
Avalanche:一系列新的共识协议
Abstrak
Avalanche Peron 30/06/2020 Kevin Sekniqi, Daniel Laine, Stephen Buttolph, dan Emin G¨un Sirer Abstrak. Makalah ini memberikan gambaran arsitektur rilis pertama platform Avalanche, dengan nama kode Avalanche Borealis. Untuk detail tentang perekonomian token asli, berlabel $AVAX, kami 5 membimbing pembaca ke makalah dinamika token yang menyertainya [2]. Pengungkapan: Informasi yang diuraikan dalam makalah ini bersifat awal dan dapat berubah sewaktu-waktu. Selain itu, makalah ini mungkin berisi “pernyataan berwawasan ke depan.”1 Komit Git: 7497e4a4ba0a1ea2dc2a111bc6deefbf3023708e 1 Pendahuluan 10 Makalah ini memberikan gambaran arsitektur platform Avalanche. Fokus utamanya ada pada tiga kunci tersebut pembeda platform: mesin, model arsitektur, dan mekanisme tata kelola. 1.1 Avalanche Tujuan dan Prinsip Avalanche adalah platform blockchain yang berkinerja tinggi, dapat diskalakan, dapat disesuaikan, dan aman. Ini menargetkan tiga kasus penggunaan yang luas: 15 – Membangun blockchain khusus aplikasi, mencakup izin (pribadi) dan tanpa izin (publik) penerapan. – Membangun dan meluncurkan aplikasi yang sangat skalabel dan terdesentralisasi (Dapps). – Membangun aset digital yang kompleks secara sewenang-wenang dengan aturan khusus, perjanjian, dan pengendara (aset pintar). 1 Pernyataan berwawasan ke depan umumnya berhubungan dengan kejadian di masa depan atau kinerja kami di masa depan. Ini termasuk, namun tidak terbatas pada, proyeksi kinerja Avalanche; perkembangan bisnis dan proyek yang diharapkan; eksekusi mengenai visi dan strategi pertumbuhannya; dan penyelesaian proyek yang sedang berjalan, dalam pengembangan atau sebaliknya sedang dipertimbangkan. Pernyataan berwawasan ke depan mewakili keyakinan dan asumsi manajemen kami hanya pada tanggal presentasi ini. Pernyataan-pernyataan ini bukan merupakan jaminan kinerja di masa depan dan tidak semestinya ketergantungan tidak boleh ditempatkan pada mereka. Pernyataan-pernyataan berwawasan ke depan tersebut tentu saja melibatkan hal-hal yang diketahui dan tidak diketahui risiko, yang dapat menyebabkan kinerja aktual dan hasil pada periode mendatang berbeda secara material dari proyeksi tersurat maupun tersirat di sini. Avalanche tidak berkewajiban memperbarui pernyataan berwawasan ke depan. Meskipun pernyataan berwawasan ke depan adalah prediksi terbaik kami pada saat dibuat, tidak ada jaminan bahwa hal tersebut akan terjadi akan terbukti akurat, karena hasil aktual dan kejadian di masa depan dapat berbeda secara signifikan. Pembaca diperingatkan untuk tidak melakukannya untuk menempatkan ketergantungan yang tidak semestinya pada pernyataan berwawasan ke depan.
摘要
Avalanche 平台 2020/06/30 凯文·塞克尼奇、丹尼尔·莱恩、斯蒂芬·布托夫和艾敏·古恩·西雷尔 摘要。本文提供了 Avalanche 平台第一个版本的架构概述, 代号 Avalanche Borealis。有关本地 token(标记为 $AVAX)的经济学详细信息,我们 5 引导读者阅读随附的 token 动态论文 [2]。 披露:本文中描述的信息是初步的,可能随时更改。 此外,本文可能包含“前瞻性陈述”。1 Git 提交:7497e4a4ba0a1ea2dc2a111bc6deefbf3023708e 1 简介 10 本文提供了 Avalanche 平台的架构概述。重点关注三个关键 该平台的区别在于:引擎、架构模型和治理机制。 1.1 Avalanche 目标和原则 Avalanche 是一个高性能、可扩展、可定制且安全的 blockchain 平台。它的目标是三个 广泛的用例: 15 – 构建特定于应用程序的 blockchains,跨越许可(私有)和无需许可(公共) 部署。 – 构建和启动高度可扩展和去中心化的应用程序(Dapps)。 – 使用自定义规则、契约和附加条款构建任意复杂的数字资产(智能资产)。 1 前瞻性陈述通常与未来事件或我们未来的业绩有关。这包括但不包括 仅限于 Avalanche 的预计表现;其业务和项目的预期发展;执行 其愿景和增长战略;以及目前正在进行、开发或完成的项目 否则正在考虑中。前瞻性陈述代表我们管理层的信念和假设 仅截至本演示文稿发布之日。这些陈述不是对未来业绩和不当行为的保证 不应依赖他们。此类前瞻性陈述必然涉及已知和未知 风险,可能导致未来期间的实际业绩和结果与任何预测存在重大差异 此处明示或暗示。 Avalanche 不承担更新前瞻性陈述的义务。虽然 前瞻性陈述是我们做出时的最佳预测,不能保证它们是正确的 将被证明是准确的,因为实际结果和未来事件可能存在重大差异。请读者注意不要 过度依赖前瞻性陈述。
Perkenalan
10 Makalah ini memberikan gambaran arsitektur platform Avalanche. Fokus utamanya ada pada tiga kunci tersebut pembeda platform: mesin, model arsitektur, dan
介绍
10 本文提供了 Avalanche 平台的架构概述。重点关注三个关键 该平台的区别在于:引擎、架构模型和
Mesin
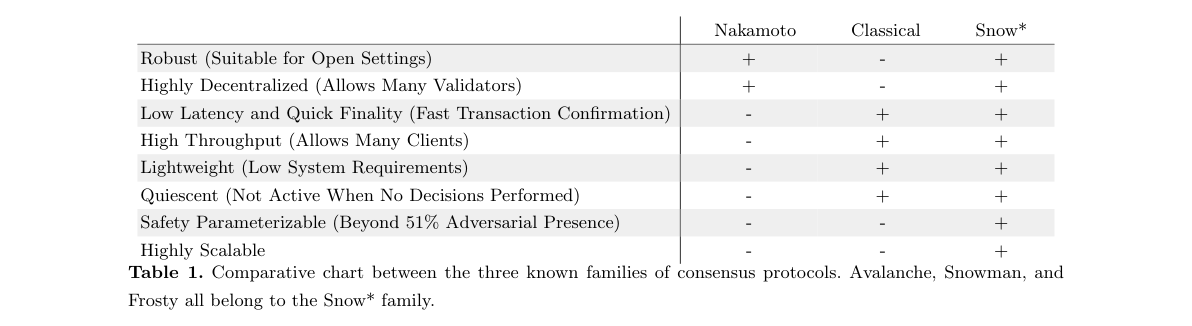
60 Pembahasan platform Avalanche dimulai dengan komponen inti yang menggerakkan platform: the mesin konsensus. Latar Belakang Pembayaran yang terdistribusi dan – yang lebih umum – perhitungan, memerlukan kesepakatan antar kelompok mesin. Oleh karena itu, protokol konsensus, yang memungkinkan sekelompok node untuk mencapai kesepakatan, terletak pada jantung dari blockchains, serta hampir setiap sistem terdistribusi industri skala besar yang diterapkan. Topiknya 65 telah mendapat pengawasan ketat selama hampir lima dekade, dan upaya tersebut, hingga saat ini, hanya menghasilkan dua keluarga protokol: protokol konsensus klasik, yang mengandalkan komunikasi semua-ke-semua, dan konsensus Nakamoto, yang mengandalkan penambangan proof-of-work ditambah dengan aturan rantai terpanjang. Sedangkan protokol konsensus klasik dapat memiliki latensi rendah dan throughput tinggi, namun tidak dapat menskalakan peserta dalam jumlah besar, juga tidak kuat dengan adanya perubahan keanggotaan, yang sebagian besar telah menurunkan status mereka menjadi yang diberi izin 70 penerapan statis. Protokol konsensus Nakamoto [5, 7, 4], di sisi lain, kuat, namun mengalami hambatan. latensi konfirmasi yang tinggi, throughput yang rendah, dan memerlukan pengeluaran energi yang konstan untuk keamanannya. Rangkaian protokol Snow, yang diperkenalkan oleh Avalanche, menggabungkan properti terbaik dari protokol konsensus klasik dengan konsensus Nakamoto yang terbaik. Berdasarkan mekanisme pengambilan sampel jaringan yang ringan, mereka mencapai latensi rendah dan throughput tinggi tanpa perlu menyepakati keanggotaan yang tepat 75 sistem. Mereka mencakup ribuan hingga jutaan peserta yang berpartisipasi langsung dalam protokol konsensus. Selain itu, protokol ini tidak menggunakan penambangan PoW, sehingga menghindari penambangan yang terlalu mahal pengeluaran energi dan kebocoran nilai selanjutnya dalam ekosistem, menghasilkan energi yang ringan, ramah lingkungan, dan tidak bersuara protokol. Mekanisme dan Properti Protokol Snow beroperasi dengan pengambilan sampel jaringan secara berulang. Setiap simpul 80 melakukan jajak pendapat terhadap sekelompok tetangga yang kecil, berukuran konstan, dan dipilih secara acak, dan mengubah proposalnya menjadi mayoritas super mendukung nilai yang berbeda. Sampel diulang sampai konvergensi tercapai, yang terjadi dengan cepat operasi normal. Kami menjelaskan mekanisme operasi melalui contoh nyata. Pertama, transaksi dibuat oleh pengguna dan dikirim ke node validasi, yaitu node yang berpartisipasi dalam prosedur konsensus. Saat itulah 85 disebarkan ke node lain dalam jaringan melalui gosip. Apa yang terjadi jika pengguna tersebut juga mengeluarkan konflik4 Kevin Sekniqi, Daniel Laine, Stephen Buttolph, dan Emin G¨un Sirer transaksi, yaitu pembelanjaan ganda? Untuk memilih di antara transaksi yang bertentangan dan mencegah pembelanjaan ganda, setiap node secara acak memilih sebagian kecil node dan menanyakan transaksi mana yang bertentangan. node yang ditanyai menganggapnya valid. Jika node yang melakukan kueri menerima respons mayoritas super yang mendukung dari satu transaksi, maka node mengubah responnya sendiri terhadap transaksi tersebut. Setiap node dalam jaringan 90 mengulangi prosedur ini sampai seluruh jaringan mencapai konsensus mengenai salah satu transaksi yang bertentangan. Anehnya, meskipun mekanisme inti operasinya cukup sederhana, protokol-protokol ini menghasilkan hasil yang sangat tinggi dinamika sistem yang diinginkan sehingga cocok untuk penerapan skala besar. – Tanpa Izin, Terbuka untuk Churn, dan Kuat. Banyak proyek blockchain terbaru menggunakan gaya klasik protokol konsensus dan oleh karena itu memerlukan pengetahuan keanggotaan penuh. Mengetahui keseluruhan set par95 peserta cukup sederhana dalam sistem tertutup dan berizin, namun menjadi semakin sulit dalam sistem terbuka, jaringan terdesentralisasi. Keterbatasan ini menimbulkan risiko keamanan yang tinggi bagi karyawan yang sudah ada protokol seperti itu. Sebaliknya, protokol Snow mempertahankan jaminan keamanan yang tinggi bahkan ketika terdapat perbedaan yang terkuantifikasi dengan baik antara tampilan jaringan dari dua node mana pun. Validator protokol Snow nikmati kemampuan untuk memvalidasi tanpa pengetahuan keanggotaan penuh yang berkelanjutan. Oleh karena itu, mereka kuat 100 dan sangat cocok untuk blockchain umum. – Dapat Diskalakan dan Terdesentralisasi Fitur inti dari keluarga Snow adalah