
솔라나: 고성능 블록체인을 위한 새로운 아키텍처
Abstract
Este documento presenta una nueva arquitectura para una blockchain de alto rendimiento. Solana implementa un novedoso mecanismo de cronometraje llamado Proof of History (PoH) -- una prueba para verificar el orden y el paso del tiempo entre eventos. PoH se utiliza para codificar el paso del tiempo de manera trustless en un ledger, creando un registro historico que demuestra que un evento ocurrio en un momento especifico en el tiempo.
La innovacion clave es que PoH permite que los nodos de la red establezcan un orden temporal de eventos sin necesidad de comunicarse entre si. Al utilizar una funcion de retardo verificable implementada como una cadena secuencial de hashes, el sistema genera un reloj criptografico que proporciona una forma de verificar el paso del tiempo entre eventos. Esto permite que la red procese miles de transacciones por segundo manteniendo la descentralizacion y la seguridad.
PoH esta integrado con un mecanismo de consenso Proof of Stake (PoS). La combinacion permite una arquitectura blockchain altamente optimizada donde los validadores pueden verificar transacciones en paralelo y alcanzar consenso de manera eficiente. El sistema esta disenado para escalar con la Ley de Moore, aprovechando los aumentos en el rendimiento del hardware para mejorar el throughput sin sacrificar las garantias de seguridad de una red descentralizada.
Abstract
본 논문은 고성능 블록체인을 위한 새로운 아키텍처를 제시한다. Solana는 Proof of History(PoH)라는 새로운 시간 기록 메커니즘을 구현한다. 이는 이벤트 간의 순서와 시간 경과를 검증하기 위한 증명이다. PoH는 신뢰가 필요 없는 시간 경과를 원장에 인코딩하는 데 사용되며, 특정 시점에 이벤트가 발생했음을 증명하는 역사적 기록을 생성한다.
핵심 혁신은 PoH가 네트워크의 노드들이 서로 통신할 필요 없이 이벤트의 시간적 순서를 확립할 수 있도록 한다는 점이다. 순차적 해시 체인으로 구현된 검증 가능한 지연 함수(VDF)를 사용함으로써, 시스템은 이벤트 간 시간 경과를 검증하는 방법을 제공하는 암호학적 시계를 생성한다. 이를 통해 네트워크는 탈중앙화와 보안을 유지하면서 초당 수천 건의 트랜잭션을 처리할 수 있다.
PoH는 Proof of Stake(PoS) 합의 메커니즘과 통합된다. 이 조합은 검증자가 트랜잭션을 병렬로 검증하고 효율적으로 합의에 도달할 수 있는 고도로 최적화된 블록체인 아키텍처를 가능하게 한다. 이 시스템은 무어의 법칙에 맞춰 확장되도록 설계되었으며, 분산 네트워크의 보안 보장을 희생하지 않으면서 하드웨어 성능 향상을 활용하여 처리량을 개선한다.
Introduction
El desafio fundamental en los sistemas blockchain es lograr un alto rendimiento de transacciones mientras se mantiene la descentralizacion y la seguridad. Las implementaciones actuales de blockchain estan limitadas por sus mecanismos de consenso, que requieren una comunicacion extensa entre nodos para acordar el tiempo y el ordenamiento de eventos. Esta sobrecarga de coordinacion crea un cuello de botella que impide que las blockchains existentes escalen para satisfacer las demandas de aplicaciones a escala global.
El problema central es el tiempo. En sistemas distribuidos, los nodos no pueden depender de relojes externos porque no pueden confiar en que las marcas de tiempo de otros nodos sean precisas. Los protocolos de consenso blockchain tradicionales resuelven esto haciendo que los nodos se comuniquen extensamente para acordar el estado actual y el orden de las transacciones. Esta sobrecarga de comunicacion limita fundamentalmente el rendimiento, ya que la red solo puede procesar transacciones tan rapido como los nodos pueden alcanzar consenso sobre su ordenamiento.
Solana introduce Proof of History como solucion a este problema de sincronizacion. PoH proporciona una forma criptografica de demostrar que ha pasado una cierta cantidad de tiempo entre eventos sin depender de marcas de tiempo de actores potencialmente maliciosos. Al crear un registro historico verificable, PoH permite que los nodos procesen transacciones de forma independiente mientras pueden demostrar el orden en que ocurrieron los eventos. Este avance permite que la red paralelice el procesamiento de transacciones y aumente dramaticamente el rendimiento.
La idea clave es que si podemos crear una fuente de tiempo sin confianza, podemos eliminar el cuello de botella de coordinacion del consenso. Con PoH proporcionando un reloj criptografico, los validadores pueden procesar transacciones en paralelo y solo necesitan comunicarse para finalizar el ordenamiento canonico. Este cambio arquitectonico permite a Solana alcanzar niveles de rendimiento que antes se consideraban imposibles en una blockchain descentralizada.
Introduction
블록체인 시스템의 근본적인 과제는 탈중앙화와 보안을 유지하면서 높은 트랜잭션 처리량을 달성하는 것이다. 현재의 블록체인 구현은 시간과 이벤트 순서에 대해 합의하기 위해 노드 간 광범위한 통신을 요구하는 합의 메커니즘에 의해 제한된다. 이러한 조율 오버헤드는 기존 블록체인이 글로벌 규모의 애플리케이션 수요를 충족하기 위해 확장하는 것을 방해하는 병목 현상을 만든다.
핵심 문제는 시간이다. 분산 시스템에서 노드는 다른 노드의 타임스탬프가 정확한지 신뢰할 수 없기 때문에 외부 시계에 의존할 수 없다. 전통적인 블록체인 합의 프로토콜은 현재 상태와 트랜잭션 순서에 합의하기 위해 노드들이 광범위하게 통신하는 방식으로 이 문제를 해결한다. 이러한 통신 오버헤드는 근본적으로 처리량을 제한하는데, 네트워크는 노드가 순서에 대해 합의에 도달할 수 있는 속도만큼만 트랜잭션을 처리할 수 있기 때문이다.
Solana는 이 타이밍 문제에 대한 해결책으로 Proof of History를 도입한다. PoH는 악의적인 행위자의 타임스탬프에 의존하지 않고도 이벤트 사이에 일정량의 시간이 경과했음을 증명하는 암호학적 방법을 제공한다. 검증 가능한 역사적 기록을 생성함으로써, PoH는 노드가 이벤트 발생 순서를 증명할 수 있으면서도 독립적으로 트랜잭션을 처리할 수 있게 한다. 이 혁신은 네트워크가 트랜잭션 처리를 병렬화하고 처리량을 극적으로 증가시킬 수 있게 한다.
핵심 통찰은 신뢰가 필요 없는 시간 소스를 만들 수 있다면, 합의에서 조율 병목을 제거할 수 있다는 것이다. PoH가 암호학적 시계를 제공함으로써, 검증자는 트랜잭션을 병렬로 처리할 수 있으며 정규 순서를 확정하기 위해서만 통신하면 된다. 이러한 아키텍처 전환은 Solana가 탈중앙화된 블록체인에서 이전에 불가능하다고 여겨졌던 성능 수준을 달성할 수 있게 한다.
Outline
Este documento describe la arquitectura tecnica de Solana, centrándose en como Proof of History permite la operacion blockchain de alto rendimiento. El documento primero explica el mecanismo PoH en si — como una cadena de hash secuencial crea un ordenamiento temporal verificable de eventos. Detallamos las propiedades criptograficas que hacen seguro a PoH y demostramos como los validadores pueden verificar eficientemente la secuencia PoH.
Luego el documento explora como PoH se integra con el consenso Proof of Stake. Describimos Tower BFT, un algoritmo PoS disenado especificamente para aprovechar las propiedades temporales de PoH. La integracion permite a los validadores votar sobre el estado del libro mayor en marcas de tiempo PoH especificas, creando un mecanismo de consenso que es rapido y seguro. Tambien explicamos las condiciones de penalizacion que previenen el comportamiento malicioso.
A continuacion, presentamos el diseno de red de Solana y los protocolos de propagacion de datos. El protocolo Gulf Stream permite el reenvio de transacciones sin necesidad de un mempool, permitiendo a los clientes enviar transacciones directamente a los proximos lideres. Describimos como funciona la rotacion de lideres y como la red mantiene un alto rendimiento incluso cuando cambia el liderazgo.
Finalmente, discutimos la arquitectura del sistema incluyendo la Transaction Processing Unit (TPU), el runtime paralelo Sealevel y Proof of Replication para la verificacion del almacenamiento de datos. Las proyecciones de rendimiento demuestran que Solana puede procesar mas de 700,000 transacciones por segundo en una red gigabit estandar, con un rendimiento que escala a medida que mejora el hardware.
Outline
본 논문은 Proof of History가 고성능 블록체인 운영을 가능하게 하는 방식에 초점을 맞추어 Solana의 기술 아키텍처를 설명한다. 문서는 먼저 PoH 메커니즘 자체 — 순차적 해시 체인이 검증 가능한 시간적 순서를 생성하는 방법 — 를 설명한다. PoH를 안전하게 만드는 암호학적 속성을 상세히 기술하고, 검증자가 PoH 시퀀스를 효율적으로 검증할 수 있는 방법을 보여준다.
이어서 논문은 PoH가 Proof of Stake 합의와 어떻게 통합되는지 탐구한다. PoH의 시간적 속성을 활용하도록 특별히 설계된 PoS 알고리즘인 Tower BFT를 설명한다. 이 통합은 검증자가 특정 PoH 타임스탬프에서 원장 상태에 투표할 수 있게 하여, 빠르고 안전한 합의 메커니즘을 만든다. 또한 악의적 행동을 방지하는 슬래싱 조건도 설명한다.
