
Chainlink:去中心化的预言机网络
Abstrak
Dalam whitepaper ini, kami mengartikulasikan visi evolusi Chainlink melampaui konsep awalnya dalam whitepaper Chainlink asli. Kami meramalkan peran yang semakin luas untuk jaringan oracle, yang mana jaringan tersebut melengkapi dan meningkatkan blockchain yang sudah ada dan yang baru dengan menyediakan layanan yang cepat, andal, dan konektivitas universal yang menjaga kerahasiaan dan komputasi off-chain untuk smart contractdtk. Landasan rencana kami adalah apa yang kami sebut Jaringan Oracle Terdesentralisasi, atau DONs singkatnya. DON adalah jaringan yang dikelola oleh komite Chainlink node. Ini mendukung berbagai fungsi oracle yang tidak terbatas yang dipilih penyebaran oleh panitia. Dengan demikian, DON bertindak sebagai lapisan abstraksi yang kuat, menawarkan antarmuka untuk smart contracts ke sumber daya off-chain yang luas dan sangat sumber daya komputasi off-chain yang efisien namun terdesentralisasi dalam DON itu sendiri. Dengan DONs sebagai batu loncatan, Chainlink berencana untuk fokus pada kemajuan dalam tujuh bidang utama: • Hybrid smart contracts: Menawarkan kerangka kerja umum yang kuat untuk meningkatkan kemampuan smart contract yang ada dengan menyusun on-chain secara aman dan sumber daya komputasi off-chain menjadi apa yang kami sebut hybrid smart contracts. • Mengabstraksi kompleksitas: Menghadirkan pengembang dan pengguna dengan sederhana fungsionalitas menghilangkan kebutuhan untuk memahami hal-hal mendasar yang kompleks protokol dan batasan sistem. • Penskalaan: Memastikan bahwa layanan oracle mencapai latensi dan throughput dituntut oleh sistem desentralisasi yang berkinerja tinggi. • Kerahasiaan: Memungkinkan sistem generasi berikutnya yang menggabungkan blockchains' transparansi bawaan dengan perlindungan kerahasiaan baru yang kuat untuk sensitif data. • Kewajaran pesanan untuk transaksi: Mendukung pengurutan transaksi dengan berbagai cara yang adil bagi pengguna akhir dan mencegah serangan front-running dan lainnya bot dan penambang eksploitatif. • Minimalkan kepercayaan: Menciptakan lapisan dukungan yang sangat dapat dipercaya smart contracts dan sistem lain yang bergantung pada oracle melalui desentralisasi, penahan yang kuat pada blockchains dengan keamanan tinggi, kriptografi teknik, dan jaminan kriptoekonomi. • Keamanan berbasis insentif (kriptoekonomi): Merancang secara ketat dan menerapkan mekanisme yang kuat untuk memastikan node di DONs memiliki insentif ekonomi yang kuat untuk berperilaku andal dan benar, bahkan dalam menghadapi musuh yang mempunyai sumber daya yang baik. Kami menyajikan inovasi awal dan berkelanjutan dari komunitas Chainlink di masing-masing bidang tersebut, memberikan gambaran mengenai perluasan dan peningkatannya kemampuan canggih yang direncanakan untuk jaringan Chainlink.
摘要
在本白皮书中,我们阐述了 Chainlink 的演变愿景,超越了原始 Chainlink 白皮书中的最初构想。 我们预见 oracle 网络的作用日益扩大,通过提供快速、可靠和可靠的服务来补充和增强现有和新的 blockchain 保密性通用连接和链外计算 smart contracts。 我们计划的基础是我们所说的去中心化预言机网络,或者 简称 DONs。 DON 是由 Chainlink 委员会维护的网络 节点。 它支持任何无限范围的 oracle 函数选择 由委员会部署。因此 DON 充当强大的抽象层, 为 smart contract 提供广泛的链下资源和高度的接口 DON 本身内高效且去中心化的链外计算资源。 以 DONs 作为跳板,Chainlink 计划重点关注七个方面的进展 关键领域: • 混合smart contracts:提供一个强大的通用框架,通过安全地在链上组合来增强现有的smart contract功能 和链下计算资源进入我们所说的混合smart contract。 • 抽象化复杂性:向开发人员和用户提供简单的 功能消除了熟悉复杂底层的需要 协议和系统边界。 • 扩展:确保oracle 服务实现延迟和吞吐量 高性能去中心化系统的需求。 • 保密性:支持结合blockchains’的下一代系统 与生俱来的透明度,为敏感信息提供强大的新保密保护 数据。 • 交易的顺序公平性:以多种方式支持交易排序 这对最终用户来说是公平的,并防止抢先交易和其他攻击 机器人和剥削性矿工。 • 信任最小化:创建高度值得信赖的支持层 smart contracts 和其他 oracle 依赖系统,通过去中心化、强锚定于高安全性 blockchains、加密 技术和加密经济保证。 • 基于激励的(加密经济)安全性:严格设计和稳健部署机制,确保 DON 中的节点具有强大的经济激励,即使面对资源充足的对手,也能可靠、正确地行事。 我们展示 Chainlink 社区的初步和持续创新 在每个领域,提供了一幅不断扩大和日益增长的图景 为 Chainlink 网络规划的强大功能。
Perkenalan
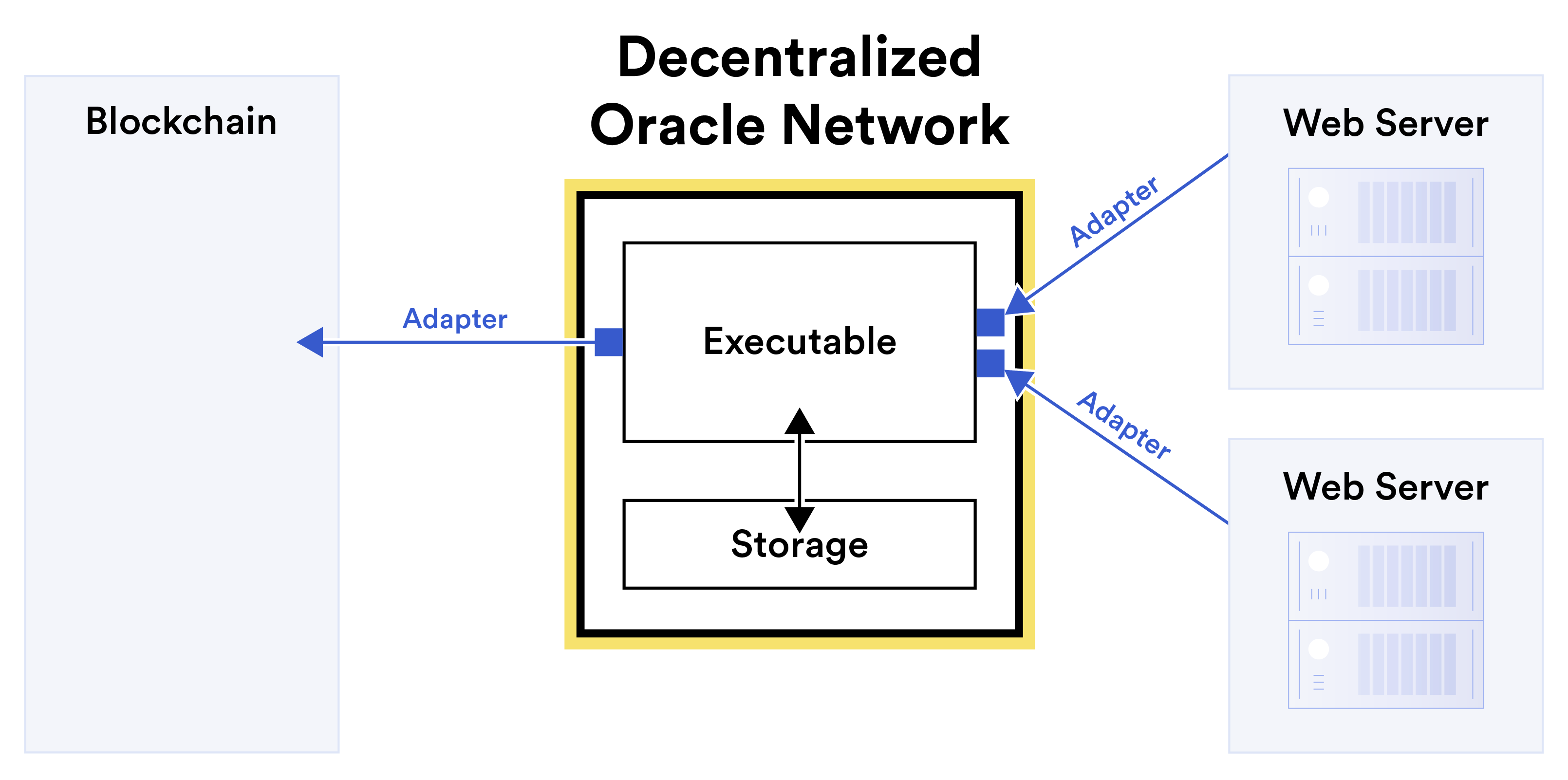
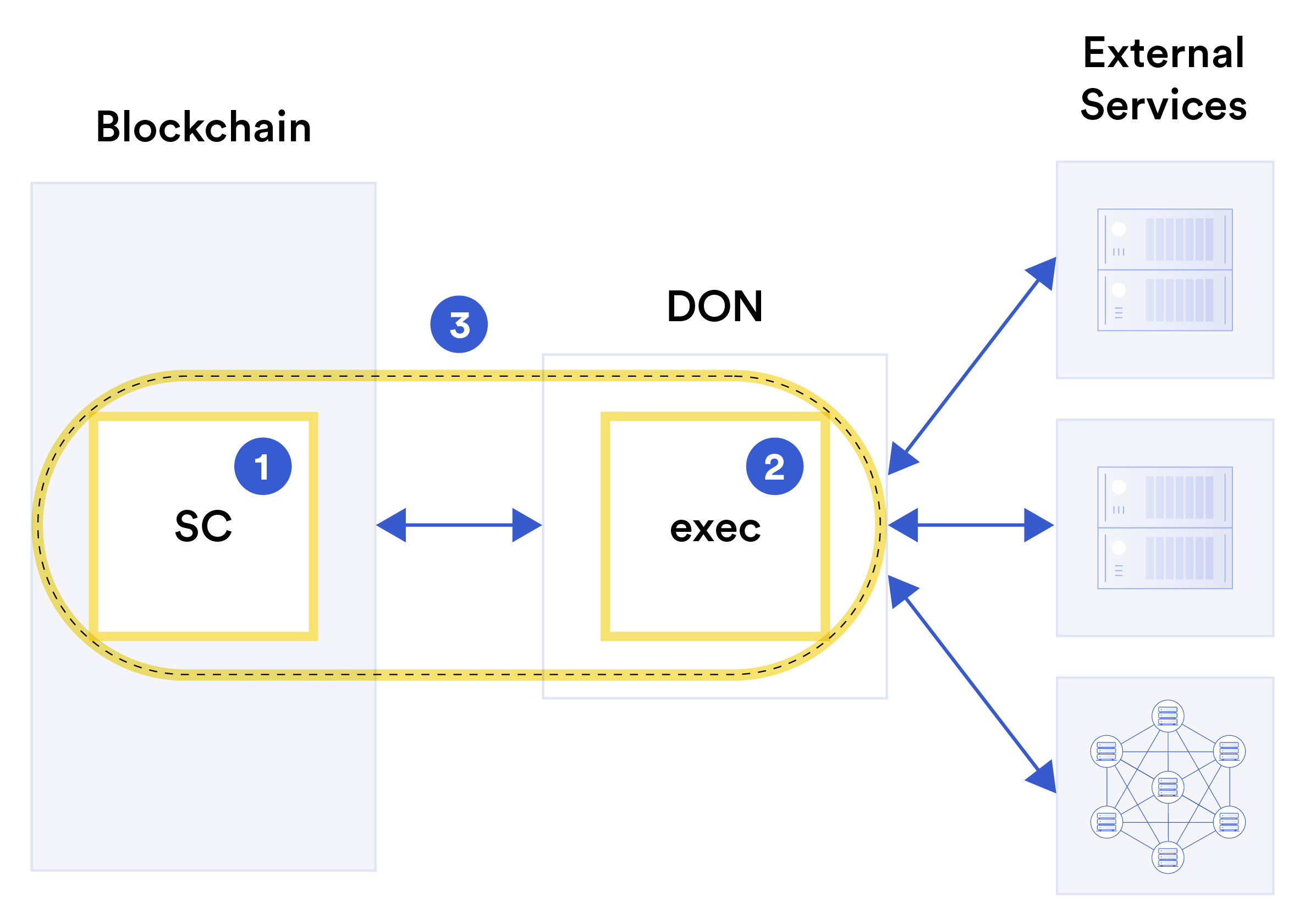
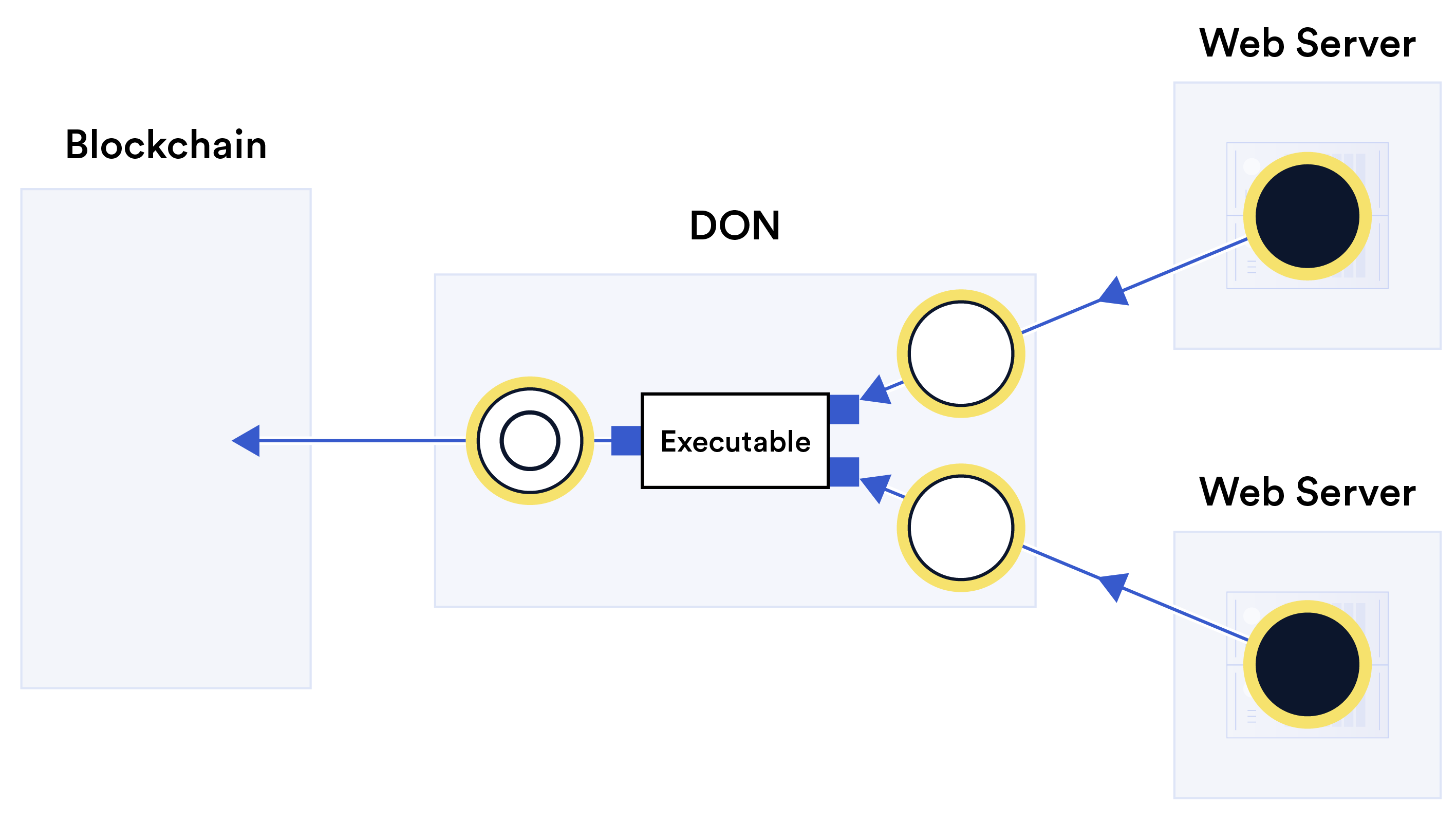
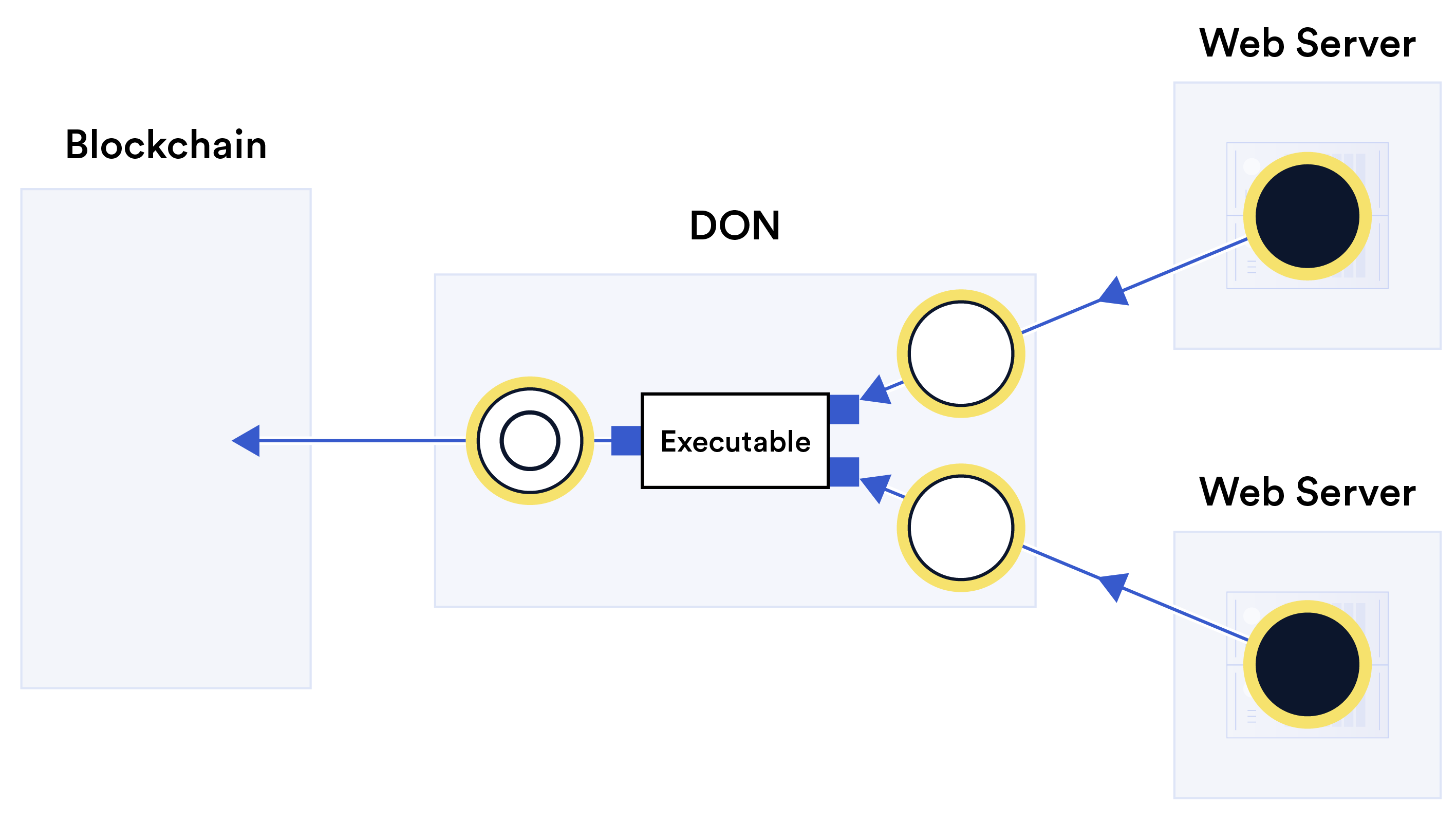
Blockchain oracles saat ini sering dipandang sebagai layanan terdesentralisasi dengan satu tujuan: untuk meneruskan data dari sumber daya off-chain ke blockchains. Namun ini adalah langkah singkat, mulai dari meneruskan data hingga menghitungnya, menyimpannya, atau mengirimkannya secara dua arah. Pengamatan ini membenarkan gagasan yang lebih luas tentang fungsi oracles. Begitu juga memenuhi kebutuhan layanan smart contracts yang semakin meningkat dan semakin beragam teknologi yang mengandalkan jaringan oracle. Singkatnya, oracle bisa dan perlu menjadi antarmuka dengan tujuan umum, dua arah, dan mendukung komputasi antara dan di antara sistem onchain dan off-chain. Peran Oracles dalam ekosistem blockchain adalah untuk meningkatkan kinerja, fungsionalitas, dan interoperabilitas smart contracts sehingga bisa membawa model kepercayaan dan transparansi baru ke berbagai industri. Transformasi ini akan terjadi melalui perluasan penggunaan smart contract hibrida, yang dapat digabungkan properti khusus blockchains dengan kemampuan unik sistem off-chain seperti oracle jaringan dan dengan demikian mencapai jangkauan dan kekuatan yang jauh lebih besar daripada sistem on-chain dalam isolasi. Dalam whitepaper ini, kami mengartikulasikan visi untuk apa yang kami sebut Chainlink 2.0, sebuah evolusi dari Chainlink melampaui konsepsi awalnya dalam whitepaper Chainlink asli [98]. Kami memperkirakan peran jaringan oracle akan semakin besar, salah satunya adalah mereka melengkapi dan menyempurnakan blockchain yang sudah ada dan yang baru dengan menyediakan konektivitas dan komputasi universal yang cepat, andal, dan menjaga kerahasiaan untuk perangkat hybrid smart contracts. Kami percaya bahwa jaringan oracle bahkan akan berkembang menjadi utilitas untuk mengekspor data tingkat blockchain berintegritas tinggi ke sistem di luar blockchain ekosistem. Saat ini, Chainlink node yang dijalankan oleh beragam entitas berkumpul di oracle jaringan untuk menyampaikan data ke smart contracts dalam apa yang dikenal sebagai laporan. Kita bisa melihatnya oracle node sebagai komite serupa dengan konsensus klasik blockchain [72], namun dengan tujuan mendukung blockchain yang sudah ada, dibandingkan menyediakan fungsionalitas yang berdiri sendiri. Dengan fungsi acak yang dapat diverifikasi (VRF) dan Pelaporan Off-Chain (OCR), Chainlink telah berkembang menuju kerangka kerja dan infrastruktur tujuan umum untuk menyediakan sumber daya komputasi yang smart contracts butuhkan untuk fungsionalitas tingkat lanjut. Landasan rencana kami untuk Chainlink 2.0 adalah apa yang kami sebut Oracle Terdesentralisasi Jaringan, atau disingkat DONs. Sejak kami memperkenalkan istilah “oracle jaringan” di whitepaper Chainlink asli [98], oracles telah mengembangkan fungsionalitas yang lebih kaya dan luasnya aplikasi. Dalam makalah ini, kami menawarkan definisi baru tentang istilah menurut untuk visi masa depan kami untuk ekosistem Chainlink. Dalam tampilan ini, DON adalah jaringan dikelola oleh komite yang terdiri dari Chainlink node. Berakar pada protokol konsensus, itu mendukung berbagai fungsi oracle yang tidak terbatas yang dipilih untuk diterapkan oleh panitia. Dengan demikian, DON bertindak sebagai lapisan abstraksi blockchain, menyediakan antarmuka ke sumber daya off-chain untuk smart contracts dan sistem lainnya. Ini juga menyediakan akses ke sumber daya komputasi off-chain yang sangat efisien namun terdesentralisasi. Secara umum, a DON mendukung operasi pada rantai utama. Tujuannya adalah untuk memungkinkan keamanan dan fleksibilitasble hybrid smart contracts, yang menggabungkan komputasi on-chain dan off-chain dengan koneksi ke sumber daya eksternal. Kami menekankan bahwa bahkan dengan penggunaan komite di DONs, Chainlink itu sendiri pada dasarnya tetap tanpa izin. DONs bertindak sebagai fondasi tanpa izin kerangka kerja di mana node dapat bersatu untuk mengimplementasikan jaringan oracle khusus rezim mereka sendiri untuk penyertaan node, yang mungkin diizinkan atau tanpa izin. Dengan DONs sebagai landasan, kami berencana untuk fokus pada Chainlink 2.0 pada kemajuan dalam tujuh area utama: hybrid smart contracts, mengabstraksikan kompleksitas, penskalaan, kerahasiaan, keadilan pesanan untuk transaksi, minimalisasi kepercayaan, dan keamanan berbasis insentif (kriptoekonomi). Dalam pengantar makalah ini, kami menyajikan gambaran umum tentang Desentralisasi Oracle Networks di Bagian 1.1 dan tujuh bidang inovasi utama kami di Bagian 1.2. Kami menjelaskan organisasi sisa makalah ini di Bagian 1.3. 1.1 Jaringan Oracle Terdesentralisasi Jaringan Oracle Terdesentralisasi dirancang untuk meningkatkan dan memperluas kemampuan dari smart contracts pada target blockchain atau rantai utama melalui fungsi yang tidak tersedia secara asli. Mereka melakukannya dengan menyediakan tiga sumber daya dasar yang terdapat di dalamnya sistem komputasi: jaringan, penyimpanan, dan komputasi. DON bertujuan untuk menawarkan sumber daya ini dengan sifat kerahasiaan, integritas, dan ketersediaan yang kuat,1 seperti serta akuntabilitas. DONs dibentuk oleh komite oracle node yang bekerja sama untuk memenuhi tujuan tertentu pekerjaan atau memilih untuk menjalin hubungan jangka panjang untuk memberikan layanan yang gigih kepada klien. DON dirancang dengan cara blockchain-agnostik. Mereka berjanji untuk melayani sebagai alat yang kuat dan fleksibel bagi pengembang aplikasi untuk menciptakan dukungan off-chain smart contracts mereka di rantai utama mana pun yang didukung. Dua jenis fungsi mewujudkan kemampuan DON: executable dan adaptor. Executable adalah program yang berjalan terus menerus dan terdesentralisasi di DON. Meskipun mereka tidak secara langsung menyimpan aset rantai utama, mereka memiliki manfaat penting, termasuk kinerja tinggi dan kemampuan untuk melakukan aktivitas rahasia. komputasi. Executable berjalan secara mandiri pada DON dan bekerja secara deterministik operasi. Mereka bekerja sama dengan adaptor yang menghubungkan DON ke sumber daya eksternal dan dapat dipanggil oleh executable. Adaptor, seperti yang kami bayangkan untuk DONs, adalah a generalisasi adaptor eksternal di Chainlink hari ini. Sementara adaptor yang ada biasanya hanya mengambil data dari sumber data, adaptor dapat beroperasi dua arah; di DONs, mereka juga dapat memanfaatkan komputasi gabungan sebanyak DON node untuk mencapai fitur tambahan, seperti mengenkripsi laporan untuk konsumsi yang menjaga privasi sebuah yang dapat dieksekusi. Untuk memberikan gambaran tentang operasi dasar DON, Gambar 1 menunjukkan secara konseptual bagaimana a DON mungkin digunakan untuk mengirim laporan ke blockchain dan dengan demikian mencapai fungsionalitas oracle tradisional yang sudah ada. DONs dapat memberikan banyak fitur tambahan, namun lebih dari itu 1 “Tiga serangkai CIA” dalam keamanan informasi [123, hal. 26, §2.3.5].jaringan Chainlink yang ada. Misalnya, dalam struktur umum Gambar 1, yang dapat dieksekusi dapat merekam data harga aset yang diambil di DON, menggunakan data tersebut untuk menghitung, misalnya, rata-rata tambahan untuk laporannya. Gambar 1: Gambar konseptual yang menunjukkan contoh bagaimana Jaringan Oracle Terdesentralisasi dapat mewujudkan fungsionalitas dasar oracle, yaitu menyampaikan data off-chain ke kontrak. Sebuah executable menggunakan adaptor untuk mengambil data off-chain, yang digunakan untuk menghitung, mengirimkan output melalui adaptor lain ke target blockchain. (Adaptor dimulai dengan kode di DON, diwakili oleh kotak kecil berwarna biru; panah menunjukkan arah aliran data untuk ini contoh tertentu.) Eksekusi juga dapat membaca dan menulis ke DON lokal penyimpanan untuk menjaga status dan/atau berkomunikasi dengan executable lainnya. Jaringan, komputasi, dan penyimpanan yang fleksibel dalam DONs, semuanya terwakili di sini, memungkinkan sejumlah hal baru aplikasi. Manfaat utama DON adalah kemampuannya untuk mem-bootstrap layanan blockchain baru. DONs adalah sarana dimana jaringan oracle yang ada dapat dengan cepat menjalankan aplikasi layanan yang saat ini memerlukan penciptaan jaringan yang dibangun khusus. Kami memberikan beberapa contoh penerapan tersebut di Bagian 4. Di Bagian 3, kami memberikan detail selengkapnya tentang DONs, yang menjelaskan kemampuannya dari segi antarmuka yang mereka hadirkan untuk pengembang dan pengguna. 1.2 Tujuh Tujuan Desain Utama Di sini kami meninjau secara singkat tujuh fokus utama evolusi yang disebutkan di atas Chainlink, yaitu:Hibrida smart contracts: Inti dari visi kami untuk Chainlink adalah gagasan tentang keamanan menggabungkan komponen on-chain dan off-chain dalam smart contracts. Kami mengacu pada kontrak mewujudkan ide ini sebagai smart contracts hybrid atau kontrak hybrid.2 Blockchain sedang dan akan terus memainkan dua peran penting dalam layanan terdesentralisasi ekosistem: Keduanya merupakan lokasi di mana kepemilikan mata uang kripto terwakili dan landasan yang kuat untuk layanan yang terdesentralisasi. Oleh karena itu, kontrak pintar harus direpresentasikan atau dieksekusi secara berantai, namun kemampuan on-chainnya sangat terbatas. Murni kode kontrak on-chain lambat, mahal, dan sempit, tidak dapat mengambil manfaat dari dunia nyata data dan berbagai fungsi yang secara inheren tidak dapat dicapai dalam rantai, termasuk berbagai bentuk komputasi rahasia, pembuatan keacakan (semu) yang aman terhadap manipulasi penambang / validator, dll. Oleh karena itu, agar smart contracts dapat mewujudkan potensi penuhnya, diperlukan smart contracts untuk dirancang dengan dua bagian: bagian on-chain (yang biasanya kami tunjukkan dengan SC) dan bagian off-chain, yang dapat dieksekusi berjalan pada DON (yang biasanya kami nyatakan dengan eksekutif). Tujuannya adalah untuk mencapai komposisi fungsionalitas on-chain yang aman dengan banyaknya layanan off-chain yang ingin disediakan oleh DONs. Bersama-sama, dua bagian membuat kontrak hibrida. Kami menyajikan ide tersebut secara konseptual pada Gambar 2. Hari ini, Chainlink layanan3 seperti data feed dan VRF diaktifkan jika tidak dapat dicapai smart contract aplikasi, mulai dari DeFi hingga NFT yang dihasilkan secara wajar hingga asuransi yang terdesentralisasi, sebagai langkah pertama menuju kerangka kerja yang lebih umum. Sebagai layanan Chainlink berkembang dan tumbuh lebih berkinerja sesuai dengan visi kami dalam whitepaper ini akankah kekuatan smart contract sistem di seluruh blockchains. Enam fokus utama kami yang lain dalam whitepaper ini dapat dipandang sebagai tindakan dalam layanan yang pertama, mencakup salah satu kontrak hibrida. Fokus ini melibatkan penghapusan yang terlihat kompleksitas dari kontrak hibrid, menciptakan layanan off-chain tambahan yang memungkinkan pembangunan kontrak hibrida yang semakin mumpuni, dan, dalam kasus minimalisasi kepercayaan, memperkuat properti keamanan yang dicapai oleh kontrak hibrida. Kami meninggalkan ide itu kontrak hibrida tersirat di sebagian besar makalah ini, namun kombinasi apa pun darinya Logika MAINCHAIN dengan DON dapat dipandang sebagai kontrak hibrid. Mengabstraksi kompleksitas: DONs dirancang untuk memanfaatkan desentralisasi sistem mudah bagi pengembang dan pengguna dengan mengabstraksikan mesin yang seringkali rumit di balik rangkaian layanan DONs yang kuat dan fleksibel. Layanan Chainlink yang ada sudah memiliki fitur ini. Misalnya, data feed di Chainlink saat ini menyajikan antarmuka onchain yang tidak mengharuskan pengembang untuk memikirkan detail tingkat protokol, seperti cara OCR menerapkan pelaporan konsensus di antara sejumlah perusahaan. 2Ide komposisi kontrak on-chain / off-chain telah muncul sebelumnya dalam berbagai kendala bentuk, misalnya, sistem lapisan-2, blockchains [80] berbasis TEE, dll. Tujuan kami adalah untuk mendukung dan menggeneralisasi pendekatan ini dan memastikan bahwa pendekatan tersebut dapat mencakup akses data off-chain dan oracle penting lainnya layanan. Layanan 3Chainlink terdiri dari berbagai layanan dan fungsi terdesentralisasi yang tersedia melalui jaringan. Mereka ditawarkan oleh banyak operator node yang terdiri dari berbagai jaringan oracle di seluruh ekosistem.Gambar 2: Gambar konseptual yang menggambarkan komposisi kontrak on-chain / off-chain. SEBUAH hybrid smart contract 3⃝terdiri dari dua komponen yang saling melengkapi: on-chain komponen SC 1⃝, berada di blockchain, dan komponen off-chain exec 2⃝yang dijalankan pada DON. DON juga berfungsi sebagai jembatan antara kedua komponen seperti menghubungkan kontrak hybrid dengan sumber daya off-chain seperti layanan web, dan lainnya blockchains, penyimpanan terdesentralisasi, dll. kumpulan node yang terdesentralisasi. DONs melangkah lebih jauh dalam arti memperluas berbagai layanan yang Chainlink dapat menawarkan lapisan abstraksi kepada pengembang menyertai antarmuka yang disederhanakan untuk layanan tingkat tinggi. Kami menyajikan beberapa contoh penerapan di Bagian 4 yang menyoroti pendekatan ini. Kami membayangkan perusahaan, misalnya, menggunakan DONs sebagai bentuk middleware yang aman untuk sambungkan sistem lama mereka ke blockchains. (Lihat Bagian 4.2.) Penggunaan DON ini menghilangkan kompleksitas dinamika blockchain secara umum (biaya, pengaturan ulang, dll.). Itu juga mengabstraksi fitur-fitur blockchain tertentu, sehingga memungkinkan perusahaan untuk menghubungkan sistem mereka yang ada ke rangkaian sistem blockchain yang semakin luas tanpa kebutuhan akan keahlian khusus dalam sistem ini atau, yang lebih umum, dalam pengembangan sistem yang terdesentralisasi. Pada akhirnya, ambisi kami adalah untuk mendorong tingkat abstraksi yang dicapai oleh Chainlink sampai pada penerapan apa yang kami sebut sebagai lapisan meta terdesentralisasi. Lapisan seperti itu akan mengabstraksikan perbedaan on-chain / off-chain untuk semua kelas pengembang dan pengguna DApps, memungkinkan pembuatan dan penggunaan layanan terdesentralisasi dengan lancar.Untuk menyederhanakan proses pengembangan, pengembang dapat menentukan fungsionalitas DApp di metalayer sebagai aplikasi virtual dalam model mesin terpadu. Mereka bisa kemudian gunakan kompiler metalayer terdesentralisasi untuk membuat instance DApp secara otomatis sebagai serangkaian fungsi terdesentralisasi yang saling beroperasi yang mencakup blockchains, DONs, dan layanan eksternal. (Salah satu layanan eksternal ini bisa berupa sistem perusahaan, sehingga metalayer berguna untuk aplikasi yang melibatkan sistem perusahaan lama.) Seperti itu kompilasi mirip dengan kompiler modern dan kit pengembangan perangkat lunak (SDK) mendukung pemrogram generalis dalam menggunakan potensi penuh perangkat keras heterogen arsitektur yang terdiri dari CPU tujuan umum dan perangkat keras khusus seperti GPU, akselerator pembelajaran mesin, atau kantong tepercaya. Gambar 3 menyajikan ide ini pada tingkat konseptual. Hybrid smart contracts adalah langkah pertama menuju visi ini dan konsep yang kami sebut kontrak meta. Kontrak meta adalah aplikasi yang dikodekan secara terdesentralisasi metalayer dan secara implisit mencakup logika on-chain (smart contracts), serta komputasi off-chain dan konektivitas antara berbagai blockchains dan off-chain yang ada layanan. Mengingat kebutuhan akan dukungan bahasa dan kompiler, model keamanan baru, dan harmonisasi konseptual dan teknis dari teknologi yang berbeda, namun, realisasinya dari metalayer terdesentralisasi yang sebenarnya adalah tujuan ambisius yang kami cita-citakan dalam jangka panjang cakrawala waktu. Meskipun demikian, ini merupakan model ideal yang berguna untuk diingat saat membaca makalah ini, tidak dirinci di sini, tetapi sesuatu yang kami rencanakan untuk menjadi fokus dalam pekerjaan kami di masa depan Chainlink. Penskalaan: Tujuan yang sangat penting dalam desain kami yang terus berkembang adalah memungkinkan Jaringan Chainlink untuk memenuhi kebutuhan penskalaan ekosistem blockchain yang terus meningkat. Dengan kemacetan jaringan menjadi masalah berulang dalam izin yang ada blockchains [86], desain blockchain yang baru dan lebih berperforma mulai digunakan, misalnya, [103, 120, 203], serta teknologi penskalaan lapisan-2 yang saling melengkapi, misalnya, [5, 12, 121, 141, 169, 186, 187]. Layanan Oracle harus mencapai latensi dan throughput yang memenuhi tuntutan kinerja sistem ini sekaligus meminimalkan biaya on-chain (misalnya, biaya bahan bakar) untuk operator kontrak dan pengguna biasa. Dengan DONs, Chainlink fungsionalitas bertujuan untuk melangkah lebih jauh dan memberikan kinerja yang cukup tinggi untuk sistem berbasis web murni. DONs memperoleh sebagian besar peningkatan kinerjanya dari penggunaan protokol konsensus yang cepat, berbasis komite, atau tanpa izin, yang digabungkan dengan blockchains mereka mendukung. Kami berharap banyak DON dengan konfigurasi berbeda dijalankan secara paralel; DApps yang berbeda dan pengguna dapat menavigasi trade-off dalam pilihan konsensus yang mendasarinya sesuai dengan persyaratan aplikasi mereka. DONs dapat dianggap sebagai teknologi lapisan-2. Kami mengharapkan itu di antara layanan lainnya, DONs akan mendukung Kerangka Eksekusi Transaksi (TEF), yang memfasilitasi integrasi yang efisien dari DONs dan dengan demikian oracles dengan kinerja tinggi lainnya sistem lapisan-2—misalnya, rollups, sistem yang menggabungkan transaksi secara off-chain untuk mencapai peningkatan kinerja. Kami memperkenalkan TEF di Bagian 6.
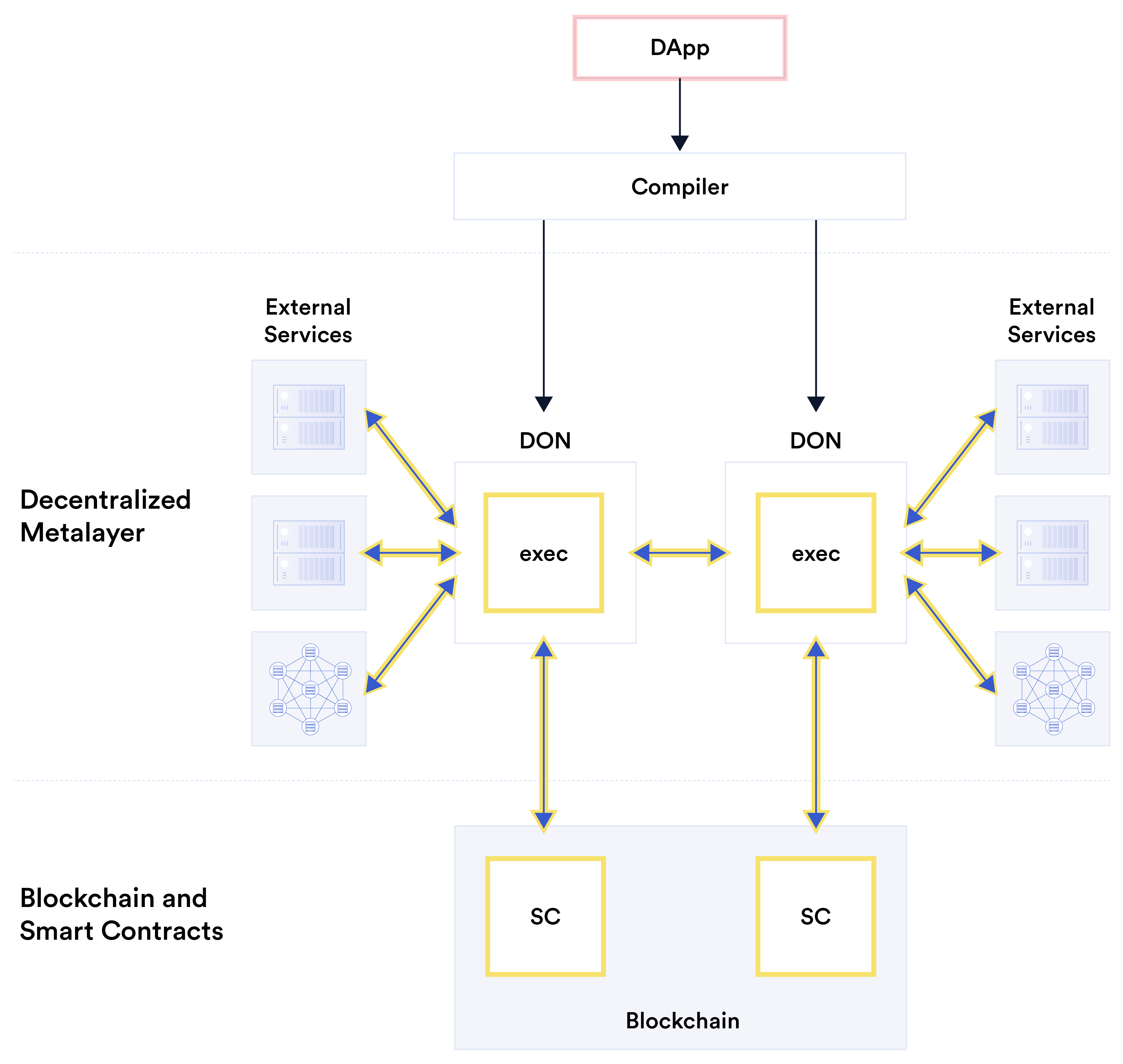
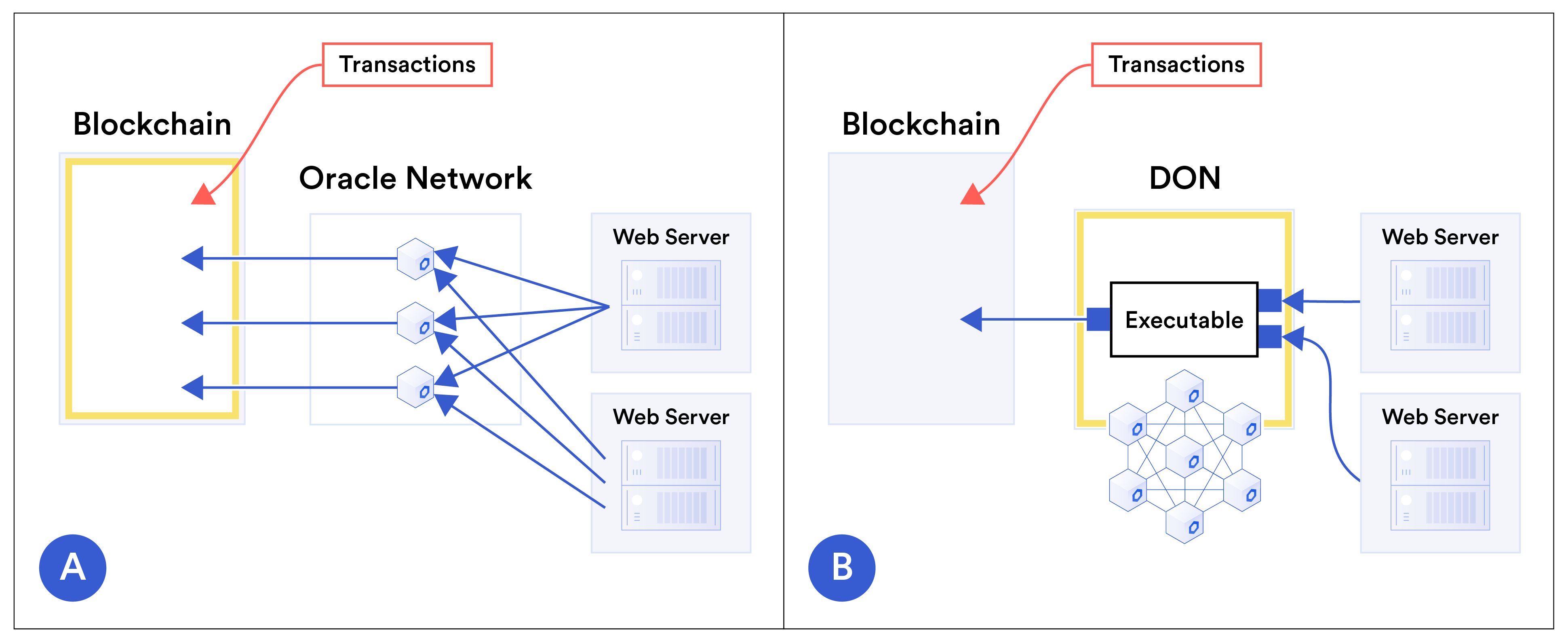
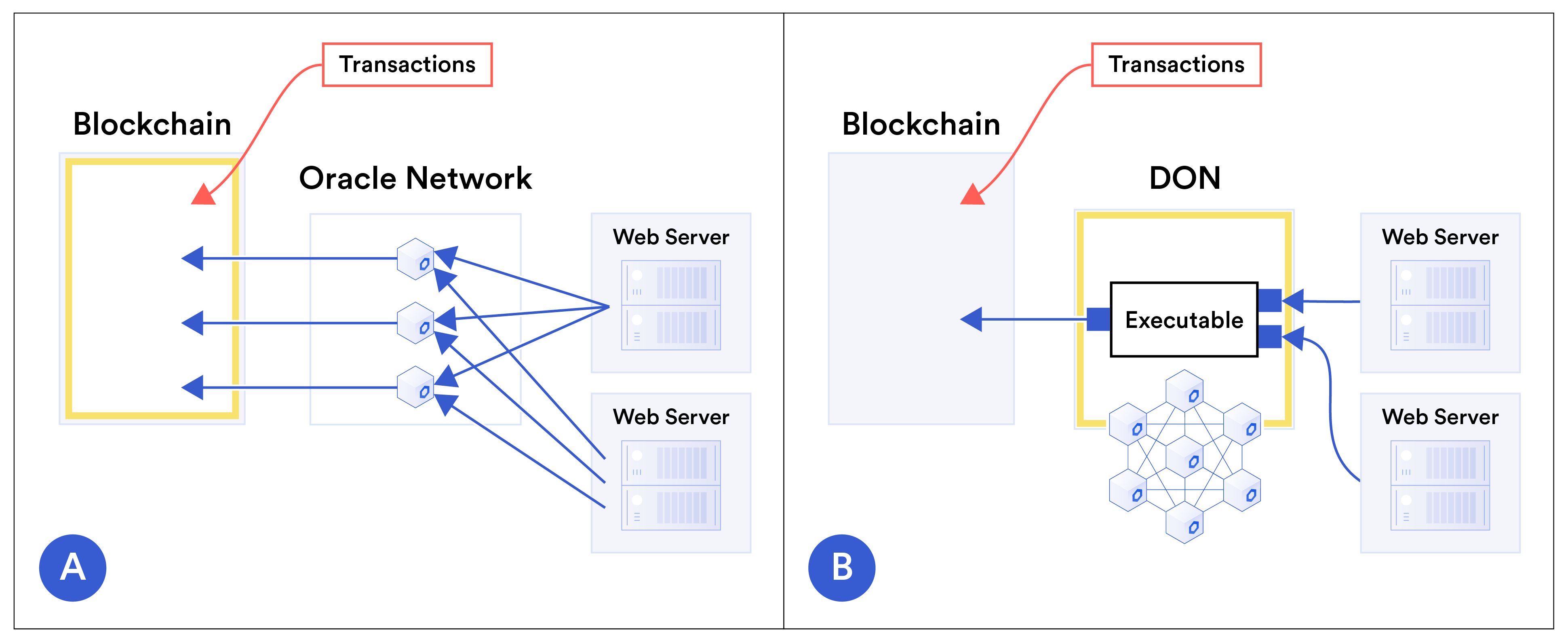
Gambar 3: Gambar konseptual yang menunjukkan realisasi ideal dari lapisan meta yang terdesentralisasi. Untuk kemudahan pengembangan, pengembang menentukan DApp, disorot dalam warna merah muda, sebagai virtual aplikasi dalam model mesin terpadu. Kompiler metalayer terdesentralisasi secara otomatis menghasilkan fungsi interoperasi yang sesuai: smart contracts (dilambangkan oleh SC), logika (dilambangkan dengan exec) pada DONs, adaptor yang terhubung ke layanan eksternal target, dan seterusnya, seperti yang ditunjukkan dalam sorotan kuning. Gambar 4 menunjukkan secara konseptual bagaimana DONs meningkatkan penskalaan blockchain (smart contract) dengan memusatkan transaksi dan oracle-pemrosesan laporan secara off-chain, bukan pada rantai. Pergeseran dalam lokus utama komputasi ini mengurangi latensi transaksi dan biaya sambil meningkatkan throughput transaksi. Kerahasiaan: Blockchain memberikan transparansi yang belum pernah ada sebelumnya untuk smart contracts dan penerapannya. Namun ada ketegangan mendasar antara transparansi dan kerahasiaan. Saat ini, misalnya, pertukaran desentralisasi penggunaGambar 4: Gambar konseptual yang menunjukkan bagaimana Jaringan Oracle Terdesentralisasi meningkatkan penskalaan blockchain yang diaktifkan smart contracts. Gambar A ⃝menunjukkan oracle konvensional arsitektur. Transaksi dikirim langsung ke blockchain, begitu pula laporan oracle. Jadi blockchain yang diberi tanda warna kuning merupakan lokus utama pemrosesan transaksi. Gambar B⃝menunjukkan penggunaan DON untuk mendukung kontrak di blockchain. Sebuah DON transaksi proses yang dapat dieksekusi bersama dengan data dari sistem eksternal dan seterusnya hasil—misalnya, transaksi gabungan atau perubahan status kontrak akibat dampak transaksi—ke blockchain. DON, yang disorot dengan warna kuning, adalah yang utama tempat pemrosesan transaksi. tindakan dicatat secara berantai, sehingga memudahkan untuk memantau perilaku pertukaran, tetapi juga membuat transaksi keuangan pengguna terlihat oleh publik. Demikian pula, data diteruskan ke smart kontrak tetap berantai. Hal ini membuat data tersebut mudah diaudit, namun bertindak sebagai disinsentif bagi penyedia data yang ingin memberikan smart contract dengan informasi sensitif atau data kepemilikan. Kami percaya bahwa jaringan oracle akan memainkan peran penting dalam mengkatalisasi generasi mendatang sistem yang menggabungkan transparansi bawaan blockchains dengan perlindungan kerahasiaan baru. Dalam makalah ini, kami menunjukkan bagaimana mereka akan melakukannya dengan menggunakan tiga pendekatan utama: • Adaptor yang menjaga kerahasiaan: Dua teknologi dengan penerapan terencana di jaringan Chainlink, DECO [234] dan Town Crier [233], aktifkan oracle node untuk mengambil data dari sistem off-chain dengan cara yang melindungi privasi dan data pengguna kerahasiaan. Mereka akan memainkan peran penting dalam desain adaptor untuk DONs. (Lihat Bagian 3.6.2 untuk rincian mengenai kedua teknologi ini.) • Perhitungan rahasia: DONs dapat dengan mudah menyembunyikan perhitungannya agar tidak mengandalkan blockchains. Menggunakan komputasi multi-pihak yang aman dan/atau lingkungan eksekusi tepercaya, kerahasiaan yang lebih kuat juga dimungkinkan di mana DON node menghitung data yang tidak dapat mereka lihat sendiri.