kemampuannya untuk melakukan penskalaan tanpa menimbulkan biaya pengorbanan mendasar. Protokol salju dapat diskalakan hingga puluhan ribu atau jutaan node, tanpa delegasi ke subkumpulan validators. Protokol-protokol ini menikmati desentralisasi sistem terbaik di kelasnya, sehingga memungkinkan setiap node untuk memvalidasi sepenuhnya. Partisipasi langsung yang berkelanjutan mempunyai implikasi yang mendalam terhadap keamanan 105 dari sistem. Di hampir setiap protokol proof-of-stake yang mencoba menskalakan ke kumpulan peserta yang besar, mode operasi umumnya adalah mengaktifkan penskalaan dengan mendelegasikan validasi ke subkomite. Tentu saja, hal ini menyiratkan bahwa keamanan sistem kini sama tingginya dengan kerugian akibat korupsi subkomite. Subkomite selanjutnya tunduk pada pembentukan kartel. Dalam protokol tipe Snow, delegasi seperti itu tidak diperlukan, sehingga setiap operator node dapat memiliki 110 node pertama. ucapan tangan dalam sistem, setiap saat. Desain lain, biasanya disebut sebagai state sharding, merupakan upaya untuk memberikan skalabilitas dengan memparalelkan serialisasi transaksi ke jaringan independen validators. Sayangnya, keamanan sistem dalam desain seperti itu hanya setinggi yang paling mudah dirusak pecahan independen. Oleh karena itu, baik pemilihan subkomite maupun sharding bukanlah strategi penskalaan yang cocok untuk platform kripto. 115 – Adaptif. Tidak seperti sistem berbasis pemungutan suara lainnya, protokol Snow mencapai kinerja yang lebih tinggi ketika musuhnya kecil, namun sangat tangguh menghadapi serangan besar. – Aman secara Asinkron. Protokol Snow, tidak seperti protokol rantai terpanjang, tidak memerlukan sinkronisitas beroperasi dengan aman, dan oleh karena itu mencegah pembelanjaan ganda bahkan saat menghadapi partisi jaringan. Dalam Bitcoin, misalnya, jika asumsi sinkronisitas dilanggar, maka dimungkinkan untuk beroperasi pada fork independen 120 Bitcoin jaringan untuk jangka waktu yang lama, yang akan membatalkan transaksi apa pun setelah fork menyembuhkan. – Latensi Rendah. Kebanyakan blockchain saat ini tidak dapat mendukung aplikasi bisnis, seperti perdagangan atau harian pembayaran ritel. Tidak mungkin menunggu beberapa menit, atau bahkan berjam-jam, untuk konfirmasi transaksi. Oleh karena itu, salah satu sifat protokol konsensus yang paling penting namun sering diabaikan adalah 125 waktu menuju finalitas. Protokol Snow biasanya mencapai finalitas dalam waktu ≤1 detik, yang jauh lebih rendah daripada protokol Snow. baik protokol rantai terpanjang maupun blockchain yang dipecah, keduanya biasanya mencakup finalitas suatu masalah menit.Avalanche Platform 2020/06/30 5 – Throughput Tinggi. Protokol Snow, yang dapat membangun rantai linier atau DAG, mencapai ribuan transaksi per detik (5000+ tps), dengan tetap mempertahankan desentralisasi penuh. Solusi blockchain baru yang diklaim 130 TPS yang tinggi biasanya mengorbankan desentralisasi dan keamanan dan memilih sistem yang lebih tersentralisasi dan tidak aman. mekanisme konsensus. Beberapa proyek melaporkan angka-angka dari pengaturan yang sangat terkontrol, sehingga terjadi kesalahan pelaporan hasil kinerja sebenarnya. Angka-angka yang dilaporkan untuk $AVAX diambil langsung dari jaringan Avalanche yang nyata dan diterapkan sepenuhnya yang berjalan pada 2000 node di AWS, didistribusikan secara geografis ke seluruh dunia pada jaringan low-end mesin. Hasil kinerja yang lebih tinggi (10.000+) dapat dicapai dengan mengasumsikan bandwidth yang lebih tinggi 135 penyediaan untuk setiap node dan perangkat keras khusus untuk verifikasi tanda tangan. Akhirnya, kami mencatat bahwa metrik yang disebutkan di atas berada di lapisan dasar. Solusi penskalaan lapisan-2 segera meningkatkan hasil ini secara signifikan. Bagan Perbandingan Konsensus Tabel 1 menjelaskan perbedaan antara tiga keluarga yang diketahui protokol konsensus melalui serangkaian 8 sumbu kritis. 140 Nakamoto Klasik Salju Kuat (Cocok untuk Pengaturan Terbuka) + - + Sangat Terdesentralisasi (Memungkinkan Banyak Validator) + - + Latensi Rendah dan Finalitas Cepat (Konfirmasi Transaksi Cepat) - + + Throughput Tinggi (Memungkinkan Banyak Klien) - + + Ringan (Persyaratan Sistem Rendah) - + + Diam (Tidak Aktif Bila Tidak Ada Keputusan yang Dilakukan) - + + Keamanan Dapat Diparameterisasi (Melampaui 51% Kehadiran Musuh) - - + Sangat Skalabel - - + Tabel 1. Bagan perbandingan antara tiga kelompok protokol konsensus yang diketahui. Avalanche, Manusia Salju, dan Frosty semuanya milik keluarga Snow*.
发动机
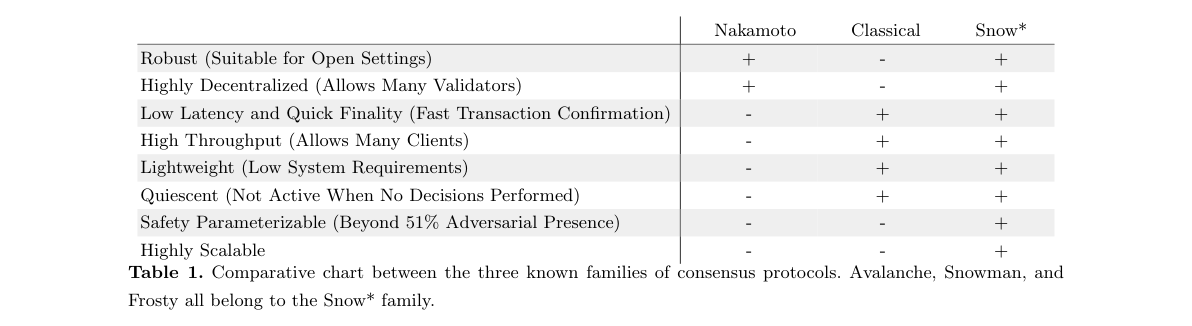
60 对 Avalanche 平台的讨论从为平台提供动力的核心组件开始: 共识引擎。 背景 分布式支付和(更一般地说)计算,需要一组之间达成一致 机器。因此,共识协议是让一组节点达成一致的协议。 blockchains 的核心,以及几乎所有部署的大型工业分布式系统。主题 65 近五年来受到了广泛的审查,而迄今为止,这一努力只取得了两个家庭的成果 协议:经典共识协议,依赖于所有人对所有人的通信,以及中本聪共识, 它依赖于 proof-of-work 挖掘和最长链规则。虽然经典共识协议 可以具有低延迟和高吞吐量,它们不能扩展到大量参与者,也不能 在成员资格变更的情况下表现强劲,这使得它们大多被降级为许可的、大多是 70 静态部署。另一方面,中本聪共识协议 [5,7,4] 很稳健,但存在以下问题: 确认延迟高、吞吐量低,并且需要持续的能量消耗来保证其安全性。 Snow 系列协议由 Avalanche 推出,结合了经典共识协议的最佳特性和中本聪共识的最佳特性。基于轻量级网络采样机制, 他们实现了低延迟和高吞吐量,而无需就确切的成员资格达成一致。 75 系统。它们的参与者规模从数千到数百万不等,直接参与共识协议。此外,该协议不使用 PoW 挖矿,因此避免了其过高的成本 生态系统中的能源消耗和随后的价值泄漏,产生轻量级、绿色和静态 协议。 机制和属性 Snow 协议通过对网络进行重复采样来运行。每个节点 80 轮询一小部分、大小恒定、随机选择的邻居,并在绝大多数情况下改变其提议 支持不同的值。重复采样直到达到收敛,这一过程在 正常操作。 我们通过一个具体的例子来阐明其运行机制。首先,创建一个交易 用户并发送到验证节点,验证节点是参与共识过程的节点。正是那时 85 通过八卦传播到网络中的其他节点。如果该用户也发出了冲突的问题,会发生什么情况4 凯文·塞克尼奇、丹尼尔·莱恩、斯蒂芬·布托夫和艾敏·古恩·西雷尔 交易,即双花?为了在冲突交易中进行选择并防止双花,每个节点随机选择一小部分节点并查询哪些交易是冲突的 被查询的节点认为是有效的。如果查询节点收到绝大多数赞成的响应 一个交易,然后节点改变自己对该交易的响应。网络中的每个节点 90 重复此过程,直到整个网络就其中一项冲突交易达成共识。 令人惊讶的是,虽然核心操作机制非常简单,但这些协议导致高度 理想的系统动态使它们适合大规模部署。 – 无需许可、开放、稳定且稳健。最新的 blockchain 项目采用经典 共识协议,因此需要充分的成员知识。了解par95整套 参与者在封闭的、许可的系统中非常简单,但在开放的、许可的系统中变得越来越困难。 去中心化网络。这种限制给现有的现有企业带来了很高的安全风险 此类协议。相比之下,即使任何两个节点的网络视图之间存在明确量化的差异,Snow 协议也能保持高度的安全保证。 Snow 协议的验证者 享受无需持续完整的会员知识即可进行验证的能力。因此,它们非常坚固 100 非常适合公共 blockchains。 – 可扩展和去中心化 Snow 系列的一个核心特征是它能够在不产生任何影响的情况下进行扩展 基本的权衡。 Snow 协议可以扩展到数万或数百万个节点,而无需委托给 validator 的子集。这些协议享有一流的系统去中心化,允许 每个节点都需要充分验证。第一手持续参与对安全影响深远 105 系统的。在几乎每个尝试扩展到大型参与者集的 proof-of-stake 协议中, 典型的操作模式是通过将验证委托给小组委员会来实现扩展。当然,这意味着系统的安全性现在与系统的腐败成本一样高。 小组委员会。此外,小组委员会还可能形成卡特尔。 在 Snow 型协议中,这种委托是不必要的,允许每个节点运营商拥有第一个 110 随时在系统中手动说出。另一种设计,通常称为状态分片,尝试 通过将事务序列化并行化到 validator 的独立网络来提供可扩展性。 不幸的是,这种设计中系统的安全性仅与最容易损坏的系统一样高。 独立分片。因此,小组委员会选举和分片都不是合适的扩容策略 对于加密平台。 115 – 自适应。与其他基于投票的系统不同,Snow 协议在以下情况下可实现更高的性能: 对手虽小,但在大规模攻击下却具有很强的弹性。 – 异步安全。 Snow 协议与最长链协议不同,不需要同步性 安全运行,因此即使在网络分区的情况下也能防止双花。在 Bitcoin 中, 例如,如果违反了同步性假设,则可以对独立的分叉进行操作 120 Bitcoin 网络长时间运行,一旦分叉,任何交易都会失效 治愈。 – 低延迟。如今,大多数 blockchain 无法支持业务应用程序,例如交易或日常应用程序 零售支付。等待几分钟甚至几个小时来确认交易是根本行不通的。 因此,共识协议最重要但又被高度忽视的属性之一是 125 最终确定的时间。 Snow 协议通常在 ≤1 秒内达到最终结果,这明显低于 最长链协议和分片 blockchain,这两种协议通常都涵盖了某个问题的最终结果 分钟。Avalanche 平台 2020/06/30 5 – 高吞吐量。 Snow 协议可以构建线性链或 DAG,达到每秒数千笔交易(5000+ tps),同时保留完全去中心化。新的 blockchain 解决方案声称 130 高 TPS 通常会权衡去中心化和安全性,并选择更加中心化和不安全的 共识机制。一些项目报告的数字来自高度控制的环境,从而导致误报 真实的性能结果。 $AVAX 的报告数字直接取自真实的、完全实现的 Avalanche 网络,该网络在 AWS 上的 2000 个节点上运行,在低端设备上分布在全球各地 机器。通过假设更高的带宽可以实现更高的性能结果(10,000+) 135 为每个节点和签名验证专用硬件进行配置。最后,我们注意到 上述指标位于基础层。第 2 层扩展解决方案立即增强了这些结果 相当大。 共识比较图 表 1 描述了三个已知家族之间的差异 通过一组 8 个关键轴制定共识协议。 140 中本 古典 雪 坚固(适合开放设置) + - + 高度去中心化(允许许多验证者) + - + 低延迟和快速最终确定(快速交易确认) - + + 高吞吐量(允许许多客户端) - + + 轻量级(系统要求低) - + + 静止(未执行任何决策时不活动) - + + 安全参数化(超过 51% 的对抗性存在) - - + 高度可扩展 - - + 表 1. 三个已知共识协议家族之间的比较图表。 Avalanche,雪人,和 Frosty都属于Snow家族。
Ikhtisar Platform
Pada bagian ini, kami memberikan gambaran arsitektur platform dan mendiskusikan berbagai implementasi detail. Platform Avalanche dengan jelas memisahkan tiga masalah: rantai (dan aset yang dibangun di atasnya), eksekusi lingkungan, dan penyebaran. 3.1 Arsitektur 145 Subjaringan Subjaringan, atau subnet, adalah kumpulan dinamis validator yang bekerja sama untuk mencapai konsensus pada keadaan himpunan blockchains. Setiap blockchain divalidasi oleh satu subnet, dan satu subnet dapat memvalidasi banyak blockchains secara acak. validator dapat menjadi anggota dari banyak subnet yang berubah-ubah. Sebuah subnet memutuskan yang boleh memasukinya, dan mungkin mengharuskan validator konstituennya memiliki sifat tertentu. Avalanche platform mendukung pembuatan dan pengoperasian banyak subnet secara sewenang-wenang. Untuk membuat subnet baru 150 atau untuk bergabung dengan subnet, seseorang harus membayar biaya dalam mata uang $AVAX.
