Chainlink
Chainlink
Операции DON с сохранением конфиденциальности
Context
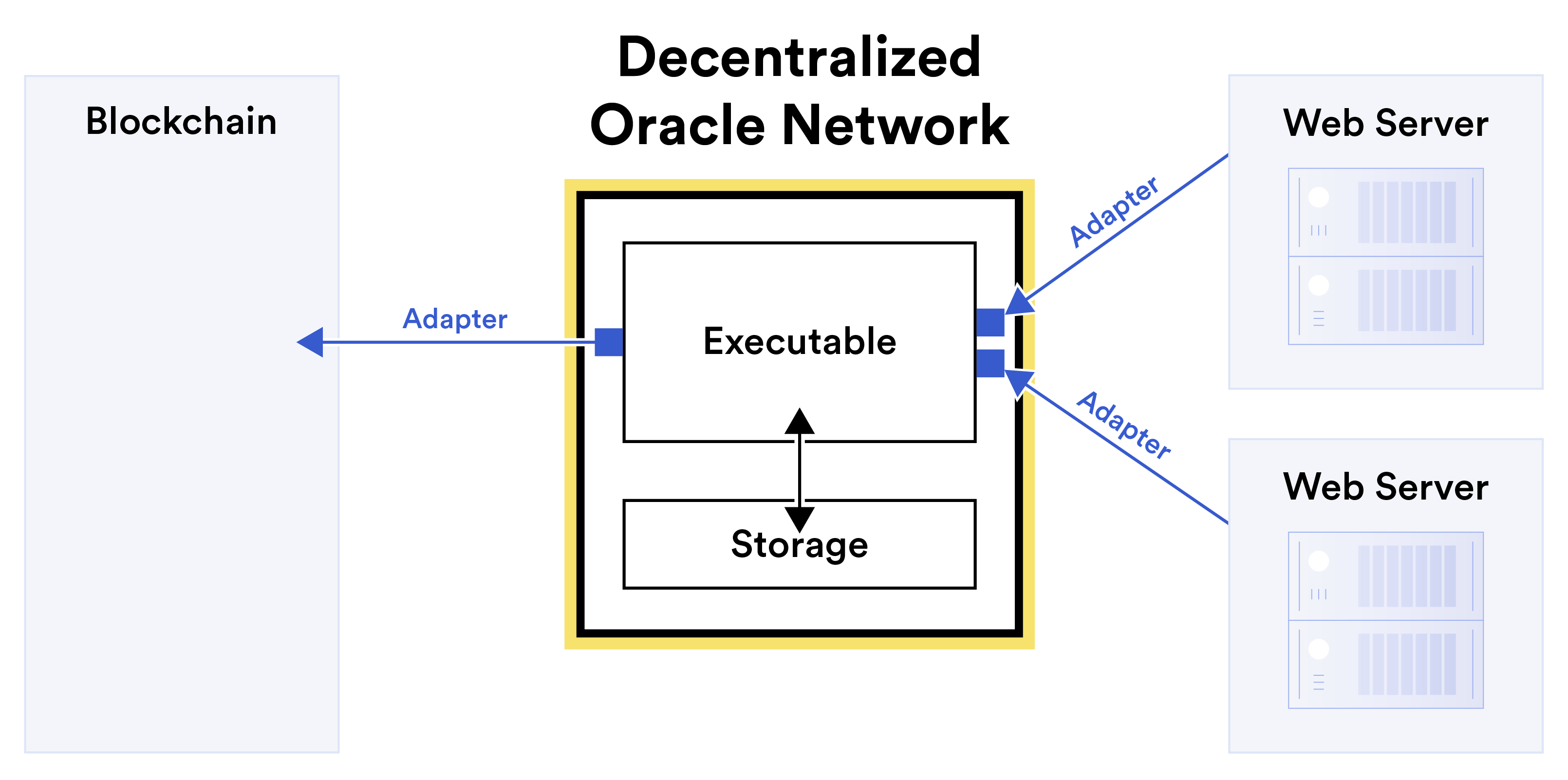
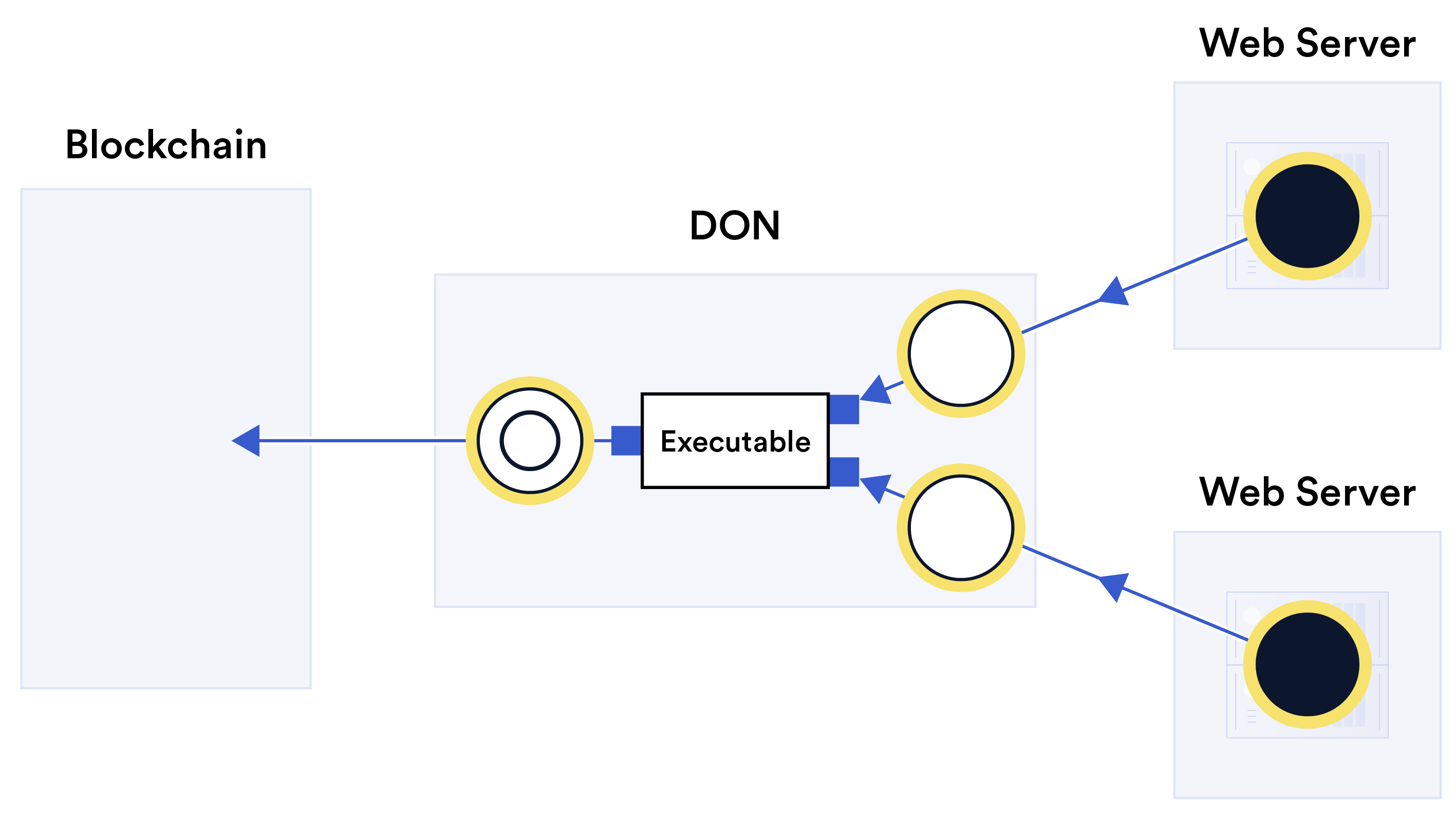
This figure appears in the Introduction during the discussion of confidentiality, describing how oracle networks can combine blockchain transparency with new privacy protections. It illustrates the flow of sensitive data from external web servers through confidentiality-preserving adapters and confidential computation within a DON before a sanitized report reaches the blockchain. The whitepaper identifies three approaches to confidentiality: confidentiality-preserving adapters, confidential computation, and support for confidential layer-2 systems.
What This Figure Shows
The figure shows sensitive source data (black circles) residing in web servers being extracted to the DON via confidentiality-preserving adapters (blue double-arrowed lines). The DON receives derived data (hollow circles) from these adapters—the result of applying either a function or secret-sharing to the sensitive source data—rather than the raw sensitive values themselves. An executable on the DON then applies confidential computation to the derived data to construct a report (double circle), which it sends over an adapter to the blockchain. Technologies such as DECO and Town Crier enable this privacy-preserving extraction without requiring modifications to the target web servers.
Significance
This figure illustrates how DONs can unlock applications that are currently infeasible due to privacy requirements, including private DeFi, decentralized identity, credit-based on-chain lending, and KYC processes. It demonstrates that strong confidentiality and blockchain transparency are not mutually exclusive but can be combined through careful architectural design.