
Cosmos:分布式账本网络
Introduction
Le succès combiné de l'écosystème open source, le partage de fichiers décentralisé et les crypto-monnaies publiques ont a inspiré une compréhension que les protocoles Internet décentralisés peut être utilisé pour améliorer radicalement les infrastructures socio-économiques. Nous avons vu des applications blockchain spécialisées comme Bitcoin [1] (un crypto-monnaie), Zerocash [2] (une crypto-monnaie pour la confidentialité), et plateformes smart contract généralisées telles que Ethereum [3], avec d'innombrables applications distribuées pour l'Etherium Virtual Machine (EVM) telle qu'Augur (un marché de prédiction) et TheDAO [4] (un club d'investissement). Cependant, à ce jour, ces blockchain ont souffert de plusieurs d'inconvénients, y compris leur inefficacité énergétique flagrante, leur mauvaise ou des performances limitées et des mécanismes de gouvernance immatures. Propositions visant à augmenter le débit des transactions de Bitcoin, telles que Les témoins séparés [5] et BitcoinNG [6] sont à mise à l'échelle verticale. des solutions qui restent limitées par la capacité d’un seul organisme physique machine, afin de garantir la propriété d'une auditabilité complète. Le Lightning Network [7] peut aider à faire évoluer la transaction Bitcoin
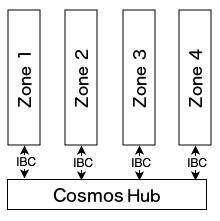
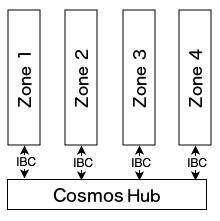
volume en laissant certaines transactions hors du grand livre, et est bien adapté aux micropaiements et à la préservation de la confidentialité rails de paiement, mais peuvent ne pas convenir à des applications plus généralisées besoins de mise à l’échelle. Une solution idéale est celle qui permet à plusieurs blockchain parallèles de interopérer tout en conservant leurs propriétés de sécurité. Cela a s'est avéré difficile, voire impossible, avec proof-of-work. Fusionné l'exploitation minière, par exemple, permet au travail effectué de sécuriser un parent chaîne à réutiliser sur une chaîne enfant, mais les transactions doivent toujours être validé, dans l'ordre, par chaque nœud, et un blockchain fusionné est vulnérable aux attaques si la majorité du pouvoir hashing sur le le parent ne fusionne pas activement l'enfant. Une revue académique d'architectures de réseau blockchain alternatives sont fournies contexte supplémentaire, et nous fournissons des résumés d’autres propositions et leurs inconvénients dans les travaux connexes. Nous présentons ici Cosmos, une nouvelle architecture réseau blockchain qui répond à tous ces problèmes. Cosmos est un réseau de nombreux des blockchain indépendants, appelés zones. Les zones sont alimentées par Tendermint Core [8], qui fournit une haute performance, moteur de consensus cohérent et sécurisé de type PBFT, où des garanties strictes de responsabilité fork s'appliquent au comportement des éléments malveillants. acteurs. L'algorithme de consensus BFT de Tendermint Core est bien adapté pour la mise à l'échelle des proof-of-stake blockchain publics. La première zone sur Cosmos est appelée le hub Cosmos. Le Cosmos Hub est une crypto-monnaie proof-of-stake multi-actifs avec un simple mécanisme de gouvernance qui permet au réseau de s’adapter et mise à niveau. De plus, le hub Cosmos peut être étendu de connecter d’autres zones. Le hub et les zones du réseau Cosmos communiquent avec entre eux via un protocole de communication inter-blockchain (IBC), une sorte d'UDP ou TCP virtuel pour les blockchain. Les jetons peuvent être transféré d’une zone à une autre de manière sécurisée et rapidesans qu’il soit nécessaire d’échanger des liquidités entre zones. Au lieu de cela, tous les transferts inter-zones token passent par le Hub Cosmos, qui garde une trace du montant total de tokens détenu par chaque zone. Le Le hub isole chaque zone de la défaillance des autres zones. Parce que n'importe qui peut connecter une nouvelle zone au hub Cosmos, les zones le permettent pour une compatibilité future avec les nouvelles innovations blockchain. Dans cette section, nous décrivons le protocole de consensus Tendermint et l'interface utilisée pour créer des applications avec. Pour plus détails, voir l'annexe. Dans les algorithmes byzantins classiques de tolérance aux pannes (BFT), chaque nœud a le même poids. Dans Tendermint, les nœuds ont une valeur non négative quantité de pouvoir de vote et nœuds qui ont un vote positif puissance sont appelés validators. Les validateurs participent au protocole de consensus en diffusant des signatures cryptographiques, ou votes, pour se mettre d’accord sur le prochain bloc. Les pouvoirs de vote des validateurs sont déterminés dès la genèse, ou sont modifié de manière déterministe par le blockchain, en fonction du demande. Par exemple, dans une application proof-of-stake telle que le Cosmos Hub, le pouvoir de vote peut être déterminé par le montant de staking tokens cautionné en garantie. REMARQUE : Les fractions telles que ⅔ et ⅓ font référence à des fractions du total des votes. puissance, jamais le nombre total de validator, à moins que tous les validator ont un poids égal. >⅔ signifie « plus de ⅔ », ≥⅓ signifie « au moins ⅓”. Tendermint est un protocole de consensus BFT partiellement synchrone dérivé de l'algorithme de consensus DLS [20]. La menthe tendre est
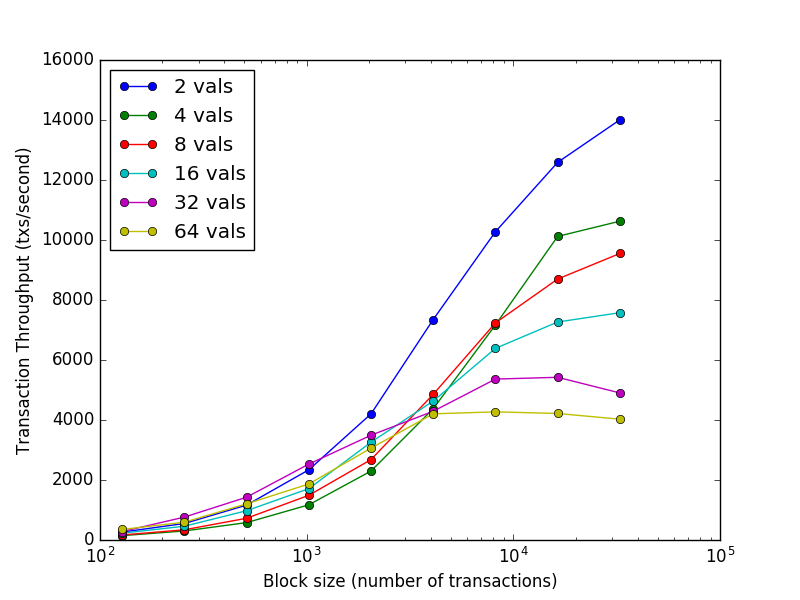
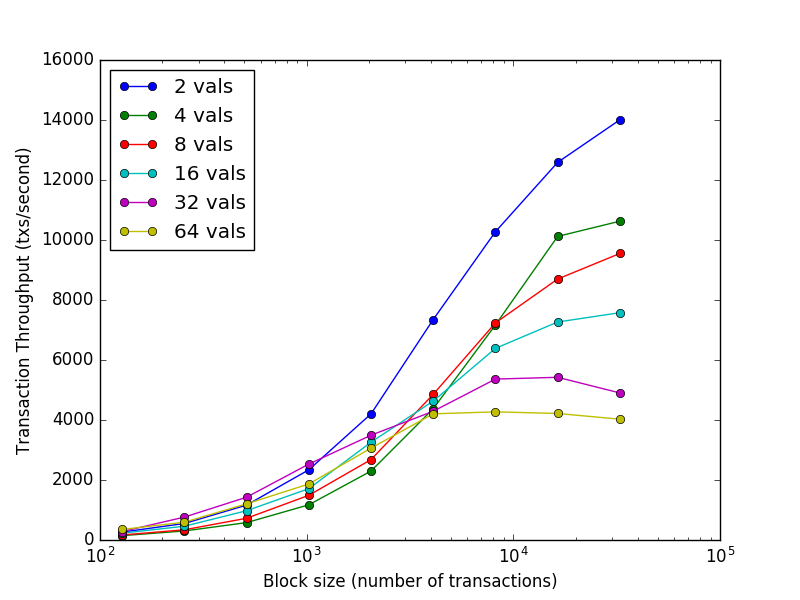
remarquable par sa simplicité, ses performances et sa responsabilité fork. Le protocole nécessite un ensemble connu et fixe de validator, où chaque validator est identifié par sa clé publique. Les validateurs tentent de parvenir à un consensus sur un bloc à la fois, où un bloc est une liste de transactions. Le vote pour le consensus sur un bloc se déroule dans tours. Chaque tour a un leader, ou proposant, qui propose un bloc. Les validator votent ensuite, par étapes, pour savoir si pour accepter le blocage proposé ou passer au tour suivant. Le le proposant pour un tour est choisi de manière déterministe parmi les liste des validator, proportionnellement à leur pouvoir de vote. Les détails complets du protocole sont décrits ici. La sécurité de Tendermint découle de son utilisation optimale du byzantin tolérance aux pannes via un vote à super majorité (>⅔) et un verrouillage mécanisme. Ensemble, ils veillent à ce que : ≥⅓ du pouvoir de vote doit être byzantin pour provoquer une violation de la sécurité, où plus de deux valeurs sont engagées. si un ensemble de validator réussit à violer la sécurité, ou même tente de le faire, ils peuvent être identifiés par le protocole. Ceci comprend à la fois le vote pour les blocs conflictuels et la diffusion votes injustifiés. Malgré ses fortes garanties, Tendermint offre des performances. Dans des benchmarks de 64 nœuds répartis sur 7 des datacenters sur les 5 continents, sur des instances cloud commodités, Le consensus Tendermint peut traiter des milliers de transactions par deuxièmement, avec des latences de validation de l’ordre d’une à deux secondes. Notamment, la performance de plus d'un millier de transactions par la seconde est maintenue même dans des conditions adverses difficiles, avec validators plante ou diffuse des votes frauduleux. Voir la figure ci-dessous pour plus de détails.
Un avantage majeur de l’algorithme de consensus de Tendermint est la simplification sécurité client légère, ce qui en fait un candidat idéal pour les applications mobiles et cas d'utilisation de l'Internet des objets. Alors qu'un client léger Bitcoin doit se synchroniser chaînes d'en-têtes de bloc et trouver celle avec le plus de preuves de fonctionnent, les clients légers de Tendermint n'ont qu'à suivre les changements à l'ensemble validator, puis vérifiez les >⅔ PreCommits dans le dernier bloc pour déterminer le dernier état. Des épreuves client légères et succinctes permettent également d'inter-blockchain communications. Tendermint dispose de mesures de protection pour empêcher certains attaques notables, comme les doubles dépenses à longue portée sans enjeu et la censure. Ceux-ci sont discutés plus en détail dans l’annexe.L'algorithme de consensus Tendermint est implémenté dans un programme appelé Tendermint Core. Tendermint Core est un « moteur de consensus » indépendant des applications, capable de transformer n'importe quelle application de boîte noire déterministe dans une application répliquée de manière distribuée blockchain. Tendermint Core se connecte aux applications blockchain via l'interface Application Blockchain (ABCI) [17]. Ainsi, ABCI permet de programmer des applications blockchain dans n'importe quel langage, pas seulement le langage de programmation que le consensus moteur est écrit. De plus, ABCI permet de facilement échangez la couche de consensus de toute pile blockchain existante. Nous faisons une analogie avec la célèbre crypto-monnaie Bitcoin. Bitcoin est une crypto-monnaie blockchain où chaque nœud conserve une base de données entièrement auditée sur les résultats des transactions non dépensées (UTXO). Si on voulait créer un système de type Bitcoin au-dessus de ABCI, Tendermint Core serait responsable de Partage de blocs et de transactions entre nœuds Établir un ordre canonique/immuable des transactions (le blockchain) Pendant ce temps, l'application ABCI serait chargée de Maintenance de la base de données UTXO Validation des signatures cryptographiques des transactions Empêcher les transactions de dépenser des fonds inexistants Autoriser les clients à interroger la base de données UTXO Tendermint est capable de décomposer la conception blockchain en offrant une API très simple entre le processus de candidature et processus de consensus.
介绍
开源生态系统的共同成功, 去中心化的yle共享,公共加密货币已经 激发了人们对去中心化互联网协议的理解 可用于从根本上改善社会经济基础设施。 我们已经看到了专门的 blockchain 应用程序,例如 Bitcoin [1] ( 加密货币)、Zerocash [2](一种保护隐私的加密货币)以及 通用 smart contract 平台,例如 Ethereum [3], 以太坊虚拟的无数分布式应用程序 机器(EVM),例如 Augur(预测市场)和 TheDAO [4](投资俱乐部)。 然而,迄今为止,这些 blockchain 已经遭受了许多问题的困扰。 的缺点,包括其总体能源效率低下、贫穷或 绩效有限,治理机制不成熟。 扩大 Bitcoin 交易吞吐量的建议,例如 隔离见证 [5] 和 BitcoinNG [6],是垂直缩放 解决方案仍然受到单个物理容量的限制 机,以保证性能的完全可审核性。 闪电网络 [7] 可以帮助扩展 Bitcoin 交易
通过将一些交易完全从分类账中删除来增加交易量, 非常适合小额支付和隐私保护 支付轨道,但可能不适合更普遍的情况 扩展需求。 理想的解决方案是允许多个并行 blockchain 互操作,同时保留其安全属性。这有 事实证明,对于 proof-of-work 来说,即使不是不可能,也是很困难的。合并 例如,采矿可以确保父母的安全 链可以在子链上重用,但交易仍然必须 按顺序由每个节点进行验证,并合并挖掘 blockchain 如果 hashing 上的大部分功率都容易受到攻击 父级没有积极地对子级进行合并挖掘。学术评论 提供了替代的 blockchain 网络架构 其他背景,我们提供其他提案的摘要 以及它们在相关工作中的缺点。 在这里,我们介绍 Cosmos,一种新颖的 blockchain 网络架构 解决所有这些问题。 Cosmos 是一个由许多人组成的网络 独立的 blockchain,称为区域。这些区域的动力来自 Tendermint Core [8],提供高性能、 一致、安全的类似 PBFT 的共识引擎,其中严格的责任保证可以抑制恶意行为 演员。 Tendermint Core 的 BFT 共识算法非常适合 用于缩放 public proof-of-stake blockchains。 Cosmos 上的第一个区域称为 Cosmos 中心。 Cosmos Hub 是一种多资产 proof-of-stake 加密货币,具有简单的 使网络能够适应和适应的治理机制 升级。此外,Cosmos 集线器可以通过以下方式扩展: 连接其他区域。 Cosmos 网络的集线器和区域与 彼此通过 blockchain 间通信 (IBC) 协议, blockchains 的一种虚拟 UDP 或 TCP。代币可以是 安全、快速地从一个区域转移到另一个区域无需在区域之间交换流动性。相反, 所有区域间 token 传输均通过 Cosmos 中心,该中心 跟踪每个区域持有的 token 总量。的 集线器将每个区域与其他区域的故障隔离开来。因为 任何人都可以将新区域连接到 Cosmos 集线器,区域允许 为了与新的 blockchain 创新未来兼容。 在本节中,我们将描述 Tendermint 共识协议 以及用于构建应用程序的接口。了解更多 详情见附录。 在经典拜占庭容错 (BFT) 算法中,每个节点 具有相同的重量。在 Tendermint 中,节点具有非负数 投票权的大小以及投票赞成的节点 电源称为 validators。验证者参与 通过广播加密签名达成共识协议,或者 投票,就下一个区块达成一致。 验证者的投票权是在创世时决定的,或者是 由 blockchain 确定性地更改,具体取决于 应用程序。例如,在 proof-of-stake 应用程序中,例如 Cosmos Hub,投票权可以由 作为抵押品的 staking token 数量。 注:像 ⅔ 和 ⅓ 这样的分数是指总投票数的分数 功率,绝不是 validator 的总数,除非所有 validator 都 具有相同的权重。 >⅔表示“超过⅔”,≥⅓表示“至少 ⅓”。 Tendermint 是一个部分同步的 BFT 共识协议 源自 DLS 共识算法 [20]。嫩薄荷是
以其简单性、性能和分叉责任而闻名。 该协议需要一组已知的 validator,其中每个 validator 由其公钥识别。验证者试图 一次就一个区块达成共识,其中一个区块就是一个列表 的交易。对区块进行投票以达成共识 回合。每轮都有一位轮次领导者或提议者,他们 提出一个区块。然后 validator 分阶段投票决定是否 接受提议的区块或进入下一轮。的 一轮的提议者是从有序的中确定性地选择的 validator 列表,按其投票权比例。 此处描述了该协议的完整细节。 Tendermint 的安全性源自其对最佳拜占庭式的使用 通过绝对多数 (>⅔) 投票和锁定实现容错 机制。他们共同确保: ≥⅓ 投票权必须是拜占庭式的才会导致违反 安全,承诺两个以上的价值观。 如果任何一组 validator 曾经成功违反安全性,甚至 尝试这样做时,它们可以被协议识别。这个 包括对冲突区块的投票和广播 不公正的选票。 尽管有强有力的保证,Tendermint 仍提供卓越的服务 性能。在分布在 7 个节点的 64 个节点的基准测试中 数据中心遍布五大洲,位于商品云实例上, Tendermint 共识可以处理数千笔交易 其次,提交延迟约为一到两秒。 值得注意的是,每笔交易的性能远远超过一千笔 即使在恶劣的对抗条件下,第二个也能保持, validators 崩溃或广播恶意制作的投票。参见 详情请参见下图。
Tendermint 共识算法的一个主要好处是简化 轻客户端安全性,使其成为移动和 物联网用例。虽然 Bitcoin 轻客户端必须同步 区块头链,并找到拥有最多证明的区块头链 工作,Tendermint 轻客户端只需要跟上变化 到 validator 集,然后验证 >⅔ PreCommits 最新块来确定最新状态。 简洁的轻客户端证明还可以实现blockchain之间的交互 沟通。 Tendermint 有保护措施来防止某些 值得注意的攻击,例如远程无利害关系双花 和审查制度。这些在附录中进行了更全面的讨论。Tendermint 共识算法是在 名为 Tendermint Core 的程序。 Tendermint 核心是 与应用程序无关的“共识引擎”,可以改变任何 将确定性黑盒应用程序转化为分布式复制 blockchain。 Tendermint Core 连接到 blockchain 应用程序 通过应用程序区块链接口 (ABCI) [17]。因此,ABCI 允许 blockchain 应用程序在任何 语言,而不仅仅是达成共识的编程语言 引擎被写入。此外,ABCI 可以轻松地 交换任何现有 blockchain 堆栈的共识层。 我们用著名的加密货币Bitcoin进行类比。 Bitcoin 是每个节点维护的加密货币 blockchain 经过全面审核的未花费交易输出 (UTXO) 数据库。如果 有人想在 ABCI 之上创建一个类似 Bitcoin 的系统, Tendermint Core 将负责 节点之间共享区块和交易 建立规范/不可变的交易顺序( blockchain) 同时,ABCI 应用程序将负责 维护 UTXO 数据库 验证交易的加密签名 防止交易花费不存在的资金 允许客户端查询 UTXO 数据库 Tendermint 能够通过以下方式分解 blockchain 设计: 在应用程序进程和 共识过程。
Cosmos Architecture
Cosmos est un réseau de blockchain parallèles indépendants qui sont chacun alimenté par des algorithmes de consensus classiques BFT comme Menthe tendre 1. La première blockchain de ce réseau sera le Cosmos Hub. Le Cosmos Hub se connecte à de nombreux autres blockchain (ou zones) via un nouveau protocole de communication inter-blockchain. Le hub Cosmos suit de nombreux types token et conserve une trace du total nombre de token dans chaque zone connectée. Les jetons peuvent être transféré d’une zone à une autre de manière sécurisée et rapide sans avoir besoin d'un échange liquide entre zones, car tout les transferts de pièces inter-zones passent par le Hub Cosmos. Cette architecture résout de nombreux problèmes que l'espace blockchain auxquels sont confrontés aujourd'hui, tels que l'interopérabilité des applications, l'évolutivité et évolutivité transparente. Par exemple, les zones dérivées de Bitcoind, Go-Ethereum, CryptoNote, ZCash ou tout autre système blockchain peut être branché sur le hub Cosmos. Ces zones permettent à Cosmos de évoluer à l’infini pour répondre à la demande mondiale de transactions. Les zones sont également un excellent outil pour un échange distribué, qui sera pris en charge en tant que eh bien. Cosmos n'est pas qu'un seul grand livre distribué, et le Cosmos Hub n’est pas un jardin clos ni le centre de son univers. Nous sommes concevoir un protocole pour un réseau ouvert de registres distribués qui peut servir de nouvelle base aux futurs systèmes financiers, basé sur les principes de la cryptographie, d'une économie saine et du consensus théorie, transparence et responsabilité. Le Cosmos Hub est le premier blockchain public du Cosmos Réseau, alimenté par l'algorithme de consensus BFT de Tendermint. Le Le projet open source Tendermint est né en 2014 pour répondre au la vitesse, l'évolutivité et les problèmes environnementaux de l'algorithme de consensus de preuve de travail de Bitcoin. En utilisant et en améliorant des solutions éprouvées