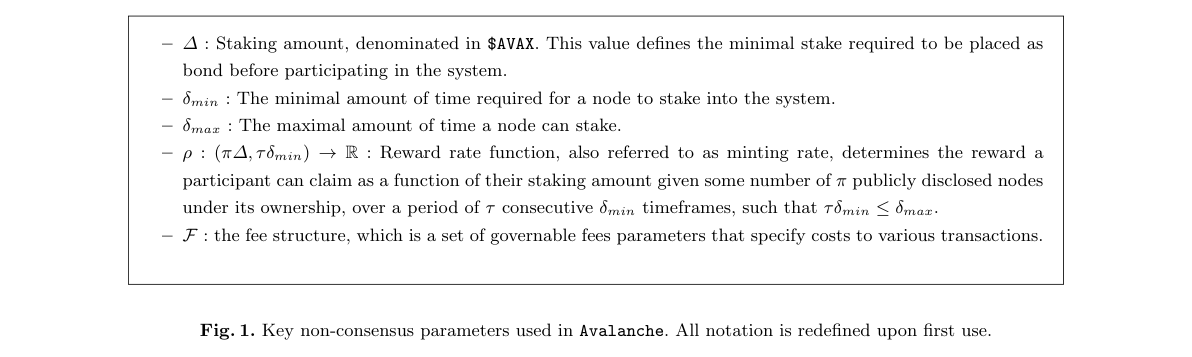
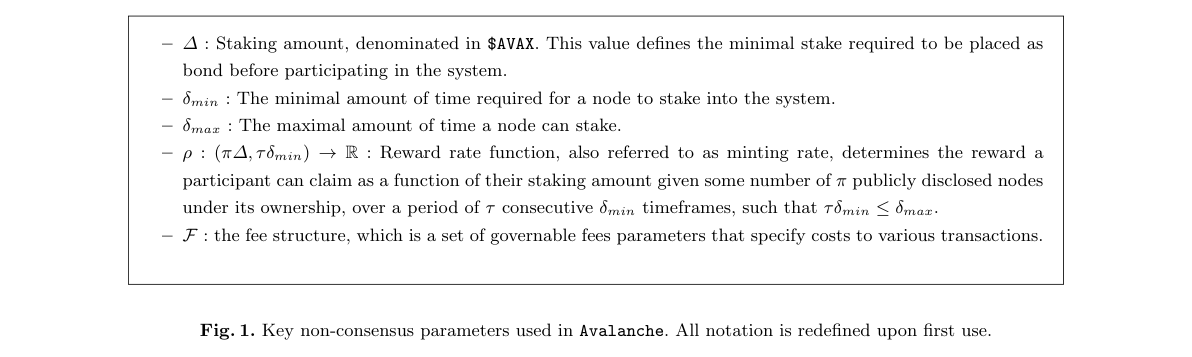
6 Kevin Sekniqi, Daniel Laine, Stephen Buttolph, dan Emin G¨un Sirer Model subnet menawarkan sejumlah keuntungan: – Jika validator tidak peduli dengan blockchain di subnet tertentu, ia tidak akan bergabung dengan subnet tersebut. Hal ini mengurangi lalu lintas jaringan, serta sumber daya komputasi yang diperlukan selama validators. Ini masuk berbeda dengan proyek blockchain lainnya, di mana setiap validator harus memvalidasi setiap transaksi, bahkan 155 mereka yang tidak mereka pedulikan. – Karena subnet menentukan siapa yang boleh memasukinya, seseorang dapat membuat subnet pribadi. Artinya, setiap blockchain masuk subnet hanya divalidasi oleh sekumpulan validator yang tepercaya. – Seseorang dapat membuat subnet yang setiap validator memiliki properti tertentu. Misalnya, seseorang dapat membuat a subnet di mana setiap validator terletak di yurisdiksi tertentu, atau di mana setiap validator terikat oleh beberapa 160 kontrak dunia nyata. Hal ini mungkin bermanfaat untuk alasan kepatuhan. Ada satu subnet khusus yang disebut Subnet Default. Ini divalidasi oleh semua validators. (Yaitu, secara berurutan untuk memvalidasi subnet apa pun, kita juga harus memvalidasi Subnet Default.) Subnet Default memvalidasi satu set blockchain yang telah ditentukan sebelumnya, termasuk blockchain tempat $AVAX berada dan diperdagangkan. Mesin Virtual Setiap blockchain adalah turunan dari Mesin Virtual (VM.) VM adalah cetak biru untuk a 165 blockchain, seperti kelas yang merupakan cetak biru untuk suatu objek dalam bahasa pemrograman berorientasi objek. Itu antarmuka, status, dan perilaku blockchain ditentukan oleh VM yang dijalankan blockchain. Berikut ini properti dari blockchain, dan lainnya, ditentukan oleh VM: – Isi satu blok – Transisi keadaan yang terjadi ketika sebuah blok diterima 170 – API yang diekspos oleh blockchain dan titik akhirnya – Data yang disimpan ke disk Kami mengatakan bahwa blockchain “menggunakan” atau “menjalankan” VM tertentu. Saat membuat blockchain, seseorang menentukan VM itu berjalan, serta keadaan asal blockchain. blockchain baru dapat dibuat menggunakan yang sudah ada sebelumnya VM, atau pengembang dapat membuat kode yang baru. Mungkin ada banyak blockchain yang menjalankan VM yang sama. 175 Setiap blockchain, bahkan yang menjalankan VM yang sama, secara logis independen dari yang lain dan mempertahankannya negara bagian sendiri. 3.2 Bootstrap Langkah pertama dalam berpartisipasi dalam Avalanche adalah bootstrap. Prosesnya terjadi dalam tiga tahap: koneksi untuk menyemai jangkar, penemuan jaringan dan negara, dan menjadi validator. 180 Seed Anchors Setiap sistem jaringan rekan yang beroperasi tanpa izin (yaitu hard-coded) kumpulan identitas memerlukan beberapa mekanisme untuk penemuan rekan. Dalam jaringan berbagi file peer-to-peer, satu set pelacak digunakan. Dalam jaringan kripto, mekanisme yang umum adalah penggunaan node benih DNS (yang kami rujukAvalanche Platform 2020/06/30 7 menjadi seed jangkar), yang terdiri dari sekumpulan alamat IP awal yang terdefinisi dengan baik yang menjadi asal anggota lainnya jaringan dapat ditemukan. Peran node benih DNS adalah untuk memberikan informasi berguna tentang kumpulan tersebut 185 peserta aktif dalam sistem. Mekanisme yang sama digunakan di Bitcoin Inti [1], dimana File src/chainparams.cpp dari kode sumber menyimpan daftar node benih yang dikodekan secara keras. Perbedaan antara BTC dan Avalanche adalah BTC hanya memerlukan satu node benih DNS yang benar, sedangkan Avalanche memerlukan yang sederhana mayoritas jangkar benar. Sebagai contoh, pengguna baru dapat memilih untuk melakukan bootstrap pada tampilan jaringan melalui serangkaian bursa yang sudah mapan dan bereputasi baik, yang mana pun secara individual tidak dapat dipercaya. 190 Namun, kami mencatat bahwa kumpulan node bootstrap tidak perlu dikodekan secara keras atau statis, dan bisa saja disediakan oleh pengguna, meskipun untuk kemudahan penggunaan, klien dapat memberikan pengaturan default yang mencakup secara ekonomis aktor penting, seperti pertukaran, yang dengannya klien ingin berbagi pandangan dunia. Tidak ada hambatan untuk itu menjadi jangkar benih, oleh karena itu sekumpulan jangkar benih tidak dapat menentukan apakah suatu node boleh masuk atau tidak jaringan, karena node dapat menemukan jaringan terbaru dari Avalanche rekan dengan melampirkan ke kumpulan benih mana pun 195 jangkar. Penemuan Jaringan dan Negara Setelah terhubung ke jangkar benih, sebuah node menanyakan kumpulan terbaru transisi keadaan. Kami menyebut rangkaian transisi negara ini sebagai batas yang diterima. Untuk sebuah rantai, batas yang diterima adalah blok terakhir yang diterima. Untuk DAG, garis depan yang diterima adalah himpunan simpul yang diterima, namun sudah dimiliki tidak ada anak yang diterima. Setelah mengumpulkan batas-batas yang diterima dari jangkar benih, negara mentransisikannya 200 diterima oleh sebagian besar benih jangkar didefinisikan sebagai diterima. Keadaan yang benar kemudian diekstraksi dengan menyinkronkan dengan node sampel. Selama ada mayoritas node yang benar di jangkar benih ditetapkan, maka transisi keadaan yang diterima harus ditandai sebagai diterima oleh setidaknya satu node yang benar. Proses penemuan keadaan ini juga digunakan untuk penemuan jaringan. Himpunan keanggotaan jaringan tersebut adalah didefinisikan pada rantai validator. Oleh karena itu, sinkronisasi dengan rantai validator memungkinkan node untuk menemukannya 205 kumpulan validators saat ini. Rantai validator akan dibahas lebih lanjut di bagian selanjutnya. 3.3 Pengendalian dan Keanggotaan Sybil Protokol konsensus memberikan jaminan keamanannya dengan asumsi hingga angka ambang batas anggota dalam sistem bisa menjadi musuh. Serangan Sybil, dimana sebuah node membanjiri jaringan dengan harga murah dengan identitas jahat, dapat dengan mudah membatalkan jaminan ini. Pada dasarnya, serangan seperti itu hanya bisa terjadi 210 dihalangi dengan memperdagangkan kehadiran dengan bukti sumber daya yang sulit dipalsukan [3]. Sistem masa lalu telah mengeksplorasi penggunaannya mekanisme pencegahan Sybil yang mencakup proof-of-work (PoW), proof-of-stake (PoS), bukti waktu yang telah berlalu (POET), bukti ruang dan waktu (PoST), dan bukti otoritas (PoA). Pada intinya, semua mekanisme ini memiliki fungsi yang sama: mekanisme tersebut mengharuskan setiap peserta memilikinya beberapa “skin in the game” dalam bentuk komitmen ekonomi, yang pada gilirannya memberikan dampak ekonomi 215 penghalang terhadap perilaku buruk yang dilakukan peserta tersebut. Semuanya melibatkan suatu bentuk pasak, baik itu dalam bentuk rig penambangan dan hash daya (PoW), ruang disk (PoST), perangkat keras tepercaya (POET), atau identitas yang disetujui (PoA). Taruhan ini menjadi dasar biaya ekonomi yang harus ditanggung oleh para peserta untuk memperoleh suara. Untuk Misalnya, di Bitcoin, kemampuan untuk menyumbangkan blok yang valid berbanding lurus dengan hash kekuatan dari peserta pengusul. Sayangnya, terdapat juga kebingungan besar antara protokol konsensus8 Kevin Sekniqi, Daniel Laine, Stephen Buttolph, dan Emin G¨un Sirer versus mekanisme kontrol Sybil. Kami mencatat bahwa pilihan protokol konsensus, sebagian besar, ortogonal dengan pilihan mekanisme kontrol Sybil. Ini tidak berarti bahwa mekanisme kendali Sybil memang demikian saling menggantikan satu sama lain, karena pilihan tertentu mungkin memiliki implikasi terhadap hal yang mendasarinya jaminan protokol konsensus. Namun, keluarga Snow* dapat digabungkan dengan banyak keluarga yang dikenal mekanisme, tanpa modifikasi yang signifikan. 