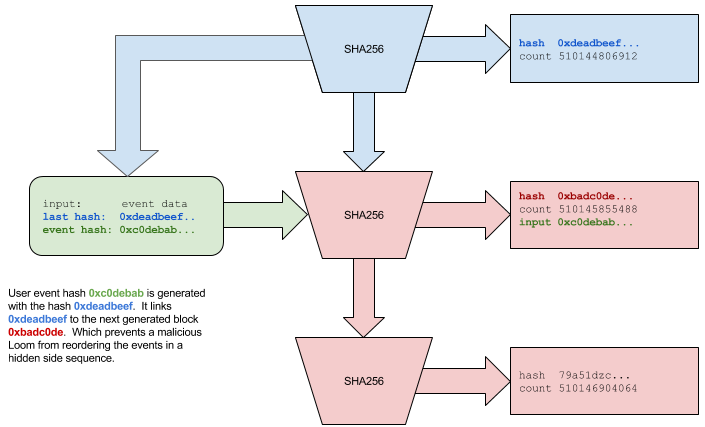
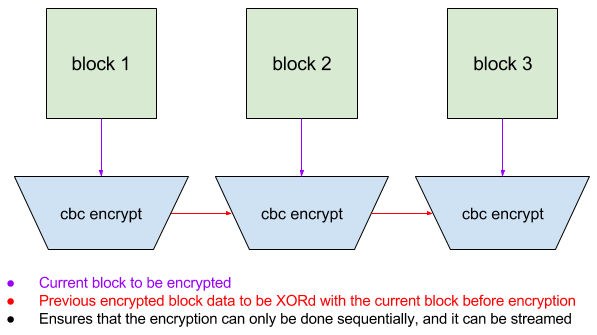
This figure appears in the 'Streaming Proof of Replication' section, which describes how Solana validators prove they are storing complete copies of the ledger. The section explains that naive storage proofs are vulnerable to outsourcing attacks — a validator could claim to store data it actually retrieves on demand from another validator. CBC encryption with a validator-specific key prevents this by making each validator's encrypted copy unique and computationally bound to their identity.
What This Figure Shows
The diagram illustrates Cipher Block Chaining (CBC) mode encryption as applied to ledger data: each plaintext block P_n is XORed with the ciphertext of the previous block C_{n-1} before being encrypted with the validator's key, producing ciphertext C_n = Encrypt(P_n XOR C_{n-1}). This chaining means that to compute C_n, the validator must have already computed C_{n-1}, which required C_{n-2}, and so on back to C_0. The validator cannot compute the encrypted block at position n without having processed all preceding blocks sequentially, ensuring that the encrypted ledger is a faithful sequential replica of the original data. Because each validator uses a different key derived from their public key and a PoH-derived seed, no two validators produce the same ciphertext, making it impossible to fake a storage proof by copying another validator's encrypted data.
Significance
CBC mode is the cryptographic primitive that enforces sequential processing in Solana's Proof of Replication, transforming a storage verification problem into a computation verification problem. Without this chaining property, a validator could selectively store only the blocks it expects to be challenged on; with it, the validator must process the entire sequence to produce any valid encrypted block. The diagram makes the dependency chain tangible and explains why arbitrary challenge positions cannot be answered without full sequential storage.