BFT algorithmes développés au MIT en 1988 [20], le Tendermint L'équipe a été la première à démontrer conceptuellement un proof-of-stake crypto-monnaie qui résout le problème de l'enjeu nul subi par les crypto-monnaies proof-of-stake de première génération telles que comme NXT et BitShares1.0. Aujourd'hui, pratiquement tous les portefeuilles mobiles Bitcoin utilisent des serveurs de confiance pour fournissez-leur la vérification des transactions. En effet, la preuve de travail nécessite d'attendre de nombreuses confirmations avant qu'un la transaction peut être considérée comme irréversiblement engagée. Des attaques à double dépense ont déjà été démontrées sur des services comme CoinBase. Contrairement aux autres systèmes de consensus blockchain, Tendermint propose vérification instantanée et prouvée des paiements des clients mobiles. Puisque le Tendermint est conçu pour ne jamais bifurquer du tout, les appareils mobiles les portefeuilles peuvent recevoir une confirmation de transaction instantanée, ce qui rend les paiements sans confiance et pratiques sont une réalité sur les smartphones. Ceci a des implications importantes pour les applications de l'Internet des objets, car eh bien. Les validateurs de Cosmos ont un rôle similaire à celui des mineurs de Bitcoin, mais utilisez plutôt des signatures cryptographiques pour voter. Les validateurs sont des machines sécurisées et dédiées qui sont responsables de la validation blocs. Les non-validator peuvent déléguer leurs staking token (appelés "atomes") à n'importe quel validator pour gagner une partie des frais forfaitaires et des atomes récompenses, mais ils encourent le risque d'être punis (coupés) si le le délégué validator est piraté ou viole le protocole. Le éprouvé les garanties de sécurité du consensus Tendermint BFT et les garanties dépôt des parties prenantes – validators et délégants – fournir sécurité prouvable et quantifiable pour les nœuds et les clients légers. Les grands livres publics distribués devraient avoir une constitution et un système de gouvernance. Bitcoin s'appuie sur la Fondation Bitcoin etl'exploitation minière pour coordonner les mises à niveau, mais c'est un processus lent. Ethereum s'est divisé en ETH et ETC après avoir difficilement résolu Le DAO hack, en grande partie parce qu'il n'y avait pas de contrat social préalable ni aucun mécanisme pour prendre de telles décisions. Les validateurs et les délégués du hub Cosmos peuvent voter sur propositions qui peuvent modifier les paramètres prédéfinis du système automatiquement (comme la limite de gaz du bloc), coordonner les mises à niveau, comme ainsi que voter sur les amendements à la constitution lisible par l'homme qui régissent les politiques du Hub Cosmos. La Constitution permet une cohésion entre les parties prenantes sur des questions telles que le vol et les bugs (tels que l'incident TheDAO), permettant une intervention plus rapide et résolution plus propre. Chaque zone peut également avoir sa propre constitution et sa propre gouvernance mécanisme également. Par exemple, le hub Cosmos pourrait avoir un constitution qui impose l'immuabilité au Hub (pas de rollbacks, sauf pour les bogues de l'implémentation du nœud Hub Cosmos), tandis que chaque zone peut définir ses propres politiques concernant les restaurations. En permettant l'interopérabilité entre les différentes zones politiques, le Le réseau Cosmos offre à ses utilisateurs une liberté et un potentiel ultimes pour expérimentation sans autorisation. Nous décrivons ici un nouveau modèle de décentralisation et d'évolutivité. Cosmos est un réseau de nombreux blockchain alimentés par Menthe tendre. Alors que les propositions existantes visent à créer un « blockchain » avec l'ordre global total des transactions, Cosmos permet à plusieurs blockchain de s'exécuter simultanément les uns avec les autres tout en conservant l'interopérabilité. A la base, le Hub Cosmos gère de nombreux blockchains appelés « zones » (parfois appelés « fragments », en référence à la technique de mise à l’échelle de la base de données connue sous le nom de « sharding »).
Un flux constant de validations de blocs récentes provenant de zones publiées sur le Hub permet au Hub de suivre l'état de chaque zone. De même, chaque zone suit l'état du Hub (mais les zones ne se suivent pas, sauf indirectement à travers le Moyeu). Des paquets d'informations sont ensuite communiqués à partir d'un zone à une autre en affichant des preuves Merkle comme preuve que le les informations ont été envoyées et reçues. Ce mécanisme est appelé communication inter-blockchain, ou IBC pour faire court. N'importe laquelle des zones peut elle-même être des hubs pour former un graphe acyclique, mais par souci de clarté, nous décrirons uniquement le simple conyguration où il n'y a qu'un seul hub et de nombreux non-hub zones. Le Cosmos Hub est un blockchain qui héberge un multi-actifs grand livre distribué, où les token peuvent être détenus par des utilisateurs individuels ou par zones elles-mêmes. Ces token peuvent être déplacés d'une zone à un autre dans un paquet spécial IBC appelé « paquet de pièces ». Le moyeu est chargé de préserver l’invariance globale du total montant de chaque token dans les zones. IBC paquet de pièces les transactions doivent être validées par l'expéditeur, le hub et le destinataire blockchains.Étant donné que le hub Cosmos agit comme le grand livre central pour l'ensemble système, la sécurité du Hub est d’une importance primordiale. Tandis que chaque zone peut être un Tendermint blockchain sécurisé par seulement 4 (ou même moins si le consensus BFT n'est pas nécessaire), le Hub doit être sécurisé par un ensemble globalement décentralisé de validator qui peut résister aux scénarios d'attaque les plus sévères, tels qu'un partition du réseau continental ou attaque parrainée par un État-nation. Une zone Cosmos est une zone blockchain indépendante qui échange IBC messages avec le Hub. Du point de vue du Hub, une zone est un compte multi-signatures à adhésion dynamique multi-actifs qui peut envoyer et recevoir des token en utilisant des paquets IBC. Comme un compte de crypto-monnaie, une zone ne peut pas transférer plus de tokens que il l'a fait, mais peut recevoir des token d'autres personnes qui les possèdent. Une zone peut être désigné comme une « source » d'un ou plusieurs types token, lui accordant le pouvoir d'augmenter cet approvisionnement token. Les atomes du Hub Cosmos peuvent être jalonnés par les validator d'une zone connecté au Hub. Tandis que les attaques à double dépense sur ces zones entraînerait la réduction des atomes avec la responsabilité fork de Tendermint, une zone où >⅔ du pouvoir de vote sont Les Byzantins peuvent commettre un état invalide. Le hub Cosmos ne vérifier ou exécuter des transactions validées sur d'autres zones, il est donc la responsabilité des utilisateurs d’envoyer des token aux zones en lesquelles ils ont confiance. À l'avenir, le système de gouvernance du Hub Cosmos pourrait réussir des propositions d'amélioration qui tiennent compte des défaillances de zone. Pour Par exemple, les transferts sortants token depuis certaines (ou toutes) zones peuvent être étranglé pour permettre la coupure de circuit d'urgence des zones (un arrêt temporaire des transferts token) lorsqu'une attaque est détectée. Voyons maintenant comment le Hub et les zones communiquent entre eux. autre. Par exemple, s'il y a trois blockchain, "Zone1", "Zone2",
et « Hub », et nous souhaitons que « Zone1 » produise un paquet destiné pour « Zone2 » en passant par « Hub ». Pour déplacer un paquet d'un blockchain à un autre, un BAT est affiché sur la chaîne de réception. La preuve indique que la chaîne d'envoi a publié un paquet pour le destination présumée. Pour que la chaîne de réception puisse vérifier cette preuve, il doit être capable de suivre les en-têtes de bloc de l’expéditeur. Ceci Le mécanisme est similaire à celui utilisé par les sidechains, ce qui nécessite deux chaînes en interaction pour prendre conscience l'une de l'autre via un flux bidirectionnel de datagrammes de preuve d'existence (transactions). Le protocole IBC peut naturellement être défini à l'aide de deux types de transactions : une transaction IBCBlockCommitTx , qui permet un blockchain pour prouver à tout observateur de son bloc le plus récent-hash, et une transaction IBCPacketTx , qui permet à un blockchain de prouver à tout observateur que le paquet donné a bien été publié par l’application de l’expéditeur, via une preuve Merkle au récent bloc-hash. En divisant la mécanique IBC en deux transactions distinctes, nous permettre au mécanisme de marché des frais natifs de la chaîne de réception de déterminer quels paquets sont validés (c'est-à-dire reconnus), tandis que permettant une liberté totale sur la chaîne d'envoi quant à la manière dont de nombreux paquets sortants sont autorisés. Dans l'exemple ci-dessus, afin de mettre à jour le bloc-hash de "Zone1" sur « Hub » (ou de « Hub » sur « Zone2 »), un IBCBlockCommitTxla transaction doit être publiée sur « Hub » avec le bloc-hash de « Zone1 » (ou sur « Zone2 » avec le bloc-hash de « Hub »). Voir IBCBlockCommitTx et IBCPacketTx pour plus d'informations. sur les deux types de transactions IBC. De la même manière que Bitcoin est plus sécurisé en étant distribué, grand livre répliqué en masse, nous pouvons rendre les échanges moins vulnérables aux hacks externes et internes en l'exécutant sur le blockchain. Nous appelez cela un échange distribué. Ce que la communauté des cryptomonnaies appelle un système décentralisé Aujourd’hui, les échanges sont basés sur ce que l’on appelle des transactions « atomiques crosschain » (AXC). Avec une transaction AXC, deux utilisateurs sur deux chaînes différentes peuvent effectuer deux transactions de transfert qui sont engagés ensemble sur les deux registres, ou aucun (c'est-à-dire atomiquement). Par exemple, deux utilisateurs peuvent échanger des bitcoins contre de l'éther (ou deux token sur deux grands livres différents) en utilisant les transactions AXC, même si Bitcoin et Ethereum ne sont pas connectés l'un à l'autre autre. L'avantage d'exécuter un échange sur les transactions AXC est qu'aucun utilisateur n'a besoin de se faire confiance ni de se faire confiance service. L'inconvénient est que les deux parties doivent être en ligne pour le commerce ait lieu. Un autre type d'échange décentralisé est un échange répliqué en masse. échange distribué qui fonctionne tout seul blockchain. Utilisateurs sur ce type d'échange peut soumettre un ordre limité et transformer son ordinateur éteint, et la transaction peut s'exécuter sans que l'utilisateur soit en ligne. Le blockchain correspond et termine la transaction au nom du commerçant.
Cosmos 架构
Cosmos 是一个独立并行 blockchain 的网络,它们是 每个都由经典的 BFT 共识算法提供支持,例如 嫩薄荷 1. 该网络中的第一个 blockchain 将是 Cosmos 中心。的 Cosmos 集线器通过一个连接到许多其他 blockchain(或区域) 新颖的blockchain间通信协议。 Cosmos 中心 跟踪众多 token 类型并记录总数 每个连接区域中的 token 数量。代币可以是 安全、快速地从一个区域转移到另一个区域 无需在区域之间进行液体交换,因为所有 区域间硬币转账通过 Cosmos 中心。 该架构解决了 blockchain 空间的许多问题 今天面临的问题,例如应用程序互操作性、可扩展性和 无缝升级能力。例如,从 Bitcoind 派生的区域, Go-Ethereum、CryptoNote、ZCash 或任何 blockchain 系统都可以 插入 Cosmos 集线器。这些区域允许 Cosmos 无限扩展以满足全球交易需求。区域还有 对于分布式交换来说,这是一个很棒的 yt,它将得到以下支持: 好吧。 Cosmos 不仅仅是一个分布式账本,而且 Cosmos Hub 不是一个有围墙的花园,也不是宇宙的中心。我们是 为分布式账本的开放网络设计协议 可以作为未来金融系统的新基础, 基于密码学原理、健全的经济学、共识 理论、透明度和问责制。 Cosmos 中心是 Cosmos 中的第一个公共 blockchain 网络,由 Tendermint 的 BFT 共识算法提供支持。的 Tendermint 开源项目诞生于 2014 年,旨在解决 Bitcoin 的工作量证明共识算法的速度、可扩展性和环境问题。通过使用和改进经过验证的
BFT 于 1988 年在 MIT 开发的算法 [20],Tendermint 团队是第一个概念性地演示 proof-of-stake 解决无利害关系问题的加密货币 遭受第一代 proof-of-stake 加密货币的困扰,例如 如 NXT 和 BitShares1.0。 如今,几乎所有 Bitcoin 移动钱包都使用可信服务器来 为他们提供交易验证。这是因为工作量证明需要在执行之前等待许多确认。 事务可以被视为不可逆转地提交。双花攻击已经在诸如 币库。 与其他 blockchain 共识系统不同,Tendermint 提供 即时且可证明安全的移动客户端支付验证。 由于 Tendermint 被设计为根本不会分叉,因此移动 钱包可以接收即时交易确认,这使得 无需信任且实用的支付在智能手机上成为现实。这个 对物联网应用具有重大影响,如 好吧。 Cosmos 中的验证者与 Bitcoin 矿工具有类似的角色,但是 而是使用加密签名进行投票。验证器是 负责提交的安全、专用机器 块。非 validator 可以委托其 staking token(称为 “atoms”)到任何 validator 以赚取部分区块费用和atom 奖励,但如果 委托 validator 被黑客攻击或违反协议。经证实的 Tendermint BFT 共识的安全保证以及抵押品 利益相关者的押金 –validators 和委托人 – 提供 节点和轻客户端的可证明、可量化的安全性。 分布式公共账本应该有一个章程和一个 治理体系。 Bitcoin 依赖于 Bitcoin 基金会并且挖矿来协调升级,但这是一个缓慢的过程。 Ethereum 硬分叉后分裂为 ETH 和 ETC 以解决 DAO 黑客攻击,很大程度上是因为没有事先的社会契约 也没有做出此类决定的机制。 Cosmos Hub 上的验证者和委托者可以投票 可以更改系统预设参数的建议 自动(例如区块gas limit),坐标升级,如 并对人类可读的宪法修正案进行投票 管理 Cosmos 中心的政策。宪法 允许利益相关者在以下问题上保持凝聚力: 盗窃和错误(例如TheDAO事件),允许更快和 更清晰的分辨率。 每个区域也可以有自己的宪法和治理 机制也是如此。例如,Cosmos 集线器可能有一个 强制中心不变性的宪法(无回滚, 保存 Cosmos Hub 节点实现的错误),同时 每个区域都可以设置自己的回滚策略。 通过实现不同政策区域之间的互操作性, Cosmos 网络为其用户提供最终的自由和潜力 未经许可的实验。 在这里,我们描述了一种去中心化和可扩展性的新颖模型。 Cosmos 是一个由许多 blockchain 组成的网络,由 嫩薄荷。虽然现有提案旨在创建“单一 blockchain”,全局交易排序总额为 Cosmos 允许许多 blockchain 彼此同时运行 同时保留互操作性。 在此基础上,Cosmos Hub 管理着许多独立的 blockchain 称为“区域”(有时称为“分片”,在 参考称为“分片”的数据库扩展技术)。