다음으로, Solana의 네트워크 설계와 데이터 전파 프로토콜을 제시한다. Gulf Stream 프로토콜은 멤풀 없이 트랜잭션 전달을 가능하게 하여, 클라이언트가 다가오는 리더에게 직접 트랜잭션을 보낼 수 있게 한다. 리더 교체가 어떻게 작동하는지, 그리고 네트워크가 리더십이 변경되는 동안에도 높은 처리량을 유지하는 방법을 설명한다.
마지막으로, Transaction Processing Unit(TPU), Sealevel 병렬 런타임, 데이터 저장 검증을 위한 Proof of Replication을 포함한 시스템 아키텍처를 논의한다. 성능 예측은 Solana가 표준 기가비트 네트워크에서 초당 700,000건 이상의 트랜잭션을 처리할 수 있으며, 하드웨어가 개선됨에 따라 처리량이 확장됨을 보여준다.
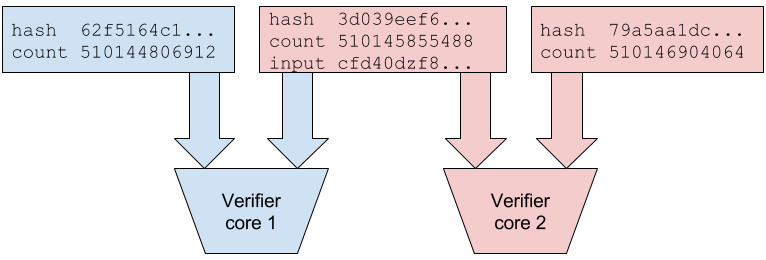
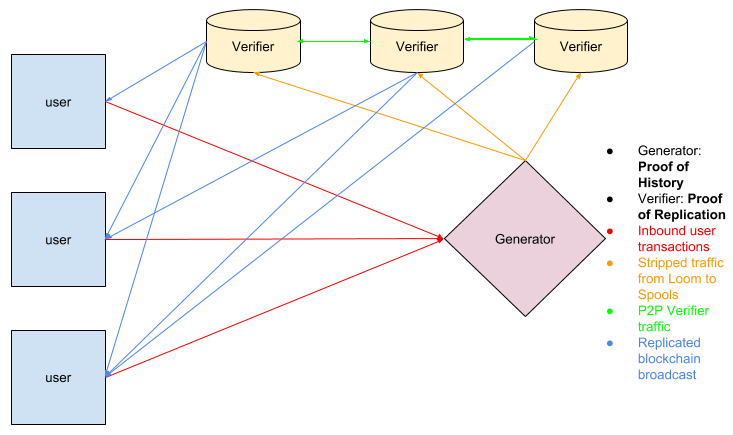
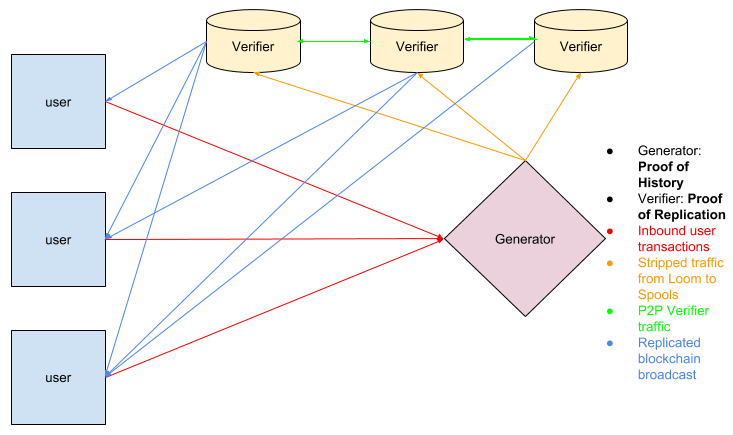
Network Design
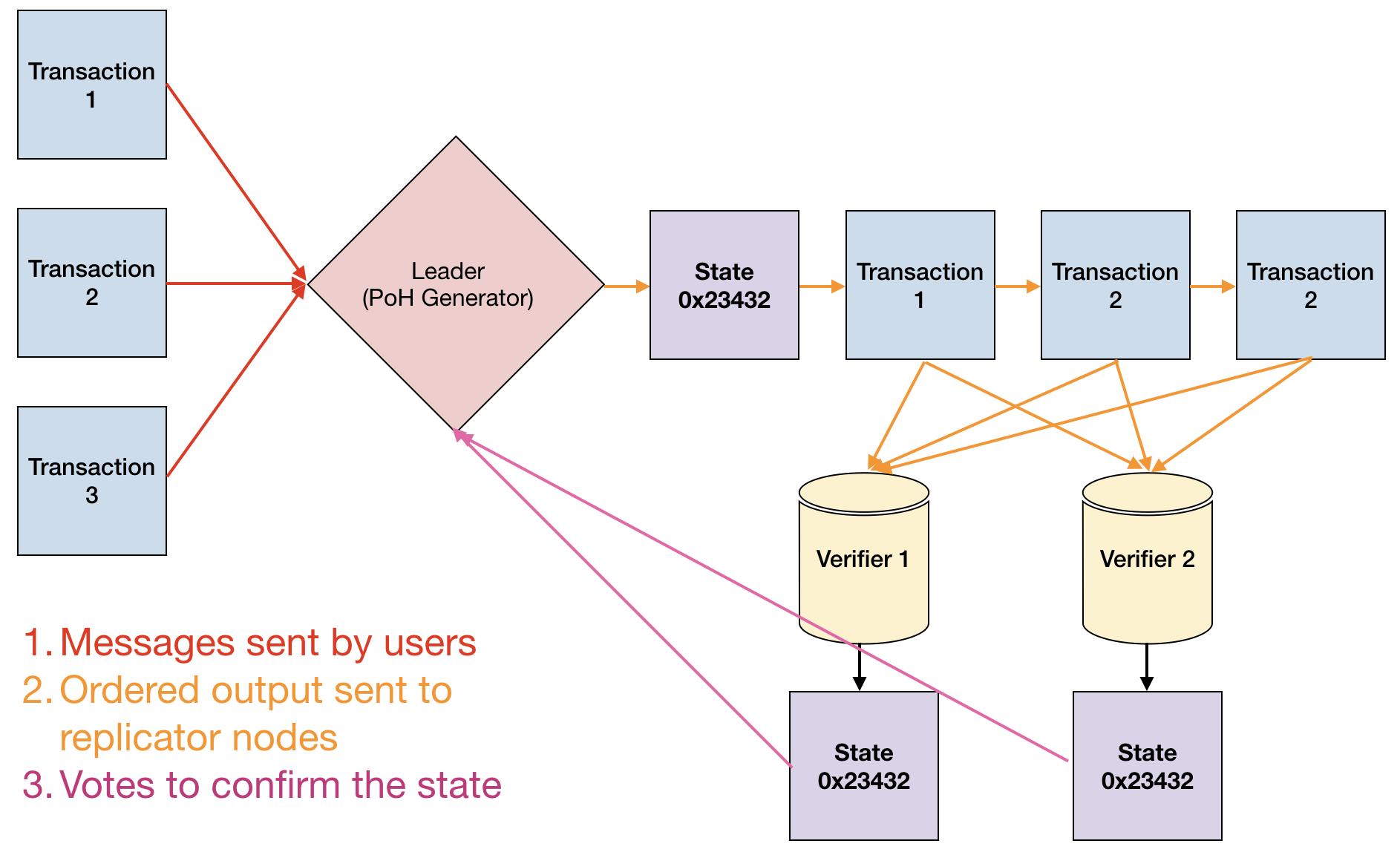
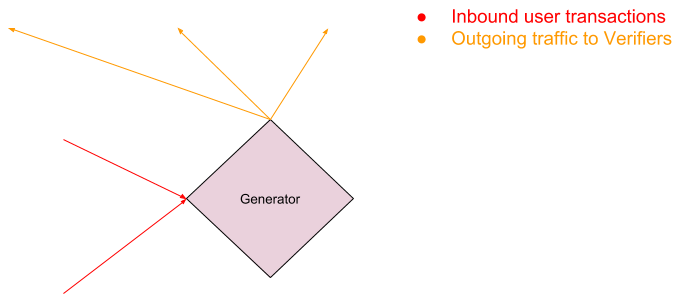
El diseno de red de Solana se centra en un sistema de lideres rotativos donde los validadores se turnan para producir bloques. El lider es responsable de secuenciar las transacciones entrantes en el flujo PoH y publicar los bloques resultantes en la red. Los lideres se seleccionan mediante un algoritmo ponderado por participacion, y el calendario de rotacion se conoce de antemano, lo que permite a la red optimizar el reenvio de transacciones.
El protocolo Gulf Stream elimina la necesidad de un mempool tradicional al permitir que los clientes reenvien transacciones directamente a los proximos lideres. Cuando un cliente envia una transaccion, se reenvia al lider esperado segun el calendario de rotacion. Si el lider actual no puede procesar la transaccion, la reenvia al siguiente lider esperado. Este diseno reduce la latencia de confirmacion y permite a los validadores ejecutar transacciones por adelantado, optimizando aun mas el rendimiento.
La propagacion de transacciones utiliza un enfoque multicapa. Los clientes envian transacciones a los validadores, quienes las reenvian al lider actual o proximo. El lider secuencia las transacciones en el flujo PoH, creando un ordenamiento total. Una vez secuenciadas, el lider transmite el flujo PoH y los datos de transaccion a los validadores, quienes verifican la secuencia PoH y ejecutan las transacciones en paralelo.