225 Pada akhirnya, demi keamanan dan untuk memastikan bahwa insentif para peserta selaras dengan manfaatnya jaringan, $AVAX pilih PoS ke mekanisme kontrol inti Sybil. Beberapa bentuk taruhan pada dasarnya bersifat inheren terpusat: manufaktur rig penambangan (PoW), misalnya, pada dasarnya terpusat di tangan segelintir orang orang-orang dengan pengetahuan yang sesuai dan akses terhadap lusinan paten yang diperlukan untuk VLSI yang kompetitif manufaktur. Selain itu, kebocoran nilai penambangan PoW disebabkan oleh besarnya subsidi penambang setiap tahunnya. Demikian pula, 230 ruang disk paling banyak dimiliki oleh operator pusat data besar. Selanjutnya, semua mekanisme kontrol sybil yang menimbulkan biaya berkelanjutan, mis. biaya listrik untuk hashing, nilai kebocoran ekosistem, belum lagi menghancurkan lingkungan. Hal ini, pada gilirannya, mengurangi kelayakan untuk token, yang mana akan merugikan pergerakan harga dalam jangka waktu singkat dapat membuat sistem tidak dapat dioperasikan. Proof-of-work secara inheren memilih untuk penambang yang memiliki koneksi untuk mendapatkan listrik murah, tidak ada hubungannya dengan kemampuan penambang 235 untuk membuat serial transaksi atau kontribusinya terhadap ekosistem secara keseluruhan. Di antara pilihan-pilihan ini, kami memilih proof-of-stake, karena hijau, mudah diakses, dan terbuka untuk semua. Namun, kami mencatat bahwa saat $AVAX digunakan PoS, jaringan Avalanche memungkinkan subnet diluncurkan dengan PoW dan PoS. Staking adalah mekanisme alami untuk berpartisipasi dalam jaringan terbuka karena memungkinkan terjadinya ekonomi langsung argumen: kemungkinan keberhasilan suatu serangan berbanding lurus dengan biaya moneter yang ditentukan dengan baik 240 fungsi. Dengan kata lain, node yang melakukan staking termotivasi secara ekonomi untuk tidak melakukan perilaku tersebut mungkin merusak nilai taruhan mereka. Selain itu, taruhan ini tidak menimbulkan biaya pemeliharaan tambahan (lainnya kemudian biaya peluang berinvestasi pada aset lain), dan memiliki properti yang, tidak seperti peralatan pertambangan, dikonsumsi sepenuhnya jika digunakan dalam serangan bencana. Untuk operasi PoW, peralatan penambangan bisa dengan sederhana digunakan kembali atau – jika pemiliknya memutuskan untuk – dijual seluruhnya kembali ke pasar. 245 Sebuah node yang ingin memasuki jaringan dapat dengan bebas melakukannya dengan terlebih dahulu memasang pasak yang tidak dapat bergerak selama durasi partisipasi dalam jaringan. Pengguna menentukan jumlah durasi taruhan. Setelah diterima, taruhan tidak dapat dikembalikan. Tujuan utamanya adalah untuk memastikan bahwa node berbagi secara substansial tampilan jaringan yang sebagian besar stabil. Kami mengantisipasi pengaturan waktu minimum staking pada pesanan a minggu. 250 Tidak seperti sistem lain yang juga mengusulkan mekanisme PoS, $AVAX tidak menggunakan pemotongan, dan oleh karena itu semua taruhan dikembalikan ketika periode staking berakhir. Ini mencegah skenario yang tidak diinginkan seperti kegagalan perangkat lunak atau perangkat keras klien yang menyebabkan hilangnya koin. Ini sesuai dengan filosofi desain kami membangun teknologi yang dapat diprediksi: token yang dipertaruhkan tidak berisiko, bahkan dengan adanya perangkat lunak atau kelemahan perangkat keras. 255 Di Avalanche, sebuah node yang ingin berpartisipasi mengeluarkan transaksi pasak khusus ke rantai validator. Nama transaksi staking jumlah yang dipertaruhkan, kunci staking peserta yaitu staking, durasi, dan waktu validasi akan dimulai. Setelah transaksi diterima, dana akan dikunci hingga akhir periode staking. Jumlah minimum yang diperbolehkan ditentukan dan diberlakukan oleh sistem. Taruhannya jumlah yang ditempatkan oleh seorang peserta mempunyai implikasi terhadap besarnya pengaruh yang dimiliki peserta dalamAvalanche Platform 2020/06/30 9 proses konsensus, serta imbalannya, seperti yang akan dibahas nanti. Durasi staking yang ditentukan, harus antara δmin dan δmax, jangka waktu minimum dan maksimum di mana setiap taruhan dapat dikunci. Seperti halnya Jumlah staking, periode staking juga mempunyai implikasi terhadap imbalan dalam sistem. Kehilangan atau pencurian Kunci staking tidak dapat menyebabkan hilangnya aset, karena kunci staking hanya digunakan dalam proses konsensus, bukan untuk aset transfer. 265 3.4 Kontrak Cerdas di $AVAX Saat peluncuran Avalanche mendukung smart contracts berbasis Soliditas standar melalui mesin virtual Ethereum (EVM). Kami membayangkan bahwa platform ini akan mendukung rangkaian smart contract yang lebih kaya dan lebih kuat alat, antara lain: – Kontrak pintar dengan eksekusi off-chain dan verifikasi on-chain. 270 – Kontrak pintar dengan eksekusi paralel. Setiap smart contract yang tidak beroperasi pada negara bagian yang sama di subnet apa pun di Avalanche akan dapat dijalankan secara paralel. – Soliditas yang ditingkatkan, disebut Soliditas++. Bahasa baru ini akan mendukung pembuatan versi, matematika yang aman dan aritmatika titik tetap, sistem tipe yang ditingkatkan, kompilasi ke LLVM, dan eksekusi tepat waktu. Jika pengembang memerlukan dukungan EVM tetapi ingin menerapkan smart contract di subnet pribadi, mereka 275 dapat memutar subnet baru secara langsung. Beginilah cara Avalanche mengaktifkan sharding khusus fungsi subnet. Selain itu, jika pengembang memerlukan interaksi dengan Ethereum smart yang saat ini diterapkan kontrak, mereka dapat berinteraksi dengan subnet Athereum, yaitu sendok Ethereum. Terakhir, jika seorang pengembang memerlukan lingkungan eksekusi yang berbeda dari mesin virtual Ethereum, mereka mungkin memilih untuk menerapkan smart contract mereka melalui subnet yang mengimplementasikan lingkungan eksekusi yang berbeda, seperti DAML 280 atau WASM. Subnet dapat mendukung fitur tambahan di luar perilaku VM. Misalnya, subnet dapat menerapkan persyaratan kinerja untuk validator node yang lebih besar yang menampung smart contracts untuk jangka waktu yang lebih lama, atau validators yang memegang kontrak negara secara pribadi. 4 Tata Kelola dan Token $AVAX 4.1 Token Asli $AVAX 285 Kebijakan Moneter token asli, $AVAX, adalah pasokan terbatas, dengan batas ditetapkan pada 720.000.000 tokens, dengan 360.000.000 tokens tersedia pada peluncuran mainnet. Namun, tidak seperti tokens pasokan terbatas lainnya yang mana meningkatkan tingkat pencetakan secara terus-menerus, \(AVAX is designed to react to changing economic conditions. In particular, the objective of \)kebijakan moneter AVAX adalah untuk menyeimbangkan insentif pengguna untuk mempertaruhkan token dibandingkan menggunakannya untuk berinteraksi dengan berbagai layanan yang tersedia di platform. Peserta di platform 290 secara kolektif bertindak sebagai bank cadangan yang terdesentralisasi. Pengungkit yang tersedia di Avalanche adalah staking hadiah, biaya, dan airdrop, yang semuanya dipengaruhi oleh parameter yang dapat diatur. Imbalan staking ditentukan oleh tata kelola on-chain, dan diatur oleh fungsi yang dirancang untuk tidak pernah melampaui pasokan yang dibatasi. Staking dapat diinduksi dengan menaikkan biaya atau meningkatkan staking hadiah. Di sisi lain, kita dapat mendorong peningkatan keterlibatan dengan layanan platform Avalanche dengan menurunkan biaya, dan mengurangi hadiah staking.10 Kevin Sekniqi, Daniel Laine, Stephen Buttolph, dan Emin G¨un Sirer Kegunaan Pembayaran Pembayaran peer-to-peer yang terdesentralisasi sebagian besar merupakan impian yang belum terwujud bagi industri ini kurangnya kinerja petahana saat ini. $AVAX sama kuat dan mudahnya digunakan seperti halnya pembayaran Visa, memungkinkan ribuan transaksi secara global setiap detik, dengan cara yang sepenuhnya tidak