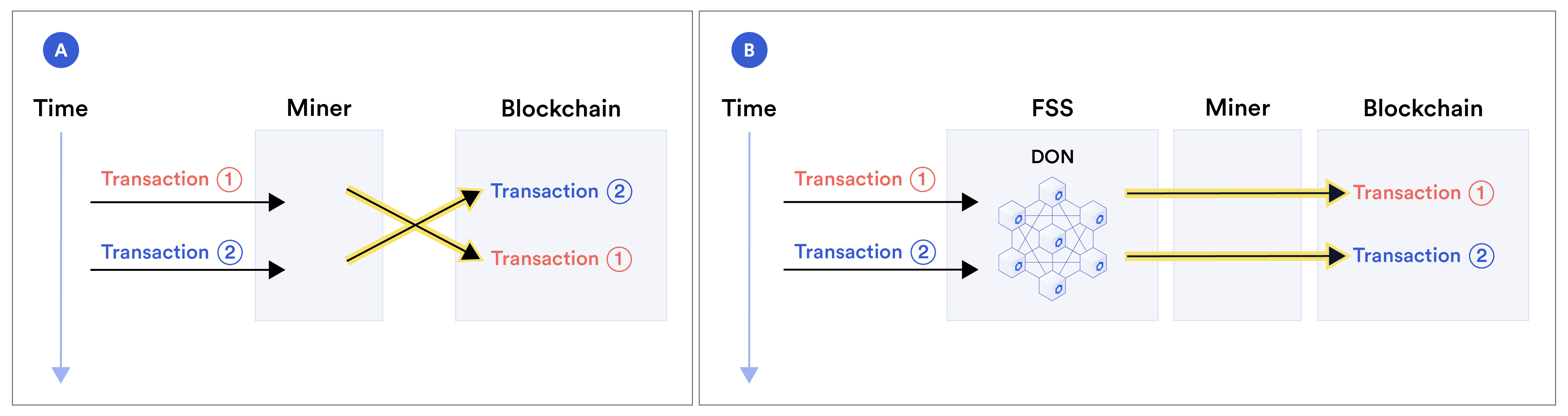
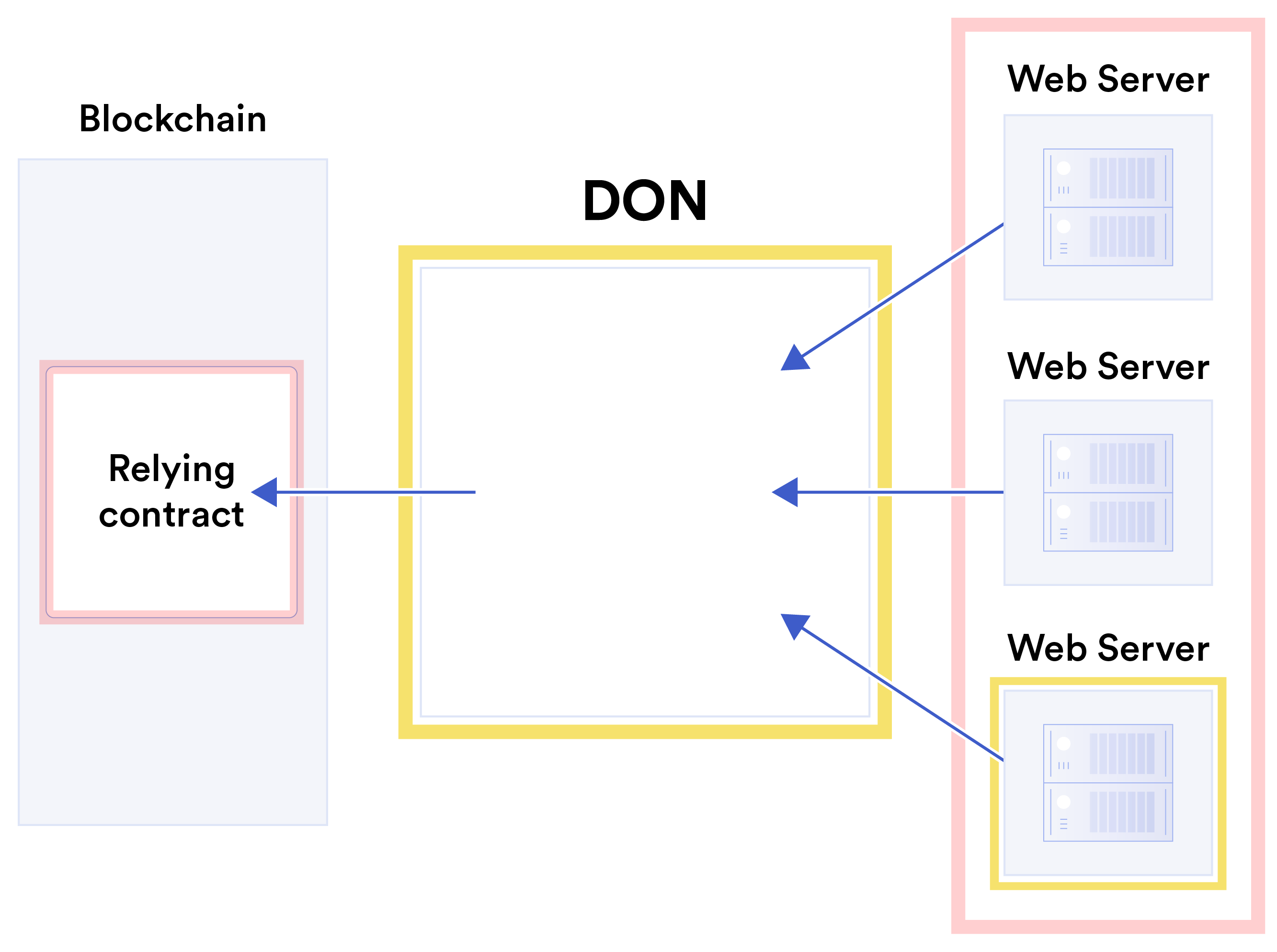
• Dukungan untuk sistem lapisan-2 rahasia: TEF dirancang untuk mendukung berbagai sistem lapisan-2, banyak di antaranya menggunakan bukti tanpa pengetahuan untuk memberikan berbagai bentuk kerahasiaan transaksi. Kami membahas pendekatan-pendekatan ini di Bagian 3 (dengan rincian tambahan di Bagian 6, Lampiran B.1, dan Lampiran B.2). Gambar 5 menyajikan pandangan konseptual tentang bagaimana data sensitif dapat mengalir dari sumber eksternal ke smart contract melalui adaptor yang menjaga kerahasiaan dan perhitungan rahasia dalam DON. Gambar 5: Diagram konseptual operasi menjaga kerahasiaan di DON di data sensitif (disorot dengan warna kuning). Data sumber sensitif (lingkaran hitam) di web server diekstraksi ke DON menggunakan adaptor yang menjaga kerahasiaan (garis biru, panah ganda). DON menerima data turunan (lingkaran berongga) dari adaptor ini— hasil penerapan suatu fungsi atau, misalnya, berbagi rahasia, ke sumber sensitif data. Eksekusi pada DON dapat menerapkan penghitungan rahasia pada data turunan untuk membuat laporan (lingkaran ganda), yang dikirimkan melalui adaptor ke blockchain. Kami percaya bahwa alat yang ampuh untuk menangani data rahasia akan membuka keseluruhannya berbagai aplikasi. Diantaranya adalah keuangan swasta yang terdesentralisasi (dan terpusat), identitas yang terdesentralisasi, pinjaman on-chain berbasis kredit, dan sistem yang lebih efisien dan efisien. protokol kenali pelanggan dan akreditasi yang mudah digunakan, seperti yang kita bahas di Bagian 4. Kewajaran pesanan untuk transaksi: Desain blockchain hari ini sedikit kotor rahasia umum: Mereka terpusat secara sementara. Penambang dan validator dapat memesan trans-tindakan apapun yang mereka pilih. Urutan transaksi juga dapat dimanipulasi oleh pengguna seperti fungsi dari biaya jaringan yang mereka bayarkan (misalnya, harga gas di Ethereum) dan beberapa sejauh mana dengan memanfaatkan koneksi jaringan yang cepat. Manipulasi seperti itu bisa, misalnya Misalnya saja dalam bentuk front-running, dimana aktor strategis seperti penambang mengamati transaksi pengguna dan memasukkan transaksi eksploitatifnya ke transaksi sebelumnya posisi di blok yang sama—secara efektif mencuri uang dari pengguna dengan memanfaatkan pengetahuan awal tentang transaksi pengguna. Misalnya, bot dapat melakukan pemesanan pembelian sebelum pengguna. Perusahaan kemudian dapat mengambil keuntungan dari kenaikan harga aset yang disebabkan oleh perdagangan pengguna. Dijalankan terlebih dahulu oleh beberapa bot yang merugikan pengguna biasa—sama dengan frekuensi tinggi perdagangan di Wall Street—sudah lazim dan terdokumentasi dengan baik [90], dan sebagainya serangan seperti [159] yang berjalan kembali dan peniruan transaksi otomatis [195]. Proposal untuk mensistematisasikan eksploitasi pesanan oleh para penambang bahkan telah muncul baru-baru ini [110]. Teknologi lapisan-2 seperti rollups tidak menyelesaikan masalah, namun hanya memusatkan kembali memesan, menempatkannya di tangan entitas yang menciptakan rollup. Salah satu tujuan kami adalah memperkenalkan Chainlink layanan yang disebut Fair Sequencing Layanan (FSS) [137]. FSS membantu smart contract desainer memastikan pemesanan yang adil untuk mereka transaksi dan menghindari serangan yang berjalan di depan, berjalan di belakang, dan serangan terkait terhadap transaksi pengguna serta jenis transaksi lainnya, seperti transmisi laporan oracle. FSS memungkinkan DON untuk mengimplementasikan ide-ide seperti gagasan keadilan ketertiban yang ketat dan sementara yang diperkenalkan di [144]. Sebagai manfaat tambahan, FSS juga dapat menurunkan jaringan pengguna biaya (misalnya, biaya bahan bakar). Singkatnya, di FSS, transaksi melewati DON, bukan disebarkan langsung ke target smart contract. DON memerintahkan transaksi dan kemudian meneruskannya mereka ke kontrak. Gambar 6: Contoh manfaat FSS. Gambar ⃝menunjukkan bagaimana seorang penambang, mengeksploitasinya kekuasaan terpusat untuk memesan transaksi, dapat menukar sepasang transaksi: transaksi 1⃝ tiba sebelum 2⃝, namun penambang malah mengurutkannya setelah 2⃝. Sebaliknya, Gambar B⃝menunjukkan bagaimana DON mendesentralisasikan proses pemesanan di antara DON node. Jika kuorum node yang jujur menerima 1⃝sebelum 2⃝, FSS menyebabkan 1⃝muncul sebelum 2⃝pada rantai— mencegah pemesanan ulang penambang dengan melampirkan nomor urut yang dapat ditegakkan kontrak. Gambar 6 membandingkan penambangan standar dengan FSS. Ini menunjukkan bagaimana dalam penambangan standar,proses pemesanan transaksi dipusatkan pada penambang dan karenanya tunduk pada manipulasi, seperti menyusun ulang sepasang transaksi sehubungan dengan kedatangannya kali. Sebaliknya, di FSS, prosesnya didesentralisasi di antara DON node. Dengan asumsi kuorum node yang jujur, FSS membantu menegakkan kebijakan seperti pemesanan sementara transaksi, mengurangi peluang manipulasi oleh penambang dan entitas lainnya. Selain itu, karena pengguna tidak perlu bersaing untuk mendapatkan pemesanan preferensial berdasarkan harga bahan bakar, mereka dapat membayar harga bahan bakar yang relatif rendah (sementara transaksi dari DON dapat dilakukan secara batch untuk penghematan gas). Minimalkan kepercayaan: Tujuan umum kami dalam desain DONs adalah untuk memfasilitasi lapisan dukungan yang dapat dipercaya untuk smart contracts dan sistem lain yang bergantung pada oracle melalui desentralisasi, alat kriptografi, dan jaminan ekonomi kripto. DON itu sendiri terdesentralisasi, dan pengguna dapat memilih dari DON mana pun yang tersedia mendukung rantai utama yang ingin mereka operasikan atau menghasilkan DON tambahan dengan komite node yang mereka percayai. Namun, untuk beberapa aplikasi, khususnya smart contracts, Chainlink pengguna mungkin pilihlah model kepercayaan yang memperlakukan rantai utama yang didukung oleh DON sebagai lebih dapat dipercaya daripada DON itu sendiri. Untuk pengguna seperti itu, kami sudah memiliki atau berencana untuk menggabungkannya ke dalam arsitektur jaringan Chainlink sejumlah mekanisme yang memungkinkan kontrak pada rantai utama untuk memperkuat jaminan keamanan yang diberikan oleh DONs, sementara di pada saat yang sama juga menerapkan perlindungan terhadap kemungkinan sumber data rusak seperti server web tempat DON memperoleh data. Kami menjelaskan mekanisme ini di Bagian 7. Mekanisme ini terbagi dalam lima judul utama: • Autentikasi sumber data: Alat yang memungkinkan penyedia data menandatangani secara digital data mereka dan dengan demikian memperkuat rantai pengawasan antara negara asal dan mengandalkan kontrak. • DON laporan minoritas: Bendera yang dikeluarkan oleh subset minoritas dari DON node yang mengamati penyimpangan mayoritas di DON. • Rel pengaman: Logika pada rantai utama yang mendeteksi kondisi anomali dan jeda atau menghentikan pelaksanaan kontrak (atau meminta remediasi lainnya). • Tata kelola yang minim kepercayaan: Penggunaan pembaruan yang dirilis secara bertahap untuk memfasilitasi inspeksi masyarakat, serta intervensi darurat yang terdesentralisasi untuk mempercepat respons terhadap kegagalan sistem. • Otentikasi entitas terdesentralisasi: Penggunaan infrastruktur kunci publik (PKI) untuk mengidentifikasi entitas di jaringan Chainlink. Gambar 7 menyajikan skema konseptual tujuan minimalisasi kepercayaan kami. Keamanan berbasis insentif (kriptoekonomi): Desentralisasi pembuatan laporan di seluruh oracle node membantu memastikan keamanan bahkan ketika beberapa node rusak.
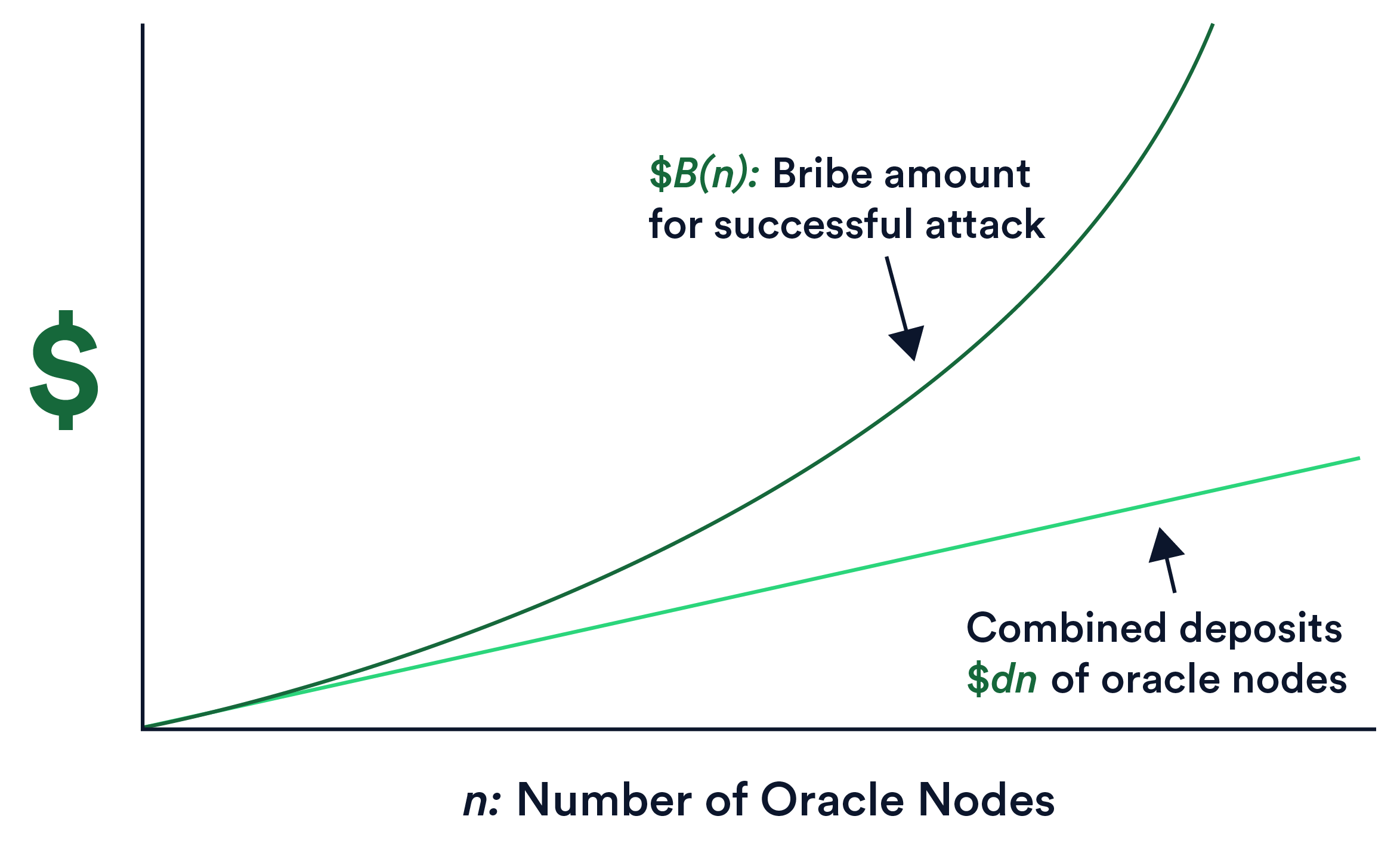
Gambar 7: Penggambaran konseptual tujuan minimalisasi kepercayaan Chainlink, yaitu untuk meminimalkan kebutuhan pengguna akan perilaku yang benar dari DON dan sumber data seperti web server. Sorotan kuning pada gambar menunjukkan lokus minimalisasi kepercayaan: DON dan kumpulan server web individu atau minoritas. Sorotan merah muda menunjukkan komponen sistem yang sangat dapat dipercaya dengan asumsi: kontrak pada blockchain dan mayoritas server web, yaitu server web secara agregat. Namun, yang tidak kalah pentingnya adalah memastikan bahwa node memiliki insentif finansial untuk berperilaku benar. Staking, yaitu mengharuskan node untuk menyediakan deposit LINK dan pemotongan (menyita) simpanan ini jika terjadi perilaku buruk, akan memainkan peran penting dalam Chainlink. Ini adalah desain insentif penting yang telah digunakan di sejumlah blockchains, misalnya, [81, 103, 120, 204]. Namun, staking di Chainlink terlihat sangat berbeda dari staking di standalone blockchains. Staking di blockchains bertujuan untuk mencegah serangan terhadap konsensus. Ini memiliki tujuan yang berbeda di Chainlink: untuk memastikan pengiriman laporan oracle yang benar secara tepat waktu. Sistem staking yang dirancang dengan baik untuk jaringan oracle akan menghasilkan serangan seperti penyuapan tidak menguntungkan bagi musuh, bahkan ketika targetnya adalah smart contract dengan tinggi nilai moneter. Dalam makalah ini, kami menyajikan pendekatan umum untuk staking di Chainlink dengan tiga kunci inovasi:1. Model permusuhan yang kuat yang mencakup serangan-serangan yang diabaikan saat ini pendekatan. Salah satu contohnya adalah apa yang kita sebut suap prospektif. Ini adalah suatu bentuk penyuapan yang menentukan node mana yang menerima suap berdasarkan kondisi, misalnya, menawarkan jaminan suap terlebih dahulu ke node yang dipilih oleh mekanisme staking di acak untuk peran tertentu (seperti memicu pengambilan keputusan laporan). 2. Dampak staking super-linear, artinya secara informal bahwa agar berhasil, musuh harus memiliki anggaran $B lebih besar daripada gabungan simpanan seluruh oracle node. Lebih tepatnya, yang kami maksud adalah sebagai fungsi dari n, \(B(n) ≫\)dn di a jaringan n oracle node masing-masing dengan jumlah deposit tetap $d (lebih formalnya, \(B(n) is asymptotically larger in n than \)dn). Gambar 8 memberikan pandangan konseptual tentang properti ini. 3. Kerangka Insentif Implisit (IIF), sebuah model insentif yang telah kami rancang mencakup insentif yang dapat diukur secara empiris di luar yang disetorkan secara eksplisit staking dana, termasuk peluang biaya node di masa depan. IIF memperluas gagasan tentang mempertaruhkan di luar deposit node eksplisit. Gambar 8: Diagram konseptual yang menggambarkan penskalaan super-linear di Chainlink staking. Itu suap $B(n) yang dibutuhkan oleh musuh tumbuh lebih cepat di n dibandingkan gabungan simpanan $dn dari semua oracle node. Kami menunjukkan bagaimana dampak IIF dan super-linear staking bersama-sama menginduksi apa yang kita menyebut siklus baik keamanan ekonomi untuk jaringan oracle. Saat pengguna baru masuk
sistem, meningkatkan potensi pendapatan masa depan dari menjalankan Chainlink node, the penurunan biaya marjinal keamanan ekonomi bagi pengguna saat ini dan masa depan. Dalam rezim permintaan elastis, penurunan biaya ini memberi insentif kepada pengguna tambahan untuk memanfaatkannya jaringan, terus melanggengkan adopsi dalam siklus kebajikan yang berkelanjutan. Catatan: Meskipun whitepaper ini menguraikan elemen-elemen penting dari visi kami untuk evolusi Chainlink, whitepaper ini bersifat informal dan mencakup sedikit rincian teknis yang rinci. Kami berencana untuk melakukannya merilis makalah teknis yang berfokus pada fitur dan pendekatan tambahan seiring dengan perkembangannya. Lebih lanjut, penting untuk ditekankan bahwa banyak elemen dari visi yang disampaikan di sini (peningkatan skala, teknologi kerahasiaan, FSS, dll.) dapat dan akan terjadi diterapkan dalam bentuk awal bahkan sebelum DON tingkat lanjut menjadi fitur dasar Chainlink. 1.3 Organisasi Makalah ini Kami menyajikan model dan notasi keamanan kami di Bagian 2 dan menguraikan Desentralisasi Oracle Network API di Bagian 3. Di Bagian 4, kami menyajikan sejumlah contoh aplikasi yang DONs menyediakan platform penerapan yang menarik. Pembaca bisa pelajari sebagian besar konsep utama makalah ini dengan membaca hingga titik ini. Sisa makalah ini berisi rincian lebih lanjut. Kami menjelaskan Urutan yang Adil Layanan (FSS) di Bagian 5 dan Kerangka Eksekusi Transaksi (TEF) di Bagian 6. Kami menjelaskan pendekatan kami terhadap minimalisasi kepercayaan di Bagian 7. Kami mempertimbangkan beberapa persyaratan penerapan DON yang penting, yaitu peluncuran fitur secara bertahap, keanggotaan buku besar dinamis, dan akuntabilitas di Bagian 8. Terakhir, di Bagian 9, kami memberikan gambaran umum tentang pendekatan kami yang berkembang terhadap desain insentif. Kami menyimpulkan di Bagian 10. Untuk membantu pembaca yang memiliki pemahaman terbatas terhadap konsep-konsep dalam makalah ini, kami berikan glosarium di Lampiran A. Kami menyajikan detail lebih lanjut pada antarmuka DON dan fungsionalitas di Lampiran B dan sajikan beberapa contoh adaptor di Lampiran C. Dalam Lampiran D, kami menjelaskan primitif kriptografi untuk sumber data yang diminimalkan kepercayaan otentikasi disebut tanda tangan fungsional dan memperkenalkan varian baru yang disebut tanda tangan fungsional terdiskritisasi. Kami membahas beberapa pertimbangan yang ada di komite seleksi untuk DONs di Lampiran F.
介绍
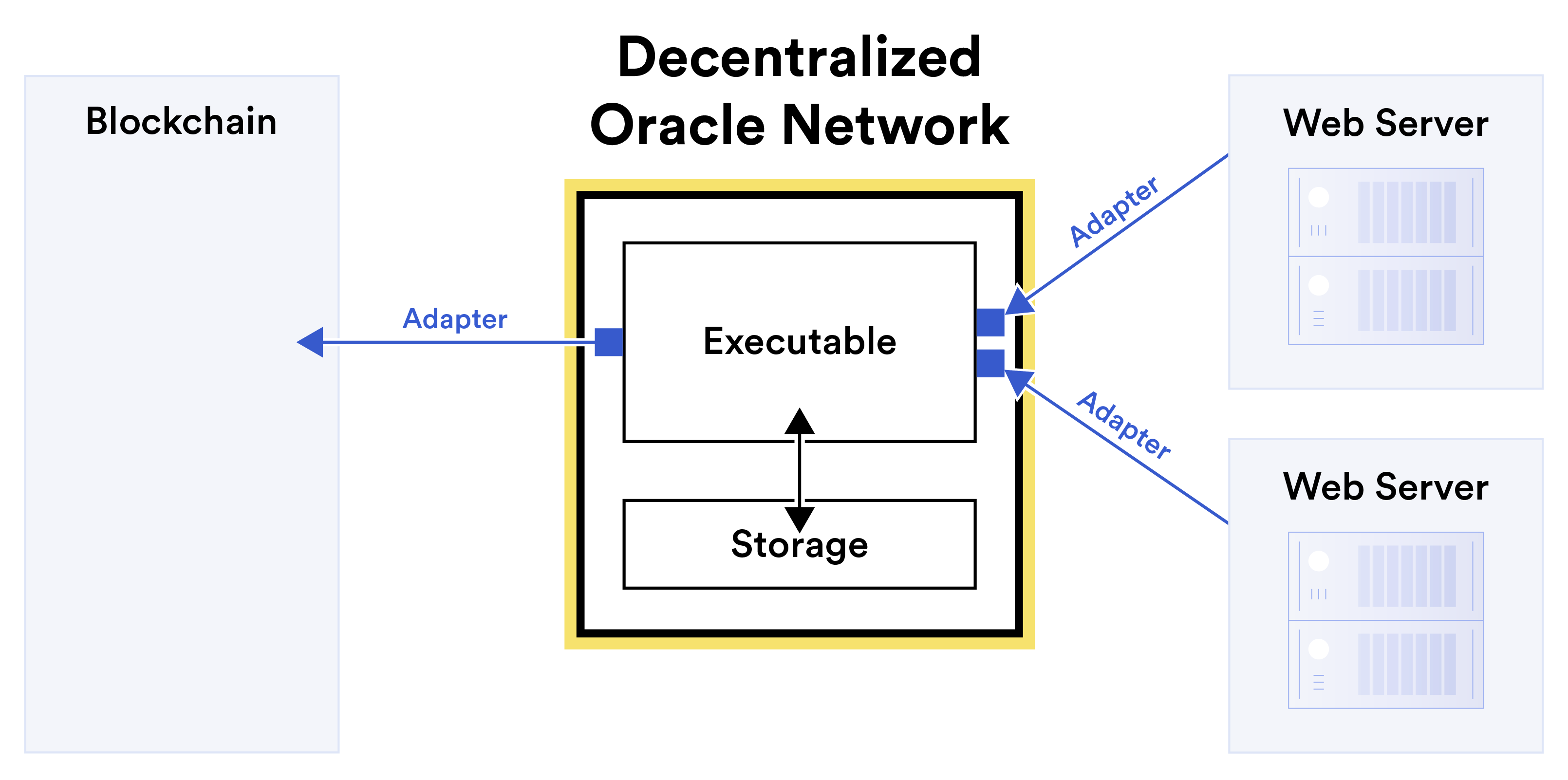
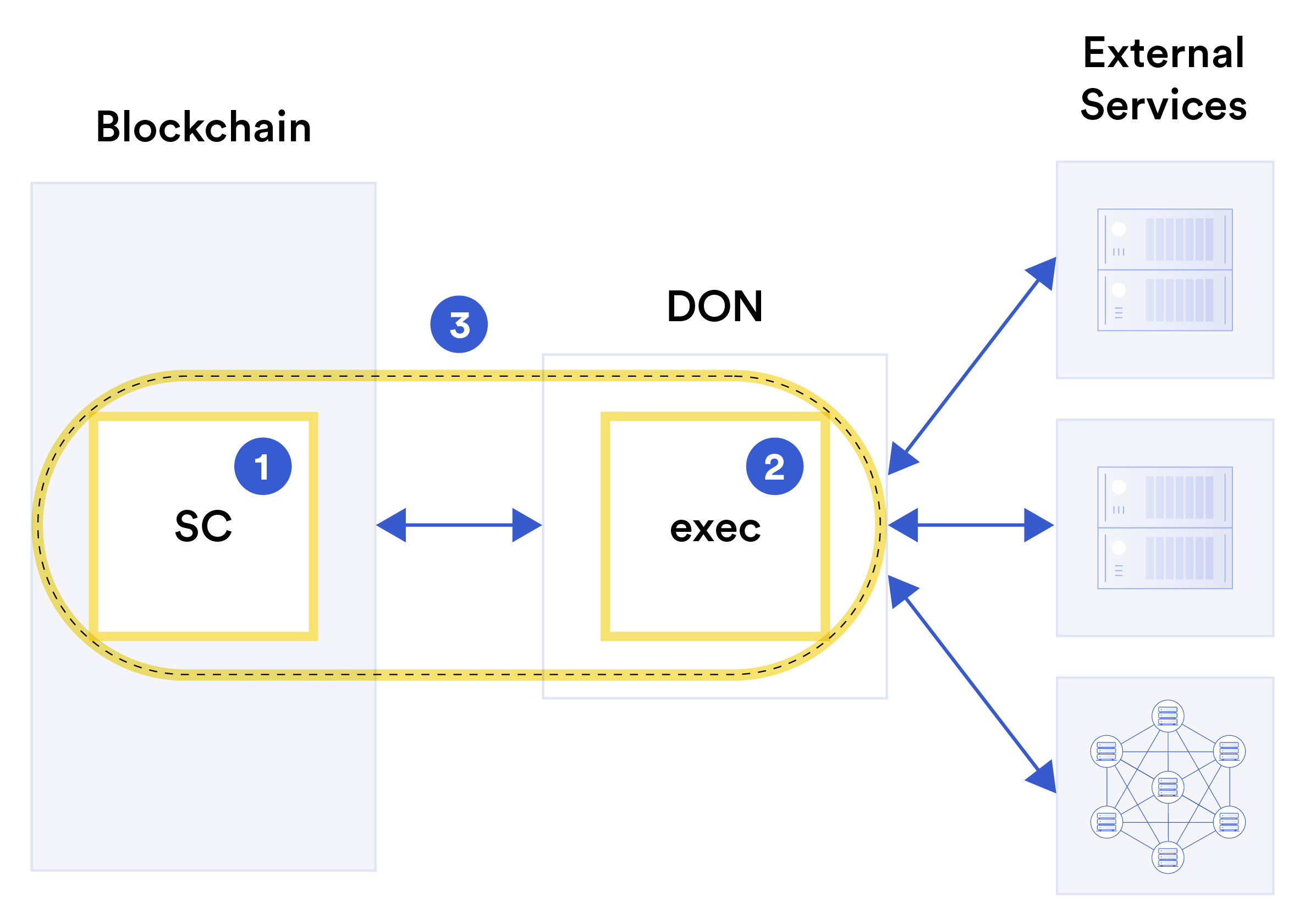
如今,区块链 oracle 通常被视为具有一个目标的去中心化服务: 将数据从链下资源转发到 blockchains。虽然这只是一小步, 从转发数据到计算、存储或双向传输。这一观察结果证实了 oracles 功能的更广泛概念。也是如此 满足 smart contract 不断增长的服务需求并且日益多元化 依赖 oracle 网络的技术。简而言之,oracle 可以而且需要 成为链上和链下系统之间的通用、双向、支持计算的接口。预言机在 blockchain 生态系统中的作用是增强 smart contract 的性能、功能和互操作性,以便它们能够 为多个行业带来新的信任模式和透明度。这种转变将通过扩大混合 smart contract 的使用来实现,它融合了 blockchains 的特殊属性以及链下系统的独特功能,例如 oracle 网络,从而实现比链上系统更大的覆盖范围和能力 处于孤立状态。 在本白皮书中,我们阐述了 Chainlink 2.0 的愿景,这是 Chainlink 的演变,超越了原始 Chainlink 白皮书 [98] 中的最初构想。我们预见 oracle 网络的作用将日益扩大,其中 它们通过为混合动力提供快速、可靠且保密的通用连接和计算来补充和增强现有和新的 blockchain smart contracts。我们相信 oracle 网络甚至会发展成为公用事业 用于将高完整性 blockchain 级数据导出到 blockchain 之外的系统 生态系统。 如今,由不同实体集运行的 Chainlink 节点聚集在 oracle 网络中,将数据转发到 smart contract,即所谓的报告。我们可以查看这样的 oracle 节点作为类似于经典共识 blockchain [72] 中的委员会, 但目标是支持现有的 blockchain,而不是提供独立的功能。具有可验证的随机函数(VRF)和链外报告 (OCR),Chainlink 已经向通用框架和基础设施发展,以提供 smart contracts 所需的计算资源 先进的功能。 我们的 Chainlink 2.0 计划的基础是我们所说的去中心化预言机 网络,简称 DONs。由于我们在 中引入了术语“oracle 网络” 原始 Chainlink 白皮书 [98]、oracle 开发了更丰富的功能和 应用范围。在本文中,我们根据 我们对 Chainlink 生态系统的未来愿景。在此视图中,DON 是一个网络 由 Chainlink 节点委员会维护。植根于共识协议,它 支持任何无限范围的 oracle 选择用于部署的功能 委员会。因此,DON 充当 blockchain 抽象层,提供接口 smart contract 和其他系统的链外资源。它还提供 访问高效且去中心化的链下计算资源。一般来说, a DON 支持主链上的操作。其目标是实现安全和灵活ble Hybrid smart contracts,将链上和链外计算与 与外部资源的连接。 我们强调,即使在 DONs 中使用委员会,Chainlink 本身 本质上仍然是未经许可的。 DONs 充当无需许可的基础 框架,其中节点可以聚集在一起实现自定义 oracle 网络 他们自己的节点包含制度,可能是经过许可的,也可能是未经许可的。 以 DONs 为基础,我们计划在 Chainlink 2.0 中重点关注七个方面的进展 关键领域:混合 smart contracts、抽象复杂性、扩展性、保密性、交易秩序公平性、信任最小化和基于激励的(加密经济)安全性。在本文的介绍中,我们概述了去中心化 第 1.1 节介绍了 Oracle 网络,然后第 1.2 节介绍了我们的七个关键创新领域。我们在 1.3 节中描述了本文其余部分的组织。 1.1 去中心化预言机网络 去中心化预言机网络旨在增强和扩展功能 目标 blockchain 或主链上的 smart contract 通过以下函数 本地不可用。他们通过提供以下三种基本资源来做到这一点: 计算系统:网络、存储和计算。 DON 旨在提供 这些资源具有很强的保密性、完整性和可用性,1 以及问责制。 DON 由 oracle 节点组成的委员会组成,这些节点合作完成特定的任务 工作或选择建立长期关系以提供持久的服务 给客户。 DON 以与 blockchain 无关的方式设计。他们承诺将作为 一个强大而灵活的工具,供应用程序开发人员创建链下支持 他们在任何受支持的主链上的 smart contract。 有两种类型的功能实现 DON 的功能:可执行文件和 适配器。可执行文件是在 DON 上以分散方式连续运行的程序。虽然它们不直接存储主链资产,但它们具有重要的好处,包括高性能和执行机密的能力 计算。可执行文件在 DON 上自主运行并执行确定性 操作。它们与将 DON 连接到外部资源的适配器协同工作 并且可以由可执行文件调用。正如我们为 DON 设想的那样,适配器是一个 今天 Chainlink 中外部适配器的通用化。虽然现有适配器 通常仅从数据源获取数据,适配器可以双向操作;在 DONs,它们还可以利用 DON 节点的联合计算来实现 附加功能,例如加密报告以保护隐私 一个可执行文件。 为了让您了解 DON 的基本操作,图 1 从概念上展示了 DON 是如何 DON 可用于将报告发送到 blockchain,从而实现传统的现有 oracle 功能。然而,DONs 可以提供许多附加功能 1信息安全的“中央情报局三合会”[123,第 14 页] 26,第 2.3.5 节]。Chainlink 的现有网络。例如,在图1的总体结构中, 可执行文件可以在 DON 上记录获取的资产价格数据,使用这些数据 计算例如其报告的追踪平均值。 图 1:概念图,以示例显示去中心化预言机网络如何实现基本的 oracle 功能,即将链外数据中继到合约。安 可执行文件使用适配器来获取链外数据,并对其进行计算,发送输出 通过另一个适配器连接到目标 blockchain。 (适配器由以下代码启动 DON,用小蓝框表示;箭头表示数据流的方向 特定示例。)可执行文件还可以读取和写入本地 DON 用于保持状态和/或与其他可执行文件通信的存储。 DONs 中灵活的网络、计算和存储,全部都在这里展示,使许多新颖的 应用程序。 DON 的一个主要好处是它们能够引导新的 blockchain 服务。 DONs 是现有oracle网络可以快速建立服务应用程序的工具 今天,这需要创建专门的网络。我们给出了一些 第 4 节中此类应用的示例。 在第 3 节中,我们提供了有关 DON 的更多详细信息,描述了它们的功能 他们向开发人员和用户呈现的界面术语。 1.2 七个关键设计目标 在这里,我们简要回顾一下上面列举的七个关键点: Chainlink,即:混合 smart contracts: 我们 Chainlink 愿景的核心是安全的理念 在 smart contracts 中组合链上和链下组件。我们参考合同 通过混合 smart contract 或混合合约来实现这一想法。2 区块链现在并将继续在去中心化服务中发挥两个关键作用 生态系统:它们都是代表加密货币所有权的场所 以及去中心化服务的强大锚点。因此,智能合约必须在链上表示或执行,但其链上功能受到严重限制。纯粹地 链上合约代码缓慢、昂贵且孤立,无法从现实世界中受益 数据和各种在链上本质上无法实现的功能,包括各种形式的机密计算、(伪)随机性安全的生成 反对矿工/validator操纵等。 因此,为了让smart contracts充分发挥其潜力,需要smart contracts 由两部分组成:链上部分(我们通常用 SC 表示) 以及链下部分,即在 DON 上运行的可执行文件(我们通常用 执行)。目标是实现链上功能的安全组合 DONs 旨在提供多种链下服务。两部分放在一起 制定混合合同。我们在图 2 中概念性地提出了这个想法。今天, Chainlink 服务3(例如数据馈送和 VRF)正在实现原本无法实现的目标 smart contract 应用程序,范围从 DeFi 到公平生成的 NFT 到去中心化保险,作为迈向更通用框架的第一步。作为 Chainlink 服务 根据我们在本白皮书中的愿景,扩大并提高绩效,也是如此 smart contract 系统在所有 blockchain 上的能力。 我们在本白皮书中的其他六个重点可能被视为服务中的行为 第一个是混合合同的总体内容。这些焦点涉及消除可见的 混合合约的复杂性,创建额外的链下服务,使 构建能力更强的混合合约,并且在信任最小化的情况下,增强混合合约所实现的安全属性。我们留下想法 混合合约隐含在本文的大部分内容中,但任何组合 具有 DON 的主链逻辑可以被视为混合合约。 抽象掉复杂性: DONs 旨在利用去中心化的 通过抽象出通常复杂的机制,为开发人员和用户提供方便的系统 DONs 强大而灵活的一系列服务的背后。 现有 Chainlink 服务 已经有这个功能了。 例如,Chainlink 中的数据馈送现在提供了链上接口,这些接口不需要开发人员关心协议级别的细节,例如 OCR 强制执行共识报告的方式。 2链上/链下合约组合的想法之前已经在各种受限环境中出现过 形式,例如,第 2 层系统、基于 TEE 的 blockchains [80] 等。我们的目标是支持和泛化 这些方法并确保它们可以包含链外数据访问和其他关键 oracle 服务。 3Chainlink 服务包括各种可通过以下方式获得的去中心化服务和功能: 网络。它们由组成各种 oracle 网络的众多节点运营商提供 整个生态系统。图 2:描述链上/链下合约构成的概念图。一个 混合 smart contract 3⃝由两个互补的组件组成:一个链上组件 组件 SC 1⃝,驻留在 blockchain 上,以及链外组件 exec 2⃝ 在 DON 上执行。 DON 也充当两个组件之间的桥梁 将混合合约与链下资源(例如网络服务、其他资源)连接起来 blockchains、去中心化存储等 分散的节点集。 DONs 更进一步,因为它们扩展了 Chainlink 可以为开发人员提供抽象层的一系列服务 伴随高级服务的简化界面。 我们在第 4 节中介绍了几个应用示例来强调这种方法。 例如,我们设想企业使用 DONs 作为一种安全中间件形式 将他们的旧系统连接到 blockchains。 (参见第 4.2 节。)DON 的这种使用抽象了一般 blockchain 动态的复杂性(费用、重组等)。它还 抽象出特定 blockchain 的功能,从而使企业能够将其现有系统连接到不断扩大的 blockchain 系统,而无需 需要这些系统或更广泛的分散系统开发方面的专业知识。 最终,我们的目标是推动 Chainlink 实现的抽象程度 到了实现我们所说的去中心化元层的程度。这样的一层 将为所有类别的开发人员抽象出链上/链下的区别 和 DApp 的用户,允许无缝创建和使用去中心化服务。为了简化开发过程,开发人员可以将元层中的 DApp 功能指定为统一机器模型中的虚拟应用程序。他们可以 然后使用去中心化元层编译器自动将 DApp 实例化为 一组互操作的分散功能,涵盖 blockchains、DONs 和 外部服务。 (这些外部服务之一可以是企业系统,使得元层对于涉及遗留企业系统的应用程序非常有用。) 编译类似于现代编译器和软件开发工具包 (SDK) 支持通才程序员充分发挥异构硬件的潜力 由通用 CPU 和 GPU 等专用硬件组成的架构, 机器学习加速器或可信飞地。图 3 在概念层面上展示了这一想法。 混合 smart contract 是实现这一愿景和我们称为元合约的概念的第一步。元合约是在去中心化平台上编码的应用程序 元层并隐式包含链上逻辑 (smart contracts),以及各种 blockchains 和现有链下之间的链下计算和连接 服务。考虑到对语言和编译器支持、新安全模型的需求,以及 然而,不同技术的概念和技术协调 真正的去中心化元层是一个雄心勃勃的目标,我们长期以来一直渴望实现这一目标 时间范围。尽管如此,它仍然是一个在阅读时牢记的有用的理想模型 这篇论文,这里没有详细介绍,但我们计划在未来的工作中重点关注 Chainlink。 缩放比例: 在我们不断发展的设计中,一个极其重要的目标是使 Chainlink 网络,以满足 blockchain 生态系统不断增长的扩展需求。 随着网络拥塞成为现有无许可环境中反复出现的问题 blockchains [86],新的、性能更高的 blockchain 设计正在投入使用, 例如,[103,120,203],以及补充的第 2 层扩展技术,例如[5, 12、121、141、169、186、187]。 Oracle 服务必须实现延迟和吞吐量 满足这些系统的性能需求,同时最大限度地减少链上费用 (例如,天然气成本)对于合同运营商和普通用户来说都是如此。与 DONs、Chainlink 功能旨在更进一步,为纯粹基于网络的系统提供足够高的性能。 DONs 的大部分性能提升来自于使用快速、基于委员会或无需许可的共识协议,并将其与 blockchains 相结合 他们支持。我们期望许多具有不同配置的 DON 并行运行;不同的 DApp 和用户可以在底层共识选择中进行权衡 根据他们的应用要求。 DONs 实际上可以被视为第 2 层技术。 我们期望其中 其他服务,DONs 将支持事务执行框架 (TEF),该框架 促进 DONs 以及 oracles 与其他高性能的有效集成 第 2 层系统——例如 rollups,将链下交易捆绑在一起以实现 性能改进。我们在第 6 节中介绍了 TEF。
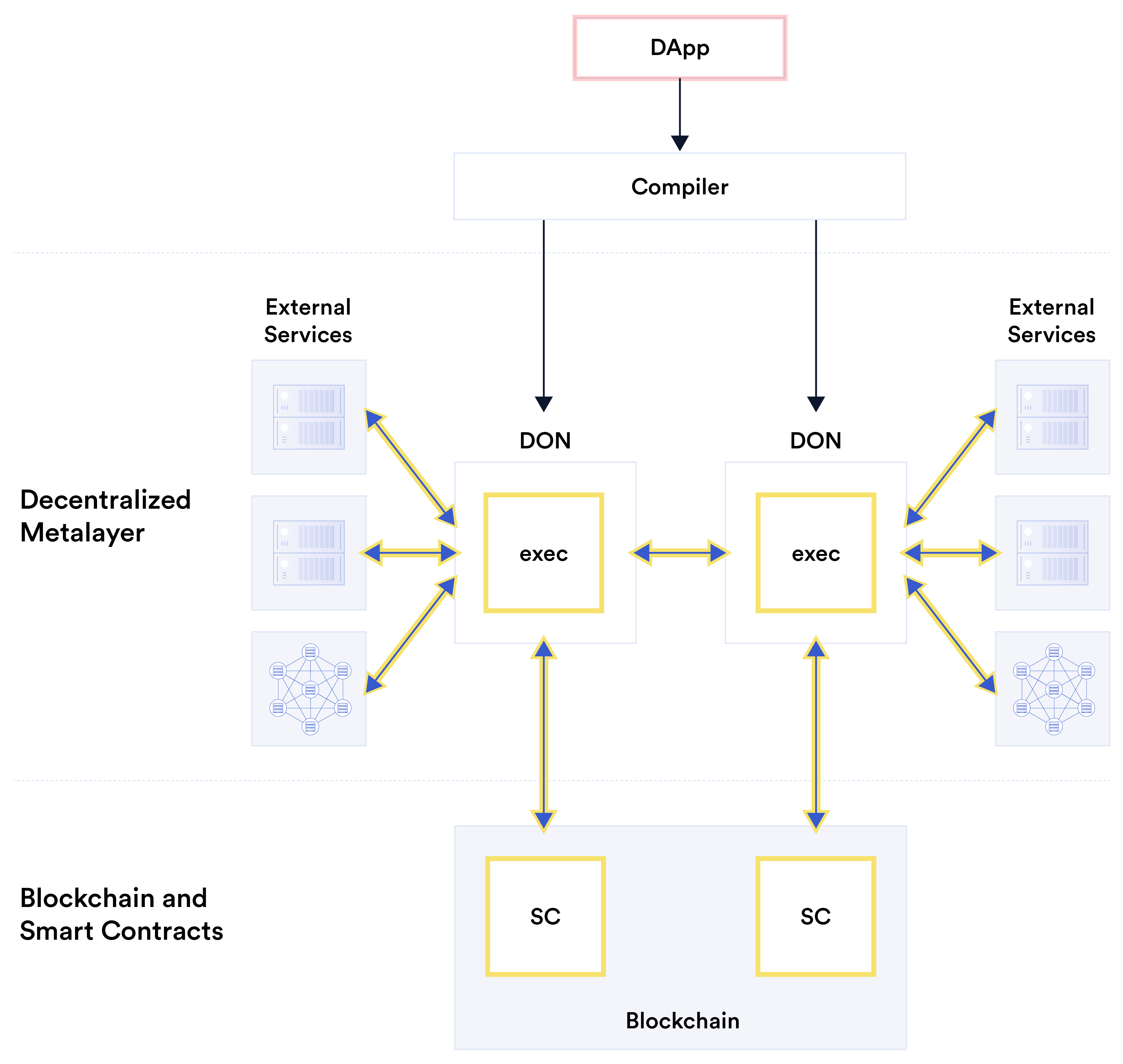
图 3:概念图显示了去中心化元层的理想实现。对于 为了便于开发,开发人员指定一个 DApp(以粉色突出显示)作为虚拟的 统一机器模型中的应用。去中心化元层编译器自动生成相应的互操作功能:smart contracts(表示为 由 SC 表示)、DON 上的逻辑(由 exec 表示)、连接到目标外部服务的适配器等等,如黄色突出显示所示。 图 4 从概念上展示了 DONs 如何改进 blockchain (smart contract) 缩放 通过集中交易和oracle-报告处理在链外,而不是在链上 链。计算主要位置的这种转变减少了交易延迟并 费用,同时提高交易吞吐量。 保密性: 区块链为 smart contract 及其实现的应用程序提供了前所未有的透明度。但透明度和保密性之间存在着基本的紧张关系。例如,今天,用户的去中心化交易所交易图 4:概念图显示去中心化预言机网络如何改进 blockchain 启用的 smart contracts 的缩放。图A ⃝显示传统的oracle 架构。交易直接发送至 blockchain,oracle 报告也是如此。 因此,以黄色突出显示的 blockchain 是事务处理的主要位置。图 B⃝显示了使用 DON 来支持 blockchain 上的合约。 DON 可执行文件处理交易以及来自外部系统的数据并转发 结果(例如,由于交易影响而导致的捆绑交易或合约状态更改)发送至 blockchain。因此,以黄色突出显示的 DON 是主要的 交易处理的场所。 行为记录在链上,方便监控交易所行为,同时也 使用户的金融交易公开可见。同样,数据转发到智能 合约仍然在链上。这使得此类数据可以方便地进行审计,但充当 对于希望向 smart contracts 提供敏感或敏感信息的数据提供商来说,这是一种抑制因素 专有数据。 我们相信 oracle 网络将在催化下一代方面发挥关键作用 将 blockchains 固有的透明度与新的保密保护相结合的系统。在本文中,我们展示了他们如何使用三种主要方法来做到这一点: • 保密适配器:计划部署的两种技术 在 Chainlink 的网络中,DECO [234] 和 Town Crier [233],启用 oracle 节点 以保护用户隐私和数据的方式从链下系统检索数据 保密性。它们将在 DON 的适配器设计中发挥关键作用。 (有关这两种技术的详细信息,请参见第 3.6.2 节。) • 机密计算:DONs 可以简单地向依赖blockchains 隐藏其计算。使用安全的多方计算和/或可信执行环境,还可以实现更强的保密性,其中 DON 节点 对他们本身不可见的数据进行计算。
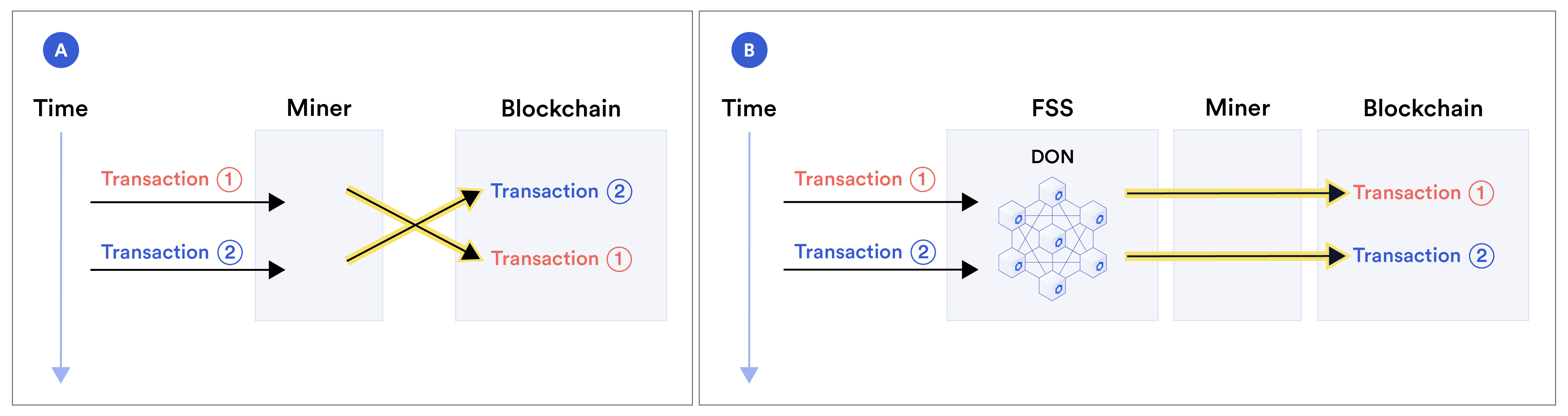
• 支持机密第 2 层系统:TEF 旨在支持各种第 2 层系统,其中许多系统使用零知识证明来提供 各种形式的交易保密性。 我们在第 3 节中讨论这些方法(更多详细信息请参见第 6 节、附录 B.1 和附录 B.2)。 图 5 展示了敏感数据如何通过保密适配器从外部源流向 smart contract 的概念视图 DON 中的机密计算。 图 5:DON 上的保密操作的概念图 敏感数据(以黄色突出显示)。 网络中的敏感源数据(黑圈) 使用保密适配器(蓝色双箭头线)将服务器提取到 DON。 DON 从这些适配器接收派生数据(空心圆圈)— 将函数或秘密共享等应用到敏感源的结果 数据。 DON 上的可执行文件可以对派生数据应用机密计算 构建报告(双圆圈),通过适配器将其发送到 blockchain。 我们相信,处理机密数据的强大工具将打开一个完整的领域。 应用范围。 其中包括私人去中心化(和中心化)金融、去中心化身份、基于信用的链上借贷以及更高效、更高效的金融服务。 用户友好的了解你的客户和认证协议,正如我们在第 4 节中讨论的那样。 交易的顺序公平性: 今天的 blockchain 设计有点肮脏 公开的秘密:它们是暂时集中的。矿工和 validators 可以订购交易无论他们选择什么行动。用户也可以操纵交易顺序 他们支付的网络费用的函数(例如 Ethereum 中的汽油价格)以及某些 利用快速网络连接的优势。这种操纵可以,对于 例如,采取抢先交易的形式,其中战略参与者(例如矿工) 观察用户的交易并将其自己的可利用交易插入到较早的交易中 在同一个区块中的位置——利用对用户交易的预先了解,有效地从用户那里窃取资金。例如,机器人可能会下买单 在用户之前。然后,它可以利用由资产价格上涨引起的资产价格上涨。 用户的交易。 一些机器人抢先交易,损害普通用户——类似于高频 华尔街交易已经很普遍并且有据可查 [90],如相关 诸如后台运行 [159] 和自动交易模仿 [195] 等攻击。最近甚至出现了将矿工的订单利用系统化的提议[110]。 rollups 等第 2 层技术并不能解决问题,而只是重新集中化 排序,将其置于创建 rollup 的实体手中。 我们的目标之一是向 Chainlink 引入一项名为“公平排序”的服务 服务 (FSS) [137]。 FSS 帮助 smart contract 设计师确保其产品的公平订购 避免对用户交易以及其他类型的交易(例如 oracle 报告传输)进行前置、后台和相关攻击。 FSS 使 DON 能够实现 [144] 中引入的严格的、暂时的秩序公平概念等想法。作为一个附带的好处,FSS 还可以降低用户的网络 费用(例如燃气费)。 简而言之,在 FSS 中,交易通过 DON,而不是直接传播到目标 smart contract。 DON 对交易进行排序,然后转发 他们签订合同。 图 6:FSS 如何发挥作用的示例。图A ⃝展示了矿工如何利用其 集中权力来排序交易,可以交换一对交易:交易1⃝ 在 2⃝ 之前到达,但矿工将其排序在 2⃝ 之后。相比之下,图B⃝显示 DON 如何在 DON 节点之间分散排序过程。如果法定人数为 诚实节点在 2⃝ 之前收到 1⃝,FSS 导致 1⃝ 在链上出现在 2⃝ 之前 — 通过附加合同可执行的序列号来防止矿工重新排序。 图 6 比较了标准挖矿与 FSS。它展示了如何在标准挖矿中,交易排序过程由矿工集中处理,因此受制于 操纵,例如对一对交易的到达进行重新排序 次。相比之下,在 FSS 中,该过程分散在 DON 节点之间。假设 诚实节点的法定数量,FSS 有助于执行策略,例如时间排序 交易,减少矿工和其他实体操纵的机会。 此外,由于用户无需根据Gas价格来争夺优先订购权, 他们可以支付相对较低的汽油价格(而来自 DON 的交易可以批量进行 以节省燃气)。 信任最小化: 我们设计 DONs 的总体目标是促进高度 对 smart contract 和其他 oracle 依赖系统的值得信赖的支持层 通过去中心化、加密工具和加密经济保证。 DON 本身是去中心化的,用户可以从任何可用的 DON 中进行选择 支持他们希望在其上操作或产生额外 DON 的主链 与他们信任的节点委员会。 然而,对于某些应用程序,特别是 smart contracts,Chainlink 用户可能会 支持将 DON 支持的主链视为更值得信赖的信任模型 比 DON 本身。对于此类用户,我们已经或计划将其纳入 Chainlink 网络的架构 一些支持合约的机制 在主链上,以加强 DONs 提供的安全保证,同时在 同时还加强保护,防止数据源损坏的可能性 例如 DON 从中获取数据的 Web 服务器。 我们在第 7 节中描述了这些机制。它们分为五个主要标题: • 数据源身份验证:支持数据提供者进行数字签名的工具 他们的数据,从而加强原产地和 依赖合同。 • DON 少数报告:由 DON 节点的少数子集发出的标志 观察到 DON 中存在多数渎职行为。 • 护栏:主链上的逻辑,用于检测异常情况并暂停 或停止合同执行(或调用其他补救措施)。 • 信任最小化治理:利用逐步发布的更新来促进社区检查,以及分散的紧急干预措施以实现快速 对系统故障的响应。 • 去中心化实体身份验证:使用公钥基础设施 (PKI) 识别 Chainlink 网络中的实体。 图 7 展示了我们的信任最小化目标的概念示意图。 基于激励(加密经济)的安全性: 跨 oracle 节点分散生成报告有助于确保安全,即使某些节点损坏也是如此。
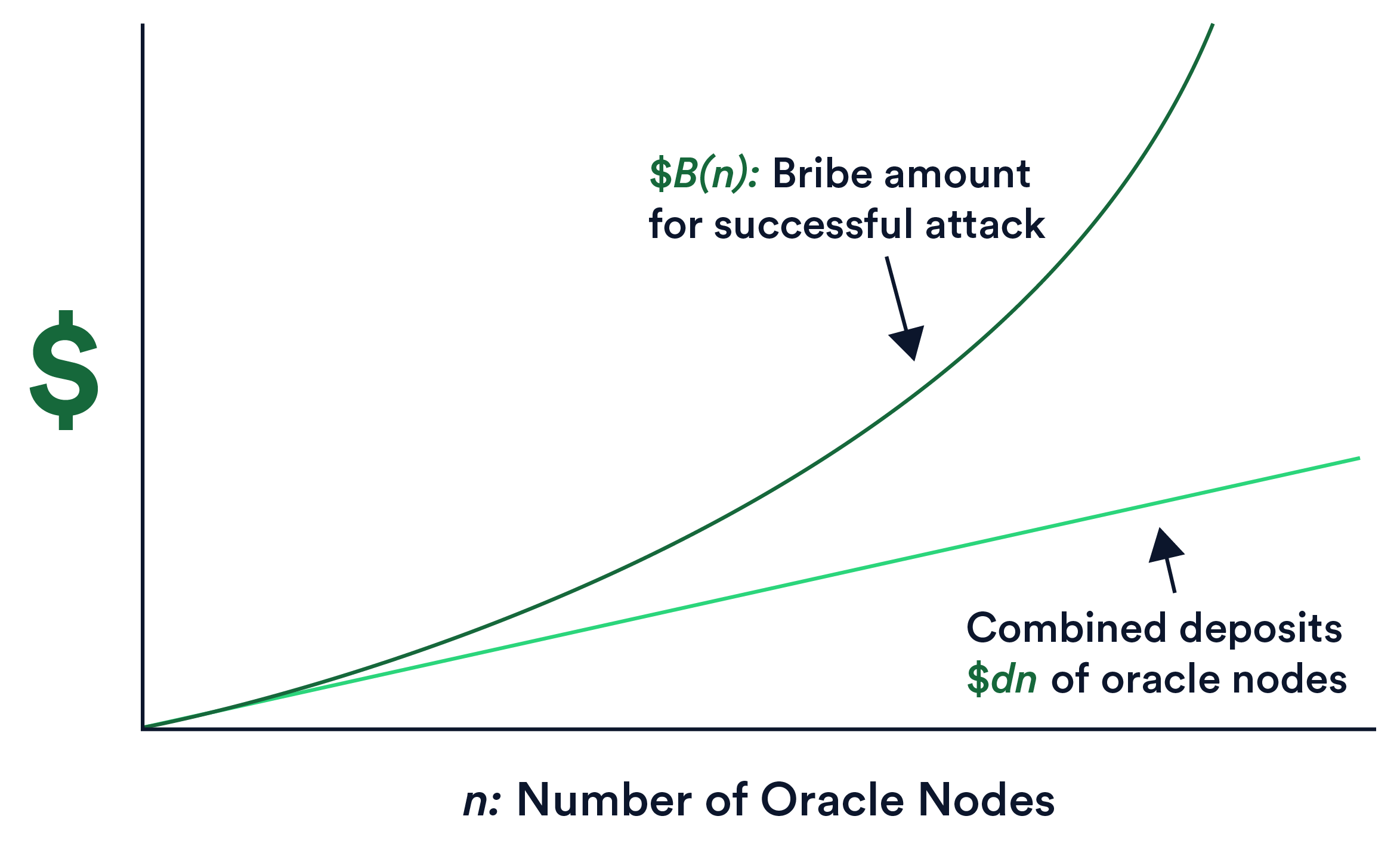
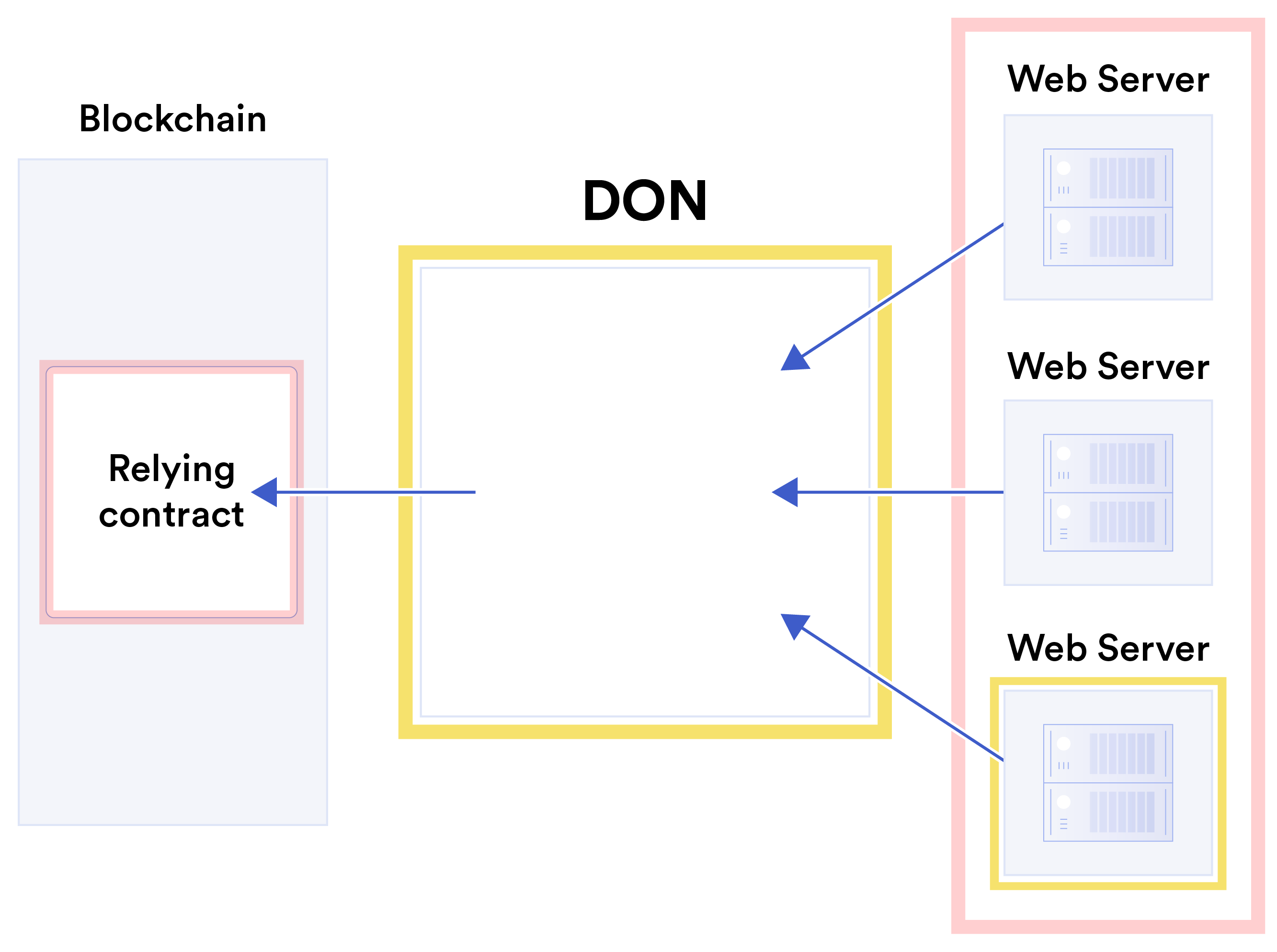
图 7:Chainlink 信任最小化目标的概念描述,即 最大限度地减少用户对 DON 和数据源(例如网络)正确行为的需求 服务器。图中的黄色突出显示表示信任最小化位点:DON 和 单个或少数网络服务器组。粉色高亮显示系统组件 假设高度可信:blockchain 上的合同和大多数 Web 服务器的数量,即 Web 服务器的总数。 然而,同样重要的是确保节点有正确行为的经济激励。质押,即要求节点提供 LINK 押金和削减 如果出现不当行为,(没收)这些存款将在 Chainlink 中发挥关键作用。这是一个重要的激励设计,已在许多 blockchain 中使用, 例如,[81、103、120、204]。 然而,在 Chainlink 中的质押看起来与独立的 staking 有很大不同 blockchains。质押 blockchains 的目的是防止对共识的攻击。它有一个 Chainlink 中的不同目标:确保及时交付正确的 oracle 报告。用于 oracle 网络的精心设计的 staking 系统应该会引发诸如贿赂之类的攻击 即使目标是具有高值的 smart contract,对对手来说也是无利可图的 货币价值。 在本文中,我们提出了 Chainlink 中 staking 的通用方法,具有三个关键 创新点:1. 强大的对抗模型,涵盖现有技术中被忽视的攻击 接近。一个例子就是我们所说的潜在贿赂。这是一种形式 贿赂,确定哪些节点有条件地接受贿赂,例如, 提前向 staking 机制选择的节点提供有保证的贿赂 对于特定角色是随机的(例如触发报告裁决)。 2. 超线性 staking 影响,非正式地意味着要成功,对手的预算 B 美元必须大于所有 oracle 存款的总和 节点。 更准确地说,我们的意思是,作为 n 的函数, \(B(n) ≫\)dn 在 由 n 个 oracle 节点组成的网络,每个节点都有固定的存款金额 $d(更正式地说, \(B(n) is asymptotically larger in n than \)dn)。图8给出了概念图 此属性。 3. 隐性激励框架(IIF),我们设计的激励模型 除了明确存入staking之外,还包括根据经验可衡量的激励措施 资金,包括节点未来的费用机会。 IIF 扩展了以下概念: 超出明确节点存款的权益。 图 8:描述 Chainlink staking 中超线性缩放的概念图。的 对手所需的贿赂 $B(n) 在 n 中的增长速度快于存款总额的增长速度 所有 oracle 节点的 $dn。 我们展示了 IIF 和超线性 staking 共同影响如何导致我们 称之为 oracle 网络经济安全的良性循环。当新用户进入时
系统,增加运行 Chainlink 节点的未来潜在收入, 当前和未来用户的经济安全边际成本下降。在一个政权 需求弹性,成本的降低会激励更多用户使用 网络,在持续的良性循环中持续不断地采用。 注意:虽然本白皮书概述了我们对 Chainlink 发展愿景的重要元素,但它是非正式的,并且包含一些详细的技术细节。我们计划 随着其他功能和方法的发展,发布重点技术论文。 此外,必须强调的是,所提出的愿景的许多要素 这里(扩展改进、保密技术、FSS 等)可以而且将会 甚至在高级 DON 成为基本功能之前就以初步形式部署 Chainlink。 1.3 本文的组织 我们在第 2 节中介绍了我们的安全模型和符号,并概述了去中心化 Oracle Network API 在第 3 节中。在第 4 节中,我们提供了一些示例 DONs 为其提供有吸引力的部署平台的应用程序。读者可以 通过阅读到目前为止,您可以了解本文的大部分关键概念。 本文的其余部分包含更多详细信息。我们描述公平排序 第 5 节中的服务 (FSS) 和第 6 节中的事务执行框架 (TEF)。我们在第 7 节中描述了我们的信任最小化方法。我们考虑了一些 重要的 DON 部署要求,即第 8 节中的功能增量推出、动态账本成员资格和问责制。最后,在第 9 节中,我们给出 我们正在开发的激励设计方法的概述。我们在第 10 节中得出结论。 为了帮助对本文概念了解有限的读者,我们 附录 A 中提供了术语表。我们提供了有关 DON 接口的更多详细信息 和功能见附录 B,并在附录 C 中介绍一些示例适配器。 在附录 D 中,我们描述了信任最小化数据源的加密原语 身份验证称为功能签名,并引入一种称为离散功能签名的新变体。我们讨论与委员会有关的一些考虑因素 附录 F 中 DONs 的选择。
Model dan Sasaran Keamanan
Jaringan Oracle Terdesentralisasi adalah sistem terdistribusi berbeda yang kami harapkan akan demikian pada awalnya biasanya dilaksanakan—walaupun belum tentu—oleh sebuah komite yang berbasis protokol konsensus dan dijalankan oleh sekumpulan oracle node. DON dirancang terutama untuk menambah kemampuan smart contract pada rantai utama dengan oracle laporan dan layanan lainnya, namun dapat menyediakan layanan pendukung yang sama ke sistem nonblockchain lainnya, sehingga tidak perlu diasosiasikan dengan rantai utama tertentu.