El diseno de red tambien incluye un protocolo de propagacion de bloques Turbine que divide los bloques en paquetes mas pequenos y los distribuye a traves de la red en una estructura de arbol. Este enfoque minimiza los requisitos de ancho de banda para validadores individuales mientras asegura una rapida propagacion de bloques. Combinado con la capacidad de PoH para verificar el ordenamiento de transacciones, esta arquitectura permite a Solana lograr un alto rendimiento sin sacrificar la descentralizacion.
Network Design
Solana의 네트워크 설계는 검증자들이 교대로 블록을 생성하는 순환 리더 시스템을 중심으로 한다. 리더는 수신되는 트랜잭션을 PoH 스트림으로 시퀀싱하고 결과 블록을 네트워크에 게시하는 책임을 진다. 리더는 스테이크 가중 알고리즘을 통해 선출되며, 교체 일정은 사전에 알려져 있어 네트워크가 트랜잭션 전달을 최적화할 수 있다.
Gulf Stream 프로토콜은 클라이언트가 다가오는 리더에게 직접 트랜잭션을 전달할 수 있게 함으로써 기존의 멤풀 필요성을 제거한다. 클라이언트가 트랜잭션을 제출하면, 교체 일정에 따라 예상 리더에게 전달된다. 현재 리더가 트랜잭션을 처리할 수 없는 경우, 다음 예상 리더에게 전달한다. 이 설계는 확인 지연을 줄이고 검증자가 미리 트랜잭션을 실행할 수 있게 하여 처리량을 더욱 최적화한다.
트랜잭션 전파는 다층 접근 방식을 사용한다. 클라이언트는 검증자에게 트랜잭션을 보내고, 검증자는 현재 또는 다가오는 리더에게 이를 전달한다. 리더는 트랜잭션을 PoH 스트림으로 시퀀싱하여 전체 순서를 생성한다. 시퀀싱이 완료되면, 리더는 PoH 스트림과 트랜잭션 데이터를 검증자에게 전송하고, 검증자는 PoH 시퀀스를 검증하고 트랜잭션을 병렬로 실행한다.
네트워크 설계에는 블록을 더 작은 패킷으로 나누어 트리 구조로 네트워크 전체에 분산하는 turbine 블록 전파 프로토콜도 포함된다. 이 접근 방식은 빠른 블록 전파를 보장하면서 개별 검증자의 대역폭 요구 사항을 최소화한다. PoH의 트랜잭션 순서 검증 능력과 결합된 이 아키텍처는 Solana가 탈중앙화를 희생하지 않으면서 높은 처리량을 달성할 수 있게 한다.
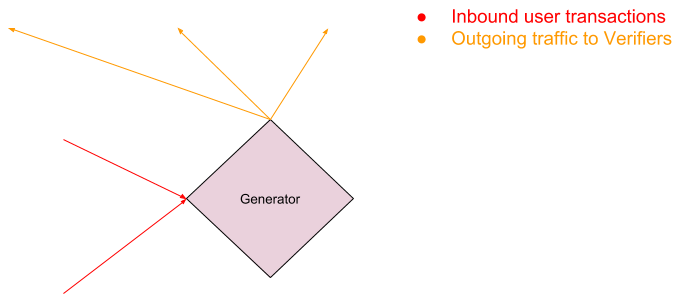
Proof of History
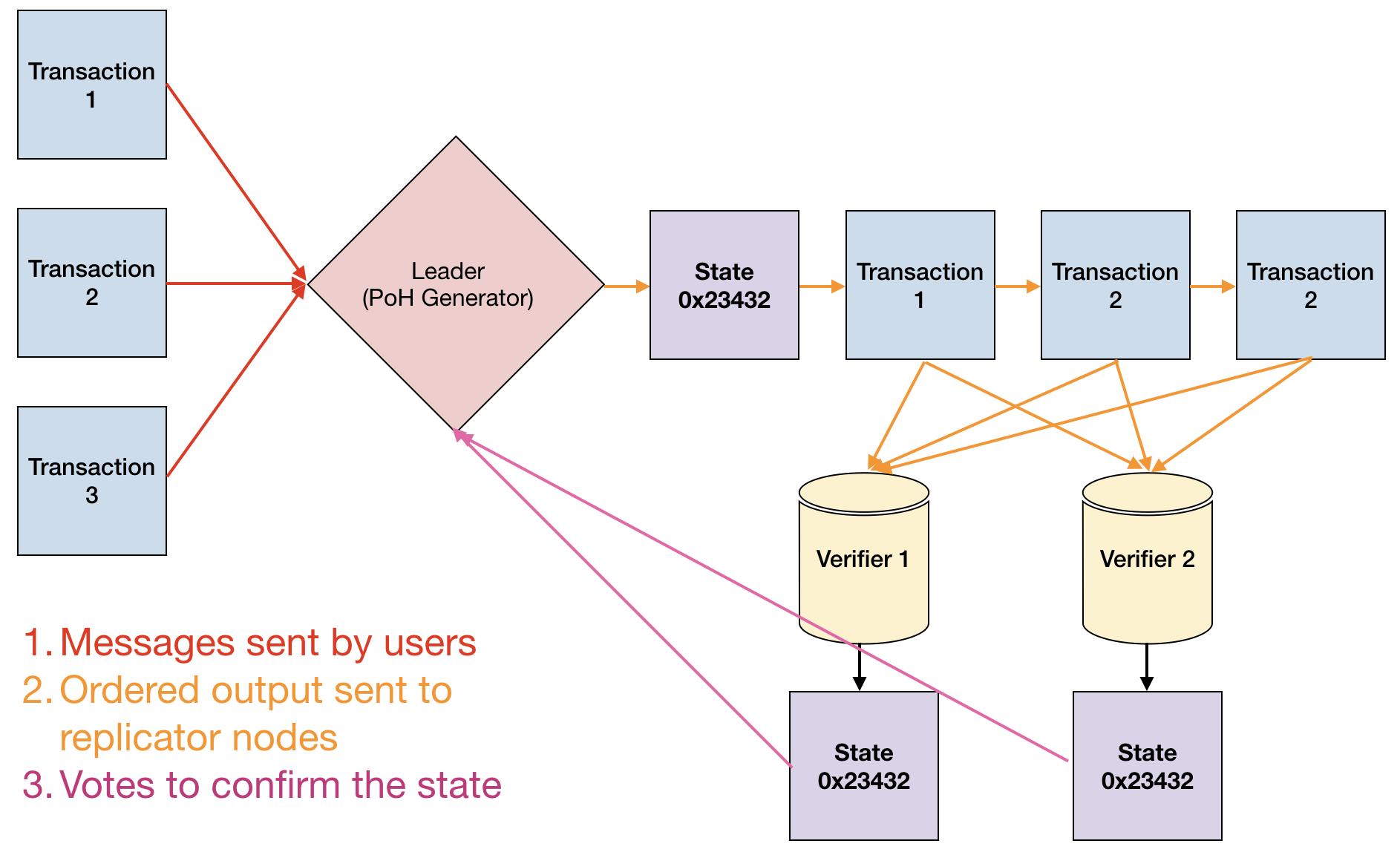
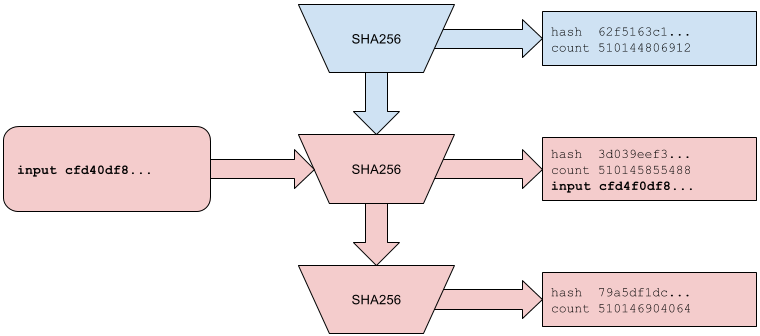
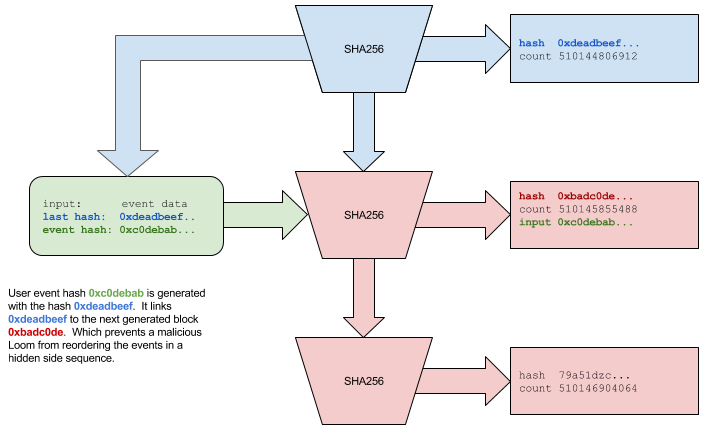
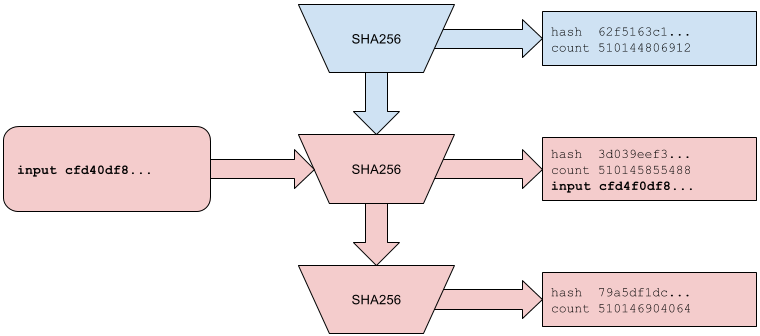
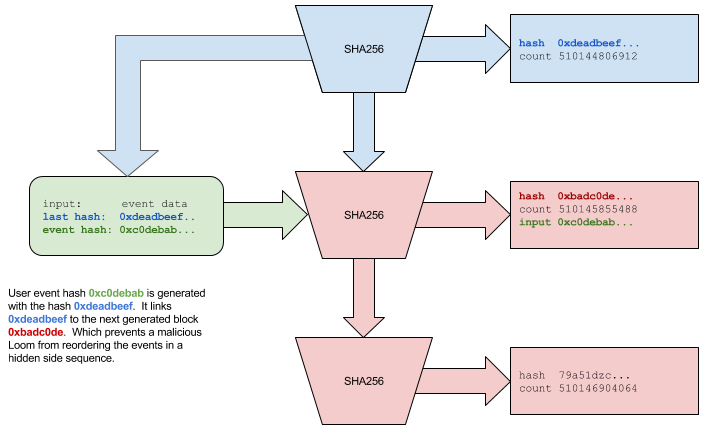
Proof of History es una funcion de retardo verificable implementada como una cadena de hash secuencial usando SHA-256. El generador PoH calcula continuamente hashes SHA-256, usando cada salida como entrada para el siguiente hash. Esto crea una cadena secuencial donde cada hash solo puede calcularse despues del anterior, estableciendo un ordenamiento temporal verificable. El requisito computacional para generar cada hash impone un retardo de tiempo minimo entre eventos.