来自发布的区域的最近块提交的持续流 Hub 允许 Hub 跟上每个区域的状态。 同样,每个区域都与集线器的状态保持同步(但区域 除非间接通过 枢纽)。然后,信息包从一个 通过发布默克尔证明作为证据,将区域转移到另一个区域 信息已发送和接收。这种机制被称为 blockchain 间通信,简称 IBC。 任何区域本身都可以成为形成非循环图的中心, 但为了清楚起见,我们只描述简单的 只有一个集线器和许多非集线器的配置 区。 Cosmos 中心是托管多资产的 blockchain 分布式账本,其中 token 可以由个人用户持有或 由区域本身。这些 token 可以从一个区域移动 到另一个特殊的 IBC 数据包中,称为“硬币数据包”。枢纽是 负责保持总的全局不变性 跨区域的每个 token 的数量。 IBC 硬币包 交易必须由发送者、集线器和接收者提交 blockchains。由于 Cosmos Hub 充当整个系统的中央分类账 系统中,Hub 的安全至关重要。同时 每个区域都可以是 Tendermint blockchain,由 as 保护 少至 4 个(如果不需要 BFT 共识,甚至更少),Hub 必须由一组全球分散的 validator 来保证安全 可以承受最严重的攻击场景,例如 大陆网络分区或民族国家发起的攻击。 Cosmos 区域是一个独立的 blockchain,可交换 IBC 与 Hub 的消息。从 Hub 的角度来看,一个区域就是一个 多资产动态会员多重签名账户 可以使用 IBC 数据包发送和接收 tokens。就像一个 加密货币账户,一个区域不能传输超过 tokens 它有,但可以从拥有它们的其他人那里接收 token。 A区 可以被指定为一种或多种 token 类型的“源”, 授予其启动 token 电源的权力。 Cosmos 中心的原子可以由区域的 validator 质押 连接到集线器。虽然对这些区域进行双花攻击 将导致 Tendermint 的 forkaccountability 中的原子被削减,在该区域中,>⅔ 的投票权是 拜占庭可以提交无效状态。 Cosmos 集线器不 验证或执行在其他区域提交的交易,因此 用户有责任将 token 发送到他们信任的区域。 未来Cosmos Hub的治理体系可能会通过Hub 解决区域故障的改进建议。对于 例如,从某些(或所有)区域出站 token 传输可能会 被限制以允许区域紧急断路 (暂时停止 token 传输)当检测到攻击时。 现在我们看看中心和区域如何相互通信 其他。例如,如果有三个blockchain,“Zone1”,“Zone2”,
和“Hub”,我们希望“Zone1”生成一个数据包 “Zone2”穿过“Hub”。从一个数据包中移动一个数据包 blockchain 到另一个,一个证明被发布在接收链上。 该证明表明发送链发布了一个数据包 所谓的目的地。为了让接收链检查这个证明,它 必须能够跟上发送者的块头。这个 机制与侧链使用的机制类似,需要 两个相互作用的链通过 存在性数据报的双向流 (交易)。 IBC 协议自然可以使用两种类型来定义 交易:一个 IBCBlockCommitTx 交易,它允许 blockchain 向任何观察者证明其最新区块-hash, 和一个 IBCPacketTx 交易,它允许 blockchain 向任何观察者证明给定的数据包确实已发布 通过发送者的应用程序,通过对最近的 Merkle 证明 块-hash。 通过将 IBC 机制拆分为两个单独的事务,我们 允许接收链的原生费用市场机制 确定哪些数据包被提交(即确认),同时 允许发送链上完全自由地决定如何 允许许多出站数据包。 上例中,为了更新“Zone1”的块-hash 在“Hub”(或“Zone2”上的“Hub”)上,一个 IBCBlockCommitTx交易必须发布在“Hub”上,区块为hash “Zone1”(或在“Zone2”上,具有“Hub”的块hash)。 有关更多信息,请参阅 IBCBlockCommitTx 和 IBCPacketTx 关于两种 IBC 交易类型。 同样,Bitcoin 通过分布式更安全, 大规模复制的账本,我们可以使交易所不易受到 通过在 blockchain 上运行它来进行外部和内部黑客攻击。我们 称之为分布式交换。 加密货币社区所谓的去中心化 今天的交易所基于所谓的“原子跨链”(AXC)交易。通过 AXC 交易,两个用户 两条不同的链可以进行两笔转账交易 在两个分类账上一起承诺,或者根本没有承诺(即 原子地)。例如,两个用户可以用比特币交换以太币(或 两个不同分类账上的任意两个 token)使用 AXC 交易, 即使 Bitcoin 和 Ethereum 没有连接到每个 其他。在 AXC 交易上运行交易所的好处是 用户不需要互相信任或交易匹配 服务。缺点是双方都需要在线 交易发生。 另一种类型的去中心化交易所是大规模复制的 自行运行的分布式交换 blockchain。用户在 这种交易所可以提交限价订单并将其转为 计算机关闭,无需用户操作即可执行交易 在线。 blockchain 代表匹配并完成交易 交易者的。
Applications
Un échange centralisé peut créer un carnet de commandes important et limité commandes et ainsi attirer plus de commerçants. La liquidité engendre plus liquidité dans le monde des changes, il existe donc un réseau solide effet (ou au moins un effet gagnant-prenant le plus) dans l'échange entreprise. Le leader actuel des échanges de crypto-monnaie aujourd'hui se trouve Poloniex avec un volume sur 24 heures de 20 millions de dollars, et en deuxième position se trouve Bitynex avec un volume sur 24 heures de 5 millions de dollars. Étant donné un réseau aussi solide effets, il est peu probable que les échanges décentralisés basés sur AXC gagner du volume sur les échanges centralisés. Pour une décentralisation bourse pour rivaliser avec une bourse centralisée, il lui faudrait pour prendre en charge des carnets de commandes importants avec des ordres limités. Seulement un distribué un échange sur un blockchain peut fournir cela. Tendermint offre des avantages supplémentaires d'une transaction plus rapide s'engage. En privilégiant la qualité rapide sans sacrifier cohérence, les zones de Cosmos peuvent ynaliser les transactions rapidement – par exemple les transactions d'ordres d'échange ainsi que les transferts IBC token vers et d'autres zones. Compte tenu de l’état actuel des échanges de crypto-monnaie, un grand l'application pour Cosmos est l'échange distribué (alias le Cosmos DEX). La capacité de débit des transactions ainsi que la latence de validation peut être comparable à celle des systèmes centralisés échanges. Les traders peuvent soumettre des ordres limités qui peuvent être exécutés sans que les deux parties n'aient besoin d'être en ligne. Et avec Tendermint, le hub Cosmos et IBC, les traders peuvent transférer des fonds vers et depuis l'échange vers et depuis d'autres zones avec rapidité. Une zone privilégiée peut agir comme source d'un token ponté de une autre crypto-monnaie. Un pont est semblable à la relation entre un hub et une zone Cosmos ; les deux doivent suivre le rythme derniers blocs de l'autre afin de vérifier les preuves que les token ont déplacé de l'un à l'autre. Une "zone-pont" sur le Cosmos le réseau suit le Hub ainsi que les autres
crypto-monnaie. L'indirection à travers la zone du pont permet la logique du Hub pour rester simple et agnostique par rapport aux autres Stratégies consensuelles de blockchain telles que proof-of-work de Bitcoin exploitation minière. Chaque zone de pont validator exécuterait un système alimenté par Tendermint blockchain avec une application de pont spéciale ABCI, mais aussi un nœud complet de l’« origine » blockchain. Lorsque de nouveaux blocs sont extraits à l'origine, la zone de pont validators parviendront à un accord sur les blocs engagés en signant et partageant leur vision locale respective du blockchain d’origine pointe. Lorsqu'une zone-pont reçoit un paiement à l'origine (et il a été convenu que des confirmations suffisantes avaient été vues dans le cas d'une chaîne PoW telle que Ethereum ou Bitcoin), un correspondant un compte est créé sur la zone pont avec ce solde. Dans le cas de Ethereum, la zone pont peut partager la même validator-défini comme hub Cosmos. Du côté Ethereum (le origine), un contrat-relais permettrait aux détenteurs d'éther d'envoyer de l'éther à la zone-pont en l'envoyant au contrat-pont le Ethereum. Une fois que l'éther est reçu par le contrat-pont, le l'éther ne peut pas être retiré à moins qu'un paquet IBC approprié ne soit reçu par le contrat-pont de la zone-pont. Le Le contrat de pont suit l'ensemble validator de la zone de pont, qui peut être identique à l’ensemble validator du Hub Cosmos. Dans le cas de Bitcoin, le concept est similaire sauf qu'au lieu de un seul contrat-relais, chaque UTXO serait contrôlé par un seuil multisignature publication P2SH. En raison des limites de le système P2SH, les signataires ne peuvent pas être identiques aux Cosmos Hub validator-set.L'éther sur la zone pont («bridged-ether») peut être transféré vers et depuis le Hub, puis être détruit avec une transaction qui l'envoie à une adresse de retrait particulière le Ethereum. Un IBC paquet prouvant que la transaction a eu lieu sur la zone pont peut être posté sur le contrat-relais Ethereum pour permettre à l'éther à retirer. Dans le cas de Bitcoin, le système de script restreint permet Il est difficile de reproduire le mécanisme de transfert de pièces IBC. Chaque UTXO a son propre pubscript indépendant, donc chaque UTXO doit être migré vers un nouveau UTXO lorsqu'il y a un changement dans l'ensemble des Bitcoin signataires du dépôt fiduciaire. Une solution consiste à compresser et décompressez l'ensemble UTXO si nécessaire pour conserver le nombre total des UTXOs en panne. Le risque d'un tel contrat de transition est un ensemble validator voyou. ≥⅓ Le pouvoir de vote byzantin pourrait provoquer un fork, retirant l'éther du contrat-pont sur Ethereum tout en gardant le bridgedether sur la zone-pont. Pire encore, >⅔ du pouvoir de vote byzantin peut voler de l'éther à ceux qui l'ont envoyé au contrat-pont en s'écartant de la logique de pontage originale de la zone-pont. Il est possible de résoudre ces problèmes en concevant le pont pour qu'il soit totalement responsable. Par exemple, tous les paquets IBC, provenant du hub et l'origine, pourrait nécessiter une reconnaissance par la zone de pont dans de telle sorte que toutes les transitions d'état de la zone de pont puissent être efficacement contesté et vérifié soit par le hub, soit par l'origine contrat-relais. Le Hub et l'origine devraient permettre aux zones de pont validator de déposer des garanties, et token les transferts hors de la zone de pont. le contrat-relais devrait être retardé (et le détachement des garanties période suffisamment longue) pour permettre d'éventuelles contestations auditeurs indépendants. Nous quittons la conception de la spécification et mise en œuvre de ce système ouvert comme un avenir Cosmos
proposition d'amélioration, à adopter par le Hub Cosmos système de gouvernance. La résolution du problème de mise à l’échelle est un problème ouvert pour Ethereum. Actuellement, les nœuds Ethereum traitent chaque transaction et stocker également tous les états. lien. Puisque Tendermint peut valider des blocs beaucoup plus rapidement que ceux de Ethereum Zones proof-of-work, EVM alimentées par le consensus Tendermint et fonctionnant sur de l'éther ponté peut fournir des performances plus élevées à Ethereum blockchains. De plus, bien que le hub Cosmos et La mécanique des paquets IBC ne permet pas une logique de contrat arbitraire exécution en soi, il peut être utilisé pour coordonner les mouvements token entre les contrats Ethereum fonctionnant sur des zones différentes, fournissant une base pour une mise à l'échelle token centrée sur Ethereum via partage. Les zones Cosmos exécutent une logique d'application arbitraire, définie à le début de la vie de la zone et peut éventuellement être mis à jour au fil du temps par la gouvernance. Une telle zexibilité permet aux zones Cosmos de agir comme des ponts vers d'autres crypto-monnaies telles que Ethereum ou Bitcoin, et il autorise également les dérivés de ces blockchain, en utilisant la même base de code mais avec un ensemble validator différent et distribution initiale. Cela permet à de nombreuses crypto-monnaies existantes frameworks, tels que ceux de Ethereum, Zerocash, Bitcoin, CryptoNote et ainsi de suite, à utiliser avec Tendermint Core, qui est un moteur de consensus plus performant, sur un réseau commun, ouvrant une formidable opportunité d’interopérabilité à travers plates-formes. De plus, en tant que blockchain multi-actifs, un seul La transaction peut contenir plusieurs entrées et sorties, où chacune l'entrée peut être n'importe quel type token, permettant à Cosmos de servir directement de une plateforme d'échange décentralisé, bien que les commandes soient assuméesà égaler via d'autres plateformes. Alternativement, une zone peut servir en tant qu'échange distribué tolérant aux pannes (avec carnets de commandes), qui peut être une amélioration stricte par rapport au système centralisé existant échanges de crypto-monnaie qui ont tendance à être piratés au fil du temps. Les zones peuvent également servir de versions d'entreprise soutenues par blockchain et les systèmes gouvernementaux, où les éléments d'un service particulier qui sont traditionnellement gérés par une organisation ou un groupe d’organisations sont plutôt exécutés en tant qu'application ABCI sur une certaine zone, ce qui lui permet d'hériter de la sécurité et de l'interopérabilité du public Cosmos réseau sans sacrifier le contrôle sur le sous-jacent service. Ainsi, Cosmos peut offrir le meilleur des deux mondes pour les organisations qui cherchent à utiliser la technologie blockchain mais qui sont se méfier de céder complètement le contrôle à un tiers distribué fête. Certains affirment qu'un problème majeur lié à la recherche de cohérence les algorithmes de consensus comme Tendermint sont que n'importe quel réseau partition qui fait qu'il n'y a pas de partition unique avec >⅔ le pouvoir de vote (par exemple ≥⅓ du magazine) mettra complètement fin au consensus. L'architecture Cosmos peut aider à atténuer ce problème en utilisant une plaque tournante mondiale avec des zones régionales autonomes, où le pouvoir de vote pour chaque zone sont répartis selon une répartition géographique commune région. Par exemple, un paradigme commun peut être celui d'un individu villes, ou régions, d'exploiter leurs propres zones tout en partageant un pôle commun (par exemple le Hub Cosmos), permettant à l'activité municipale de persister dans le cas où le hub s'arrête en raison d'un réseau temporaire partition. Notons que cela permet de réelles conséquences géologiques, politiques et caractéristiques topologiques de réseau à prendre en compte dans la conception de systèmes robustes systèmes fédérés tolérants aux pannes.
NameCoin a été l'un des premiers blockchain à tenter de résoudre le problème. problème de résolution de nom en adaptant le Bitcoin blockchain. Malheureusement, cette approche a posé plusieurs problèmes. Avec Namecoin, on peut vérifier que, par exemple, @satoshi était enregistré avec une clé publique particulière à un moment donné dans le passé, mais nous ne saurions pas si la clé publique a été mis à jour récemment sauf si nous téléchargeons tous les blocs depuis le dernier mise à jour de ce nom. Cela est dû à la limitation de Bitcoin UTXO modèle de Merkle-isation des transactions, où seul le les transactions (mais pas l'état d'application mutable) sont Merkle-isées dans le bloc-hash. Cela nous permet de prouver l'existence, mais pas la non-existence de mises à jour ultérieures d'un nom. Ainsi, nous ne pouvons pas savoir pour certain de la valeur la plus récente d'un nom sans faire confiance à un nœud, ou encourir des coûts importants en bande passante en téléchargeant le tout blockchain. Même si un arbre de recherche Merkle était implémenté dans NameCoin, sa dépendance à proof-of-work rend la vérification client légère problématique. Les clients légers doivent télécharger une copie complète du en-têtes pour tous les blocs de l'ensemble du blockchain (ou au moins de tous les en-têtes depuis la dernière mise à jour d'un nom). Cela signifie que le les besoins en bande passante évoluent de manière linéaire avec le temps [21]. De plus, les changements de nom sur un proof-of-work blockchain nécessite d'attendre des blocs de confirmation proof-of-work supplémentaires, ce qui peut prendre jusqu'à une heure le Bitcoin. Avec Tendermint, tout ce dont nous avons besoin est le bloc le plus récent -hash signé par un quorum de validators (par droit de vote) et un Merkle preuve à la valeur actuelle associée au nom. Cela fait possible d'avoir un client léger succinct, rapide et sécurisé vérification des valeurs de nom. Dans Cosmos, nous pouvons reprendre ce concept et l'étendre davantage. Chacun La zone d'enregistrement de nom dans Cosmos peut avoir un nom de domaine de premier niveau (TLD) associé tel que « .com » ou « .org », et chaque nom-
la zone d'enregistrement peut avoir sa propre gouvernance et son propre enregistrement règles.