dapat dipercaya dan terdesentralisasi. Lebih lanjut, bagi merchant di seluruh dunia, $AVAX memberikan proposisi nilai langsung dibandingkan Visa, yaitu lebih rendah 300 biaya. Staking: Mengamankan Sistem Pada platform Avalanche, kontrol sybil dicapai melalui staking. Secara berurutan untuk memvalidasi, peserta harus mengunci koin, atau mempertaruhkan. Validator, terkadang disebut sebagai pemangku kepentingan, adalah kompensasi untuk layanan validasi mereka berdasarkan jumlah staking dan durasi staking, antara lain properti. Fungsi kompensasi yang dipilih harus meminimalkan varians, memastikan bahwa pemangku kepentingan besar tidak melakukan hal yang sama 305 menerima lebih banyak kompensasi secara tidak proporsional. Peserta juga tidak tunduk pada faktor “keberuntungan” apa pun, seperti pada Penambangan PoW. Skema penghargaan seperti itu juga menghambat pembentukan penambangan atau kumpulan staking yang benar-benar memungkinkan partisipasi yang terdesentralisasi dan tidak dapat dipercaya dalam jaringan. Pertukaran atom Selain memberikan keamanan inti sistem, $AVAX token berfungsi sebagai unit universal pertukaran. Dari sana, platform Avalanche akan mampu mendukung pertukaran atom tanpa kepercayaan secara asli di 310 platform yang memungkinkan pertukaran asli dan benar-benar terdesentralisasi untuk semua jenis aset langsung di Avalanche. 4.2 Tata Kelola Tata kelola sangat penting dalam pengembangan dan penerapan platform apa pun karena – sama seperti platform lainnya sistem – Avalanche juga akan menghadapi evolusi dan pembaruan alami. $AVAX menyediakan tata kelola on-chain untuk parameter penting jaringan di mana peserta dapat memberikan suara pada perubahan pada jaringan dan 315 menyelesaikan keputusan peningkatan jaringan secara demokratis. Ini termasuk faktor-faktor seperti jumlah minimum staking, tingkat pencetakan, serta parameter ekonomi lainnya. Hal ini memungkinkan platform untuk secara efektif melakukan optimasi parameter dinamis melalui kerumunan oracle. Namun, tidak seperti beberapa platform tata kelola lainnya di luar sana, Avalanche tidak mengizinkan perubahan tak terbatas pada aspek sistem yang sewenang-wenang. Sebaliknya, hanya a sejumlah parameter yang telah ditentukan sebelumnya dapat dimodifikasi melalui tata kelola, sehingga menjadikan sistem lebih dapat diprediksi 320 dan meningkatkan keselamatan. Selanjutnya, semua parameter yang dapat diatur tunduk pada batasan dalam batasan waktu tertentu, memperkenalkan histeresis, dan memastikan bahwa sistem tetap dapat diprediksi dalam rentang waktu yang singkat. Proses yang bisa diterapkan untuk menemukan nilai parameter sistem yang dapat diterima secara global sangat penting untuk sistem desentralisasi tanpa penjaga. Avalanche dapat menggunakan mekanisme konsensusnya untuk membangun sistem yang memungkinkan siapa pun untuk mengusulkan transaksi khusus yang, pada dasarnya, merupakan jajak pendapat seluruh sistem. Setiap node yang berpartisipasi boleh 325 mengeluarkan proposal seperti itu. Tingkat imbalan nominal adalah parameter penting yang memengaruhi mata uang apa pun, baik digital maupun fiat. Sayangnya, mata uang kripto yang memperbaiki parameter ini mungkin menghadapi berbagai masalah, termasuk deflasi atau inflasi. Untuk itu, tingkat imbalan nominal tunduk pada tata kelola, dalam batasan yang telah ditentukan sebelumnya. Ini akan izinkan pemegang token untuk memilih apakah $AVAX pada akhirnya akan dibatasi, tidak dibatasi, atau bahkan deflasi.Avalanche Platform 2020/06/30 11 Biaya transaksi, yang dilambangkan dengan himpunan F, juga tunduk pada tata kelola. F secara efektif adalah tupel yang menggambarkan biaya yang terkait dengan berbagai instruksi dan transaksi. Terakhir, staking kali dan jumlah juga dapat diatur. Daftar parameter ini didefinisikan pada Gambar 1. – ∆: Jumlah staking, dalam mata uang $AVAX. Nilai ini menentukan taruhan minimal yang diperlukan untuk ditempatkan obligasi sebelum berpartisipasi dalam sistem. – δmin : Jumlah waktu minimal yang dibutuhkan sebuah node untuk melakukan staking ke dalam sistem. – δmax : Jumlah waktu maksimal yang dapat dipertaruhkan oleh sebuah node. – ρ : (π∆, τδmin) →R : Fungsi tingkat imbalan, juga disebut sebagai tingkat pencetakan, menentukan imbalan a peserta dapat mengklaim sebagai fungsi dari jumlah staking mereka dengan sejumlah π node yang diungkapkan secara publik di bawah kepemilikannya, selama jangka waktu τ berturut-turut δmin, sehingga τδmin ≤δmax. – F : struktur biaya, yang merupakan sekumpulan parameter biaya yang dapat diatur yang menentukan biaya untuk berbagai transaksi. Gambar 1. Parameter utama non-konsensus yang digunakan di Avalanche. Semua notasi didefinisikan ulang pada penggunaan pertama. Sejalan dengan prinsip prediktabilitas dalam sistem keuangan, tata kelola di $AVAX memiliki histeresis, artinya perubahan parameter sangat bergantung pada perubahan terkini. Ada dua batasan 335 terkait dengan setiap parameter yang dapat diatur: waktu dan jangkauan. Setelah parameter diubah menggunakan tata kelola transaksi, menjadi sangat sulit untuk mengubahnya kembali dengan segera dan dalam jumlah besar. Kesulitan ini dan batasan nilai mengendur seiring berjalannya waktu sejak perubahan terakhir. Secara keseluruhan, ini mencegah sistem berubah secara drastis dalam waktu singkat, memungkinkan pengguna memprediksi parameter sistem dengan aman jangka pendek, serta memiliki kendali dan fleksibilitas yang kuat untuk jangka panjang. 340
平台概览
在本节中,我们提供平台的架构概述并讨论各种实现 详细信息。 Avalanche 平台清楚地分离了三个问题:链(以及构建在其上的资产)、执行 环境和部署。 3.1 建筑 145 子网络 子网络或子网是一组动态的 validator ,它们一起工作以达成共识 关于一组 blockchain 的状态。每个 blockchain 由一个子网验证,一个子网可以验证 任意多个 blockchain。 validator 可以是任意多个子网的成员。子网决定 谁可以进入它,并且可能要求其组成部分 validator 具有某些属性。 Avalanche 平台支持任意多个子网的创建和操作。为了创建一个新的子网 150 或者要加入子网,必须支付以 $AVAX 计价的费用。
6 凯文·塞克尼奇、丹尼尔·莱恩、斯蒂芬·布托夫和艾敏·古恩·西雷尔 子网模型具有许多优点: – 如果 validator 不关心给定子网中的 blockchain,它就不会加入该子网。 这减少了网络流量以及 validators 所需的计算资源。这是在 与其他 blockchain 项目相比,其中每个 validator 都必须验证每笔交易,甚至 155 那些他们不关心的人。 – 由于子网决定谁可以进入它们,因此可以创建私有子网。也就是说,每个 blockchain 中 子网仅由一组受信任的 validator 进行验证。 – 可以创建一个子网,其中每个 validator 都具有某些属性。例如,可以创建一个 每个 validator 位于某个司法管辖区的子网,或者每个 validator 受某些管辖区约束的子网 160 现实世界的合同。出于合规性原因,这可能是有益的。 有一个特殊的子网,称为默认子网。它由所有 validator 验证。 (也就是说,按顺序 要验证任何子网,还必须验证默认子网。)默认子网验证一组 预定义的 blockchain,包括 $AVAX 存在和交易的 blockchain。 虚拟机 每个 blockchain 都是虚拟机 (VM) 的一个实例。VM 是一个蓝图 165 blockchain,就像面向对象编程语言中的类是对象的蓝图一样。的 blockchain 的接口、状态和行为由 blockchain 运行的 VM 定义。以下 blockchain 的属性和其他属性由 VM 定义: – 块的内容 – 接受块时发生的状态转换 170 – blockchain 及其端点公开的 API – 持久化到磁盘的数据 我们说 blockchain “使用”或“运行”给定的虚拟机。创建 blockchain 时,指定 VM 它运行,以及 blockchain 的创世状态。可以使用预先存在的 blockchain 创建新的 blockchain VM 或开发人员可以编写新的代码。可以有任意多个 blockchain 运行同一 VM。 175 每个 blockchain,即使是那些运行相同虚拟机的,在逻辑上独立于其他虚拟机,并维护其自身的特性。 自己的状态。 3.2 自举 参与 Avalanche 的第一步是引导。该过程分三个阶段进行: 连接 播种锚、网络和状态发现,并成为 validator。 180 种子锚点 任何未经许可(即硬编码)运行的对等网络系统 一组身份需要某种机制来进行对等发现。在点对点文件共享网络中,一组 使用跟踪器。在加密网络中,一个典型的机制是使用 DNS 种子节点(我们称之为Avalanche 平台 2020/06/30 7 作为种子锚点),其中包含一组明确定义的种子 IP 地址,其他成员可以从中使用这些地址 可以发现网络。 DNS种子节点的作用是提供有关集合的有用信息 185 系统中的活跃参与者。 Bitcoin 核心 [1] 中采用了相同的机制,其中 源代码的 src/chainparams.cpp 文件包含硬编码种子节点的列表。之间的区别 BTC 和 Avalanche 的区别在于,BTC 只需要一个正确的 DNS 种子节点,而 Avalanche 则需要一个简单的 DNS 种子节点。 大多数锚是正确的。例如,新用户可以选择引导网络视图 通过一系列完善且信誉良好的交易所,其中任何一个交易所单独都不可信。 190 然而,我们注意到,引导节点集不需要是硬编码或静态的,并且可以是 由用户提供,但为了便于使用,客户端可以提供默认设置,其中包括经济的 客户希望与之分享世界观的重要参与者,例如交流。没有任何障碍 成为种子锚点,因此一组种子锚点不能决定节点是否可以进入 网络,因为节点可以通过附加到任何种子集来发现 Avalanche 对等点的最新网络 195 锚点。 网络和状态发现 一旦连接到种子锚点,节点就会查询最新的一组 状态转换。我们将这组状态转换称为可接受的边界。对于链来说,可接受的边界 是最后接受的块。对于 DAG,接受边界是已接受但具有以下特征的顶点集: 不接受儿童。从种子锚点收集接受的边界后,状态转换 200 被大多数种子锚点接受被定义为被接受。然后提取正确的状态 通过与采样节点同步。只要种子锚点中有大多数正确节点 设置,则接受的状态转换必须已被至少一个正确的节点标记为接受。 该状态发现过程也用于网络发现。网络的成员资格集是 定义在 validator 链上。