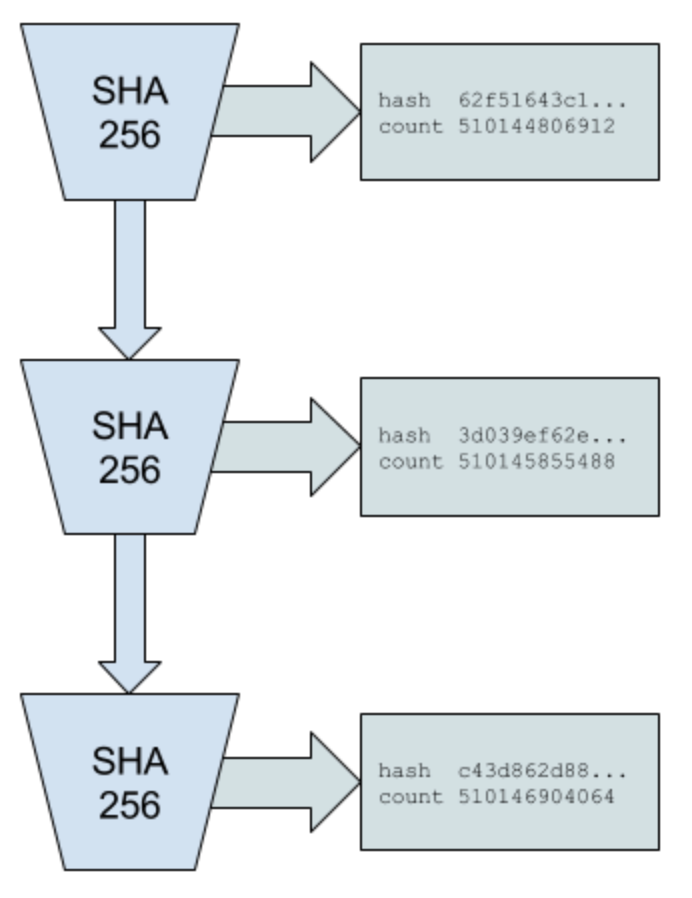
La propiedad clave de PoH es que es barato de verificar pero costoso de producir. Un verificador puede comprobar toda la secuencia de hash en paralelo dividiéndola en segmentos y verificando cada segmento de forma independiente, luego comprobando que los segmentos se conectan correctamente. Sin embargo, la generacion debe ser secuencial — no hay forma de predecir la salida de la cadena de hash sin calcular realmente cada paso intermedio. Esta asimetria entre generacion y verificacion es lo que hace practico a PoH.
Los eventos externos y los datos de transaccion se insertan en la secuencia PoH mezclándolos en la cadena de hash. Cuando llega una transaccion, su hash se combina con el estado PoH actual, creando un registro que demuestra que la transaccion existio en ese punto de la secuencia. El generador PoH registra periodicamente puntos de control, publicando el valor hash actual junto con el conteo de hashes calculados desde el ultimo punto de control. Estos puntos de control permiten a los validadores verificar eficientemente la secuencia PoH sin recalcular cada hash.
La secuencia PoH sirve como un reloj criptografico para toda la red. Debido a que la cadena de hash es secuencial y verificable, cualquier nodo puede demostrar que ha pasado una cierta cantidad de tiempo entre dos eventos simplemente mostrando los hashes que se calcularon durante ese intervalo. Esto elimina la necesidad de que los nodos confien en marcas de tiempo externas o se coordinen entre si para establecer un ordenamiento temporal, eliminando un cuello de botella fundamental en el consenso blockchain tradicional.
Proof of History
Proof of History는 SHA-256을 사용한 순차적 해시 체인으로 구현된 검증 가능한 지연 함수(VDF)이다. PoH 생성기는 각 출력을 다음 해시의 입력으로 사용하여 SHA-256 해시를 지속적으로 계산한다. 이는 각 해시가 이전 해시 이후에만 계산될 수 있는 순차적 체인을 생성하여, 검증 가능한 시간적 순서를 확립한다. 각 해시를 생성하기 위한 계산 요구 사항은 이벤트 간 최소 시간 지연을 강제한다.
PoH의 핵심 속성은 검증은 저렴하지만 생성은 비용이 많이 든다는 것이다. 검증자는 해시 시퀀스를 세그먼트로 나누어 각 세그먼트를 독립적으로 검사한 후 세그먼트가 올바르게 연결되는지 확인함으로써 전체 해시 시퀀스를 병렬로 검사할 수 있다. 그러나 생성은 반드시 순차적이어야 한다 — 모든 중간 단계를 실제로 계산하지 않고는 해시 체인의 출력을 예측할 방법이 없다. 생성과 검증 사이의 이러한 비대칭성이 PoH를 실용적으로 만드는 것이다.
외부 이벤트와 트랜잭션 데이터는 해시 체인에 혼합되어 PoH 시퀀스에 삽입된다. 트랜잭션이 도착하면, 그 해시가 현재 PoH 상태와 결합되어 해당 트랜잭션이 시퀀스의 그 시점에 존재했음을 증명하는 기록이 생성된다. PoH 생성기는 주기적으로 체크포인트를 기록하며, 마지막 체크포인트 이후 계산된 해시 수와 함께 현재 해시 값을 게시한다. 이러한 체크포인트는 검증자가 모든 해시를 재계산하지 않고도 PoH 시퀀스를 효율적으로 검증할 수 있게 한다.
PoH 시퀀스는 전체 네트워크의 암호학적 시계 역할을 한다. 해시 체인은 순차적이고 검증 가능하므로, 어떤 노드든 해당 구간 동안 계산된 해시를 보여줌으로써 두 이벤트 사이에 일정량의 시간이 경과했음을 증명할 수 있다. 이는 노드가 외부 타임스탬프를 신뢰하거나 시간적 순서를 확립하기 위해 서로 조율할 필요를 제거하여, 전통적인 블록체인 합의의 근본적인 병목을 해소한다.
Proof of History Sequence
La secuencia de Proof of History es una cadena continua de hashes SHA-256 donde cada hash depende de la salida anterior. La secuencia comienza con un valor semilla inicial, que se hashea para producir la primera salida. Esta salida se convierte en la entrada para el siguiente hash, y el proceso se repite indefinidamente. El generador tambien mantiene un contador que rastrea el numero total de hashes calculados, que sirve como la "marca de tiempo" PoH para eventos en el libro mayor.
Cuando se necesita insertar datos en la secuencia (como hashes de transacciones o firmas de validadores), se combinan con el estado hash actual usando una funcion de mezcla determinista. Por ejemplo, si el estado hash actual es hash_n y queremos insertar datos D, calculamos hash_{n+1} = SHA256(hash_n || D), donde || denota concatenacion. El punto de insercion se registra junto con el valor del contador, demostrando que los datos D existian en ese punto especifico de la secuencia.