Oleh karena itu, model dan properti yang kami pertimbangkan sebagian besar tidak bergantung pada penggunaannya aplikasi khusus dari DON. 2.1 Model Arsitektur Saat Ini Penting untuk ditekankan bahwa Chainlink saat ini bukanlah layanan monolitik, melainkan kerangka kerja tanpa izin yang memungkinkan peluncuran yang berbeda dan independen jaringan oracle node [77]. Jaringan memiliki kumpulan operator node yang heterogen dan desain. Mereka juga mungkin berbeda dalam hal jenis layanan yang mereka berikan, yang mungkin saja berbeda mencakup, misalnya, umpan data, Bukti Cadangan, keacakan yang dapat diverifikasi, dan sebagainya. Lainnya Perbedaannya dapat mencakup tingkat desentralisasi, ukuran jaringan, dan sebagainya nilai terkunci yang didukungnya, dan berbagai parameter tingkat layanan, seperti frekuensi data dan akurasi. Model tanpa izin Chainlink mendorong pertumbuhan ekosistem di mana penyedia layanan mengkhususkan diri pada layanan yang paling mampu mereka berikan kepada masyarakat. Ini Model ini kemungkinan besar akan menghasilkan biaya yang lebih rendah bagi pengguna dan kualitas layanan yang lebih tinggi dibandingkan model yang mengharuskan semua node dan jaringan untuk menyediakan berbagai layanan, sebuah pendekatan yang dapat dengan mudah beralih ke adopsi layanan yang paling sedikit mewakili seluruh sistem penyebut umum sumber daya yang tersedia untuk node. Seiring berkembangnya Chainlink menuju desain berbasis DON di Chainlink 2.0, kami terus melanjutkan mendukung model kerangka kerja terbuka dan tanpa izin, dengan tetap memperhatikan tujuan memberi pengguna berbagai pilihan layanan yang secara global menghasilkan kecocokan terbaik dengan persyaratan aplikasi tertentu. 2.2 Asumsi Konsensus Kami menggunakan istilah Jaringan Oracle Terdesentralisasi untuk mencakup fungsionalitas penuh sistem oracle yang kami jelaskan: baik struktur data yang dipelihara oleh oracle node maupun API inti berlapis di atasnya. Kami menggunakan istilah buku besar (huruf kecil), dilambangkan dengan L, yang berarti data yang mendasarinya struktur yang dikelola oleh DON dan digunakan untuk mendukung layanan tertentu yang disediakannya. Kami menekankan bahwa kerangka DON kami tidak memperlakukan L sebagai sistem yang berdiri sendiri a blockchain: Tujuannya adalah untuk mendukung blockchains dan sistem lainnya. Blockchain adalah, tentu saja, ada satu cara untuk mewujudkan buku besar yang dapat dipercaya, namun ada cara lain. Kami berharap DONs dalam banyak kasus untuk merealisasikan buku besar yang mendasarinya menggunakan Byzantine Fault Tolerant (BFT) sistem, yang jauh lebih tua dari blockchain seperti Bitcoin [174]. Kami menggunakan BFT-jenis notasi dan properti di seluruh makalah untuk kenyamanan, meskipun kami tekankan bahwa DONs dapat direalisasikan menggunakan protokol konsensus tanpa izin. Secara konseptual, buku besar L adalah papan buletin tempat data diurutkan secara linier. Kami memandang buku besar secara umum memiliki beberapa properti utama yang umumnya dianggap berasal darinya blockchains [115]. Buku besar adalah: • Hanya tambahan: Data, setelah ditambahkan, tidak dapat dihapus atau diubah.• Publik: Siapapun dapat membaca isinya, yang konsisten sepanjang waktu di dalamnya pandangan semua pengguna.4 • Tersedia: Buku besar selalu dapat ditulis dan dibaca oleh penulis yang berwenang oleh siapa pun pada waktu yang tepat. Properti alternatif dimungkinkan dalam buku besar untuk DON bila direalisasikan oleh a panitia. Misalnya, akses menulis buku besar mungkin dibatasi untuk pengguna tertentu, seperti mungkin akses baca untuk beberapa aplikasi, yaitu, buku besar tidak perlu bersifat publik seperti yang ditentukan di atas. Demikian pula, aturan buku besar mungkin mengizinkan modifikasi atau redaksi data. Kami tidak melakukannya namun secara eksplisit mempertimbangkan varian tersebut dalam makalah ini. Desain modular DONs dapat mendukung berbagai macam BFT modern protokol, misalnya, Hotstuff[231]. Pilihan yang tepat akan bergantung pada asumsi kepercayaan dan karakteristik jaringan di antara oracle node. DON pada prinsipnya bisa sebagai alternatif gunakan blockchain tanpa izin yang berkinerja tinggi untuk buku besarnya dalam perannya mendukung sistem lapisan-2 atau blockchain yang sama-sama dapat diskalakan. Demikian pula, hibridisasi juga dimungkinkan: DON pada prinsipnya dapat terdiri dari node yang validators dalam sistem yang sudah ada blockchain, misalnya, dalam sistem Proof-of-Stake di mana komite dipilih untuk melaksanakan transaksi, misalnya, [8, 81, 120, 146, 204]. Mode operasi khusus ini memerlukan hal itu node beroperasi dengan cara penggunaan ganda, yaitu beroperasi sebagai blockchain node dan DON node. (Lihat Bagian 8.2 untuk pembahasan mengenai teknik-teknik untuk menjamin kesinambungan perubahan komite dan Lampiran F untuk beberapa peringatan mengenai pemilihan komite acak.) Dalam praktiknya, dalam algoritme BFT modern, node menandatangani pesan secara digital di buku besar. Kami berasumsi untuk kemudahan bahwa L memiliki kunci publik terkait pkL dan isinya ditandatangani oleh kunci pribadi yang sesuai. Notasi umum ini berlaku bahkan ketika data di L ditandatangani menggunakan tanda tangan ambang batas.5 Tanda tangan ambang batas mudah digunakan, karena mereka mengaktifkan identitas tetap untuk DON bahkan dengan perubahan keanggotaan node yang menjalankannya. (Lihat Lampiran B.1.3.) Dengan demikian kita berasumsi bahwa skL dibagikan secara rahasia dengan cara (k, n)-ambang batas untuk beberapa parameter keamanan k, misalnya k = 2f + 1 dan n = 3f + 1, dimana f adalah jumlah node yang berpotensi rusak. (Dengan memilih k dalam hal ini dengan cara ini, kami memastikan bahwa node yang salah tidak dapat mempelajari skL atau melakukan penolakan layanan serangan mencegah penggunaannya.) Pesan pada L berbentuk M = (m, z), dimana m adalah string dan z unik nomor indeks berurutan. Jika memungkinkan, kami menulis pesan dalam bentuk m = ⟨Jenis Pesan : muatan⟩. Jenis pesan MessageType adalah gula sintaksis yang menunjukkan fungsi pesan tertentu. 4Dalam kasus di mana blockchain tanpa finalitas merealisasikan buku besar, inkonsistensi biasanya diabstraksikan pergi dengan mengabaikan blok yang tidak cukup dalam atau “pemangkasan” [115]. 5Dalam praktiknya, beberapa basis kode, misalnya LibraBFT [205], varian dari Hotstuff, saat ini telah mengadopsi tanda tangan multi-tanda tangan, bukan tanda tangan ambang batas, sehingga mengurangi kompleksitas komunikasi rekayasa yang lebih sederhana. Dengan sejumlah biaya tambahan, node oracle dapat menambahkan tanda tangan ambang batas ke pesan ditulis ke L meskipun protokol konsensus yang digunakan untuk L tidak menerapkannya.2.3 Notasi Kami menyatakan himpunan n oracle node yang menjalankan buku besar dengan O = {Oi}n saya=1. Seperti itu kumpulan node sering disebut komite. Untuk mempermudah, kita asumsikan bahwa himpunan oracles mengimplementasikan fungsionalitas DON, yaitu layanan di atas L, identik dengan yang mempertahankan L, tetapi keduanya bisa berbeda. Kita biarkan pki menunjukkan kunci publik dari pemain Oi, dan mainkan kunci pribadi yang sesuai. Kebanyakan algoritma BFT memerlukan setidaknya n = 3f + 1 node, dimana f adalah jumlah node yang berpotensi rusak; node yang tersisa jujur, dalam arti mengikuti protokol persis seperti yang ditentukan. Kami menyebut panitia O jujur jika memenuhi hal tersebut persyaratan, yaitu, memiliki lebih dari 2/3 fraksi node jujur. Kecuali sebaliknya dinyatakan, kami berasumsi bahwa O jujur (dan model korupsi yang statis). Kami menggunakan pkO / skO dapat dipertukarkan dengan pkL/skL, tergantung konteksnya. Kita misalkan σ = Sigpk[m] menunjukkan tanda tangan pada pesan m sehubungan dengan pk, yaitu menggunakan sk kunci pribadi yang sesuai. Misalkan verifikasi(pk, σ, m) →{salah, benar} menunjukkan algoritma verifikasi tanda tangan yang sesuai. (Kami membiarkan pembuatan kunci tersirat di seluruh makalah ini.) Kami menggunakan notasi S untuk menunjukkan sumber data dan S untuk menunjukkan himpunan lengkap sumber nS dalam konteks tertentu. Kami menunjukkan dengan MAINCHAIN kontrak pintar yang diaktifkan blockchain didukung oleh DON. Kami menggunakan istilah kontrak mengandalkan untuk menunjukkan kecerdasan apa pun kontrak di MAINCHAIN yang berkomunikasi dengan DON, dan menggunakan notasi SC untuk menunjukkan kontrak seperti itu. Secara umum kita berasumsi bahwa DON mendukung satu rantai utama MAINCHAIN, meskipun dapat mendukung beberapa rantai seperti itu, seperti yang kami tunjukkan pada contoh di Bagian 4. A DON dapat dan biasanya akan mendukung beberapa kontrak yang mengandalkan MAINCHAIN. (Sebagai disebutkan di atas, DON dapat mendukung layanan non-blockchain.) 2.4 Catatan tentang Model Kepercayaan Seperti disebutkan di atas, DONs dapat dibangun berdasarkan protokol konsensus berbasis komite, dan kami berharap mereka biasanya akan menggunakan protokol seperti itu. Ada banyak argumentasi kuat yang menyatakan hal tersebut salah satu dari dua alternatif, blockchains berbasis komite atau tanpa izin, menyediakan keamanan yang lebih kuat dari yang lain. Penting untuk menyadari bahwa keamanan berbasis komite vs. tanpa izin sistem desentralisasi tidak dapat dibandingkan. Mengompromikan PoW atau PoS blockchain melalui serangan 51% mengharuskan musuh memperoleh sumber daya mayoritas secara sementara dan berpotensi secara anonim, misalnya dengan menyewa hash listrik dalam sistem PoW. Seperti itu serangan dalam praktiknya telah berdampak pada beberapa blockchain [200, 34]. Sebaliknya, mengkompromikan sistem berbasis komite berarti merusak jumlah ambang batas (biasanya sepertiga) dari node-nodenya, dimana node-node tersebut mungkin diketahui publik, mempunyai sumber daya yang baik, dan entitas yang dapat dipercaya. Di sisi lain, sistem berbasis komite (serta “hibrida” tidak memiliki izin sistem yang mendukung komite) dapat mendukung lebih banyak fungsi daripada yang hanya dilakukan secara ketat.sistem tanpa misi. Ini termasuk kemampuan untuk menjaga rahasia yang terus-menerus, seperti penandatanganan dan/atau kunci enkripsi—salah satu kemungkinan dalam desain kami. Kami menekankan bahwa DON pada prinsipnya dapat dibangun berdasarkan komite atau protokol konsensus tanpa izin dan DON yang menerapkan pada akhirnya dapat memilih untuk mengadopsinya pendekatan mana pun. Memperkuat model kepercayaan: Fitur utama Chainlink saat ini adalah kemampuan pengguna untuk melakukannya pilih node berdasarkan catatan desentralisasi dari riwayat kinerjanya, seperti yang telah dibahas di Bagian 3.6.4. Mekanisme staking dan Kerangka Insentif Implisit yang kami perkenalkan di Bagian 9 bersama-sama merupakan rancangan mekanisme yang memiliki cakupan luas dan ketat kerangka kerja yang akan memberdayakan pengguna dengan kemampuan yang jauh lebih luas untuk mengukur keamanan DONs. Kerangka kerja yang sama ini juga akan memungkinkan DONs itu sendiri untuk menegakkan berbagai persyaratan keamanan pada node yang berpartisipasi dan memastikan operasi dalam model kepercayaan yang kuat. Dimungkinkan juga untuk menggunakan alat yang dijelaskan dalam makalah ini untuk DONs guna menerapkan persyaratan model kepercayaan khusus, seperti kepatuhan terhadap persyaratan peraturan. Untuk Misalnya, dengan menggunakan teknik yang dibahas di Bagian 4.3, node dapat menyajikan bukti karakteristik node-operator, misalnya wilayah operasi, yang dapat digunakan untuk membantu menegakkan kepatuhan terhadap, misalnya, Peraturan Perlindungan Data Umum (GDPR) Pasal 3 (“Cakupan Teritorial”) [105]. Kepatuhan seperti itu bisa jadi sulit untuk dilakukan bertemu dalam sistem desentralisasi [45]. Selain itu, di Bagian 7 kami membahas rencana untuk memperkuat ketahanan DONs melalui mekanisme minimalisasi kepercayaan pada rantai utama yang mereka dukung.
安全模型和目标
去中心化预言机网络是一个独特的分布式系统,我们预计它将 最初通常(尽管不一定)由以委员会为基础的委员会实施 共识协议并由一组 oracle 节点运行。 DON 主要设计为 使用 oracle 报告增强主链上 smart contract 的功能 和其他服务,但它可以为其他非blockchain系统提供相同的支持服务,因此不需要与特定的主链相关联。
因此,我们考虑的模型和属性在很大程度上独立于 DON 的特定应用。 2.1 当前的建筑模型 需要强调的是,今天的 Chainlink 不是一个单一的服务,而是 一个无需许可的框架,可以在其中启动独特的、独立的 oracle 节点 [77] 的网络。网络具有异构的节点运营商集, 设计。他们提供的服务类型也可能有所不同,这可以 包括例如数据馈送、储备证明、可验证的随机性等。其他 差异可能包括去中心化程度、网络规模 它支持的锁定值以及各种服务级别参数,例如数据频率 和准确性。 Chainlink 的无需许可模式鼓励生态系统的发展,其中 提供商专注于他们最有能力为社区提供的服务。这个 与模型相比,模型可能会降低用户成本并提高服务质量 要求所有节点和网络提供全方位的服务,一种方法 这可以很容易地转变为全系统采用代表最少的服务 节点可用资源的共同点。 随着 Chainlink 在 Chainlink 2.0 中向基于 DON 的设计发展,我们继续 支持无需许可的开放框架模型,同时考虑到以下目标: 为用户提供一系列服务选择,在全球范围内实现最佳匹配 具有特定的应用要求。 2.2 共识假设 我们使用术语“去中心化预言机网络”来涵盖 我们描述的 oracle 系统: oracle 节点维护的数据结构和 核心 API 位于其之上。 我们使用术语“账本”(小写),用 L 表示,表示基础数据 由 DON 维护的结构,用于支持它提供的特定服务。 我们强调,我们的 DON 框架并不将 L 视为独立系统,例如 a blockchain:其目的是支持blockchains和其他系统。区块链是, 当然,这是实现可信账本的一种方法,但还有其他方法。我们期望 在许多情况下,DONs 使用拜占庭容错来实现其底层账本 (BFT) 系统,其大大早于 blockchain,例如 Bitcoin [174]。我们使用 为了方便起见,尽管我们在整篇论文中使用了 BFT 类型符号和属性 强调 DONs 可以使用无需许可的共识协议来实现。 从概念上讲,账本 L 是一个公告板,上面的数据是线性排序的。 我们通常认为分类账具有一些通常归因于的关键属性 blockchains [115]。账本是: • 仅附加: 数据一旦添加就无法删除或修改。• 公共: 任何人都可以阅读其内容,这些内容在时间上是一致的 所有用户的视图.4 • 可用:账本始终可以由授权写入者写入和读取 任何人及时。 当由 DON 实现时,分类帐中可能存在替代属性 委员会。例如,分类账写访问可能仅限于某些用户,如 可能会读取某些应用程序的访问权限,即分类帐不需要按照定义公开 上面。同样,分类账规则可能允许修改或编辑数据。我们不 然而,本文明确考虑了此类变体。 DONs 的模块化设计可以支持任何多种现代 BFT 协议,例如 Hotstuff[231]。确切的选择将取决于信任假设和 oracle 节点之间的网络特征。原则上 DON 也可以 使用高性能的无许可 blockchain 为其分类帐提供支持 同样可扩展的第 2 层或 blockchain 系统。同样,杂交也是可能的: DON 原则上可以由现有节点中的 validator 节点组成。 blockchain,例如,在选择委员会执行的权益证明系统中 交易,例如 [8, 81, 120, 146, 204]。这种特殊的操作模式要求 节点以双重用途方式运行,即既作为 blockchain 节点又作为 DON 运行 节点。 (参见第 8.2 节,了解确保变革连续性的技术讨论 委员会和附录 F 有关随机委员会选择的一些注意事项。) 实际上,在现代 BFT 算法中,节点对账本上的消息进行数字签名。 为了方便起见,我们假设 L 有一个关联的公钥 pkL 并且其内容 由相应的私钥签名。即使当 L 上的数据使用门限签名进行签名。5 门限签名很方便, 因为即使会员资格发生变化,它们也可以为 DON 提供持久的身份 运行它的节点。 (参见附录 B.1.3。)因此我们假设 skL 是秘密共享的 对于某些安全参数 k,以 (k, n) 阈值方式,例如 k = 2f + 1 且 n = 3f + 1,其中 f 是潜在故障节点的数量。 (通过在此选择 k 这样,我们确保故障节点既无法学习 skL,也无法发起拒绝服务攻击 攻击阻止其使用。) L 上的消息采用 M = (m, z) 的形式,其中 m 是字符串,z 是唯一的 顺序索引号。 在适用的情况下,我们以 m = 的形式编写消息 ⟨消息类型:有效负载⟩。消息类型MessageType是指示特定消息的功能的语法糖。 4在没有最终性的 blockchain 实现账本的情况下,通常会抽象出不一致性 通过忽略深度不足的块或“修剪”[115] 来消除。 5在实践中,一些代码库,例如 LibraBFT [205](Hotstuff 的一个变体)目前已采用 多重签名,而不是阈值签名,以降低通信复杂性为代价 更简单的工程。通过一些额外的成本,oracle 节点可以将阈值签名附加到消息中 写入 L,即使用于 L 的共识协议不使用它们。2.3 符号 我们将运行账本的 n 个 oracle 节点集表示为 O = {Oi}n 我=1。 这样一个 节点集通常称为委员会。为了简单起见,我们假设集合 oracles 实现 DON 功能,即 L 之上的服务,与 保持 L,但它们可以是不同的。我们让 pki 表示公钥 玩家Oi,并ski相应的私钥。 大多数 BFT 算法至少需要 n = 3f + 1 个节点,其中 f 是节点数 潜在的故障节点;其余节点是诚实的,因为它们遵循 协议完全按照规定。如果委员会 O 符合此要求,我们称其为诚实的 要求,即诚实节点的比例大于 2/3。除非另有说明 如上所述,我们假设 O 是诚实的(并且是腐败的静态模型)。我们使用 pkO / skO 与 pkL / skL 可以互换,具体取决于上下文。 我们让 σ = Sigpk[m] 表示消息 m 相对于 pk 的签名,即使用 对应的私钥sk.令 verify(pk, σ, m) →{false, true} 表示相应的签名验证算法。 (我们在整篇论文中都隐含了密钥生成。) 我们使用符号 S 来表示数据源,并使用 S 来表示完整的数据集 给定上下文中的 nS 源。我们用 MAINCHAIN 表示启用了智能合约的 blockchain 由 DON 支持。我们使用术语依赖合约来表示任何智能合约 与 DON 通信的主链上的合约,并使用符号 SC 来 表示这样的合同。 我们通常假设 DON 支持单个主链 MAINCHAIN,尽管它可以支持多个这样的链,如我们在第 4 节的示例中所示。 DON 可以并且通常会支持主链上的多个依赖合约。 (如 如上所述,DON 也可以支持非 blockchain 服务。) 2.4 关于信任模型的说明 如上所述,DONs 可以构建在基于委员会的共识协议之上,并且我们 预计他们会普遍使用此类协议。有许多有力的论据表明 两种选择之一(基于委员会的或无需许可的 blockchains)提供 比其他的安全性更强。 重要的是要认识到基于委员会与未经许可的安全性 去中心化系统是不可通约的。危害 PoW 或 PoS blockchain 通过 51% 攻击,要求对手暂时获得多数资源,并且 可能是匿名的,例如通过在 PoW 系统中租用 hash 电力。这样的 实践中的攻击已经影响了几个 blockchain [200, 34]。相比之下, 损害基于委员会的系统意味着破坏其阈值数量(通常是三分之一)的节点,其中节点可能是公开的、资源丰富的、 和值得信赖的实体。 另一方面,基于委员会的系统(以及“混合”未经许可的系统) 支持委员会的系统)可以支持比严格要求更多的功能无任务系统。这包括维护持久秘密的能力,例如 签名和/或加密密钥——我们设计中的一种可能性。 我们强调 DON 原则上可以建立在基于委员会或 无许可共识协议和 DON 部署者最终可能选择采用 任一方法。 支持信任模型: 如今 Chainlink 的一个关键功能是用户能够 如所讨论的,根据节点性能历史记录的分散记录来选择节点 在第 3.6.4 节中。我们在第 9 节中介绍的 staking 机制和隐性激励框架共同构成了范围广泛且严格的机制设计 该框架将使用户能够极大地扩展衡量 DONs 安全性的能力。同样的框架也将使 DONs 本身成为可能 对参与节点执行各种安全要求并确保运行 在强大的信任模型中。 还可以使用本文中为 DON 描述的工具来强制实施特殊的信任模型要求,例如遵守监管要求。对于 例如,使用第 4.3 节中讨论的技术,节点可以提供以下证据: 节点运营商特征,例如运营区域,可用于帮助 强制遵守《通用数据保护条例》(GDPR) 第 3 条(“领土范围”)[105] 等规定。否则,这种合规性可能会对 在去中心化系统[45]中见面。 此外,在第 7 节中,我们讨论了加强 DONs 稳健性的计划 通过他们支持的主链上的信任最小化机制。
Antarmuka Jaringan Oracle Terdesentralisasi dan Ca-
kemampuan Di sini kami menguraikan secara singkat kemampuan DONs dalam hal sederhana namun kuat antarmuka yang dirancang untuk mereka wujudkan. Aplikasi pada DON terdiri dari executable dan adaptor. Yang dapat dieksekusi adalah sebuah program yang logika intinya adalah program deterministik, analog dengan smart contract. Sebuah executable juga memiliki sejumlah inisiator yang menyertainya, program yang memanggil entri poin dalam logika eksekusi ketika peristiwa yang telah ditentukan terjadi—misalnya, pada waktu tertentu (seperti tugas cron), ketika harga melewati ambang batas, dll.—seperti Keeper (lihat Bagian 3.6.3). Adaptor menyediakan antarmuka ke sumber daya off-chain dan dapat dipanggil oleh baik inisiator atau logika inti dalam executable. Karena perilaku mereka mungkin bergantung pada hal itu sumber daya eksternal, pemrakarsa dan adaptor mungkin berperilaku non-deterministik. Kami menjelaskan antarmuka pengembang DON dan fungsi executable dan adaptor dalam kaitannya dengan tiga sumber daya yang biasanya digunakan untuk mengkarakterisasi sistem komputasi: jaringan, komputasi, dan penyimpanan. Kami memberikan gambaran singkat tentang masing-masing hal ini sumber daya di bawah ini dan berikan rincian lebih lanjut di Lampiran B.
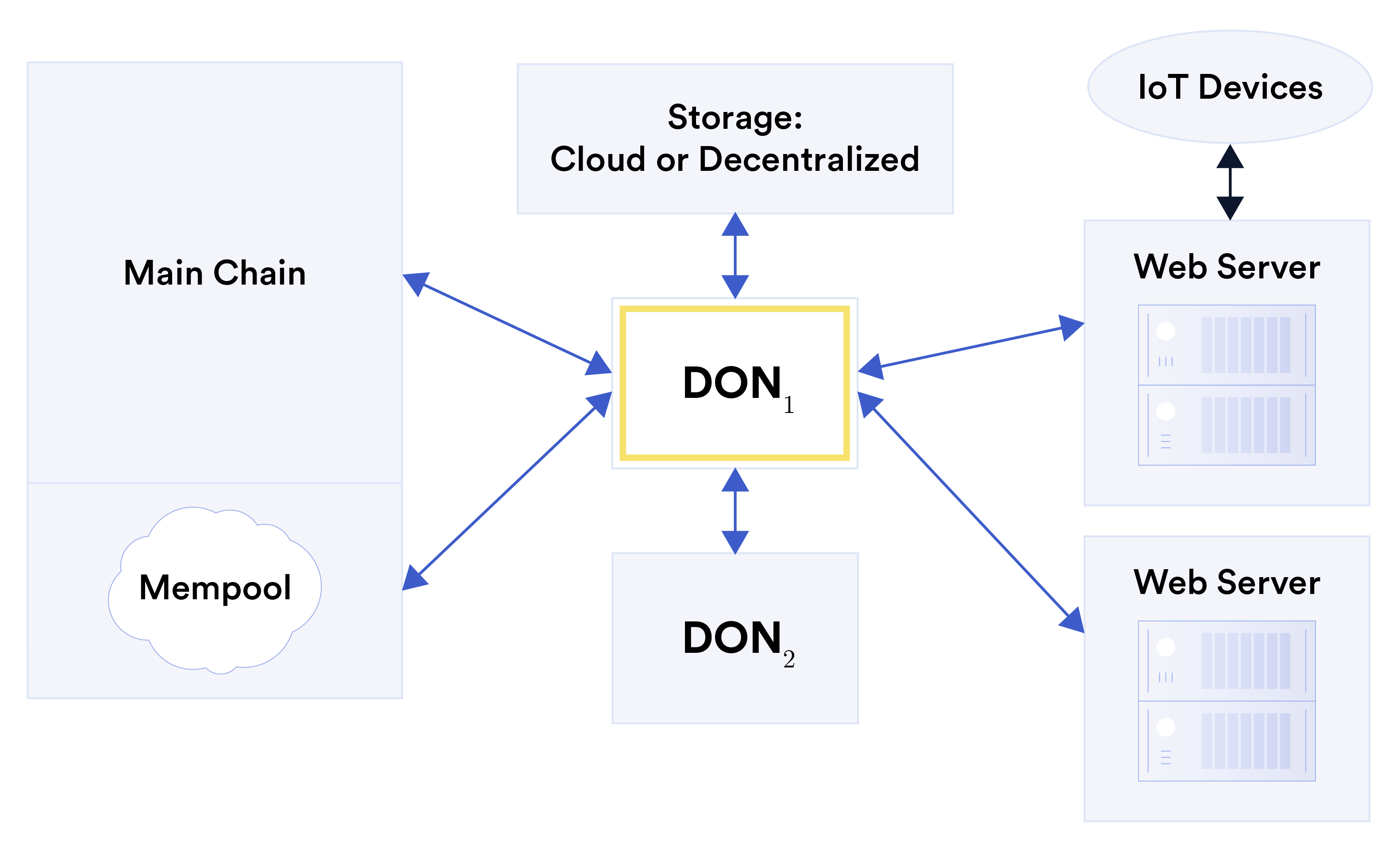
3.1 Jaringan Adaptor adalah antarmuka yang dapat digunakan oleh executable yang berjalan pada DON untuk mengirim dan menerima data dari sistem off-DON. Adaptor dapat dipandang sebagai generalisasi dari adaptor yang digunakan di Chainlink hari ini [20]. Adaptor mungkin bersifat dua arah—yaitu tidak bisa hanya menarik, tetapi mendorong data dari DON ke server web. Mereka mungkin juga memanfaatkan protokol terdistribusi serta fungsi kriptografi seperti multi-pihak yang aman komputasi. Gambar 9: Adaptor yang menghubungkan DON, dilambangkan DON1, dengan serangkaian sumber daya berbeda, termasuk DON lainnya, dilambangkan DON2, blockchain (rantai utama) dan rangkaiannya mempool, penyimpanan eksternal, server web, dan perangkat IoT (melalui server web). Contoh sumber daya eksternal yang dapat digunakan untuk membuat adaptor ditampilkan pada Gambar 9. Ini termasuk: • Blockchain: Adaptor dapat menentukan cara mengirim transaksi ke blockchain dan cara membaca blok, transaksi individu, atau keadaan lain darinya. Sebuah adaptor juga dapat didefinisikan untuk mempool blockchain. (Lihat Bagian 3.5.) • Server web: Adaptor dapat menentukan API yang dapat digunakan untuk mengambil data dari server web, termasuk sistem lama yang tidak diadaptasi secara khusus berinteraksi dengan DONs. Adaptor tersebut juga dapat menyertakan API untuk mengirim data server seperti itu. Server web yang terhubung dengan DON dapat berfungsi sebagai gerbang ke sumber daya tambahan, seperti perangkat Internet-of-Things (IoT).• Penyimpanan eksternal: Adaptor dapat menentukan metode untuk membaca dan menulis ke penyimpanan layanan di luar DON, seperti sistem file terdesentralisasi [40, 188] atau cloud penyimpanan. • DONs lainnya: Adaptor dapat mengambil dan mengirimkan data antara DONs. Kami berharap penerapan awal DONs akan mencakup serangkaian elemen penyusun adaptor untuk sumber daya eksternal yang umum digunakan dan selanjutnya akan memungkinkan DON-spesifik adaptor yang akan dipublikasikan oleh DON node. Saat smart contract pengembang menulis adaptor saat ini, kami berharap mereka akan membuat adaptor yang lebih kuat lagi dengan menggunakan teknologi canggih ini fungsionalitas. Kami berharap pada akhirnya pengguna dapat membuat adaptor baru di a cara tanpa izin. Beberapa adaptor harus dibangun sedemikian rupa sehingga menjamin persistensi dan ketersediaan sumber daya eksternal yang dikendalikan oleh DON. Misalnya, penyimpanan cloud mungkin memerlukan pemeliharaan akun layanan cloud. Selain itu, DON dapat berfungsi pengelolaan kunci privat yang terdesentralisasi atas nama pengguna (misalnya, [160]) dan/atau executable. Akibatnya, DON mampu mengendalikan sumber daya, seperti mata uang kripto, yang dapat digunakan, misalnya, untuk mengirim transaksi pada target blockchain. Lihat Lampiran B.1 untuk rincian lebih lanjut tentang adaptor DON, seperti Lampiran C untuk beberapa contoh adaptor. 3.2 Perhitungan Eksekusi adalah unit kode dasar pada DON. Yang dapat dieksekusi adalah pasangan exec = (logika, init). Di sini, logika adalah program deterministik dengan sejumlah entri yang ditentukan poin (logic1, logic2, . . . , logicℓ) dan init adalah sekumpulan inisiator yang sesuai (init1, init2, . . . , init). Untuk memastikan kemampuan audit penuh dari DON, logika yang dapat dieksekusi menggunakan buku besar yang mendasari L untuk semua input dan output. Jadi, misalnya, adaptor apa pun data yang berfungsi sebagai input ke executable harus disimpan terlebih dahulu di L. Pemrakarsa: Inisiator di Chainlink hari ini menyebabkan eksekusi pekerjaan yang bergantung pada peristiwa Chainlink simpul [21]. Inisiator di DONs berfungsi dengan cara yang hampir sama. Namun, inisiator DON secara khusus dikaitkan dengan executable. Seorang inisiator mungkin bergantung pada peristiwa atau keadaan eksternal, pada waktu saat ini, atau pada predikat pada keadaan DON. Dengan ketergantungan mereka pada peristiwa, tentu saja inisiator dapat berperilaku non-deterministik (seperti tentu saja adaptor). Inisiator dapat mengeksekusi dalam DON node individual sehingga tidak perlu bergantung pada adaptor. (Lihat Contoh 1 di bawah.) Inisiator adalah fitur penting yang membedakan executable dari smart contracts. Karena executable dapat dijalankan sebagai respons terhadap inisiator, maka executable dapat beroperasi secara efektif secara mandiri, tentu saja dengan perluasan kontrak hibrida yang menggabungkan kontrak yang dapat dieksekusi. Salah satu bentuk inisiator saat ini adalah Chainlink Keeper yang menyediakan transaksilayanan otomatisasi, memicu eksekusi smart contract—seperti likuidasi pinjaman tanpa jaminan dan eksekusi perdagangan limit-order—berdasarkan laporan oracle. Mudahnya, inisiator di DONs juga dapat dilihat sebagai cara untuk menentukan perjanjian layanan yang berlaku untuk executable, karena perjanjian tersebut mendefinisikan keadaan di bawah yang mana DON harus menyebutnya. Contoh berikut mengilustrasikan cara kerja inisiator dalam executable: Contoh 1 (Umpan harga yang dipicu oleh deviasi). smart contract SC mungkin memerlukan yang baru data harga pakan (lihat Bagian 3.6.3) setiap kali ada perubahan besar, misalnya 1%, pada nilai tukar antara sepasang aset, misalnya ETH-USD. Harga sensitif terhadap volatilitas feed didukung di Chainlink saat ini, namun ada baiknya kita melihat bagaimana feed tersebut dapat didukung direalisasikan pada DON melalui execfeed yang dapat dieksekusi. Execfeed yang dapat dieksekusi mempertahankan harga ETH-USD terbaru di L, di bentuk rangkaian ⟨HargaBaru : j, r⟩entri, dengan j adalah indeks yang ditambah dengan setiap pembaruan harga. Inisiator init1 menyebabkan setiap node Oi memantau harga ETH-USD saat ini penyimpangan minimal 1% dari harga yang disimpan terakhir r dengan indeks j. Setelah mendeteksi penyimpangan tersebut, Oi menulis pandangan terkininya tentang harga baru ke L menggunakan entri formulir ⟨PriceView : i, j + 1, ri⟩. Inisiator kedua dimulai ketika setidaknya ada k entri PriceView dengan harga baru nilai untuk indeks j + 1 yang dibuat oleh node berbeda telah terakumulasi di L. Kemudian, init2 memanggil logika titik masuk2 untuk menghitung median ρ dari k nilai tampilan harga baru yang valid dan menulis nilai baru ⟨NewPrice : j + 1, ρ⟩to L . (Secara operasional, node dapat bergiliran sebagai penulis yang ditunjuk.) Inisiator ketiga, init3, mengawasi entri NewPrice di L. Setiap kali ada laporan baru ⟨Harga Baru : j, r⟩muncul di sana, memanggil logika titik masuk3 yang mendorong (j, r) ke SC menggunakan adaptor. Seperti yang telah kami catat, executable memiliki kemampuan yang serupa dengan smart contract. Namun, selain kinerjanya yang lebih tinggi, kontrak ini berbeda dari kontrak rantai utama pada umumnya dalam dua cara penting: 1. Kerahasiaan: Sebuah executable dapat melakukan komputasi rahasia, yaitu, program rahasia dapat memproses masukan teks yang jelas, atau program yang diterbitkan dapat memproses data masukan rahasia, atau kombinasi keduanya. Dalam model sederhana, data rahasia bisa diakses oleh DON node, yang menyembunyikan hasil antara dan hanya mengungkapkan nilai yang diproses dan dibersihkan ke MAINCHAIN. Data sensitif juga dapat disembunyikan dari DONs itu sendiri: DONs dimaksudkan untuk mendukung pendekatan seperti itu sebagai komputasi multi-pihak, misalnya, [42, 157], dan lingkungan eksekusi tepercaya (TEEs) [84, 133, 152, 229] untuk tujuan ini.6 6Selain itu, menjaga kerahasiaan executable sehubungan dengan DON node juga dimungkinkan, meskipun hal ini hanya praktis saat ini untuk executable non-trivial yang menggunakan TEE.2. Peran pendukung: Sebuah executable dimaksudkan untuk mendukung smart contracts pada main rantai, daripada menggantinya. Sebuah executable memiliki beberapa keterbatasan yaitu a smart contract tidak: (a) Model kepercayaan: Sebuah executable beroperasi dalam model kepercayaan yang ditentukan oleh DON: Eksekusi yang benar bergantung pada perilaku jujur O. (A main namun, rantai dapat memberikan beberapa pagar pengaman terhadap DON penyimpangan, seperti dibahas di Bagian 7.3.) (b) Akses aset: DON dapat mengontrol akun di blockchain—dan dengan demikian mengontrol aset di dalamnya melalui adaptor. Tapi DON tidak bisa secara otoritatif mewakili aset yang dibuat pada rantai utama, misalnya Ether atau ERC20 tokens, karena rantai asal mereka menyimpan catatan resmi kepemilikan mereka. (c) Siklus Hidup: DON dapat dibuat dengan sengaja dengan masa hidup terbatas, seperti ditentukan oleh perjanjian tingkat layanan on-chain antara DONs dan pemilik mengandalkan kontrak. Sebaliknya, Blockchain dimaksudkan untuk berfungsi sebagai sistem arsip permanen. Lihat Lampiran B.2 untuk rincian lebih lanjut tentang perhitungan DON. 3.3 Penyimpanan Sebagai sistem berbasis komite, DON dapat menyimpan data dalam jumlah sedang secara terus-menerus di L dengan biaya yang jauh lebih rendah daripada blockchain tanpa izin. Selain itu, melalui adaptor, DONs dapat mereferensikan sistem desentralisasi eksternal untuk penyimpanan data, misalnya Filecoin [85], dan dengan demikian dapat menghubungkan sistem tersebut ke smart contracts. Opsi ini khususnya menarik untuk data massal sebagai cara untuk mengatasi masalah “penggembungan” yang meluas blockchain sistem. DONs dapat menyimpan data secara lokal atau eksternal untuk digunakan dalam layanan yang didukung secara khusus. DON juga dapat menggunakan data tersebut secara rahasia, komputasi pada data yang: (1) dibagikan secara rahasia di DON node atau dienkripsi di bawah kunci yang dikelola oleh DON node dengan cara yang sesuai untuk komputasi multi-pihak yang aman atau enkripsi sebagian atau seluruhnya homomorfik; atau (2) dilindungi menggunakan eksekusi tepercaya lingkungan. Kami berharap DONs akan mengadopsi model manajemen memori sederhana yang umum digunakan sistem kontrak pintar: Sebuah executable hanya dapat menulis ke memorinya sendiri. Dapat dieksekusi mungkin, bagaimanapun, membaca dari memori executable lainnya. Lihat Lampiran B.3 untuk rincian lebih lanjut tentang penyimpanan DON. 3.4 Kerangka Eksekusi Transaksi (TEF) DONs dimaksudkan untuk mendukung kontrak pada rantai utama MAINCHAIN (atau pada beberapa rantai utama). Kerangka Eksekusi Transaksi (TEF), dibahas secara rincidi Bagian 6, adalah pendekatan tujuan umum untuk pelaksanaan kontrak secara efisien SC melintasi MAINCHAIN dan DON. TEF dimaksudkan untuk mendukung FSS dan layer-2 teknologi—secara bersamaan, jika diinginkan. Memang kemungkinan besar akan berfungsi sebagai kendaraan utama untuk penggunaan FSS (dan oleh karena itu, kami tidak membahas FSS lebih lanjut di bagian ini). Singkatnya, di TEF kontrak target asli SC dirancang atau dikembangkan untuk MAINCHAIN difaktorkan ulang menjadi kontrak hibrid. Refactoring ini menghasilkan keduanya saling beroperasi bagian dari kontrak hybrid: kontrak MAINCHAIN SCa yang kami rujuk untuk kejelasan dalam konteks TEF sebagai kontrak jangkar dan eksekutif yang dapat dieksekusi pada DON. Itu kontrak SCa menjaga aset pengguna, melaksanakan transisi status otoritatif, dan juga menyediakan pagar pengaman (lihat Bagian 7.3) terhadap kegagalan di DON. Para eksekutif yang dapat dieksekusi mengurutkan transaksi dan menyediakan data oracle terkait untuk transaksi tersebut. Itu bisa dibundel transaksi untuk SCa dengan salah satu dari beberapa cara—misalnya, menggunakan berbasis validitas atau rollups yang optimis, eksekusi rahasia oleh DON, dll. Kami berharap dapat mengembangkan alat yang memudahkan pengembang untuk mempartisi kontrak SC ditulis dalam bahasa tingkat tinggi menjadi potongan-potongan logika MAINCHAIN dan DON, SCa dan masing-masing eksekutif, yang menulis dengan aman dan efisien. Menggunakan TEF untuk mengintegrasikan skema transaksi berkinerja tinggi dengan kinerja tinggi oracles merupakan bagian integral dari pendekatan penskalaan oracle kami. 3.5 Layanan Mempool Fitur lapisan aplikasi penting yang ingin kami terapkan pada DONs sebagai dukungan FSS dan TEF adalah Mempool Services (MS). MS dapat dipandang sebagai adaptor, tapi yang memiliki dukungan kelas satu. MS menyediakan dukungan untuk pemrosesan transaksi yang kompatibel dengan warisan. Dalam penggunaan ini, MS menyerap dari mempool rantai utama transaksi-transaksi yang dimaksudkan untuk kontrak target SC di RANTAI UTAMA. MS kemudian meneruskan transaksi ini ke executable di DON, di mana mereka diproses dengan cara yang diinginkan. Data MS dapat digunakan oleh DON untuk membuat transaksi yang kemudian dapat diteruskan langsung ke SC dari DON atau ke kontrak lain yang memanggil SC. Misalnya, DON dapat meneruskan transaksi dipanen melalui MS, atau dapat menggunakan data MS untuk menetapkan harga gas untuk transaksi yang dikirimkannya RANTAI UTAMA. Karena memonitor mempool, MS dapat memperoleh transaksi dari pengguna yang berinteraksi langsung dengan SC. Dengan demikian pengguna dapat terus melakukan transaksi menggunakan perangkat lunak lama, yaitu aplikasi yang tidak mengetahui keberadaan MS dan konfigurasi MS kontrak. (Dalam hal ini, SC harus diubah untuk mengabaikan transaksi asli dan hanya menerima yang diproses oleh MS, untuk menghindari pemrosesan ganda.) Untuk digunakan dengan kontrak target SC, MS dapat digunakan dengan FSS dan/atau TEF.3.6 Batu Loncatan: Kemampuan Chainlink yang Ada 3.6.1 Pelaporan Off-Chain (OCR) Pelaporan Off-Chain (OCR) [60] adalah mekanisme di Chainlink untuk oracle agregasi dan transmisi laporan ke SC kontrak yang mengandalkan. Baru-baru ini diterapkan dengan harga Chainlink jaringan umpan, ini mewakili langkah pertama menuju DONs penuh. Pada intinya, OCR adalah protokol BFT yang dirancang untuk beroperasi secara sinkron sebagian jaringan. Ini memastikan keaktifan dan kebenaran di hadapan f < n/3 secara sewenang-wenang node yang salah, menjamin properti siaran Bizantium yang andal, tetapi sebenarnya tidak protokol konsensus BFT yang lengkap. Node tidak menyimpan log pesan yang ada konsisten dalam arti mewakili buku besar yang identik dalam semua pandangannya, dan pemimpin protokol dapat mengelak tanpa melanggar keselamatan. OCR saat ini dirancang untuk jenis pesan tertentu: agregasi median (setidaknya 2f +1) nilai yang dilaporkan oleh node yang berpartisipasi. Ini memberikan jaminan penting laporan yang dihasilkannya untuk SC, disebut laporan yang dibuktikan: Nilai median dalam sebuah laporan yang dibuktikan laporan sama dengan atau terletak di antara nilai yang dilaporkan oleh dua node jujur. Properti ini adalah kondisi keamanan utama untuk OCR. Pemimpin mungkin mempunyai pengaruh terhadap median nilai dalam laporan yang dibuktikan, tetapi hanya tunduk pada kondisi kebenaran ini. OCR bisa diperluas ke jenis pesan yang mengumpulkan nilai dengan cara berbeda. Sementara tujuan keaktifan dan kebenaran jaringan Chainlink saat ini tidak memerlukannya OCR merupakan protokol konsensus yang lengkap, namun memerlukan OCR untuk menyediakan beberapa bentuk fungsi tambahan yang tidak ada dalam protokol BFT konvensional, terutama: 1. Laporan off-chain semua atau tidak sama sekali disiarkan: OCR memastikan bahwa laporan telah dibuktikan dibuat tersedia dengan cepat untuk semua node yang jujur atau tidak sama sekali. Ini adalah sebuah keadilan properti yang membantu memastikan bahwa node yang jujur memiliki peluang untuk berpartisipasi dalam transmisi laporan yang dibuktikan. 2. Transmisi yang andal: OCR memastikan, bahkan jika ada yang salah atau berbahaya node, bahwa semua laporan dan pesan OCR dikirimkan ke SC dalam jangka waktu tertentu, interval waktu yang telah ditentukan sebelumnya. Ini adalah properti keaktifan. 3. Minimalkan kepercayaan berbasis kontrak: SC memfilter laporan yang dihasilkan OCR yang berpotensi salah, misalnya, jika nilai yang dilaporkan menyimpang secara signifikan dari nilai lain. yang baru saja diterima. Hal ini merupakan bentuk penegakan kebenaran ekstra protokol. Ketiga properti ini akan memainkan peran alami dalam DONs. Siaran off-chain semua atau tidak sama sekali (DON) merupakan landasan penting untuk jaminan ekonomi kripto seputar transmisi yang andal, yang pada gilirannya merupakan properti adaptor yang penting. Percaya minimalisasi di SC adalah jenis pagar pembatas, seperti yang dibahas dalam Bagian 7.3. OCR juga memberikan dasar untuk penerapan operasional dan penyempurnaan protokol BFT di jaringan oracle Chainlink dan dengan demikian, seperti disebutkan di atas, merupakan jalan menuju fungsionalitas DONs.3.6.2 DECO dan Town Crier DECO [234] dan Town Crier [233] adalah sepasang teknologi terkait yang saat ini sedang dikembangkan dikembangkan di jaringan Chainlink. Sebagian besar server web saat ini memungkinkan pengguna untuk terhubung melalui saluran aman menggunakan protokol disebut Keamanan Lapisan Transportasi (TLS) [94]. (HTTPS menunjukkan varian HTTP itu diaktifkan dengan TLS, yaitu URL yang diawali dengan “https” menunjukkan penggunaan TLS untuk keamanan.) Namun, sebagian besar server yang mendukung TLS memiliki batasan penting: Server tidak menandatangani secara digital data. Akibatnya, pengguna atau Prover tidak dapat menampilkan data yang diterimanya dari server kepada pihak ketiga atau Pemverifikasi, seperti oracle atau smart contract, dengan cara yang menjamin keaslian datanya. Bahkan jika server menandatangani data secara digital, masih ada masalah kerahasiaan. Seorang Prover mungkin ingin menyunting atau mengubah data sensitif sebelum menyajikannya kepada a Pemverifikasi. Namun, tanda tangan digital dirancang khusus untuk membatalkan validitas data yang dimodifikasi. Dengan demikian, hal-hal tersebut mencegah Prover melakukan perubahan demi menjaga kerahasiaan ke data. (Lihat Bagian 7.1 untuk diskusi lebih lanjut.) DECO dan Town Crier dirancang untuk memungkinkan Prover memperoleh data dari web server dan menyajikannya kepada Verifikasi dengan cara yang menjamin integritas dan kerahasiaan. Kedua sistem menjaga integritas dalam arti memastikan bahwa data disajikan oleh Prover ke Verifier berasal secara asli dari server target. Mereka mendukung kerahasiaan dalam arti mengizinkan Prover untuk menyunting atau mengubah data (sambil tetap menjaga integritas). Fitur utama dari kedua sistem ini adalah bahwa keduanya tidak memerlukan modifikasi apa pun pada a server web sasaran. Mereka dapat beroperasi dengan server apa pun yang mendukung TLS. Faktanya, mereka transparan ke server: Dari sudut pandang server, Provernya transparan membangun koneksi biasa. Kedua sistem tersebut memiliki tujuan yang serupa, namun berbeda dalam model kepercayaan dan implementasinya seperti yang akan kami jelaskan secara singkat. DECO memanfaatkan protokol kriptografi secara mendasar untuk mencapai integritasnya dan sifat kerahasiaan. Saat membuat sesi dengan server target menggunakan DECO, Prover terlibat pada saat yang sama dalam protokol interaktif dengan Pemverifikasi. Protokol ini memungkinkan Pemeriksa membuktikan kepada Pemverifikasi bahwa ia telah menerimanya sepotong data D tertentu dari server selama sesi saat ini. Pepatah bisa sebagai alternatif, berikan kepada Pemverifikasi bukti tanpa pengetahuan tentang beberapa properti D dan dengan demikian tidak mengungkapkan D secara langsung. Dalam penggunaan DECO pada umumnya, pengguna atau satu node dapat mengekspor data D dari data pribadi sesi dengan server web ke semua node di DON. Alhasil, DON penuh bisa membuktikan keaslian D (atau fakta yang diturunkan dari D melalui bukti tanpa pengetahuan). Selain contoh aplikasi yang diberikan nanti di makalah ini, kemampuan ini juga bisa digunakan untuk memperkuat akses integritas tinggi ke sumber data dengan DON. Meski hanya satu simpul memiliki akses langsung ke sumber data—misalnya karena perjanjian eksklusif dengan penyedia data—masih mungkin bagi seluruh DON untuk membuktikan kebenarannyalaporan yang dikeluarkan oleh node itu. Town Crier mengandalkan penggunaan lingkungan eksekusi tepercaya (TEE) seperti Intel SGX. Singkatnya, TEE berfungsi sebagai semacam kotak hitam yang mengeksekusi aplikasi dalam a cara tamperproof dan rahasia. Pada prinsipnya, bahkan pemilik host yang mana TEE yang sedang berjalan tidak dapat (tanpa terdeteksi) mengubah aplikasi yang dilindungi TEE juga melihat status aplikasi, yang mungkin berisi data rahasia. Town Crier dapat mencapai semua fungsi DECO dan banyak lagi. DECO membatasi Prover untuk berinteraksi dengan satu Verifier. Sebaliknya, Town Crier mengaktifkan sebuah Prover untuk menghasilkan bukti yang dapat diverifikasi secara publik pada data D yang diambil dari server target, yaitu, bukti bahwa siapa pun, bahkan smart contract, dapat memverifikasi secara langsung. Town Crier bisa juga menyerap dan memanfaatkan rahasia dengan aman (misalnya, kredensial pengguna). Keterbatasan utama Town Crier adalah ketergantungannya pada TEEs. TEE produksi punya baru-baru ini terbukti memiliki sejumlah kerentanan serius, meskipun teknologi ini masih dalam tahap awal dan pasti akan matang. Lihat Lampiran B.2.1 dan B.2.2 untuk diskusi lebih lanjut tentang TEE. Untuk beberapa contoh penerapan DECO dan Town Crier, lihat Bagian 4.3, 4.5 dan 9.4.3 dan Lampiran C.1. 3.6.3 Layanan Chainlink On-Chain yang Ada Chainlink oracle jaringan menyediakan sejumlah layanan utama di berbagai blockchains dan sistem desentralisasi lainnya saat ini. Evolusi lebih lanjut seperti yang dijelaskan dalam whitepaper ini akan memberikan layanan-layanan yang ada dengan kemampuan tambahan dan mencapai. Tiga contohnya adalah: Umpan data: Saat ini, mayoritas Chainlink pengguna mengandalkan smart contracts penggunaan data feed. Ini adalah laporan tentang nilai terkini dari data penting menurut ke sumber off-chain yang otoritatif. Misalnya, feed harga adalah feed yang melaporkan harga aset—mata uang kripto, komoditas, valas, indeks, ekuitas, dll.—menurut pertukaran atau layanan agregasi data. Umpan-umpan seperti itu saat ini sudah membantu mengamankan miliaran dolar dolar dalam nilai on-chain melalui penggunaannya dalam sistem DeFi seperti Aave [147] dan Sintetis [208]. Contoh lain dari data feed Chainlink mencakup data cuaca asuransi tanaman parametrik [75] dan data pemilu [93], dan masih banyak lagi. Penerapan DONs dan teknologi lain yang dijelaskan dalam makalah ini akan meningkatkan penyediaan data feed di jaringan Chainlink dalam banyak hal, termasuk: • Penskalaan: OCR dan selanjutnya DON bertujuan untuk memungkinkan Chainlink layanan ditingkatkan secara dramatis di banyak blockchain yang mereka dukung. Misalnya saja yang kita harapkan bahwa DONs akan membantu meningkatkan jumlah data feed yang disediakan oleh node yang menggunakan Chainlink dari 100 hingga 1000 dan seterusnya. Penskalaan seperti itu akan membantu Chainlink ekosistem mencapai tujuannya untuk menyediakan data yang relevan dengan smart contract secara komprehensif dan memenuhi serta mengantisipasi kebutuhan saat ini dan masa depan.• Peningkatan keamanan: Dengan menyimpan laporan perantara, DONs akan menyimpan catatan perilaku node untuk pemantauan dan pengukuran kinerja dan akurasi dengan ketelitian tinggi, memungkinkan landasan empiris yang kuat untuk sistem reputasi untuk Chainlink node. FSS dan TEF akan memungkinkan penggabungan feed harga dengan data transaksi dengan cara yang fleksibel yang mencegah serangan seperti front-running. (Eksplisit) staking akan meningkatkan perlindungan keamanan kriptoekonomi yang ada umpan data. • Kelincahan feed: Seperti sistem blockchain-agnostik (bahkan, lebih luas lagi, sistem agnostik konsumen), DONs dapat memfasilitasi penyediaan feed data dalam jumlah yang banyak dari sistem yang mengandalkan. Satu DON dapat mendorong umpan tertentu secara bersamaan ke satu set dari blockchain yang berbeda, menghilangkan kebutuhan akan jaringan oracle per rantai dan memungkinkan penerapan cepat feed yang ada pada blockchain baru dan tambahan feed di blockchain yang saat ini dilayani. • Kerahasiaan: Kemampuan untuk melakukan komputasi umum dalam DON memungkinkan komputasi pada data sensitif dilakukan secara off-chain, menghindari on-chain paparan. Selain itu, dengan menggunakan DECO atau Town Crier, hal ini dapat dicapai kerahasiaan yang lebih kuat, memungkinkan pembuatan laporan berdasarkan data yang bukan data terkena bahkan ke DON node. Lihat Bagian 4.3 dan Bagian 4.5 untuk contohnya. Fungsi Acak yang Dapat Diverifikasi (VRF): Beberapa jenis DApps memerlukan sumber keacakan yang dapat diverifikasi untuk memungkinkan verifikasi pengoperasian yang adil. Token Non-Fungible (NFTs) adalah contohnya. Kelangkaan fitur NFT di Aavegotchi [23] dan Axie Infinity [35] ditentukan oleh Chainlink VRF, begitu pula distribusinya dari NFTs melalui pengundian berbasis tiket di Kartu Ether [102]; berbagai macam DApps game yang hasilnya diacak; dan instrumen keuangan yang tidak konvensional, misalnya permainan tabungan tanpa rugi seperti PoolTogether [89], yang mengalokasikan dana ke pemenang acak. Aplikasi blockchain dan non-blockchain lainnya juga memerlukan keamanan sumber keacakan, termasuk pemilihan komite dengan sistem desentralisasi dan pelaksanaan lotere. Meskipun blok hashes dapat berfungsi sebagai sumber keacakan yang tidak dapat diprediksi, blok tersebut rentan terhadap manipulasi oleh penambang yang bermusuhan (dan sampai batas tertentu oleh pengguna yang mengirimkan transaksi). Chainlink VRF [78] menawarkan alternatif yang jauh lebih aman. Sebuah oracle memiliki pasangan kunci privat/publik terkait (sk, pk) yang kunci privatnya dipertahankan secara off-chain dan pk kunci publiknya dipublikasikan. Untuk menampilkan nilai acak, it menerapkan sk pada benih yang tidak dapat diprediksi x yang dilengkapi dengan kontrak yang dapat diandalkan (misalnya, blok hash dan parameter khusus DApp) menggunakan fungsi F, menghasilkan y = Fsk(x) bersama dengan a bukti kebenarannya. (Lihat [180] untuk VRF yang tersedia di Chainlink.) Apa yang membuat VRF yang dapat diverifikasi adalah fakta bahwa dengan pengetahuan tentang pk, dimungkinkan untuk memeriksa kebenaran pembuktian dan juga y. Oleh karena itu, nilai y tidak dapat diprediksi oleh an musuh yang tidak dapat memprediksi x atau mempelajari sk dan tidak layak untuk dimanipulasi oleh layanan.Chainlink VRF dapat dipandang hanya sebagai salah satu dari serangkaian aplikasi yang melibatkan penyimpanan kunci pribadi secara offchain. Secara umum, DONs dapat menawarkan keamanan, penyimpanan terdesentralisasi dari kunci individual untuk aplikasi dan/atau pengguna, dan digabungkan kemampuan ini dengan komputasi umum. Hasilnya adalah sejumlah aplikasi, tentu saja yang beberapa contohnya kami berikan pada tulisan ini, termasuk manajemen kunci untuk Proof of Cadangan (lihat Bagian 4.1) dan untuk kredensial terdesentralisasi pengguna (dan data digital lainnya aset) (lihat Bagian 4.3). Penjaga: Chainlink Penjaga [87] memungkinkan pengembang menulis kode untuk desentralisasi eksekusi pekerjaan off-chain, umumnya untuk memicu eksekusi smart contracts. Sebelum munculnya Keeper, pengembang biasanya mengoperasikan off-chain seperti itu logika mereka sendiri, menciptakan titik-titik kegagalan yang terpusat (serta banyak upaya pembangunan yang diduplikasi). Penjaga malah menyediakan kerangka kerja yang mudah digunakan outsourcing yang terdesentralisasi pada operasi ini, memungkinkan siklus pengembangan yang lebih pendek dan jaminan kuat akan keaktifan dan properti keamanan lainnya. Penjaga dapat mendukung siapa pun dari berbagai macam tujuan pemicu, termasuk likuidasi pinjaman atau pelaksanaan transaksi keuangan, inisiasi airdrop atau pembayaran yang bergantung pada waktu dalam sistem dengan pemanenan hasil, dan sebagainya. Dalam kerangka DON, inisiator dapat dipandang sebagai generalisasi Penjaga dalam beberapa pengertian. Inisiator dapat menggunakan adaptor, dan dengan demikian dapat memanfaatkan a perpustakaan antarmuka yang termodulasi ke sistem on-chain dan off-chain, memungkinkan proses yang cepat pengembangan fungsionalitas yang aman dan canggih. Inisiator memulai komputasi di executable, yang menawarkan keserbagunaan penuh DONs, memungkinkan penggunaan yang luas berbagai layanan terdesentralisasi yang kami sajikan dalam makalah ini untuk aplikasi on-chain dan off-chain. 3.6.4 Reputasi Node / Riwayat Kinerja Ekosistem Chainlink yang ada secara asli mendokumentasikan riwayat kinerja menyumbangkan node pada rantai. Fitur ini telah memunculkan kumpulan sumber daya berorientasi reputasi yang menyerap, menyaring, dan memvisualisasikan data kinerja individu operator node dan data feed. Pengguna dapat mereferensikan sumber daya ini untuk mendapatkan informasi keputusan dalam pemilihan node dan untuk memantau pengoperasian jaringan yang ada. Kemampuan serupa akan membantu pengguna memilih DONs. Misalnya, pasar tanpa izin saat ini seperti market.link mengizinkan node operator untuk mencantumkan layanan oracle mereka dan membuktikan identitas off-chain mereka melalui layanan seperti Keybase [4], yang mengikat profil sebuah node di Chainlink ke nama domain dan akun media sosial pemilik yang ada. Selain itu, kinerja alat analisis, seperti yang tersedia di market.link dan reputasi.link, mengizinkan pengguna untuk melihat statistik kinerja historis masing-masing node, termasuk node mereka latensi respons rata-rata, penyimpangan nilai dalam laporan mereka dari nilai konsensus diteruskan pada rantai, pendapatan yang dihasilkan, pekerjaan yang terpenuhi, dan banyak lagi. Alat analisis ini juga memungkinkan pengguna melacak adopsi berbagai jaringan oracle oleh pengguna lain, suatu bentukdukungan implisit terhadap node yang mengamankan jaringan tersebut. Hasilnya adalah “jaring” yang datar kepercayaan” di mana, dengan menggunakan node tertentu, terciptalah aplikasi terdesentralisasi yang bernilai tinggi sinyal kepercayaan mereka pada node yang dapat diamati dan diperhitungkan oleh pengguna lain keputusan pemilihan node sendiri. Dengan DONs (dan awalnya dengan OCR) terjadi pergeseran dalam pemrosesan transaksi dan aktivitas kontrak secara lebih umum di luar rantai. Model terdesentralisasi untuk merekam node kinerja tetap dimungkinkan dalam DON itu sendiri. Memang performanya tinggi dan kapasitas data sebesar DONs memungkinkan pembuatan catatan dengan cara yang lebih detail cara dan juga untuk melakukan perhitungan terdesentralisasi pada catatan-catatan ini, menghasilkan ringkasan yang dapat dipercaya yang dapat digunakan oleh layanan reputasi dan diperiksa di RANTAI UTAMA. Meskipun ada kemungkinan bagi DON pada prinsipnya untuk salah menggambarkan perilaku node konstituen jika sebagian besar node rusak, kami mencatat bahwa kolektif kinerja DON itu sendiri dalam mengirimkan data on-chain terlihat di MAINCHAIN dan dengan demikian tidak dapat disalahartikan. Selain itu, kami berencana untuk mengeksplorasi mekanisme itu memberi insentif pada pelaporan internal yang akurat tentang perilaku node di DON. Misalnya, dengan melaporkan subkumpulan node berperforma tinggi yang paling cepat mengembalikan kontribusi data ke laporan yang disampaikan secara berantai, DON menciptakan insentif bagi node untuk menyatakan kesalahan laporan: Salah memasukkan node dalam subset ini berarti salah mengecualikan node yang seharusnya dimasukkan dan oleh karena itu memberikan sanksi yang tidak sah kepada mereka. Kegagalan pelaporan yang berulang-ulang oleh DON juga akan menciptakan insentif bagi node yang jujur untuk meninggalkan DON. Kompilasi sejarah kinerja yang akurat dan konsekuensinya secara terdesentralisasi kemampuan pengguna untuk mengidentifikasi node berkinerja tinggi dan untuk membangun operator node reputasi adalah ciri pembeda yang penting dari ekosistem Chainlink. Kami tunjukkan di Bagian 9 bagaimana kita dapat mempertimbangkannya sebagai bagian penting dari pendekatan yang ketat dan pandangan luas tentang keamanan ekonomi yang diberikan oleh DONs.