应用领域
中心化交易所可以创建深度限价订单簿 订单,从而吸引更多的交易者。流动性产生更多 交易所世界的流动性,因此有强大的网络 交换中的效应(或至少是赢家通吃的效应) 业务。当今加密货币交易所的当前领导者 Poloniex 的 24 小时交易量为 2000 万美元,位居第二的是 Bitynex 24 小时交易量为 500 万美元。鉴于如此强大的网络 影响,基于 AXC 的去中心化交易所不太可能 赢得中心化交易所的交易量。对于去中心化的 交易所要与中心化交易所竞争,需要 支持带有限价订单的深度订单簿。只有一个分布式 blockchain 上的交换可以提供这一点。 Tendermint 提供更快交易的额外好处 承诺。通过优先考虑快速性而不牺牲 一致性,Cosmos 中的区域可以快速分析事务 – 用于 交换订单交易以及 IBC token 转账至 以及来自其他区域的。 鉴于当今加密货币交易所的状况,一个伟大的 Cosmos 的应用程序是分布式交换(又名 Cosmos DEX)。交易吞吐能力以及 提交延迟可以与集中式的延迟相媲美 交流。交易者可以提交可以执行的限价订单 无需双方都在线。和 Tendermint 一起, Cosmos 中心和 IBC,交易者可以将资金转入和转出 与其他区域的快速交换。 特权区域可以充当桥接 token 的源 另一种加密货币。桥梁类似于关系 Cosmos 中心和区域之间;两者都必须跟上 另一个的最新区块,以验证 tokens 拥有的证据 从一个移动到另一个。 Cosmos 上的“桥接区” 网络与集线器以及其他设备保持同步
加密货币。通过桥接区的间接允许 中心的逻辑保持简单并且与其他人无关 blockchain 共识策略,例如 Bitcoin 的 proof-of-work 采矿。 每个桥区 validator 将运行由 Tendermint 驱动的 blockchain 具有特殊的 ABCI 桥接应用程序,而且也是一个全节点 “起源”blockchain。 当在原点开采新区块时,桥接区 validators 将通过签名就承诺区块达成一致 并分享他们各自对原产地 blockchain 的本地看法 小费。当桥接区域在来源处收到付款时(以及 已同意在本案中看到足够的确认 PoW 链(例如 Ethereum 或 Bitcoin),相应的 帐户是在桥接区域上用该余额创建的。 在 Ethereum 的情况下,桥接区域可以共享相同的 validator-设置为 Cosmos 集线器。在 Ethereum 一侧( 起源),桥接合约将允许以太币持有者发送以太币 通过将其发送到桥接合约来发送到桥接区 Ethereum。一旦桥接合约收到以太币, 除非有适当的 IBC 数据包,否则无法提取以太币 由桥接合同从桥接区接收。的 桥接合约跟踪桥接区域的 validator 集,其中 可能与 Cosmos 集线器的 validator 集相同。 在 Bitcoin 的情况下,概念类似,只不过不是 一个桥梁合约,每个 UTXO 将由 阈值多重签名 P2SH pubscript。由于限制 P2SH 系统中,签名者不能与 Cosmos 相同 轮毂 validator-套。桥接区域上的以太币(“桥接以太币”)可以转移到 并从中心,然后通过交易销毁 将其发送到 Ethereum 上的特定提款地址。 IBC 证明事务发生在桥接区域的数据包 可以发布到 Ethereum 桥接合约以允许以太币 被撤回。 在 Bitcoin 的情况下,受限脚本系统使其 很难反映 IBC 硬币转移机制。每个 UTXO 有自己独立的pubscript,因此每个 UTXO 必须是 当集合发生变化时迁移到新的 UTXO Bitcoin 托管签名者。一种解决方案是压缩并 根据需要解压 UTXO-set 以保留总数 UTXO 秒下降。 这种桥接合约的风险是流氓 validator 集。 ≥⅓ 拜占庭投票权可能会导致分叉,提取以太币 来自 Ethereum 的桥接合约,同时将桥接以太币保持在桥接区域。更糟糕的是,>⅔ 拜占庭投票权可以 从发送到桥接合约的人那里直接窃取以太币 偏离了桥接区的原始桥接逻辑。 可以通过设计桥梁来解决这些问题 完全负责。例如,来自集线器的所有 IBC 数据包和 起源,可能需要桥接区的确认 这样桥区的所有状态转换都可以 受到枢纽或始发地的有效挑战和验证 过桥合同。中心和来源应允许桥区 validators 发布抵押品,并且 token 转出 过渡合同应该被推迟(并且抵押品解绑 足够长的时间)以允许提出任何挑战 独立审计师。我们留下规格的设计和 该系统的实施作为未来开放 Cosmos
改进提案,由 Cosmos 中心通过 治理体系。 解决缩放问题是 Ethereum 的一个悬而未决的问题。 目前,Ethereum 节点处理每笔交易并 还存储所有状态。关联。 由于 Tendermint 提交区块的速度比 Ethereum 快得多 proof-of-work、EVM 由 Tendermint 共识支持的区域和 在桥接以太网上运行可以提供更高的性能 Ethereum blockchains。此外,虽然 Cosmos 集线器和 IBC 数据包机制不允许任意合约逻辑 执行本身,它可用于协调 token 运动 在不同区域运行的 Ethereum 合约之间, 为以 token 为中心的 Ethereum 扩展提供基础 分片。 Cosmos 区域运行任意应用程序逻辑,其定义为 该区域生命的开始,并且有可能更新 随着时间的推移,通过治理。这种灵活性允许 Cosmos 区域 充当其他加密货币的桥梁,例如 Ethereum 或 Bitcoin,并且它还允许这些 blockchain 的衍生物, 使用相同的代码库但具有不同的 validator 集并且 初始分布。这使得许多现有的加密货币 框架,例如 Ethereum、Zerocash、Bitcoin 的框架, CryptoNote 等,与 Tendermint Core 一起使用, 在公共网络上更高性能的共识引擎, 为跨领域的互操作性提供了巨大的机会 平台。此外,作为多资产 blockchain,单一资产 交易可能包含多个输入和输出,其中每个 输入可以是任何 token 类型,使 Cosmos 能够直接用作 去中心化交易平台,但假设有订单通过其他平台进行匹配。或者,区域可以服务 作为分布式容错交易所(带有订单簿), 可以是对现有集中式的严格改进 随着时间的推移,加密货币交易所往往会遭到黑客攻击。 区域还可以用作 blockchain 支持的企业版本 和政府系统,其中特定服务的各个部分 传统上由一个组织或一组组织运营 相反,它们作为 ABCI 应用程序在某个区域上运行, 让它继承大众的安全性和互操作性 Cosmos 网络而不牺牲对底层的控制 服务。因此,Cosmos 可能会提供两全其美的方案: 希望利用 blockchain 技术但谁是的组织 警惕将控制权完全交给分布式第三方 聚会。 一些人声称,有利于一致性的一个主要问题是 像 Tendermint 这样的共识算法是任何网络 分区导致不存在 >⅔ 的单个分区 投票权(例如≥⅓)将完全停止共识。 Cosmos 架构可以通过使用来帮助缓解这个问题 拥有区域自治区的全球中心,拥有投票权 每个区域都根据共同的地理分布 地区。例如,一个共同的范式可能适用于个人 城市或地区在共享资源的同时运营自己的区域 公共中心(例如 Cosmos 中心),使市政活动能够 在集线器由于临时网络而停止的情况下继续存在 分区。请注意,这允许真实的地质、政治和 设计鲁棒性时要考虑的网络拓扑特征 联合容错系统。
NameCoin 是第一个尝试解决这个问题的 blockchain 之一 通过调整 Bitcoin blockchain 来解决名称解析问题。 不幸的是,这种方法存在几个问题。 通过 Namecoin,我们可以验证,例如,@satoshi 是 在过去的某个时刻使用特定的公钥注册, 但我们不知道公钥是否已经被 最近更新,除非我们下载自上次以来的所有块 该名称的更新。这是由于 Bitcoin 的限制 UTXO 交易默克尔化模型,其中只有 交易(但不是可变的应用程序状态)是 Merkle 化的 进入块-hash。这让我们可以证明名称的存在,但不能证明名称的后续更新不存在。因此,我们无法得知 确定名称的最新值而不信任完整的 节点,或者通过下载产生大量带宽成本 整个blockchain。 即使在 NameCoin 中实现了 Merkle 化的搜索树, 它对 proof-of-work 的依赖使得轻客户端验证 有问题的。轻客户端必须下载完整的副本 整个 blockchain 中所有块的标头(或者至少是所有 自上次更新名称以来的标题)。这意味着 带宽需求随时间量线性变化 [21]。此外,proof-of-work blockchain 上的名称更改 需要等待额外的 proof-of-work 确认块, Bitcoin 上最多可能需要一个小时。 对于 Tendermint,我们只需要最新的区块 -hash 由 validator 的法定人数(通过投票权)和 Merkle 签署 证明与该名称关联的当前值。这使得 可以拥有一个简洁、快速、安全的轻客户端 名称值的验证。 在Cosmos中,我们可以采用这个概念并进一步扩展它。每个 Cosmos 中的名称注册区域可以有一个关联的顶级域 (TLD) 名称,例如“.com”或“.org”,并且每个名称-
注册区可以有自己的治理和注册 规则。
Gouvernance et économie
Bien que le Cosmos Hub soit un grand livre distribué multi-actifs, il existe un token natif spécial appelé l'atome. Les atomes sont les seuls staking token du hub Cosmos. Les atomes sont une licence pour le détenteur de voter, valider ou déléguer à d'autres validator. Comme celui de Ethereum éther, les atomes peuvent également être utilisés pour payer les frais de transaction pour atténuer le spam. Atomes inzationnaires supplémentaires et transaction de bloc les honoraires sont récompensés aux validator et aux délégataires qui délèguent à validators. La transaction BurnAtomTx peut être utilisée pour récupérer n'importe quel montant proportionnel de tokens provenant du pool de réserve. La distribution initiale des atomes token et validator sur Genesis ira aux donateurs de la collecte de fonds Cosmos (75 %), principaux donateurs (5 %), Cosmos Network Foundation (10 %) et ALL IN BITS, Inc. (10%). À partir de la genèse, 1/3 de la quantité totale d'atomes sera être récompensé chaque année par les validator et les délégués cautionnés. Consultez le plan Cosmos pour plus de détails. Contrairement à Bitcoin ou à d'autres proof-of-work blockchain, un Tendermint blockchain devient plus lent avec plus de validator en raison de l'augmentation complexité des communications. Heureusement, nous pouvons soutenir suffisamment validators pour créer un blockchain robuste distribué à l'échelle mondiale avec des temps de confirmation des transactions très rapides et, comme bande passante,
stockage et la capacité de calcul parallèle augmente, nous pourrons pour prendre en charge davantage de validator à l'avenir. Le jour de la genèse, le nombre maximum de validator sera fixé à 100, et ce nombre augmentera au rythme de 13% pendant 10 ans, et s'établir à 300 validators. Les détenteurs d'atomes qui ne le sont pas déjà peuvent devenir validator en signer et soumettre une transaction BondTx . Le montant de les atomes fournis en garantie doivent être différents de zéro. N'importe qui peut devenir un validator à tout moment, sauf lorsque la taille du courant L'ensemble validator est supérieur au nombre maximum de validator. autorisé. Dans ce cas, la transaction n'est valable que si le montant de Le nombre d’atomes est supérieur à la quantité d’atomes effectifs détenus par le le plus petit validator, où les atomes efficaces incluent les atomes délégués. Lorsqu'un nouveau validator remplace un validator existant de cette manière, le validator existant devient inactif et tous les atomes et les atomes délégués entrent dans l’état de déliaison. Une pénalité doit être imposée aux validator pour tout déviation intentionnelle ou non des règles sanctionnées protocole. Certaines preuves sont immédiatement recevables, comme une double signe à la même hauteur et rond, ou une violation de Année 0 : 100 Année 1 : 113 Année 2 : 127 Année 3 : 144 Année 4 : 163 Année 5 : 184 Année 6 : 208 Année 7 : 235 Année 8 : 265 Année 9 : 300 Année 10 : 300 ...
« empêcher le verrouillage » (une règle du protocole de consensus Tendermint). Une telle preuve entraînera la perte de la réputation du validator. et ses atomes liés ainsi que sa part proportionnelle de tokens dans le pool de réserve – collectivement appelé sa « mise » – sera réduit. Parfois, les validator ne seront pas disponibles, soit en raison de conditions régionales perturbations du réseau, panne de courant ou autres raisons. Si, à tout moment point dans les blocs ValidatorTimeoutWindow passés, un validator le vote de validation n'est pas inclus dans le blockchain plus de ValidatorTimeoutMaxAbsent fois, ce validator deviendra inactif et perdez ValidatorTimeoutPenalty (DEFAULT 1 %) de son enjeu. Certains comportements « malveillants » ne produisent pas d’effets visiblement perceptibles. preuve sur le blockchain. Dans ces cas, les validator peuvent coordonner hors bande pour forcer l'expiration du délai d'attente de ces éléments malveillants validators, s'il existe un consensus à la grande majorité. Dans les situations où le Hub Cosmos s'arrête en raison d'une coalition ≥⅓ de le pouvoir de vote disparaît, ou dans des situations où une coalition ≥⅓ des pouvoirs de vote censurent les preuves de comportement malveillant de la part de en entrant dans le blockchain, le hub doit récupérer avec un hard-fork proposition de réorganisation. (Lien vers « Forks et attaques de censure »). Les hubs Cosmos validator peuvent accepter n'importe quel type ou combinaison de token de types comme frais de traitement d’une transaction. Chaque validator peut fixer subjectivement le taux de change qu'il souhaite et choisir quelles que soient les transactions souhaitées, à condition que le BlockGasLimit soit pas dépassé. Les frais perçus, déduction faite des éventuelles taxes précisées ci-dessous, sont redistribués aux parties prenantes cautionnées au prorata de leurs atomes liés, chaque ValidatorPayoutPeriod (DEFAULT 1 heure).Parmi les frais de transaction collectés, ReserveTax (2 % PAR DÉFAUT) sera allez vers la réserve pour augmenter la réserve et augmenter la sécurité et la valeur du réseau Cosmos. Ces les fonds peuvent également être distribués conformément aux décisions faite par le système de gouvernance. Détenteurs d'atomes qui délèguent leur pouvoir de vote à d'autres validator verser une commission au délégué validator. La commission peut être défini par chaque validator. La sécurité du hub Cosmos est fonction de la sécurité du sous-jacents aux validator et au choix de la délégation par les délégants. Afin d'encourager la découverte et la déclaration précoce des espèces trouvées vulnérabilités, le Cosmos Hub encourage les pirates à publier exploits réussis via une transaction ReportHackTx qui dit : "Ceci validator a été piraté. Veuillez envoyer la prime à cette adresse ». Sur un tel exploit, le validator et les délégants deviendront inactifs, HackPunishmentRatio (par défaut 5 %) des atomes de chacun obtiendront réduit et HackRewardRatio (par défaut 5 %) des atomes de chacun sera récompensé à l’adresse de prime du pirate informatique. Le validator doit récupérer les atomes restants en utilisant leur clé de sauvegarde. Afin d'éviter que cette fonctionnalité ne soit utilisée de manière abusive pour transférer atomes non investis, la proportion d'atomes investis et non investis de Les validator et les délégants avant et après le ReportHackTx resteront les mêmes, et la prime des hackers inclura certains atomes non investis, le cas échéant. Le hub Cosmos est exploité par une organisation distribuée qui nécessite un mécanisme de gouvernance bien défini afin de coordonner divers changements au blockchain, comme la variable
paramètres du système, ainsi que les mises à niveau logicielles et amendements constitutionnels. Tous les validator sont responsables du vote sur toutes les propositions. A défaut de voter sur une proposition en temps opportun entraînera le validator étant automatiquement désactivé pendant une période de temps appelée AbsenteeismPenaltyPeriod (PAR DÉFAUT 1 semaine). Les délégués héritent automatiquement du vote du délégué validator. Ce vote peut être annulé manuellement. Atomes non liés n'obtenez aucun vote. Chaque proposition nécessite un dépôt de MinimumProposalDeposit tokens, qui peuvent être une combinaison d'un ou plusieurs tokens y compris les atomes. Pour chaque proposition, les électeurs peuvent voter pour prendre le dépôt. Si plus de la moitié des électeurs choisissent de voter dépôt (par exemple parce que la proposition était du spam), le dépôt va à le pool de réserve, à l’exception des atomes brûlés. Pour chaque proposition, les électeurs peuvent voter avec les options suivantes : Ouais OuiAvecForce Non NonAvecForce S'abstenir Une stricte majorité de votes Oui ou OuiAvecForce (ou Non ou Votes NayWithForce) est requis pour que la proposition soit décidée comme réussi (ou décidé comme échec), mais 1/3+ peut opposer son veto à la majorité décision en votant « avec force ». Lorsqu'on oppose son veto à une majorité stricte, tout le monde est puni en perdant VetoPenaltyFeeBlocks (PAR DÉFAUT 1 jour de blocs) de frais (sauf taxes qui ne sera pas affecté), et le parti qui a opposé son veto à la majorité
la décision sera en outre punie par la perte de VetoPenaltyAtoms (PAR DÉFAUT 0,1%) de ses atomes. N'importe lequel des paramètres définis ici peut être modifié avec le transmission d'une ParameterChangeProposal . Les atomes peuvent être inzés et les fonds du pool de réserve dépensés avec le adoption d'une BountyProposal . Toutes les autres propositions, comme une proposition de mise à niveau du protocole, sera coordonné via la TextProposal générique. Voir le Plan. Il y a eu de nombreuses innovations dans le consensus blockchain et évolutivité au cours des deux dernières années. Cette section fournit un bref enquête sur un certain nombre de sujets importants. Le consensus en présence de participants malveillants est un problème datant du début des années 1980, lorsque Leslie Lamport a inventé le expression « faute byzantine » pour faire référence à un comportement de processus arbitraire qui s'écarte du comportement prévu, contrairement à un « défaut de crash », dans lequel un processus plante tout simplement. Des premières solutions ont été découvertes pour les réseaux synchrones où il existe une limite supérieure surlatence des messages, bien que l'utilisation pratique soit limitée à des environnements contrôlés tels que les contrôleurs d’avion et centres de données synchronisés via des horloges atomiques. Ce n'est que lorsque fin des années 90, la tolérance aux pannes byzantine pratique (PBFT) [11] était présenté comme un consensus efficace partiellement synchrone algorithme capable de tolérer jusqu'à ⅓ des processus se comportant arbitrairement. PBFT est devenu l'algorithme standard, engendrant de nombreuses variantes, dont la plus récente créée par IBM dans le cadre de leur contribution à Hyperledger. Le principal avantage du consensus Tendermint sur PBFT est que Tendermint a une structure sous-jacente améliorée et simplifiée, dont certains sont le résultat de l’adoption du paradigme blockchain. Les blocs Tendermint doivent être validés dans l'ordre, ce qui évite le complexité et surcharge de communication associées aux PBFT changements de vue. Dans Cosmos et dans de nombreuses crypto-monnaies, il n'y a pas il faut autoriser le bloc N+i où i >= 1 à valider, lorsque le bloc N lui-même ne s’est pas encore engagé. Si la bande passante est la raison pour laquelle le bloc N ne s'est pas engagé dans une zone Cosmos, alors cela ne sert à rien d'utiliser votes de partage de bande passante pour les blocs N+i. Si une partition réseau ou ofzine nodes est la raison pour laquelle le bloc N n'a pas été validé, alors N+je ne m’engagerai pas de toute façon. De plus, le regroupement des transactions en blocs permet Merkle-hashing régulier de l'état de l'application, plutôt que des résumés périodiques comme avec le schéma de points de contrôle de PBFT. Cela permet pour des validations de transactions prouvables plus rapides pour les clients légers et plus rapides communication inter-blockchain. Tendermint Core comprend également de nombreuses optimisations et fonctionnalités qui vont au-delà de ce qui est spécifié dans PBFT. Par exemple, les blocs proposés par validators sont découpés en parties, Merkle-isées, et bavardé d'une manière qui améliore la diffusion performances (voir LibSwift [19] pour l'inspiration). Aussi, menthe tendre Core ne fait aucune hypothèse sur le point à point