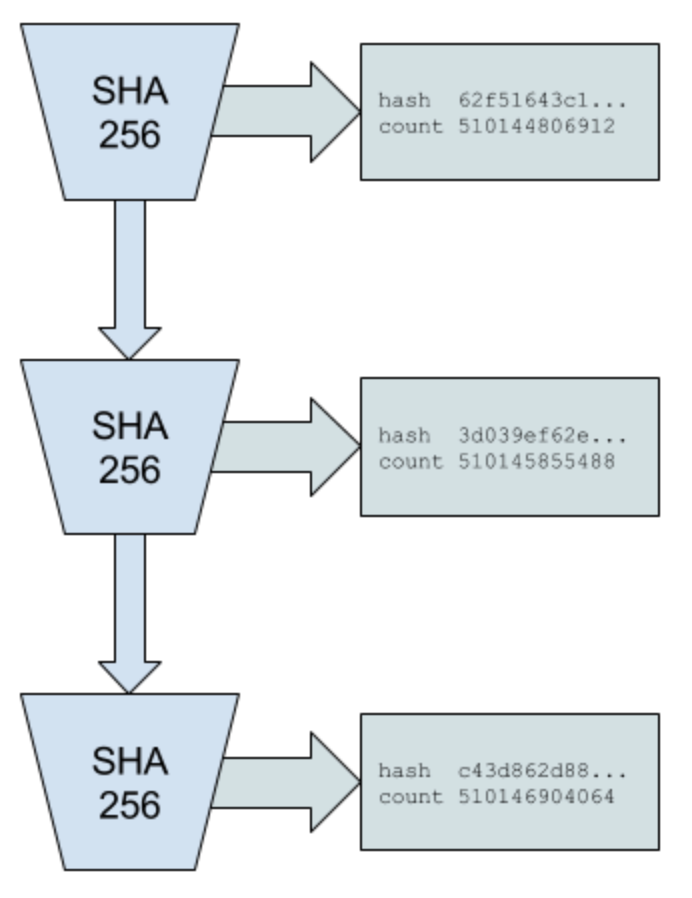
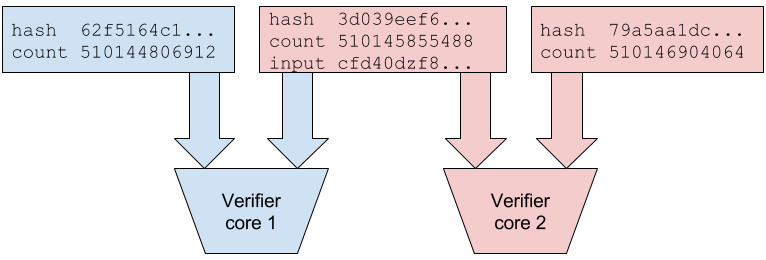
La verificacion de la secuencia PoH puede paralelizarse dividiendo la cadena en segmentos. Por ejemplo, un validador podria recibir puntos de control PoH cada 10,000 hashes. Para verificar la secuencia entre puntos de control, el validador puede dividir los 10,000 hashes en 100 segmentos de 100 hashes cada uno, verificar cada segmento independientemente en paralelo, y luego verificar que los segmentos se conectan correctamente. Esto permite que la verificacion escale horizontalmente con el numero de nucleos de CPU disponibles.
La secuencia tambien soporta pruebas eficientes de que dos eventos ocurrieron en un orden especifico. Dadas dos inserciones de datos en valores de contador n y m donde n m, cualquiera puede verificar que el evento en n ocurrio antes del evento en m comprobando la cadena de hash entre esos puntos. Esta propiedad permite a Solana crear un registro historico verificable de todos los eventos en la red sin requerir que los nodos esten en linea continuamente o confien en fuentes de tiempo externas.
Proof of History Sequence
Proof of History 시퀀스는 각 해시가 이전 출력에 의존하는 연속적인 SHA-256 해시 체인이다. 시퀀스는 초기 시드 값에서 시작하며, 이 값을 해싱하여 첫 번째 출력을 생성한다. 이 출력은 다음 해시의 입력이 되고, 이 과정이 무한히 반복된다. 생성기는 또한 계산된 총 해시 수를 추적하는 카운터를 유지하며, 이는 원장에서 이벤트의 PoH "타임스탬프" 역할을 한다.
데이터를 시퀀스에 삽입해야 할 때(트랜잭션 해시나 검증자 서명 등), 결정론적 혼합 함수를 사용하여 현재 해시 상태와 결합된다. 예를 들어, 현재 해시 상태가 hash_n이고 데이터 D를 삽입하려면, hash_{n+1} = SHA256(hash_n || D)를 계산한다. 여기서 ||는 연결(concatenation)을 나타낸다. 삽입 지점은 카운터 값과 함께 기록되어, 데이터 D가 시퀀스의 해당 특정 지점에 존재했음을 증명한다.
PoH 시퀀스의 검증은 체인을 세그먼트로 분할하여 병렬화할 수 있다. 예를 들어, 검증자가 10,000 해시마다 PoH 체크포인트를 수신할 수 있다. 체크포인트 간 시퀀스를 검증하기 위해, 검증자는 10,000개의 해시를 각 100개씩 100개의 세그먼트로 분할하고, 각 세그먼트를 병렬로 독립적으로 검증한 다음, 세그먼트가 올바르게 연결되는지 확인할 수 있다. 이를 통해 검증은 사용 가능한 CPU 코어 수에 따라 수평적으로 확장될 수 있다.
시퀀스는 또한 두 이벤트가 특정 순서로 발생했음에 대한 효율적인 증명을 지원한다. n m인 카운터 값 n과 m에서의 두 데이터 삽입이 주어지면, 누구나 해당 지점 사이의 해시 체인을 확인하여 n의 이벤트가 m의 이벤트보다 먼저 발생했음을 검증할 수 있다. 이 속성은 Solana가 노드가 지속적으로 온라인 상태이거나 외부 시간 소스를 신뢰할 필요 없이 네트워크의 모든 이벤트에 대한 검증 가능한 역사적 기록을 생성할 수 있게 한다.
Timestamp
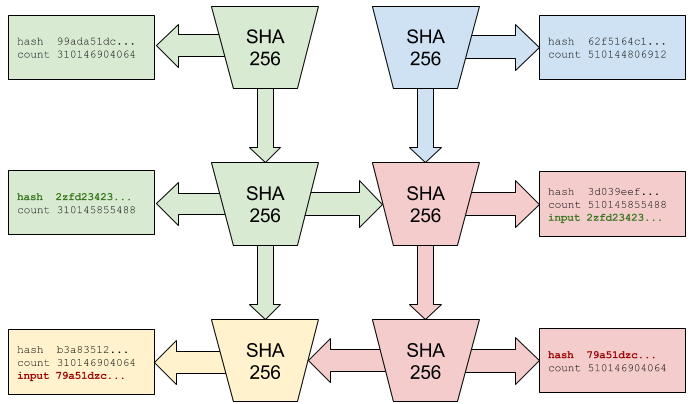
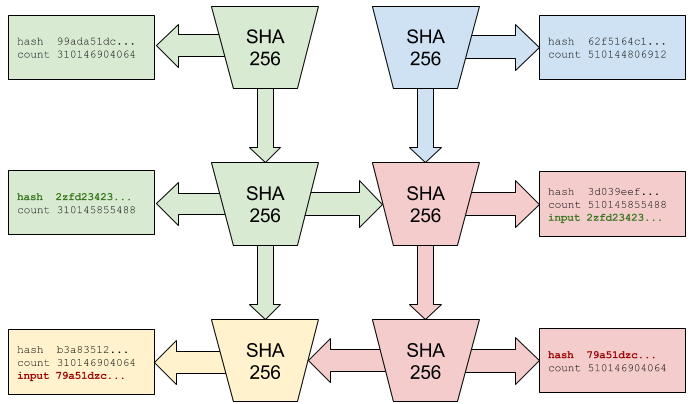
Proof of History funciona como un reloj descentralizado que asigna marcas de tiempo a eventos sin depender del tiempo de reloj de pared. Cada hash PoH representa un "tick" discreto del reloj criptografico, y el valor del contador sirve como la marca de tiempo. Debido a que la cadena de hash es secuencial y verificable, estas marcas de tiempo son sin confianza — cualquier observador puede verificar que una marca de tiempo es legitima comprobando la cadena de hash.
En Solana, cada validador puede generar su propia secuencia PoH cuando actua como lider. Cuando los validadores rotan el liderazgo, sincronizan sus secuencias PoH usando el ultimo punto de control confirmado del lider anterior. Esto asegura la continuidad del registro temporal incluso cuando diferentes validadores se turnan para producir bloques. La red establece una linea temporal canonica al alcanzar consenso sobre que secuencias PoH aceptar como parte del libro mayor oficial.
El sistema maneja la deriva del reloj y la varianza en el rendimiento del hardware a traves de una combinacion de rotacion de lideres y consenso. Si un lider malicioso o defectuoso intenta generar marcas de tiempo PoH a una tasa incorrecta (demasiado rapida o demasiado lenta), los validadores pueden detectar esto comparando la tasa de ticks PoH con sus propios generadores PoH locales. Las desviaciones significativas de la tasa esperada indican un problema, y los validadores pueden rechazar bloques de lideres cuyas secuencias PoH divergen demasiado de la mediana de la red.
Este mecanismo de marcas de tiempo resuelve uno de los problemas fundamentales en sistemas distribuidos: establecer una nocion comun de tiempo sin una autoridad central de confianza. Al usar PoH como un reloj descentralizado, Solana permite que los validadores procesen transacciones en paralelo mientras mantienen un ordenamiento globalmente consistente. Las marcas de tiempo tambien proporcionan una base para caracteristicas basadas en tiempo como la expiracion de transacciones, operaciones programadas y medicion de rendimiento.
Timestamp
Proof of History는 벽시계 시간에 의존하지 않고 이벤트에 타임스탬프를 할당하는 탈중앙화된 시계로 기능한다. 각 PoH 해시는 암호학적 시계의 개별 "틱"을 나타내며, 카운터 값이 타임스탬프 역할을 한다. 해시 체인은 순차적이고 검증 가능하므로, 이러한 타임스탬프는 신뢰가 필요 없다 — 어떤 관찰자든 해시 체인을 확인하여 타임스탬프가 정당한지 검증할 수 있다.
Solana에서 각 검증자는 리더로 활동할 때 자체 PoH 시퀀스를 생성할 수 있다. 검증자가 리더십을 교체할 때, 이전 리더의 마지막 확인된 체크포인트를 사용하여 PoH 시퀀스를 동기화한다. 이는 서로 다른 검증자가 교대로 블록을 생성하더라도 시간 기록의 연속성을 보장한다. 네트워크는 공식 원장의 일부로 수용할 PoH 시퀀스에 대해 합의에 도달하여 정규 타임라인을 확립한다.