因此,与 validator 链同步可以让节点发现 205 当前的 validator 组。 validator 链将在下一节中进一步讨论。 3.3 Sybil 控制和成员资格 共识协议在假设数量达到阈值的情况下提供安全保证 系统中的成员可能是敌对的。女巫攻击,其中节点廉价地淹没网络 恶意身份可能会轻易使这些保证失效。从根本上来说,这种攻击只能是 210 通过用难以伪造的资源 [3] 的证据来交换存在来阻止。过去的系统已经探索过使用 跨越 proof-of-work (PoW)、proof-of-stake (PoS) 的 Sybil 威慑机制,经过时间证明 (POET)、时空证明(PoST)和权威证明(PoA)。 从本质上讲,所有这些机制都具有相同的功能:它们要求每个参与者都有 某种经济承诺形式的“利益攸关者”,这反过来又提供了一种经济承诺 215 防止该参与者不当行为的障碍。它们都涉及一种形式的股权,无论是哪种形式 采矿设备和 hash 电力 (PoW)、磁盘空间 (PoST)、可信硬件 (POET) 或经批准的身份 (PoA)。这种股权构成了参与者为获得发言权而必须承担的经济成本的基础。对于 例如,在 Bitcoin 中,贡献有效块的能力与 hash 的幂成正比。 提议参与者。不幸的是,共识协议之间也存在很大的混乱8 凯文·塞克尼奇、丹尼尔·莱恩、斯蒂芬·布托夫和艾敏·古恩·西雷尔 与 Sybil 控制机制相比。我们注意到,共识协议的选择在很大程度上是: 与 Sybil 控制机制的选择正交。这并不是说 Sybil 控制机制是 互相替换,因为特定的选择可能会对底层产生影响 共识协议的保证。然而,Snow* 系列可以与许多已知的 机制,无需进行重大修改。 225 最终,为了安全并确保参与者的激励与利益相一致 网络方面,$AVAX选择PoS作为核心Sybil控制机制。某些形式的股权本质上是 集中化:例如,采矿设备制造(PoW)本质上集中在少数人手中 拥有适当专业知识并能够获得具有竞争力的 VLSI 所需的数十项专利的人员 制造。此外,由于每年大量的矿工补贴,PoW 挖矿的价值也随之流失。同样, 230 大型数据中心运营商拥有最丰富的磁盘空间。此外,所有女巫控制机制 会产生持续成本,例如hashing 的电力成本,从生态系统中泄漏价值,更不用说 破坏环境。这反过来又降低了 token 的可行性范围,其中不利的 价格在短时间内波动可能导致系统无法运行。工作量证明本质上选择 矿工有关系网可以获得廉价电力,这与矿工的能力关系不大 235 序列化交易或其对整个生态系统的贡献。在这些选项中,我们选择 proof-of-stake,因为它是绿色的、可访问的并且向所有人开放。然而,我们注意到,虽然 $AVAX 使用 PoS,Avalanche 网络使子网能够通过 PoW 和 PoS 启动。 质押是参与开放网络的自然机制,因为它可以实现直接的经济 论点:攻击成功的概率与明确定义的货币成本成正比 240 功能。换句话说,参与质押的节点出于经济动机不参与以下行为: 可能会损害他们所持股份的价值。此外,该股份不会产生任何额外的维护成本(其他 然后是投资另一种资产的机会成本),并且具有与采矿设备不同的属性, 如果用于灾难性攻击,则会被完全消耗。对于 PoW 操作,挖矿设备可以简单地 重复使用,或者——如果所有者决定的话——完全卖回市场。 245 希望进入网络的节点可以通过首先投入固定的股份来自由地这样做 在参与网络期间。用户决定质押金额的持续时间。 一旦被接受,股份就无法恢复。主要目标是确保节点充分共享 网络的基本稳定视图相同。我们预计将最小 staking 时间设置为 一周。 250 与其他也提出 PoS 机制的系统不同,$AVAX 不使用削减,并且 因此,当 staking 期限到期时,所有赌注都会退还。这可以防止出现不必要的情况,例如 客户端软件或硬件故障导致硬币丢失。这与我们的设计理念相吻合 构建可预测技术:即使存在软件或,所抵押的 token 也不会面临风险。 硬件缺陷。 255 在 Avalanche 中,想要参与的节点向 validator 链发出特殊的权益交易。 质押交易指定质押金额、参与者的 staking 密钥(即 staking)、持续时间、 以及验证开始的时间。一旦交易被接受,资金将被锁定,直到 staking 期间结束。最小允许金额由系统决定并强制执行。股份 参与者投入的金额会影响参与者在市场中的影响力Avalanche 平台 2020/06/30 9 共识过程以及奖励,稍后讨论。指定的 staking 持续时间必须介于 δmin 和 δmax,可以锁定任何权益的最小和最大时间范围。与 staking 金额,staking 期间也对系统中的奖励有影响。丢失或被盗 staking 密钥不会导致资产丢失,因为 staking 密钥仅用于共识过程,不用于资产 转移。 265 3.4 $AVAX 中的智能合约 发布时,Avalanche 通过 Ethereum 虚拟机 (EVM) 支持标准的基于 Solidity 的 smart contract。我们预计该平台将支持更丰富、更强大的 smart contract 集 工具,包括: – 具有链下执行和链上验证的智能合约。 270 – 并行执行的智能合约。任何不在相同状态下运行的 smart contract Avalanche 中的任何子网都能够并行执行。 – 改进的 Solidity,称为 Solidity++。这种新语言将支持版本控制、安全数学 定点算术、改进的类型系统、LLVM 编译以及即时执行。 如果开发人员需要 EVM 支持,但想要在私有子网中部署 smart contract,他们 275 可以直接启动一个新的子网。这就是 Avalanche 通过以下方式实现特定于功能的分片的方式: 子网。此外,如果开发人员需要与当前部署的 Ethereum 智能交互 合约,它们可以与 Athereum 子网交互,该子网是 Ethereum 的勺子。最后,如果开发者 需要与 Ethereum 虚拟机不同的执行环境,他们可以选择部署 它们的 smart contract 通过实现不同执行环境(例如 DAML)的子网 280 或 WASM。子网可以支持 VM 行为之外的其他功能。例如,子网可以强制 较大的 validator 节点在较长时间内保存 smart contracts 的性能要求,或者 validator 私下持有合约状态。 4 治理和 $AVAX 代币 4.1 $AVAX 原生代币 第285章 货币政策 原生 token,$AVAX,是有供应上限的,上限设置为 720, 000, 000 tokens, 主网启动时可使用 360, 000, 000 token。然而,与其他上限供应 token 不同的是 永久提高铸币率,\(AVAX is designed to react to changing economic conditions. In particular, the objective of \)AVAX 的货币政策是平衡用户质押 token 的激励 与使用它与平台上提供的各种服务进行交互。平台参与者 290 共同充当分散的储备银行。 Avalanche 上可用的杠杆有 staking 奖励、费用、 和空投,所有这些都受到可控参数的影响。质押奖励由链上治理设定,并由旨在永不超过上限供应的函数控制。可以诱导质押 通过增加费用或增加 staking 奖励。另一方面,我们可以提高参与度 通过降低费用和减少 staking 奖励来使用 Avalanche 平台服务。10 凯文·塞克尼奇、丹尼尔·莱恩、斯蒂芬·布托夫和艾敏·古恩·西雷尔 用途 支付 真正的去中心化点对点支付对于该行业来说在很大程度上是一个未实现的梦想,因为 当前任职者缺乏绩效。 $AVAX 与使用支付方式一样强大且易于使用 Visa,以完全去信任、去中心化的方式每秒允许全球数千笔交易。 此外,对于世界各地的商家来说,$AVAX 提供了比 Visa 更直接的价值主张,即更低的价格 300 费用。 质押:保护系统在 Avalanche 平台上,女巫控制是通过 staking 实现的。按顺序 为了验证,参与者必须锁定代币或质押。验证者,有时称为质押者,是 根据 staking 金额和 staking 持续时间等对验证服务进行补偿 属性。所选择的补偿函数应该最小化方差,确保大的利益相关者不会 305 不成比例地获得更多补偿。参与者也不受任何“运气”因素的影响,如 工作量证明挖矿。这样的奖励计划也会阻止挖矿或 staking 池的形成,从而真正实现 去中心化、无需信任的网络参与。 原子交换 除了提供系统的核心安全性之外,$AVAX token 还充当通用单元 的交换。从那时起,Avalanche 平台将能够原生支持无需信任的原子交换 310 该平台可直接在 Avalanche 上进行任何类型资产的本地、真正去中心化交易。 4.2 治理 治理对于任何平台的开发和采用都至关重要,因为与所有其他类型一样 系统 - Avalanche 也将面临自然演变和更新。 $AVAX 提供链上治理 对于网络的关键参数,参与者可以对网络的更改进行投票,并且 315 以民主方式解决网络升级决策。这包括诸如最小 staking 金额等因素, 铸币率以及其他经济参数。这使得平台能够通过人群oracle有效地执行动态参数优化。然而,与其他一些治理平台不同 在那里,Avalanche 不允许对系统的任意方面进行无限制的更改。相反,只有一个 可以通过治理修改预先确定的参数数量,从而使系统更具可预测性 320 并提高安全性。此外,所有可控制的参数都受到特定时间范围内的限制, 引入滞后现象,并确保系统在短时间内保持可预测性。 对于没有托管人的去中心化系统来说,寻找全球可接受的系统参数值的可行过程至关重要。 Avalanche 可以利用其共识机制来构建一个系统,允许 任何人都可以提出特殊交易,这些交易本质上是全系统民意调查。任何参与节点都可以 325 提出此类建议。 名义奖励率是影响任何货币(无论是数字货币还是法定货币)的重要参数。不幸的是,修复此参数的加密货币可能会面临各种问题,包括通货紧缩或通货膨胀。 为此,名义奖励率在预先设定的范围内受到治理。这将 允许 token 持有者选择 $AVAX 最终是上限、无上限,还是通货紧缩。Avalanche 平台 2020/06/30 11 交易费用(用 F 组表示)也受到治理。 F 实际上是一个元组,描述了与各种指令和交易相关的费用。最后,staking 次和金额 也是可以治理的。这些参数的列表在图 1 中定义。 – Δ:质押金额,以 $AVAX 计价。该值定义了需要放置的最小赌注 参与系统之前先绑定。 – δmin :节点投入系统所需的最短时间。 – δmax :节点可以质押的最长时间。 – ρ : (πΔ, τδmin) →R : 奖励率函数,也称为铸币率,决定奖励 a 给定一定数量的 π 公开披露的节点,参与者可以根据其 staking 金额进行索赔 在其所有权下,在 τ 个连续 δmin 时间范围内,使得 τδmin ≤δmax。 – F :费用结构,是一组可管理的费用参数,指定各种交易的成本。 图 1. Avalanche 中使用的关键非共识参数。所有符号在首次使用时都会重新定义。 根据金融系统的可预测性原则,$AVAX 的治理具有滞后性, 这意味着参数的更改高度依赖于它们最近的更改。有两个限制 第335章 与每个可控制参数相关:时间和范围。使用治理更改参数后 交易后,立即再次进行大量更改变得非常困难。这些困难 自上次更改以来,随着时间的推移,价值约束会放松。总的来说,这可以防止系统 在短时间内发生巨大变化,使用户能够安全地预测系统参数 短期内具有较强的控制力和灵活性,长期内则具有较强的控制力和灵活性。 340
Tata Kelola
1.1 Avalanche Tujuan dan Prinsip Avalanche adalah platform blockchain yang berkinerja tinggi, dapat diskalakan, dapat disesuaikan, dan aman. Ini menargetkan tiga kasus penggunaan yang luas: 15 – Membangun blockchain khusus aplikasi, mencakup izin (pribadi) dan tanpa izin (publik) penerapan. – Membangun dan meluncurkan aplikasi yang sangat skalabel dan terdesentralisasi (Dapps). – Membangun aset digital yang kompleks secara sewenang-wenang dengan aturan khusus, perjanjian, dan pengendara (aset pintar). 1 Pernyataan berwawasan ke depan umumnya berhubungan dengan kejadian di masa depan atau kinerja kami di masa depan. Ini termasuk, namun tidak terbatas pada, proyeksi kinerja Avalanche; perkembangan bisnis dan proyek yang diharapkan; eksekusi mengenai visi dan strategi pertumbuhannya; dan penyelesaian proyek yang sedang berjalan, dalam pengembangan atau sebaliknya sedang dipertimbangkan. Pernyataan berwawasan ke depan mewakili keyakinan dan asumsi manajemen kami hanya pada tanggal presentasi ini. Pernyataan-pernyataan ini bukan merupakan jaminan kinerja di masa depan dan tidak semestinya ketergantungan tidak boleh ditempatkan pada mereka. Pernyataan-pernyataan berwawasan ke depan tersebut tentu saja melibatkan hal-hal yang diketahui dan tidak diketahui risiko, yang dapat menyebabkan kinerja aktual dan hasil pada periode mendatang berbeda secara material dari proyeksi tersurat maupun tersirat di sini. Avalanche tidak berkewajiban memperbarui pernyataan berwawasan ke depan. Meskipun pernyataan berwawasan ke depan adalah prediksi terbaik kami pada saat dibuat, tidak ada jaminan bahwa hal tersebut akan terjadi akan terbukti akurat, karena hasil aktual dan kejadian di masa depan dapat berbeda secara signifikan. Pembaca diperingatkan untuk tidak melakukannya untuk menempatkan ketergantungan yang tidak semestinya pada pernyataan berwawasan ke depan.2 Kevin Sekniqi, Daniel Laine, Stephen Buttolph, dan Emin G¨un Sirer Tujuan utama dari Avalanche adalah untuk menyediakan platform pemersatu untuk penciptaan, transfer, dan perdagangan 20 aset digital. Berdasarkan konstruksi, Avalanche memiliki properti berikut: Avalanche yang dapat diskalakan dirancang agar dapat diskalakan secara masif, kuat, dan efisien. Mesin konsensus inti mampu mendukung jaringan global yang berpotensi memiliki ratusan juta perangkat yang terhubung ke internet, berdaya rendah dan tinggi, yang beroperasi dengan lancar, dengan latensi rendah, dan transaksi per detik yang sangat tinggi. 