connectivité et fonctionne aussi longtemps que le réseau P2P est faiblement connecté. Bien que ce ne soit pas la première année à déployer proof-of-stake (PoS), BitShares1.0 [12] contribué considérablement à la recherche et à l’adoption du PoS blockchain, en particulier ceux dits PoS « délégués ». Dans BitShares, les actionnaires élisent des "témoins", chargés de passer commande et commettre des transactions, et des « délégués », chargés de coordonner les mises à jour logicielles et les modifications de paramètres. BitShares2.0 vise à atteindre des performances élevées (100 000 tx/s, 1 s latence) dans des conditions idéales, chaque bloc étant signé par un seul signataire et la qualité de la transaction prend un peu plus de temps que le intervalle de bloc. Une spécification canonique est encore en développement. Les parties prenantes peuvent supprimer ou remplacer les témoins qui se comportent mal lors d'une réunion. quotidiennement, mais il n'y a pas de garantie significative de témoins ou des délégataires à l'image de Tendermint PoS qui sont coupés le cas d’une attaque réussie à double dépense. S'appuyant sur une approche lancée par Ripple, Stellar [13] a créé un modèle d'accord byzantin fédéré dans lequel les processus la participation au consensus ne constitue pas un objectif fixe et global ensemble connu. Au lieu de cela, chaque nœud de processus gère un ou plusieurs des « tranches de quorum », chacune constituant un ensemble de processus de confiance. Un Le « quorum » dans Stellar est défini comme étant un ensemble de nœuds qui contiennent au au moins une tranche de quorum pour chaque nœud de l'ensemble, tel que un accord peut être trouvé. La sécurité du mécanisme Stellar repose sur l'hypothèse que l'intersection de deux quorums quelconques n'est pas vide, tandis que le la disponibilité d'un nœud nécessite au moins une de ses tranches de quorum pour se composent entièrement de nœuds corrects, créant un compromis entre en utilisant des tranches de quorum grandes ou petites qui peuvent être difficiles à équilibrer sans imposer d’hypothèses significatives sur la confiance. Finalement,les nœuds doivent d'une manière ou d'une autre choisir des tranches de quorum adéquates pour y parvenir. être suffisamment tolérant aux pannes (ou à tout « nœuds intacts », dont dont dépendent une grande partie des résultats de l'article), et le seul la stratégie fournie pour garantir qu'une telle conyguration est hiérarchique et similaire au Border Gateway Protocol (BGP), utilisé par les meilleurs FAI sur Internet pour établir des tables de routage globales, et par celui utilisé par les navigateurs pour gérer les certificats TLS ; tous deux notoires pour leur insécurité. Les critiques formulées dans l'article Stellar concernant les systèmes de preuve de participation basés sur Tendermint sont atténuées par la stratégie token décrite. ici, dans lequel un nouveau type de token appelé atome est émis qui représentent des réclamations sur des portions futures de frais et de récompenses. Le L'avantage de proof-of-stake basé sur Tendermint est donc son relatif simplicité, tout en offrant une sécurité suffisante et prouvable garanties. BitcoinNG est une amélioration proposée à Bitcoin qui permettrait pour les formes d'évolutivité verticale, telles que l'augmentation de la taille des blocs, sans les conséquences économiques négatives généralement associées avec un tel changement, comme l'impact disproportionné sur les petits mineurs. Cette amélioration est obtenue en séparant élection du leader à partir de la diffusion de la transaction : les dirigeants sont les premiers élu par proof-of-work en « micro-blocs », et pouvoir alors transactions de diffusion à valider jusqu'à un nouveau micro-bloc est trouvé. Cela réduit les besoins en bande passante nécessaires pour gagner la course PoW, permettant aux petits mineurs de concourir plus équitablement, et permettre que les transactions soient commises plus régulièrement par le dernier mineur à trouver un micro-bloc. Casper [16] est un algorithme de consensus proof-of-stake proposé pour Ethereum. Son principal mode de fonctionnement est le « consensus par pari ». Par laisser validators parier de manière itérative sur le bloc qui, selon eux, sera
s'engager dans le blockchain en fonction des autres paris qu'ils ont vu jusqu'à présent, la ynalité peut éventuellement être atteinte. lien. Il s’agit d’un domaine de recherche actif de l’équipe Casper. Le Le défi consiste à construire un mécanisme de pari qui puisse être s'est avérée être une stratégie évolutive stable. Le principal avantage de Casper, par rapport à Tendermint, pourrait offrir une « disponibilité » sur la cohérence » – le consensus n’exige pas un quorum >⅔ de pouvoir de vote – peut-être au détriment de la vitesse de validation ou complexité de mise en œuvre. Le protocole Interledger [14] n'est pas strictement une solution d'évolutivité. Il fournit une interopération ad hoc entre différents registres systèmes à travers un réseau de relations bilatérales faiblement couplées. À l'instar du Lightning Network, l'objectif d'ILP est de faciliter paiements, mais il se concentre spécifiquement sur les paiements à travers des types de grand livre et étend le mécanisme de transaction atomique à inclure non seulement des hash-serrures, mais également un quorum de notaires (appelé le Protocole de Transport Atomique). Ce dernier mécanisme pour l'application de l'atomicité dans les transactions inter-grands livres est similaire à Le mécanisme SPV client léger de Tendermint, donc une illustration du la distinction entre ILP et Cosmos/IBC est justifiée, et fournis ci-dessous. 1. Les notaires d'un connecteur en ILP ne prennent pas en charge l'adhésion changements et ne permettent pas une pondération zexible entre notaires. D'autre part, IBC est conçu spécifiquement pour blockchains, où validators peuvent avoir des poids différents, et où l'adhésion peut changer au cours de la blockchain. 2. Comme dans Lightning Network, le destinataire du paiement en ILP doit être en ligne pour renvoyer une confirmation à l'expéditeur. Dans untoken transfert via IBC, l'ensemble validator du récepteur blockchain est responsable de fournir la confirmation, et non le utilisateur récepteur. 3. La différence la plus frappante est que les connecteurs d'ILP ne sont pas responsable ou gardant l'autorité en matière de paiements, alors que dans Cosmos, les validator d'un hub sont l'autorité de l'état des transferts IBC token ainsi que l'autorité du montant de tokens détenu par chaque zone (mais pas le montant de tokens détenus par chaque compte dans une zone). C'est le innovation fondamentale qui permet une sécurité asymétrique transfert de token de zone en zone ; l'analogue des ILP Le connecteur dans Cosmos est un connecteur persistant et sécurisé au maximum. Grand livre blockchain, le hub Cosmos. 4. Les paiements inter-grand livre dans ILP doivent être garantis par un carnet d’ordres de change, car il n’y a pas de transfert asymétrique de pièces de monnaie d'un registre à un autre, seul le transfert de valeur ou équivalents du marché. Les sidechains [15] sont un mécanisme proposé pour faire évoluer le Bitcoin réseau via des blockchain alternatifs qui sont « rattachés dans les deux sens » à le Bitcoin blockchain. (L'ancrage bidirectionnel équivaut à pontage. Dans Cosmos, nous disons « bridging » pour distinguer le marketpegging). Les sidechains permettent aux bitcoins de passer efficacement du Bitcoin blockchain au sidechain et à l'arrière, et permettre expérimentation de nouvelles fonctionnalités sur la sidechain. Comme dans le Cosmos Hub, la sidechain et Bitcoin servent de clients légers de les uns les autres, en utilisant des preuves SPV pour déterminer quand les pièces doivent être transféré à la sidechain et inversement. Bien sûr, depuis Bitcoin utilise proof-of-work, les sidechains centrés autour de Bitcoin souffrent des nombreux problèmes et risques de proof-of-work en tant que mécanisme de consensus. De plus, c'est un Bitcoin-maximaliste solution qui ne prend pas en charge nativement une variété de token et
topologie de réseau inter-zones comme le fait Cosmos. Cela dit, le noyau le mécanisme de la cheville à double sens est en principe le même que celui employé par le réseau Cosmos. Ethereum recherche actuellement un certain nombre de stratégies différentes pour fragmenter l'état du Ethereum blockchain pour répondre besoins d’évolutivité. Ces efforts ont pour objectif de maintenir couche d'abstraction offerte par la machine virtuelle Ethereum actuelle à travers l’espace d’état partagé. De multiples efforts de recherche sont en cours à ce moment. [18][22] Cosmos et Ethereum 2.0 Mauve [22] ont des objectifs de conception différents. Cosmos concerne spécifiquement les token. Mauve est une question de mise à l'échelle calcul général. Cosmos n'est pas lié à EVM, donc même différentes machines virtuelles peuvent interopérer. Cosmos permet au créateur de la zone de déterminer qui valide la zone. N'importe qui peut créer une nouvelle zone dans Cosmos (sauf si la gouvernance en décide autrement). Le hub isole les défaillances de zone afin que les invariants globaux token soient préservé. Le réseau Lightning est un réseau de transfert proposé token fonctionnant à une couche au-dessus du Bitcoin blockchain (et d'autres blockchains), permettant une amélioration de plusieurs ordres de grandeur dans le débit des transactions en déplaçant la majorité des transactions en dehors du registre consensuel vers ce que l’on appelle les « canaux de paiement ».Ceci est rendu possible par les scripts de crypto-monnaie en chaîne, qui permettre aux parties de conclure des contrats étatiques bilatéraux dans lesquels l'état peut être mis à jour en partageant des signatures numériques et des contrats peut être clôturé en publiant ynally des preuves sur le blockchain, un mécanisme popularisé pour la première fois par les échanges atomiques inter-chaînes. Par ouvrir des canaux de paiement avec de nombreuses parties, participants au Lightning Network peut devenir des points focaux pour le routage des paiements de tiers, conduisant à un canal de paiement entièrement connecté réseau, au prix d’un capital immobilisé sur les canaux de paiement. Bien que le réseau Lightning puisse également s'étendre facilement sur plusieurs blockchain indépendants pour permettre le transfert de valeur via un marché des changes, il ne peut pas être utilisé pour transférer des token d'un blockchain à un autre. Le principal avantage du réseau Cosmos décrit ici est de permettre une telle token transferts. Cela dit, nous nous attendons à ce que les canaux de paiement et le Lightning Network sera largement adopté avec notre Mécanisme de transfert token, pour des raisons d'économie et de confidentialité. Le témoin séparé est un lien de proposition d'amélioration Bitcoin qui vise à augmenter le débit de transaction par bloc de 2X ou 3X, tout en accélérant simultanément la synchronisation des blocs pour les nouveaux nœuds. Le génie de cette solution réside dans la façon dont elle fonctionne au sein du limitations du protocole actuel de Bitcoin et permet un soft-fork mise à niveau (c'est-à-dire que les clients avec des versions plus anciennes du logiciel seront continuer à fonctionner après la mise à niveau). Tendermint, étant un nouveau protocole, n'a aucune restriction de conception, il a donc une mise à l'échelle différente priorités. Principalement, Tendermint utilise un algorithme round-robin BFT basé sur des signatures cryptographiques au lieu du minage, ce qui permet trivialement une mise à l'échelle horizontale à travers plusieurs parallèles blockchains, tandis que les validations de bloc régulières et plus fréquentes permettent mise à l'échelle verticale également.
治理与经济
虽然 Cosmos Hub 是一个多资产分布式账本,但 一个特殊的原生 token 称为原子。原子是唯一的 staking Cosmos 中心的 token。原子是持有者的许可证 投票、验证或委托给其他 validator。就像 Ethereum 的 以太,原子也可以用来支付交易费用 减少垃圾邮件。额外的信息原子和区块交易 费用奖励给 validator 和委托给的委托人 validators。 BurnAtomTx 交易可用于恢复任何 从储备池中按比例分配 token。 Genesis 上原子 tokens 和 validators 的初始分布 将捐给 Cosmos 筹款活动的捐助者 (75%),主要捐助者 (5%)、Cosmos 网络基金会 (10%) 和 ALL IN BITS, Inc (10%)。从创世开始,原子总数的 1/3 将 每年都会奖励给绑定的 validator 和委托人。 有关更多详细信息,请参阅 Cosmos 计划。 与 Bitcoin 或其他 proof-of-work blockchain 不同,Tendermint 由于 validator 的数量增加,blockchain 会变慢 通信复杂性。幸运的是,我们可以支持足够多的人 validators 打造强大的全球分布式 blockchain 具有非常快的交易确认时间和带宽,
存储和并行计算能力的增加,我们将能够 将来支持更多 validator。 在创世日,validator 的最大数量将设置为 100,并且这个数字将在10年内以13%的速度增长,并且 稳定在 300 validators。 尚未成为 validators 的 Atom 持有者可以通过以下方式成为 validators: 签署并提交 BondTx 交易。金额 作为抵押品提供的原子必须非零。任何人都可以成为 a validator 在任何时候,除非当前的大小 validator 设置大于 validator 的最大数量 允许。在这种情况下,交易仅在金额达到 原子数大于所持有的有效原子数 最小的 validator,其中有效原子包括委托原子。 当新的 validator 以这种方式替换现有的 validator 时, 现有的 validator 变得不活跃,所有原子和 委托原子进入脱键状态。 必须对 validator 处以任何处罚 有意或无意偏离制裁规定 协议。有些证据可以立即采纳,例如 在相同的高度和轮次处进行双重签名,或者违反 第 0 年:100 第一年:113 第二年:127 第三年:144 第四年:163 5 年:184 第六年:208 7 年:235 8 年:265 9 年:300 10 年:300 ...
“prevote-the-lock”(Tendermint 共识协议的规则)。 此类证据将导致 validator 失去良好信誉 及其键合原子以及 tokens 的比例份额 储备池——统称为“股份”——将被削减。 有时,由于区域原因,validators 将不可用 网络中断、电源故障或其他原因。如果,在任何 在过去的 ValidatorTimeoutWindow 块中,validator 的点 提交投票未包含在 blockchain 中超过 ValidatorTimeoutMaxAbsent 次,validator 将变为 不活动,并失去其 ValidatorTimeoutPenalty(默认 1%) 股份。 一些“恶意”行为不会产生明显可辨别的结果 blockchain 上的证据。在这些情况下,validator 可以 带外协调以强制这些恶意软件超时 validators,如果达成绝大多数共识。 在 Cosmos 集线器因 ≥⅓ 联盟而停止的情况下 投票权消失,或者在 ≥⅓ 联盟的情况下 投票权审查的恶意行为证据 进入blockchain,集线器必须通过硬分叉恢复 重组提案。 (链接至“分叉和审查攻击”)。 Cosmos 集线器 validators 可接受任何 token 类型或组合 作为处理交易的费用的类型。每个 validator 可以 主观设定想要的汇率,然后选择 无论它想要什么交易,只要 BlockGasLimit 是 没有超过。收取的费用减去下面指定的任何税费, 按比例重新分配给担保利益相关者 他们的键合原子,每个 ValidatorPayoutPeriod (默认 1 小时)。在收取的交易费用中,保留税(默认 2%)将 前往储备池增加储备池并 提高 Cosmos 网络的安全性和价值。这些 资金也可以根据决定进行分配 由治理体系制定。 将投票权委托给其他 validator 的 Atom 持有者 向受委托人 validator 支付佣金。委员会可以 由每个 validator 设置。 Cosmos 集线器的安全性取决于 底层 validator 以及委托人的委托选择。 为了鼓励发现并及早报告所发现的 漏洞,Cosmos 中心鼓励黑客发布 通过 ReportHackTx 交易成功利用该交易,该交易表示:“这 validator 被黑了。请将赏金发送至此地址”。之上 这样的漏洞,validator 和委托人将变得不活跃, 每个人的原子都会受到 HackPunishmentRatio(默认 5%) 削减,以及每个人原子的 HackRewardRatio(默认 5%) 将获得奖励至黑客的赏金地址。 validator 必须使用其备份密钥恢复剩余的原子。 为了防止该功能被滥用进行转账 未归属原子,已归属原子与未归属原子的部分 ReportHackTx 之前和之后的 validators 和委托人将 保持不变,黑客赏金将包括一些 未归属的原子,如果有的话。 Cosmos 中心由一个分布式组织运营,该组织 需要一个明确的治理机制 协调对 blockchain 的各种更改,例如变量
系统参数,以及软件升级和 宪法修正案。 所有 validator 负责对所有提案进行投票。未能 及时对提案进行投票将产生 validator 自动停用一段时间,称为 缺勤处罚期(默认 1 周)。 委托人自动继承被委托人的投票权 validator。该投票可能会被手动覆盖。未键合的原子 没有投票权。 每个提案都需要缴纳最低提案存款 (MinimumProposalDeposit) tokens,可以是一个或多个tokens的组合 包括原子。对于每项提案,选民可以投票通过 押金。如果超过半数选民选择投票 存款(例如,因为该提案是垃圾邮件),存款将转到 储备池,除了被燃烧的任何原子。 对于每项提案,选民可以对以下选项进行投票: 是啊 力挺 不 强行反对 弃权 绝对多数赞成票或 YeaWithForce 票(或反对票或反对票) NayWithForce 投票)需要提案被决定为 通过(或判定失败),但 1/3+ 可以否决多数 通过“强力”投票做出决定。当绝对多数被否决时, 每个人都会因失去 VetoPenaltyFeeBlocks 而受到惩罚 (默认 1 天的区块)价值的费用(税费除外) 不会受到影响),以及否决多数票的一方
决定将受到失去 VetoPenaltyAtoms 的额外惩罚 (默认 0.1%)其原子。 此处定义的任何参数都可以通过以下命令更改 传递 ParameterChangeProposal。 原子可以被注入,储备池资金可以用在 通过赏金提案。 所有其他提案,例如升级协议的提案, 将通过通用的 TextProposal 进行协调。 参见计划。 blockchain 共识有很多创新, 过去几年的可扩展性。本节提供了一个简短的 对选定的一些重要问题进行的调查。 存在恶意参与者的共识是一个问题 可以追溯到 20 世纪 80 年代初,当时 Leslie Lamport 创造了 短语“拜占庭错误”指的是任意进程行为 与“崩溃故障”相比,偏离了预期的行为, 其中一个进程简单地崩溃了。发现了早期的解决方案 对于有上限的同步网络消息延迟,尽管实际使用仅限于高度 受控环境,例如飞机控制器和 通过原子钟同步的数据中心。直到 90 年代末,实用拜占庭容错 (PBFT) [11] 作为有效的部分同步共识引入 算法能够容忍多达 ⅓ 的进程行为 任意地。 PBFT 成为标准算法,催生了许多 变体,包括 IBM 最近创建的一个变体,作为 他们对超级账本的贡献。 Tendermint 共识对 PBFT 的主要好处是 Tendermint 具有改进和简化的底层结构, 其中一些是采用 blockchain 范式的结果。 Tendermint 区块必须按顺序提交,这可以避免 与 PBFT 相关的复杂性和通信开销 视图更改。在 Cosmos 和许多加密货币中,没有 需要允许块 N+i(其中 i >= 1)提交,当块 N 本身还没有承诺。如果带宽是阻止 N 的原因 尚未在 Cosmos 区域中提交,那么使用它无济于事 N+i 块的带宽共享投票。如果网络分区或 ofzine节点是区块N没有提交的原因,那么 无论如何,N+i 都不会承诺。 此外,将交易分批放入区块允许 应用程序状态的常规 Merkle-hashing,而不是 与 PBFT 的检查点方案一样的定期摘要。这允许 为轻客户端提供更快的可证明事务提交,并且速度更快 blockchain 之间的通信。 Tendermint Core 还包括许多优化和功能 超出 PBFT 中指定的范围。例如, validators 提出的区块被分成几个部分,默克尔化, 并以改善广播的方式传播八卦 性能(请参阅 LibSwift [19] 以获取灵感)。还有,嫩薄荷 Core 不做任何关于点对点的假设
只要 P2P 网络存在,连接性和功能就一直存在 弱连接。 虽然不是第一次部署 proof-of-stake (PoS),但 BitShares1.0 [12] 为 PoS 的研究和采用做出了巨大贡献 blockchains,特别是那些被称为“委托”PoS 的。在 比特股,利益相关者选举“见证人”,负责排序 并提交交易,以及“代表”,负责 协调软件更新和参数更改。 BitShares2.0旨在实现高性能(100k tx/s,1s 延迟)在理想条件下,每个块由单个签名 签名者和交易 ynality 花费的时间比 块间隔。规范规范仍在开发中。 利益相关者可以删除或更换行为不端的证人 每日进行,但没有重要的证人或证据 Tendermint PoS 中的委托人被削减 成功的双花攻击的情况。 基于 Ripple 首创的方法,Stellar [13] 雷尼德 联邦拜占庭协议模型,其中的过程 参与共识并不构成yxed和全球性的 已知集。相反,每个流程节点都会策划一个或多个 “仲裁切片”,每个切片构成一组可信进程。一个 Stellar 中的“quorum”被定义为包含以下内容的一组节点: 集合中的每个节点至少有一个仲裁片,这样 可以达成协议。 Stellar 机制的安全性依赖于以下假设 任意两个法定人数的交集非空,而 节点的可用性至少需要其仲裁片之一 完全由正确的节点组成,在之间创建一个权衡 使用可能难以平衡的大或小的仲裁片 无需对信任强加重大假设。最终,节点必须以某种方式选择足够的仲裁片 具有足够的容错能力(或任何“完整节点”,其中 论文的大部分结果取决于),并且唯一的 提供了确保这种配置是分层的策略 类似于边界网关协议 (BGP),互联网上的顶级 ISP 使用它来建立全球路由表,并且 浏览器用来管理 TLS 证书;都臭名昭著 因为他们的不安全感。 Stellar 论文中对基于 Tendermint 的权益证明系统的批评通过所描述的 token 策略得到了缓解 这里,发出了一种称为原子的新类型 token 代表对未来部分费用和奖励的要求。的 那么,基于 Tendermint 的 proof-of-stake 的优势是它的相对优势 简单性,同时仍然提供充分且可证明的安全性 保证。 BitcoinNG 是对 Bitcoin 的拟议改进,允许 对于垂直可扩展性的形式,例如增加块大小, 不会产生通常相关的负面经济后果 有了这样的变化,比如不成比例的巨大影响 关于小矿工。这种改进是通过分离来实现的 交易广播中的领导者选举:领导者是第一名 由 proof-of-work 在“微块”中选出,然后能够 广播要提交的交易,直到出现新的微块 被发现。这降低了所需的带宽要求 赢得 PoW 竞赛,让小矿工更公平地竞争, 并允许交易更定期地由 最后一个矿工创建一个微块。 Casper [16] 是一种提议的 proof-of-stake 共识算法 Ethereum。其主要运作模式是“投注共识”。由 让 validators 迭代地押注他们认为会出现的区块
根据其他赌注投入 blockchain 到目前为止,他们已经看到,最终可以实现 ynality。关联。 这是 Casper 团队的一个活跃研究领域。的 挑战在于构建一个可以 被证明是一种进化稳定的策略。主要好处是 Casper 与 Tendermint 相比可能在于提供“可用性” 过度一致性”——共识不需要>⅔法定人数 投票权 – 可能以牺牲提交速度或 实施复杂度。 Interledger 协议 [14] 严格来说并不是一个可扩展性解决方案。它 提供不同账本之间的临时互操作 系统通过松散耦合的双边关系网络。 与闪电网络一样,ILP 的目的是促进 支付,但它特别关注不同领域的支付 账本类型,并将原子交易机制扩展到 不仅包括 hash-锁,还包括法定人数的公证人(称为 原子传输协议)。后一种机制用于 在账本间交易中强制执行原子性类似于 Tendermint 的轻客户端 SPV 机制,因此说明 ILP 和 Cosmos/IBC 之间的区别是有保证的,并且 下面提供。 1. ILP中连接器的公证人不支持会员资格 变化,并且不允许在之间进行灵活的权重 公证人。另一方面,IBC 是专门为 blockchains,其中 validators 可以有不同的权重,并且 成员资格可以在整个过程中发生变化 blockchain。 2. 与闪电网络一样,ILP中的付款接收方 必须在线才能将确认信息发送回发件人。在一个token 通过 IBC 传输,即接收器的 validator 集 blockchain 负责提供确认,而不是 接收用户。 3. 最显着的区别是 ILP 的连接器不是 对付款负责或保持权威状态, 而在 Cosmos 中,集线器的 validator 是 IBC token 的状态转移以及权限 每个区域持有的 token 数量(但不是 区域内每个账户持有的 tokens)。这是 允许安全不对称的根本性创新 将 tokens 从一个区域转移到另一个区域; ILP 的类似物 Cosmos 中的连接器是持久且高度安全的 blockchain 分类账,Cosmos 中心。 4. ILP 中的账本间支付需要有一个 交换订单簿,因为不存在非对称转移 硬币从一个分类账到另一个分类账,仅转移价值或 市场等价物。 侧链 [15] 是一种提议的用于扩展 Bitcoin 的机制 通过“双向挂钩”的替代 blockchain 网络 Bitcoin blockchain。 (双向挂钩相当于 桥接。在 Cosmos 中,我们说“桥接”以区别于市场挂钩)。侧链允许比特币有效地从 Bitcoin blockchain 到侧链和后面,并允许 侧链新功能的实验。正如在 Cosmos Hub、侧链和 Bitcoin 作为轻客户端 彼此之间,使用 SPV 证明来确定硬币何时应该被 转移到侧链并返回。当然,从 Bitcoin 开始 使用 proof-of-work,以 Bitcoin 为中心的侧链受到影响 从 proof-of-work 作为一个 共识机制。此外,这是一个 Bitcoin-最大化主义 本身不支持各种 token 的解决方案和