去中心化的 Oracle 网络接口和 Ca-
能力 在这里,我们简单地描述了 DONs 的功能,简单但强大 它们旨在实现的接口。 DON 上的应用程序由可执行文件和适配器组成。可执行文件是 其核心逻辑是确定性程序的程序,类似于 smart contract。 可执行文件还具有许多附带的启动程序,即调用入口的程序 当预定事件发生时(例如,在某些时间),可执行文件逻辑中的点 (就像 cron 作业),当价格超过阈值时,等等——很像 Keepers(参见第 3.6.3 节)。适配器提供链下资源的接口,可以被调用 可执行文件中的发起者或核心逻辑。因为他们的行为可能取决于此 外部资源、启动器和适配器的行为可能是不确定的。 我们描述了 DON 开发者界面以及可执行文件的功能和 适配器通常用于表征计算系统的三种资源:网络、计算和存储。我们对其中每一个进行简要概述 以下资源并在附录 B 中提供更多详细信息。
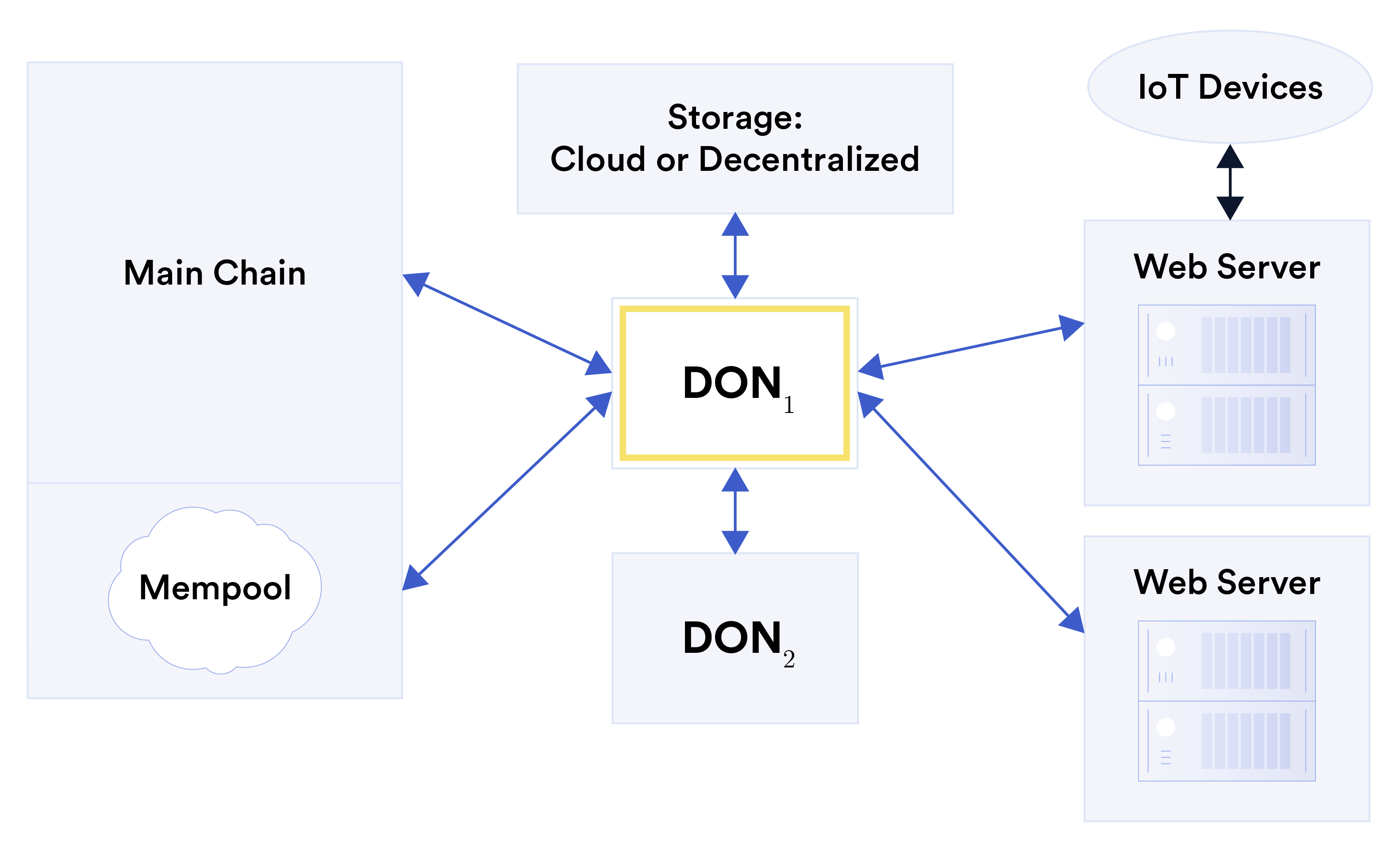
3.1 网络 适配器是在 DON 上运行的可执行文件可以通过其发送和接收信息的接口。 从off-DON系统接收数据。适配器可以被视为泛化 今天 Chainlink 使用的适配器 [20]。适配器可以是双向的,即它们 不能只是从 DON 拉取数据,而是将数据推送到 Web 服务器。他们还可以利用 分布式协议以及加密功能,例如安全多方 计算。 图 9:适配器连接 DON(表示为 DON1)与一系列不同的资源,包括另一个 DON(表示为 DON2)、一条 blockchain(主链)及其 mempool、外部存储、Web 服务器和 IoT 设备(通过 Web 服务器)。 显示了可以为其创建适配器的外部资源的示例 如图 9 所示。它们包括: • 区块链:适配器可以定义如何将交易发送到 blockchain 并 如何从中读取区块、单个交易或其他状态。适配器一个 也可以为 blockchain 的内存池定义。 (参见第 3.5 节。) • Web 服务器:适配器可以定义可检索数据的 API 来自网络服务器,包括不专门适应的遗留系统 与 DONs 连接。此类适配器还可以包含用于将数据发送到的 API 这样的服务器。 DON 连接的 Web 服务器可以充当网关 其他资源,例如物联网 (IoT) 设备。• 外部存储:适配器可以定义读取和写入存储的方法 DON 之外的服务,例如去中心化文件系统 [40, 188] 或云 存储。 • 其他DON:适配器可以在DON 之间检索和传输数据。 我们预计 DONs 的初始部署将包括一组构建块 此类常用外部资源的适配器,并将进一步允许 DON 特定的 由 DON 节点发布的适配器。作为 smart contract 开发人员编写适配器 今天,我们预计他们将使用这种先进的技术构建更强大的适配器 功能。 我们期望用户最终能够在一个新的适配器中创建新的适配器。 未经许可的方式。 某些适配器的构造方式必须确保由 DON 控制的外部资源的持久性和可用性。例如,云存储可以 需要维护云服务帐户。此外,DON 可以执行 代表用户对私钥进行去中心化管理(例如 [160])和/或 可执行文件。因此,DON能够控制可用于例如在目标blockchain上发送交易的资源,例如加密货币。 有关 DON 适配器的更多详细信息,请参阅附录 B.1,一些适配器的详细信息请参阅附录 C。 示例适配器。 3.2 计算 可执行文件是 DON 上的基本代码单元。可执行文件是一对 exec = (逻辑,初始化)。这里,逻辑是一个具有多个指定入口的确定性程序 点 (logic1,logic2,...,logicℓ) 和 init 是一组相应的启动器 (初始化1、初始化2、……、初始化)。确保可执行文件逻辑 DON 的完全可审计性 使用底层账本 L 来处理所有输入和输出。因此,例如,任何适配器 作为可执行文件输入的数据必须首先存储在 L 上。 发起人: 今天 Chainlink 中的启动器会导致事件相关的作业执行 Chainlink 节点 [21]。 DONs 中的启动器的功能大致相同。然而,DON 启动器与可执行文件特定关联。发起者可能取决于 基于外部事件或状态、当前时间或 DON 状态的谓词。 由于对事件的依赖,发起者的行为当然可能是不确定的 (当然也可以是适配器)。启动器可以在各个 DON 节点内执行 因此不需要依赖适配器。 (参见下面的示例 1。) 启动器是区分可执行文件和 smart contract 的一个重要特征。 因为可执行文件可以响应启动器而运行,所以它可以有效地操作 自主地,当然通过扩展可以包含可执行文件的混合合同。如今发起者的一种形式是 Chainlink 守护者,它提供交易自动化服务,根据 oracle 报告触发 smart contract 执行,例如清算抵押不足的贷款和执行限价订单交易。 方便地,DONs 中的启动器也可以被视为指定 适用于可执行文件的服务协议,因为它们定义了以下情况 DON 必须调用它。 以下示例说明启动器如何在可执行文件中工作: 示例 1(偏差触发的喂价)。 smart contract SC 可能需要新鲜的 每当价格发生重大变化(例如 1%)时,喂价数据(参见第 3.6.3 节) 一对资产之间的汇率,例如 ETH-USD。波动敏感的价格 今天 Chainlink 支持提要,但了解它们如何实现是有启发性的 通过可执行的 execfeed 在 DON 上实现。 可执行文件 execfeed 在 L 上维护最新的 ETH-USD 价格 r,在 ⟨NewPrice : j, r⟩entries 序列的形式,其中 j 是递增的索引 每次价格更新。 发起者 init1 使每个节点 Oi 监控当前 ETH-USD 价格 与索引 j 的最近存储的价格 r 的偏差至少为 1%。之上 检测到这种偏差,Oi 将新价格的当前视图 ri 写入 L 使用 ⟨PriceView : i, j + 1, ri⟩ 形式的条目。 当至少 k 个这样的 PriceView 条目具有新价格时,第二个启动器 init2 就会触发 由不同节点创建的索引 j + 1 的值已累积在 L 上。然后,init2 调用入口点逻辑 2 来计算前 k 个新的有效价格视图值的中位数 ρ 并将新值 ⟨NewPrice : j + 1, ρ⟩ 写入 L 。 (操作上,节点 可以轮流担任指定撰稿人。) 第三个发起者 init3 监视 L 上的 NewPrice 条目。每当有新报告时 ⟨NewPrice : j, r⟩出现在那里,它调用一个入口点逻辑 3,将 (j, r) 推送到 SC 使用适配器。 正如我们所指出的,可执行文件的功能与 smart contract 类似。 然而,除了其更高的性能之外,它与典型的主链合约不同 以两种基本方式: 1. 机密性:可执行文件可以执行机密计算,即秘密程序可以处理明文输入,或者发布的程序可以处理 秘密输入数据,或两者的组合。在一个简单的模型中,秘密数据可以 由 DON 节点访问,隐藏中间结果并仅公开 处理和清理的值到主链。也可以从 DON 本身隐藏敏感数据:DON 旨在支持此类方法 作为多方计算,例如 [42, 157] 和可信执行环境 (TEE) [84, 133, 152, 229] 为此目的。6 6通过扩展,也可以对 DON 节点保持可执行文件本身的秘密, 尽管这在今天仅适用于使用 TEE 的重要可执行文件。2. 支持角色:可执行文件旨在支持主系统上的 smart contracts 链,而不是取代它们。可执行文件有几个限制: smart contract 不: (a) 信任模型:可执行文件在由 DON:其正确执行依赖于 O 的诚实行为。(主要 然而,链条可以提供一些防范 DON 渎职行为的防护措施,如 第 7.3 节中讨论。) (b) 资产访问:DON 可以控制 blockchain 上的帐户,因此 通过适配器控制其上的资产。但 DON 不能权威地 代表在主链上创建的资产,例如以太坊或 ERC20 tokens,因为 他们的本地链维护其所有权的权威记录。 (c) 生命周期:DONs 可能会故意以有限的生命周期建立起来,因为 由 DON 和所有者之间的链上服务水平协议定义 依赖合同。 相比之下,区块链的作用是 永久档案系统。 有关 DON 计算的更多详细信息,请参阅附录 B.2。 3.3 存储 作为基于委员会的系统,DON 可以持久存储适量的数据 在 L 上的成本比未经许可的 blockchain 低得多。此外,通过适配器, DONs 可以引用外部去中心化系统进行数据存储,例如 Filecoin [85], 从而可以将此类系统连接到 smart contracts。这个选项特别 作为解决普遍存在的“膨胀”问题的一种手段,对大量数据很有吸引力 blockchain 系统。 因此,DONs 可以在本地或外部存储数据,以便在其特定支持的服务中使用。 DON 还可以以保密的方式使用此类数据, 计算以下数据:(1) 在 DON 节点之间秘密共享或在以下情况下加密 由 DON 节点以适合安全多方计算的方式管理的密钥 或部分或完全同态加密;或 (2) 使用可信执行进行保护 环境。 我们预计 DONs 将采用常见的简单内存管理模型 智能合约系统:可执行文件只能写入自己的内存。可执行文件 但是,可以从其他可执行文件的内存中读取。 有关 DON 存储的更多详细信息,请参阅附录 B.3。 3.4 交易执行框架 (TEF) DON 旨在支持主链 MAINCHAIN (或多个主链)上的合约。详细讨论事务执行框架 (TEF)第 6 节中的内容是有效执行合同的通用方法 SC 跨主链和 DON。 TEF 旨在支持 FSS 和第 2 层 技术——如果需要的话,可以同时进行。事实上,它很可能作为主要车辆 FSS 的使用(因此,我们在本节中不再进一步讨论 FSS)。 简而言之,在 TEF 中,有一个为 MAINCHAIN 设计或开发的原始目标合约 SC 被重构为混合合约。这种重构产生了两个互操作的 混合合约的组成部分:为了清楚起见,我们将其称为主链合约 SCa 在 TEF 的背景下,作为锚定合约和 DON 上的可执行执行程序。的 合约SCa托管用户的资产,执行权威的状态转换,还 提供防护栏(参见第 7.3 节)以防止 DON 中的故障。可执行的 exec 对交易进行排序并为其提供关联的 oracle 数据。可以捆绑 通过多种方式进行 SCa 交易——例如,使用基于有效性证明的或 乐观 rollups,由 DON 保密执行,等等。 我们希望开发出使开发人员能够轻松分割合约的工具 SC 用高级语言编写成 MAINCHAIN 和 DON 逻辑块,SCa 和 分别执行,安全高效地组合。 使用TEF将高性能交易方案与高性能相结合 oracles 是我们的 oracle 缩放方法的组成部分。 3.5 内存池服务 我们打算在 DON 上部署一项重要的应用程序层功能以提供支持 FSS 和 TEF 的核心是 Mempool Services(MS)。 MS 可以被视为一个适配器, 但拥有一流的支持。 MS 提供对传统兼容事务处理的支持。在此用途中,MS 从主链的内存池中摄取那些用于目标合约的交易 主链上的 SC。然后,MS 将这些事务传递给 DON 上的可执行文件, 它们以所需的方式进行处理。 MS 数据可由 DON 使用 组成交易,然后可以直接从 DON 传递到 SC 或 到另一个名为 SC 的合约。例如,DON可以转发交易 通过 MS 收集,或者它可以使用 MS 数据为其发送到的交易设置 Gas 价格 主链。 由于它监控内存池,MS 可以从直接与 SC 交互的用户获取交易。因此,用户可以继续使用以下方式生成交易 遗留软件,即不知道 MS 和 MS 配置的存在的应用程序 合同。 (在这种情况下,必须更改 SC 以忽略原始交易并 仅接受MS处理过的内容,以避免双重处理。) 为了与目标合同 SC 一起使用,MS 可以与 FSS 和/或 TEF 一起使用。3.6 垫脚石:现有 Chainlink 功能 3.6.1 链下报告(OCR) 链外报告 (OCR) [60] 是 Chainlink 中的一种机制,用于 oracle 报告聚合和传输到依赖合约 SC。最近以 Chainlink 价格部署 馈送网络,它代表了通往完整 DON 之路的第一步。 OCR 的核心是 BFT 协议,旨在以部分同步的方式运行 网络。它确保任意存在 f < n/3 时的活性和正确性 故障节点,保证了拜占庭可靠广播的特性,但事实并非如此 完整的 BFT 共识协议。节点不维护消息日志 一致的意思是代表一个在所有观点上都相同的账本, 协议的领导者可以在不违反安全的情况下含糊其辞。 OCR 目前是为特定消息类型设计的: 参与节点报告的(至少 2f +1)个值。它提供了关键保证 它为 SC 输出的报告称为经过验证的报告:经过验证的报告中的中值 报告等于或位于两个诚实节点报告的值之间。此属性是 OCR 的关键安全条件。领导者可能对中位数有一定影响 经证明的报告中的值,但仅受此正确性条件的限制。光学字符识别可以 可以扩展到以不同方式聚合值的消息类型。 虽然 Chainlink 网络今天的活跃度和正确性目标不需要 OCR 是一个成熟的共识协议,它们确实需要 OCR 提供传统 BFT 协议中不存在的一些附加形式的功能,最值得注意的是: 1. 全有或全无的链下报告广播:OCR 确保经过验证的报告 快速可供所有诚实节点使用,或者不可供任何节点使用。这是一种公平 有助于确保诚实节点有机会参与的属性 在经过验证的报告传输中。 2. 可靠传输:OCR 确保即使存在错误或恶意 节点,所有OCR报告和消息在一定时间内传输到SC, 预先定义的时间间隔。这是一个活跃的属性。 3. 基于合同的信任最小化:SC 过滤掉潜在错误的 OCR 生成的报告,例如,如果它们报告的值与其他值显着偏差 最近收到的。这是协议外正确性强制的一种形式。 所有这三个属性都将在 DONs 中发挥自然作用。全有或全无链下 (DON) 广播是加密经济保证的重要组成部分 围绕可靠的传输,这又是适配器的一个重要属性。信任 SC 中的最小化是一种护栏,如第 7.3 节所述。 OCR 还为 Chainlink 的 oracle 网络中的 BFT 协议的操作部署和细化提供了基础,因此,如上所述,这是一条通往完整的路径。 DONs 的功能。3.6.2 德科和城市公告员 DECO [234] 和 Town Crier [233] 是目前正在开发的一对相关技术 在 Chainlink 网络中开发。 如今,大多数 Web 服务器允许用户使用协议通过安全通道进行连接 称为传输层安全 (TLS) [94]。 (HTTPS 表示 HTTP 的一个变体, 启用了 TLS,即以“https”为前缀的 URL 表示使用 TLS 来确保安全。) 不过,大多数启用 TLS 的服务器都有一个显着的限制:它们不进行数字签名 数据。因此,用户或证明者无法呈现她从服务器接收的数据 向第三方或验证者,例如 oracle 或 smart contract,以确保 数据的真实性。 即使服务器对数据进行数字签名,仍然存在保密问题。证明者可能希望在将敏感数据呈现给证明者之前对其进行编辑或修改 验证者。然而,数字签名是专门为使修改后的数据失效而设计的。因此,它们阻止证明者进行保密性的更改 到数据。 (更多讨论请参见第 7.1 节。) DECO 和 Town Crier 旨在允许证明者从网络获取数据 服务器并以确保完整性和机密性的方式将其呈现给验证者。 这两个系统在确保数据呈现的意义上保持完整性 证明者到验证者确实源自目标服务器。他们支持 机密性是指允许证明者编辑或修改数据(同时仍然 保持完整性)。 这两个系统的一个关键特点是它们不需要对系统进行任何修改 目标网络服务器。它们可以与任何现有的启用 TLS 的服务器一起运行。事实上, 它们对服务器是透明的:从服务器的角度来看,证明者是 建立普通连接。 这两个系统具有相似的目标,但在信任模型和实现方面有所不同,正如我们现在简要解释的那样。 DECO 从根本上利用加密协议来实现其完整性 和保密性。在使用 DECO 与目标服务器建立会话时,证明者同时与目标服务器建立交互协议 验证者。该协议使证明者能够向验证者证明它已收到 在当前会话期间来自服务器的给定数据 D。证明者可以 或者向验证者提供 D 的某些属性的零知识证明 因此不直接揭示 D。 在 DECO 的典型使用中,用户或单个节点可以从私有节点导出数据 D。 与 Web 服务器的会话到 DON 中的所有节点。因此,完整的 DON 可以 证明 D 的真实性(或通过零知识证明从 D 导出的事实)。 除了本文后面给出的示例应用程序之外,此功能还可以 用于通过 DON 放大对数据源的高完整性访问。即使只有一个节点 可以直接访问数据源——例如,由于与 数据提供者——整个 DON 仍然有可能证明以下内容的正确性该节点发出的报告。 Town Crier 依赖于使用可信执行环境 (TEE),例如 Intel 新交所。简而言之,TEE 的功能就像一种黑匣子,在特定环境中执行应用程序 防篡改和保密的方式。原则上,即使是主机的所有者 TEE 正在运行既不能(无法检测地)改变受 TEE 保护的应用程序,也不能 查看应用程序的状态,其中可能包括秘密数据。 Town Crier 可以实现 DECO 的所有功能以及更多功能。 DECO 将证明者限制为与单个验证者交互。相比之下,Town Crier 能够 证明者对从目标服务器获取的数据 D 生成可公开验证的证明, 即任何人,甚至 smart contract,都可以直接验证的证明。城镇公告员可以 还可以安全地获取和使用秘密(例如用户凭据)。 Town Crier 的主要限制是它对 TEE 的依赖。生产 TEE 具有 最近被证明存在许多严重的漏洞,尽管该技术还处于起步阶段,并且无疑会成熟。参见附录 B.2.1 和 B.2.2 TEE 的进一步讨论。 有关 DECO 和 Town Crier 的一些示例应用程序,请参阅第 4.3、4.5 节 9.4.3 和附录 C.1。 3.6.3 现有链上 Chainlink 服务 Chainlink oracle 网络提供多种主要服务 blockchains 和当今的其他去中心化系统。 如所描述的进一步演变 在本白皮书中,将赋予这些现有服务额外的功能和 达到。三个例子是: 数据源: 今天,大多数 Chainlink 用户依赖 smart contracts 使用数据源。这些是根据关键数据的当前价值的报告 权威的链下来源。例如,价格源是报告价格的源 资产——加密货币、商品、外汇、指数、股票等——根据 交换或数据聚合服务。如今,此类信息流已经帮助确保了数十亿美元的安全 通过在 DeFi 系统(如 Aave [147] 和)中使用美元来实现链上价值 Synthetix [208]。 Chainlink 数据源的其他示例包括以下天气数据 参数农作物保险 [75] 和选举数据 [93] 等。 本文中描述的 DON 和其他技术的部署将以多种方式增强 Chainlink 网络中数据馈送的提供,包括: • 扩展:OCR 和随后的 DON 旨在使 Chainlink 服务能够扩展 他们支持的许多 blockchain 都具有显着的差异。例如,我们期望 DONs 将有助于增加节点提供的数据馈送数量 Chainlink 从 100 到 1000 甚至更长。这种缩放将有助于 Chainlink 生态系统实现了全面提供与 smart contract 相关的数据并满足和预测现有和未来需求的目标。• 增强安全性:通过存储中间报告,DONs 将保留记录 节点行为的高保真监控和测量其性能和准确性,为声誉系统提供强有力的经验基础 对于 Chainlink 节点。 FSS 和 TEF 将纳入价格反馈 以灵活的方式处理交易数据,防止抢先交易等攻击。 (明确)staking 将加强现有的加密经济安全保护 数据源。 • 馈送敏捷性:作为与 blockchain 无关的系统(实际上,更广泛地说,与消费者无关的系统),DON 可以促进向多重性提供数据馈送 依赖系统。单个 DON 可以将给定的 feed 同时推送到一组 不同的 blockchain ,消除了对每链 oracle 网络的需求, 能够在新的 blockchain 和其他设备上快速部署现有源 为当前服务的 blockchain 提供数据。 • 保密性:在 DON 中执行广义计算的能力使得敏感数据的计算能够在链外进行,避免在链上进行 曝光。 此外,使用 DECO 或 Town Crier,可以实现 更强的保密性,允许基于非公开数据生成报告 甚至暴露于 DON 节点。示例请参见第 4.3 节和第 4.5 节。 可验证随机函数(VRF): 几种类型的 DApp 需要可验证的正确随机源,以验证其自身的公平运行。 不可替代代币 (NFTs) 就是一个例子。 Aavegotchi [23] 和 Axie Infinity [35] 中 NFT 特征的稀有度由 Chainlink VRF 决定,分布也是如此 通过以太卡 [102] 中基于票证的抽奖方式获得 NFT 份;种类繁多的 结果随机的游戏 DApp;以及非常规金融工具,例如 PoolTogether [89] 等无损储蓄游戏,它将资金分配给 随机获胜者。其他 blockchain 和非 blockchain 应用程序也需要安全 随机性的来源,包括去中心化系统委员会的选择和 彩票的执行。 虽然区块 hashes 可以作为不可预测的随机性来源,但它们很容易受到敌对矿工的操纵(在某种程度上,用户提交 交易)。 Chainlink VRF [78] 提供了一种更安全的替代方案。安 oracle 有一个关联的私钥/公钥对(sk,pk),其私钥在链外维护,其公钥 pk 已发布。为了输出一个随机值,它 将 sk 应用于由依赖合约提供的不可预测的种子 x(例如,区块 hash 和 DApp 特定参数)使用函数 F,产生 y = Fsk(x) 以及 正确性证明。 (有关 Chainlink 上提供的 VRF,请参阅 [180]。) VRF 可验证的事实是,有了 pk 的知识,就可以检查证明的正确性,从而检查 y 的正确性。因此,y 值对于 对手无法预测 x 或学习 sk 并且服务无法操纵。Chainlink VRF 可能被视为涉及链下私钥托管的一系列应用程序之一。更一般地说,DONs 可以提供安全、 应用程序和/或用户的单个密钥的分散存储,并结合 这种能力具有广义计算。结果是大量的应用程序, 我们在本文中给出了一些示例,包括证明的密钥管理 储备金(参见第 4.1 节)和用户的去中心化凭证(以及其他数字 资产)(参见第 4.3 节)。 饲养员: Chainlink Keepers [87] 使开发人员能够为去中心化编写代码 链外作业的执行,通常会触发依赖smart contracts的执行。 在 Keepers 出现之前,开发者进行此类链下操作是很常见的 逻辑本身,造成集中的故障点(以及大量的重复开发工作)。相反,Keeper 提供了一个易于使用的框架 这些业务的分散外包,缩短了开发周期 活性和其他安全属性的有力保证。守护者可以支持任何 各种各样的触发目标,包括依赖于价格的贷款清算或 金融交易的执行、空投或付款的时间依赖启动 在具有产量收获的系统中,等等。 在 DON 框架中,发起者可以被视为多种意义上的守护者的概括。发起者可以使用适配器,因此可以利用 链上和链下系统的模块化接口库,允许快速 开发安全、复杂的功能。发起者发起计算 可执行文件,它们本身提供 DON 的全部多功能性,允许广泛的 我们在本文中为链上和链下应用程序提供了一系列去中心化服务。 3.6.4 节点声誉/性能历史记录 现有的 Chainlink 生态系统本身记录了性能历史记录 链上贡献节点。这一功能催生了一系列以声誉为导向的资源,这些资源可以摄取、过滤和可视化个人的绩效数据。 节点操作员和数据源。用户可以参考这些资源来获取信息 决定节点选择并监控现有网络的运行。 类似的功能将帮助用户选择DONs。 例如,当今的无许可市场(例如 market.link)允许节点 运营商列出他们的 oracle 服务并通过以下方式证明他们的链外身份 诸如 Keybase [4] 之类的服务,它将 Chainlink 中的节点的配置文件绑定到其 所有者现有的域名和社交媒体帐户。此外,性能 分析工具,例如 market.link 和reputation.link 上提供的工具,允许 用户可以查看各个节点的历史性能统计数据,包括其 平均响应延迟,报告中的值与共识值的偏差 在链上传递、产生收入、实现就业等等。这些分析工具还 允许用户跟踪其他用户对各种 oracle 网络的采用情况,这是一种形式保护此类网络的节点的隐式认可。结果是一个扁平的“网络” 信任”,其中通过使用特定节点,高价值的去中心化应用程序创建 他们对这些节点的信任信号,其他用户可以观察并纳入他们的考虑因素 自己的节点选择决策。 随着 DONs(最初是 OCR)带来了交易处理和 合同活动更普遍地是链下的。记录节点的去中心化模型 DON 本身的性能仍然是可能的。确实,高性能 DONs 的数据容量使得以细粒度构造记录成为可能 方式,并对这些记录执行去中心化计算,产生可信的摘要,可供信誉服务使用并在其上设置检查点 主链。 虽然原则上 DON 有可能在大部分节点损坏的情况下歪曲组成节点的行为,但我们注意到集体 DON 本身在传递链上数据方面的性能在主链上可见 因此不能被歪曲。此外,我们计划探索以下机制: 激励 DON 中节点行为的准确内部报告。例如,通过报告最快返回数据贡献的高性能节点的子集 对于链上转发的报告,DON 会激励节点对不正确的内容提出异议 报告:错误地在此子集中包含节点意味着错误地排除节点 这应该被包括在内,因此对他们的惩罚是无效的。 DON 重复报告失败也会激励诚实节点离开 DON。 准确的绩效历史记录和后续结果的分散编制 用户识别高性能节点以及节点运营商构建的能力 声誉是 Chainlink 生态系统的重要区别特征。 我们 第 9 节展示了我们如何将它们推理为严格且可靠的模型的关键部分。 对 DONs 提供的经济安全的广阔视野。
Layanan Terdesentralisasi Diaktifkan oleh Terdesentralisasi
Jaringan Oracle Untuk mengilustrasikan keserbagunaan DON dan cara DON mengaktifkan sejumlah layanan baru, kami menyajikan lima contoh aplikasi berbasis DON di bagian ini dan menjelaskannya kontrak hibrida yang mewujudkannya: (1) Bukti Cadangan, suatu bentuk layanan lintas rantai; (2) Berinteraksi dengan sistem enterprise/legacy, yaitu menciptakan berbasis middleware lapisan abstraksi yang memfasilitasi pengembangan aplikasi blockchain dengan minimal blockchain kode atau keahlian khusus; (3) Identitas terdesentralisasi, alat yang memungkinkan pengguna untuk memperoleh dan mengelola dokumen identitas dan kredensial mereka sendiri; (4) Saluran prioritas, layanan yang memastikan penyertaan transaksi infrastruktur penting secara tepat waktu (misalnya, oracle laporan) pada blockchain; dan (5) Menjaga kerahasiaan DeFi, yaitu keuangan smart contracts yang menyembunyikan data sensitif pihak yang berpartisipasi. Di sini, kita
gunakan SC untuk menunjukkan bagian MAINCHAIN dari kontrak hibrida dan menjelaskan DON komponen secara terpisah atau dalam istilah exec yang dapat dieksekusi. 4.1 Bukti Cadangan Untuk banyak aplikasi, berguna untuk menyampaikan status antara atau di antara blockchains. SEBUAH Aplikasi populer dari layanan tersebut adalah pembungkusan mata uang kripto. Koin yang dibungkus seperti itu karena WBTC [15] menjadi aset populer di Keuangan Terdesentralisasi (DeFi). Mereka melibatkan penyimpanan aset pendukung yang "terbungkus" pada sumbernya blockchain MAINCHAIN(1) dan membuat token yang sesuai pada target blockchain MAINCHAIN(2) yang berbeda. Misalnya, WBTC adalah ERC20 token di Ethereum blockchain yang sesuai ke BTC di Bitcoin blockchain. Karena kontrak pada MAINCHAIN(2) tidak memiliki visibilitas langsung ke MAINCHAIN(1), mereka harus bergantung secara eksplisit atau implisit pada oracle untuk melaporkan simpanan yang dibungkus aset dalam smart contract, menghasilkan apa yang terkadang disebut Bukti Cadangan. Di WBTC [15], misalnya, kustodian BitGo memegang BTC dan menerbitkan WBTC, dengan Chainlink jaringan menyediakan Bukti Cadangan [76]. DON sendiri dapat memberikan Bukti Cadangan. Namun, dengan DON, hal itu mungkin dilakukan untuk melangkah lebih jauh. DON dapat mengelola rahasia dan, melalui penggunaan adaptor yang sesuai, dapat bertransaksi di blockchain mana pun yang diinginkan. Oleh karena itu, DON dapat bertindak sebagai salah satu di antara sejumlah kustodian—atau bahkan sebagai satu-satunya kustodian yang terdesentralisasi—untuk aset yang dibungkus. DONs dengan demikian dapat berfungsi sebagai platform untuk meningkatkan keamanan layanan yang ada yang menggunakan Bukti Cadangan. Misalnya, MAINCHAIN(1) adalah Bitcoin dan MAINCHAIN(2) adalah Ethereum. Di MAINCHAIN(2), kontrak SC menerbitkan tokens yang mewakili BTC yang dibungkus. DON mengontrol alamat BTC addr (1) DON. Untuk membungkus BTC, pengguna U mengirimkan X BTC dari tambahan(1) kamu untuk menambahkan(1) DON bersama dengan alamat MAINCHAIN(2)(2) kamu. Monitor DON tambahan(1) DON melalui adaptor ke MAINCHAIN(1). Saat mengamati deposit U, dengan konfirmasi probabilitas yang cukup tinggi, ia mengirimkan pesan ke SC melalui adaptor ke RANTAI UTAMA(2). Pesan ini menginstruksikan SC untuk mencetak X tokens untuk addr(2) kamu. Jika U melepaskan X tokens, hal sebaliknya akan terjadi. Namun, di MAINCHAIN(1), tambahan(1) DON mengirimkan X BTC ke alamat(1) U (atau ke alamat lain, jika diminta oleh pengguna). Tentu saja, protokol-protokol ini dapat diadaptasi untuk bekerja dengan bursa, bukan secara langsung dengan pengguna. 4.2 Berinteraksi dengan Sistem Perusahaan / Warisan DONs dapat berfungsi sebagai jembatan antara blockchains, seperti pada contoh Bukti Cadangan, namun tujuan lainnya adalah agar cadangan tersebut bertindak sebagai jembatan dua arah di antara keduanya blockchains dan sistem lama [176] atau sistem serupa blockchain seperti bank sentral mata uang digital [30]. Perusahaan menghadapi sejumlah tantangan dalam menghubungkan sistem dan sistem yang ada proses ke sistem desentralisasi, termasuk:• Ketangkasan Blockchain: Sistem Blockchain berubah dengan cepat. Suatu perusahaan mungkin menghadapi kemunculan baru yang cepat atau peningkatan popularitas blockchains pihak lawan ingin melakukan transaksi, tetapi perusahaan tidak memilikinya dukungan infrastruktur yang ada. Secara umum, dinamisme blockchains membuat sulit bagi masing-masing perusahaan untuk tetap mengikuti ekosistem secara keseluruhan. • Sumber daya pengembangan khusus Blockchain: Bagi banyak organisasi, merekrut atau menginkubasi keahlian blockchain yang mutakhir adalah hal yang sulit, terutama mengingat tantangan ketangkasan. • Manajemen kunci pribadi: Mengelola kunci pribadi untuk blockchains atau mata uang kripto memerlukan keahlian operasional yang berbeda dari keamanan siber tradisional praktek dan tidak tersedia untuk banyak perusahaan. • Kerahasiaan: Perusahaan enggan mengungkapkan hal-hal sensitif dan hak milik mereka data pada rantai. Untuk mengatasi tiga kesulitan pertama ini, pengembang cukup menggunakan DON sebagai lapisan middleware yang aman untuk memungkinkan sistem perusahaan membaca atau menulis blockchaindtk. DON dapat mengabstraksi pertimbangan teknis terperinci seperti dinamika gas, reorganisasi rantai, dan sebagainya, baik untuk pengembang maupun pengguna. Oleh menghadirkan antarmuka blockchain yang disederhanakan ke sistem perusahaan, dengan demikian DON dapat sangat menyederhanakan pengembangan aplikasi perusahaan yang sadar akan blockchain, menghilangkan beban perusahaan dalam memperoleh atau menginkubasi sumber daya pengembangan khusus blockchain. Penggunaan DONs seperti ini sangat menarik karena memungkinkan pengembang perusahaan untuk melakukannya membuat aplikasi kontrak pintar yang sebagian besar blockchain agnostik. Akibatnya, lebih besar kumpulan blockchain yang mana DON diinstrumentasikan untuk bertindak sebagai middleware, maka lebih besar kumpulan blockchain yang dapat diakses dengan mudah oleh pengguna perusahaan. Pengembang dapat mem-porting aplikasi dari blockchain yang ada ke yang baru dengan sedikit modifikasi ke aplikasi yang dikembangkan secara internal. Untuk mengatasi masalah tambahan kerahasiaan, pengembang dapat mengajukan banding ke alat yang kami perkenalkan dalam makalah ini dan diharapkan dapat diterapkan untuk mendukung aplikasi DON. Ini termasuk DECO dan Town Crier Bagian 3.6.2 serta menjaga kerahasiaan Modifikasi API dibahas di Bagian 7.1.2 dan sejumlah pendekatan khusus aplikasi yang dibahas di sisa bagian ini. Sistem DON ini dapat menyediakan pengesahan on-chain berintegritas tinggi tentang status sistem perusahaan tanpa mengungkapkannya data sumber perusahaan yang sensitif pada rantai. 4.3 Identitas Terdesentralisasi Identitas terdesentralisasi adalah istilah umum untuk gagasan bahwa pengguna harus dapat melakukannya memperoleh dan mengelola kredensial mereka sendiri, daripada mengandalkan pihak ketiga untuk melakukannya jadi. Kredensial yang terdesentralisasi adalah pengesahan terhadap atribut atau pernyataan pemegangnya,yang sering disebut klaim. Kredensial ditandatangani secara digital oleh entitas, sering disebut penerbit, yang secara resmi dapat mengaitkan klaim dengan pengguna. Dalam sebagian besar skema yang diusulkan, klaim dikaitkan dengan Pengidentifikasi Terdesentralisasi (DID), yaitu pengidentifikasi universal untuk pengguna tertentu. Kredensial terikat pada kunci publik yang kunci privatnya dimiliki pengguna. Dengan demikian, pengguna dapat membuktikan kepemilikan klaim menggunakan kunci pribadinya. Visioner sebagai identitas terdesentralisasi adalah skema yang ada dan yang diusulkan, misalnya [14, 92, 129, 216], memiliki tiga keterbatasan parah: • Kurangnya kompatibilitas warisan: Sistem identitas terdesentralisasi yang ada bergantung pada a komunitas otoritas, yang disebut penerbit, untuk menghasilkan kredensial DID. Karena layanan web yang ada umumnya tidak menandatangani data secara digital, penerbit harus diluncurkan sebagai sistem tujuan khusus. Karena tidak ada insentif untuk melakukan hal ini tanpa a ekosistem identitas yang terdesentralisasi, menimbulkan masalah ayam dan telur. Di tempat lain Dengan kata lain, tidak jelas bagaimana melakukan bootstrap pada ekosistem emiten. • Manajemen kunci yang tidak dapat diterapkan: Sistem identitas yang terdesentralisasi mengharuskan pengguna untuk melakukan hal tersebut mengelola kunci pribadi, sesuatu yang ditunjukkan oleh pengalaman dengan mata uang kripto menjadi tanggung jawab yang tidak bisa dijalankan. Diperkirakan sekitar 4.000.000 Bitcoin telah terjadi hilang selamanya karena kegagalan manajemen kunci [194], dan banyak pengguna menyimpannya aset kripto dengan bursa [193], sehingga merusak desentralisasi. • Kurangnya penolakan Sybil untuk menjaga privasi: Persyaratan keamanan dasar aplikasi seperti pemungutan suara, alokasi token yang adil selama token penjualan, dll. adalah bahwa pengguna tidak dapat menyatakan banyak identitas. Proposal identitas terdesentralisasi yang ada mengharuskan pengguna untuk mengungkapkan identitas dunia nyata mereka untuk mencapai hal tersebut Penolakan Sybil, sehingga merusak jaminan privasi yang penting. Masalah-masalah ini dapat diatasi dengan menggunakan kombinasi komite node melakukan komputasi terdistribusi dalam DON dan penggunaan alat seperti DECO atau Town Crier, seperti yang ditunjukkan dalam sistem bernama CanDID [160]. DECO atau Town Crier dengan desain dapat mengubah layanan web yang ada tanpa modifikasi menjadi penerbit kredensial yang menjaga kerahasiaan. Mereka mengaktifkan DON untuk mengekspor relevan data untuk tujuan ini menjadi kredensial sambil menyembunyikan data sensitif yang tidak seharusnya muncul dalam kredensial. Selain itu, untuk memfasilitasi pemulihan kunci bagi pengguna, sehingga mengatasi manajemen kunci masalahnya, DON dapat memungkinkan pengguna untuk menyimpan kunci pribadi dalam bentuk yang dibagikan secara rahasia. Pengguna bisa memulihkan kunci mereka dengan membuktikan ke node di DON—demikian pula, menggunakan Town Crier atau DECO—kemampuan untuk masuk ke akun dengan serangkaian penyedia web yang telah ditentukan (misalnya, Twitter, Google, Facebook). Keuntungan menggunakan Town Crier atau DECO, dibandingkan dengan OAUTH, adalah privasi pengguna. Kedua alat tersebut memungkinkan pengguna menghindari pengungkapan ke DON pengidentifikasi penyedia web—dari mana identitas dunia nyata sering kali dapat diperoleh. Terakhir, untuk memberikan perlawanan kepada Sybil, seperti yang ditunjukkan pada [160], DON dapat melakukan melakukan transformasi yang menjaga privasi dari pengidentifikasi dunia nyata yang unik bagi pengguna (misalnya, Nomor Jaminan Sosial (SSN)) ke dalam pengidentifikasi on-chain setelah pendaftaran pengguna.Sistem dengan demikian dapat mendeteksi registrasi duplikat tanpa data sensitif seperti SSN diungkapkan ke masing-masing DON node.7 DON dapat menyediakan layanan apa pun atas nama identitas desentralisasi eksternal sistem pada blockchains tanpa izin atau izin, misalnya, instance Hyperledger Indy [129]. Contoh aplikasi: KYC: Identitas yang terdesentralisasi menjanjikan sebagai sarana untuk mencapai tujuan tersebut merampingkan persyaratan untuk aplikasi keuangan di blockchains sambil meningkatkan pengguna privasi. Dua tantangan yang dapat diatasi adalah akreditasi dan kewajiban kepatuhan berdasarkan peraturan anti pencucian uang/kenali pelanggan Anda (AML/KYC). Peraturan AML di banyak negara mewajibkan lembaga keuangan (dan badan usaha lainnya) untuk menetapkan dan memverifikasi identitas individu dan badan usaha yang menjadi mitra mereka. mereka melakukan transaksi. KYC merupakan salah satu komponen lembaga keuangan kebijakan AML yang lebih luas, yang biasanya juga mencakup pemantauan perilaku pengguna dan pengawasan aliran dana. KYC biasanya melibatkan presentasi kredensial identitas pengguna dalam beberapa bentuk (misalnya, masuk ke formulir web online, memegang dokumen identitas di depan wajah pengguna dalam sesi video, dll.). Amankan pembuatan dan presentasi kredensial terdesentralisasi pada prinsipnya dapat menjadi alternatif yang bermanfaat dalam beberapa hal, yaitu dengan: (1) Pembuatan proses KYC lebih efisien bagi pengguna dan lembaga keuangan, karena sekaligus a kredensial diperoleh, maka dapat disajikan secara lancar ke lembaga keuangan mana pun; (2) Mengurangi penipuan dengan mengurangi peluang pencurian identitas melalui kompromi informasi pengidentifikasi pribadi (PII) dan pemalsuan selama verifikasi video; dan (3) Mengurangi risiko kompromi PII di lembaga keuangan, karena pengguna tetap memegang kendali dari data mereka sendiri. Mengingat denda miliaran dolar yang dibayarkan oleh lembaga keuangan atas kegagalan kepatuhan AML, dan banyaknya lembaga keuangan yang menghabiskan jutaan dolar setiap tahunnya untuk KYC, perbaikan dapat menghasilkan penghematan yang cukup besar bagi lembaga keuangan. dan, selanjutnya, untuk konsumen [196]. Sementara sektor keuangan tradisional berjalan lambat untuk mengadopsi alat kepatuhan baru, sistem DeFi semakin banyak yang menerapkannya [43]. Contoh penerapan: Pinjaman dengan jaminan rendah: Kebanyakan DeFi aplikasi itu pinjaman dukungan saat ini hanya berasal dari pinjaman yang dijamin sepenuhnya. Ini adalah pinjaman yang diberikan kepada peminjam yang menyetorkan aset mata uang kripto yang nilainya melebihi pinjaman. Baru-baru ini muncul minat terhadap apa yang umumnya disebut oleh komunitas DeFi sebagai pinjaman tanpa jaminan. Sebaliknya, ini adalah pinjaman yang memiliki agunan yang sesuai mempunyai nilai yang lebih kecil dari pokok pinjaman. Pinjaman dengan jaminan rendah menyerupai pinjaman yang sering diberikan oleh lembaga keuangan tradisional. Daripada mengandalkan atas jaminan yang dititipkan sebagai jaminan pelunasan pinjaman, mereka justru mendasarkan pemberian pinjaman keputusan tentang sejarah kredit peminjam. 7Transformasi ini bergantung pada fungsi pseudorandom terdistribusi (PRF).Pinjaman dengan jaminan rendah merupakan bagian pasar pinjaman DeFi yang baru lahir namun terus berkembang. Mereka bergantung pada mekanisme seperti yang digunakan oleh keuangan tradisional institusi, seperti kontrak hukum [91]. Persyaratan penting untuk pertumbuhan mereka akan menjadi kemampuan untuk memberikan data mengenai kelayakan kredit pengguna—faktor kunci dalam keputusan pemberian pinjaman konvensional—ke sistem DeFi dengan cara yang memberikan integritas yang kuat, yaitu, jaminan data yang benar. Sistem identitas terdesentralisasi yang mendukung DON akan memungkinkan calon peminjam untuk melakukannya menghasilkan kredensial dengan jaminan tinggi yang membuktikan kelayakan kredit mereka sambil menjaganya kerahasiaan informasi sensitif. Secara khusus, peminjam dapat menghasilkan dana ini kredensial berdasarkan catatan dari sumber online yang berwenang dan hanya mengekspos data yang dibuktikan oleh DON, tanpa memaparkan data lain yang berpotensi sensitif. Untuk Misalnya, peminjam dapat menghasilkan kredensial yang menunjukkan bahwa nilai kreditnya dengan a sekelompok biro kredit melebihi ambang batas tertentu (misalnya 750), tanpa mengungkapkannya skor tepat atau data lain apa pun dalam catatannya. Selain itu, jika diinginkan, kredensial tersebut dapat dibuat secara anonim, yaitu nama pengguna dapat diperlakukan sebagai data sensitif dan dirinya sendiri tidak terekspos ke oracle node atau dalam kredensial terdesentralisasinya. Kredensial sendiri dapat digunakan secara chain atau offchain, tergantung pada aplikasinya. Singkatnya, peminjam dapat memberikan informasi penting kepada pemberi pinjaman atas kreditnya sejarah dengan integritas yang kuat dan tanpa risiko pemaparan yang tidak perlu dan sensitif data. Peminjam juga dapat memberikan berbagai kredensial yang menjaga kerahasiaan lainnya membantu dalam membuat keputusan peminjaman. Misalnya, kredensial dapat membuktikan identitas peminjam kepemilikan aset (off-chain), seperti yang kami tunjukkan pada contoh berikutnya. Contoh permohonan: Akreditasi: Banyak yurisdiksi membatasi kelas investor yang dapat menjual sekuritas yang tidak terdaftar. Misalnya, di AS, SEC Peraturan D menetapkan bahwa untuk mendapatkan akreditasi bagi peluang penanaman modal tersebut, an individu harus memiliki kekayaan bersih $1 juta, memenuhi persyaratan pendapatan minimum tertentu, atau memiliki kualifikasi profesional tertentu [209, 210]. Akreditasi saat ini prosesnya rumit dan tidak efisien, seringkali memerlukan surat pengesahan akuntan, atau bukti serupa. Sistem identitas yang terdesentralisasi akan memungkinkan pengguna untuk menghasilkan kredensial akun layanan keuangan online yang ada yang membuktikan kepatuhan terhadap akreditasi peraturan, memfasilitasi proses KYC yang lebih efisien dan menjaga privasi. Itu Terlebih lagi, properti DECO dan Town Crier yang menjaga privasi akan mengizinkan hal ini kredensial yang harus dihasilkan dengan jaminan integritas yang kuat tanpa secara langsung mengungkapkan rincian status keuangan pengguna. Misalnya, pengguna dapat membuat kredensial membuktikan bahwa dia memiliki kekayaan bersih setidaknya $1 juta tanpa mengungkapkan tambahan apa pun informasi tentang status keuangannya. 4.4 Saluran Prioritas Saluran prioritas adalah layanan baru yang berguna dan mudah dibuat menggunakan DON. Mereka
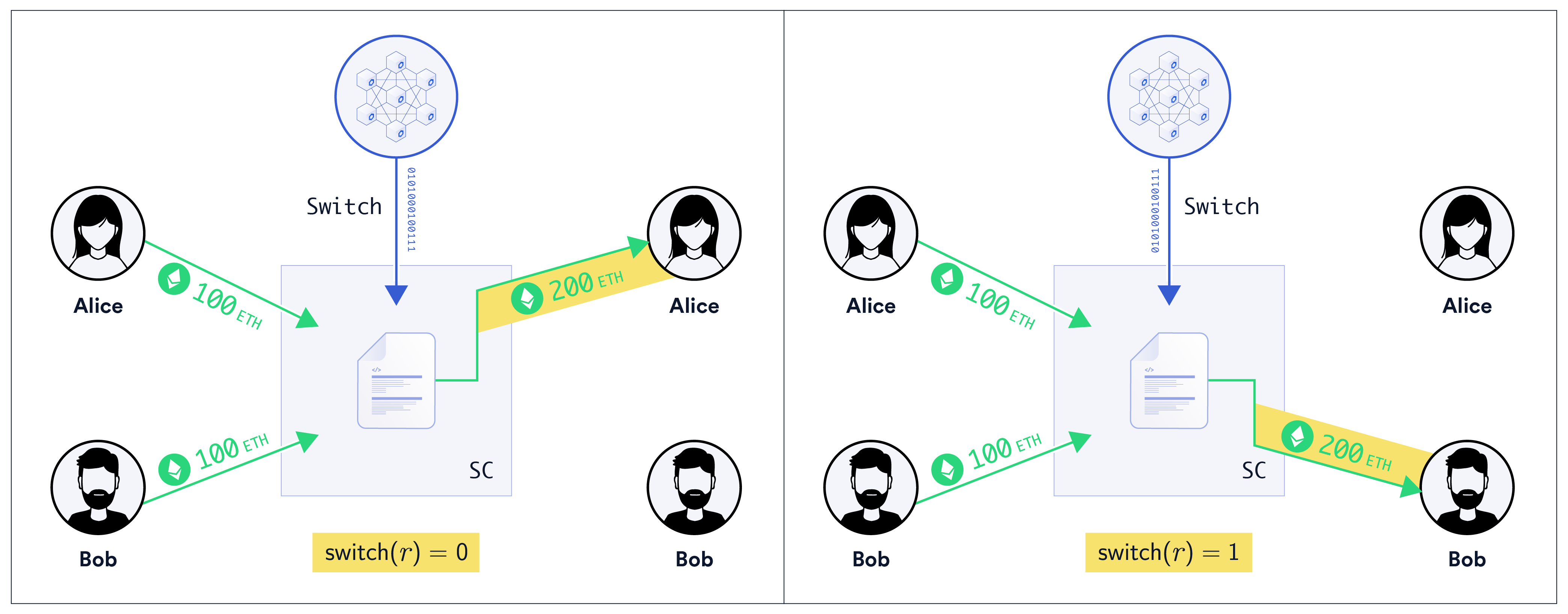
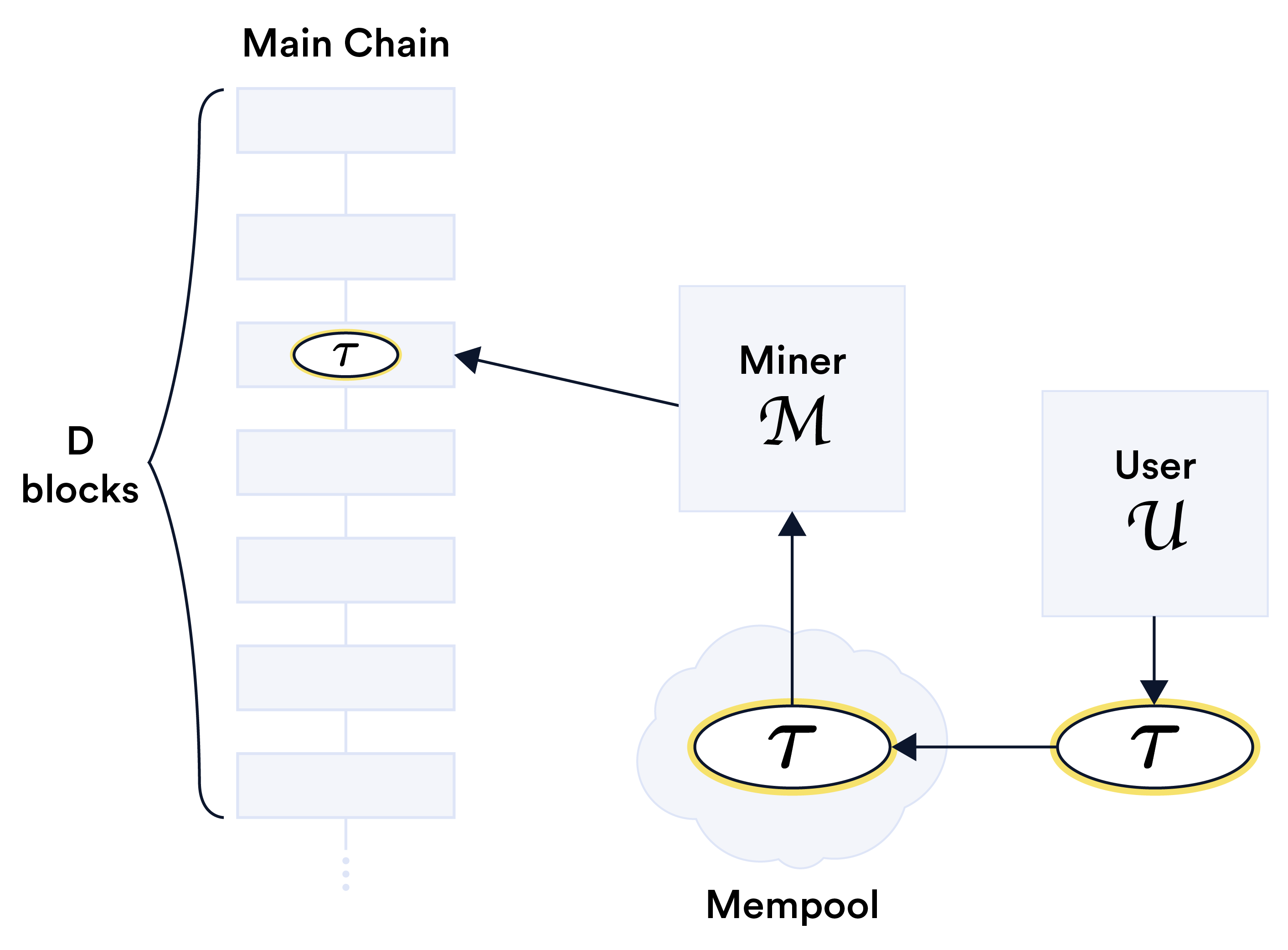
tujuannya adalah untuk mengirimkan transaksi terpilih dan berprioritas tinggi secara tepat waktu di MAINCHAIN selama periode kemacetan jaringan. Saluran prioritas dapat dilihat sebagai salah satu bentuk kontrak berjangka pada ruang blok dan dengan demikian sebagai komoditas kripto, sebuah istilah yang diciptakan sebagai bagiannya dari Proyek Chicago [61, 136]. Saluran prioritas ditujukan secara khusus bagi para penambang untuk mengaktifkan layanan infrastruktur, seperti oracles, fungsi tata kelola untuk kontrak, dll.—bukan untuk aktivitas tingkat pengguna biasa seperti transaksi keuangan. Faktanya, seperti yang dirancang di sini, menjadi prioritas saluran yang diterapkan oleh kurang dari 100% kekuatan penambangan di jaringan saja bisa memberikan batasan yang longgar pada waktu pengiriman, mencegah penggunaannya karena sangat bergantung pada kecepatan tujuan seperti berlari ke depan. Gambar 10: Saluran prioritas adalah jaminan yang diberikan oleh penambang M—atau, lebih umum, a kumpulan penambang M—kepada pengguna U bahwa transaksinya τ akan ditambang dalam blok D penyertaan dalam mempool. SC kontrak dapat menggunakan pemantauan DON untuk menegakkan peraturan tersebut persyaratan layanan saluran. Saluran prioritas berbentuk kesepakatan antara penambang atau sekumpulan penambang (atau kumpulan penambangan) M yang menyediakan saluran dan pengguna U yang membayar biaya untuk akses. M setuju bahwa ketika U mengajukan transaksi τ ke mempool (dengan harga gas berapa pun,tetapi batas gas yang telah disepakati sebelumnya), M akan menempatkannya pada rantai di dalam blok D berikutnya.8 Idenya digambarkan secara skematis pada Gambar 10. Deskripsi kontrak saluran prioritas: Saluran prioritas dapat diwujudkan sebagai a hybrid smart contract kira-kira sebagai berikut. Kami membiarkan SC menunjukkan logika pada MAINCHAIN dan itu di DON oleh exec. SC menerima deposit/taruhan \(d from M and an advance payment \)p dari U. A DON executable exec memonitor mempool, memicu penempatan transaksi oleh U. Ini mengirimkan pesan sukses ke SC jika U mengirimkan transaksi yang ditambang oleh M cara yang tepat waktu dan pesan kegagalan jika terjadi kegagalan layanan. SC mengirimkan pembayaran $p ke M dengan pesan sukses dan mengirimkan semua sisa dana, termasuk $d, ke U jika menerima pesan kegagalan. Setelah penghentian berhasil, itu melepaskan deposit $d ke M. Penambang M tentu saja dapat menyediakan saluran prioritas secara bersamaan ke beberapa saluran pengguna dan dapat membuka saluran prioritas dengan U untuk sejumlah pesan yang telah disepakati sebelumnya. 4.5 Menjaga Kerahasiaan DeFi / Campuran Saat ini, DeFi aplikasi [1] memberikan sedikit atau bahkan tidak ada sama sekali kerahasiaan bagi pengguna: Semua transaksi terlihat secara berantai. Berbagai pendekatan berbasis nol pengetahuan, misalnya, [149, 217], dapat memberikan privasi transaksi, dan TEF cukup umum untuk mendukungnya. Tapi pendekatan-pendekatan ini tidak komprehensif, dan, misalnya, biasanya tidak menyembunyikan hal tersebut aset yang menjadi dasar transaksi. Serangkaian alat komputasi yang pada akhirnya ingin kami dukung dalam DONs akan memungkinkan privasi dalam sejumlah cara berbeda yang dapat menutup kesenjangan tersebut, membantu melengkapi jaminan privasi sistem lain. Misalnya, Mixicles, instrumen DeFi yang menjaga kerahasiaan yang diusulkan oleh Chainlink peneliti Labs [135], dapat menyembunyikan jenis aset yang mendukung instrumen keuangan, dan secara alami cocok dengan DON kerangka kerja. Mixicles paling mudah dijelaskan dalam hal penggunaannya untuk mewujudkan biner sederhana pilihan. Opsi biner adalah instrumen keuangan yang memiliki dua pengguna, yaitu kami lihat di sini untuk konsistensi dengan [135] sebagai pemain, bertaruh pada acara dengan dua kemungkinan hasil, misalnya, apakah suatu aset melebihi harga target pada waktu yang telah ditentukan. Contoh berikut mengilustrasikan gagasan tersebut. Contoh 2. Alice dan Bob adalah pihak dalam opsi biner berdasarkan nilai suatu aset disebut Token Gelembung Carol (CBT). Alice bertaruh bahwa CBT akan memiliki harga pasar sebesar minimal 250 USD pada waktu T = tengah hari tanggal 21 Juni 2025; Bob bertaruh sebaliknya. Setiap pemain menyetor 100 ETH dengan batas waktu yang telah ditentukan. Pemain dengan posisi menang menerima 200 ETH (yaitu, memperoleh 100 ETH). 8D tentu saja harus cukup besar untuk memastikan bahwa M dapat memenuhi probabilitas yang tinggi. Untuk Misalnya, jika M mengontrol 20% kekuatan penambangan di jaringan, ia mungkin memilih D = 100, memastikan probabilitas kegagalan sebesar ≈2 × 10−10, yaitu kurang dari satu dalam satu miliar.Mengingat jaringan O Chainlink oracle yang sudah ada, implementasi sistem cerdas dapat dilakukan dengan mudah. kontrak SC yang merealisasikan perjanjian pada Contoh 2. Kedua pemain masing-masing melakukan deposit 100 ETH di SC. Beberapa saat setelah T, permintaan q dikirim ke O meminta harga r CBT pada saat T.O mengirimkan laporan r harga tersebut kepada SC. SC kemudian mengirimkan uang ke Alice jika r ≥250 dan Bob jika tidak. Pendekatan ini, bagaimanapun, mengungkapkan r pada rantai—membuatnya menjadi mudah bagi pengamat untuk menyimpulkan aset yang mendasari opsi biner. Dalam terminologi Mixicles, akan sangat membantu jika memikirkan secara konseptual tentang hasilnya dari SC dalam bentuk Switch yang mentransmisikan nilai biner yang dihitung sebagai predikat beralih (r). Dalam contoh kita, switch(r) = 0 jika r ≥250; mengingat hasil ini, Alice menang. Jika tidak, switch(r) = 1 dan Bob menang. DON dapat mewujudkan Mixicle dasar sebagai kontrak hibrid dengan menjalankan executable exec yang menghitung switch(r) dan melaporkannya secara berantai ke SC. Kami menunjukkan konstruksi ini pada Gambar 11. Gambar 11: Diagram Mixicle dasar pada Contoh 2. Untuk memberikan kerahasiaan on-chain laporkan r, dan dengan demikian aset yang mendasari opsi biner, oracle dikirimkan ke kontrak SC melalui Switch hanya saklar nilai biner (r). Kami menentukan adaptor ConfSwitch di Lampiran C.3 yang memudahkan untuk mencapai hal ini gol dalam DON. Ide dasar di balik ConfSwitch cukup sederhana. Daripada melaporkan nilai r, ConfSwitch hanya melaporkan nilai saklar biner saklar (r). SC bisa dirancang untuk melakukan pembayaran yang benar berdasarkan switch(r) saja, dan switch(r) dengan sendirinya tidak mengungkapkan informasi tentang aset dasar—CBT dalam contoh kita. Selain itu, dengan menempatkan ciphertext pada (q, r) pada buku besar yang dienkripsi dengan pkaud, kunci publik dari seorang auditor, adaptor ConfSwitch menciptakan jejak audit yang menjaga kerahasiaan. Mixicle dasar yang kami pilih untuk kesederhanaan untuk dijelaskan di sini hanya menyembunyikannya aset dan bertaruh di belakang opsi biner dalam contoh kita. Mixicle lengkap [135] kaleng memberikan dua bentuk kerahasiaan. Ia menyembunyikan dari pengamat: (1) Peristiwa apa pemain bertaruh pada (yaitu, q dan r) tetapi juga (2) Pemain mana yang memenangkan taruhan. Karena Mixicles dieksekusi di MAINCHAIN, salah satu pemain harus melakukan relay switch(r) dari DON ke MAINCHAIN, atau exec yang dapat dieksekusi dapat dibuat
dipicu pada output oleh ConfSwitch dan memanggil adaptor lain untuk mengirim switch(r). RANTAI UTAMA. Jenis kerahasiaan yang ketiga dan halus juga patut dipertimbangkan. Dalam implementasi dasar ConfSwitch, O menjalankan adaptor di DON dan dengan demikian mempelajari aset—CBT dalam contoh kita—dan dengan demikian sifat dari opsi biner. Seperti yang dibahas pada Lampiran C.3, namun, DECO atau Town Crier juga dapat digunakan untuk bahkan menyembunyikan informasi ini dari O. Dalam kasus ini, O tidak mengetahui informasi lebih lanjut daripada pengamat publik SC. Untuk rincian lebih lanjut tentang Mixicles, kami merujuk pembaca ke [135].