시스템은 리더 교체와 합의의 조합을 통해 클록 드리프트와 하드웨어 성능의 편차를 처리한다. 악의적이거나 결함이 있는 리더가 잘못된 속도(너무 빠르거나 너무 느리게)로 PoH 타임스탬프를 생성하려고 시도하면, 검증자는 자체 로컬 PoH 생성기와 비교하여 PoH 틱 속도를 비교함으로써 이를 감지할 수 있다. 예상 속도에서의 상당한 편차는 문제를 나타내며, 검증자는 PoH 시퀀스가 네트워크 중앙값에서 너무 벗어난 리더의 블록을 거부할 수 있다.
이 타임스탬핑 메커니즘은 분산 시스템의 근본적인 문제 중 하나인 신뢰할 수 있는 중앙 기관 없이 공통의 시간 개념을 확립하는 문제를 해결한다. PoH를 탈중앙화된 시계로 사용함으로써, Solana는 검증자가 전역적으로 일관된 순서를 유지하면서 트랜잭션을 병렬로 처리할 수 있게 한다. 타임스탬프는 또한 트랜잭션 만료, 예약된 작업, 성능 측정과 같은 시간 기반 기능의 기초를 제공한다.
Proof of Stake Consensus
El mecanismo de consenso de Solana, llamado Tower BFT, es un algoritmo Proof of Stake disenado especificamente para aprovechar las propiedades temporales de Proof of History. Los validadores apuestan tokens SOL para participar en el consenso y ganar recompensas por validar correctamente los bloques. El sistema de votacion ponderado por participacion asegura que los validadores con mas interes economico en la red tengan proporcionalmente mas influencia sobre las decisiones de consenso.
La innovacion central en Tower BFT es el uso de periodos de bloqueo que aumentan exponencialmente con cada voto consecutivo. Cuando un validador vota sobre un hash PoH, se compromete con esa bifurcacion del libro mayor durante un cierto numero de ticks PoH. Si votan en el siguiente bloque de esa bifurcacion, el periodo de bloqueo se duplica. Esto crea un fuerte incentivo economico para que los validadores continuen votando en la misma bifurcacion, ya que cambiar de bifurcacion requeriria esperar a que expiren los bloqueos anteriores.
Especificamente, si un validador vota en un bloque en la marca de tiempo PoH t, no puede votar en una bifurcacion conflictiva hasta que hayan pasado 2^n ticks, donde n es el numero de votos consecutivos que ha realizado en la bifurcacion actual. Este mecanismo de bloqueo exponencial hace que el sistema sea seguro contra ataques de largo alcance mientras permite una finalidad rapida. Una vez que una supermayoria de participacion ha votado en un bloque con suficiente profundidad, ese bloque esta efectivamente finalizado.
Las condiciones de penalizacion imponen un comportamiento honesto. Si un validador vota en dos bifurcaciones conflictivas durante un periodo en el que deberia estar bloqueado, es penalizado — sus tokens apostados son parcialmente destruidos y es removido del conjunto de validadores. Esto hace economicamente irracional intentar la equivocacion u otro comportamiento bizantino. La combinacion de las marcas de tiempo verificables de PoH y los bloqueos exponenciales de Tower BFT crea un mecanismo de consenso que es rapido y seguro, logrando finalidad en segundos mientras mantiene las garantias de seguridad de los sistemas BFT tradicionales.
Proof of Stake Consensus
Tower BFT라 불리는 Solana의 합의 메커니즘은 Proof of History의 시간적 속성을 활용하도록 특별히 설계된 Proof of Stake 알고리즘이다. 검증자는 SOL 토큰을 스테이킹하여 합의에 참여하고 블록을 올바르게 검증하면 보상을 받는다. 스테이크 가중 투표 시스템은 네트워크에 더 많은 경제적 이해관계를 가진 검증자가 합의 결정에 비례적으로 더 큰 영향력을 갖도록 보장한다.
Tower BFT의 핵심 혁신은 연속 투표마다 기하급수적으로 증가하는 잠금 기간의 사용이다. 검증자가 PoH 해시에 투표하면, 일정 수의 PoH 틱 동안 해당 원장의 포크에 대해 커밋한다. 해당 포크의 다음 블록에 투표하면 잠금 기간이 두 배가 된다. 이는 검증자가 동일한 포크에 계속 투표하도록 강력한 경제적 인센티브를 만드는데, 포크를 전환하려면 이전 잠금이 만료될 때까지 기다려야 하기 때문이다.
구체적으로, 검증자가 PoH 타임스탬프 t에서 블록에 투표하면, 2^n 틱이 경과할 때까지 충돌하는 포크에 투표할 수 없다. 여기서 n은 현재 포크에서 연속으로 한 투표 수이다. 이 기하급수적 잠금 메커니즘은 빠른 최종성을 허용하면서 장거리 공격에 대한 시스템의 보안을 유지한다. 충분한 깊이로 블록에 대해 스테이크의 초과반수가 투표하면, 해당 블록은 사실상 확정된다.
슬래싱 조건은 정직한 행동을 강제한다. 검증자가 잠금 상태여야 하는 기간 동안 두 개의 충돌하는 포크에 투표하면, 슬래싱된다 — 스테이킹된 토큰이 부분적으로 소각되고 검증자 세트에서 제거된다. 이는 이중 투표나 기타 비잔틴 행동을 시도하는 것을 경제적으로 비합리적으로 만든다. PoH의 검증 가능한 타임스탬프와 Tower BFT의 기하급수적 잠금의 조합은 빠르고 안전한 합의 메커니즘을 만들어, 전통적인 BFT 시스템의 보안 보장을 유지하면서 수 초 만에 최종성을 달성한다.
Streaming Proof of Replication
Proof of Replication (PoRep) es un mecanismo que permite a los validadores demostrar que estan almacenando los datos del libro mayor sin revelar los datos mismos ni requerir una computacion intensiva. Solana implementa una version de streaming de PoRep donde los validadores demuestran continuamente que estan replicando el estado de la blockchain. Esto es esencial para la seguridad de la red, ya que asegura que los datos del libro mayor esten distribuidos adecuadamente entre los validadores y no concentrados en unas pocas ubicaciones.
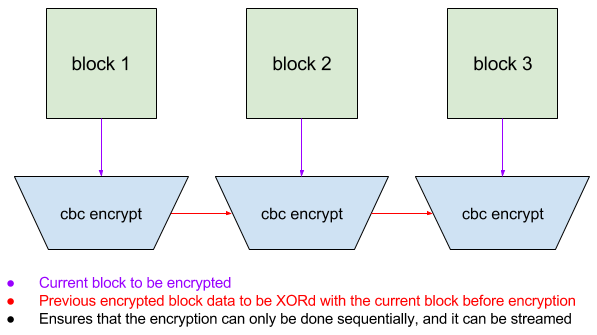
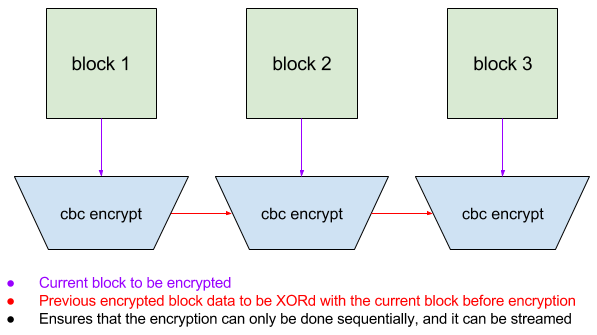
El mecanismo PoRep funciona haciendo que los validadores cifren segmentos del libro mayor usando encriptacion en modo CBC (Cipher Block Chaining) con una clave especifica del validador derivada de su identidad. El proceso de encriptacion es tal que cada bloque cifrado depende del bloque anterior, creando una cadena que es unica para cada validador. Esto evita que los validadores simplemente copien datos cifrados entre si — cada validador debe almacenar y procesar los datos originales del libro mayor para generar su version cifrada unica.
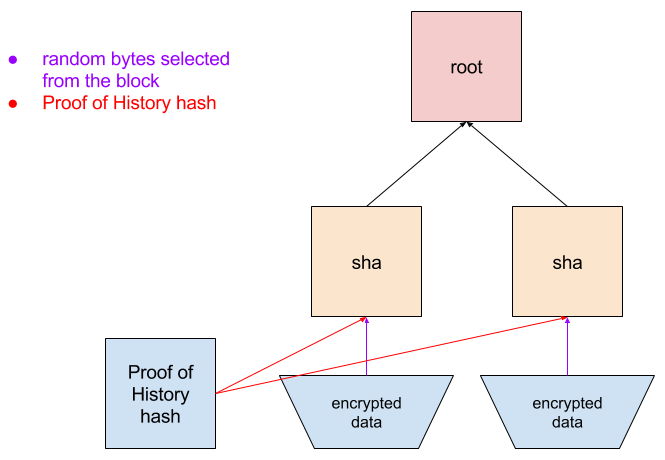
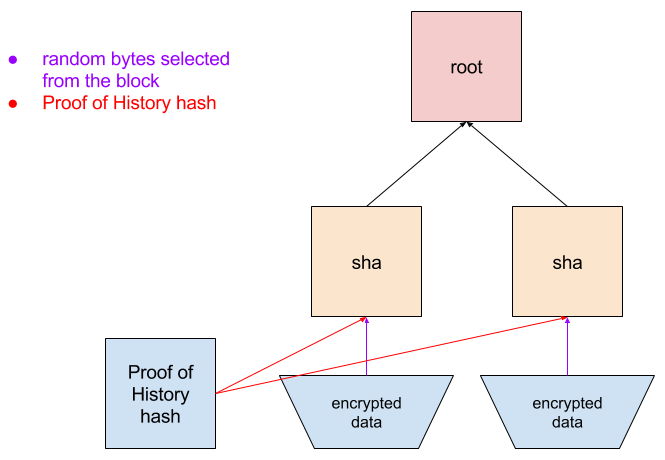
Periodicamente, la red emite desafios a los validadores solicitando que proporcionen bloques cifrados especificos. Debido a que la encriptacion esta encadenada, el validador debe haber almacenado todos los bloques anteriores para generar la respuesta correcta. El validador envia su bloque cifrado junto con una prueba de Merkle que muestra su posicion en su libro mayor cifrado. La red puede verificar esta prueba rapidamente sin necesidad de descifrar o re-cifrar los datos.