区域间网络拓扑如 Cosmos 那样。也就是说,核心 双向挂钩的机制原理上是一样的 受雇于 Cosmos 网络。 Ethereum 目前正在研究多种不同的策略 将 Ethereum blockchain 的状态分片以寻址 可扩展性需求。这些努力的目标是维持 当前 Ethereum 虚拟机提供的抽象层 跨越共享状态空间。多项研究工作正在 此时正在进行。 [18][22] Cosmos 和 Ethereum 2.0 Mauve [22] 具有不同的设计目标。 Cosmos 特别是关于 tokens。紫红色是关于缩放 一般计算。 Cosmos 未绑定到 EVM,因此即使不同的虚拟机也可以 互操作。 Cosmos 让区域创建者确定谁验证该区域 区。 任何人都可以在 Cosmos 中启动一个新区域(除非治理 另有决定)。 集线器隔离区域故障,因此全局 token 不变量是 保存下来。 闪电网络是提议的 token 传输网络 在 Bitcoin blockchain (以及其他公共 blockchains),实现多个数量级的改进 通过移动大部分交易来提高交易吞吐量 在共识账本之外进入所谓的“支付渠道”。这是通过链上加密货币脚本实现的,该脚本 使各方能够签订双边国家合同,其中 状态可以通过共享数字签名和合约来更新 可以通过将证据发布到 blockchain 来关闭,a 这种机制最早是通过跨链原子交换而普及的。由 与多方、参与者开放支付渠道 闪电网络可以成为路由的焦点 他人支付,形成全连接的支付通道 网络,代价是资金被束缚在支付渠道上。 虽然闪电网络也可以轻松地跨 多个独立的 blockchain 允许价值转移 通过交易市场,它不能被用来不对称地 将 token 从一个 blockchain 转移到另一个。主要收益 这里描述的 Cosmos 网络的目的是启用这种直接 token 转账。也就是说,我们期望支付渠道和 闪电网络将与我们一起被广泛采用 token 传输机制,出于节省成本和隐私的原因。 隔离见证是一个 Bitcoin 改进提案链接, 旨在将每块交易吞吐量提高 2 倍或 3 倍, 同时使新节点的块同步速度更快。 该解决方案的出色之处在于它如何在 Bitcoin 当前协议的限制并允许软分叉 升级(即使用旧版本软件的客户端将 升级后继续使用)。 Tendermint,成为新的 协议,没有设计限制,所以它有不同的缩放比例 优先事项。 Tendermint 主要使用 BFT 循环算法 基于加密签名而不是挖掘,这 简单地允许通过多个并行进行水平缩放 blockchains,而定期、更频繁的块提交允许 垂直缩放也是如此。
Consensus et détails techniques
Un protocole de consensus bien conçu devrait fournir garanties en cas de dépassement de la capacité de tolérance et le consensus échoue. Ceci est particulièrement nécessaire dans le domaine économique systèmes, où le comportement byzantin peut avoir des conséquences financières substantielles récompense. La plus importante de ces garanties est une forme de responsabilité fork, où les processus qui ont conduit au consensus échouer (c'est-à-dire avoir amené les clients du protocole à accepter des valeurs différentes - un fourchette) peuvent être identifiés et sanctionnés selon les règles de la protocole ou, éventuellement, le système juridique. Lorsque le système juridique est peu fiables ou excessivement coûteux à invoquer, les validator peuvent être obligés de faire des dépôts de garantie pour pouvoir participer, et ceux les dépôts peuvent être révoqués ou réduits en cas de comportement malveillant détecté [10]. Notez que cela diffère de Bitcoin, où le forking est un phénomène régulier en raison de l'asynchronie du réseau et de la nature probabiliste du ynding collisions partielles hash. Puisque dans de nombreux cas, un fork malveillant est impossible à distinguer d'un fork en raison de l'asynchronie, Bitcoin ne peut pas mettre en œuvre de manière fiable la responsabilité fork, autre que la responsabilité implicite coût d’opportunité payé par les mineurs pour l’exploitation d’un bloc orphelin. Nous appelons les étapes de vote PreVote et PreCommit. Un vote peut être pour un bloc particulier ou pour Nil. Nous appelons une collection de >⅔ PreVotes pour un seul bloc dans le même tour, une Polka et une collection de >⅔ PreCommits pour un seul bloc au cours du même tour d’un Commit. Si >⅔ PreCommit pour Nil dans le même tour, ils passent au suivant rond. Notez qu’un déterminisme strict dans le protocole entraîne une faible hypothèse de synchronisation car les leaders défectueux doivent être détectés et
sauté. Ainsi, les validator attendent un certain temps, TimeoutPropose, avant de pré-voter Nil, et la valeur de TimeoutPropose augmente à chaque tour. Progression à travers le reste d'un tour est entièrement asynchrone, dans la mesure où la progression n'est que effectué une fois qu'un validator entend de >⅔ du réseau. En pratique, il faudrait un adversaire extrêmement puissant pour contrecarrer indéfiniment l'hypothèse de synchronisation faible (ce qui fait que le consensus ne parvient pas à jamais commettre un blocage), et cela peut être rendu encore plus difficile en utilisant des valeurs aléatoires de TimeoutPropose sur chaque validator. Un ensemble supplémentaire de contraintes, ou règles de verrouillage, garantit que le Le réseau finira par engager un seul bloc à chaque hauteur. N'importe lequel tentative malveillante de provoquer la validation de plusieurs blocs à une hauteur donnée peut être identifié. Tout d'abord, un PreCommit pour un bloc doit être accompagné d'une justification, sous la forme d'une Polka pour ce bloc. Si le validator a déjà PreCommit un bloc au tour R_1, nous disent qu'ils sont verrouillés sur ce bloc, et la Polka avait l'habitude de justifier le le nouveau PreCommit au tour R_2 doit arriver dans un tour R_polka où R_1 < R_polka <= R_2. Deuxièmement, les validator doivent proposer et/ou PréVote le bloc sur lequel ils sont verrouillés. Ensemble, ces conditions garantissent qu'un validator ne fait pas de PreCommit sans preuves suffisantes comme justification, et que validators qui ont PreCommit ne peut déjà pas contribuer aux preuves à PreCommit autre chose. Cela garantit à la fois la sécurité et la vivacité du algorithme de consensus. Les détails complets du protocole sont décrits ici. La nécessité de synchroniser tous les en-têtes de bloc est éliminée dans TendermintPoS car l'existence d'une chaîne alternative (un fork) signifie ≥⅓ de la mise sous caution peut être réduite. Bien sûr, puisque couper nécessite que quelqu'un partage la preuve d'un fork, les clients légers devraient stocker tout bloc-hash valide qu'il voit. De plus, les clients légerspourrait périodiquement rester synchronisé avec les modifications apportées à l'ensemble validator, dans afin d'éviter les attaques à longue portée (mais d'autres solutions sont possibles). Dans un esprit similaire à Ethereum, Tendermint permet aux applications de intégrer une racine Merkle globale hash dans chaque bloc, permettant facilement requêtes d'état vérifiables pour des éléments tels que les soldes des comptes, la valeur stocké dans un contrat, ou l’existence d’une transaction non dépensée sortie, en fonction de la nature de l’application. En supposant un ensemble de réseaux de diffusion suffisamment résilients et un ensemble validator statique, n'importe quelle fourchette du blockchain peut être détecté et les dépôts des validator incriminés réduits. Ceci l'innovation, suggérée pour la première fois par Vitalik Buterin début 2014, résout le problème sans enjeu des autres proof-of-stake crypto-monnaies (voir Travaux connexes). Cependant, puisque validator définit doit pouvoir modifier, sur une longue période de temps, l'original Les validator peuvent tous devenir déliés et seraient donc libres de créer une nouvelle chaîne à partir du bloc Genesis, sans aucun coût car ils n'ont plus de dépôts bloqués. Cette attaque a eu lieu connue sous le nom d'attaque à longue portée (LRA), par opposition à une attaque à courte portée. Attaque à distance, où les validator qui sont actuellement liés provoquent un fork et sont donc punissables (en supposant qu'un fork soit responsable BFT algorithme comme le consensus Tendermint). Les attaques à longue portée sont souvent considéré comme un coup critique porté à proof-of-stake. Heureusement, la LRA peut être atténuée comme suit. D'abord, pour un validator pour se désengager (récupérant ainsi leur dépôt de garantie et ne percevant plus de frais pour participer au consensus), le le dépôt doit être rendu intransférable pendant un certain temps connue sous le nom de « période de détachement », qui peut être de l’ordre de semaines ou mois. Deuxièmement, pour qu'un client léger soit sécurisé, la première année chaque fois qu'il se connecte au réseau, il doit vérifier un bloc récent-hash contre une source fiable, ou de préférence plusieurs sources. Ceci
Cette condition est parfois qualifiée de « subjectivité faible ». Enfin, pour rester sécurisé, il doit se synchroniser avec le dernier validator défini sur au moins aussi souvent que la durée de la période de détachement. Ceci garantit que le client léger est informé des modifications apportées au validator fixé avant qu'un validator voit son capital délié et donc plus en jeu, ce qui lui permettrait de tromper le client en effectuant une attaque à longue portée en créant de nouveaux blocs en commençant à un hauteur où il a été collé (en supposant qu'il contrôle suffisamment plusieurs des premières clés privées). Il convient de noter que vaincre la LRA de cette manière nécessite une refonte du système. le modèle de sécurité d'origine de proof-of-work. Dans PoW, c'est supposé qu'un client léger peut se synchroniser avec la hauteur actuelle à partir du bloc Genesis de confiance à tout moment simplement en traitant la preuve de travail dans chaque en-tête de bloc. Toutefois, pour vaincre la LRA, nous exiger qu'un client léger se connecte avec une certaine régularité pour suivre les modifications dans l'ensemble validator, et que la première fois qu'ils lorsqu'ils se connectent, ils doivent être particulièrement attentifs à s'authentifier ce qu'ils entendent du réseau par rapport à des sources fiables. De bien sûr, cette dernière exigence est similaire à celle de Bitcoin, où le protocole et le logiciel doivent également être obtenus auprès d'un source. La méthode ci-dessus pour prévenir l’ARL est bien adaptée aux validator et les nœuds complets d'un blockchain alimenté par Tendermint, car ceux-ci les nœuds sont censés rester connectés au réseau. Le La méthode convient également aux clients légers dont on peut s'attendre à synchronisez-vous fréquemment avec le réseau. Cependant, pour les clients légers qui ne sont pas censés avoir un accès fréquent à Internet ou au blockchain réseau, encore une autre solution peut être utilisée pour surmonter la LRA. Les non-titulaires de validator token peuvent publier leurs token comme garantie avec une période de détachement très longue (par exemple beaucoup plus longue que la période de détachement pour validators) et servir des clients légers avec une méthode secondaire d'attestation de la validité des informations actuelles et bloc passé-hashes. Bien que ces token ne comptent pas pour le sécurité du consensus du blockchain, ils peuvent néanmoinsoffrir de solides garanties aux clients légers. Si bloc historique-hash les requêtes étaient prises en charge dans Ethereum, n'importe qui pouvait lier son tokens dans un smart contract spécialement conçu et fournir services d'attestation payants, créant ainsi un marché pour la sécurité des clients légers LRA. En raison de la définition d’un block commit, toute coalition ≥⅓ de le pouvoir de vote peut arrêter le blockchain en sortant du zine ou non diffuser leurs votes. Une telle coalition peut également censurer transactions particulières en rejetant les blocs qui incluent ces transactions, même si cela entraînerait une proportion importante de propositions de blocs seraient rejetées, ce qui ralentirait le rythme de validations de bloc du blockchain, réduisant ainsi son utilité et sa valeur. La coalition malveillante pourrait également diffuser les votes au compte-goutte afin quant à broyer, le bloc blockchain s'engage à s'arrêter presque ou à s'engager dans toute combinaison de ces attaques. Enfin, cela peut provoquer le blockchain à fork, en double-signant ou en violant le verrouillage règles. Si un adversaire actif à l’échelle mondiale était également impliqué, il pourrait diviser le réseau de telle manière qu'il puisse sembler que le mauvais un sous-ensemble de validators était responsable du ralentissement. Ce n'est pas juste une limitation de Tendermint, mais plutôt une limitation de tous protocoles de consensus dont le réseau est potentiellement contrôlé par un adversaire actif. Pour ces types d'attaques, un sous-ensemble des validator doit se coordonner par des moyens externes pour signer une proposition de réorganisation qui choisit un fork (et toute preuve de celui-ci) et le sous-ensemble initial de validators avec leurs signatures. Les validateurs qui signent une telle proposition de réorganisation renoncent à leur garantie sur tous les autres forks. Les clients devraient vérifier les signatures sur la proposition de réorganisation, vérifier toute preuve, et porter un jugement ou demander à l'utilisateur final de prendre une décision. Pour Par exemple, une application de portefeuille téléphonique peut demander à l'utilisateur un code de sécurité
avertissement, alors qu'un réfrigérateur peut accepter toute proposition de réorganisation signé par +½ des validator originaux avec droit de vote. Aucun algorithme byzantin tolérant aux pannes non synchrone ne peut venir au consensus lorsque ≥⅓ des droits de vote sont malhonnêtes, mais une fourchette suppose que ≥⅓ des voix ont déjà été malhonnêtes par double signature ou changement de serrure sans justification. Alors, je signe la proposition de réorganisation est un problème de coordination qui ne peut pas être résolu par n'importe quel protocole non synchrone (c'est-à-dire automatiquement, et sans faire d'hypothèses sur la fiabilité du réseau sous-jacent). Pour l’instant, nous laissons le problème de la coordination des propositions de réorganisation à la coordination humaine via le consensus social. sur les médias Internet. Les validateurs doivent veiller à ce qu'il y ait il n'y a plus de partitions réseau avant la signature d'une proposition de réorganisation, afin d'éviter les situations dans lesquelles deux propositions de réorganisation contradictoires sont signées. En supposant que le support et le protocole de coordination externe soient robuste, il s'ensuit que les forks sont moins préoccupants que la censure attaques. En plus des forks et de la censure, qui nécessitent ≥⅓ byzantin pouvoir de vote, une coalition de >⅔ pouvoir de vote peut s'engager état arbitraire et invalide. Ceci est caractéristique de tout (BFT) système de consensus. Contrairement à la double signature, qui crée des forks avec des preuves facilement vérifiables, détectant l'engagement d'un un état invalide nécessite que des pairs non validateurs vérifient des blocs entiers, ce qui implique qu'ils conservent une copie locale de l'état et exécutent chaque transaction, calculant indépendamment la racine d'état pour eux-mêmes. Une fois détecté, la seule façon de gérer une telle panne passe par le consensus social. Par exemple, dans les situations où Bitcoin a échoué, que ce soit en raison de bugs logiciels (comme en mars 2013), ou commettant un état invalide en raison du comportement byzantin de mineurs (comme en juillet 2015), la communauté bien connectée de entreprises, développeurs, mineurs et autres organisations établi un consensus social sur les actions manuellesrequis par les participants pour guérir le réseau. De plus, puisque On peut s'attendre à ce que validators d'un Tendermint blockchain soient identifiable, l'engagement d'un état invalide peut même être punissable par la loi ou par une jurisprudence externe, si vous le souhaitez. ABCI se compose de 3 types de messages principaux qui sont transmis à partir de le cœur de l’application. L'application répond avec messages de réponse correspondants. Le message AppendTx est le cheval de bataille de l'application. Chacun La transaction dans le blockchain est livrée avec ce message. Le l'application doit valider chaque transaction reçue avec le Message AppendTx contre l'état actuel, le protocole d'application, et les informations d'identification cryptographiques de la transaction. Un validé la transaction doit ensuite mettre à jour l'état de l'application - en en liant une valeur dans un magasin de valeurs clés, ou en mettant à jour le UTXO base de données. Le message CheckTx est similaire à AppendTx, mais il est uniquement destiné à valider les transactions. Vérifications de l'année du pool de mémoire de Tendermint Core la validité d'une transaction avec CheckTx, et uniquement les relais valides transactions avec ses pairs. Les applications peuvent vérifier une incrémentation nonce dans la transaction et renvoie une erreur lors de CheckTx si le nonce est ancien. Le message Commit est utilisé pour calculer un chiffrement engagement envers l’état actuel de l’application, à placer dans le en-tête de bloc suivant. Cela a des propriétés pratiques. Les incohérences dans la mise à jour de cet état apparaîtront désormais sous la forme blockchain forks qui capture toute une classe de programmation erreurs. Cela simplifie également le développement de logiciels légers et sécurisés. clients, car les preuves Merkle-hash peuvent être vérifiées en vérifiant par rapport le bloc-hash, et le bloc-hash est signé par un quorum de validators (par droit de vote).