去中心化支持的去中心化服务
甲骨文网络 为了说明 DON 的多功能性以及它们如何启用大量新服务, 我们在本节中介绍了五个基于 DON 的应用程序示例,并描述了 实现它们的混合合约:(1)储备证明,一种跨链服务形式; (2)与企业/遗留系统对接,即创建基于中间件的 抽象层,有助于以最少的成本开发 blockchain 应用程序 blockchain-特定代码或专业知识; (3) 去中心化的身份,使用户能够 获取并管理自己的身份证件和凭证; (4) 优先通道, 确保及时纳入关键基础设施交易的服务(例如 oracle 报告)在 blockchain 上; (5) 保密DeFi,即财务信息 smart contract 隐藏参与方的敏感数据。 在这里,我们
使用 SC 表示混合合约的主链部分并描述 DON 组件单独或作为可执行文件执行。 4.1 储备金证明 对于许多应用程序来说,在 blockchain 之间中继状态非常有用。一个 此类服务的流行应用是加密货币包装。包裹硬币之类的 随着 WBTC [15] 正在成为去中心化金融 (DeFi) 中的流行资产。他们 涉及将“包装”的支持资产存入其源 blockchain MAINCHAIN(1) 并在不同的目标 blockchain MAINCHAIN(2) 上创建相应的 token。 例如,WBTC 是 Ethereum blockchain 上的 ERC20 token 对应的 至 Bitcoin blockchain 上的 BTC。 由于 MAINCHAIN(2) 上的合约无法直接查看 MAINCHAIN(1), 他们必须显式或隐式依赖 oracle 来报告已包装的存款 smart contract 中的资产,产生有时称为储备证明的东西。在 WBTC [15],例如托管人 BitGo 持有 BTC 并发行 WBTC, Chainlink 网络提供储备证明 [76]。 DON 本身可以提供储备证明。但是,使用 DON 是可能的 走得更远。 DON 可以管理机密,并通过使用适当的适配器, 可以在任何所需的 blockchain 上进行交易。因此,DON 可以采取行动 作为众多托管人之一,甚至作为唯一的去中心化托管人 打包的资产。 DONs 因此可以作为增强安全性的平台 使用储备证明的现有服务。 例如,假设 MAINCHAIN(1) 为 Bitcoin,MAINCHAIN(2) 为 Ethereum。 在 MAINCHAIN(2) 上,合约 SC 发行代表打包 BTC 的 tokens。 DON 控制BTC地址addr(1) DON。为了包装 BTC,用户 U 从 地址(1) U 至地址(1) DON 以及 MAINCHAIN(2)-地址 addr(2) 乌。 DON 监视器 地址(1) DON 通过 MAINCHAIN(1) 的适配器。 在观察到 U 的存款后,以足够高的概率确认,它通过适配器向 SC 发送一条消息 主链(2)。该消息指示 SC 为 addr(2) 铸造 X tokens 乌。 当 U 释放 X tokens 时,会发生相反的情况。 然而,在 MAINCHAIN(1) 上, 地址(1) DON 发送 X BTC 到 addr(1) U(或另一个地址,如果用户如此请求)。 当然,这些协议可以进行调整,以便与交易所合作,而不是直接 与用户。 4.2 与企业/遗留系统接口 DONs 可以充当 blockchains 之间的桥梁,如证明的示例所示 储备金,但另一个目标是让它们充当储备金之间的双向桥梁 blockchain 和旧系统 [176] 或 blockchain 类似系统,例如中央银行 数字货币[30]。 企业在连接现有系统和 去中心化系统的流程,包括:• 区块链敏捷性:区块链系统变化迅速。企业可能会遇到 blockchain 的快速新出现或流行度上升,其中 交易对手有意愿进行交易,但企业无能力进行交易 现有基础设施的支持。一般来说,blockchains 的活力使得 单个企业很难跟上整个生态系统的步伐。 • 区块链特定的开发资源:对于许多组织来说,雇用或孵化尖端的blockchain 专业知识是很困难的,特别是考虑到 敏捷性的挑战。 • 私钥管理:管理 blockchain 或加密货币的私钥需要不同于传统网络安全的运营专业知识 实践中,很多企业都无法做到这一点。 • 保密性:企业对于暴露其敏感和专有信息持谨慎态度。 数据上链。 为了解决前三个困难,开发人员可以简单地使用 DON 作为安全的中间件层,使企业系统能够读取或写入 blockchains。 DON 可以抽象出详细的技术考虑因素,例如 为开发者和用户提供气体动力学、链重组等。由 为企业系统提供简化的 blockchain 接口,因此 DON 可以 大大简化了 blockchain 感知企业应用程序的开发,消除了企业获取或孵化 blockchain 特定开发资源的负担。 DONs 的这种使用特别有吸引力,因为它使企业开发人员能够 创建很大程度上与 blockchain 无关的智能合约应用程序。结果, 较大的 blockchain 集(其中 DON 被检测为充当中间件), 企业用户可以轻松访问的更大的 blockchain 集合。开发商 可以通过最少的修改将应用程序从现有的 blockchain 移植到新的应用程序 到他们内部开发的应用程序。 为了解决额外的保密问题,开发人员可以向 我们在本文中介绍并期望部署以支持 DON 应用程序的工具。 其中包括 DECO 和 Town Crier 第 3.6.2 节以及保密性 第 7.1.2 节讨论了 API 修改,本节其余部分介绍了一些特定于应用程序的方法。这些 DON 系统可以提供 关于企业系统状态的高完整性、链上证明而不泄露 敏感企业源数据上链。 4.3 去中心化身份 去中心化身份是用户应该能够 获取并管理自己的凭证,而不是依赖第三方来做 所以。去中心化凭证是对持有者属性或主张的证明,这通常称为索赔。凭证由实体进行数字签名,通常称为 发行者,可以权威地将声明与用户关联起来。在大多数提议的方案中, 声明与去中心化标识符(DID)相关联,这是一个通用标识符 给定用户。凭证绑定到用户持有其私钥的公钥。 因此,用户可以使用她的私钥证明拥有索赔。 去中心化身份是有远见的,现有的和拟议的方案,例如,[14, 92, 129, 216],具有三个严重的局限性: • 缺乏遗留兼容性:现有的去中心化身份系统依赖于 由称为发行者的权威机构组成的社区,负责生成 DID 凭证。因为 现有的网络服务通常不会对数据进行数字签名,必须启动发行者 作为特殊用途的系统。因为没有动力就没有动力这样做 去中心化的身份生态系统,就会出现先有鸡还是先有蛋的问题。在其他方面 换句话说,目前还不清楚如何引导发行人生态系统。 • 密钥管理不可行:去中心化身份系统要求用户 管理私钥,加密货币的经验已经证明了这一点 成为一个不可行的责任。据估计,大约有 4,000,000 个 Bitcoin 已被 由于密钥管理故障 [194] 而永远丢失,并且许多用户存储了他们的 加密资产与交易所[193],从而破坏权力下放。 • 缺乏保护隐私的女巫抵抗:投票、token 销售期间公平分配 token 等应用程序的基本安全要求是: 用户无法断言多个身份。现有的去中心化身份提案要求用户透露他们的现实世界身份才能实现这一目标 女巫抵抗,从而破坏重要的隐私保证。 可以使用节点委员会的组合来解决这些问题 在 DON 中执行分布式计算并使用 DECO 等工具 或 Town Crier,如名为 CanDID [160] 的系统中所示。 DECO 或 Town Crier 可以通过设计将现有的 Web 服务转变为无需修改 成为保密凭证颁发者。它们使 DON 能够导出相关的 为此目的的数据到凭证中,同时隐藏不应该的敏感数据 出现在凭证中。 另外,为了方便用户恢复密钥,从而解决密钥管理问题 问题,DON 可以允许用户以秘密共享的形式存储私钥。用户可以 通过向 DON 中的节点证明来恢复其密钥——类似地,使用 Town Crier 或 DECO——通过一组预先确定的网络提供商(例如, 推特、谷歌、脸书)。相对于使用 Town Crier 或 DECO 的好处 OAUTH,是用户隐私。这两个工具使用户能够避免向 DON 泄露信息 网络提供商标识符——通常可以从中导出现实世界的身份。 最后,为了提供 Sybil 抵抗,如 [160] 所示,DON 可以 为用户执行独特的现实世界标识符的隐私保护转换 (例如,社会安全号码(SSN))在用户注册时添加到链上标识符中。因此,系统可以检测重复注册,而无需敏感数据,例如 SSN 被泄露给各个 DON 节点。7 DON 可以代表外部去中心化身份提供任何这些服务 未经许可或经过许可的 blockchain 上的系统,例如 Hyperledger 的实例 印地[129]。 应用示例:KYC: 去中心化身份有望作为一种手段 简化 blockchains 上金融应用程序的要求,同时提高用户体验 隐私。它可以帮助解决两个挑战,即反洗钱/了解你的客户 (AML / KYC) 法规下的认证和合规义务。 许多国家的反洗钱法规要求金融机构(和其他企业)建立并验证与其进行交易的个人和企业的身份。 他们执行交易。 KYC 是金融机构的一个组成部分 更广泛的反洗钱政策,通常还涉及监控用户行为和资金流动等。 KYC 通常涉及用户以某种形式呈现身份凭证(例如, 进入在线网络表单,在用户面前举起身份证件 在视频会议等)。安全创建和呈现去中心化凭证 原则上在几个方面可能是一个有益的替代方案,即:(1) KYC 流程对于用户和金融机构来说更加高效,因为一旦 获得证书后,可以无缝地向任何金融机构出示; (2) 通过妥协减少身份盗窃的机会,从而减少欺诈 个人身份信息 (PII) 和视频验证过程中的欺骗;和 (3) 由于用户保留控制权,降低金融机构 PII 泄露的风险 他们自己的数据。 考虑到金融机构因 AML 合规失败而支付的数十亿美元罚款,以及许多金融机构每年在 KYC 上花费数百万美元,改进措施可以为金融机构带来可观的节省 并且,推而广之,对于消费者[196]。虽然传统金融业发展缓慢 为了采用新的合规工具,DeFi 系统越来越多地采用它 [43]。 应用示例: 抵押贷款不足: 大多数 DeFi 应用程序 如今的支持贷款仅源自完全抵押贷款。这些是贷款 对于存入价值超过贷款价值的加密货币资产的借款人。 最近,人们对 DeFi 社区通常所说的抵押不足贷款产生了兴趣。相比之下,这些贷款需要相应的抵押品 其价值小于贷款本金的价值。抵押贷款不足 类似于传统金融机构通常发放的贷款。而不是依靠 他们以存入的抵押品作为贷款偿还的保证,而是以贷款为基础 对借款人信用记录的决定。 7 此转换依赖于分布式伪随机函数 (PRF)。抵押不足的贷款是 DeFi 贷款市场的一个新兴但不断增长的部分。他们依赖于传统金融所采用的机制 机构,例如法律合同 [91]。是他们成长的必备条件 将能够以提供强大完整性的方式向 DeFi 系统提供有关用户信用度的数据(传统贷款决策的关键因素),即 保证数据正确。 启用 DON 的去中心化身份系统将使潜在借款人能够 生成高保证的凭证,证明其信誉度,同时保留 敏感信息的机密性。具体来说,借款人可以生成这些 基于权威在线来源记录的凭据,同时仅公开 数据由 DON 证明,而不暴露其他潜在敏感数据。对于 例如,借款人可以生成一个凭证,表明她的信用评分 信用局集合超过特定阈值(例如 750),但未透露她的信息 精确的分数或她记录中的任何其他数据。此外,如果需要,此类凭证 可以匿名生成,即用户名可以被视为敏感数据 并且其本身不会暴露于 oracle 节点或她的去中心化凭证中。凭证 它本身可以在链上或链下使用,具体取决于应用程序。 总之,借款人可以向贷方提供有关其信用的重要信息 历史具有很强的完整性,并且没有暴露不必要的敏感信息的风险 数据。 借款人还可以提供各种其他保密凭证 有助于做出贷款决策。例如,凭证可以证明借款人的 拥有(链下)资产,正如我们在下一个示例中所示。 应用示例: 认证: 许多司法管辖区限制可以出售未注册证券的投资者类别。例如,在美国,SEC D 条例规定,要获得此类投资机会的认可, 个人必须拥有 100 万美元的净资产,满足某些最低收入要求,或具有某些专业资格 [209, 210]。目前的认证 流程繁琐且低效,通常需要来自以下机构的证明信 会计师或类似的证据。 去中心化的身份系统将使用户能够从以下位置生成凭证 证明符合认可的现有在线金融服务账户 法规,促进更高效和保护隐私的 KYC 流程。 的 此外,DECO 和 Town Crier 的隐私保护特性将允许这些 生成的凭证具有强有力的完整性保证,而不会直接泄露用户财务状况的详细信息。例如,用户可以生成凭证 证明她的净资产至少为 100 万美元,且无需透露任何其他信息 有关她的财务状况的信息。 4.4 优先频道 优先通道是一项有用的新服务,可以使用 DON 轻松构建。他们的
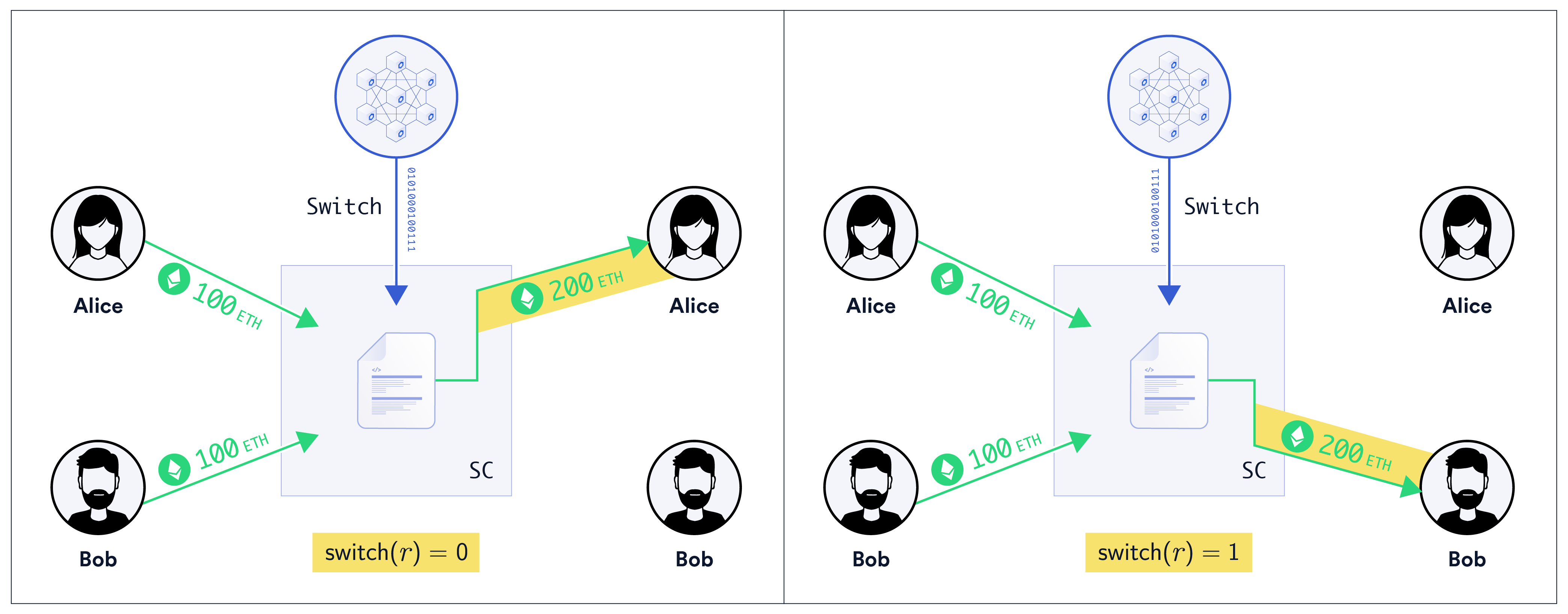
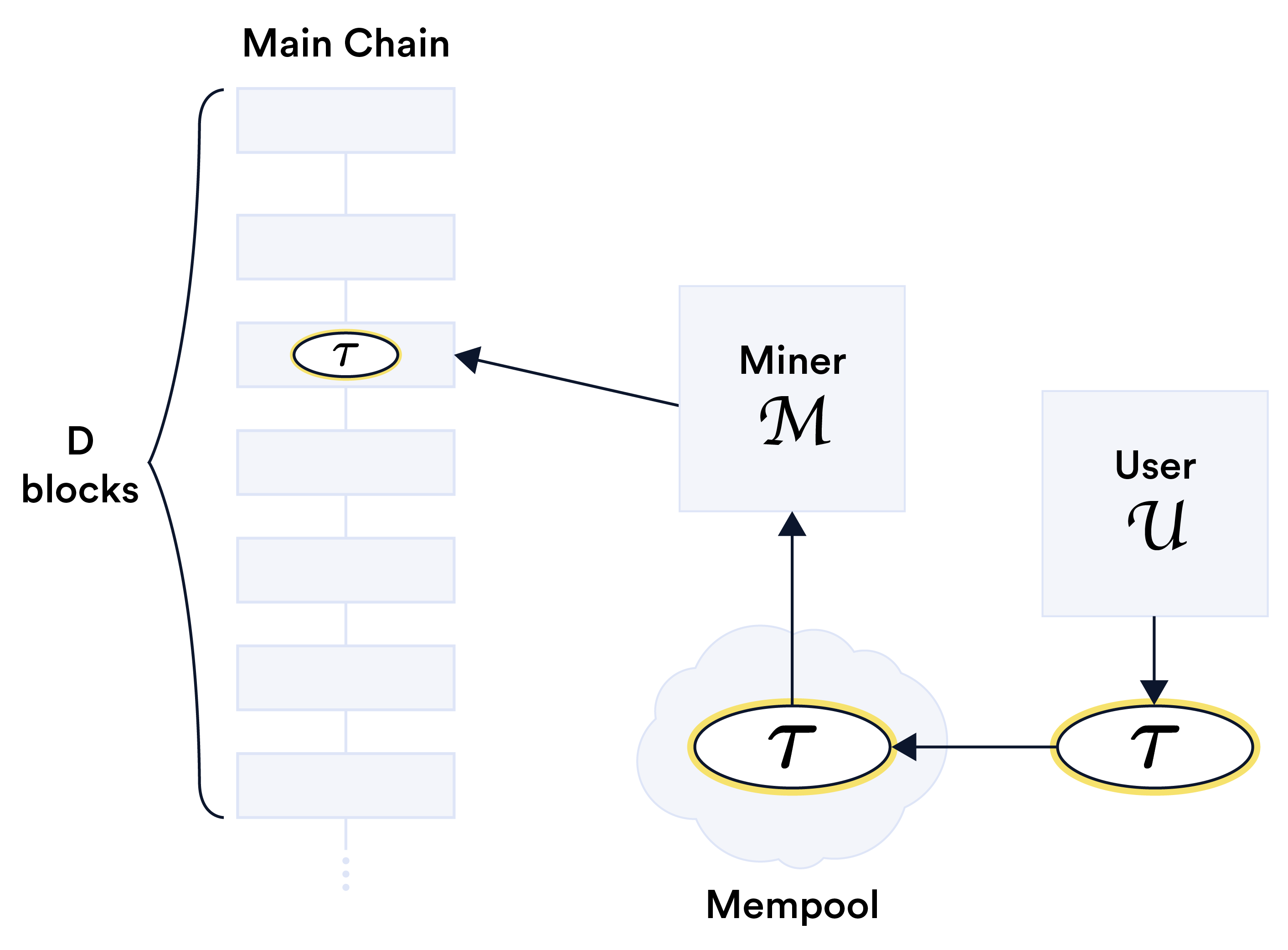
目标是在主链上及时交付精选的高优先级交易 在网络拥塞期间。优先通道可以被视为一种形式 区块空间上的期货合约,因此作为一种加密商品,这个术语是作为一部分创造的 芝加哥项目 [61, 136]。 优先通道专门用于矿工启用基础设施服务,例如 oracles、合约的治理功能等,而不是用于金融交易等普通用户级活动。 事实上,按照这里的设计,优先 网络中不到100%的算力实施的通道只能 对交货时间提供宽松的限制,防止其用于高度依赖速度的 目标,例如抢先交易。 图 10:优先通道是矿工 M 的保证,或者更一般地说,是矿工 M 的保证 一组矿工 M——向用户 U 表示她的交易 τ 将在 D 块内被开采 包含在内存池中。合约 SC 可以使用 DON 监控来强制执行 频道的服务条款。 优先通道采用一个或一组矿工之间协议的形式 提供通道的(或矿池)M和支付访问费用的用户U。 M 同意当 U 向内存池提交交易 τ 时(无论 Gas 价格如何,但预先商定的 Gas 限制),M 会将其放在接下来的 D 区块内的链上。8 图 10 示意性地描述了这个想法。 优先通道合约说明: 优先级信道可以被实现为 混合 smart contract 大致如下。我们让 SC 表示 MAINCHAIN 上的逻辑 以及 exec 的 DON 上的内容。 SC 接受来自 U. A 的存款/股份 \(d from M and an advance payment \)p DON 可执行文件 exec 监视内存池,在交易放置时触发 如果U提交了M挖矿的交易,它会向SC发送成功消息 服务失败时的及时方式和失败消息。 SC 在收到成功消息后将付款 $p 发送给 M,并发送所有剩余资金, 包括 $d,如果收到失败消息,则发送给 U。成功终止后, 将存款 $d 释放给 M。 矿工M当然可以同时向多个矿工提供优先通道 用户可以与 U 打开优先通道以接收预先商定数量的消息。 4.5 保密 DeFi / Mixicles 如今,DeFi 应用程序 [1] 为用户提供的保密性几乎为零:所有交易在链上都是可见的。各种基于零知识的方法,例如[149, 217], 可以提供交易隐私,并且 TEF 足够通用来支持它们。但是 这些方法并不全面,例如,通常不会隐藏 交易所基于的资产。 我们最终打算在 DONs 中支持的广泛计算工具将 通过多种不同方式实现隐私保护,可以弥补此类差距,有助于补充其他系统的隐私保证。例如,Mixicles,一种由 Chainlink 实验室研究人员 [135] 提出的保密 DeFi 工具,可以隐藏 支持金融工具的资产类型,非常自然地适合 DON 框架。 Mixicles 最容易解释为它们用于实现简单的二进制文件 选项。 二元期权是一种有两个用户的金融工具,我们将 请参阅此处以与 [135] 作为玩家保持一致,对有两种可能的赛事进行投注 结果,例如资产是否在预先指定的时间超过目标价格。 下面的例子说明了这个想法。 示例 2. Alice 和 Bob 是基于资产价值的二元期权的参与方 称为卡罗尔的泡沫代币(CBT)。 Alice 打赌 CBT 的市场价格为 时间 T = 2025 年 6 月 21 日中午至少 250 美元;鲍勃打赌相反。每个玩家 在预定期限内存入 100 ETH。获胜位置的玩家 收到 200 ETH(即收益 100 ETH)。 8D当然必须足够大,以保证M能够符合高概率。 对于 例如,如果M控制网络中20%的算力,它可能会选择D = 100,确保 失效概率为 ≈2 × 10−10,即小于十亿分之一。给定现有的 Chainlink oracle 网络 O,很容易实现智能 实现例2协议的合约SC,两个玩家各自存款 100 ETH 为 SC。 T 之后的某个时间,查询 q 被发送到 O 请求价格 r CBT 在 T.O 时间向 SC 发送该价格的报告 r。 SC然后将钱发送给Alice 如果 r ≥250,则 Bob 如果不是。然而,这种方法揭示了链上的 r——使其变得容易 让观察者推断出二元期权背后的资产。 在 Mixicles 的术语中,从概念上思考结果是有帮助的 SC 就 Switch 而言,它传输作为谓词计算的二进制值 开关(r)。在我们的示例中,如果 r ≥250,则 switch(r) = 0;鉴于此结果,爱丽丝获胜。 否则 switch(r) = 1 并且 Bob 获胜。 DON 可以通过运行可执行文件将基本 Mixicle 实现为混合合约 exec 计算 switch(r) 并将其在链上报告给 SC。我们展示这个结构 如图 11 所示。 图 11:示例 2 中的基本 Mixicle 图表。为以下内容提供链上保密性: 报告 r,因此二元期权的基础资产 oracle 发送到 仅通过 Switch 签订二进制值 switch(r) 合约 SC。 我们在附录 C.3 中指定了一个适配器 ConfSwitch,可以轻松实现这一点 DON 的目标。 ConfSwitch 背后的基本思想非常简单。而不是报告 r 值,ConfSwitch 仅报告二进制开关值 switch(r)。 SC 可以 旨在仅基于 switch(r) 和 switch(r) 本身进行正确支付 没有透露有关标的资产(在我们的示例中为 CBT)的信息。另外, 通过将密文放在账本上的 (q, r) 上,并使用 pkaud 的公钥进行加密 作为审计员,适配器 ConfSwitch 创建保密审计跟踪。 为了简单起见,我们在这里选择的基本 Mixicle 只隐藏了 在我们的示例中,二元期权背后的资产和赌注。一个成熟的 Mixicle [135] 可以 提供两种形式的保密性。它向观察者隐瞒了:(1)发生了什么事件 玩家对(即 q 和 r)下注,还对 (2) 哪位玩家赢得了赌注。 由于 Mixicles 是在主链上执行的,因此任一玩家都需要中继 switch(r) 从 DON 到 MAINCHAIN,或者可以创建一个可执行的 exec
由 ConfSwitch 输出触发并调用另一个适配器将 switch(r) 发送到 主链。 第三种微妙的保密方式也值得考虑。在 ConfSwitch 的基本实现中,O 在 DON 上运行适配器,从而学习 资产——在我们的例子中是 CBT——以及二元期权的本质。正如所讨论的 然而,在附录 C.3 中,还可以使用 DECO 或 Town Crier 来 甚至向 O 隐瞒此信息。在这种情况下,O 不会了解更多信息 而非 SC 的公共观察员。 有关 Mixicles 的更多详细信息,我们建议读者参阅 [135]。
Layanan Pengurutan yang Adil
Salah satu layanan penting yang kami harapkan akan ditawarkan oleh DONs yang memanfaatkan kemampuan jaringan, komputasi, dan penyimpanannya disebut Fair Sequencing Services (FSS). Meskipun FSS mungkin dipandang hanya sebagai aplikasi yang diwujudkan dalam kerangka DON, kami menyorotinya sebagai layanan yang kami yakini akan memiliki permintaan tinggi di seluruh dunia. blockchains, dan kami berharap jaringan Chainlink akan mendukung secara aktif. Ketika dijalankan di jaringan blockchain publik, banyak aplikasi DeFi saat ini mengungkapkan informasi yang dapat dimanfaatkan oleh pengguna untuk keuntungan mereka sendiri, serupa dengan jenis kebocoran orang dalam dan peluang manipulasi yang tersebar luas pasar [64, 155]. FSS malah membuka jalan menuju ekosistem DeFi yang adil. FSS membantu pengembang membangun kontrak DeFi yang terlindungi dari manipulasi pasar akibat kebocoran informasi. Mengingat masalah yang kami soroti di bawah ini, FSS adalah jawabannya sangat menarik untuk layanan lapisan-2 dan cocok dengan kerangka layanan tersebut yang kita bahas di Bagian 6. Tantangannya: Dalam sistem tanpa izin yang ada, transaksi diurutkan seluruhnya atas kebijaksanaan penambang. Dalam jaringan yang berizin, node validator mungkin digunakan kekuatan yang sama. Ini adalah bentuk sentralisasi sementara yang sebagian besar tidak diakui di negara ini jika tidak, sistem terdesentralisasi. Seorang penambang dapat (sementara) menyensor transaksinya keuntungan sendiri [171] atau susun ulang untuk memaksimalkan keuntungannya sendiri, sebuah gagasan yang disebut nilai yang dapat diekstraksi (minerextractable value/MEV) [90]. Istilah MEV sedikit menipu: Istilah ini tidak merujuk hanya untuk nilai yang dapat ditangkap oleh penambang: Beberapa MEV dapat ditangkap oleh pengguna biasa. Namun, karena penambang memiliki kekuatan yang lebih besar daripada pengguna biasa, MEV mewakili batas atas jumlah nilai yang dapat diperoleh entitas mana pun melalui penataan ulang permusuhan. dan penyisipan transaksi pelengkap. Bahkan ketika penambang memesan transaksi dengan sederhana berdasarkan biaya (gas), tanpa manipulasi, pengguna sendiri dapat memanipulasi harga gas untuk menguntungkan transaksi mereka dibandingkan transaksi yang kurang canggih. Daian dkk. [90] mendokumentasikan dan mengukur cara yang dilakukan bot (bukan penambang). keuntungan dinamika gas dengan cara yang merugikan pengguna sistem DeFi saat ini dan bagaimana caranya MEV bahkan mengancam stabilitas lapisan konsensus yang mendasarinya di blockchain. Contoh lain dari manipulasi urutan transaksi muncul secara teratur, misalnya, [50, 154].Metode pemrosesan transaksi baru seperti rollups adalah pendekatan yang sangat menjanjikan untuk masalah penskalaan blockchains throughput tinggi. Namun mereka tidak membahasnya masalah MEV. Sebaliknya, mereka mengalihkannya ke entitas yang menghasilkan rollup. Itu entitas, baik operator smart contract atau pengguna yang memberikan (zk-)rollup dengan bukti keabsahan, mempunyai kuasa untuk memerintahkan dan memasukkan transaksi. Dengan kata lain, rollups tukar MEV dengan REV: Nilai Rollup-Extractable. MEV mempengaruhi transaksi mendatang yang telah dikirimkan ke mempool tetapi belum berkomitmen pada rantai. Informasi tentang transaksi tersebut tersebar luas tersedia di jaringan. Penambang, validators, dan peserta jaringan biasa bisa oleh karena itu manfaatkan pengetahuan ini dan ciptakan transaksi yang bergantung. Selain itu, penambang dan validator dapat memengaruhi urutan transaksi yang mereka lakukan diri mereka sendiri dan memanfaatkannya untuk keuntungan mereka. Masalah pengaruh yang tidak semestinya dari para pemimpin terhadap tatanan transaksi berdasarkan konsensus protokol telah dikenal dalam literatur sejak tahun 1990an [71, 190], namun belum ada yang memuaskan. solusi telah direalisasikan dalam praktik sejauh ini [97]. Alasan utamanya adalah solusi-solusi yang diusulkan—setidaknya hingga saat ini—tidak dapat langsung diintegrasikan ke masyarakat blockchains, karena mereka mengandalkan konten transaksi yang tetap dirahasiakan hingga setelahnya pesanan mereka telah ditentukan. Ikhtisar Layanan Pengurutan Adil (FSS): DONs akan menyediakan alat untuk mendesentralisasikan pemesanan transaksi dan menerapkannya sesuai dengan kebijakan yang ditentukan oleh pihak yang mengandalkan pembuat kontrak, idealnya yang adil, dan tidak menguntungkan pihak-pihak yang menginginkannya memanipulasi pemesanan transaksi. Secara kolektif, alat-alat ini merupakan FSS. FSS mencakup tiga komponen. Yang pertama adalah pemantauan transaksi. Di FSS, oracle node di O memantau mempool MAINCHAIN dan (jika diinginkan) mengizinkan penyerahan transaksi off-chain melalui saluran khusus. Yang kedua adalah urutan transaksi. Node dalam transaksi pesanan O untuk kontrak yang mengandalkan sesuai dengan kebijakan yang ditentukan untuk kontrak itu. Yang ketiga adalah posting transaksi. Setelah transaksi diurutkan, node-node di O bersama-sama mengirimkan transaksi tersebut ke rantai utama. Manfaat potensial dari FSS meliputi: • Kewajaran pesanan: FSS mencakup alat untuk membantu pengembang memastikan transaksi tersebut masukan pada suatu kontrak tertentu diurutkan sedemikian rupa sehingga tidak menimbulkan ketidakadilan keuntungan bagi pengguna yang memiliki sumber daya yang baik dan/atau paham secara teknis. Kebijakan pemesanan dapat ditentukan untuk tujuan ini. • Pengurangan atau penghapusan kebocoran informasi: Dengan memastikan bahwa peserta jaringan tidak dapat memanfaatkan pengetahuan tentang transaksi yang akan datang, FSS dapat mengurangi atau menghilangkan serangan seperti front-running yang didasarkan pada informasi yang tersedia di jaringan sebelum transaksi dilakukan. Mencegah eksploitasi terhadap hal tersebut kebocoran memastikan bahwa transaksi permusuhan yang bergantung pada pending asli transaksi tidak dapat masuk ke buku besar sebelum transaksi awal dilakukan.• Mengurangi biaya transaksi: Dengan menghilangkan kebutuhan pemain akan kecepatan dalam mengirimkan transaksi mereka ke smart contract, FSS dapat sangat mengurangi biaya pemrosesan transaksi. • Urutan prioritas: SJK secara otomatis dapat memberikan prioritas khusus pada transaksi-transaksi penting memesan. Misalnya, untuk mencegah serangan terdepan terhadap oracle laporan, misalnya [79], FSS dapat memasukkan laporan oracle ke dalam aliran transaksi secara surut. Tujuan umum FSS di DONs adalah memberdayakan DeFi pencipta untuk mewujudkan keadilan sistem keuangan, yaitu sistem yang tidak menguntungkan pengguna (atau penambang) tertentu atas yang lain berdasarkan kecepatan, pengetahuan orang dalam, atau kemampuan untuk melakukan teknis manipulasi. Meskipun gagasan umum tentang keadilan masih sulit dipahami, dan keadilan yang sempurna tetap ada akal sehat apa pun tidak dapat dicapai, FSS bertujuan untuk menyediakan pengembang dengan kekuatan seperangkat alat sehingga mereka dapat menerapkan kebijakan yang membantu memenuhi tujuan desain mereka untuk DeFi. Kami mencatat bahwa tujuan utama FSS adalah bertindak sebagai layanan pengurutan yang adil RANTAI UTAMA yang menjadi target DON, beberapa dari keinginan keadilan yang sama dengan FSS jaminan juga dapat sesuai untuk protokol (terdesentralisasi) yang dijalankan di antara mereka DON pesta. Dengan demikian, FSS dapat dipandang lebih luas sebagai layanan yang disediakan oleh suatu subset dari DON node untuk mengurutkan secara wajar tidak hanya transaksi yang dikirim oleh pengguna MAINCHAIN tetapi juga transaksi (yaitu pesan) yang dibagikan di antara DON node lainnya. Di bagian ini, kami akan fokus terutama pada tujuan mengurutkan transaksi MAINCHAIN. Organisasi bagian: Di Bagian 5.1, kami menjelaskan dua aplikasi tingkat tinggi yang memotivasi desain FSS: mencegah laporan oracle yang berjalan di awal dan mencegah transaksi pengguna yang berjalan di depan. Kami kemudian memberikan rincian lebih lanjut tentang desain FSS di Bagian 5.2. Bagian 5.3 menjelaskan contoh-contoh jaminan dan sarana ketertiban yang adil untuk mencapainya. Terakhir, Bagian 5.4 dan Bagian 5.5 membahas ancaman tingkat jaringan terhadap kebijakan dan cara untuk mengatasinya, masing-masing untuk banjir jaringan dan Sybil serangan. 5.1 Masalah yang Berjalan di Depan Untuk menjelaskan tujuan dan desain FSS, kami menjelaskan dua bentuk umum front-running serangan dan keterbatasan solusi yang ada. Front-running mencontohkan sebuah kelas serangan pemesanan transaksi: Ada sejumlah serangan terkait seperti backrunning dan sandwiching (front-running plus back-running) [237] yang tidak kami bahas di sini, namun FSS juga membantu mengatasinya. 5.1.1 Oracle Terdepan Dalam peran tradisionalnya dalam menyediakan data off-chain ke blockchain aplikasi, oracles menjadi target alami untuk serangan terdepan.Pertimbangkan pola desain umum yang menggunakan oracle untuk memasok berbagai feed harga ke bursa on-chain: secara berkala (katakanlah setiap jam), oracle mengumpulkan data harga untuk aset yang berbeda dan mengirimkannya ke kontrak pertukaran. Transaksi data harga ini menghadirkan peluang arbitrase yang jelas: Misalnya, jika laporan oracle terbaru mencantumkan harga yang jauh lebih tinggi untuk beberapa aset, musuh dapat menjalankan laporan oracle terlebih dahulu ke membeli aset dan segera menjualnya kembali setelah laporan oracle diproses. Guncangan kecepatan dan penetapan harga yang berlaku surut: Solusi alami untuk masalah awal oracle adalah dengan memberikan prioritas khusus pada laporan oracle dibandingkan transaksi lainnya. Untuk misalnya, laporan oracle dapat dikirim dengan biaya tinggi untuk mendorong penambang agar memprosesnya mereka terlebih dahulu. Namun hal ini tidak akan mencegah terjadinya front-running jika peluang arbitrase tinggi, juga tidak dapat mencegah arbitrase yang dilakukan oleh para penambang itu sendiri. Oleh karena itu, beberapa bursa terpaksa menerapkan “speedbumps” kelas berat, seperti mengantri transaksi pengguna untuk sejumlah blok sebelum diproses. mereka, atau menyesuaikan harga secara surut ketika laporan oracle baru tiba. Kerugian dari solusi ini adalah menambah kompleksitas pada implementasi pertukaran, meningkatkan kebutuhan penyimpanan dan biaya transaksi, serta mengganggu pengalaman pengguna karena pertukaran aset hanya dikonfirmasi setelah jangka waktu yang signifikan. Membonceng: Sebelum beralih ke FSS, kita bahas piggybacking, cara yang cukup sederhana dan solusi elegan untuk masalah oracle yang sedang berjalan. Ini tidak berlaku untuk alamat Namun, berjalan paling depan dalam skenario lain. Singkatnya, alih-alih mengirimkan laporan secara berkala ke kontrak on-chain, oracles menerbitkan laporan bertanda tangan yang ditambahkan pengguna ke transaksi mereka saat membeli atau menjual aset on-chain. Pertukaran kemudian hanya memeriksa apakah laporan tersebut valid dan baru (misalnya, oracle dapat menandatangani rentang blok yang laporannya valid), dan mengekstrak umpan harga yang relevan darinya. Pendekatan sederhana ini memiliki sejumlah keunggulan dibandingkan “kecepatan” di atas. pendekatan: (1) Kontrak pertukaran tidak perlu mempertahankan status harga, yang seharusnya menyebabkan biaya transaksi lebih rendah; (2) Karena laporan oracle diposting secara berantai berdasarkan kebutuhan, oracles dapat menghasilkan pembaruan yang lebih sering (misalnya, setiap menit), sehingga meminimalkan peluang arbitrase dalam menjalankan laporan9; (3) Transaksi dapat divalidasi segera, karena mereka selalu menyertakan feed harga baru. Namun pendekatan ini tidak sempurna. Pertama, solusi membonceng ini mengedepankan tanggung jawab pengguna bursa untuk mengambil laporan oracle terkini dan melampirkannya ke transaksi. Kedua, meskipun membonceng meminimalkan peluang arbitrase, hal ini tidak bisa dilakukan sepenuhnya mencegahnya tanpa mempengaruhi keberlangsungan kontrak on-chain. Memang benar, jika sebuah Laporan oracle valid sampai beberapa blok nomor n, kemudian transaksi dikirimkan ke blok n + 1 akan memerlukan laporan baru yang valid. Karena keterlambatan yang melekat dalam penyebaran laporan dari oracles ke pengguna, laporan baru yang valid untuk blok n + 1 akan memiliki 9Arbitrase hanya bermanfaat jika perbedaan harga aset yang dapat dieksploitasi melebihi perbedaan yang ada biaya yang diperlukan untuk membeli dan menjual aset, misalnya aset yang dikumpulkan oleh penambang dan bursa.untuk dipublikasikan beberapa waktu sebelum blok n + 1 ditambang, katakanlah di blok n −k, dengan demikian membuat urutan k blok di mana terdapat peluang arbitrase berumur pendek. Kami sekarang jelaskan bagaimana FSS mengatasi keterbatasan ini. Memprioritaskan laporan oracle dengan FSS: FSS dapat mengatasi oracle yang berjalan di depan masalah dengan mengembangkan solusi dukungan di atas, tetapi mendorong solusi tambahan pekerjaan menambah transaksi dengan laporan oracle ke Jaringan Oracle Terdesentralisasi. Pada tingkat tinggi, node oracle mengumpulkan transaksi yang ditujukan untuk pertukaran on-chain, menyetujui feed harga real-time, dan memposting feed harga bersama dengan transaksi yang dikumpulkan ke kontrak rantai utama. Secara konseptual, pendekatan ini dapat dianggap sebagai a “pengelompokan transaksi yang ditambah data”, di mana oracle memastikan bahwa umpan harga selalu ditambahkan ke transaksi. Solusi FSS dapat diimplementasikan secara transparan kepada pengguna bursa, dan dengan perubahan minimal pada logika kontrak, seperti yang kami jelaskan secara lebih rinci di Bagian 5.2. Memastikan bahwa laporan oracle baru selalu diprioritaskan dibandingkan transaksi pengguna hanyalah salah satu contohnya kebijakan pemesanan yang dapat diadopsi dan ditegakkan oleh FSS. Kebijakan FSS untuk memastikan ketertiban keadilan dijelaskan secara lebih umum di Bagian 5.3. 5.1.2 Transaksi Pengguna yang Berjalan di Depan Kita sekarang beralih ke front-running dalam aplikasi generik, dimana metode pertahanan di atas tidak berfungsi. Permasalahannya dapat ditangkap secara luas melalui skenario berikut: Musuh melihat beberapa transaksi pengguna tx1 dikirim ke jaringan P2P dan menyuntikkannya transaksi lawannya sendiri tx2, sehingga tx2 diproses sebelum tx1 (misalnya dengan membayar biaya transaksi yang lebih tinggi). Misalnya, front-running seperti ini biasa terjadi di kalangan bot yang mengeksploitasi peluang arbitrase di sistem DeFi [90] dan telah memengaruhi pengguna berbagai aplikasi terdesentralisasi [101]. Menerapkan ketertiban yang adil di antara transaksi diproses pada blockchain mengatasi masalah ini. Lebih mendasar lagi, melihat detail tx1 terkadang bahkan tidak diperlukan dan pengetahuan tentang keberadaannya saja dapat memungkinkan musuh untuk menyerang tx1 melaluinya memiliki tx2 dan menipu pengguna yang tidak bersalah yang membuat tx1. Misalnya, pengguna mungkin diketahui memperdagangkan aset tertentu pada waktu yang teratur. Untuk mencegah serangan tersebut diperlukan mitigasi yang menghindari kebocoran metadata juga [62]. Beberapa solusi untuk masalah ini memang ada, namun hal ini menimbulkan masalah penundaan dan kegunaan. Dari pesanan jaringan hingga pesanan selesai dengan FSS: Peluang untuk menjadi yang terdepan muncul karena sistem yang ada tidak memiliki mekanisme untuk menjamin ketertiban transaksi muncul dalam rantai menghormati urutan peristiwa dan aliran informasi di luar jaringan. Hal ini menunjukkan masalah yang timbul dari kekurangan dalam implementasi aplikasi (misalnya, platform perdagangan) pada blockchain. Idealnya, seseorang akan melakukannya memastikan bahwa transaksi dilakukan pada blockchain dalam urutan yang sama seperti sebelumnya dibuat dan dikirim ke jaringan P2P blockchain. Namun sejak jaringan blockchain
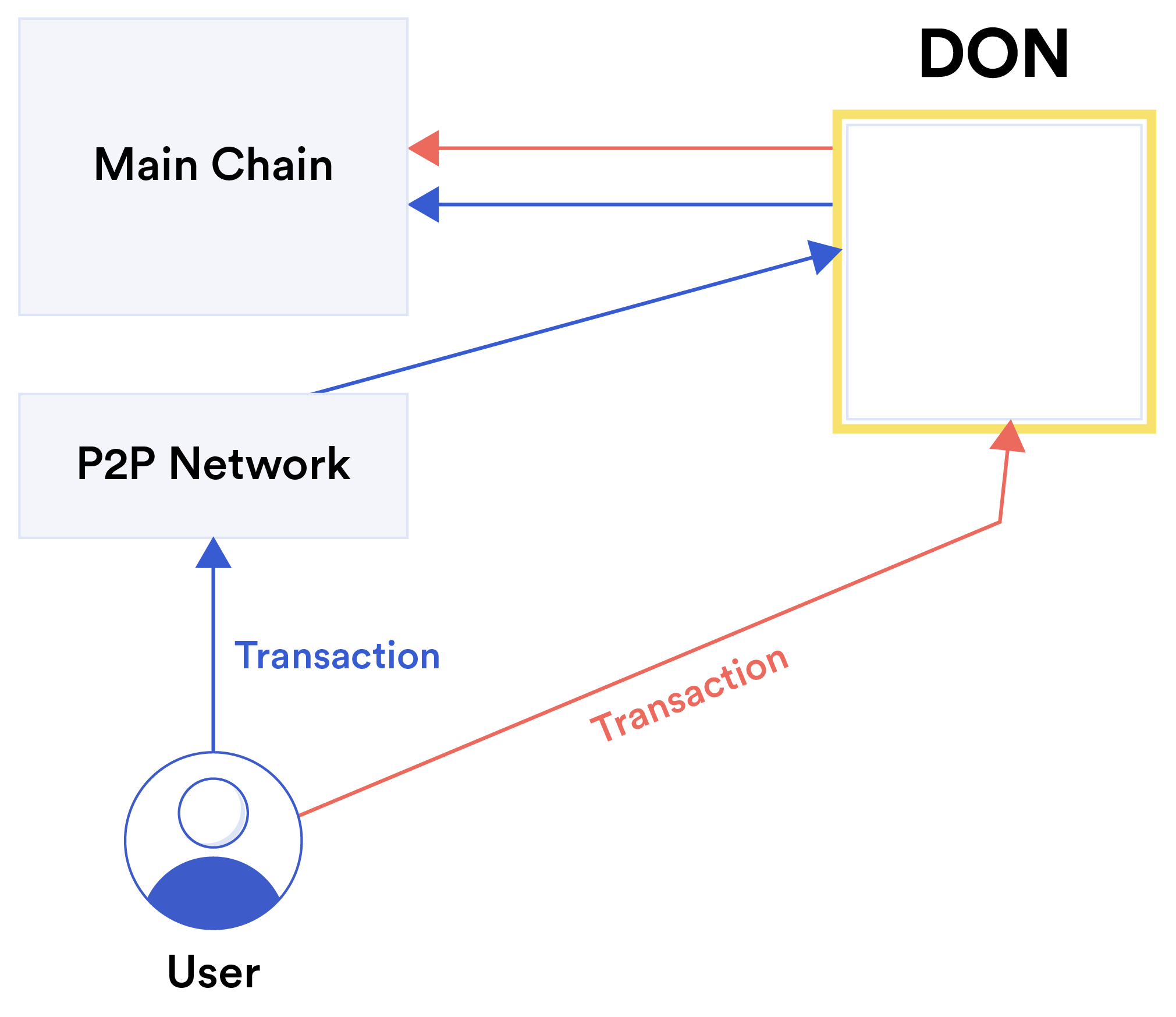
didistribusikan, tidak ada pesanan seperti itu yang dapat ditangkap. Oleh karena itu FSS memperkenalkan mekanisme untuk menjaga terhadap pelanggaran keadilan, yang timbul hanya karena didistribusikan sifat jaringan blockchain. 5.2 Detail FSS Gambar 12: Mempool pesanan adil dengan dua jalur transaksi berbeda: langsung dan berbasis mempool. Gambar 12 menunjukkan skema umum FSS. Untuk memastikan keadilan, DON penyedia FSS harus mengganggu aliran transaksi saat memasuki MAINCHAIN. Penyesuaian pada klien, pada smart contract di MAINCHAIN, atau keduanya mungkin diperlukan. Pada tingkat tinggi, pemrosesan transaksi oleh FSS dapat dipecah menjadi tiga tahapan yang diuraikan sebagai berikut: (1) Pemantauan transaksi; (2) Urutan transaksi; dan (3) Posting transaksi. Bergantung pada metode pemesanan yang digunakan untuk pengurutan transaksi, langkah-langkah protokol tambahan diperlukan, seperti yang dijelaskan di bagian berikutnya. 5.2.1 Pemrosesan Transaksi Pemantauan transaksi: Kami membayangkan dua pendekatan berbeda untuk dipantau oleh FSS transaksi pengguna yang ditujukan untuk smart contract tertentu, langsung dan berbasis mempool: • Langsung: Pendekatan langsung secara konseptual paling sederhana, namun memerlukan perubahan klien pengguna sehingga transaksi dikirim langsung ke Oracle TerdesentralisasiNode jaringan, bukan ke node rantai utama. DON dikumpulkan transaksi pengguna ditujukan ke smart contract SC tertentu dan mengurutkannya berdasarkan pada beberapa kebijakan pemesanan. DON kemudian mengirimkan transaksi pesanan ke smart contract pada rantai utama. Beberapa mekanisme pemesanan juga memerlukan pendekatan langsung karena pengguna yang membuat transaksi harus secara kriptografis lindungi sebelum mengirimnya ke FSS. • Berbasis Mempool: Untuk memfasilitasi integrasi FSS dengan klien lama, DON dapat menggunakan Mempool Services (MS) untuk memantau mempool rantai utama dan mengumpulkannya transaksi. Penularan langsung kemungkinan besar merupakan penerapan pilihan bagi banyak kontrak, dan kami yakin hal ini cukup praktis dalam banyak kasus. Kami membahas secara singkat bagaimana DApps yang ada dapat dimodifikasi secara minimal untuk mendukung transmisi langsung sambil menjaga pengalaman pengguna yang baik. Kami menjelaskan pendekatan menggunakan Ethereum dan MetaMask [6] karena ini adalah pilihan paling populer saat ini, tapi teknik yang disebutkan harus diperluas ke rantai dan dompet lainnya. Ethereum baru-baru ini Proposal Perbaikan, “EIP-3085: Dompet menambahkan Ethereum metode RPC rantai” [100], akan memudahkan penargetan rantai Ethereum khusus (menggunakan ID RANTAI yang berbeda dari yaitu MAINCHAIN untuk mencegah serangan replay) dari MetaMask dan dompet berbasis browser lainnya. Setelah penerapan proposal ini, DApp ingin menggunakan DON hanya akan menambahkan satu panggilan metode ke front-end mereka untuk dapat mengirimkan secara langsung transaksi ke DON mana pun yang menampilkan API yang kompatibel dengan Ethereum. Sementara itu, “EIP-712: Ethereum mengetik data terstruktur hashing dan penandatanganan” [49] memberikan sedikit alternatif yang lebih terlibat tetapi sudah diterapkan secara luas, yang dapat digunakan oleh pengguna DApp MetaMask untuk menandatangani data terstruktur yang menentukan transaksi DON. DApp dapat mengirim ini menandatangani data terstruktur ke DON. Terakhir, kami mencatat bahwa pendekatan hibrid juga dimungkinkan. Misalnya warisan klien dapat terus mengirim transaksi ke mempool rantai utama, tetapi penting transaksi (misalnya, laporan oracle) dikirim ke DON node secara langsung (khususnya, kumpulan node yang menyediakan laporan oracle seperti pembaruan umpan harga dan kumpulan node asalkan FSS mungkin tumpang tindih atau identik). Urutan transaksi: Tujuan utama FSS adalah untuk menjamin bahwa transaksi pengguna diatur sesuai dengan kebijakan yang telah ditentukan sebelumnya. Sifat dari kebijakan ini akan bergantung pada kebutuhan aplikasi dan jenis pemesanan transaksi tidak adil yang dilakukannya bertujuan untuk mencegah. Karena FSS di DON mampu memproses data dan memelihara keadaan lokal, mereka mungkin menerapkan kebijakan pengurutan yang sewenang-wenang berdasarkan informasi yang ada tersedia di oracles. Kebijakan pemesanan tertentu dan implementasinya dibahas selanjutnya di Bagian 5.3.Postingan transaksi: Setelah mengumpulkan dan memesan transaksi pengguna, yang diterima langsung dari pengguna atau dikumpulkan dari mempool, DON mengirimkan transaksi ini ke rantai utama. Dengan demikian, interaksi DON dengan rantai utama tetap ada tunduk pada pemesanan transaksi (yang berpotensi tidak adil) yang diatur oleh penambang rantai utama. Untuk memanfaatkan manfaat pemesanan transaksi yang terdesentralisasi, targetnya cerdas kontrak SC dengan demikian harus dirancang untuk memperlakukan DON sebagai warga negara “kelas satu”. Kami membedakan dua pendekatan: • Kontrak khusus DON: Opsi desain paling sederhana adalah membuat rantai utama cerdas kontrak SC hanya menerima transaksi yang telah diproses oleh DON. Ini memastikan bahwa smart contract memproses transaksi sesuai urutan yang diusulkan oleh DON, namun secara de facto membatasi smart contract untuk beroperasi dalam sistem berbasis komite (yaitu, komite DON sekarang mempunyai kekuasaan yang berkelanjutan untuk menentukan pemesanan dan penyertaan transaksi). • Kontrak kelas ganda: Desain yang disukai dan lebih terperinci memiliki rantai utama yang cerdas kontrak SC menerima transaksi yang berasal dari DON dan dari warisan pengguna,10 tetapi menempatkan “kecepatan” tradisional pada transaksi yang tidak diproses oleh DON. Misalnya, transaksi dari DON dapat diproses segera, sedangkan transaksi lama akan “disangga” oleh smart contract untuk jangka waktu tertentu. Mekanisme standar lainnya untuk mencegah front-running seperti skema pengungkapan komitmen atau VDF [53] juga dapat diterapkan pada warisan transaksi. Hal ini memastikan bahwa transaksi yang dipesan DON benar-benar diproses perintah tersebut disetujui, tanpa memberikan DON wewenang yang tidak diinginkan untuk melakukan sensor transaksi. Karena penerapan pemesanan transaksi oleh FSS mengharuskan transaksi diagregasi secara “off-chain,” solusi ini secara alami dikombinasikan dengan teknik agregasi lain yang bertujuan untuk mengurangi biaya pemrosesan on-chain. Misalnya setelah mengumpulkan dan memesan transaksi, DON dapat mengirimkan transaksi ini ke rantai utama sebagai a satu “transaksi batch” (misalnya, rollup), sehingga mengurangi transaksi agregat biaya. Menegakkan perintah transaksi: Baik dalam desain DON saja atau kelas ganda, rantai utama smart contract SC dan DON harus dirancang bersama untuk menjamin bahwa pemesanan transaksi DON ditegakkan. Di sini juga, kami membayangkan hal yang berbeda pilihan desain: • Nomor urut: DON dapat menambahkan nomor urut ke setiap transaksi, dan mengirimkan transaksi ini ke mempool rantai utama. Yang utama 10Jika pemantauan transaksi DON didasarkan pada mempool, transaksi lama harus dapat dibedakan dari transaksi DON sehingga tidak dikumpulkan oleh DON, misalnya melalui tag khusus melekat dalam transaksi atau dengan menentukan harga gas tertentu, misalnya DON transaksi ada bensin harga di bawah ambang batas tertentu.rantai smart contract SC mengabaikan transaksi yang datang “di luar urutan.” Kami perhatikan bahwa dalam pengaturan ini, penambang rantai utama dapat memutuskan untuk mengabaikan DON pemesanan transaksi, sehingga menyebabkan transaksi gagal. Hal ini dimungkinkan dengan mempertahankan status (mahal) agar SC dapat menegakkan urutan transaksi yang benar analog dengan bagaimana TCP melakukan buffer terhadap paket yang rusak hingga paket hilang diterima. • Transaksi nonces: Untuk banyak blockchains, dan khususnya untuk Ethereum, Pendekatan penomoran urut di atas dapat memanfaatkan nonces transaksi bawaan menjadi menegakkan bahwa rantai utama smart contract SC memproses transaksi secara berurutan. Di sini, node DON mengirimkan transaksi ke rantai utama melalui satu akun rantai utama, dilindungi dengan kunci yang dibagikan di antara node DON. Akun itu transaksi nonce memastikan bahwa transaksi ditambang dan diproses dalam urutan yang benar. • Transaksi gabungan: DON dapat menggabungkan beberapa transaksi dalam rollup (atau dalam bundel yang mirip dengan rollup). Rantai utama smart contract harus ada dirancang untuk menangani transaksi agregat tersebut. • Gabungkan transaksi dengan proksi rantai utama: Di sini, DON juga mengelompokkan transaksi ke dalam satu “meta-transaksi” untuk rantai utama, namun bergantung pada proxy khusus smart contract untuk membongkar transaksi dan meneruskannya ke kontrak target SC. Teknik ini dapat berguna untuk kompatibilitas lama. Metatransaksi bertindak seperti rollup tetapi berbeda karena terdiri dari transaksi yang tidak terkompresi daftar transaksi yang diposting satu kali ke rantai utama. Desain terakhir memiliki keunggulan dalam mendukung transaksi pengguna secara lancar mereka sendiri diproksi melalui kontrak rantai utama sebelum mencapai target DON kontrak SC. Misalnya, pertimbangkan pengguna yang mengirim transaksi ke dompet tertentu kontrak, yang pada gilirannya mengirimkan transaksi internal ke SC. Menugaskan urutan nomor untuk transaksi seperti itu akan rumit, kecuali kontrak dompet penggunanya dirancang khusus untuk meneruskan nomor urut pada setiap transaksi internal SC. Demikian pula, transaksi internal tersebut tidak dapat dengan mudah digabungkan menjadi metatransaksi yang dikirim langsung ke SC. Kami mendiskusikan pertimbangan desain lebih lanjut untuk transaksi proxy seperti di bawah ini. 5.2.2 Atomisitas Transaksi Diskusi kita sejauh ini secara implisit mengasumsikan bahwa transaksi berinteraksi dengan satu transaksi on-chain smart contract (misalnya, pengguna mengirimkan permintaan pembelian ke bursa). Namun, di sistem seperti Ethereum, satu transaksi dapat terdiri dari beberapa transaksi internal, misalnya, satu smart contract yang memanggil fungsi dalam kontrak lain. Di bawah ini, kami menjelaskan dua strategi tingkat tinggi untuk mengurutkan transaksi “multi-kontrak”, sementara menjaga atomitas transaksi (yaitu, urutan tindakan yang ditentukan oleh semua transaksi dieksekusi dalam urutan yang benar, atau tidak dieksekusi sama sekali).Atomisitas yang kuat: Solusi paling sederhana adalah dengan menerapkan FSS, seperti dijelaskan di atas, langsung ke seluruh transaksi “multi-kontrak”. Artinya, pengguna mengirimkan transaksinya ke dalam jaringan dan FSS memantau, mengurutkan, dan memposting transaksi ini ke rantai utama. Pendekatan ini secara teknis sederhana, namun memiliki satu potensi keterbatasan: Jika pengguna transaksi berinteraksi dengan dua kontrak SC1 dan SC2 yang keduanya ingin dimanfaatkan secara adil layanan pengurutan, maka kebijakan pengurutan kedua kontrak ini harus konsisten. Artinya, diberikan dua transaksi berbeda tx1 dan tx2 yang masing-masing berinteraksi baik SC1 maupun SC2, kebijakan SC1 tidak boleh memerintahkan tx1 sebelum tx2 sedangkan kebijakan SC2 mengatur urutan sebaliknya. Untuk sebagian besar skenario yang menjadi perhatian, kami memperkirakan bahwa urutan kebijakan yang diadopsi oleh kontrak yang berbeda akan konsisten. Misalnya, SC1 dan SC2 mungkin ingin transaksi diurutkan berdasarkan perkiraan waktu kedatangannya di mempool, dan SC1 mungkin ingin laporan oracle tertentu selalu dikirimkan terlebih dahulu. Sebagai transaksi laporan oracle terakhir tidak berinteraksi dengan SC2, kebijakannya konsisten. Atomisitas lemah: Secara umum, FSS dapat diterapkan pada tingkat individu transaksi internal. Pertimbangkan transaksi dalam bentuk tx = { ˜txpre, ˜txSC, ˜txpost}, yang terdiri dari beberapa inisial transaksi ˜txpre, yang menghasilkan transaksi internal ˜txSC ke SC, yang pada gilirannya mengeluarkan transaksi internal ˜txpost. Kebijakan pengurutan SC mungkin menentukan caranya transaksi internal ˜txSC harus dipesan sehubungan dengan transaksi lain yang dikirim ke SC, tetapi biarkan urutan pengurutan untuk ˜txpre dan ˜txpost tetap terbuka. Mengingat hakikat pemrosesan transaksi dalam sistem seperti Ethereum, mengembangkan layanan pengurutan yang menargetkan transaksi internal tertentu tidaklah mudah. Dengan kontrak SC yang dirancang khusus, hal ini dapat diwujudkan sebagai berikut: 1. Transaksi tx dikirim ke jaringan dan ditambang (tanpa urutan apa pun dilakukan oleh FSS). ˜txpre awal dijalankan, dan memanggil ˜txSC. 2. SC tidak mengeksekusi ˜txSC dan kembali. 