25 Aman Avalanche dirancang agar kuat dan mencapai keamanan tinggi. Protokol konsensus klasik adalah dirancang untuk menahan hingga f penyerang, dan gagal total saat berhadapan dengan penyerang berukuran f + 1 atau lebih besar, dan konsensus Nakamoto tidak memberikan keamanan jika 51% penambangnya adalah Bizantium. Sebaliknya, Avalanche memberikan jaminan keamanan yang sangat kuat ketika penyerang berada di bawah ambang batas tertentu, yang dapat diparametrikan oleh perancang sistem, dan memberikan degradasi yang baik ketika penyerang melampauinya 30 ambang batas ini. Ini dapat menjunjung jaminan keamanan (tetapi bukan keaktifan) bahkan ketika penyerang melebihi 51%. Itu benar sistem tanpa izin pertama yang memberikan jaminan keamanan yang kuat. Avalanche yang terdesentralisasi dirancang untuk memberikan desentralisasi yang belum pernah terjadi sebelumnya. Ini menyiratkan komitmen untuk beberapa implementasi klien dan tidak ada kontrol terpusat dalam bentuk apa pun. Ekosistem dirancang untuk menghindari pembagian antar kelas pengguna dengan kepentingan yang berbeda. Yang terpenting, tidak ada perbedaan antara penambang, 35 pengembang, dan pengguna. $AVAX yang Ramah Pemerintahan dan Demokratis adalah platform yang sangat inklusif, yang memungkinkan siapa saja untuk terhubung dengannya jaringan dan berpartisipasi dalam validasi dan langsung dalam tata kelola. Pemegang token mana pun dapat memberikan suaranya memilih parameter keuangan utama dan dalam memilih bagaimana sistem berkembang. Dapat Dioperasikan dan Fleksibel Avalanche dirancang untuk menjadi infrastruktur universal dan fleksibel untuk banyak orang 40 dari blockchains/assets, dengan basis $AVAX digunakan untuk keamanan dan sebagai unit hitung untuk pertukaran. Itu sistem ini dimaksudkan untuk mendukung, dengan cara yang netral nilai, banyak blockchain yang akan dibangun di atasnya. Platformnya dirancang dari awal untuk memudahkan porting blockchain yang ada ke dalamnya, untuk mengimpor saldo, ke mendukung berbagai bahasa skrip dan mesin virtual, serta mendukung banyak penerapan secara bermakna skenario. 45 Garis Besar Sisa tulisan ini dipecah menjadi empat bagian besar. Bagian 2 menguraikan rincian mesin yang menggerakkan platform. Bagian 3 membahas model arsitektur di balik platform, termasuk subjaringan, mesin virtual, bootstrap, keanggotaan, dan staking. Bagian 4 menjelaskan tata kelola model yang memungkinkan perubahan dinamis pada parameter ekonomi utama. Terakhir, di Bagian 5 mengeksplorasi berbagai hal topik periferal yang menarik, termasuk potensi optimasi, kriptografi pasca-kuantum, dan realistis 50 musuh.
Avalanche Platform 2020/06/30 3 Konvensi Penamaan Nama platformnya adalah Avalanche, dan biasanya disebut sebagai “Avalanche platform”, dan dapat dipertukarkan/identik dengan “jaringan Avalanche”, atau – sederhananya – Avalanche. Basis kode akan dirilis menggunakan tiga pengidentifikasi numerik, diberi label “v.[0-9].[0-9].[0-100]”, di mana angka pertama menunjukkan pelepasan besar, angka kedua menunjukkan pelepasan kecil, dan angka ketiga menunjukkan pelepasan kecil. 55 mengidentifikasi tambalan. Rilis publik pertama, dengan nama kode Avalanche Borealis, adalah v. 1.0.0. token asli platform ini disebut “$AVAX”. Kelompok protokol konsensus yang digunakan oleh platform Avalanche adalah disebut sebagai keluarga Snow*. Ada tiga contoh konkret, yang disebut Avalanche, Snowman, dan sangat dingin.
治理
1.1 Avalanche 目标和原则 Avalanche 是一个高性能、可扩展、可定制且安全的 blockchain 平台。它的目标是三个 广泛的用例: 15 – 构建特定于应用程序的 blockchains,跨越许可(私有)和无需许可(公共) 部署。 – 构建和启动高度可扩展和去中心化的应用程序(Dapps)。 – 使用自定义规则、契约和附加条款构建任意复杂的数字资产(智能资产)。 1 前瞻性陈述通常与未来事件或我们未来的业绩有关。这包括但不包括 仅限于 Avalanche 的预计表现;其业务和项目的预期发展;执行 其愿景和增长战略;以及目前正在进行、开发或完成的项目 否则正在考虑中。前瞻性陈述代表我们管理层的信念和假设 仅截至本演示文稿发布之日。这些陈述不是对未来业绩和不当行为的保证 不应依赖他们。此类前瞻性陈述必然涉及已知和未知 风险,可能导致未来期间的实际业绩和结果与任何预测存在重大差异 此处明示或暗示。 Avalanche 不承担更新前瞻性陈述的义务。虽然 前瞻性陈述是我们做出时的最佳预测,不能保证它们是正确的 将被证明是准确的,因为实际结果和未来事件可能存在重大差异。请读者注意不要 过度依赖前瞻性陈述。2 凯文·塞克尼奇、丹尼尔·莱恩、斯蒂芬·布托夫和艾敏·古恩·西雷尔 Avalanche 的总体目标是为创造、转让和交易提供一个统一的平台 20 数字资产。 通过构造,Avalanche 具有以下属性: 可扩展 Avalanche 被设计为可大规模扩展、稳健且高效。核心共识引擎 能够支持由数亿个连接互联网的低功率和高性能设备组成的全球网络,这些设备可以无缝运行,延迟低,每秒交易量非常高。 25 安全 Avalanche 旨在坚固耐用并实现高安全性。经典的共识协议是 设计用于抵御最多 f 个攻击者,并且在面对大小为 f + 1 的攻击者时完全失败或 更大,当 51% 的矿工是拜占庭矿工时,中本聪共识无法提供安全性。相比之下, 当攻击者低于一定阈值时,Avalanche提供了非常强大的安全保证,这 可以由系统设计者参数化,并且当攻击者超过 30 这个门槛。即使攻击者超过 51%,它也能保证安全(但不能保证活性)。它是 第一个提供如此强大安全保证的免许可系统。 去中心化 Avalanche 旨在提供前所未有的去中心化。这意味着一种承诺 多个客户端实现并且没有任何类型的集中控制。该生态系统旨在避免 具有不同兴趣的用户类别之间的划分。至关重要的是,矿工之间没有区别, 35 开发者、用户。 治理和民主 $AVAX 是一个高度包容的平台,任何人都可以连接到它 网络并参与验证和第一手治理。任何 token 持有者都可以投票 选择关键财务参数并选择系统如何发展。 可互操作且灵活 Avalanche 旨在成为适用于众多用户的通用且灵活的基础设施 40 blockchains/assets,其中基础 $AVAX 用于安全性并作为交换的记账单位。的 系统旨在以价值中立的方式支持在其上构建的许多 blockchain。平台 是从头开始设计的,以便可以轻松地将现有的 blockchain 移植到其上,导入余额, 支持多种脚本语言和虚拟机,并有意义地支持多种部署 场景。 45 概述 本文的其余部分分为四个主要部分。第 2 节概述了详细信息 为平台提供动力的引擎。第 3 节讨论平台背后的架构模型,包括 子网、虚拟机、引导、成员资格和 staking。第 4 节解释治理 能够动态改变关键经济参数的模型。最后,第 5 节探讨了各种 感兴趣的外围主题,包括潜在的优化、后量子密码学和现实的 50 对手。
Avalanche 平台 2020/06/30 3 命名约定 平台名称为 Avalanche,通常称为“Avalanche” 平台”,并且与“Avalanche 网络”可互换/同义,或者 – 简单地 – Avalanche。 代码库将使用三个数字标识符发布,标记为“v.[0-9].[0-9].[0-100]”,其中 第一个数字表示主要版本,第二个数字表示次要版本,第三个数字表示 55 识别补丁。第一个公开版本的版本号为 Avalanche Borealis,版本为 v.1.0.0。本地 token 该平台的名称为“$AVAX”。 Avalanche 平台使用的共识协议系列是 被称为 Snow* 家族。共有三个具体实例,分别称为 Avalanche、Snowman 和 冷淡的。
Diskusi
5.1 Pengoptimalan Pemangkasan Banyak platform blockchain, terutama yang menerapkan konsensus Nakamoto seperti Bitcoin, menderita pertumbuhan negara yang terus-menerus. Ini karena – berdasarkan protokol – mereka harus menyimpan seluruh riwayat transaksi. Namun, agar blockchain dapat tumbuh secara berkelanjutan, ia harus mampu memangkas sejarah lama. 345 Hal ini sangat penting terutama untuk blockchain yang mendukung kinerja tinggi, seperti Avalanche. Pemangkasan mudah dilakukan di keluarga Snow*. Berbeda dengan Bitcoin (dan protokol serupa), yang tidak melakukan pemangkasan mungkin sesuai persyaratan algoritmik, di $AVAX node tidak perlu memelihara bagian DAG itu mendalam dan berkomitmen tinggi. Node-node ini tidak perlu membuktikan riwayat masa lalu apa pun untuk bootstrapping baru node, dan oleh karena itu hanya perlu menyimpan status aktif, yaitu saldo saat ini, serta tidak terikat 350 transaksi. Jenis Klien Avalanche dapat mendukung tiga jenis klien yang berbeda: arsip, penuh, dan ringan. Arsip node menyimpan seluruh riwayat subnet $AVAX, subnet staking, dan subnet smart contract, semuanya12 Kevin Sekniqi, Daniel Laine, Stephen Buttolph, dan Emin G¨un Sirer cara untuk genesis, artinya node ini berfungsi sebagai node bootstrapping untuk node baru yang masuk. Selain itu node ini dapat menyimpan riwayat lengkap subnet lain yang mereka pilih sebagai validators. Arsip 355 node biasanya merupakan mesin dengan kemampuan penyimpanan tinggi yang dibayar oleh node lain saat mengunduh negara bagian lama. Node penuh, di sisi lain, berpartisipasi dalam validasi, tetapi alih-alih menyimpan seluruh riwayat, mereka malah berpartisipasi cukup simpan status aktif (mis. set UTXO saat ini). Terakhir, bagi mereka yang hanya perlu berinteraksi dengan aman dengan jaringan yang menggunakan sumber daya paling sedikit, Avalanche mendukung klien ringan yang bisa membuktikan bahwa beberapa transaksi telah dilakukan tanpa perlu mengunduh atau menyinkronkan riwayat. Ringan 360 klien terlibat dalam fase pengambilan sampel berulang dari protokol untuk memastikan komitmen yang aman dan jaringan yang luas konsensus. Oleh karena itu, klien ringan di Avalanche memberikan jaminan keamanan yang sama seperti node penuh. Sharding Sharding adalah proses mempartisi berbagai sumber daya sistem untuk meningkatkan kinerja dan mengurangi beban. Ada berbagai jenis mekanisme sharding. Dalam network sharding, kumpulan peserta dibagi menjadi subjaringan terpisah untuk mengurangi beban algoritmik; dalam state sharding, para peserta menyetujuinya 365 menyimpan dan memelihara hanya bagian tertentu dari keseluruhan negara global; terakhir, dalam sharding transaksi, peserta setuju untuk memisahkan pemrosesan transaksi yang masuk. Di Avalanche Borealis, bentuk sharding pertama ada melalui fungsi subjaringan. Untuk Misalnya, seseorang dapat meluncurkan subnet emas dan subnet real estat lainnya. Kedua subnet ini bisa ada seluruhnya paralel. Subnet hanya berinteraksi ketika pengguna ingin membeli kontrak real estat menggunakan kepemilikan emasnya, 370 pada titik mana Avalanche akan mengaktifkan pertukaran atom antara dua subnet. 