Este enfoque de streaming para PoRep tiene una baja sobrecarga comparado con los sistemas tradicionales de prueba de almacenamiento. Los validadores pueden cifrar datos a medida que llegan y responder a los desafios con una latencia minima. El sistema tambien permite la recuperacion en caso de perdida de datos — si un validador pierde parte del libro mayor, puede volver a descargarlo de otros validadores y re-cifrarlo. La combinacion de PoRep con marcas de tiempo PoH crea un sistema de responsabilidad completo donde la red puede verificar tanto cuando se crearon los datos como que estan almacenados correctamente en toda la red de validadores.
Streaming Proof of Replication
Proof of Replication(PoRep)은 검증자가 데이터 자체를 공개하거나 집약적인 계산을 요구하지 않고도 원장 데이터를 저장하고 있음을 증명할 수 있는 메커니즘이다. Solana는 검증자가 블록체인 상태를 복제하고 있음을 지속적으로 입증하는 스트리밍 버전의 PoRep을 구현한다. 이는 원장 데이터가 소수의 위치에 집중되지 않고 검증자 전체에 적절히 분산되도록 보장하므로 네트워크 보안에 필수적이다.
PoRep 메커니즘은 검증자가 자신의 아이덴티티에서 파생된 검증자 고유 키를 사용하여 CBC(Cipher Block Chaining) 모드 암호화로 원장의 세그먼트를 암호화하는 방식으로 작동한다. 암호화 프로세스는 각 암호화된 블록이 이전 블록에 의존하도록 되어 있어, 각 검증자에 고유한 체인을 생성한다. 이는 검증자가 단순히 서로의 암호화된 데이터를 복사하는 것을 방지한다 — 각 검증자는 고유한 암호화 버전을 생성하기 위해 원본 원장 데이터를 저장하고 처리해야 한다.
주기적으로, 네트워크는 검증자에게 특정 암호화된 블록을 제공하도록 요구하는 챌린지를 발행한다. 암호화가 체인으로 연결되어 있으므로, 검증자는 올바른 응답을 생성하기 위해 모든 선행 블록을 저장하고 있어야 한다. 검증자는 암호화된 원장에서의 위치를 보여주는 Merkle 증명과 함께 암호화된 블록을 제출한다. 네트워크는 데이터를 복호화하거나 재암호화할 필요 없이 이 증명을 신속하게 검증할 수 있다.
이 스트리밍 방식의 PoRep은 전통적인 저장 증명 시스템에 비해 오버헤드가 낮다. 검증자는 데이터가 도착하는 대로 암호화하고 최소한의 지연으로 챌린지에 응답할 수 있다. 시스템은 또한 데이터 손실 시 복구를 가능하게 한다 — 검증자가 원장의 일부를 잃으면, 다른 검증자로부터 다시 다운로드하여 재암호화할 수 있다. PoRep과 PoH 타임스탬프의 조합은 네트워크가 데이터가 생성된 시기와 검증자 네트워크 전체에 적절히 저장되어 있는지를 모두 검증할 수 있는 완전한 책임 시스템을 만든다.
System Architecture
La arquitectura del sistema de Solana esta disenada como un pipeline donde diferentes etapas del procesamiento de transacciones ocurren en paralelo. La Transaction Processing Unit (TPU) es el componente central responsable de manejar las transacciones entrantes. La TPU consta de varias etapas: fetch (recoleccion de transacciones), verificacion de firmas, banking (ejecucion de transacciones) y write (escritura en almacenamiento). Cada etapa opera en paralelo sobre diferentes transacciones, similar al pipeline de una CPU.
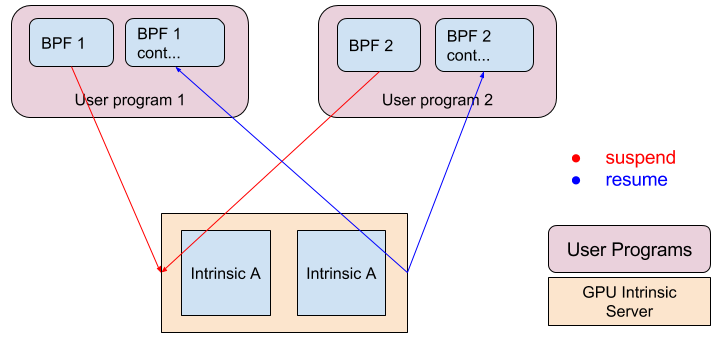
La verificacion de firmas se acelera usando GPUs, que son altamente eficientes en las operaciones de criptografia de curva eliptica necesarias para verificar firmas de transacciones. Al descargar esta tarea computacionalmente intensiva a las GPUs, Solana puede verificar firmas a tasas que exceden 900,000 por segundo en hardware comercial. Esta verificacion de firmas en paralelo evita que la validacion criptografica se convierta en un cuello de botella incluso a tasas de transaccion muy altas.
El runtime Sealevel es el motor de ejecucion de contratos inteligentes en paralelo de Solana. A diferencia de las blockchains tradicionales que ejecutan transacciones secuencialmente, Sealevel analiza las transacciones para identificar que cuentas acceden y ejecuta transacciones no conflictivas en paralelo a traves de multiples nucleos de CPU. Las transacciones que acceden a las mismas cuentas se ejecutan secuencialmente para mantener la consistencia, pero las transacciones que acceden a diferentes cuentas pueden ejecutarse simultaneamente. Este paralelismo es posible porque PoH establece un ordenamiento global — los validadores pueden ejecutar transacciones en cualquier orden siempre que las apliquen al estado en la secuencia especificada por PoH.
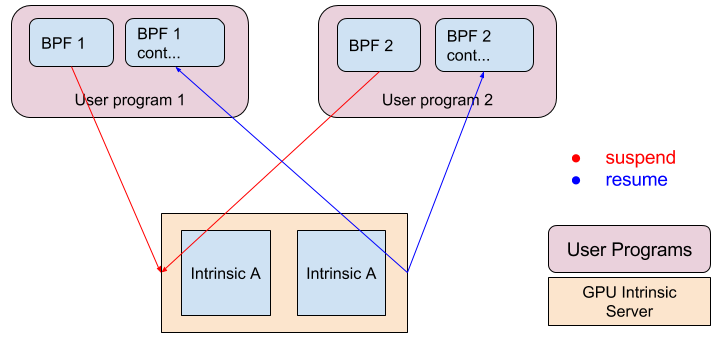
La arquitectura tambien incluye componentes optimizados para la propagacion y almacenamiento de bloques. El protocolo de propagacion de bloques Turbine usa codificacion de borrado para dividir bloques en paquetes mas pequenos que se distribuyen a traves de la red en una estructura de arbol, minimizando los requisitos de ancho de banda. La red de Archivers proporciona almacenamiento descentralizado para datos historicos del libro mayor, usando PoRep para asegurar la disponibilidad de datos. Juntos, estos componentes crean un sistema que puede procesar cientos de miles de transacciones por segundo mientras mantiene las propiedades de descentralizacion y seguridad de una blockchain.
System Architecture
Solana의 시스템 아키텍처는 트랜잭션 처리의 여러 단계가 병렬로 진행되는 파이프라인으로 설계되었다. Transaction Processing Unit(TPU)은 수신되는 트랜잭션을 처리하는 핵심 구성 요소이다. TPU는 여러 단계로 구성된다: 페치(트랜잭션 수집), 서명 검증, 뱅킹(트랜잭션 실행), 쓰기(스토리지에 커밋). 각 단계는 CPU 파이프라이닝과 유사하게 서로 다른 트랜잭션에 대해 병렬로 작동한다.
서명 검증은 트랜잭션 서명 검증에 필요한 타원 곡선 암호화 연산에 매우 효율적인 GPU를 사용하여 가속된다. 이 계산 집약적인 작업을 GPU에 오프로딩함으로써, Solana는 범용 하드웨어에서 초당 900,000건 이상의 속도로 서명을 검증할 수 있다. 이 병렬 서명 검증은 매우 높은 트랜잭션 속도에서도 암호화 검증이 병목이 되는 것을 방지한다.
Sealevel 런타임은 Solana의 병렬 스마트 컨트랙트 실행 엔진이다. 트랜잭션을 순차적으로 실행하는 기존 블록체인과 달리, Sealevel은 트랜잭션이 접근하는 계정을 분석하여 충돌하지 않는 트랜잭션을 여러 CPU 코어에 걸쳐 병렬로 실행한다. 동일한 계정에 접근하는 트랜잭션은 일관성을 유지하기 위해 순차적으로 실행되지만, 서로 다른 계정에 접근하는 트랜잭션은 동시에 실행될 수 있다. 이 병렬성은 PoH가 전역 순서를 확립하기 때문에 가능하다 — 검증자는 PoH가 지정한 시퀀스로 상태에 적용하기만 하면 어떤 순서로든 트랜잭션을 실행할 수 있다.