3. FSS memonitor transaksi internal ke SC, mengurutkannya, dan mempostingnya kembali ke SC (yaitu dengan mengirimkan transaksi ˜txSC langsung ke SC). 4. SC memproses transaksi ˜txSC yang diterima dari FSS, dan menerbitkan transaksi internal ˜txpost yang dihasilkan dari ˜txSC. Dengan pendekatan ini, transaksi tidak dieksekusi sepenuhnya secara atomik (yaitu, transaksi asli transaksi tx dipecah menjadi beberapa transaksi on-chain), tetapi urutannya transaksi internal dipertahankan. Solusi ini memerlukan sejumlah kendala desain. Misalnya, 'txpre tidak bisa asumsikan bahwa ˜txSC dan ˜txpost akan dieksekusi. Selain itu, SC harus dirancang sedemikian rupa mengeksekusi transaksi ˜txSC dan ˜txpost atas nama pengguna tertentu, meskipun demikiandikirim oleh FSS. Karena alasan ini, solusi “Strong Atomicity” lebih berbutir kasar di atas mungkin lebih disukai dalam praktiknya. Untuk menghormati ketergantungan yang lebih kompleks, yang melibatkan banyak transaksi dan transaksi internalnya masing-masing, dapat dimuat dalam penjadwal transaksi FSS fungsi rumit yang mirip dengan yang ditemukan pada manajer transaksi relasional manajer basis data. 5.3 Urutan Transaksi yang Adil Di sini kita membahas dua gagasan tentang keadilan dalam pengurutan transaksi dan penerapannya, yang dapat diwujudkan oleh FSS: keadilan ketertiban berdasarkan kebijakan diberlakukan oleh FSS dan pelestarian kausalitas yang aman, yang memerlukan metode kriptografi tambahan di FSS. Keadilan ketertiban: Keadilan ketertiban adalah gagasan keadilan sementara dalam protokol konsensus yang pertama kali diperkenalkan secara formal oleh Kelkar et al. [144]. Kelkar dkk. bertujuan untuk mencapai suatu bentuk kebijakan alami di mana transaksi berada diurutkan berdasarkan waktu pertama kali diterima oleh DON (atau jaringan P2P, dalam kasus FSS berbasis mempool). Namun, dalam sistem desentralisasi, hal ini berbeda node mungkin melihat transaksi tiba dalam urutan yang berbeda. Membangun ketertiban total pada semua transaksi adalah masalah yang diselesaikan oleh protokol konsensus yang mendasarinya RANTAI UTAMA. Kelkar dkk. [144] oleh karena itu perkenalkan gagasan yang lebih lemah dicapai dengan bantuan Jaringan Oracle Terdesentralisasi, yang disebut “keadilan urutan blok.” Ini mengelompokkan transaksi yang diterima DON selama interval waktu ke dalam a "blok" dan memasukkan semua transaksi blok secara bersamaan dan pada posisi yang sama (yaitu, tinggi) menjadi MAINCHAIN. Oleh karena itu, mereka diperintahkan bersama dan harus dapat dieksekusi secara paralel, tanpa menimbulkan konflik di antara mereka. Secara kasar, orderfairness kemudian menyatakan bahwa jika sebagian besar node melihat transaksi τ1 sebelum τ2, maka τ1 akan diurutkan sebelum atau di blok yang sama dengan τ2. Dengan memaksakan yang begitu kasar Dengan perincian pesanan transaksi, peluang terjadinya serangan front-running dan serangan terkait pesanan lainnya akan sangat berkurang. Kelkar dkk. mengusulkan keluarga protokol yang disebut Aequitas [144], yang alamatnya model penerapan yang berbeda, termasuk pengaturan jaringan sinkron, sinkron sebagian, dan asinkron. Protokol Aequitas membebankan overhead komunikasi yang signifikan dibandingkan dengan konsensus dasar BFT dan oleh karena itu tidak ideal untuk penggunaan praktis. Namun kami yakin akan muncul varian praktis dari Aequitas yang dapat digunakan untuk pengurutan transaksi di FSS dan aplikasi lainnya. Beberapa skema terkait telah telah diusulkan yang memiliki formalisme yang lebih sedikit dan sifat yang lebih lemah, misalnya, [36, 151, 236], tetapi kinerja praktisnya lebih baik. Skema ini dapat didukung di FSS juga. Perlu juga dicatat bahwa istilah “keadilan” muncul di tempat lain dalam blockchain sastra dengan arti yang berbeda, yaitu keadilan dalam arti memberikan kesempatan bagipenambang sebanding dengan sumber daya yang mereka berkomitmenkan [106, 181] atau dalam hal validators kesempatan yang sama [153]. Pelestarian kausalitas yang aman: Pendekatan yang paling dikenal luas untuk mencegah pelanggaran frontrunning dan pelanggaran pemesanan lainnya pada platform terdistribusi bergantung pada kriptografi teknik. Fitur umum mereka adalah menyembunyikan data transaksi itu sendiri, menunggu sampai urutan pada lapisan konsensus telah ditetapkan, dan untuk mengungkapkan data transaksi nanti untuk diproses. Ini menjaga urutan sebab akibat di antara transaksi-transaksi yang ada dieksekusi oleh blockchain. Gagasan keamanan dan protokol kriptografi yang relevan telah dikembangkan secara signifikan sebelum munculnya blockchains [71, 190]. Kondisi keamanan “input kausalitas” [190] dan “pelestarian kausalitas yang aman” [71, 97] mensyaratkan secara formal bahwa tidak ada informasi tentang suatu transaksi yang diketahui sebelum posisi transaksi ini dalam tatanan global ditentukan. Musuh tidak boleh dapat menyimpulkan informasi apa pun sampai saat itu, secara kriptografis rasa yang kuat. Seseorang dapat membedakan empat teknik kriptografi untuk mempertahankan kausalitas: • Protokol pengungkapan komitmen [29, 142, 145]: Daripada transaksi diumumkan yang jelas, hanya komitmen kriptografi terhadap transaksi yang disiarkan. Setelah semua transaksi yang dilakukan tetapi tersembunyi telah dipesan (di awal blockchain sistem di MAINCHAIN sendiri, tetapi di sini oleh FSS), pengirim harus membuka komitmen dan mengungkapkan data transaksi dalam interval waktu yang telah ditentukan. Jaringan kemudian memverifikasi bahwa pembukaan tersebut memenuhi komitmen sebelumnya. Itu asal muasal metode ini dimulai sebelum munculnya blockchains. Walaupun sederhana, pendekatan ini mempunyai banyak kelemahan dan tidak mudah diterapkan karena dua alasan. Pertama, karena hanya komitmen yang ada pada tingkat protokol pemesanan, maka semantik transaksi tidak dapat divalidasi selama konsensus. Perjalanan pulang pergi tambahan ke klien diperlukan. Namun, yang lebih parah adalah kemungkinan tidak adanya pembukaan pernah tiba, yang bisa berarti serangan penolakan layanan. Selain itu, itu sulit untuk menentukan apakah pembukaan tersebut valid secara konsisten dan terdistribusi cara karena semua peserta harus sepakat apakah pembukaan sudah tiba waktu. • Protokol pengungkapan komitmen dengan pemulihan tertunda [145]: Satu tantangan dengan Pendekatan commit-reveal adalah bahwa klien dapat melakukan transaksi secara spekulatif dan mengungkapkannya nanti hanya jika transaksi berikutnya menghasilkan keuntungan. SEBUAH Varian terbaru dari pendekatan commit-reveal meningkatkan ketahanan terhadap hal ini jenis perilaku buruk. Secara khusus, protokol TEX [145] mengatasi masalah ini menggunakan pendekatan cerdas di mana transaksi terenkripsi menyertakan kunci dekripsi dapat diperoleh dengan menghitung fungsi penundaan yang dapat diverifikasi (VDF) [53, 221]. Jika klien gagal mendekripsi transaksinya tepat waktu, orang lain dalam sistem akan mendekripsi itu atas namanya dengan memecahkan teka-teki kriptografi yang cukup sulit.• Enkripsi ambang batas [71, 190]: Metode ini mengeksploitasi yang dapat dilakukan oleh DON operasi kriptografi ambang batas. Asumsikan FSS memelihara enkripsi publik kunci pkO dan oracles berbagi kunci pribadi yang sesuai di antara mereka sendiri. Klien kemudian mengenkripsi transaksi di bawah pkO dan mengirimkannya ke FSS. perintah FSS transaksi di DON, lalu mendekripsinya, dan terakhir memasukkannya ke dalam RANTAI UTAMA dalam urutan tetap. Oleh karena itu enkripsi memastikan bahwa pemesanan dilakukan bukan berdasarkan isi transaksi, tetapi data itu sendiri tersedia kapan dibutuhkan. Metode ini awalnya diusulkan oleh Reiter dan Birman [190] dan kemudian disempurnakan oleh Cachin et al. [71], yang diintegrasikan dengan konsensus yang diizinkan protokol. Penelitian yang lebih baru telah mengeksplorasi penggunaan kriptografi ambang batas sebagai mekanisme tingkat konsensus untuk pesan umum [33, 97] dan untuk komputasi umum dengan data bersama [41]. Dibandingkan dengan protokol commit-reveal, enkripsi ambang batas mencegah serangan penolakan layanan sederhana (walaupun diperlukan kehati-hatian mengingat biaya komputasi dekripsi). Ini memungkinkan DON berjalan secara mandiri, dengan kecepatannya sendiri dan tanpa kecepatan menunggu tindakan klien selanjutnya. Transaksi dapat divalidasi segera setelah didekripsi. Selain itu, klien mengenkripsi semua transaksi dengan satu kunci untuk DON dan pola komunikasinya tetap sama seperti yang lain transaksi. Mengelola kunci ambang batas dengan aman dan dengan perubahan node Namun, O mungkin menimbulkan kesulitan tambahan. • Melakukan pembagian rahasia [97]: Daripada mengenkripsi data transaksi di bawah kunci yang dipegang oleh DON, klien juga dapat membagikannya secara rahasia untuk node di O. Menggunakan skema pembagian rahasia yang hibrid dan aman secara komputasi, transaksinya dienkripsi terlebih dahulu menggunakan sandi simetris dengan kunci acak. Hanya kunci simetris terkait yang dibagikan dan teks sandi dikirimkan ke DON. Klien harus mengirimkan satu key share ke setiap node di O menggunakan pesan terenkripsi secara terpisah. Langkah-langkah protokol lainnya sama dengan ambang batas enkripsi, kecuali data transaksi didekripsi dengan simetris algoritma setelah merekonstruksi kunci per transaksi dari bagiannya. Metode ini tidak memerlukan pengaturan atau pengelolaan sistem kriptografi kunci publik terkait dengan DON. Namun, klien harus mengetahui node di dalamnya HAI dan berkomunikasi dalam konteks yang aman dengan masing-masing dari mereka, di mana tempatnya beban tambahan pada klien. Meskipun metode kriptografi menawarkan perlindungan lengkap terhadap informasi bocor dari transaksi yang dikirimkan ke jaringan, mereka tidak menyembunyikan metadata. Untuk misalnya, alamat IP atau alamat Ethereum pengirim masih dapat digunakan musuh untuk melakukan serangan depan dan serangan lainnya. Berbagai peningkatan privasi teknik yang diterapkan pada lapisan jaringan, misalnya, [52, 95, 107], atau lapisan transaksi, misalnya, [13, 65], akan diperlukan untuk mencapai tujuan ini. Dampak dari suatu karya tertentu metadata, yaitu ke kontrak mana suatu transaksi dikirimkan, dapat (sebagian) disembunyikanmelalui multiplexing banyak kontrak pada DON yang sama. Penyembunyian kriptografi transaksi itu sendiri juga tidak mencegah prioritas transaksi yang dirusak DON node berkolusi dengan pengirim transaksi. Kausalitas yang aman sebagaimana dijamin oleh protokol kriptografi melengkapi jaminan ketertiban keadilan untuk kebijakan apa pun, dan kami bermaksud untuk mengeksplorasi kombinasi keduanya. metode, jika hal ini memungkinkan. Jika musuh tidak dapat memperoleh keuntungan yang signifikan mengamati metadata, protokol pelestarian kausalitas yang aman dapat digunakan bersamaan pendekatan pemesanan yang naif juga. Misalnya, node oracle dapat menulis transaksi ke L segera setelah mereka menerimanya, tanpa duplikasi. Transaksi kemudian akan terjadi diurutkan menurut penampilannya di L dan kemudian didekripsi. Kami juga berencana untuk mempertimbangkan penggunaan TEE sebagai cara untuk membantu menegakkan ketertiban yang adil; untuk Misalnya, Tesseract [44] mungkin dipandang mencapai bentuk keteraturan kausal, tapi satu diperkuat dengan kemampuan TEE dalam memproses transaksi dalam bentuk eksplisit sementara menjaga kerahasiaan mereka. 5.4 Pertimbangan Lapisan Jaringan Sejauh ini, uraian kami mengenai SJK terutama terfokus pada masalah penegakan hukum urutan transaksi yang diselesaikan cocok dengan urutan yang diamati dalam jaringan. Selanjutnya, kami mempertimbangkan masalah keadilan yang mungkin timbul pada lapisan jaringan itu sendiri. Pedagang frekuensi tinggi di pasar elektronik konvensional berinvestasi dalam jumlah besar sumber daya untuk mendapatkan kecepatan jaringan superior [64], dan pedagang di bursa mata uang kripto menunjukkan perilaku serupa [90]. Kecepatan jaringan memberikan keuntungan dalam hal keduanya mengamati transaksi pihak lain dan dalam menyampaikan transaksi pesaing. Salah satu pengobatan yang diterapkan dalam praktik dan dipopulerkan dalam buku Flash Boys [155] adalah "speed bump" pertama kali diperkenalkan di bursa IEX [128] dan kemudian di bursa lainnya pertukaran [179] (dengan hasil beragam [19]). Mekanisme ini memberlakukan penundaan (350 mikrodetik di IEX) pada akses ke pasar, dengan tujuan menetralisir keuntungan dalam kecepatan. Bukti empiris, mis. [128], mendukung keampuhannya dalam menurunkan perdagangan tertentu biaya untuk investor biasa. FSS dapat digunakan secara sederhana untuk mengimplementasikan asimetris speed bump—yang menunda transaksi masuk. Budish, Cramton, dan Shim [64] berpendapat bahwa eksploitasi keunggulan dalam kecepatan tidak dapat dihindari dalam pasar waktu berkelanjutan, dan mendukung perbaikan struktural dalam pasar waktu berkelanjutan bentuk pasar berbasis lelang batch. Namun pendekatan ini belum diterapkan secara luas di platform perdagangan yang ada. Sistem perdagangan konvensional bersifat terpusat, biasanya menerima transaksi melalui satu koneksi jaringan. Sebaliknya, dalam sistem desentralisasi, hal ini dimungkinkan mengamati penyebaran transaksi dari berbagai sudut pandang. Akibatnya, adalah mungkin untuk mengamati perilaku seperti banjir jaringan di jaringan P2P. Kami bermaksud untuk mengeksplorasi pendekatan lapisan jaringan terhadap FSS yang membantu pengembang menentukan kebijakan melarang perilaku jaringan yang tidak diinginkan tersebut.5.5 Kebijakan Kewajaran Tingkat Entitas Keadilan ketertiban dan kausalitas yang aman bertujuan untuk menegakkan ketertiban atas transaksi itu menghormati waktu ketika mereka dibuat dan pertama kali dikirimkan ke jaringan. Keterbatasan dari gagasan keadilan ini adalah bahwa hal itu tidak mencegah serangan yang dilakukan oleh musuh mendapatkan keuntungan dengan membanjiri sistem dengan banyak transaksi, sebuah strategi yang diamati di alam liar sebagai cara untuk melakukan sniping transaksi yang efektif dalam token penjualan [159] dan untuk menciptakan kemacetan yang mengakibatkan likuidasi posisi utang yang dijaminkan (CDP) [48]. Dengan kata lain, keadilan ketertiban menegakkan keadilan dalam kaitannya dengan transaksi, bukan pemain. Seperti yang ditunjukkan dalam sistem CanDID [160], dimungkinkan untuk menggunakan alat oracle seperti DECO atau Town Crier bersama dengan komite node (seperti DON) untuk mencapai berbagai bentuk perlawanan Sybil sekaligus melindungi privasi. Pengguna dapat mendaftarkan identitas dan memberikan bukti keunikannya tanpa mengungkapkan identitas dirinya. Kredensial yang tahan sybil menawarkan pendekatan yang mungkin untuk memperkaya pemesanan transaksi kebijakan dengan cara yang akan membatasi peluang serangan banjir. Misalnya, a token penjualan mungkin hanya mengizinkan satu transaksi per pengguna terdaftar, tempat pendaftaran memerlukan bukti keunikan tanda pengenal nasional, seperti Nomor Jaminan Sosial. Pendekatan seperti ini tidaklah mudah, namun bisa menjadi kebijakan yang berguna untuk memitigasi serangan banjir transaksi.
公平测序服务
我们期望 DONs 将提供一项利用其网络、计算和存储功能的重要服务,称为公平排序服务 (FSS)。 尽管 FSS 可能被简单地视为在 DON 框架内实现的应用程序,但我们强调它是一项我们相信在各个领域都有很高需求的服务。 blockchains,我们希望 Chainlink 网络积极支持。 当在公共 blockchain 网络上执行时,当今的许多 DeFi 应用程序 揭示可以被用户利用以谋取自身利益的信息,类似于 现有的内幕泄密和操纵机会普遍存在 市场 [64, 155]。相反,FSS 为公平的 DeFi 生态系统铺平了道路。 FSS 帮助开发人员构建免受市场操纵的DeFi合约 因信息泄露而造成的。鉴于我们在下面强调的问题,FSS 是 对于第 2 层服务特别有吸引力,并且适合此类服务的框架 我们将在第 6 节中讨论。 挑战: 在现有的无需许可的系统中,交易是完全有序的 由矿工自行决定。在许可网络中,validator 节点可能会施加 相同的力量。这是一种在很大程度上未被认识到的短暂集中化形式。 否则分散的系统。矿工可以(暂时)审查其交易 自己的利益[171]或重新排序以最大化自己的收益,这一概念称为可开采价值(MEV)[90]。 MEV 这个术语有一点欺骗性:它并不指代 只考虑矿工可以捕获的价值:一些MEV可以被普通用户捕获。 然而,由于矿工比普通用户拥有更多的权力,MEV 代表了任何实体通过对抗性重新排序可以获得的价值上限 和补充交易插入。即使矿工简单地下令交易 基于费用(gas),无需操纵,用户自己可以操纵gas价格 使他们的交易比那些不太复杂的交易更有优势。 戴安等人。 [90] 记录并量化机器人(而非矿工)采取的方式 利用气体动力学的方式损害当今 DeFi 系统的用户以及如何 MEV 甚至威胁到 blockchain 中底层共识层的稳定性。 交易订单操纵的其他例子也经常出现,例如[50, 154]。新的事务处理方法(例如 rollups)是一种非常有前途的方法 解决高吞吐量 blockchains 的扩展问题。然而,他们并没有解决 MEV的问题。相反,他们将其转移到生成 rollup 的实体。那 实体,无论是 smart contract 的操作员还是提供 (zk-)rollup 的用户 有效性证明,有权订购和插入交易。换句话说,rollups 将 MEV 替换为 REV:汇总可提取值。 MEV 影响即将提交到内存池的交易 但尚未在链上承诺。有关此类交易的信息广泛 在网络中可用。矿工、validators和普通网络参与者可以 因此,利用这些知识并创建相关交易。此外,矿工和 validators 可能会影响他们提交的交易的顺序 并利用这一点为自己谋利。 领导者对共识交易排序施加不当影响的问题 自 20 世纪 90 年代以来,协议在文献中就已为人所知 [71, 190],但还没有令人满意的 到目前为止,解决方案已在实践中实现[97]。 主要原因是所提出的解决方案(至少直到最近)无法轻易地与公众整合 blockchains,因为它们依赖于交易内容在之后仍然保密 他们的顺序已经确定。 公平测序服务 (FSS) 概述: DONs 将提供去中心化交易排序的工具,并根据依赖项指定的策略来实施它 合同创建者,理想情况下是公平的,而不是让那些希望这样做的参与者受益 操纵交易顺序。这些工具共同构成了 FSS。 FSS 包括三个组成部分。首先是交易监控。在FSS中, O 中的 oracle 节点都监视 MAINCHAIN 的内存池并(如果需要)允许 通过专门的渠道在链下提交交易。二是交易顺序。依赖合约的 O 订单交易中的节点 根据为该合同定义的策略。第三是交易记录。 交易排序后,O中的节点共同将交易发送到 主链。 FSS 的潜在好处包括: • 订单公平性:FSS 包含帮助开发人员确保交易的工具 对特定合同的输入以不会产生不公平的方式排序 对于资源丰富和/或技术精湛的用户来说是有优势的。订购政策 可以为此目的指定网络。 • 减少或消除信息泄漏:通过确保网络参与者无法利用有关即将进行的交易的知识,FSS 可以减少或消除信息泄漏。 消除基于现有信息的抢先交易等攻击 提交交易之前的网络。防止利用此类 泄漏确保依赖于原始未决的对抗性交易 在原始交易提交之前,交易无法进入账本。• 降低交易成本:消除玩家对提交速度的要求 他们的交易为smart contract,FSS可以大大降低交易处理的成本。 • 优先排序:FSS 可以自动给予关键事务特殊优先级 订购。例如,为了防止针对 oracle 的抢先交易攻击 报告,例如 [79],FSS 可以将 oracle 报告插入交易流中 追溯性地。 FSS 在 DON 中的首要目标是帮助 DeFi 创作者实现公平 金融系统,即不利于特定用户(或矿工)的系统 基于速度、内部知识或执行技术的能力优于其他人 操纵。虽然公平的明确、普遍的概念是难以捉摸的,但完美的公平在 任何合理的感觉都是无法实现的,FSS旨在为开发者提供强大的 一套工具,以便他们能够执行有助于实现 DeFi 设计目标的策略。 我们注意到,虽然 FSS 的主要目标是充当公平排序服务 DON 的目标主链,某些与 FSS 相同的公平性需求 保证也适用于在其中运行的(去中心化)协议 DON 派对。因此,FSS 可以更广泛地视为由子集提供的服务 DON 节点不仅可以对主链用户发送的交易进行公平排序 还包括其他 DON 节点之间共享的事务(即消息)。在本节中, 我们将主要关注对主链交易进行排序的目标。 章节组织:在第 5.1 节中,我们描述了推动 FSS 设计的两个高级应用程序:防止 oracle 报告的抢先交易和防止 用户交易的抢先交易。然后我们提供有关 FSS 设计的更多细节 在第 5.2 节中。第 5.3 节描述了公平排序保证和手段的示例 来实现它们。最后,第 5.4 节和第 5.5 节讨论了网络级威胁 分别针对网络洪水和女巫攻击的此类政策和解决方法 攻击。 5.1 抢先交易问题 为了解释 FSS 的目标和设计,我们描述了两种常见的抢先交易形式 攻击和现有解决方案的局限性。 抢先交易是一个类的例子 交易排序攻击:有许多相关的攻击,例如我们没有涵盖的反向运行和夹心(前端运行加反向运行)[237] 在这里,但 FSS 也可以帮助解决这个问题。 5.1.1 Oracle抢先交易 oracles 的传统角色是向 blockchain 应用程序提供链下数据 成为抢先交易攻击的天然目标。考虑使用 oracle 提供各种价格源的常见设计模式 到链上交易所:oracle 定期(例如每小时)收集价格数据 不同的资产并将它们发送到交换合约。这些价格数据交易 呈现明显的套利机会:例如,如果最新的 oracle 报告列出 某些资产的价格要高得多,对手可能会抢先发送 oracle 报告给 购买资产并在 oracle 的报告处理完毕后立即转售。 减速带和追溯定价: oracle 抢先交易问题的自然解决方案是给予 oracle 报告高于其他交易的特殊优先级。对于 例如,可以以高额费用发送 oracle 报告,以鼓励矿工处理 首先是他们。但如果套利机会很高,这并不能阻止抢先交易, 也无法阻止矿工自己套利。 因此,一些交易所采取了更重量级的“减速带”,例如在处理之前将用户交易排队等待多个区块 或在新的 oracle 报告到达时追溯调整价格。这些解决方案的缺点是它们增加了交换实现的复杂性, 增加存储需求,从而增加交易成本,并破坏用户体验,因为资产交换只有在相当长的一段时间后才会得到确认。 捎带: 在继续讨论 FSS 之前,我们先讨论搭载,这是一种非常简单且 oracle 抢先交易问题的优雅解决方案。不适用于地址 然而,在其他情况下却是抢先交易。 简而言之,不是定期向链上合约发送报告,而是 oracles 发布用户在购买或出售时附加到其交易中的签名报告 链上资产。然后交易所只需检查报告是否有效且最新 (例如,oracle 可以签署报告有效的一系列区块),并提取 从中获取相关价格。 与上述“减速带”相比,这种简单的方法具有许多优点 方法:(1)交易合约不需要保存喂价状态,这应该 导致交易成本降低; (2) 由于 oracle 报告是根据需要发布到链上的,因此 oracle 可以生成更频繁的更新(例如每分钟),从而 最大限度地减少抢先报告带来的套利机会9; (3)交易可以 立即得到验证,因为它们始终包含新鲜的价格信息。 然而,这种方法并不完美。首先,这个搭载解决方案将 交易所用户有责任获取最新的 oracle 报告并将其附加到他们的 交易。其次,虽然捎带交易最大限度地减少了套利机会,但它不能 在不影响链上合约活跃性的情况下完全防止它们。确实,如果一个 oracle 报告在某个区块号 n 之前有效,然后将交易提交到区块 n + 1 将需要新的有效报告。由于传播的固有延迟 从 oracles 向用户报告,对块 n + 1 有效的新报告将具有 9只有当资产价格的可利用差异超过无关的资产价格差异时,套利才有价值。 买卖资产所需的费用,例如矿工和交易所收取的费用。在区块 n + 1 被开采之前的某个时期(例如在区块 n −k 处)公布,从而 创建一个包含 k 个区块的序列,其中存在短暂的套利机会。我们 现在描述 FSS 如何克服这些限制。 通过 FSS 对 oracle 报告进行优先级排序: FSS 可以解决 oracle 抢先交易问题 通过构建上述捎带解决方案来解决问题,但推动额外的 使用 oracle 向去中心化预言机网络报告增强交易的工作。 在较高层面上,oracle 节点收集用于链上交换的交易, 就实时价格反馈达成一致,并将价格反馈连同收集的交易一起发布到主链合约中。从概念上讲,人们可以将这种方法视为一种 “数据增强事务批处理”,其中 oracle 确保最新的 喂价总是添加到交易中。 FSS 解决方案可以对交易所用户透明地实施,并且 正如我们在第 5.2 节中更详细描述的那样,对合约逻辑的更改最小。确保 新的 oracle 报告始终优先于用户交易只是一个例子 FSS 可以采用和执行的订购政策。社会保障基金秩序保障政策 第 5.3 节更概括地描述了公平性。 5.1.2 抢先交易的用户交易 我们现在转向通用应用程序中的抢先交易,其中上述防御方法 不起作用。可以通过以下场景概括地捕获该问题: 对手看到一些用户交易 tx1 发送到 P2P 网络并注入 它自己的对抗性交易 tx2,以便 tx2 在 tx1 之前被处理(例如,通过支付 更高的交易费用)。例如,这种抢先交易在 利用 DeFi 系统 [90] 中的套利机会的机器人,并影响了 各种去中心化应用程序[101]。建立公平的交易秩序 在 blockchain 上处理可以解决此问题。 更根本的是,有时甚至没有必要查看 tx1 的详细信息,并且 仅仅知道 tx1 的存在就可能让对手通过其抢先交易 tx1 拥有 tx2 并欺骗创建 tx1 的无辜用户。例如,用户可能 众所周知会定期交易特定资产。防止此类攻击需要 还可以避免元数据泄漏的缓解措施[62]。这个问题的一些解决方案 存在,但它们会带来延迟和可用性问题。 通过 FSS 从网络订单到最终订单: 抢先交易的机会 出现的原因是现有系统没有机制来确保执行的顺序 链上出现的交易尊重事件顺序和信息流 网络之外。这代表了由于在 blockchain 上实施应用程序(例如交易平台)的缺陷而产生的问题。理想情况下,人们会 确保事务按照原来的顺序在 blockchain 上提交 创建并发送到 blockchain 的 P2P 网络。但自从 blockchain 网络
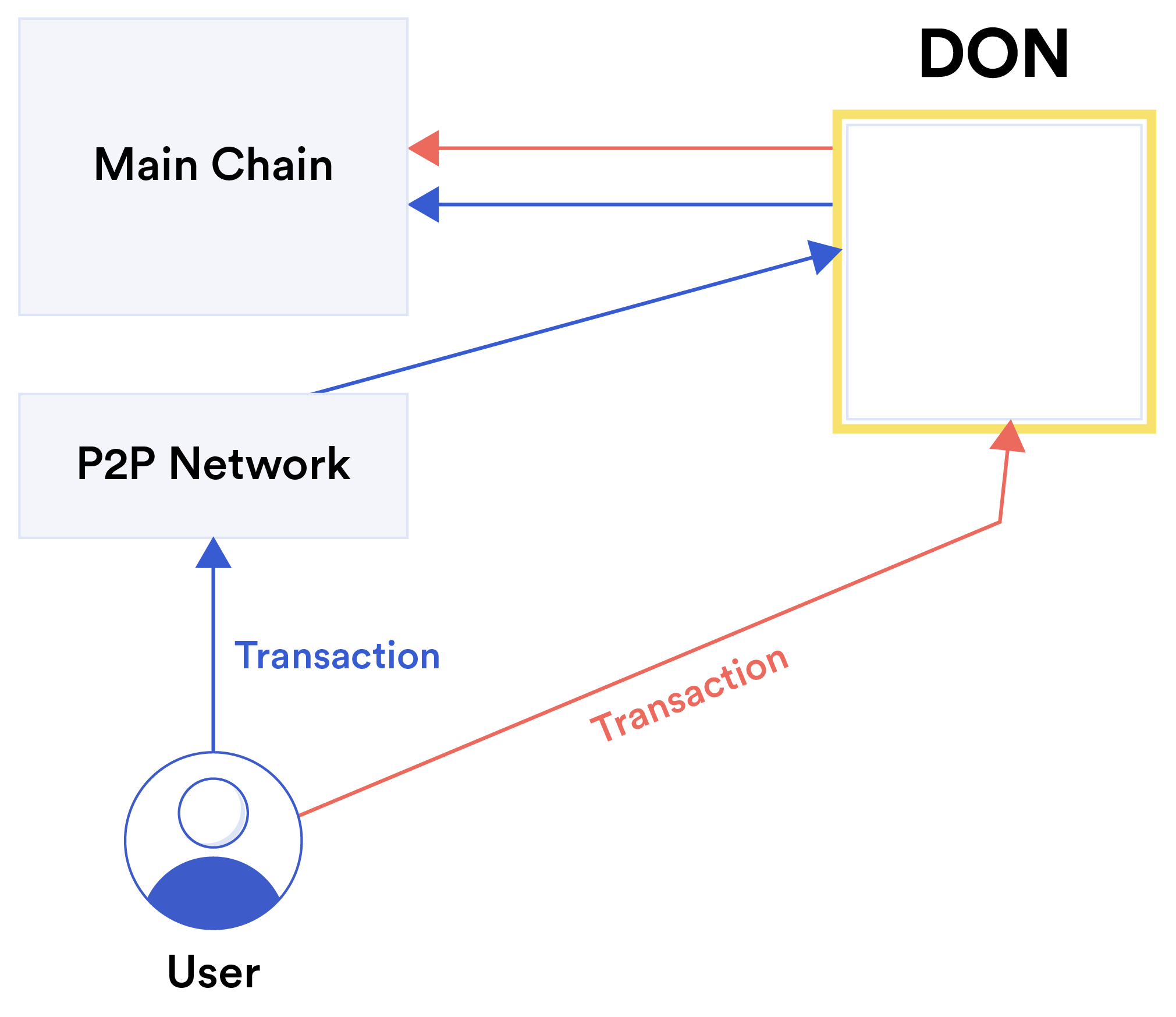
是分布式的,无法捕获这样的订单。 FSS因此引入了机制 防止违反公平性,而这种违反公平性只是因为分布式 blockchain 网络的性质。 5.2 社会保障计划详情 图 12: 具有两种不同交易路径的订单公平内存池: 直接和 基于内存池。 图 12 显示了 FSS 的总体示意图。为了确保公平,提供 FSS 的 DON 必须干扰进入主链的交易流程。 可能需要对客户端、主链上的 smart contracts 或两者进行调整。在较高的层面上,FSS 的交易处理可以分解为三个部分 阶段,描述如下: (1) 交易监控; (2) 交易排序;和 (3) 交易过帐。根据用于事务排序的排序方法,需要额外的协议步骤,如下一节所述。 5.2.1 交易处理 交易监控: 我们设想 FSS 监控采用两种不同的方法 发往特定 smart contract 的用户交易,直接且基于内存池: • 直接:直接方法在概念上是最简单的,但需要进行更改 用户客户端,以便交易直接发送到去中心化预言机网络节点,而不是主链的节点。 DON 收集 用户交易发往特定的 smart contract SC,并根据 关于某些订购政策。然后 DON 将有序交易发送到 主链上的smart contract。一些排序机制还需要直接方法,因为创建交易的用户必须以加密方式 在将其发送到 FSS 之前对其进行保护。 • 基于内存池:为了促进 FSS 与旧客户端的集成,DON 可以使用Mempool Services(MS)来监控主链的mempool并收集 交易。 直接传输可能是许多合同的首选实施方式, 我们相信它在许多情况下应该相当实用。 我们简要讨论如何对现有的 DApp 进行最小程度的修改以支持 直接传输,同时保持良好的用户体验。我们描述方法 使用 Ethereum 和 MetaMask [6] 因为这些是当今最流行的选择,但是 上述技术应该扩展到其他链和钱包。最近的 Ethereum 改进提案,“EIP-3085:钱包添加Ethereum链RPC方法”[100], 将可以轻松定位自定义 Ethereum 链(使用与 MAINCHAIN 的(以防止来自 MetaMask 和其他基于浏览器的钱包的重放攻击)。实施此提案后,一个 DApp 寻求使用 DON 只需向其前端添加一个方法调用即可直接传输 交易到任何暴露 Ethereum 兼容 API 的 DON 。与此同时, “EIP-712:Ethereum 类型化结构化数据 hash 处理和签名” [49] 提供了一个稍微 涉及更多但已经广泛部署的替代方案,DApp 用户可以使用 MetaMask 用于签署指定 DON 交易的结构化数据。 DApp可以发送 此签名的结构化数据到 DON。 最后,我们注意到混合方法也是可能的。 例如,遗产 客户可以继续将交易发送到主链的内存池中,但至关重要 交易(例如 oracle 报告)直接发送到 DON 节点(特别是 提供 oracle 报告(例如喂价更新)的节点集和节点集 提供的 FSS 可能重叠或相同)。 交易排序: FSS 的主要目的是保证用户交易按照预先定义的策略进行排序。这项政策的性质将 取决于应用程序的需求以及它所处理的不公平交易订单的类型 旨在预防。 由于 DON 上的 FSS 能够处理数据并维护本地状态, 他们可能会根据所提供的信息强加任意排序策略 可在 oracles 处购买。 特定的排序策略及其实现将在随后的 5.3 节中讨论。交易过账: 在收集并排序用户交易(直接从用户接收或从内存池收集)后,DON 将这些交易发送到主链。因此,DON 与主链的交互仍然存在 受主链矿工管辖的(可能不公平的)交易排序。为了利用去中心化交易排序的好处,目标智能 因此,合同 SC 的设计必须将 DON 视为“一等”公民。我们 区分两种方法: • DON-only 合约:最简单的设计选项是让主链变得智能 合约SC仅接受已由DON处理的交易。这个 确保 smart contract 按照建议的顺序处理交易 DON,但事实上限制 smart contract 在基于委员会的系统中运行(即 DON 委员会现在拥有持续的权力来确定 交易的排序和包含)。 • 双级合约:首选、更细粒度的设计,主链智能 合约 SC 接受源自 DON 和遗留系统的交易 用户,10 但对 DON 未处理的交易设置了传统的“减速带”。例如,可以处理来自 DON 的交易 立即,而遗留事务则由 smart contract “缓冲” 一段固定的时间。其他防止抢先交易的标准机制 例如提交-显示方案或 VDF [53] 也可以应用于遗留 交易。这确保了 DON 有序的交易确实得到处理 同意该命令,但没有赋予 DON 不必要的审查权力 交易。 由于 FSS 强加的交易排序要求交易在“链外”聚合,因此该解决方案自然地与其他旨在降低链上处理成本的聚合技术相结合。例如,收集后 对交易进行排序后,DON 可以将这些交易作为 单个“批量交易”(例如 rollup),从而减少总交易 费。 执行交易指令: 无论是仅 DON 还是双级设计, 主链smart contract SC和DON必须共同设计,以保证DON的交易顺序得到维护。在这里,我们也设想了不同的 设计选项: • 序列号:DON 可以为每笔交易附加一个序列号,并将这些交易发送到主链的内存池中。 主要 10如果 DON 的交易监控基于内存池,则遗留交易必须与 DON 交易区分开来,以便它们不会被 DON 收集,例如通过特殊标签 嵌入交易中或通过指定特定的 Gas 价格,例如DON 交易有gas 价格低于一定阈值。链 smart contract SC 忽略“无序”到达的交易。我们 请注意,在这种设置中,主链矿工可以决定忽略 DON 的 交易排序,从而导致交易失败。通过保持 SC 的(昂贵的)状态来强制执行正确的交易排序是可能的,某种程度上 类似于 TCP 如何缓冲无序数据包直到丢失的数据包被删除 收到。 • 事务nonces:对于许多blockchain,特别是Ethereum, 上述序列编号方法可以利用内置事务 nonces 来 强制主链smart contract SC按顺序处理交易。 在这里,DON 节点通过单个主链帐户将交易发送到主链,并受到 DON 节点之间共享的密钥的保护。该帐户的 交易 nonce 确保交易以正确的顺序进行挖掘和处理。 • 聚合交易:DON 可以聚合rollup 中的多个交易。 (或类似于 rollup 的捆绑包)。主链 smart contract 需要 旨在处理此类聚合交易。 • 使用主链代理聚合交易:这里,DON 类似地将交易捆绑到主链的一个“元交易”中,但依赖于 自定义代理 smart contract 来解压交易并将其转发到 目标合同 SC。该技术对于遗留兼容性很有用。元交易的行为类似于 rollup,但不同之处在于它们由未压缩的 一次发布到主链的交易列表。 最后一种设计的优点是无缝支持用户交易 在达到 DON 的目标之前,它们本身通过主链合约进行代理 合同 SC。例如,考虑将交易发送到某个钱包的用户 合约,该合约又向 SC 发送内部交易。分配序列 此类交易的编号会很棘手,除非用户的钱包合约是 专门设计用于将每笔内部交易的序列号转发至 SC。 同样,此类内部交易也无法轻松聚合成直接发送到 SC 的元交易。我们讨论进一步的设计考虑 以下此类代理交易。 5.2.2 事务原子性 到目前为止,我们的讨论隐含地假设交易与单个交易交互 链上 smart contract (例如,用户向交易所发送购买请求)。然而,在 在 Ethereum 等系统中,单个交易可以由多个内部交易组成,例如,一个 smart contract 调用另一个合约中的函数。下面,我们 描述了两种对“多合约”交易进行排序的高级策略,同时 保留事务的原子性(即,由 交易全部按照正确的顺序执行,或者根本不执行)。强原子性: 最简单的解决方案是将 FSS 直接应用于整个“多合约”交易,如上所述。也就是说,用户发送他们的交易 进入网络,FSS 监控、排序并将这些交易发布到 主链。 这种方法在技术上很简单,但有一个潜在的限制:如果用户 交易与两个合约 SC1 和 SC2 交互,两者都希望公平杠杆 排序服务,那么这两个合约的排序策略必须一致。也就是说,给定两个不同的交易 tx1 和 tx2,每个交易都与之交互 SC1 和 SC2 都不能出现 SC1 的策略先排序 tx1 后排序 tx2 而 SC2 的政策规定了相反的顺序。 对于绝大多数感兴趣的场景,我们预计不同合约采用的排序策略将是一致的。例如,SC1 和 SC2 可能希望交易按照其到达内存池的大概时间进行排序, SC1 可能还希望始终首先交付某些 oracle 报告。作为 后者oracle报告交易不与SC2交互,政策一致。 弱原子性: 就其全面的普遍性而言,FSS 可以应用于个人层面 内部交易。 考虑 tx = { txpre, txSC, txpost} 形式的交易,由一些初始的 交易〜txpre,这会导致内部交易〜txSC到SC,这反过来 发出内部交易〜txpost。 SC 的排序策略可能决定如何 内部交易 ~txSC 必须相对于发送的其他交易进行排序 到 SC,但保留 txpre 和 txpost 的排序顺序。 鉴于 Ethereum 等系统中事务处理的本质,开发针对特定内部事务的排序服务并不简单。通过专门设计的合约 SC,这可以通过以下方式实现: 1. 交易tx被发送到网络并被挖掘(没有任何排序) 由 FSS 执行)。执行初始的 txpre,并调用 txSC。 2. SC不执行~txSC并返回。 3. FSS 监控 SC 的内部事务,对它们进行排序,然后将它们发回 到 SC(即,通过将交易 ~txSC 直接发送到 SC)。 4. SC 处理从 FSS 接收到的交易 txSC,并发出由 txSC 产生的内部交易 txpost。 使用这种方法,事务不会完全原子地执行(即原始的 交易 tx 被分解为多个链上交易),但是 内部交易被保留。 该解决方案存在许多设计限制。例如,~txpre 不能 假设~txSC 和~txpost 将被执行。此外,SC 的设计应使得 代表某个用户执行交易 〜txSC 和 〜txpost,即使它们是由 FSS 发送。由于这些原因,更粗粒度的“强原子性”解决方案 以上在实践中可能是更可取的。 为了尊重更复杂的依赖关系,涉及多个事务和 它们各自的内部事务,FSS的事务调度程序可能包含 类似于关系型事务管理器中的复杂功能 数据库管理器。 5.3 公平交易排序 这里我们讨论交易排序公平性的两个概念以及相应的实现,这可以通过 FSS 来实现: 基于策略的顺序公平性 FSS 和安全因果关系保存强加的,这需要在 FSS 中使用额外的加密方法。 订单公平性: 顺序公平是共识协议中时间公平的概念 这首先是由 Kelkar 等人正式提出的。 [144]。 凯尔卡等人。旨在实现一种自然政策形式,其中交易是 根据 DON (或 P2P 网络, 对于基于内存池的 FSS)。然而,在去中心化系统中, 节点可能会看到事务以不同的顺序到达。 建立总订单 所有交易的问题正是底层共识协议所解决的问题 主链。 凯尔卡等人。 [144] 因此引入一个较弱的概念,可以 在去中心化预言机网络的帮助下实现,称为“区块订单公平性”。 它将 DON 在某个时间间隔内收到的交易分组为 “块”并同时在同一位置插入该块的所有交易 (即高度)进入主链。因此它们被排序在一起并且必须是可执行的 并行进行,而不会在它们之间造成任何冲突。 粗略地说,顺序公平性表明,如果大部分节点在 τ2 之前看到事务 τ1,那么 τ1 将在 τ2 之前或在同一块中排序。通过施加如此粗略的 交易订单的粒度,抢先交易和其他与订单相关的攻击的机会大大减少。 凯尔卡等人。提出一系列名为 Aequitas [144] 的协议,该协议解决了 不同的部署模型,包括同步、部分同步和异步网络设置。相对于基本的 BFT 共识,Aequitas 协议会带来大量的通信开销,因此对于实际使用来说并不理想。 然而,我们相信 Aequitas 的实用变体将会出现,可以使用 用于 FSS 和其他应用程序中的事务排序。一些相关方案有 已经提出了较少伴随的形式主义和较弱的性质, 例如,[36,151,236],但实际性能更好。这些方案都可以支持 在 FSS 中也是如此。 还值得注意的是,术语“公平”出现在 blockchain 的其他地方 具有不同含义的文学,即机会意义上的公平矿工与其承诺资源成正比 [106, 181] 或 validators 平等机会[153]。 安全因果关系保存: 防止分布式平台中的抢先交易和其他顺序违规的最广为人知的方法依赖于加密技术 技术。它们的共同特点是隐藏交易数据本身,等到 共识层秩序已建立,交易数据公开 稍后进行处理。这保留了交易之间的因果顺序 由 blockchain 执行。相关安全概念和密码协议 在 blockchains [71, 190] 出现之前已经得到了很大的发展。 “输入因果关系”[190] 和“安全因果关系保存”[71, 97] 的安全条件正式要求不知道任何有关交易的信息 在该交易在全球秩序中的位置尚未确定之前。在此之前,对手必须无法以加密方式推断出任何信息 强烈的感觉。 人们可以区分四种加密技术来保持因果关系: • 提交-显示协议 [29, 142, 145]:而不是宣布交易 明确地说,只有对交易的加密承诺才会被广播。在所有已提交但隐藏的事务已排序之后(在 blockchain 早期) MAINCHAIN 本身的系统,但这里是 FSS),发送者必须在预定的时间间隔内公开承诺并披露交易数据。 然后网络验证开放是否满足先前的承诺。的 此方法的起源可以追溯到 blockchains 出现之前。 虽然它特别简单,但该方法存在相当大的缺点,并且由于两个原因不容易采用。首先,由于在排序协议层面仅存在承诺,因此交易的语义 在达成共识期间无法验证。与客户的额外往返 是必需的。然而,更严重的是,权衡了没有开口可能会发生的可能性。 到达,这可能相当于拒绝服务攻击。此外,它 很难确定开局在一致的、分布式的情况下是否有效 方式,因为所有参与者必须就空缺是否到达达成一致 时间。 • 延迟恢复的提交-显示协议[145]:一项挑战 提交-显示方法是,客户端可以推测性地提交交易,并在后续交易使其有利可图时才显示它。一个 提交-显示方法的最新变体提高了对此的恢复能力 一种不当行为。特别是,TEX 协议 [145] 解决了这个问题 使用一种巧妙的方法,其中加密交易包含解密密钥 可以通过计算可验证的延迟函数(VDF)获得[53, 221]。如果一个客户 未能及时解密她的交易,系统中的其他人将解密 通过解决一个中等难度的密码难题来代表她。• 阈值加密 [71, 190]:该方法利用 DON 可以执行 阈值加密操作。假设 FSS 维护一个加密公共 key pkO 和 oracle 在它们之间共享相应的私钥。 然后,客户端在 pkO 下加密交易并将其发送到 FSS。社会保障基金订单 DON 上的交易,然后解密它们,最后将它们注入到 主链按固定顺序排列。因此,加密可确保排序 不是基于交易内容,而是数据本身在以下情况下可用: 需要。 该方法最初由 Reiter 和 Birman [190] 提出,后来由 Cachin 等人改进。 [71],它与许可共识相结合 协议。最近的工作探索了使用阈值密码学作为 用于通用消息 [33, 97] 和共享数据 [41] 的一般计算的共识级别机制。 与提交-显示协议相比,阈值加密可以防止简单的拒绝服务攻击(尽管考虑到解密的计算成本,需要小心)。它让 DON 以自己的速度自主前进,无需 等待客户的进一步行动。交易在解密后可以立即得到验证。此外,客户用一个加密所有交易 DON 的密钥,通信模式与其他相同 交易。安全地管理阈值密钥并更改节点 然而,O 可能会带来额外的困难。 • 承诺秘密共享[97]:而不是加密下的交易数据 DON 持有的密钥,客户端也可以为 O 中的节点秘密共享它。 使用混合的、计算安全的秘密共享方案,交易 首先使用带有随机密钥的对称密码进行加密。仅共享相应的对称密钥,并将密文提交给DON。 客户端必须使用单独加密的消息向 O 中的每个节点发送一个密钥共享。其余协议步骤与阈值相同 加密,只不过交易数据采用对称解密 从其份额重建每笔交易密钥后的算法。 此方法不需要设置或管理公钥密码系统 与 DON 相关。但是,客户端必须了解其中的节点 O 并在安全的环境中与每个人进行交流,这使得 给客户带来额外的负担。 尽管加密方法提供了针对信息的完整保护 从提交的交易泄漏到网络,它们不隐藏元数据。对于 例如,发件人的 IP 地址或 Ethereum 地址仍可被使用 进行抢先交易和其他攻击的对手。各种隐私增强 部署在网络层的技术,例如[52,95,107],或事务层, 例如,[13, 65],需要实现这一目标。特定作品的影响 元数据的数量,即交易发送到哪个合约,可以(部分)隐藏通过在同一个 DON 上复用许多合约。密码隐藏 交易本身也不能阻止损坏的交易的优先级 DON 节点与交易发送者勾结。 加密协议保证的安全因果关系补充了任何策略的秩序公平性保证,我们打算探索两者的结合 方法,如果可能的话。如果对手无法从中获得显着优势 观察元数据,安全的因果关系保存协议可以与 也是一种简单的订购方法。例如oracle节点可以写入交易 他们收到后立即发送给 L,不得重复。那么交易将是 根据他们在L上的出现进行排序并随后解密。 我们还计划考虑使用 TEE 作为帮助执行公平排序的一种方式;为了 例如,Tesseract [44] 可能被视为实现了一种因果排序形式,但一个 TEE 以显式形式处理交易的能力得到了加强,同时 保留他们的机密。 5.4 网络层注意事项 到目前为止,我们对 FSS 的描述主要集中在强制执行 FSS 的问题上。 最终的交易顺序与其在网络中观察到的顺序相匹配。此后, 我们考虑网络层本身可能出现的公平问题。 传统电子市场的高频交易者投入大量资金 资源以获得卓越的网络速度[64],加密货币交易所的交易者表现出类似的行为[90]。网络速度在以下方面都具有优势 观察其他方的交易并提交竞争交易。 实践中采用并在 Flash Boys [155] 一书中普及的一种补救措施是 最初在 IEX 交易所 [128] 中引入的“减速带”,后来在其他交易所中引入 交换 [179] (结果混合 [19])。该机制对市场准入施加了延迟(IEX 为 350 微秒),目的是抵消市场准入的优势。 速度。经验证据,例如[128],支持其减少某些交易的功效 普通投资者的成本。 FSS 可以简单地用于实现非对称 减速带——延迟传入交易的减速带。 Budish、Cramton 和 Shim [64] 认为,利用速度优势 在连续时间市场中是不可避免的,并主张在市场中采取结构性补救措施 以批量拍卖为基础的市场形式。但这种方法并未得到广泛采用 在现有的交易平台上。 传统的交易系统是中心化的,通常通过以下方式接收交易: 单个网络连接。相比之下,在去中心化系统中,可以 从多个有利位置观察交易传播。因此,可以观察到 P2P 网络中的网络泛洪等行为。 我们打算 探索 FSS 的网络层方法,帮助开发人员指定策略 禁止此类不良网络行为。5.5 实体级公平政策 秩序公平和安全因果关系旨在对以下交易执行排序: 尊重它们创建和首次提交到网络的时间。这种公平概念的局限性在于,它不能防止对手发起攻击 通过向系统注入大量交易来获得优势,观察到的策略 作为在 token 销售 [159] 中执行有效交易狙击的一种方式,并 造成拥堵,导致债务抵押头寸 (CDP) [48] 清算。 换句话说,秩序公平强制的是交易的公平,而不是玩家的公平。 如CanDID系统[160]所示,可以使用oracle工具,例如DECO 或 Town Crier 与节点委员会(例如 DON)结合以实现 各种形式的女巫抵抗,同时保护隐私。用户可以注册身份 并在不透露身份本身的情况下提供其独特性的证据。 抗女巫凭证提供了一种丰富交易排序的可能方法 限制洪水攻击机会的政策。例如,一个 token 销售可能只允许每个注册用户进行一笔交易,其中注册 需要国家标识符的唯一性证明,例如社会安全号码。 这种方法并非万无一失,但可能被证明是减轻交易泛滥攻击的有用策略。
Kerangka Kerja Eksekusi Transaksi DON
(DON-TEF) DONs akan memberikan oracle dan dukungan sumber daya terdesentralisasi untuk solusi lapisan-2 di dalamnya apa yang kami sebut Kerangka Eksekusi Transaksi Jaringan Oracle Terdesentralisasi (DONTEF) atau disingkat TEF. Saat ini, frekuensi pembaruan kontrak DeFi dibatasi oleh latensi rantai utama, misalnya, interval blok rata-rata 10-15 detik di Ethereum [104]—serta biaya mendorong data dalam jumlah besar secara berantai dan throughput komputasi/tx yang terbatas— memotivasi pendekatan penskalaan seperti sharding [148, 158, 232] dan eksekusi lapisan-2 [5, 12, 121, 141, 169, 186, 187]. Bahkan blockchains dengan waktu transaksi yang jauh lebih cepat, misalnya, [120], telah mengusulkan strategi penskalaan yang melibatkan komputasi off-chain [168]. TEF dimaksudkan untuk bertindak sebagai sumber daya lapisan-2 untuk sistem lapisan-1 / MAINCHAIN semacam itu. Menggunakan TEF, DONs dapat mendukung pembaruan yang lebih cepat dalam kontrak MAINCHAIN mempertahankan jaminan kepercayaan utama yang diberikan oleh rantai utama. TEF dapat mendukung salah satu dari sejumlah teknik dan paradigma eksekusi lapisan-2, termasuk rollups,11 rollups optimis, Validium, dll., serta model kepercayaan ambang batas di mana DON node mengeksekusi transaksi. TEF merupakan pelengkap FSS dan dimaksudkan untuk mendukungnya. Dengan kata lain, apapun aplikasi yang berjalan di TEF dapat menggunakan FSS. 11Sering disebut “zk-rollups,” merupakan istilah yang keliru karena tidak memerlukan bukti tanpa pengetahuan.