5.2 Kekhawatiran Kriptografi Pasca Kuantum Kriptografi pasca-kuantum baru-baru ini mendapat perhatian luas karena kemajuan dalam pengembangan komputer kuantum dan algoritma. Kekhawatiran dengan kuantum komputer adalah bahwa mereka dapat merusak beberapa protokol kriptografi yang saat ini digunakan, khususnya digital 375 tanda tangan. Model jaringan Avalanche memungkinkan sejumlah VM, sehingga mendukung ketahanan kuantum mesin virtual dengan mekanisme tanda tangan digital yang sesuai. Kami mengantisipasi beberapa jenis tanda tangan digital skema yang akan diterapkan, termasuk tanda tangan berbasis RLWE yang tahan kuantum. Mekanisme konsensus tidak menganggap kripto berat apa pun untuk operasi intinya. Mengingat desain ini, sangatlah mudah untuk melakukannya memperluas sistem dengan mesin virtual baru yang menyediakan primitif kriptografi aman kuantum. 380 Musuh yang Realistis Makalah Avalanche [6] memberikan jaminan yang sangat kuat dengan adanya musuh yang kuat dan bermusuhan, yang dikenal sebagai musuh yang adaptif dalam model point-to-point penuh. Di istilah lain, musuh memiliki akses penuh ke keadaan setiap node yang benar setiap saat, mengetahui hal tersebut pilihan acak dari semua node yang benar, serta dapat memperbarui statusnya sendiri kapan saja, sebelum dan sesudah node yang benar mempunyai peluang untuk memperbarui statusnya sendiri. Secara efektif, musuh ini sangat kuat, kecuali 385 kemampuan untuk secara langsung memperbarui status node yang benar atau mengubah komunikasi antar node yang benar node. Meskipun demikian, pada kenyataannya, musuh tersebut hanya bersifat teoritis karena implementasi praktis dari hal tersebut musuh terkuat mungkin terbatas pada perkiraan statistik keadaan jaringan. Oleh karena itu, di dalam praktiknya, kami memperkirakan serangan dengan skenario terburuk akan sulit dilakukan.Avalanche Peron 2020/06/30 13 Inklusi dan Kesetaraan Masalah umum dalam mata uang tanpa izin adalah masalah “menjadi kaya 390 lebih kaya”. Hal ini merupakan kekhawatiran yang sahih, karena sistem PoS yang diterapkan secara tidak benar justru dapat memungkinkan terjadinya hal tersebut peningkatan kekayaan secara tidak proporsional dikaitkan dengan pemegang saham yang sudah besar dalam sistem. SEBUAH Contoh sederhananya adalah protokol konsensus berbasis pemimpin, dimana subkomite atau pemimpin ditunjuk mengumpulkan semua hadiah selama operasinya, dan di mana kemungkinan terpilih untuk mengumpulkan hadiah berada sebanding dengan taruhannya, menghasilkan efek gabungan imbalan yang kuat. Selanjutnya, dalam sistem seperti Bitcoin, 395 ada fenomena “besar menjadi lebih besar” di mana penambang besar menikmati keuntungan lebih dibandingkan penambang kecil lebih sedikit anak yatim piatu dan lebih sedikit pekerjaan yang hilang. Sebaliknya, Avalanche menerapkan distribusi pencetakan uang yang egaliter: setiap peserta dalam protokol staking diberi imbalan secara adil dan proporsional berdasarkan taruhan. Dengan memungkinkan sejumlah besar orang untuk berpartisipasi langsung dalam staking, Avalanche dapat mengakomodasi jutaan orang untuk berpartisipasi secara setara di staking. Jumlah minimum yang diperlukan untuk berpartisipasi dalam 400 protokol akan diperuntukkan bagi tata kelola, namun akan diinisialisasi ke nilai yang rendah untuk mendorong partisipasi yang luas. Hal ini juga berarti bahwa delegasi tidak diharuskan berpartisipasi dengan alokasi yang kecil. 6 Kesimpulan Dalam tulisan ini, kita membahas arsitektur platform Avalanche. Dibandingkan dengan platform lain saat ini, yang menjalankan protokol konsensus gaya klasik dan oleh karena itu pada dasarnya tidak dapat diskalakan, atau digunakan 405 Konsensus gaya Nakamoto yang tidak efisien dan membebankan biaya operasional yang tinggi, Avalanche ringan, cepat, terukur, aman, dan efisien. token asli, yang berfungsi untuk mengamankan jaringan dan membayar berbagai biaya infrastruktur sederhana dan kompatibel. $AVAX memiliki kapasitas melebihi proposal lainnya untuk mencapai tingkat desentralisasi yang lebih tinggi, menahan serangan, dan memperluas skala ke jutaan node tanpa kuorum atau pemilihan komite, dan karenanya tanpa membatasi partisipasi. 410 Selain mesin konsensus, Avalanche berinovasi, dan memperkenalkan hal-hal sederhana namun penting ide dalam manajemen transaksi, tata kelola, dan banyak komponen lainnya yang tidak tersedia di platform lain. Setiap peserta dalam protokol akan memiliki suara dalam mempengaruhi bagaimana protokol berkembang setiap saat, dimungkinkan oleh mekanisme tata kelola yang kuat. Avalanche mendukung kemampuan penyesuaian yang tinggi, memungkinkan plug-and-play hampir instan dengan blockchains yang ada. 415
讨论
5.1 优化 修剪许多 blockchain 平台,特别是那些实施中本聪共识的平台,例如 Bitcoin, 遭受永久的国家增长。这是因为——按照协议——他们必须存储整个历史记录 交易。然而,为了让 blockchain 可持续发展,它必须能够修剪旧历史。 第345章 这对于支持高性能的 blockchain 尤为重要,例如 Avalanche。 Snow* 家族的修剪很简单。与 Bitcoin (和类似协议)不同,其中不进行修剪 根据算法要求,$AVAX 中的节点不需要维护 DAG 的部分内容 深刻且高度投入。这些节点不需要向新的引导证明任何过去的历史 节点,因此只需存储活动状态,即当前余额以及未提交的余额 350 交易。 客户端类型 Avalanche 可以支持三种不同类型的客户端:存档、完整和轻型。档案 节点存储 $AVAX 子网、staking 子网和 smart contract 子网的整个历史记录,所有12 凯文·塞克尼奇、丹尼尔·莱恩、斯蒂芬·布托夫和艾敏·古恩·西雷尔 创世之路,这意味着这些节点充当新传入节点的引导节点。另外 这些节点可以存储它们选择为 validator 的其他子网的完整历史记录。档案 第355章 节点通常是具有高存储能力的机器,在下载时由其他节点付费 旧状态。另一方面,完整节点参与验证,但它们不是存储所有历史记录,而是 只需存储活动状态(例如当前的 UTXO 设置)。最后,对于那些只需要安全交互的人 在网络使用最少资源的情况下,Avalanche 支持轻客户端,可以 证明某些事务已提交,无需下载或同步历史记录。光 360 客户参与协议的重复采样阶段,以确保安全承诺和网络范围 共识。因此,Avalanche中的轻客户端提供与全节点相同的安全保证。 分片 分片是对各种系统资源进行分区以提高性能的过程 并减少负载。分片机制有多种类型。在网络分片中,参与者的集合 分为单独的子网以减少算法负载;在状态分片中,参与者同意 365 仅存储和维护整个全局状态的特定子部分;最后,在交易分片中, 参与者同意分开处理传入的交易。 在 Avalanche Borealis 中,第一种分片形式通过子网功能存在。对于 例如,可以启动一个黄金子网和另一个房地产子网。这两个子网可以完全存在于 平行。仅当用户希望使用其持有的黄金购买房地产合约时,子网才会进行交互, 370 此时 Avalanche 将启用两个子网之间的原子交换。 5.2 担忧 后量子密码学 后量子密码学最近受到广泛关注 由于量子计算机和算法的发展取得了进步。对量子的担忧 计算机的最大优势在于它们可以破解一些当前部署的加密协议,特别是数字协议 第375章 签名。 Avalanche 网络模型支持任意数量的虚拟机,因此它支持抗量子 具有合适的数字签名机制的虚拟机。我们预计有几种类型的数字签名 要部署的方案,包括基于 RLWE 的抗量子签名。共识机制 其核心操作不采用任何类型的重型加密。鉴于这种设计,很容易 使用提供量子安全加密原语的新虚拟机扩展系统。 380 现实的对手 Avalanche 论文 [6] 在存在的情况下提供了非常有力的保证 强大而敌对的对手,在完整的点对点模型中被称为回合自适应对手。在 换句话说,对手可以随时完全访问每个正确节点的状态,知道 随机选择所有正确的节点,并且可以在节点之前和之后随时更新自己的状态 正确的节点有机会更新自己的状态。实际上,这个对手非常强大,除了 第385章 能够直接更新正确节点的状态或修改正确节点之间的通信 节点。尽管如此,实际上,这样的对手纯粹是理论上的,因为实际实施中 最强的可能对手仅限于网络状态的统计近似值。因此,在 在实践中,我们预计最坏情况下的攻击将很难部署。Avalanche 平台 2020/06/30 13 包容与平等 未经许可的货币的一个常见问题是“富人获得” 390 更富有”。这是一个合理的担忧,因为实施不当的 PoS 系统实际上可能会允许 财富的创造不成比例地归因于系统中已经很大的股份持有者。一个 简单的例子是基于领导者的共识协议,其中小组委员会或指定的领导者 收集其运行过程中的所有奖励,其中被选择收集奖励的概率为 与股份成正比,产生强大的回报复利效应。此外,在诸如 Bitcoin 之类的系统中, 第395章 存在一种“大变大”的现象,即大型矿商比小型矿商享有溢价 减少孤儿和失业的情况。相比之下,Avalanche 采用平等主义的铸币分配: staking 协议中的每个参与者都会根据权益获得公平且按比例的奖励。 通过让大量人员直接参与 staking,Avalanche 可以容纳 数百万人平等参与 staking。参与活动所需的最低金额 400 协议将用于治理,但它将被初始化为较低的值以鼓励广泛参与。 这也意味着代表团不需要以小额分配参与。 6 结论 在本文中,我们讨论了 Avalanche 平台的架构。与当今其他平台相比, 要么运行经典风格的共识协议,因此本质上是不可扩展的,要么利用 405 中本聪式的共识效率低下,运营成本高,Avalanche 是轻量级的, 快速、可扩展、安全且高效。本机 token,用于保护网络并支付费用 各种基础设施成本简单且向后兼容。 $AVAX 的容量超出其他提案 实现更高水平的去中心化、抵抗攻击并在没有法定人数的情况下扩展到数百万个节点 或委员会选举,因此对参与没有任何限制。 410 除了共识引擎之外,Avalanche 对堆栈进行了创新,并引入了简单但重要的 交易管理、治理以及许多其他平台上不可用的其他组件的想法。协议中的每个参与者都可以随时影响协议的发展, 强大的治理机制使之成为可能。 Avalanche 支持高度可定制性,允许 与现有的 blockchain 几乎即时即插即用。 第415章