Des messages ABCI supplémentaires permettent à l'application de suivre et modifiez l'ensemble validator, et pour que l'application reçoive le bloquer les informations, telles que la hauteur et les votes de validation. Les requêtes/réponses ABCI sont de simples messages Protobuf. Vérifier le schéma yle. Arguments : Data ([]byte) : les octets de la transaction de la demande Retours : Code (uint32) : code de réponse Données ([]octet) : octets de résultat, le cas échéant Journal (chaîne) : message de débogage ou d'erreur Utilisation :
Ajoutez et exécutez une transaction. Si la transaction est valide, renvoie CodeType.OK Arguments : Data ([]byte) : les octets de la transaction de la demande Retours : Code (uint32) : code de réponse Données ([]octet) : octets de résultat, le cas échéant Journal (chaîne) : message de débogage ou d'erreur Utilisation :
Valider une transaction. Ce message ne doit pas muter le état. Les transactions sont exécutées pour la première fois via CheckTx avant diffusé aux pairs dans la couche mempool. Vous pouvez faire CheckTx semi-stateful et effacez l'état lors de la validation ou BeginBlock , pour permettre des séquences de transactions dépendantes dans le même bloc.
Retours : Données ([]octet) : racine Merkle hash Journal (chaîne) : message de débogage ou d'erreur Utilisation :
Renvoie une racine Merkle hash de l'état de l'application. Arguments : Data ([]byte) : les octets de la requête Retours : Code (uint32) : code de réponse Data ([]byte) : octets de réponse à la requête Journal (chaîne) : message de débogage ou d'erreur Utilisation :
Videz la file d'attente de réponses. Applications qui implémentent types.L’application n’a pas besoin d’implémenter ce message – c’est gérés par le projet. Retours : Data ([]byte) : les octets d'informations Utilisation :
Renvoie des informations sur l’état de l’application. Demande spécifique. Arguments : Clé (chaîne) : Clé à définir
Value (string) : valeur à définir pour la clé Retours : Journal (chaîne) : message de débogage ou d'erreur Utilisation :
Définissez les options de l'application. Par ex. Key="mode", Value="mempool" pour une connexion mempool, ou Key="mode", Value="consensus" pour une connexion consensuelle. Les autres options sont spécifiques à l'application. Arguments : Validateurs ([]Validator) : Genèse initiale-validators Utilisation :
Appelé une fois lors de la genèse Arguments : Height (uint64) : la hauteur du bloc qui commence Utilisation :
Signale le début d’un nouveau bloc. Appelé avant tout AppendTxs. Arguments : Height (uint64) : hauteur du bloc qui s'est terminé Retours : Validateurs ([]Validator) : validators modifiés par de nouveaux pouvoirs de vote (0 pour supprimer) Utilisation :
Signale la fin d’un bloc. Appelé avant chaque commit après tout opérations Consultez le référentiel ABCI pour plus de détails.Il existe plusieurs raisons pour lesquelles un expéditeur peut souhaiter que accusé de réception d'un paquet par la chaîne réceptrice. Par exemple, l'expéditeur peut ne pas connaître l'état du chaîne de destination, si l'on s'attend à ce qu'elle soit défectueuse. Ou bien, l'expéditeur peut souhaitez imposer un délai d'attente au paquet (avec le paramètre MaxHeight rendement des paquets), alors que n'importe quelle chaîne de destination peut souffrir d'une attaque par déni de service avec une augmentation soudaine du nombre de messages entrants. paquets. Dans ces cas, l'expéditeur peut exiger un accusé de réception en définissant l'état initial du paquet sur AckPending . Ensuite, c'est le la responsabilité de la chaîne de réception de confirmer la livraison en incluant un en abrégé IBCPacket dans l'application Merkle hash. Tout d'abord, un IBCBlockCommit et un IBCPacketTx sont publiés sur « Hub ». qui prouve l'existence d'un IBCPacket sur la « Zone1 ». Dis ça IBCPacketTx a la valeur suivante : DeChainID : "Zone1" FromBlockHeight : 100 (disons) Paquet : un IBCPaquet :
En-tête : un IBCPacketHeader :
SrcChainID : "Zone1"
DstChainID : "Zone2"
Nombre : 200 (disons)
Statut : Accusé de réception en attente
Type : « pièce de monnaie »
MaxHeight : 350 (disons que « Hub » est actuellement à la hauteur de 300)
Charge utile :
FromBlockHeight : 400 (disons)
Paquet : un IBCPacket :
En-tête : un IBCPacketHeader :
SrcChainID : "Zone1"
DstChainID : "Zone2"
Numéro : 200
Statut : AcquitEnvoyé
Type : « pièce de monnaie »
Hauteur maximale : 350
PayloadHash :
statut de "Zone2" par le bloc 350, il aurait défini le statut automatiquement sur Timeout . Cette preuve d'un délai d'attente peut obtenir posté sur « Zone1 », et tous les token peuvent être renvoyés. Il existe deux types de Merkle tree pris en charge dans le Écosystème Tendermint/Cosmos : l'arbre simple et l'IAVL+ Arbre. L'arbre simple est un Merkle tree pour une liste statique d'éléments. Si le le nombre d'éléments n'est pas une puissance de deux, certaines feuilles seront à différents niveaux. Simple Tree essaie de garder les deux côtés de l'arbre même hauteur, mais la gauche peut être plus grande. Ce Merkle tree est utilisé pour Merkle-iser les transactions d'un bloc, et le niveau supérieur éléments de la racine de l’état de l’application.Le but de la structure de données IAVL+ est de fournir des stockage des paires clé-valeur dans l'état de l'application de telle sorte qu'un La racine déterministe de Merkle hash peut être calculée efficacement. Le l'arbre est équilibré à l'aide d'une variante de l'algorithme AVL, et tout les opérations sont O(log(n)). Dans un arbre AVL, les hauteurs des deux sous-arbres enfants de n'importe quel nœud diffèrent d’au plus un. Chaque fois que cette condition est violée lors d'un mise à jour, l'arborescence est rééquilibrée en créant O(log(n)) de nouveaux nœuds qui pointez vers les nœuds non modifiés de l’ancien arbre. Dans l'AVL d'origine algorithme, les nœuds internes peuvent également contenir des paires clé-valeur. L'AVL+ (notez le plus) modifie l'algorithme AVL pour conserver tout valeurs sur les nœuds feuilles, tout en utilisant uniquement des nœuds de branche pour stocker les clés. Cela simplifie l'algorithme tout en gardant la trace merkle hash court. L’arbre AVL+ est analogue aux essais de Patricia de Ethereum. Il y a compromis. Les clés n'ont pas besoin d'être hashed avant d'être insérées dans Arbres IAVL+, ce qui permet une itération ordonnée plus rapide dans la clé espace qui peut bénéficier à certaines applications. La logique est plus simple à implémenter, ne nécessitant que deux types de nœuds : les nœuds internes et nœuds feuilles. La preuve de Merkle est en moyenne plus courte, étant une * / \ / \ / \ / \ * * / \ / \ / \ / \ / \ / \ * * * h6 / \ / \ / \ h0 h1 h2 h3 h4 h5 Un SimpleTree avec 7 éléments
arbre binaire équilibré. D'autre part, la racine Merkle d'un L’arborescence IAVL+ dépend de l’ordre des mises à jour. Nous prendrons en charge des Merkle tree supplémentaires efficaces, tels que Patricia Trie de Ethereum lorsque la variante binaire devient disponible. Dans l'implémentation canonique, les transactions sont diffusées vers le Application hub Cosmos via l'interface ABCI. Le Cosmos Hub acceptera un certain nombre de transactions principales types, notamment SendTx , BondTx , UnbondTx , ReportHackTx , SlashTx , BurnAtomTx , ProposalCreateTx et ProposalVoteTx , qui sont assez explicites et seront documentés dans un révision future de cet article. Nous documentons ici les deux principaux types de transactions pour IBC : IBCBlockCommitTx et IBCPacketTx . Une transaction IBCBlockCommitTx est composée de : ChainID (string) : ID du blockchain BlockHash ([]byte) : le bloc-hash octets, la racine Merkle qui comprend l'application-hash BlockPartsHeader (PartSetHeader) : l'en-tête de l'ensemble partiel de bloc octets, uniquement nécessaires pour vérifier les signatures de vote BlockHeight (int) : la hauteur du commit BlockRound (int) : Le tour du commit Commit ([]Vote) : le >⅔ Tendermint Precommit vote qui comprendre un bloc de validation ValidatorsHash ([]byte) : une racine Merkle-tree hash du nouveau validator ensemble
ValidatorsHashProof (SimpleProof) : Un SimpleTree Merkleproof pour prouver le ValidatorsHash par rapport au BlockHash
AppHash ([]byte) : une racine IAVLTree Merkle-tree hash du
état de l'application
AppHashProof (SimpleProof) : un SimpleTree Merkle-proof pour
prouver l'AppHash contre le BlockHash
Un IBCPacket est composé de :
En-tête (IBCPacketHeader) : l'en-tête du paquet
Payload ([]byte) : octets de la charge utile du paquet. Facultatif
PayloadHash ([]byte) : le hash pour les octets du paquet.
Facultatif
L'un des éléments suivants : Payload ou PayloadHash doit être présent. Le hash
d'un IBCPacket est une simple racine Merkle des deux éléments, Header
et Charge utile . Un IBCPacket sans la charge utile complète est appelé un
paquet abrégé.
Un IBCPacketHeader est composé de :
SrcChainID (string) : ID source blockchain
DstChainID (string) : ID de destination blockchain
Number (int) : un numéro unique pour tous les paquets
Statut (énumération) : peut être AckPending , AckSent ,
AckReceived , NoAck ou Timeout
Type (chaîne) : les types dépendent de l'application. Cosmos
réserve le type de paquet "coin"
MaxHeight (int) : si le statut n'est pas NoAckWanted ou AckReceived
à cette hauteur, le statut devient Timeout . Facultatif
Une transaction IBCPacketTx est composée de :FromChainID (string) : ID du blockchain qui est
fournir ce paquet ; pas nécessairement la source
FromBlockHeight (int) : hauteur blockchain à laquelle le
Le paquet suivant est inclus (Merkle-isé) dans le bloc-hash de
la chaîne d'approvisionnement
Paquet (IBCPacket) : Un paquet de données, dont le statut peut être un
de AckPending , AckSent , AckReceived , NoAck ou Timeout
PacketProof (IAVLProof) : un IAVLTree Merkle-proof pour prouver
le hash du paquet par rapport à l'AppHash de la chaîne source à
hauteur donnée
La séquence d'envoi d'un paquet de « Zone1 » à « Zone2 »
via le « Hub » est illustré dans la {Figure X}. Tout d'abord, un IBCPacketTx
prouve à "Hub" que le paquet est inclus dans l'état de l'application de
"Zone1". Ensuite, un autre IBCPacketTx prouve à « Zone2 » que le
Le paquet est inclus dans l’état de l’application de « Hub ». Pendant ce temps
procédure, les rendements IBCPacket sont identiques : le SrcChainID est
toujours "Zone1" et DstChainID est toujours "Zone2".
Le PacketProof doit avoir le chemin d'accès correct à l'épreuve de Merkle, comme
suit :
Lorsque « Zone1 » souhaite envoyer un paquet à « Zone2 » via « Hub »,
les données IBCPacket sont identiques, que le paquet soit merkleisé sur la « Zone1 », le « Hub » ou la « Zone2 ». Le seul rendement mutable est
Statut pour le suivi de la livraison.
Nous remercions nos amis et nos pairs pour leur aide dans la conceptualisation,
examiner et fournir un soutien à notre travail avec Tendermint
et Cosmos.
IBC/
Zaki Manian de SkuChain a fourni beaucoup d'aide pour le formatage et libellé, en particulier dans la section ABCI Jehan Tremback d'Althea et Dustin Byington pour leur aide itérations initiales Andrew Miller de Honey Badger pour ses commentaires sur le consensus Greg Slepak pour ses commentaires sur le consensus et la formulation Merci également à Bill Gleim et Seunghwan Han pour divers cotisations. Votre nom et votre organisation ici pour votre contribution 1 Bitcoin : https://bitcoin.org/bitcoin.pdf 2 ZéroCash : http://zerocash-project.org/paper 3 Ethereum : https://github.com/ethereum/wiki/wiki/WhitePaper 4 LeDAO : https://download.slock.it/public/DAO/WhitePaper.pdf 5 Témoin séparé : https://github.com/bitcoin/bips/blob/master/bip0141.mediawiki 6 BitcoinNG : https://arxiv.org/pdf/1510.02037v2.pdf 7 Réseau Lightning : https://lightning.network/lightningnetwork-paper-DRAFT-0.5.pdf 8Menthe tendre : https://github.com/tendermint/tendermint/wiki 9 Impossibilité FLP : https://groups.csail.mit.edu/tds/papers/Lynch/jacm85.pdf dixSlasheur : https://blog.ethereum.org/2014/01/15/slasher-apunitive-proof-of-stake-algorithm/ 11 PBFT : http://pmg.csail.mit.edu/papers/osdi99.pdf 12 BitShares : https://bitshares.org/technology/delegatedproof-of-stake-consensus/