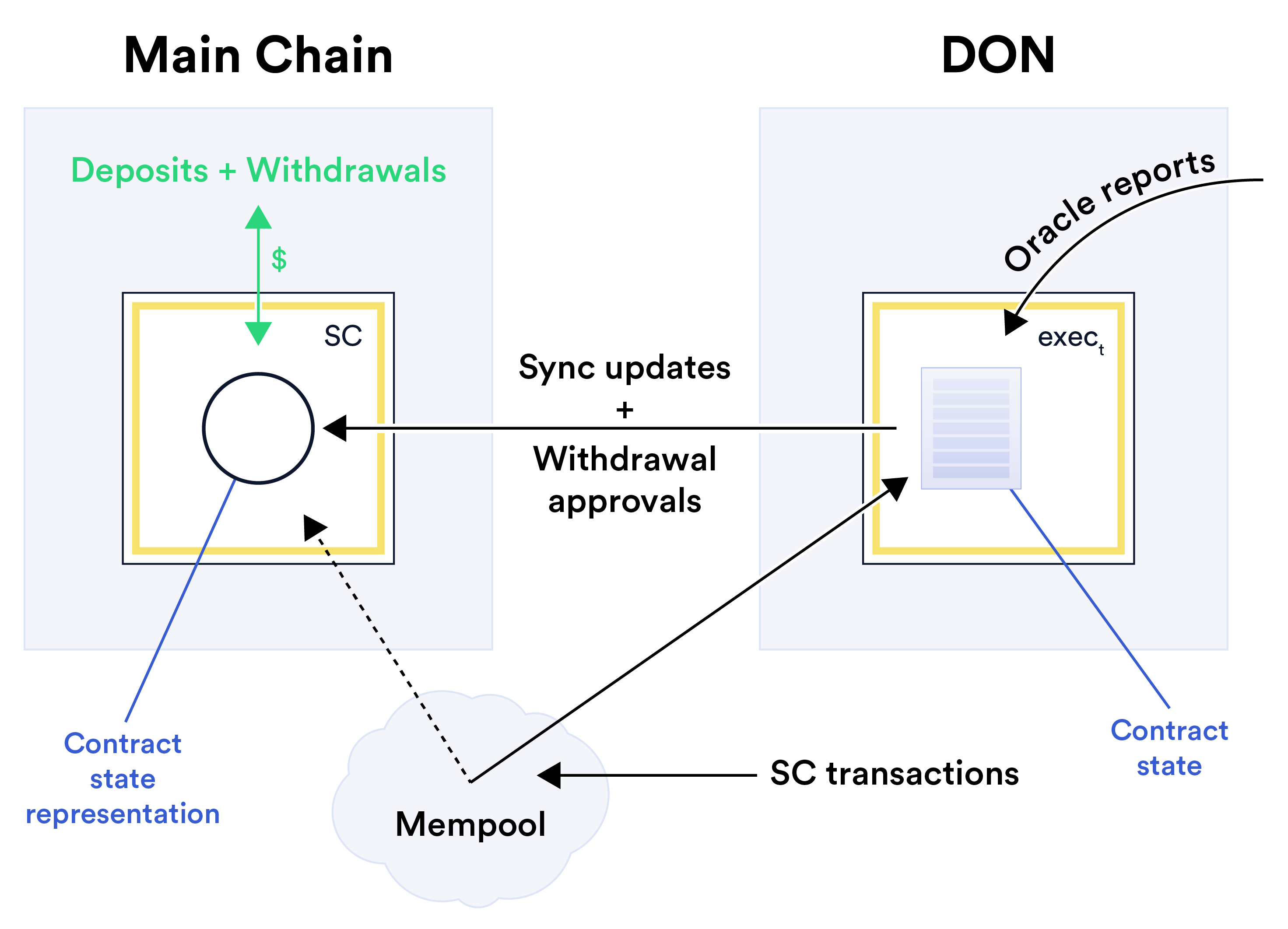
6.1 Ikhtisar TEF TEF adalah pola desain untuk konstruksi dan pelaksanaan hibrida yang berkinerja baik smart contract SC. Sesuai dengan ide utama di balik hybrid smart contracts, TEF melibatkan a dekomposisi SC menjadi dua bagian: (1) Apa yang dalam konteks TEF kita sebut sebagai jangkar kontrak SCa di MAINCHAIN dan (2) DON logika exect yang kita sebut TEF dapat dieksekusi. Kami menggunakan SC di sini untuk menunjukkan kontrak logis yang diterapkan oleh kombinasi SCa dan mengharapkan. (Seperti disebutkan di atas, kami berharap dapat mengembangkan alat kompiler untuk menguraikan a mengontrak SC secara otomatis ke dalam komponen ini.) Eksekusi TEF yang dapat dieksekusi adalah mesin yang memproses transaksi pengguna di SC. Itu dapat dijalankan dengan baik, karena dijalankan pada DON. Ini memiliki beberapa fungsi: • Penyerapan transaksi: exect menerima atau mengambil transaksi pengguna. Hal ini dapat dilakukan secara langsung, yaitu melalui penyerahan transaksi di DON, atau melalui MAINCHAIN mempool menggunakan MS. • Eksekusi transaksi cepat: memproses transaksi yang melibatkan aset di dalamnya SC. Ia melakukannya secara lokal, yaitu di DON. • Akses oracle / adaptor yang cepat dan murah: exect memiliki akses asli ke oracle laporan dan data adaptor lainnya yang menghasilkan, misalnya, aset yang lebih cepat, lebih murah, dan lebih akurat harga dari eksekusi MAINCHAIN. Selain itu, akses oracle off-chain berkurang biaya operasional oracle, maka biaya penggunaan sistem, dengan menghindari penyimpanan on-chain yang mahal. • Sinkronisasi: exect secara berkala mendorong pembaruan dari DON ke MAINCHAIN, memperbarui SCa. Kontrak jangkar adalah ujung depan MAINCHAIN SC. Sebagai komponen SC dengan tingkat kepercayaan yang lebih tinggi, komponen ini memiliki beberapa tujuan: • Penyimpanan aset: Dana pengguna disimpan, disimpan, dan ditarik dari SCa. • Sinkronisasi verifikasi: SCa dapat memverifikasi kebenaran pembaruan status saat dijalankan sinkronisasi, misalnya, SNARK yang dilampirkan ke rollups. • Pagar pembatas: SCa dapat mencakup ketentuan untuk melindungi terhadap korupsi atau kegagalan secara tepat. (Lihat Bagian 7 untuk rincian lebih lanjut.) Di TEF, dana pengguna disimpan di MAINCHAIN, artinya DON itu sendiri tidak bersifat hak asuh. Tergantung pada pilihan mekanisme sinkronisasi (lihat di bawah), pengguna mungkin memerlukannya untuk mempercayai DON hanya untuk laporan oracle yang akurat dan sinkronisasi tepat waktu dengan MAINCHAIN. Model kepercayaan yang dihasilkan sangat mirip dengan DEX berbasis buku pesanan, misalnya, [2], yang saat ini umumnya mencakup komponen off-chain untuk pencocokan pesanan dan komponen onchain untuk penyelesaian dan penyelesaian.Untuk menggunakan kosakata sistem pembayaran, orang mungkin menganggap exect sebagai komponennya SC bertanggung jawab untuk kliring, sedangkan SCa menangani penyelesaian. Lihat Gambar 13 untuk skemanya penggambaran TEF. Gambar 13: Skema TEF. Dalam contoh ini, transaksi melewati mempool dari MAINCHAIN melalui MS ke DON. Manfaat TEF: TEF membawa tiga manfaat utama: • Performa tinggi: SC mewarisi throughput DON yang jauh lebih tinggi dibandingkan MAINCHAIN untuk transaksi dan laporan oracle. Selain itu, exect dapat memproses transaksi lebih cepat dan merespons laporan oracle dengan lebih tepat waktu dibandingkan implementasi di MAINCHAIN saja. • Biaya lebih rendah: Proses sinkronisasi tidak terlalu sensitif terhadap waktu dibandingkan pemrosesan transaksi, dan transaksi dapat dikirim dari DON ke MAINCHAIN secara batch. Akibatnya, biaya on-chain per transaksi (misalnya biaya bahan bakar) dengan pendekatan ini jauh lebih rendah dibandingkan kontrak yang hanya berjalan di MAINCHAIN. • Kerahasiaan: Mekanisme kerahasiaan DON dapat dibawa ke menanggung SC.
Batasan TEF: Salah satu keterbatasan TEF adalah tidak mendukung proses instan penarikan, karena hanya terjadi di MAINCHAIN: Setelah mengirimkan permintaan penarikan bagi SCa, pengguna mungkin perlu menunggu hingga exect melakukan pembaruan status yang mencakup transaksi penarikan sebelum dapat disetujui. Kami membahas beberapa solusi parsial, namun, di Bagian 6.2. Keterbatasan lain dari TEF adalah tidak mendukung komposisi atom DeFi kontrak di MAINCHAIN, khususnya kemampuan untuk mengarahkan aset melalui beberapa DeFi kontrak dalam satu transaksi. TEF dapat, bagaimanapun, mendukung atomisitas tersebut DeFi kontrak berjalan pada DON yang sama. Kami juga membahas beberapa cara untuk mengatasi hal ini masalah di Bagian 6.2. 6.2 Perutean Transaksi Transaksi untuk SC dapat dikirim oleh pengguna langsung ke DON atau dapat disalurkan melalui mempool di MAINCHAIN (melalui FSS). Ada empat jenis transaksi yang berbeda, masing-masing diantaranya memerlukan penanganan yang berbeda: Transaksi dalam kontrak: Karena menghindari komplikasi dinamika gas, TEF memberi SC lebih banyak fleksibilitas dalam menangani transaksi dibandingkan dengan yang seharusnya. tersedia dalam kontrak lapisan-1. Misalnya, saat transaksi mempool di Ethereum dapat ditimpa oleh transaksi baru dengan harga gas yang lebih tinggi, SC dapat memperlakukan transaksi yang beroperasi pada aset dalam SC sebagai transaksi yang otoritatif segera setelah transaksi tersebut terlihat di mempool. Konsekuensinya, SC tidak perlu menunggu transaksi dikonfirmasi dalam satu blok, menghasilkan latensi yang sangat berkurang. Proksi: Pengguna mungkin ingin mengirim transaksi τ ke SC melalui kontrak dompet atau kontrak lain di MAINCHAIN. DON dapat melakukan simulasi eksekusi τ di MAINCHAIN untuk menentukan apakah menghasilkan transaksi lanjutan ke SC. Jika demikian, τ dapat diurutkan dengan transaksi lain untuk SC yang melakukan hal tersebut. Ada beberapa kemungkinan bagaimana DON mengidentifikasi transaksi tersebut: (1) DON dapat mensimulasikan semua transaksi di mempool (pendekatan yang mahal); (2) Kontrak tertentu atau jenis kontrak, misalnya dompet, dapat dicantumkan untuk dipantau oleh DON; atau (3) Pengguna bisa membubuhi keterangan transaksi untuk pemeriksaan DON. Masalah menjadi lebih rumit ketika satu transaksi berinteraksi dengan dua transaksi kontrak, SC1 dan SC2, keduanya menggunakan Layanan Pengurutan yang Adil dan memiliki kebijakan pemesanan yang tidak sesuai. DON mungkin, misalnya, mengurutkan τ paling lambat yang kompatibel dengan keduanya. Deposito: Transaksi yang menyetorkan aset MAINCHAIN ke SC perlu dikonfirmasi dalam satu blok sebelum SC dapat menganggapnya sah. Ketika mendeteksi penambangan a transaksi yang mengirimkan aset (misalnya, Ether) ke SCa, exect dapat langsung mengonfirmasinyadeposito. Misalnya, perusahaan dapat menerapkan harga yang dilaporkan oracle saat ini di DON ke aset. Penarikan: Seperti disebutkan di atas, batasan TEF adalah penarikan tidak selalu dapat dilakukan secara instan. Dalam model eksekusi tipe rollup, penarikan permintaan harus diurutkan dengan transaksi lain, yaitu digulung, agar aman diproses. Namun, ada beberapa solusi parsial terhadap keterbatasan ini. Jika DON dapat dengan cepat menghitung bukti validitas rollup hingga transaksi penarikan, kemudian mengamati transaksi pengguna τ di mempool exect dapat mengirimkan transaksi pembaruan status τ ′ untuk τ dengan harga bahan bakar yang lebih tinggi, semacam keuntungan yang berjalan di depan. Asalkan τ tidak ditambang sebelum τ ′ mencapai mempool, τ ′ akan mendahului τ, dan τ akan mempengaruhi penarikan yang disetujui. Dalam varian TEF yang DON diandalkan untuk menghitung pembaruan status (lihat varian penandatanganan ambang batas di bawah), DON sebagai alternatif dapat menentukan off-chain apakah τ harus disetujui mengingat keadaan SC pada saat pelaksanaannya. DON kemudian dapat mengirim transaksi τ ′ yang menyetujui penarikan τ—tanpa mempengaruhi penarikan penuh pembaruan negara. Jika pendekatan ini tidak memungkinkan, atau jika tidak berhasil, DON akan memulai transaksi τ ′ dapat mengirimkan dana kepada pengguna sebagai respons terhadap τ sehingga pengguna tidak memerlukannya memulai transaksi tambahan. 6.3 Sinkronisasi Eksekusi TEF secara berkala mendorong pembaruan dari DON ke MAINCHAIN, memperbarui status SCa dalam proses yang kami sebut sebagai sinkronisasi. Sinkronisasi mungkin dipertimbangkan sebagai propagasi transaksi layer-2 ke layer-1, sehingga TEF dapat menggunakan nomor mana pun teknik yang ada untuk tujuan ini, termasuk rollups [5, 12, 16, 69], optimis rollups [10, 11, 141], Validium [201], atau penandatanganan ambang batas dasar, misalnya ambang batas BLS, Schnorr, atau ECDSA [24, 54, 116, 202]. Pada prinsipnya, lingkungan eksekusi tepercaya juga dapat membuktikan kebenaran perubahan keadaan, sehingga menawarkan kinerja yang jauh lebih baik alternatif untuk rollups, tetapi dengan model kepercayaan yang bergantung pada perangkat keras. (Lihat, misalnya, [80].) Di bawah ini kami membandingkan opsi sinkronisasi ini sehubungan dengan tiga properti utama di TEF: • Ketersediaan data: Di mana status SC disimpan? Setidaknya ada tiga pilihan tersedia dalam TEF: di MAINCHAIN, di DON, atau di penyimpanan pihak ketiga penyedia seperti IPFS. Mereka mencapai jaminan keamanan dan ketersediaan yang berbeda tingkat, dan profil kinerja. Singkatnya, menyimpan status di MAINCHAIN memungkinkan kemampuan audit on-chain dan menghilangkan ketergantungan pada pihak mana pun atas ketersediaan negara; di sisi lain, penyimpanan negara secara off-chain dapat mengurangi dan meningkatkan biaya penyimpanan throughput, dengan biaya mempercayai penyedia penyimpanan (DON atau pihak ketiga) untuk ketersediaan data. Tentu saja, model fleksibel yang menggabungkan opsi-opsi ini juga demikian mungkin. Kami menunjukkan bentuk ketersediaan data yang diperlukan pada Tabel 1.• Jaminan kebenaran: Bagaimana SCa memastikan kebenaran pembaruan didorong oleh exect? Hal ini mempengaruhi beban komputasi pada exect dan SCa dan menyinkronkan latensi (lihat di bawah). • Latensi: Latensi sinkronisasi memiliki tiga faktor yang berkontribusi: (1) Waktu yang dibutuhkan misalnya untuk menghasilkan transaksi sinkronisasi τsync; (2) Waktu yang dibutuhkan untuk sinkronisasi untuk dikonfirmasi di MAINCHAIN; dan (3) Waktu untuk τsync mulai berlaku SCa. Di TEF, latensi sangat penting untuk penarikan (tetapi kurang penting untuk penarikan transaksi dalam kontrak) karena penarikan memerlukan (setidaknya parsial) sinkronisasi status. Sinkronisasi pilihan Data ketersediaan kebenaran jaminan Latensi Gabungan [5, 12, 16, 69] dalam rantai Bukti validitas Waktu yang dibutuhkan untuk menghasilkan bukti validitas (misalnya, menit dalam sistem saat ini) Validium [201] Off-rantai Bukti validitas Sama seperti di atas Optimis rollup [10, 11, 141] dalam rantai Bukti penipuan Durasi tantangan periode (misalnya, hari atau minggu) Penandatanganan ambang batas [24, 54, 116, 202] Fleksibel Tanda tangan ambang batas oleh DON Seketika Lingkungan eksekusi tepercaya [80] Fleksibel Berbasis perangkat keras pengesahan Seketika Tabel 1: Berbagai opsi sinkronisasi di TEF dan propertinya. Tabel 1 merangkum properti ini dalam lima opsi sinkronisasi utama di TEF. (Catatan bahwa kami tidak bermaksud membandingkan teknologi ini sebagai penskalaan lapisan-2 yang berdiri sendiri solusi. Untuk itu kami merujuk pembaca ke misalnya, [121].) Sekarang kita membahas setiap opsi sinkronisasi. Rollup: rollup [69] adalah protokol di mana transisi keadaan dipengaruhi oleh a kumpulan transaksi dihitung secara off-chain. Perubahan keadaan kemudian disebarkan ke RANTAI UTAMA. Untuk mengimplementasikan rollups, jangkar smart contract SCa menyimpan representasi ringkas Rstate (misalnya akar Merkle) dari keadaan sebenarnya. Untuk menyinkronkan, exect mengirimkan τsync = (T, R′ state) ke SCa dimana T adalah himpunan transaksi yang diproses sejak terakhir kalisinkronisasi dan R′ negara bagian adalah representasi kompak dari negara bagian baru yang dihitung dengan menerapkan transaksi di T ke keadaan sebelumnya Rstate. Ada dua varian populer yang berbeda dalam cara SCa memverifikasi pembaruan status di τsync. Yang pertama, (zk-)rollups, melampirkan argumen kebenaran yang ringkas, terkadang disebut bukti validitas, untuk transisi Rstate →R′ negara bagian. Untuk mengimplementasikan varian ini, exect menghitung dan menyerahkan bukti validitas (misalnya, bukti zk-SNARK) bersama dengan τsync, membuktikan bahwa R′ keadaan adalah hasil penerapan T pada keadaan SCa saat ini. Jangkar kontrak menerima pembaruan negara hanya setelah memverifikasi buktinya. rollup yang optimis tidak menyertakan argumen kebenaran, tetapi memiliki staking dan menantang prosedur yang memfasilitasi verifikasi terdistribusi transisi negara. Untuk ini Varian rollup, SCa untuk sementara menerima τsync dengan asumsi itu benar (karenanya optimisme) tapi τsync tidak berlaku sampai setelah periode tantangan, di mana pihak mana pun pemantauan MAINCHAIN dapat mengidentifikasi pembaruan status yang salah dan memberi tahu SCa untuk mengambil tindakan tindakan yang diperlukan (misalnya, mengembalikan status dan memberikan penalti jika diperlukan.) Kedua varian rollup mencapai ketersediaan data on-chain, saat transaksi diposting on-chain, dari mana keadaan penuh dapat dibangun. Latensi zk-rollups adalah didominasi oleh waktu yang diperlukan untuk menghasilkan bukti validitas, yang biasanya ada di urutan menit dalam sistem yang ada [16] dan kemungkinan akan mengalami peningkatan seiring berjalannya waktu. Sebaliknya, rollup yang optimis memiliki latensi yang lebih tinggi (misalnya, hari atau minggu) karena periode tantangan harus cukup lama agar bukti penipuan dapat berfungsi. Itu Implikasi dari konfirmasi yang lambat tidak kentara dan terkadang bersifat spesifik terhadap skema tersebut analisis menyeluruh berada di luar cakupan. Misalnya, skema tertentu mempertimbangkan pembayaran transaksi sebagai “final tanpa kepercayaan” [109] sebelum pembaruan status dikonfirmasi, karena a pengguna biasa dapat memverifikasi rollup jauh lebih cepat daripada MAINCHAIN. Validium: Validium adalah bentuk (zk-)rollup yang membuat data hanya tersedia secara off-chain dan tidak menyimpan semua data di MAINCHAIN. Secara khusus, exect hanya mengirimkan yang baru sebutkan dan buktinya tetapi bukan transaksi ke SCa. Dengan sinkronisasi gaya Validium, jalankan dan DON yang menjalankannya adalah satu-satunya pihak yang menyimpan status lengkap dan yang mengeksekusi transaksi. Seperti zk-rollups, latensi sinkronisasi didominasi oleh validitas waktu pembuatan bukti. Namun, tidak seperti zk-rollups, sinkronisasi gaya Validium mengurangi biaya penyimpanan dan meningkatkan throughput. Penandatanganan ambang batas oleh DON: Dengan asumsi ambang batas DON node adalah jujur, a Opsi sinkronisasi yang sederhana dan cepat adalah dengan meminta DON node secara kolektif menandatangani status baru. Pendekatan ini dapat mendukung ketersediaan data on-chain dan off-chain. Perhatikan bahwa jika pengguna memercayai DON untuk oracle pembaruan, mereka tidak perlu lebih memercayainya untuk menerima pembaruan status, karena sudah berada dalam model kepercayaan ambang batas. Manfaat lain dari penandatanganan ambang batas adalah latensi rendah. Dukungan untuk format tanda tangan transaksi baru sebagai diusulkan di EIP-2938 [70] dan dikenal sebagai abstraksi akun akan membuat ambang batas penandatanganan jauh lebih mudah untuk diterapkan, karena akan menghilangkan kebutuhan akan ambang batas ECDSA, yang melibatkan protokol yang jauh lebih kompleks (misalnya, [116, 117, 118])daripada alternatif seperti ambang batas tanda tangan Schnorr [202] atau BLS [55]. Lingkungan Eksekusi Tepercaya (TEE): TEE adalah lingkungan eksekusi terisolasi (biasanya diwujudkan oleh perangkat keras) yang bertujuan untuk memberikan perlindungan keamanan yang kuat untuk program yang berjalan di dalam. Beberapa TEE (misalnya, Intel SGX [84]) dapat menghasilkan bukti, dikenal sebagai pengesahan, bahwa keluaran dihitung dengan benar oleh program tertentu masukan tertentu12. Varian sinkronisasi TEF berbasis TEE dapat diimplementasikan oleh mengganti bukti di (zk-)rollups atau Validium dengan pengesahan TEE menggunakan teknik dari [80]. Dibandingkan dengan bukti tanpa pengetahuan yang digunakan di rollups dan Validium, TEE jauh lebih berguna. lebih berkinerja. Dibandingkan dengan penandatanganan ambang batas, TEE menghilangkan kerumitan menghasilkan ambang batas tanda tangan ECDSA karena pada prinsipnya hanya diperlukan satu TEE terlibat. Namun, penggunaan TEEs menimbulkan asumsi kepercayaan ekstra yang bergantung pada perangkat keras. Kita juga dapat menggabungkan TEE dengan penandatanganan ambang batas untuk menciptakan ketahanan terhadap kompromi sebagian kecil dari contoh TEE, meskipun ini merupakan tindakan perlindungan memperkenalkan kembali kompleksitas pembuatan tanda tangan ECDSA ambang batas. Fleksibilitas tambahan: Opsi sinkronisasi ini dapat disempurnakan untuk memberikan lebih banyak fleksibilitas dengan cara berikut. • Pemicu yang fleksibel: Aplikasi TEF dapat menentukan kondisi di mana sinkronisasi dipicu. Misalnya, sinkronisasi dapat berbasis batch, misalnya terjadi setelahnya setiap N transaksi, berdasarkan waktu, misalnya setiap 10 blok, atau berdasarkan peristiwa, misalnya terjadi setiap kali harga aset target bergerak secara signifikan. • Sinkronisasi parsial: Hal ini dimungkinkan dan dalam beberapa kasus diinginkan (misalnya, dengan rollups, sinkronisasi parsial dapat mengurangi latensi) dengan tujuan menyediakan sinkronisasi cepat dalam skala kecil sejumlah negara, melakukan sinkronisasi penuh mungkin hanya secara berkala. Misalnya, exect dapat menyetujui permintaan penarikan dengan memperbarui saldo pengguna di SCa tanpa memperbarui status MAINCHAIN. 6.4 Reorganisasi Reorganisasi Blockchain akibat ketidakstabilan jaringan atau bahkan dari serangan 51%. dapat menimbulkan ancaman terhadap integritas rantai utama. Dalam praktiknya, musuh telah menggunakannya mereka untuk melakukan serangan pembelanjaan ganda [34]. Sementara serangan terhadap rantai besar memang demikian sulit untuk dipasang, namun tetap layak untuk beberapa rantai [88]. Karena beroperasi secara independen dari MAINCHAIN, DON menawarkan hal yang menarik kemungkinan untuk mengamati dan memberikan beberapa perlindungan terhadap reorg yang terkait dengan serangan. Misalnya, DON dapat melaporkan ke kontrak yang mengandalkan SC di MAINCHAIN mengenai keberadaan fork pesaing dengan panjang ambang batas tertentu τ. DON juga bisa 12Rincian tambahan dapat ditemukan di Lampiran B.2.1. Mereka tidak dituntut untuk memahami.
memberikan bukti—baik dalam pengaturan PoW atau PoS—tentang keberadaan fork tersebut. Itu kontrak SC dapat menerapkan tindakan defensif yang sesuai, seperti menangguhkan eksekusi transaksi lebih lanjut untuk jangka waktu tertentu (misalnya, mengizinkan bursa memasukkan pembelanjaan ganda ke dalam daftar hitam aset). Perhatikan bahwa meskipun musuh melancarkan serangan 51%, ia mungkin berupaya melakukan sensor laporan dari DON, tindakan penanggulangan di SC adalah dengan mewajibkan laporan berkala dari DON untuk memproses transaksi (yaitu detak jantung) atau memerlukan laporan baru ke memvalidasi transaksi bernilai tinggi. Meskipun peringatan forking tersebut pada prinsipnya merupakan layanan umum yang dapat diberikan oleh DON untuk beberapa tujuan, rencana kami adalah menggabungkannya dengan TEF.
DON 事务执行框架
(DON-TEF) DONs 将为 oracle 内的第 2 层解决方案提供 oracle 和去中心化资源支持 我们称之为去中心化 Oracle 网络交易执行框架 (DONTEF) 或简称 TEF。 如今,DeFi 合约的更新频率受到主链延迟的限制, 例如,Ethereum [104] 中 10-15 秒的平均区块间隔,以及 在链上推送大量数据和有限的计算/交易吞吐量—— 激励扩展方法,例如分片 [148、158、232] 和第 2 层执行 [5、 12、121、141、169、186、187]。即使 blockchains 的交易时间要快得多, 例如,[120],提出了涉及链外计算[168]的扩容策略。 TEF 旨在充当任何此类第 1 层/主链系统的第 2 层资源。 使用 TEF,DONs 可以支持主链合约中更快的更新,同时 保留主链提供的关键信任保证。 TEF可以支持 许多第 2 层执行技术和范例中的任何一种,包括 rollups,11 乐观的rollups、Validium等,以及阈值信任模型,其中DON 节点执行交易。 TEF 是 FSS 的补充,旨在为其提供支持。换句话说,任何 在 TEF 中运行的应用程序可以使用 FSS。 11通常称为“zk-rollups”,这是用词不当,因为它们不一定需要零知识证明。
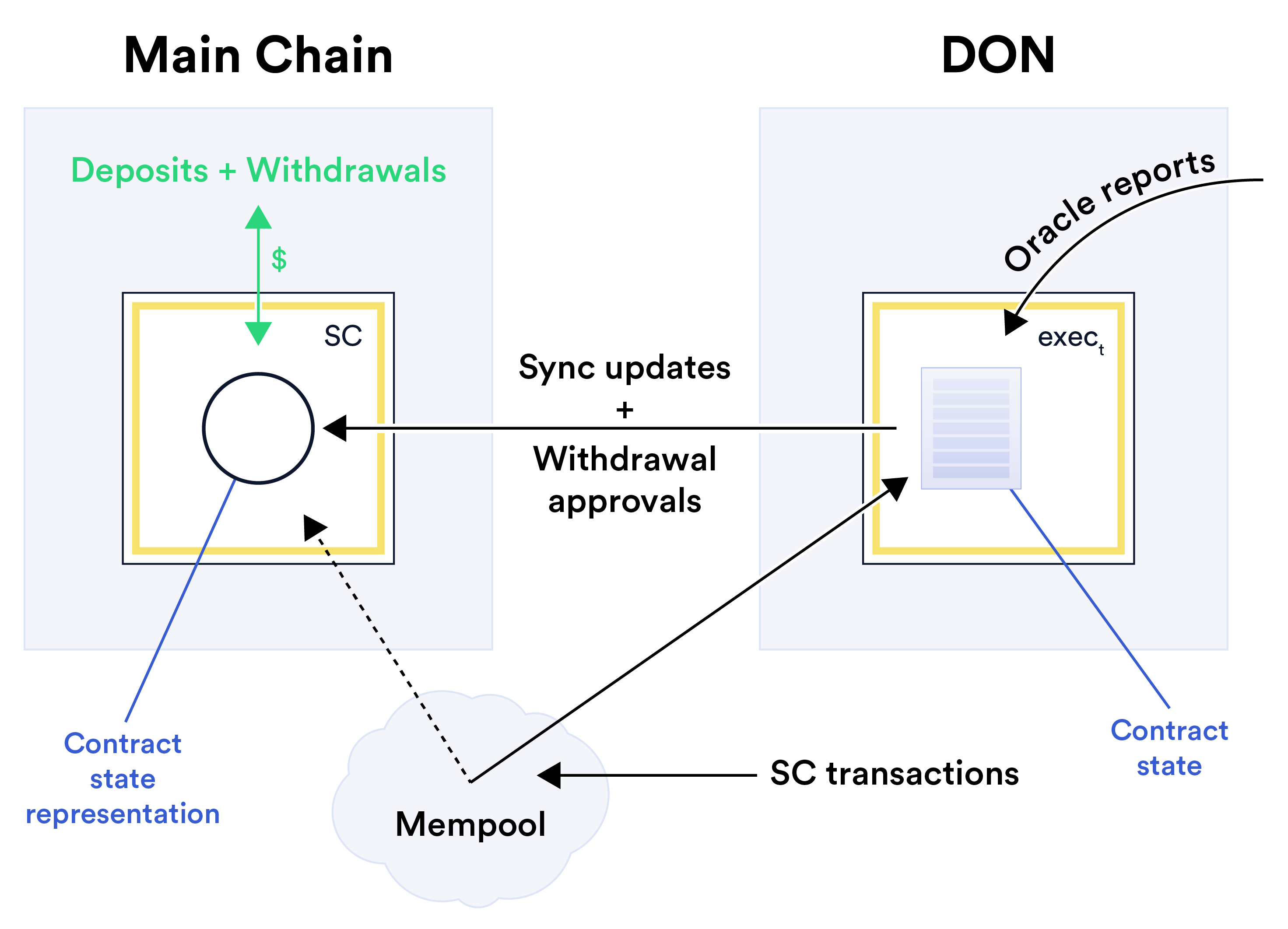
6.1 TEF 概述 TEF 是一种用于构建和执行高性能混合体的设计模式 smart contract SC。 根据混合 smart contract 背后的主要思想,TEF 涉及 将 SC 分解为两部分: (1) 我们在 TEF 上下文中称之为锚点 MAINCHAIN 上的合约 SCa 和 (2) DON 逻辑要求我们调用 TEF 可执行文件。 我们这里用SC来表示SCa组合实现的逻辑合约 并执行。 (如上所述,我们期望开发编译器工具来分解 SC 自动收缩到这些组件中。) TEF可执行exec是SC中处理用户交易的引擎。它 可以以高性能的方式执行,因为它在 DON 上运行。它有几个功能: • 交易摄取:exec 接收或获取用户的交易。它可以这样做 直接,即通过 DON 上的交易提交,或通过主链 使用 MS 的内存池。 • 快速交易执行:exec 处理涉及以下资产的交易 SC。它在本地执行此操作,即在 DON 上。 • 快速且低成本的oracle /适配器访问:exec 具有对 oracle 报告的本机访问权限 和其他适配器数据,例如更快、更便宜和更准确的资产 定价高于主链执行。此外,链下 oracle 访问减少了 oracle 的运营成本,即使用该系统的成本,通过避免 昂贵的链上存储。 • 同步:exec 定期将更新从DON 推送到主链,更新SCa。 锚定合约是SC的主链前端。作为 SC 的更高信任组件,它有几个用途: • 资产托管:用户的资金存入、持有和提取于SCa。 • 同步验证:SCa 可以在执行时验证状态更新的正确性 同步,例如附加到 rollups 的 SNARK。 • 护栏:SCa 可能包括防止腐败或故障的规定 期待中。 (更多详情请参见第 7 节。) 在 TEF 中,用户的资金托管在主链上,这意味着 DON 本身是非托管的。根据同步机制的选择(见下文),用户可能需要 仅信任 DON 以获得准确的 oracle 报告并及时与主链同步。 由此产生的信任模型与基于订单簿的 DEX 非常相似,例如 [2], 如今,它通常包括用于订单匹配的链下组件和用于清算和结算的链上组件。要使用支付系统的词汇,人们可能会认为 exct 是一个组件 SC负责清算,SCa负责结算。原理图见图 13 TEF 的描述。 图 13:TEF 原理图。在此示例中,交易通过内存池 通过 MS 到 DON 的主链。 TEF的好处: TEF 具有三个主要优势: • 高性能:SC 继承了DON 比 MAINCHAIN 高得多的吞吐量 对于交易和 oracle 报告。此外,与单独在 MAINCHAIN 上实现相比,exec 可以更快地处理交易并更及时地响应 oracle 报告。 • 费用更低:同步过程对时间的敏感性低于交易处理,并且交易可以批量从DON 发送到MAINCHAIN。 因此,这种方法的每笔交易链上费用(例如,gas 成本)比仅在主链上运行的合约低得多。 • 保密性:DON 的保密机制可用于 承担SC。
TEF 限制: TEF 的一个限制是它不支持瞬时 提款,因为它们仅发生在主链上:发送提款请求后 对于SCa,用户可能需要等待execute来执行状态更新,其中包括 在获得批准之前提款交易。我们讨论一些部分补救措施, 然而,在第 6.2 节中。 TEF 的另一个限制是它不支持 DeFi 的原子组合 主链上的合约,特别是通过多个 DeFi 路由资产的能力 单一交易中的合同。然而,TEF 可以支持这种原子性 DeFi 合约在同一个 DON 上运行。我们还讨论了一些解决这个问题的方法 6.2 节中的问题。 6.2 交易路由 SC 的交易可以由用户直接发送到 DON 或可以通过 MAINCHAIN 中的内存池(通过 FSS)。有四种不同的交易类型,每种类型 其中需要不同的处理: 合约内交易: 因为它回避了气体动力学的复杂性,TEF 为 SC 在处理交易方面提供了比普通 SC 更大的灵活性。 在第 1 层合约中可用。例如,当 Ethereum 中的内存池交易时 可以被更高 Gas 价格的新交易覆盖,SC 可以在 SC 内的资产上操作的交易一旦变得可见就视为权威交易 在内存池中。因此,SC不需要等待交易被确认 在一个块内,从而大大减少延迟。 代理: 用户可能希望通过钱包合约向 SC 发送交易 τ 或 主链上的其他合约。 DON 可以模拟执行 MAINCHAIN 上的 τ 来确定是否会导致 SC 的后续交易。 如果是这样,τ 可以与 SC 的其他交易一起排序。有几个 DON 如何识别此类交易的可能性: (1) DON 可以模拟 内存池中的所有交易(一种昂贵的方法); (2) 某些合同或 可以列出合约类型,例如钱包,以供 DON 监控;或 (3) 用户可以 注释交易以供 DON 检查。 当单个事务与两个事务交互时,事情变得更加复杂 合约 SC1 和 SC2,两者都使用公平排序服务并且具有不兼容的排序策略。例如,DON 可能会在最晚的时间对 τ 进行排序 两者兼容。 存款: 将主链资产存入 SC 的交易需要在区块中得到确认,然后 SC 才能将其视为有效。当它检测到采矿 将资产(例如以太币)发送到SCa的交易,exec可以立即确认订金。例如,它可以将 DON 的当前 oracle 报告价格应用于 资产。 提款: 如上所述,TEF 的局限性在于提款不能总是立即执行。在 rollup 类型的执行模型中,提款 请求必须与其他事务一起排序,即汇总,以便安全地进行 已处理。然而,有一些针对此限制的部分补救措施。 如果 DON 可以快速计算出 rollup 的有效性证明直到提款交易,那么观察内存池中的用户交易 τ 可以以更高的 Gas 价格发送 τ 的状态更新交易 τ ′,这是一种有益的抢先交易。 假设 τ 在 τ ′ 到达内存池之前未被开采,则 τ ′ 将先于 τ,并且 τ 将影响批准的提款。 在 TEF 变体中,依赖 DON 来计算状态更新(请参阅 下面的阈值签名变体),DON 也可以确定链下 考虑到 SC 执行时的状态,是否应该批准 τ。 DON 然后可以发送一个交易 τ ′ 来批准提款 τ,而不影响完整的交易 状态更新。 如果此方法不可行,或者在不成功的情况下,则由 DON 启动 交易 τ ′ 可以响应 τ 向用户发送资金,这样用户就不需要 发起额外交易。 6.3 正在同步 TEF 可执行文件 exec 定期将更新从 DON 推送到 MAINCHAIN, 在我们称为同步的过程中更新 SCa 的状态。可以考虑同步 作为第 2 层交易到第 1 层的传播,因此 TEF 可以利用任意数字 用于此目的的现有技术,包括 rollups [5, 12, 16, 69],乐观 rollups [10, 11, 141],Validium [201],或基本阈值签名,例如阈值 BLS, Schnorr,或 ECDSA [24,54,116,202]。原则上,可信执行环境 还可以证明状态更改的正确性,提供更高性能的 rollups 的替代方案,但具有依赖于硬件的信任模型。 (例如,参见 [80]。) 下面我们比较这些同步选项的三个关键属性 技术教育框架: • 数据可用性:SC 的状态存储在哪里?至少三个选项是 在 TEF 中可用:在主链上、在 DON 上或通过某些第三方存储 IPFS 等提供商。他们实现了不同的安全保证、可用性 级别和性能概况。简而言之,在主链上存储状态可以实现 链上可审计性并消除对任何一方的状态可用性的依赖; 另一方面,链下存储状态可以降低存储成本并提高 吞吐量,以信任存储提供商(DON 或第三方)为代价 数据可用性。当然,结合这些选项的灵活模型也可以 可能的。我们在表 1 中指出了所需的数据可用性形式。• 正确性保证:SCa 如何确定更新的正确性 由exec 推动?这会影响 exect 和 SCa 的计算负载以及 同步延迟(见下文)。 • 延迟:同步延迟有三个影响因素: (1) 所花费的时间 用于生成同步交易τsync; (2) τsync 所花费的时间 待主链确认; (3) τsync 生效的时间 SC。在 TEF 中,延迟对于提款尤为重要(但对于提款来说则不那么重要) 合约内交易)因为提款必然需要(至少 部分)状态同步。 正在同步 选项 数据 可用性 正确性 保证 延迟 汇总 [5, 12, 16, 69] 链上 有效性证明 生成所需时间 有效性证明(例如当前系统中的分钟数) 维迪乌姆 [201] 链下 有效性证明 与上面相同 乐观rollup [10, 11, 141] 链上 欺诈证明 挑战时长 期间 (例如, 天 或 周) 门槛签名 [24, 54、116、202] 灵活 DON 的阈值签名 瞬时 可信执行环境 [80] 灵活 基于硬件 证明 瞬时 表 1:TEF 中的各种同步选项及其属性。 表 1 总结了 TEF 中五个主要同步选项的这些属性。 (注 我们不打算将这些技术与独立的第 2 层扩展进行比较 解决方案。为此,我们建议读者参考 [121]。) 现在我们讨论每个同步选项。 汇总: rollup [69] 是一个协议,其中状态转换由 一批交易是在链外计算的。 然后传播状态变化 到主链上。 为了实现 rollups,锚点 smart contract SCa 存储实际状态的紧凑表示 Rstate(例如 Merkle 根)。要同步,exec 发送 τsync = (T,R′ 状态)到 SCa,其中 T 是自上次以来处理的事务集同步和R′ state 是通过应用计算出的新状态的紧凑表示 T 中的交易到先前状态 Rstate。 有两种流行的变体,它们在 SCa 验证 τsync 中状态更新的方式上有所不同。 第一个,(zk-)rollups,附加一个简洁的正确性论证,有时称为 有效性证明,用于转换 Rstate →R′ 状态。要实现此变体,请执行 计算并提交有效性证明(例如,zk-SNARK 证明)以及 τsync, 证明R′ state 是将 T 应用到 SCa 当前状态的结果。锚 合约仅在验证证明后才接受状态更新。 乐观的 rollup 不包括正确性的论点,但有 staking 和 促进状态转换的分布式验证的挑战程序。为此 rollup 变体,SCa 暂时接受 τsync 假设它是正确的(因此乐观) 但 τsync 直到挑战期结束后才生效,在此期间任何一方 监控 MAINCHAIN 可以识别错误的状态更新并通知 SCa 采取措施 必要的行动(例如,回滚状态并对exec施加惩罚。) 随着交易的发布,两个 rollup 变体都实现了链上数据可用性 链上,可以从中构建完整的状态。 zk-rollups 的延迟为 主要由生成有效性证明所需的时间决定,这通常是在 现有系统 [16] 中的分钟顺序,并且随着时间的推移可能会得到改进。 另一方面,乐观的 rollups 具有更高的延迟(例如,几天或几周) 因为挑战期需要足够长才能使欺诈证明发挥作用。的 缓慢确认的含义是微妙的,有时特定于该方案,因此 彻底的分析超出了范围。例如,某些计划考虑付款 在确认状态更新之前,交易作为“无信任最终”[109],因为 普通用户可以比主链更快地验证 rollup。 有效: Validium 是 (zk-)rollup 的一种形式,使数据仅在链外可用 并且不维护主链上的所有数据。具体来说,exec 只发送新的 状态和证明,但不向 SCa 发送交易。使用 Validium 风格的同步,执行 并且执行它的 DON 是唯一存储完整状态和 执行交易。与 zk-rollups 一样,同步延迟主要由有效性决定 证明生成时间。然而,与 zk-rollups 不同的是,Validium 风格的同步减少了 存储成本并增加吞吐量。 DON 的阈值签名: 假设 DON 个节点的阈值是诚实的, 简单而快速的同步选项是让 DON 节点共同签署新状态。 这种方法可以支持链上和链下数据的可用性。请注意,如果 用户信任 DON 的 oracle 更新,他们不需要更信任它来接受 状态更新,因为它们已经处于阈值信任模型中。 另一个好处是 阈值签名是低延迟的。支持新的交易签名格式 EIP-2938 [70] 中提出并称为帐户抽象将产生阈值 签名更容易实施,因为它将消除门槛的需要 ECDSA,涉及相当复杂的协议(例如,[116,117,118])比阈值 Schnorr [202] 或 BLS [55] 签名等替代方案更好。 可信执行环境 (TEE): TEE是隔离的执行环境(通常由硬件实现),旨在提供强大的安全保护 用于内部运行的程序。一些 TEE(例如 Intel SGX [84])可以生成证明, 称为证明,输出是由特定程序正确计算的 特定的输入12。 TEF 同步的基于 TEE 的变体可以通过以下方式实现 使用技术将 (zk-)rollups 或 Validium 中的证明替换为 TEE 证明 来自 [80]。 与 rollups 和 Validium 中使用的零知识证明相比,TEE 更 性能更高。与阈值签名相比,TEE 消除了以下复杂性: 生成阈值 ECDSA 签名,因为原则上只需要一个 TEE 参与。然而,使用 TEE 确实会引入额外的依赖于硬件的信任假设。人们还可以将 TEE 与阈值签名结合起来以创建弹性 防止一小部分 TEE 实例受到损害,尽管这种保护措施 重新引入了生成阈值 ECDSA 签名的复杂性。 额外的灵活性: 可以通过以下方式改进这些同步选项以提供更大的灵活性。 • 灵活的触发:TEF 应用程序可以确定触发条件 同步被触发。例如,同步可以是基于批处理的,例如,在 每 N 个交易、基于时间的交易(例如每 10 个区块)或基于事件的交易(例如)发生 每当目标资产价格大幅变动时。 • 部分同步:这是可能的,并且在某些情况下是可取的(例如,对于 rollups, 部分同步可以减少延迟)以提供小数据的快速同步 状态量,可能仅定期执行完全同步。例如, exect 可以通过更新 SCa 中用户的余额来批准提款请求 无需另外更新 MAINCHAIN 状态。 6.4 重组 由于网络不稳定甚至 51% 攻击而导致的区块链重组 可能对主链的完整性构成威胁。在实践中,对手已经使用了 他们发起双花攻击[34]。虽然此类针对主要区块链的攻击 安装具有挑战性,但它们对于某些链条 [88] 仍然可行。 因为它独立于主链运行,所以 DON 提供了有趣的功能 观察并提供一些针对与相关重组相关的保护的可能性 攻击。 例如,DON 可以向主链上的依赖合约 SC 报告某个阈值长度 τ 的竞争分叉的存在。 DON 还可以 12 补充细节可见附录 B.2.1。他们不需要理解。
在 PoW 或 PoS 设置中提供此类分叉存在的证据。的 合约 SC 可以实施适当的防御行动,例如在一段时间内暂停进一步的交易执行(例如,允许交易所将双花列入黑名单) 资产)。请注意,尽管对手发起 51% 攻击可以寻求审查 来自 DON 的报告,SC 的一项对策是要求来自 DON 的定期报告 DON 为了处理交易(即心跳)或需要新的报告 验证高价值交易。 虽然此类分叉警报原则上是 DON 可以提供的一般服务 出于多种目的中的任何一个,我们的计划是将它们纳入 TEF。
Minimisasi Kepercayaan
Sebagai sistem yang terdesentralisasi dengan partisipasi dari berbagai entitas yang heterogen, Jaringan Chainlink memberikan perlindungan yang kuat terhadap kegagalan dalam keaktifan (ketersediaan) dan keamanan (integritas laporan). Namun, sebagian besar sistem desentralisasi memiliki perbedaan sejauh mana komponen-komponen penyusunnya terdesentralisasi. Ini Hal ini berlaku bahkan pada sistem yang besar, dimana desentralisasi terbatas di kalangan penambang [32] dan perantara [51] telah lama hadir. Tujuan dari setiap upaya desentralisasi adalah minimalisasi kepercayaan: Kami berupaya untuk mengurangi dampak buruk dari korupsi atau kegagalan sistemik dalam jaringan Chainlink, meskipun demikian karena DON yang berbahaya. Prinsip panduan kami adalah Prinsip Hak Istimewa Terkecil [197]. Komponen sistem dan aktor dalam sistem harus memiliki hak istimewa yang dibatasi secara ketat untuk memungkinkan hanya keberhasilan penyelesaian peran yang ditugaskan kepada mereka. Di sini kami memaparkan beberapa mekanisme konkret yang dapat diterapkan oleh Chainlink dalam upayanya menuju minimalisasi kepercayaan yang semakin besar. Kami mengkarakterisasi mekanisme ini dalam istilah dari lokus, yaitu komponen sistem, di mana mereka di-root, ditunjukkan pada Gambar. 14. Kita alamat setiap lokus dalam subbagian masing-masing. 7.1 Otentikasi Sumber Data Model operasi saat ini untuk oracles dibatasi oleh fakta bahwa sedikit sumber data menandatangani secara digital data yang mereka hilangkan, sebagian besar karena TLS tidak menandatangani secara asli data. TLS memang menggunakan tanda tangan digital dalam protokol “jabat tangan” (untuk menetapkan kunci bersama antara server dan klien). Server yang mendukung HTTPS memiliki sertifikat pada kunci publik yang pada prinsipnya dapat berfungsi untuk menandatangani data, tetapi umumnya tidak digunakan sertifikat ini untuk mendukung penandatanganan data. Akibatnya, keamanan DON, sebagai di jaringan oracle saat ini, bergantung pada oracle node yang setia menyampaikan data dari suatu data sumber kontrak. Komponen penting jangka panjang dari visi kami untuk meminimalkan kepercayaan di Chainlink melibatkan autentikasi sumber data yang lebih kuat melalui dukungan alat dan standar untuk penandatanganan data. Penandatanganan data dapat membantu menegakkan jaminan integritas menyeluruh. Pada prinsipnya, jika suatu kontrak menerima sebagai masukan sepotong data D yang ditandatangani langsung oleh suatu data
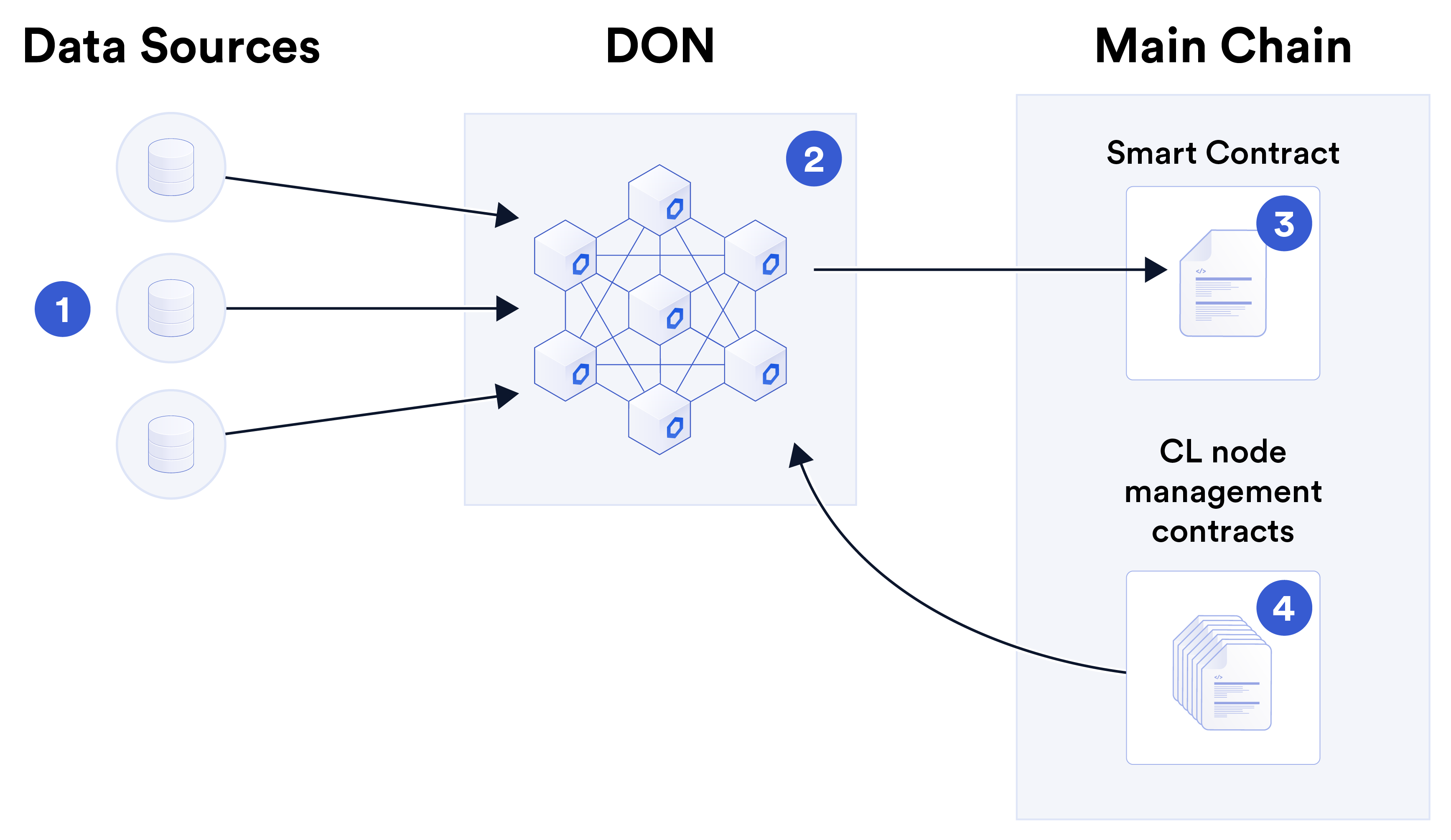