아키텍처에는 블록 전파와 스토리지를 위한 최적화된 구성 요소도 포함된다. turbine 블록 전파 프로토콜은 이레이저 코딩을 사용하여 블록을 더 작은 패킷으로 나누어 트리 구조로 네트워크에 분산하여 대역폭 요구 사항을 최소화한다. Archivers 네트워크는 PoRep을 사용하여 데이터 가용성을 보장하면서 역사적 원장 데이터에 대한 탈중앙화된 스토리지를 제공한다. 이러한 구성 요소들이 함께 블록체인의 탈중앙화와 보안 속성을 유지하면서 초당 수십만 건의 트랜잭션을 처리할 수 있는 시스템을 만든다.
Performance
La arquitectura de Solana esta disenada para alcanzar niveles de rendimiento que escalan con las mejoras de hardware, siguiendo la Ley de Moore. En una conexion de red estandar de 1 gigabit, el rendimiento maximo teorico es aproximadamente 710,000 transacciones por segundo, asumiendo 176 bytes por transaccion (incluyendo firmas y metadatos). Este calculo se basa en el ancho de banda de red como el cuello de botella principal, con los cuellos de botella computacionales eliminados a traves de la paralelizacion.
La verificacion de firmas, a menudo un factor limitante en el rendimiento de blockchain, se acelera usando paralelizacion GPU. Una sola GPU puede verificar mas de 900,000 firmas ed25519 por segundo, lo que excede el limite de rendimiento de la red. Esto significa que la verificacion de firmas no restringe el rendimiento del sistema — el cuello de botella se desplaza al ancho de banda de red y la ejecucion de transacciones. Para transacciones simples que solo transfieren valor sin logica compleja de contratos inteligentes, la etapa de banking puede procesar transacciones a tasas que igualan la tasa de entrada de la red.
El generador PoH funciona en un nucleo de CPU dedicado, produciendo aproximadamente 4,000 hashes por milisegundo en un procesador de 4GHz. A esta tasa, la secuencia PoH proporciona marcas de tiempo con una granularidad de 0.25 microsegundos, lo cual es suficiente para ordenar millones de transacciones por segundo. La naturaleza secuencial de la generacion PoH significa que este componente no puede paralelizarse, pero el rendimiento es lo suficientemente alto como para no limitar el rendimiento general del sistema.
A medida que el hardware mejora, el rendimiento de Solana escala en consecuencia. Redes mas rapidas, GPUs mas potentes y CPUs mejoradas contribuyen a tasas de transaccion mas altas. El sistema esta disenado para aprovechar estas mejoras sin requerir cambios de protocolo. Este enfoque de escalabilidad contrasta con blockchains que estan fundamentalmente limitadas por mecanismos de consenso secuenciales, permitiendo a Solana alcanzar niveles de rendimiento previamente considerados imposibles en un sistema descentralizado mientras mantiene garantias de seguridad y descentralizacion.
Performance
Solana의 아키텍처는 무어의 법칙을 따르며 하드웨어 개선에 맞춰 확장되는 성능 수준을 달성하도록 설계되었다. 표준 1기가비트 네트워크 연결에서 이론적 최대 처리량은 트랜잭션당 176바이트(서명 및 메타데이터 포함)를 가정할 때 초당 약 710,000건의 트랜잭션이다. 이 계산은 네트워크 대역폭을 주요 병목으로 하며, 병렬화를 통해 계산 병목은 제거된 것을 기반으로 한다.
블록체인 성능에서 종종 제한 요인이 되는 서명 검증은 GPU 병렬화를 사용하여 가속된다. 단일 GPU는 초당 900,000건 이상의 ed25519 서명을 검증할 수 있으며, 이는 네트워크 처리량 한도를 초과한다. 이는 서명 검증이 시스템 성능을 제약하지 않는다는 것을 의미하며 — 병목은 네트워크 대역폭과 트랜잭션 실행으로 이동한다. 복잡한 스마트 컨트랙트 로직 없이 단순히 가치를 이전하는 단순 트랜잭션의 경우, 뱅킹 단계는 네트워크 입력 속도에 맞는 속도로 트랜잭션을 처리할 수 있다.
PoH 생성기는 전용 CPU 코어에서 실행되며, 4GHz 프로세서에서 밀리초당 약 4,000개의 해시를 생성한다. 이 속도에서 PoH 시퀀스는 0.25마이크로초의 세분성으로 타임스탬프를 제공하며, 이는 초당 수백만 건의 트랜잭션을 정렬하는 데 충분하다. PoH 생성의 순차적 특성은 이 구성 요소가 병렬화될 수 없음을 의미하지만, 처리량이 충분히 높아 전체 시스템 성능을 제한하지 않는다.
하드웨어가 개선됨에 따라 Solana의 처리량은 그에 맞게 확장된다. 더 빠른 네트워크, 더 강력한 GPU, 개선된 CPU 모두가 더 높은 트랜잭션 속도에 기여한다. 시스템은 프로토콜 변경 없이 이러한 개선 사항을 활용하도록 설계되었다. 이 확장성 접근 방식은 순차적 합의 메커니즘에 의해 근본적으로 제한되는 블록체인과 대조되며, Solana가 보안과 탈중앙화 보장을 유지하면서 분산 시스템에서 이전에 불가능하다고 여겨졌던 성능 수준을 달성할 수 있게 한다.
Conclusion
Proof of History representa un avance fundamental en la arquitectura blockchain al resolver el problema de sincronizacion que ha limitado la escalabilidad de los libros mayores distribuidos. Al crear un reloj criptografico verificable, PoH permite a los validadores establecer un ordenamiento temporal de eventos sin la extensa sobrecarga de comunicacion requerida por los mecanismos de consenso tradicionales. Esta innovacion elimina un cuello de botella critico y permite que el procesamiento de transacciones se paralelice a traves de la red.
La integracion de PoH con componentes de sistema optimizados — verificacion de firmas acelerada por GPU, ejecucion de transacciones en paralelo a traves de Sealevel y protocolos de propagacion de bloques eficientes — crea una blockchain que puede procesar cientos de miles de transacciones por segundo en hardware comercial. Mas importante aun, la arquitectura esta disenada para escalar con las mejoras de hardware, lo que significa que el rendimiento continuara aumentando a medida que los procesadores se vuelvan mas rapidos y las redes mas capaces.
El diseno de Solana demuestra que el alto rendimiento y la descentralizacion no son mutuamente excluyentes. Al aprovechar PoH como base para el consenso y la coordinacion del sistema, la red alcanza niveles de rendimiento comparables a bases de datos centralizadas mientras mantiene las propiedades de seguridad y resistencia a la censura de una blockchain descentralizada. El mecanismo de consenso Tower BFT ponderado por participacion asegura que la red permanezca segura contra actores bizantinos mientras logra una finalidad rapida.
La implementacion de esta arquitectura proporciona un camino practico hacia adelante para que la tecnologia blockchain escale a la adopcion global. Las aplicaciones que requieren un alto rendimiento de transacciones — como intercambios descentralizados, plataformas de juegos y sistemas financieros — ahora pueden construirse sobre una infraestructura verdaderamente descentralizada sin comprometer el rendimiento. Proof of History abre la puerta a una nueva generacion de aplicaciones blockchain que anteriormente eran inviables debido a las limitaciones de escalabilidad.
Conclusion
Proof of History는 분산 원장의 확장성을 제한해 온 타이밍 문제를 해결함으로써 블록체인 아키텍처의 근본적인 돌파구를 나타낸다. 검증 가능한 암호학적 시계를 만듦으로써, PoH는 검증자가 전통적인 합의 메커니즘이 요구하는 광범위한 통신 오버헤드 없이 이벤트의 시간적 순서를 확립할 수 있게 한다. 이 혁신은 핵심적인 병목을 제거하고 네트워크 전체에서 트랜잭션 처리를 병렬화할 수 있게 한다.
PoH와 최적화된 시스템 구성 요소 — GPU 가속 서명 검증, Sealevel을 통한 병렬 트랜잭션 실행, 효율적인 블록 전파 프로토콜 — 의 통합은 범용 하드웨어에서 초당 수십만 건의 트랜잭션을 처리할 수 있는 블록체인을 만든다. 더 중요한 것은, 이 아키텍처가 하드웨어 개선에 맞춰 확장되도록 설계되어 있어 프로세서가 빨라지고 네트워크가 더 강력해짐에 따라 성능이 계속 향상된다는 것이다.
Solana의 설계는 고성능과 탈중앙화가 상호 배타적이지 않음을 보여준다. PoH를 합의와 시스템 조율의 기반으로 활용함으로써, 네트워크는 탈중앙화된 블록체인의 보안과 검열 저항 속성을 유지하면서 중앙화된 데이터베이스에 견줄 수 있는 처리량 수준을 달성한다. 스테이크 가중 Tower BFT 합의 메커니즘은 빠른 최종성을 달성하면서 비잔틴 행위자에 대한 네트워크 보안을 보장한다.
이 아키텍처의 구현은 블록체인 기술이 글로벌 채택으로 확장하기 위한 실질적인 경로를 제공한다. 높은 트랜잭션 처리량을 요구하는 애플리케이션 — 탈중앙화 거래소, 게임 플랫폼, 금융 시스템 — 은 이제 성능을 타협하지 않으면서 진정으로 탈중앙화된 인프라 위에 구축될 수 있다. Proof of History는 이전에 확장성 제약으로 인해 실현 불가능했던 새로운 세대의 블록체인 애플리케이션의 문을 연다.