13 Stellar : https://www.stellar.org/papers/stellar-consensusprotocol.pdf 14 Grand livre intermédiaire : https://interledger.org/rfcs/0001-interledgerarchitecture/ 15 chaînes latérales : https://blockstream.com/sidechains.pdf 16Casper : https://blog.ethereum.org/2015/08/01/introducing-casperfriendly-ghost/ 17 ABCI : https://github.com/tendermint/abci 18 Ethereum Partage : https://github.com/ethereum/EIPs/issues/53 19 LibSwift : http://www.ds.ewi.tudelft.nl/yleadmin/pds/papers/Performa nceAnalysisOfLibswift.pdf 20 DLS : http://groups.csail.mit.edu/tds/papers/Lynch/jacm88.pdf 21 Sécurité des clients légers : https://en.bitcoin.it/wiki/Thin_Client_Security 22 Ethereum 2.0 Papier Mauve : http://vitalik.ca/yles/mauve_paper.html https://www.docdroid.net/ec7xGzs/314477721-ethereumplatform-review-opportunities-and-challenges-for-privateand-consortium-blockchains.pdf.html
³ è
共识和技术细节
一个设计良好的共识协议应该提供一些 超出耐受能力时的保证 并且共识失败。这在经济上尤其必要 系统中,拜占庭行为可能会产生大量的经济影响 奖励。最重要的此类保证是一种责任形式,其中导致共识的过程 失败(即导致协议的客户端接受不同的值 - a fork)可以根据规则进行识别和惩罚 协议,或者可能是法律体系。当法律制度 不可靠或调用成本过高, validators 可能是 被迫缴纳保证金才能参加,以及那些 当恶意行为发生时,存款可以被撤销或削减 检测到 [10]。 请注意,这与 Bitcoin 不同,其中分叉是经常发生的 由于网络异步性和 ynding 的概率性质 部分 hash 碰撞。因为在很多情况下,恶意分叉是 由于异步,与分叉无法区分,Bitcoin 不能 可靠地实施分叉责任,而不是隐式的 矿工为开采孤立区块而支付的机会成本。 我们将投票阶段称为 PreVote 和 PreCommit。投票可以是 特定块或 Nil。我们称之为>⅔预投票的集合 对于同一轮 Polka 中的单个块,以及 >⅔ 的集合 在同一轮提交中预提交单个块。如果>⅔ 在同一轮中预提交为零,他们进入下一轮 圆形。 请注意,协议中的严格决定论会导致较弱的 同步假设,因为必须检测到错误的领导者并
跳过了。因此,validators 等待一段时间, TimeoutPropose,在 Prevote Nil 之前,以及值 TimeoutPropose 随着每一轮的增加而增加。进展通过 一轮的其余部分是完全异步的,因为进度只是 一旦 validator 收到来自 >⅔ 的网络消息。在实践中, 需要一个极其强大的对手才能无限期地挫败 弱同步假设(导致共识无法达成) 曾经提交过一个区块),这样做可以使更多 通过在每个上使用 TimeoutPropose 的随机值来实现困难 validator。 一组附加的约束或锁定规则,确保 网络最终将在每个高度只提交一个区块。任意 恶意尝试导致多个区块被提交 可以识别给定高度。首先,对块进行 PreCommit 必须以 Polka 的形式为该块提供合理性。 如果 validator 已经在 R_1 轮预提交了一个区块,我们 说他们被锁定在那个街区,波尔卡用来证明 R_2 轮的新 PreCommit 必须出现在 R_polka 轮中 其中 R_1 < R_polka <= R_2。其次,validators 必须提出 和/或对他们锁定的区块进行预投票。在一起,这些 条件确保 validator 不会在没有预提交的情况下进行预提交 有足够的证据作为正当理由,并且 validators PreCommit 已经无法为 PreCommit 提供证据 其他的东西。这既保证了安全性又保证了活跃性 共识算法。 此处描述了该协议的完整细节。 TendermintPoS 消除了同步所有区块头的需要,因为替代链(分叉)的存在意味着 ≥⅓ 担保权益可以被削减。当然,由于削减需要 有人分享分叉的证据,轻客户端应该存储 任何 block-hash 提交它看到的。此外,轻客户端可以定期与 validator 集的更改保持同步, 为了避免远程攻击(但其他解决方案是 可能)。 本着与 Ethereum 类似的精神,Tendermint 使应用程序能够 在每个块中嵌入一个全局 Merkle 根 hash ,从而轻松地允许 可验证的状态查询,例如帐户余额、价值 存储在合约中,或存在未花费的交易 输出,取决于应用程序的性质。 假设广播网络具有足够的弹性集合 和静态 validator 集,blockchain 中的任何分叉都可以 被发现并削减了违规 validator 的存款。这个 Vitalik Buterin 在 2014 年初提出的创新解决了 其他 proof-of-stake 的无利害关系问题 加密货币(参见相关工作)。但是,由于 validator 设置 必须能够在很长一段时间内改变原来的 validators 可能全部变为非绑定状态,因此可以自由 从创世块创建一条新链,不产生任何成本 他们不再锁定存款。这次攻击发生了 与短程攻击相比,称为远程攻击 (LRA) 范围攻击,当前绑定的 validator 会造成 分叉,因此会受到惩罚(假设分叉负责 BFT 像 Tendermint 共识这样的算法)。远程攻击是 通常被认为是对 proof-of-stake 的致命打击。 幸运的是,LRA 可以通过以下方式缓解。首先,对于一个 validator 解绑(从而收回其抵押存款 并且不再赚取参与共识的费用), 存款必须在一段时间内不可转让 称为“解绑期”,可能约为 几周或几个月。其次,为了保证轻客户端的安全,第一 当它连接到网络时,它必须验证最近的块-hash 针对可信来源,或者最好是多个来源。这个
这种情况有时被称为“弱主观性”。最后, 为了保持安全,它必须与最新的 validator 设置同步 最少与解绑期的长度一样频繁。这个 确保轻客户端知道 validator 的更改 在 validator 的资本解除绑定之前设置,因此不再 处于危险之中,这将使其能够通过执行来欺骗客户 通过从某个位置开始创建新块来进行远程攻击 它粘合的高度(假设它有足够的控制 许多早期的私钥)。 请注意,以这种方式克服 LRA 需要彻底修改 proof-of-work 的原始安全模型。在 PoW 中,是 假设轻客户端可以从 只需处理每个块头中的工作量证明即可随时获得可信创世块。然而,为了战胜上帝抵抗军,我们 要求轻客户端定期上线 跟踪 validator 集中的变化,并且第一时间他们 上网时他们必须特别小心地进行身份验证 他们从网络上听到的来自可信来源的信息。的 当然,后一个要求类似于 Bitcoin 的要求,其中 协议和软件还必须从受信任的机构获得 来源。 上述预防 LRA 的方法非常适合 validators 以及 Tendermint 支持的 blockchain 的完整节点,因为这些 节点旨在保持与网络的连接。的 该方法也适用于可以预期的轻客户端 经常与网络同步。然而,对于轻量级客户来说 预计不会经常访问互联网或 blockchain 网络,可以使用另一种解决方案来克服 圣主抵抗军。非 validator token 持有者可以将其 token 发布为 具有很长解绑期限的抵押品(例如更长的 超过 validators 的解绑期)并为轻客户端提供服务 使用第二种方法来证明当前和的有效性 过去的区块-hashes。虽然这些 token 不计入 blockchain 共识的安全性,但他们仍然可以为轻客户提供有力保障。如果历史区块-hash Ethereum 支持查询,任何人都可以绑定他们的 tokens 在专门设计的 smart contract 中并提供 付费认证服务,有效地为轻客户端 LRA 安全创造了市场。 由于块提交的定义,任何 ≥⅓ 的联盟 投票权可以通过是否关闭 blockchain 来阻止 blockchain 广播他们的选票。这样的联盟也可以审查 通过拒绝包含这些的块来特定交易 交易,尽管这会导致相当大的比例 的区块提案被拒绝,这将减慢速度 blockchain 的块提交,降低了其实用性和价值。 恶意联盟也可能会少量广播投票,以便 为了磨炼 blockchain 块,承诺几乎停止,或从事 这些攻击的任意组合。最后,它可能会导致 blockchain 通过双重签名或违反锁定来分叉 规则。 如果全球活跃的对手也参与其中,它可能会分裂 网络的方式可能会出现错误 validator 的子集导致了速度下降。这不是 只是 Tendermint 的限制,而是所有的限制 其网络可能由某个人控制的共识协议 积极的对手。 对于这些类型的攻击,validator 的子集应该 通过外部手段协调签署重组提案 选择一个分叉(及其任何证据)和初始子集 validator 及其签名。签署此类重组提案的验证者将放弃所有其他分叉上的抵押品。客户应该 验证重组提案上的签名,验证任何证据, 并做出判断或提示最终用户做出决定。对于 例如,手机钱包应用程序可能会提示用户安全
警告,而冰箱可以接受任何重组建议 由原始 validator 的 +1/2 投票权签署。 没有非同步的拜占庭容错算法可以来 当 ≥⅓ 的投票权不诚实时达成共识,但仍存在分叉 假设 ≥⅓ 的投票权已经被不诚实 没有正当理由的双重签名或锁更改。所以,签 重组提案是一个协调问题,无法解决 通过任何非同步协议解决(即自动,并且 不对可靠性做出假设 底层网络)。目前,我们将重组提案的协调问题留给人类通过社会共识进行协调 在网络媒体上。验证者必须注意确保 在签署重组提案之前没有剩余的网络分区,以避免签署两个相互冲突的重组提案的情况。 假设外部协调介质和协议是 稳健,因此与审查相比,分叉更受关注 攻击。 除了分叉和审查,需要≥⅓拜占庭 投票权,超过⅔投票权的联盟可以承诺 任意的、无效的状态。这是任何 (BFT) 的特征 共识系统。与创建分叉的双重签名不同 通过易于验证的证据,检测某人的承诺 无效状态需要非验证节点来验证整个块, 这意味着他们保留状态的本地副本并执行 每笔交易,独立计算状态根 他们自己。一旦检测到,处理此类故障的唯一方法 是通过社会共识。例如,在 Bitcoin 的情况下 失败了,是否由于软件 bug 导致分叉(如 3 月份 2013),或者由于拜占庭行为而提交无效状态 矿工(截至 2015 年 7 月),紧密联系的社区 企业、开发商、矿工和其他组织 关于什么是手动操作建立了社会共识参与者需要治愈网络。此外,由于 Tendermint blockchain 的 validator 可能预计为 无效国家的承诺甚至可能是可识别的 如果需要的话,可以受到法律或某些外部判例的惩罚。 ABCI 由 3 种主要消息类型组成,这些消息类型从 应用程序的核心。应用程序回复 相应的响应消息。 AppendTx 消息是应用程序的主力。每个 blockchain 中的事务随此消息一起传递。的 应用程序需要验证收到的每笔交易 针对当前状态、应用程序协议的 AppendTx 消息, 以及交易的加密凭证。经过验证的 然后事务需要更新应用程序状态 - 通过 将值绑定到键值存储中,或者通过更新 UTXO 数据库。 CheckTx 消息与 AppendTx 类似,但仅适用于 验证交易。 Tendermint Core 的内存池首次检查 与 CheckTx 交易的有效性,并且仅中继有效 与其同行的交易。应用程序可以检查递增 nonce 在交易中,并在 CheckTx 上返回错误,如果 nonce 已旧。 “提交”消息用于计算密码 对当前应用程序状态的承诺,将被放入 下一个块头。这有一些方便的属性。 更新该状态时的不一致现在将显示为 blockchain fork 捕获整个类的编程 错误。这也简化了安全轻量化的开发 客户,因为 Merkle-hash 证明可以通过检查来验证 区块-hash,区块-hash由法定人数签名 validators(按投票权)。
额外的 ABCI 消息允许应用程序跟踪 并更改 validator 设置,并让应用程序接收 区块信息,例如高度和提交投票。 ABCI 请求/响应是简单的 Protobuf 消息。检查 出架构yle。 论据: 数据([]byte):请求交易字节 返回: 代码 (uint32):响应代码 数据([]byte):结果字节(如果有) 日志(字符串):调试或错误消息 用途:
追加并运行事务。如果交易有效, 返回 CodeType.OK 论据: 数据([]byte):请求交易字节 返回: 代码 (uint32):响应代码 数据([]byte):结果字节(如果有) 日志(字符串):调试或错误消息 用途:
验证交易。此消息不应改变 状态。交易首先通过 CheckTx 运行 广播到内存池层中的对等点。你可以使 CheckTx 半状态并在提交时清除状态或 BeginBlock ,允许依赖的交易序列 在同一个街区。
返回: 数据([]byte):Merkle 根 hash 日志(字符串):调试或错误消息 用途:
返回应用程序状态的 Merkle 根 hash。 论据: Data ([]byte) :查询请求字节 返回: 代码 (uint32):响应代码 数据([]byte):查询响应字节 日志(字符串):调试或错误消息 用途:
刷新响应队列。实施的应用程序 types.Application 不需要实现此消息 - 它是 由项目处理。 返回: 数据([]byte):信息字节 用途:
返回有关应用程序状态的信息。应用 具体。 论据: Key(字符串):要设置的键
值(字符串):为键设置的值 返回: 日志(字符串):调试或错误消息 用途:
设置应用程序选项。例如。键=“模式”,值=“mempool” 内存池连接,或 Key=“mode”,Value=“consensus” 共识连接。其他选项是特定于应用程序的。 论据: 验证器([]Validator):初始起源-validators 用途:
创世时被召唤一次 论据: 高度 (uint64):起始区块高度 用途:
表示新块的开始。在任何之前调用 追加 Txs。 论据: 高度 (uint64):结束的区块高度 返回: 验证器([]Validator):将 validators 更改为新的 投票权(0表示删除) 用途:
发出块结束的信号。毕竟在每次提交之前调用 交易 有关更多详细信息,请参阅 ABCI 存储库。发件人可能想要的原因有多种 接收链对数据包传送的确认。 例如,发送者可能不知道消息的状态 目标链(如果预计会出现故障)。或者,发件人可以 想要对数据包施加超时(使用 MaxHeight 数据包产量),而任何目标链都可能遭受拒绝服务攻击,传入数量突然激增 数据包。 在这些情况下,发件人可以要求送达确认 将初始数据包状态设置为 AckPending。那么,就是 接收链有责任通过包括 Merkle 应用程序中缩写为 IBCPacket hash。 首先,在“Hub”上发布 IBCBlockCommit 和 IBCPacketTx 这证明了“Zone1”上存在 IBCPacket。这么说 IBCPacketTx 具有以下值: FromChainID:“Zone1” FromBlockHeight : 100 (比如说) 数据包:IBC数据包:
标头:IBCPacketHeader: 源链ID:“Zone1” 目标链 ID:“Zone2” 数量:200(比如说) 状态:确认待处理 类型:“硬币” MaxHeight:350(假设“Hub”当前高度为 300) Payload : <“硬币”有效负载的字节> 接下来,在“Zone2”上发布 IBCBlockCommit 和 IBCPacketTx 这证明了“Hub”上存在IBCPacket。这么说 IBCPacketTx 具有以下值: FromChainID : “Hub” 从块高度:300 数据包: IBC 数据包: 标头:IBCPacketHeader: 源链ID:“Zone1” 目标链 ID:“Zone2” 数量:200 状态:确认待处理 类型:“硬币” 最大高度:350 有效负载:<“硬币”有效负载的相同字节> 接下来,“Zone2”必须在其应用程序-hash中包含一个缩写数据包 显示 AckSent 的新状态。 IBCBlockCommit 和 IBCPacketTx 被发布回“Hub”,证明存在 “Zone2”上的缩写IBCPacket。说 IBCPacketTx 具有以下值: FromChainID:“Zone2”
FromBlockHeight : 400 (比如说) 数据包: IBC 数据包: 标头:IBCPacketHeader: 源链ID:“Zone1” 目标链 ID:“Zone2” 数量:200 状态:已发送 类型:“硬币” 最大高度:350 PayloadHash : <同一“硬币”有效负载的 hash 字节> 最后,“集线器”必须更新数据包的状态 AckPending 到 AckReceived。这种新的分析状态的证据 应该回到“Zone2”。假设 IBCPacketTx 具有以下内容 值: FromChainID : “Hub” 从块高度:301 数据包: IBC 数据包: 标头:IBCPacketHeader: 源链ID:“Zone1” 目标链 ID:“Zone2” 数量:200 状态:已收到 类型:“硬币” 最大高度:350 PayloadHash : <同一“硬币”有效负载的 hash 字节> 同时,“Zone1”可能乐观地认为交付成功 除非有相反的证据证明是“硬币”包 “枢纽”。在上面的示例中,如果“Hub”未收到 AckSent
块 350 来自“Zone2”的状态,它会设置状态 自动超时。这个超时的证据可以得到 发回“Zone1”,并且可以返回任何 token。 支持两种类型的 Merkle tree Tendermint/Cosmos 生态系统:简单树和 IAVL+ 树。 简单树是一个静态元素列表的 Merkle tree 。如果 项目数不是 2 的幂,有些叶子将位于 不同的级别。简单树试图保持树的两侧 高度相同,但左侧可能更大。这个 Merkle tree 是 用于对区块的交易进行 Merkle 化,顶层 应用程序状态根的元素。IAVL+数据结构的目的是提供持久性 应用程序状态中键值对的存储,以便 可以有效地计算确定性 Merkle 根 hash。的 使用 AVL 算法的变体来平衡树,并且所有 操作是 O(log(n))。 在AVL树中,任意节点的两个子子树的高度 最多相差一。每当违反此条件时 更新时,通过创建 O(log(n)) 个新节点来重新平衡树 指向旧树中未修改的节点。在原来的AVL中 算法中,内部节点也可以保存键值对。 AVL+ 算法(注意加号)修改AVL算法以保留所有 叶节点上的值,而仅使用分支节点来存储键。 这简化了算法,同时保留了 Merkle hash 踪迹 短。 AVL+ 树类似于 Ethereum 的 Patricia 尝试。有 权衡。键在插入之前不需要 hashed IAVL+ 树,因此这可以在键中提供更快的有序迭代 空间可能有利于某些应用程序。逻辑更简单 实现,只需要两种类型的节点——内部节点和 叶节点。 Merkle 证明平均较短,是 * / \ / \ / \ / \ * * / \ / \ / \ / \ / \ / \ * * * h6 / \ / \ / \ h0 h1 h2 h3 h4 h5 具有 7 个元素的 SimpleTree
平衡二叉树。另一方面,默克尔根 IAVL+树取决于更新的顺序。 我们将支持额外的高效 Merkle tree,例如 当二进制变体变为 Ethereum 的 Patricia Trie 时 可用。 在规范的实现中,交易被流式传输到 Cosmos 集线器应用程序通过 ABCI 接口。 Cosmos Hub将接受一些主要交易 类型,包括 SendTx、BondTx、UnbondTx、ReportHackTx、 SlashTx、BurnAtomTx、ProposalCreateTx 和 ProposalVoteTx、 这是相当不言自明的,并将记录在 本文的未来修订。在这里我们记录了两个主要的 IBC 的交易类型:IBCBlockCommitTx 和 IBCPacketTx。 IBCBlockCommitTx 交易由以下部分组成: ChainID(字符串):blockchain 的 ID BlockHash ([]byte) :块 hash 字节,Merkle 根 其中包括应用程序-hash BlockPartsHeader (PartSetHeader) :块部件集标头 字节,仅需要验证投票签名 BlockHeight (int) :提交的高度 BlockRound (int) :提交的轮次 提交([]投票):>⅔ Tendermint 预提交投票表明 包含一个块提交 ValidatorsHash ([]byte) :新的 Merkle 树根 hash validator 设置
ValidatorsHashProof (SimpleProof):一个 SimpleTree Merkleproof,用于根据 BlockHash 证明 ValidatorsHash AppHash ([]byte) :IAVLTree Merkle 树根 hash 应用状态 AppHashProof (SimpleProof):SimpleTree Merkle 证明 对照 BlockHash 证明 AppHash IBC数据包由以下部分组成: 标头 (IBCPacketHeader) :数据包标头 Payload ([]byte) :数据包有效负载的字节。可选 PayloadHash ([]byte) :数据包字节的 hash 。 可选 Payload 或 PayloadHash 之一必须存在。 hash IBCPacket 的 是两个项目的简单 Merkle 根,即 Header 和有效负载。没有完整负载的 IBC 数据包称为 缩写数据包。 IBCPacketHeader 由以下部分组成: SrcChainID(字符串):源 blockchain ID DstChainID(字符串):目的地 blockchain ID Number(int):所有数据包的唯一编号 状态(枚举):可以是 AckPending 、 AckSent 之一, AckReceived 、 NoAck 或超时 类型(字符串):类型取决于应用程序。 Cosmos 保留“coin”数据包类型 MaxHeight (int) :如果状态不是 NoAckWanted 或 AckReceived 到了这个高度,状态就变成 Timeout 。可选 IBCPacketTx 交易由以下部分组成:FromChainID(字符串):blockchain 的 ID,即 提供此数据包;不一定是来源 FromBlockHeight (int) : blockchain 高度,其中 以下数据包包含(Merkle 化)在块 hash 中 源链 Packet (IBCPacket) :数据包,其状态可能是一个 AckPending 、 AckSent 、 AckReceived 、 NoAck 或 Timeout PacketProof (IAVLProof):用于证明的 IAVLTree Merkle-proof 数据包的 hash 与源链的 AppHash 相对应 给定高度 从“Zone1”到“Zone2”发送数据包的顺序 通过“集线器”的情况如{图X}所示。首先,一个 IBCPacketTx 向“Hub”证明该数据包包含在应用程序状态中 “1区”。然后,另一个 IBCPacketTx 向“Zone2”证明 数据包包含在“Hub”的应用程序状态中。在此期间 过程中,IBCPacket 的结果是相同的:SrcChainID 是 始终为“Zone1”,DstChainID 始终为“Zone2”。 PacketProof 必须具有正确的 Merkle-proof 路径,如下所示 如下: 当“Zone1”想要通过“Hub”向“Zone2”发送数据包时, 无论数据包在“Zone1”、“Hub”还是“Zone2”上进行 Merkleized,IBCPacket 数据都是相同的。唯一可变的yield是 跟踪递送的状态。 我们感谢我们的朋友和同行在概念化方面提供的帮助, 审查并为我们与 Tendermint 的合作提供支持 和 Cosmos。 IBC/<源链ID>/<目标链ID>/<编号>
SkuChain 的 Zaki Manian 在格式化和 措辞,特别是在 ABCI 部分下 Althea 的 Jehan Tremback 和达斯汀·拜因顿 (Dustin Byington) 提供的帮助 初始迭代 Honey Badger 的 Andrew Miller 对共识的反馈 Greg Slepak 对共识和措辞的反馈 还要感谢 Bill Gleim 和 Seunghwan Han 所做的各种努力 贡献。 此处提供您的姓名和组织以供您贡献 1 Bitcoin:https://bitcoin.org/bitcoin.pdf 2 零现金:http://zerocash-project.org/paper 3Ethereum:https://github.com/ethereum/wiki/wiki/WhitePaper 4DAO: https://download.slock.it/public/DAO/WhitePaper.pdf 5 隔离证人: https://github.com/bitcoin/bips/blob/master/bip0141.mediawiki 6 BitcoinNG:https://arxiv.org/pdf/1510.02037v2.pdf 7 闪电网络:https://lightning.network/lightningnetwork-paper-DRAFT-0.5.pdf 8 嫩薄荷: https://github.com/tendermint/tendermint/wiki 9 FLP 不可能: https://groups.csail.mit.edu/tds/papers/Lynch/jacm85.pdf 10 杀手:https://blog.ethereum.org/2014/01/15/slasher-apunitive-proof-of-stake-algorithm/ 11 PBFT:http://pmg.csail.mit.edu/papers/osdi99.pdf 12 种比特股:https://bitshares.org/technology/delegatedproof-of-stake-consensus/
13Stellar:https://www.stellar.org/papers/stellar-consensusprotocol.pdf 14 跨账本:https://interledger.org/rfcs/0001-interledgerarchitecture/ 15 条侧链:https://blockstream.com/sidechains.pdf 16卡斯帕: https://blog.ethereum.org/2015/08/01/introducing-casperfriendly-ghost/ 17ABCI:https://github.com/tendermint/abci 18 Ethereum 分片: https://github.com/ethereum/EIPs/issues/53 19 LibSwift: http://www.ds.ewi.tudelft.nl/yleadmin/pds/papers/Performa nceAnalysisOfLibswift.pdf 20 个 DLS: http://groups.csail.mit.edu/tds/papers/Lynch/jacm88.pdf 21 瘦客户端安全: https://en.bitcoin.it/wiki/Thin_Client_Security 22 Ethereum 2.0 紫红色纸: http://vitalik.ca/yles/mauve_paper.html https://www.docdroid.net/ec7xGzs/314477721-ethereumplatform-review-opportunities-and-challenges-for-privateand-consortium-blockchains.pdf.html
Ø è