Gambar 14: Lokasi mekanisme minimalisasi kepercayaan yang dibahas pada bagian ini. 1⃝Data sumber menyediakan data ke 2⃝DON, yang menyampaikan fungsi data ke dependen 3⃝smart contract. Selain itu, jaringan DON atau oracle mencakup 4⃝node manajemen smart contracts di MAINCHAIN untuk, misalnya, node kompensasi, penjaga rel, dan sebagainya. sumber, maka jaringan oracle tidak dapat diutak-atik D. Berbagai hal yang menggembirakan upaya untuk memungkinkan penandatanganan data telah muncul, termasuk OpenID Connect, yang dirancang terutama untuk otentikasi pengguna [9], TLS-N, sebuah proyek akademis yang bertujuan untuk itu memperpanjang TLS [191] dengan menggunakan kembali sertifikat TLS, dan Ekstensi Bukti TLS [63]. Meskipun OpenID Connect telah melihat beberapa adopsi, TLS Evidence Extensions dan TLS-N belum diadopsi. Cara potensial lain untuk autentikasi sumber data adalah dengan menggunakan milik penerbit Pertukaran HTTP yang ditandatangani (SXG) [230], yang dapat disimpan dalam cache di jaringan pengiriman konten sebagai bagian dari protokol Accelerated Mobile Pages (AMP) [225]. Browser seluler Chrome menampilkan konten dari SXG yang di-cache AMP seolah-olah konten tersebut disajikan domain jaringan milik penerbitnya, bukan domain server cache. Insentif pencitraan merek ini, ditambah dengan relatif mudahnya mengaktifkannya menggunakan layanan seperti URL Asli CloudFlare [83] dan amppackager Google [124], dapat menyebabkan penerapan SXG secara luas dalam konten berita yang di-cache, yang akan memungkinkan sistem yang sederhana dan tahan terhadap gangguan. cara bagi Chainlink oracles untuk memicu peristiwa yang layak diberitakan yang dilaporkan di SXG yang valid. Meskipun SXG yang di-cache AMP dari penerbit berita tidak akan berguna untuk tempo tinggi aplikasi seperti laporan data perdagangan, mereka bisa menjadi sumber yang aman untuk kustom kontrak yang berkaitan dengan peristiwa dunia nyata seperti cuaca ekstrem atau hasil pemilu. Kami percaya bahwa penerapan yang sederhana, alat yang matang, dan fleksibilitas akan sangat penting mempercepat penandatanganan sumber data. Mengaktifkan penyedia data untuk menggunakan Chainlink node sebagai front end API yang diautentikasi tampaknya merupakan pendekatan yang menjanjikan. Kami bermaksud untuk membuatpilihan bagi node untuk berfungsi dalam mode ini, dengan atau tanpa partisipasi dalam jaringan sebagai oracle sepenuhnya. Kami menyebut kemampuan ini sebagai asal data yang diautentikasi (LALU). Dengan menggunakan Chainlink node dengan ADO, sumber data akan mendapatkan keuntungan dari pengalaman dan alat yang dikembangkan komunitas Chainlink dalam menambahkan digital kemampuan penandatanganan ke rangkaian API off-chain yang ada. Haruskah mereka memilih lari node mereka sebagai oracles, mereka juga dapat membuka potensi aliran pendapatan baru dengan model yang sama dengan penyedia data yang ada, misalnya Kraken [28], Kaiko [140], dan lainnya, yang menjalankan Chainlink node untuk menjual data API secara berantai. 7.1.1 Keterbatasan Asal Data yang Diautentikasi Penandatanganan digital oleh sumber data, meskipun dapat membantu memperkuat autentikasi, tidaklah cukup untuk mencapai semua tujuan keamanan alami atau operasional dari oracle jaringan. Untuk memulainya, bagian data D tertentu masih harus disampaikan secara kuat dan tepat waktu cara dari sumber data ke smart contract atau konsumen data lainnya. Artinya, bahkan di dalam pengaturan ideal di mana semua data ditandatangani menggunakan kunci yang telah diprogram menjadi dependen kontrak, DON masih diperlukan untuk mengomunikasikan data secara andal dari sumber untuk kontrak. Selain itu, ada sejumlah kasus di mana kontrak atau oracle-data lainnya konsumen menginginkan akses ke keluaran terotentikasi dari berbagai fungsi yang dihitung sumber data karena dua alasan utama: • Kerahasiaan: API sumber data mungkin menyediakan data sensitif atau kepemilikan yang perlu disunting atau dibersihkan sebelum dapat dilihat publik secara berantai. Namun, modifikasi apa pun pada data yang ditandatangani akan membuat tanda tangan menjadi tidak valid. Letakkan yang lain cara, ADO naif dan sanitasi data tidak kompatibel. Kami tunjukkan pada Contoh 3 bagaimana keduanya dapat didamaikan melalui bentuk ADO yang ditingkatkan. • Kesalahan sumber data: Kesalahan dan kegagalan dapat mempengaruhi sumber data, dan tanda tangan digital tidak mengatasi masalah tersebut. Sejak awal [98], Chainlink telah sudah mencakup mekanisme untuk memperbaiki kesalahan tersebut: redundansi. Laporan yang dikeluarkan oleh jaringan oracle biasanya mewakili gabungan beberapa data sumber. Kami sekarang mendiskusikan skema yang sedang kami eksplorasi dalam pengaturan ADO untuk meningkatkan kerahasiaan sumber data dan menggabungkan data dari berbagai sumber dengan aman. 7.1.2 Kerahasiaan Sumber data mungkin tidak mengantisipasi dan menyediakan keseluruhan API yang diinginkan oleh pengguna. Secara khusus, pengguna mungkin ingin mengakses data yang telah diproses sebelumnya untuk membantu memastikan kerahasiaan. Contoh berikut menggambarkan masalahnya.Contoh 3. Alice ingin mendapatkan pernyataan kredensial identitas terdesentralisasi (DID). bahwa dia berusia di atas 18 tahun (dan dengan demikian, misalnya, dapat mengambil pinjaman). Untuk melakukan jadi, dia perlu membuktikan fakta tentang usianya kepada penerbit kredensial DID. Alice berharap dapat menggunakan data dari Departemen Kendaraan Bermotor (DMV) negara bagiannya situs web untuk tujuan tersebut. DMV memiliki catatan tanggal lahirnya dan akan mengeluarkan a pengesahan A yang ditandatangani secara digital dengan bentuk sebagai berikut: A = {Nama: Alice, DoB: 16/02/1999}. Dalam contoh ini, pengesahan A mungkin cukup bagi Alice untuk membuktikan DID penerbit kredensial bahwa dia berusia di atas 18 tahun. Tapi itu tidak perlu membocorkan informasi sensitif: milik Alice DoB yang tepat. Idealnya, yang diinginkan Alice dari DMV adalah tanda tangan di a pernyataan sederhana A′ bahwa “Alice berusia di atas 18 tahun.” Dengan kata lain, dia menginginkannya keluaran suatu fungsi G pada tanggal lahirnya X, dimana (secara informal), A′ = G(X) = Benar jika Tanggal Saat Ini −X ≥18 tahun; jika tidak, G(X) = Salah. Untuk menggeneralisasi, Alice ingin dapat meminta tanda tangan dari sumber data pengesahan A′ dalam bentuk: A′ = {Nama: Alice, Fungsi:G(X), Hasil: Benar}, di mana G(X) menunjukkan spesifikasi fungsi G dan masukannya X. Kita bayangkan bahwa pengguna harus dapat memberikan G(X) yang diinginkan sebagai masukan dengan permintaannya untuk a pengesahan yang sesuai A′. Perhatikan bahwa pengesahan sumber data A′ harus menyertakan spesifikasi G(X) hingga memastikan bahwa A′ ditafsirkan dengan benar. Dalam contoh di atas, G(X) mendefinisikan maknanya dari nilai Boolean dalam A′ dan dengan demikian True menandakan subjek pengesahan berusia di atas 18 tahun. Kami mengacu pada kueri fleksibel di mana pengguna dapat menentukan G(X) sebagai kueri fungsional. Untuk mendukung kasus penggunaan seperti itu di Contoh 3, serta yang melibatkan kueri langsung dari kontrak, kami bermaksud menyertakan dukungan untuk pertanyaan fungsional yang melibatkan fungsi sederhana G sebagai bagian dari ADO. 7.1.3 Menggabungkan Data Sumber Untuk mengurangi biaya on-chain, kontrak umumnya dirancang untuk menggunakan data gabungan dari berbagai sumber, seperti yang diilustrasikan pada contoh berikut. Contoh 4 (Medianisasi data harga). Untuk memberikan umpan harga, yaitu nilai satu aset (misalnya, ETH) sehubungan dengan yang lain (misalnya, USD), jaringan oracle umumnya akan memperoleh harga saat ini dari sejumlah sumber, seperti bursa. Jaringan oracle biasanya mengirimkan ke kontrak dependen SC median dari nilai-nilai ini. Dalam lingkungan dengan penandatanganan data, jaringan oracle yang berfungsi dengan benar diperoleh dari sumber data S = {S1, . . . , SnS} barisan nilai V = {v1, v2, . . . , vnS} dari nS sumber dengan tanda tangan spesifik sumber yang menyertainya Σ = {σ1, σ2, . . . , σnS}. Setelah memverifikasi tanda tangan, ia mengirimkan harga v = median(V ) ke SC.Sayangnya, tidak ada cara sederhana bagi jaringan oracle untuk mengirimkan median nilai v dalam Contoh 4 hingga SC bersama dengan bukti singkat σ∗bahwa v dihitung dengan benar atas input yang ditandatangani. Pendekatan yang naif adalah dengan menyandikan kunci publik semua sumber data nS di SC. Jaringan oracle kemudian akan menyampaikan (V, Σ) dan memungkinkan SC menghitung median V . Namun hal ini akan menghasilkan bukti σ dengan ukuran O(nS)—yakni, σ∗tidak akan ringkas. Hal ini juga akan menimbulkan biaya bahan bakar yang tinggi bagi SC, yang harus memverifikasi semua tanda tangan di dalamnya Σ. Sebaliknya, penggunaan SNARK memungkinkan bukti ringkas tentang kombinasi nilai sumber yang diautentikasi dengan benar. Ini mungkin bisa dilakukan dalam praktiknya, tetapi bebannya cukup tinggi biaya komputasi pada peribahasa, dan biaya bahan bakar yang agak tinggi pada rantai. Penggunaan Town Crier juga merupakan suatu kemungkinan, namun membutuhkan penggunaan TEE, yang tidak cocok untuk semua orang model kepercayaan pengguna. Konsep yang berguna untuk menyusun solusi terhadap masalah umum penandatanganan data gabungan dari sumber adalah alat kriptografi yang dikenal sebagai tanda tangan fungsional [59, 132]. Singkatnya, tanda tangan fungsional memungkinkan penandatangan untuk mendelegasikan kemampuan penandatanganan, sedemikian rupa penerima delegasi hanya dapat menandatangani pesan dalam rentang fungsi F yang dipilih oleh penandatangan. Kami tunjukkan di Lampiran D bagaimana batasan fungsional ini dapat berfungsi untuk membatasi rentang nilai laporan yang dikeluarkan oleh DON sebagai fungsi dari nilai yang ditandatangani oleh sumber data. Kami juga memperkenalkan primitif baru, yang disebut tanda tangan fungsional terdiskritisasi, yang mencakup persyaratan akurasi yang lebih longgar, namun berpotensi jauh lebih berkinerja. daripada pendekatan seperti SNARK. Masalah menggabungkan sumber data dengan cara yang mencakup otentikasi sumber keluaran juga berlaku untuk agregator data, misalnya, CoinCap, CoinMarketCap, CoinGecko, CryptoCompare, dll., yang memperoleh data dari berbagai bursa, yaitu mereka bobot berdasarkan volume, menggunakan metodologi yang dalam beberapa kasus dipublikasikan dan dalam kasus lain merupakan hak milik. Agregator yang ingin mempublikasikan nilai dengan otentikasi sumber menghadapi tantangan yang sama dengan kumpulan node yang digabungkan sumber data. 7.1.4 Pengolahan Data Sumber smart contract yang canggih cenderung bergantung pada statistik agregat khusus sumber data primer, seperti volatilitas dalam riwayat harga terkini pada banyak aset, atau teks dan foto dari berita tentang peristiwa terkait. Karena komputasi dan bandwidth relatif murah dalam DON, statistik ini— bahkan model pembelajaran mesin yang kompleks dengan banyak masukan—dapat diproses secara ekonomis, selama nilai keluaran apa pun yang ditujukan untuk blockchain cukup ringkas. Untuk pekerjaan yang intensif secara komputasi di mana DON pesertanya mungkin berbeda pandangan mengenai masukan yang kompleks, putaran komunikasi ekstra antara peserta DON mungkin diperlukan untuk menetapkan konsensus mengenai masukan sebelum menghitung hasilnya. Selama nilai akhir sepenuhnya ditentukan oleh masukan, setelah konsensus masukan tercapai, masing-masing pihak dapat dengan mudah menghitung nilainya dan menyebarkannya ke pihak lain.peserta dengan sebagian tanda tangan mereka, atau mengirimkannya ke agregator. 7.2 DON Minimisasi Kepercayaan Kami membayangkan dua cara utama untuk meminimalkan kepercayaan yang diberikan pada komponen DON: klien failover dan laporan minoritas. 7.2.1 Klien Kegagalan Model permusuhan dalam literatur kriptografi dan sistem terdistribusi biasanya pertimbangkan musuh yang mampu merusak (yaitu, membahayakan) subset node, misalnya, kurang dari sepertiga untuk banyak protokol BFT. Namun hal ini umumnya diamati, bahwa jika semua node menjalankan perangkat lunak yang sama, musuh yang mengidentifikasi eksploitasi fatal dapat melakukannya pada prinsipnya mengkompromikan semua node secara bersamaan. Pengaturan ini sering terjadi disebut sebagai monokultur perangkat lunak [47]. Berbagai usulan untuk mendiversifikasi perangkat lunak dan konfigurasi perangkat lunak secara otomatis telah diajukan untuk mengatasi masalah ini, misalnya, [47, 113]. Seperti disebutkan dalam [47], namun, keragaman perangkat lunak adalah masalah yang kompleks dan memerlukan pertimbangan yang cermat. Diversifikasi perangkat lunak, misalnya, dapat menghasilkan keamanan yang lebih buruk dibandingkan monokultur meningkatkan permukaan serangan sistem dan dengan demikian kemungkinan vektor serangannya melebihi manfaat keamanan yang ditawarkannya. Kami percaya bahwa dukungan untuk klien failover yang kuat—yaitu klien ke node mana dapat beralih ketika menghadapi peristiwa bencana—merupakan bentuk yang sangat menarik diversifikasi perangkat lunak. Klien failover tidak menambah jumlah vektor potensial serangan, karena mereka tidak digunakan sebagai perangkat lunak arus utama. Mereka menawarkan manfaat yang jelas, namun, sebagai garis pertahanan kedua. Kami bermaksud untuk mendukung klien failover dalam DONs sebagai cara utama untuk mengurangi ketergantungan mereka akan keamanan pada satu klien. Chainlink sudah memiliki sistem klien failover yang kuat. Pendekatan kami melibatkan pemeliharaan versi klien sebelumnya yang telah teruji pertempuran. Saat ini, misalnya, Chainlink node dengan Off-Chain Reporting (OCR) sebagai klien utamanya menyertakan dukungan untuk sistem FluxMonitor Chainlink sebelumnya jika diperlukan. Telah digunakan untuk beberapa orang kali ini, FluxMonitor telah menerima audit keamanan dan pengujian lapangan. Ini memberikan hal yang sama fungsionalitas seperti OCR, hanya dengan biaya lebih tinggi—biaya hanya dikeluarkan berdasarkan kebutuhan. 7.2.2 Laporan Minoritas Mengingat jumlah kelompok minoritas yang cukup besar Ominoritas—sebagian kecil dari simpul jujur yang mengamati penyimpangan yang dilakukan oleh mayoritas—akan bermanfaat jika kelompok tersebut menghasilkan minoritas laporan. Ini adalah laporan atau tanda paralel, yang diteruskan ke kontrak SC on-chain yang bergantung oleh Ominoritas. SC dapat menggunakan bendera ini sesuai dengan kebijakan khusus kontraknya sendiri. Misalnya, untuk kontrak yang mengutamakan keselamatan daripada keaktifan atau daya tanggap, laporan minoritas mungkin menyebabkan kontrak meminta laporan tambahan. dari DON lain, atau memicu pemutus arus (lihat bagian selanjutnya).Laporan dari kelompok minoritas dapat memainkan peranan penting bahkan ketika kelompok mayoritas jujur, karena skema agregasi laporan apa pun, meskipun menggunakan tanda tangan fungsional, harus dilakukan beroperasi dengan cara ambang batas, untuk memastikan ketahanan terhadap oracle atau kegagalan data. Di dengan kata lain, laporan yang valid harus dapat dihasilkan berdasarkan masukan dari kS < nS oracles, untuk beberapa ambang batas kS. Ini berarti DON yang rusak memiliki beberapa kebebasan dalam memanipulasi nilai laporan dengan memilih nilai kS yang diinginkan di antara nilai-nilai tersebut nS dilaporkan dalam V dengan set lengkap oracles, meskipun semua sumber jujur. Misalnya nS = 10 dan kS = 7 dalam sistem yang menggunakan fungsional tanda tangan untuk mengautentikasi perhitungan median di atas V untuk harga USD ETH. Misalkan lima sumber melaporkan harga \(500, while the other five report \)1000. Kemudian dengan memediasi 7 laporan terendah, DON dapat menghasilkan nilai valid v = $500, dan dengan memediasi nilai tertinggi, ia dapat menghasilkan v = $1000. Dengan menyempurnakan protokol DON sehingga semua node mengetahui data mana yang berada tersedia, dan data mana yang digunakan untuk membuat laporan, node dapat mendeteksi dan menandainya kecenderungan yang signifikan secara statistik untuk lebih menyukai satu set laporan dibandingkan yang lain, dan menghasilkan sebagai hasilnya, laporan minoritas. 7.3 Rel Penjaga Model kepercayaan kami untuk DONs memperlakukan MAINCHAIN sebagai keamanan yang lebih tinggi, hak istimewa yang lebih tinggi sistem dari DONs. (Meskipun model kepercayaan ini mungkin tidak selalu benar, model ini lebih mudah untuk mengadaptasi mekanisme yang dihasilkan pada situasi di mana DON adalah keamanan yang lebih tinggi platform daripada sebaliknya.) Oleh karena itu, strategi minimalisasi kepercayaan yang alami melibatkan penerapan mekanisme pemantauan dan pengamanan kegagalan di smart contracts—baik di front end MAINCHAIN untuk DON atau langsung dalam kontrak tanggungan SC. Kami menyebut mekanisme ini sebagai pagar pengaman, dan sebutkan beberapa hal terpenting di sini: • Pemutus sirkuit: SC dapat menjeda atau menghentikan pembaruan status sebagai fungsi dari salah satu karakteristik pembaruan status itu sendiri (misalnya, varian besar di seluruh sekuensial laporan) atau berdasarkan masukan lainnya. Misalnya, pemutus arus mungkin tersandung kasus di mana laporan oracle sangat bervariasi dari waktu ke waktu. Pemutus arus mungkin juga tersandung oleh laporan minoritas. Dengan demikian, pemutus sirkuit dapat mencegah DONs dari membuat laporan yang sangat salah. Pemutus sirkuit dapat memberikan waktu untuk mempertimbangkan intervensi tambahan atau dilatih. Salah satu intervensi tersebut adalah pintu keluar darurat. • Pintu keluar untuk melarikan diri: Dalam keadaan yang merugikan, seperti yang diidentifikasi oleh sekelompok penjaga, pemegang token komunitas, atau badan pengawas lainnya, sebuah kontrak dapat diperlukan fasilitas darurat terkadang disebut pintu keluar darurat [163]. Sebuah pintu keluar menyebabkan SC dimatikan dengan cara tertentu dan/atau berakhir tertunda dan mungkin transaksi masa depan. Misalnya, ia dapat mengembalikan dana yang disimpan kepada pengguna [17]),dapat mengakhiri ketentuan kontrak [162], atau dapat membatalkan transaksi yang tertunda dan/atau di masa depan [173]. Escape hatch dapat digunakan dalam semua jenis kontrak, tidak hanya salah satu yang bergantung pada DON, namun menarik sebagai penyangga potensial terhadap DON penyimpangan. • Failover: Dalam sistem di mana SC bergantung pada DON untuk layanan penting, SC dapat menyediakan mekanisme failover yang memastikan kelanjutan layanan bahkan dalam kasus DON kegagalan atau perilaku buruk. Misalnya, dalam TEF (Bagian 6), kontrak jangkar SCa dapat menyediakan antarmuka ganda di mana keduanya on-chain dan antarmuka eksekusi off-chain didukung untuk operasi penting tertentu (misalnya, penarikan), atau untuk transaksi biasa, dengan penundaan yang sesuai untuk mencegah DON transaksi berjalan di muka. Jika sumber data menandatangani data, pengguna dapat melakukannya juga memberikan laporan kepada SCa ketika DON gagal melakukannya. Bukti penipuan, seperti yang diusulkan untuk berbagai bentuk rollup optimis (lihat Bagian 6.3), memiliki rasa yang serupa dan saling melengkapi dengan mekanisme yang kami sebutkan di atas. Mereka juga menyediakan bentuk pemantauan dan perlindungan on-chain terhadap potensi kegagalan komponen sistem off-chain. 7.4 Tata Kelola yang Meminimalkan Kepercayaan Seperti semua sistem desentralisasi, jaringan Chainlink memerlukan mekanisme tata kelola untuk menyesuaikan parameter dari waktu ke waktu, merespons keadaan darurat, dan memandu evolusinya. Beberapa dari mekanisme ini saat ini berada di MAINCHAIN, dan mungkin akan terus berlanjut melakukannya bahkan dengan penerapan DONs. Salah satu contohnya adalah mekanisme pembayaran untuk oracle penyedia node (DON node). DON kontrak ujung depan di MAINCHAIN mengandung mekanisme tambahan, seperti rel pengaman, yang mungkin dikenakan secara berkala modifikasi. Kami memperkirakan ada dua jenis mekanisme tata kelola: evolusioner dan darurat. Tata kelola yang evolusioner: Banyak modifikasi pada ekosistem Chainlink adalah sedemikian rupa sehingga implementasinya tidak menjadi hal yang mendesak: Peningkatan kinerja, peningkatan fitur, peningkatan keamanan (tidak mendesak), dan sebagainya. Seiring dengan semakin banyaknya Chainlink yang bergerak ke arah lebih banyak peserta dalam tata kelolanya, kami memperkirakan akan banyak atau sebagian besar perubahan tersebut harus diratifikasi oleh komunitas tertentu DON yang terkena dampak oleh mereka perubahan. Untuk sementara, dan mungkin pada akhirnya sebagai mekanisme paralel, kami yakin bahwa gagasan tentang hak istimewa yang paling tidak bersifat sementara dapat menjadi sarana yang berguna dalam menerapkan tata kelola yang evolusioner. Sederhananya, idenya adalah agar perubahan diterapkan secara bertahap dan memastikan masyarakat mempunyai kesempatan untuk menanggapinya. Misalnya saja migrasi ke tempat baru Kontrak MAINCHAIN dapat dibatasi sehingga kontrak baru harus diterapkan setidaknya tiga puluh hari sebelum aktivasi.Tata kelola darurat: Kerentanan yang dapat dieksploitasi atau dieksploitasi di MAINCHAIN kontrak atau bentuk kegagalan kelangsungan hidup atau keselamatan lainnya mungkin memerlukan intervensi segera untuk memastikan dampak buruknya. Tujuan kami adalah untuk mendukung multisig mekanisme intervensi di mana, untuk memastikan terhadap penyimpangan yang dilakukan oleh organisasi mana pun, penandatangan akan tersebar di seluruh organisasi. Memastikan ketersediaan penanda tangan yang konsisten dan akses tepat waktu ke rantai komando yang sesuai untuk otorisasi keadaan darurat perubahan jelas memerlukan perencanaan operasional yang cermat dan peninjauan rutin. Ini tantangannya serupa dengan tantangan yang terlibat dalam pengujian respons insiden keamanan siber lainnya kemampuan [134], dengan kebutuhan serupa untuk mengatasi masalah umum seperti penurunan kewaspadaan [223]. Tata kelola DON berbeda dengan sistem desentralisasi pada umumnya tingkat potensi heterogenitas. Setiap DON mungkin memiliki sumber data, executable, persyaratan tingkat layanan yang berbeda seperti waktu aktif, dan pengguna. Jaringan Chainlink mekanisme tata kelola harus cukup fleksibel untuk mengakomodasi variasi tersebut tujuan dan parameter operasional. Kami secara aktif mengeksplorasi ide-ide desain dan merencanakannya mempublikasikan penelitian tentang topik ini di masa depan. 7.5 Infrastruktur Kunci Publik Dengan desentralisasi yang progresif maka diperlukan identifikasi yang kuat mengenai hal ini peserta jaringan, termasuk DON node. Secara khusus, Chainlink membutuhkan yang kuat Infrastruktur Kunci Publik (PKI). PKI adalah sistem yang mengikat kunci identitas. Untuk Misalnya, PKI mendasari sistem koneksi aman (TLS) Internet: Kapan Anda terhubung ke situs web melalui HTTPS (mis., https://www.chainlinklabs.com) dan a kunci muncul di browser Anda, itu berarti kunci publik pemilik domain memilikinya telah terikat pada pemiliknya oleh suatu otoritas—khususnya, melalui tanda tangan digital yang disebut sertifikat. Sistem hierarki otoritas sertifikat (CA), yang otoritas akar tingkat atasnya tertanam dalam browser populer, membantu memastikan bahwa sertifikat dikeluarkan hanya untuk pemilik sah domain. Kami berharap Chainlink pada akhirnya akan menggunakan layanan nama yang terdesentralisasi, awalnya Ethereum Name Service (ENS) [22], sebagai landasan PKI kita. Sebagai Sesuai dengan namanya, ENS dianalogikan dengan DNS, Domain Name System yang memetakan (dapat dibaca manusia) nama domain ke alamat IP di internet. Namun, ENS malah memetakan nama Ethereum yang dapat dibaca manusia ke alamat blockchain. Karena ENS beroperasi pada Ethereum blockchain, kecuali kompromi utama, merusaknya namespace pada prinsipnya sama sulitnya dengan merusak kontrak yang mengelolanya dan/atau blockchain yang mendasarinya. (DNS, sebaliknya, secara historis rentan untuk spoofing, pembajakan, dan serangan lainnya.) Kami telah mendaftarkan data.eth dengan ENS di mainnet Ethereum, dan bermaksud untuk melakukannya menetapkannya sebagai namespace root di mana identitas layanan data oracle dan entitas jaringan Chainlink lainnya berada. Domain di ENS bersifat hierarkis, artinya setiap domain dapat berisi referensi ke nama lain di bawahnya. Subdomain di ENS dapat berfungsi sebagai cara untuk mengatur danmendelegasikan kepercayaan. Peran utama data.eth adalah sebagai layanan direktori on-chain umpan data. Secara tradisional, pengembang dan pengguna oracles telah menggunakan sumber off-chain (misalnya, situs web seperti docs.chain.link atau data.chain.link, atau jejaring sosial seperti Twitter) untuk mempublikasikan dan mendapatkan oracle alamat data feed (seperti harga ETH-USD pakan). Dengan namespace root yang sangat tepercaya seperti data.eth, dimungkinkan untuk membuat pemetaan eth-usd.data.eth ke, misalnya, alamat smart contract dari agregator jaringan oracle on-chain untuk umpan harga ETH-USD. Ini akan terjadi buat jalur aman bagi siapa pun untuk merujuk ke blockchain sebagai sumber kebenaran umpan data dari pasangan harga/nama tersebut (ETH-USD). Konsekuensinya, penggunaan ENS seperti itu menyadari dua manfaat yang tidak tersedia di sumber data off-chain: • Keamanan yang kuat: Semua perubahan dan pembaruan pada domain dicatat secara permanen dan diamankan secara kriptografis, bukan alamat teks di situs web, yang mana tidak menikmati satu pun dari dua properti keamanan ini. • Propagasi on-chain otomatis: Pembaruan pada alamat dasar smart contract datafeed dapat memicu notifikasi yang disebarkan ke smart dependen kontrak dan dapat, misalnya, secara otomatis memperbarui kontrak yang bergantung padanya alamat baru.13 Namun, namespace seperti ENS tidak secara otomatis memvalidasi kepemilikan sah dari nama-nama yang ditegaskan. Jadi, misalnya, jika namespace menyertakan entri ⟨“Acme Oracle Node Co.”, tambahan⟩, kemudian pengguna memperoleh jaminan bahwa addr adalah milik penggugat nama Acme Oracle Node Co. Tanpa mekanisme tambahan seputar administrasi namespace, namun, ia tidak memperoleh jaminan bahwa nama tersebut adalah milik suatu entitas secara sah disebut Acme Oracle Node Co. dalam arti dunia nyata yang bermakna. Pendekatan kami terhadap validasi nama, yaitu memastikan kepemilikannya oleh entitas yang sesuai dan sah di dunia nyata, bergantung pada beberapa komponen. Hari ini, Chainlink Lab secara efektif bertindak sebagai CA untuk jaringan Chainlink. Sementara Chainlink Lab akan dilanjutkan untuk memvalidasi nama, PKI kita akan berkembang menjadi model yang lebih terdesentralisasi melalui dua cara: • Model web-of-trust: Model desentralisasi dari PKI yang hierarkis sering disebut sebagai web-of-trust.14 Varian-varian telah diusulkan sejak tahun 1990-an, misalnya, [98], dan sejumlah peneliti telah mengamati bahwa blockchains dapat memfasilitasi penggunaan gagasan tersebut, misalnya, [227] dengan mencatat sertifikat dalam sistem yang konsisten secara global buku besar. Kami sedang menjajaki varian model ini untuk memvalidasi identitas entitas di jaringan Chainlink dengan cara yang lebih terdesentralisasi. 13Kontrak yang bergantung secara opsional dapat mencakup penundaan yang telah ditentukan sebelumnya untuk memungkinkan inspeksi manual dan intervensi oleh administrator kontrak yang bergantung. 14Istilah yang diciptakan oleh Phil Zimmermann untuk PGP [238].• Tautan ke validasi data: Saat ini, sejumlah besar oracle data kinerja node terlihat secara on-chain, dan dengan demikian terikat secara arsip ke alamat node. Data tersebut dapat dipandang memperkaya identitas PKI dengan memberikan bukti sejarah partisipasinya (yang dapat diandalkan) dalam jaringan tersebut. Selain itu, alat untuk identitas terdesentralisasi berdasarkan node pengaktif DECO dan Town Crier [160] untuk mengumpulkan kredensial yang berasal dari data dunia nyata. Sebagai salah satu contoh saja, a operator node dapat melampirkan kredensial ke identitas PKI-nya yang membuktikan kepemilikan dari peringkat Dun dan Bradstreet. Bentuk validasi tambahan ini bisa suplemen staking dalam menciptakan jaminan keamanan jaringan. Node oracle dengan identitas dunia nyata yang mapan dapat dianggap memiliki kepentingan dalam suatu sistem yang berasal dari reputasinya. (Lihat Bagian 4.3 dan Bagian 9.6.3.) Persyaratan terakhir untuk Chainlink PKI adalah bootstrapping yang aman, yaitu, aman menerbitkan nama root untuk jaringan Chainlink, saat ini data.eth (secara analog untuk memasang kabel domain tingkat atas di browser). Dengan kata lain, bagaimana Chainlink pengguna tentukan bahwa data.eth memang merupakan domain tingkat teratas yang terkait dengan Chainlink proyek? Solusi untuk masalah ini untuk jaringan Chainlink memiliki banyak cabang dan mungkin melibatkan: • Menambahkan data TXT [224] ke data domain kami untuk chain.link yang menentukan data.eth sebagai domain root untuk ekosistem Chainlink. (Chainlink dengan demikian secara implisit memanfaatkan PKI untuk domain internet untuk memvalidasi domain root ENS-nya.) • Menautkan ke data.eth dari situs web Chainlink yang ada, misalnya, dari https://docs.chain.link. (Penggunaan PKI lainnya secara implisit untuk domain internet.) • Membuat penggunaan data.eth diketahui melalui berbagai dokumen, termasuk whitepaper ini. • Memposting data.eth secara publik di saluran media sosial kami, seperti Twitter, dan blog Chainlink [18]. • Menempatkan LINK dalam jumlah besar di bawah kendali alamat pendaftar yang sama sebagai data.eth.
信任最小化
作为一个由一组异构实体参与的去中心化系统, Chainlink 网络在活性(可用性)和安全性(报告完整性)方面提供了针对故障的强大保护。然而,大多数去中心化系统在以下方面有所不同: 它们的组成部分本身分散的程度。这个 即使对于大型系统也是如此,矿工之间的权力下放有限 [32] 和 中介 [51] 早已存在。 任何去中心化努力的目标都是信任最小化:我们寻求减少 Chainlink 网络内系统性腐败或故障的不利影响,即使如此 由于恶意 DON。我们的指导原则是最小特权原则 [197]。 系统内的系统组件和参与者应具有严格范围内的权限 只允许成功完成分配给他们的角色。 这里我们列出了 Chainlink 在其驱动中采用的几种具体机制 走向更大程度的信任最小化。我们用以下术语来描述这些机制 基因座,即它们所扎根的系统组件,如图 14 所示。 解决相应小节中的每个基因座。 7.1 数据源认证 oracles 当前的操作模型受到以下事实的限制:数据源很少 对他们忽略的数据进行数字签名,很大程度上是因为 TLS 本身并不签名 数据。 TLS 确实在其“握手”协议中使用了数字签名(以建立 服务器和客户端之间的共享密钥)。因此启用 HTTPS 的服务器拥有证书 原则上可以用于签署数据的公钥,但它们通常不使用 这些证书支持数据签名。因此,DON 的安全性为 在当今的 oracle 网络中,依赖于 oracle 节点忠实地从数据中继数据 合同来源。 我们在 Chainlink 中实现信任最小化愿景的一个重要长期组成部分涉及通过支持数据签名工具和标准来加强数据源身份验证。数据签名可以帮助实施端到端的完整性保证。 原则上,如果合约接受由数据直接签名的一段数据 D 作为输入
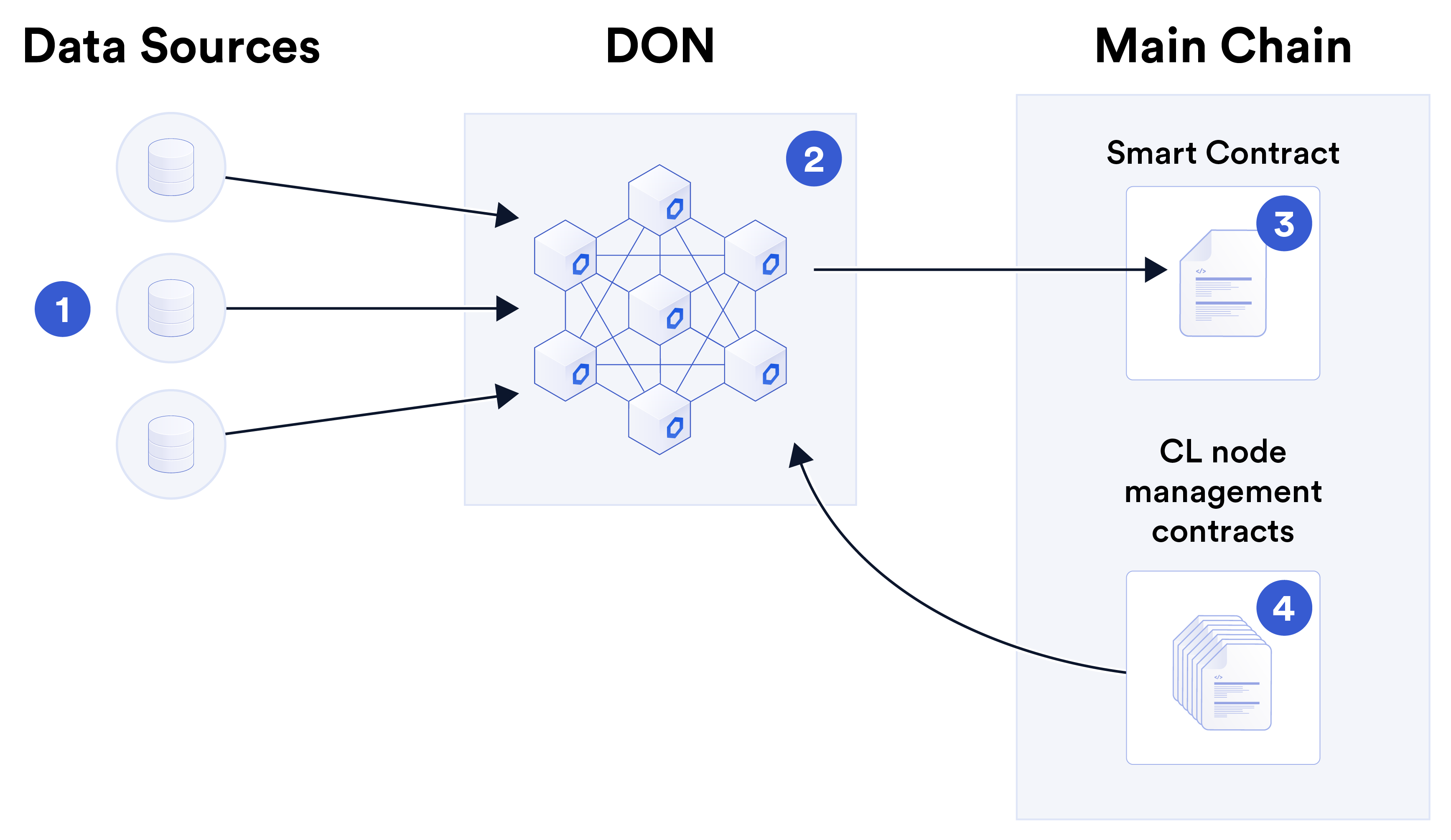
图 14:本节讨论的信任最小化机制的轨迹。 1⃝数据 源向 2⃝DON 提供数据,该 2⃝DON 将数据功能中继到依赖项 3⃝smart contract。 此外,DON 或 oracle 网络包括 4⃝节点 主链上的管理 smart contracts,例如补偿节点、保护 导轨等。 源,则 oracle 网络无法切实篡改 D. 各种鼓励 实现此类数据签名的努力已经出现,其中包括 OpenID Connect,它 主要设计用于用户身份验证[9],TLS-N,一个学术项目,旨在 通过重新利用 TLS 证书和 TLS 证据扩展 [63] 来扩展 TLS [191]。 尽管 OpenID Connect 已经得到了一些采用,但是 TLS 证据扩展 和 TLS-N 尚未得到采用。 数据源身份验证的另一个潜在途径是使用发布者自己的 签名 HTTP 交换 (SXG) [230],它们可以将其缓存在内容交付网络上,作为加速移动页面 (AMP) 协议 [225] 的一部分。 Chrome 移动浏览器显示 AMP 缓存的 SXG 中的内容,就好像它们是从 他们的发布者自己的网络域而不是缓存服务器域。这种品牌激励,加上使用 CloudFlare 的 Real URL [83] 和 Google 的 amppackager [124] 等服务相对容易地启用它,可能会导致 SXG 在缓存的新闻内容中得到广泛采用,这将实现简单、防篡改的功能。 Chainlink oracles 触发有效 SXG 中报告的有新闻价值的事件的方式。 虽然来自新闻出版商的 AMP 缓存 SXG 对于快节奏内容没有用 像交易数据报告这样的应用程序,它们可以成为自定义的安全来源 与极端天气或选举结果等现实世界事件相关的合同。 我们相信简单的部署、成熟的工具和灵活性对于 加速数据源签名。使数据提供者能够使用 Chainlink 节点作为 经过身份验证的 API 前端似乎是一种很有前途的方法。我们打算创建一个节点在此模式下运行的选项,无论是否参与网络 作为一个成熟的oracle。我们将此功能称为经过身份验证的数据源 (阿杜)。通过将 Chainlink 节点与 ADO 结合使用,数据源将能够受益 来自 Chainlink 社区在添加数字方面的经验和开发的工具 为其现有的链外 API 套件提供签名功能。他们是否应该选择跑步 他们的节点为 oracles,他们还可以开辟潜在的新收入来源 与现有数据提供商采用相同的模型,例如 Kraken [28]、Kaiko [140],以及 其他运行 Chainlink 节点来在链上出售 API 数据。 7.1.1 经过身份验证的数据来源的局限性 数据源的数字签名虽然可以帮助加强身份验证,但其本身不足以实现 oracle 的所有自然安全或操作目标 网络。 首先,给定的数据 D 仍必须以稳健且及时的方式中继 从数据源到 smart contract 或其他数据使用者的方式。也就是说,即使在 理想的设置,其中所有数据都使用预编程为依赖项的密钥进行签名 合同,仍然需要 DON 来可靠地从来源传递数据 到合同。 此外,在许多情况下,合同或其他 oracle-数据 消费者希望访问经过身份验证的各种函数计算的输出 源数据主要有两个原因: • 保密性:数据源 API 可能提供敏感或专有数据 在链上公开可见之前需要对其进行编辑或清理。 然而,对签名数据的任何修改都会使签名无效。再放一个 这样,简单的 ADO 和数据清理是不兼容的。我们在示例 3 中展示 如何通过增强形式的 ADO 协调两者。 • 数据源故障:错误和故障都会影响数据源,而数字签名无法解决这两个问题。自 [98] 成立以来,Chainlink 已 已经包含了一种修复此类故障的机制:冗余。 oracle 网络发布的报告通常代表多个网络的组合数据 来源。 现在我们讨论在 ADO 设置中探索的方案,以增强源数据的机密性并安全地组合来自多个源的数据。 7.1.2 保密性 数据源可能无法预测并提供所需的全部 API 由用户。 具体来说,用户可能希望访问预处理的数据以帮助确保 保密性。下面的例子说明了这个问题。示例 3. Alice 希望获得去中心化身份 (DID) 凭证 她已年满 18 岁(例如,因此可以申请贷款)。要做的事 因此,她需要向 DID 凭证颁发者证明有关她年龄的事实。 Alice 希望使用她所在州机动车辆管理局 (DMV) 的数据 网站为此目的。 DMV 有她的出生日期记录,并将发出 其上的数字签名证明 A 的形式如下: A = {姓名:Alice,DoB:02/16/1999}。 在此示例中,证明 A 可能足以让 Alice 向 DID 证明 凭证颁发者表示她已超过 18 岁。但这不必要地泄露了敏感信息:Alice 的 确切的 DoB。理想情况下,Alice 希望 DMV 提供的是在 简单陈述 A',“Alice 已年满 18 岁”。换句话说,她想要的是 函数 G 在她的生日 X 上的输出,其中(非正式地),A′ = G(X) = True if 当前日期−X ≥18 年;否则,G(X) = False。 概括而言,Alice 希望能够从数据源请求签名的 证明 A′ 的形式: A′ = {名称:Alice,功能:G(X),结果:True}, 其中 G(X) 表示函数 G 及其输入 X 的规范。我们设想 用户应该能够提供所需的 G(X) 作为她的请求的输入 相应的证明A′。 请注意,数据源的证明 A′ 必须包含规范 G(X) 确保 A′ 被正确解释。在上面的例子中,G(X)定义了含义 A′ 中的布尔值,因此 True 表示证明的主题 已年满 18 岁。 我们将用户可以指定 G(X) 的灵活查询称为函数查询。 为了支持示例 3 中的用例以及涉及查询的用例 直接来自合约,我们打算包括对涉及的功能查询的支持 作为 ADO 一部分的简单函数 G。 7.1.3 合并源数据 为了降低链上成本,合约通常被设计为消耗组合数据 来自多个来源,如以下示例所示。 示例 4(价格数据中值化)。提供价格信息,即一个的价值 资产(例如,ETH)相对于另一种资产(例如,美元),oracle 网络通常会 从多种来源(例如交易所)获取当前价格。 oracle 网络 通常将这些值的中值发送给从属合约 SC。 在具有数据签名的环境中,正常运行的 oracle 网络可以获得 来自数据源 S = {S1, . 。 。 , SnS} 值序列 V = {v1, v2, . 。 。 , vnS} 来自 带有特定源签名的 nS 源 Σ = {σ1, σ2, . 。 。 ,σnS}。之上 验证签名后,它将价格 v = mid(V ) 传输给 SC。不幸的是,没有简单的方法让 oracle 网络传输中值 将示例 4 中的 v 值传递给 SC,并提供 v 计算正确的简洁证明 σ 过度签名的输入。 一种简单的方法是在 SC 中对所有 nS 数据源的公钥进行编码。 然后 oracle 网络将中继 (V, Σ) 并允许 SC 计算 V 的中值。 然而,这将导致证明 σ 的大小为 O(nS),即 σ 不会简洁。 它还会给 SC 带来高昂的 Gas 成本,因为 SC 需要验证中的所有签名 Σ。 相比之下,使用 SNARK 可以简洁地证明正确组合的经过身份验证的源值。在实践中可能可行,但要求相当高 证明者的计算成本,以及链上较高的天然气成本。使用 Town Crier 也是一种可能性,但需要使用 TEE,这并不适合所有人 用户的信任模型。 一个有用的概念是一种称为功能签名的加密工具,它可以解决对来自源的组合数据进行签名的一般问题。 [59, 132]。 简而言之,功能签名允许签名者委托签名能力,这样 受委托者只能对签名者选择的函数F范围内的消息进行签名。 我们在附录 D 中展示了这个功能约束如何用于限制范围 DON 发出的报告值作为数据源签名值的函数。 我们还引入了一种新的原语,称为离散函数签名,它包括对准确性的宽松要求,但可能具有更高的性能 比 SNARK 等方法更有效。 以包括源身份验证的方式组合数据源的问题 输出也适用于数据聚合器,例如 CoinCap、CoinMarketCap、CoinGecko、 CryptoCompare 等,它们从多个交易所获取数据, 基于体积的重量,使用他们在某些情况下公开的方法 在其他情况下是专有的。希望发布值的聚合器 源认证面临与节点聚合相同的挑战 源数据。 7.1.4 处理源数据 复杂的 smart contract 可能依赖于自定义聚合统计数据 主要数据源,例如许多资产近期价格历史的波动性,或 相关事件新闻中的文字和照片。 由于 DON 中的计算和带宽相对便宜,因此这些统计数据 — 即使是具有许多输入的复杂机器学习模型,也可以经济地进行处理,只要指定给 blockchain 的任何输出值都足够简洁。 对于计算密集型工作,DON 参与者可能有不同的 对于复杂输入的看法,可能需要 DON 参与者之间进行额外的沟通,以便在计算结果之前就输入达成共识。 只要最终值完全由输入决定,一旦建立输入共识,每个参与者就可以简单地计算该值并将其广播给其他参与者参与者的部分签名,或将其发送给聚合器。 7.2 DON 信任最小化 我们设想了两种主要方法来最大限度地减少对 DON 组件的信任: 故障转移客户端和少数派报告。 7.2.1 故障转移客户端 密码学和分布式系统文献中的对抗模型通常 考虑一个能够破坏(即损害)节点子集的对手, 例如,对于许多 BFT 协议来说,不到三分之一。然而,人们普遍观察到, 如果所有节点都运行相同的软件,那么识别出致命漏洞的对手就可以 原则上或多或少同时危害所有节点。这个设置经常 称为软件单一文化 [47]。 为了解决这个问题,已经提出了自动多样化软件和软件配置的各种建议,例如[47, 113]。如 [47] 中所述, 然而,软件多样性是一个复杂的问题,需要仔细考虑。例如,如果软件多样化,可能会导致比单一文化更糟糕的安全性 增加系统的攻击面,从而增加其可能的攻击向量 它提供的安全优势。 我们相信,对强大的故障转移客户端(即节点的客户端)的支持 可以在面对灾难性事件时进行转换——是一种特别有吸引力的形式 软件多样化。故障转移客户端不会增加潜在向量的数量 攻击,因为它们没有部署为主线软件。他们提供了明显的好处, 然而,作为第二道防线。我们打算在 DONs 中支持故障转移客户端 减少安全对单个客户端的依赖的关键方法。 Chainlink 已经建立了一个强大的故障转移客户端系统。我们的方法 涉及维护以前的、经过实战检验的客户端版本。例如,今天,以链外报告(OCR)作为主要客户端的 Chainlink 节点包括支持 如果需要,可用于 Chainlink 之前的 FluxMonitor 系统。已经使用了一些 目前,FluxMonitor 已经接受了安全审核和现场测试。它提供了相同的 OCR 等功能,只是成本较高——仅根据需要产生成本。 7.2.2 少数派报告 给定足够大的少数集 Ominority(观察到大多数人不法行为的诚实节点的一小部分),这对他们生成少数派可能会有所帮助 报告。这是一个并行报告或标志,转发到链上的依赖合约 SC 由少数派。 SC 可以根据其自己的合约特定策略来使用该标志。 例如,对于安全性比活性或响应性更重要的合同,少数报告可能会导致合同要求补充报告 来自另一个 DON,或触发断路器(请参阅下一节)。即使大多数人是诚实的,少数派报告也可以发挥重要作用, 因为任何报告聚合方案,即使它使用功能签名,也必须 以阈值方式操作,以确保针对 oracle 或数据故障的恢复能力。在 换句话说,必须能够根据以下人员的输入生成有效的报告: kS < nS oracles,对于某个阈值 kS。 这意味着损坏的 DON 有一些 通过在其中选择首选 kS 值来操纵报告值的自由度 nS 在 V 中由全套 oracle 报告,即使所有来源都是诚实的。 例如,假设在使用泛函的系统中 nS = 10 且 kS = 7 签名以验证 ETH 美元价格 V 上中位数的计算。 假设五个来源报告的价格为 \(500, while the other five report \)1000。 然后通过对最低 7 个报告进行中值化,DON 可以输出有效值 v = $500, 通过对最高值进行中值化,可以输出 v = $1000。 通过增强 DON 协议,使所有节点都知道哪些数据是 以及哪些数据用于构建报告,节点可以检测并标记 倾向于一组报告而不是另一组报告的统计显着趋势,并产生 结果是一份少数派报告。 7.3 护栏 我们针对 DON 的信任模型将主链视为更高安全性、更高特权 系统比DONs。 (虽然这种信任模型可能并不总是成立,但它更容易 使生成的机制适应 DON 具有更高安全性的情况 平台,反之亦然。) 因此,自然的信任最小化策略涉及在 smart contract 中实施监控和故障安全机制——无论是在主链前端 对于 DON 或直接在从属合同 SC 中。我们将这些机制称为 护栏,并在此列举一些最重要的: • 断路器:SC 可以根据状态更新本身的特征(例如,顺序更新之间的较大差异)暂停或停止状态更新。 报告)或基于其他输入。例如,断路器可能会跳闸 oracle 报告随时间变化令人难以置信的情况。断路器可能 也会被少数派报告绊倒。因此,断路器可以防止 DONs 以免做出严重错误的报告。 断路器可以为考虑额外干预措施提供时间 或锻炼。其中一种干预措施是逃生舱口。 • 逃生舱口:在不利情况下,由一组托管人、社区 token 持有者或其他受托人团体确定,合同可以援引 有时称为逃生舱口 [163] 的紧急设施。逃生舱口 导致 SC 以某种方式关闭和/或终止挂起,并且可能 未来的交易。例如,它可能会将托管资金返还给用户[17]),可以终止合同条款[162],或者可以取消待处理和/或未来的交易[173]。逃生舱口可以部署在任何类型的合同中,而不仅仅是 依赖于 DON 的一个,但它们作为潜在的缓冲区很有趣 DON 渎职行为。 • 故障转移:在 SC 依赖 DON 提供基本服务的系统中,SC 可以提供故障转移机制来确保服务连续性,即使 在 DON 失败或行为不当的情况下。例如,在 TEF(第 6 节)中, 锚定合约SCa可以提供双接口,链上和链上都可以 某些关键操作支持链外执行接口(例如, 提款),或对于普通交易,有适当的延迟以防止 DON 交易的抢先交易。在数据源签署数据的情况下,用户可以 当 DON 未能这样做时,还需向 SCa 提供报告。 欺诈证明,如针对各种形式的乐观 rollup 所提议的(参见第 6.3 节), 与我们上面列举的机制相似且互补。他们 也提供了一种形式的链上监控和保护,防止潜在的故障 链下系统组件。 7.4 信任最小化治理 与所有去中心化系统一样,Chainlink 网络需要治理机制 随着时间的推移调整参数、响应紧急情况并指导其演变。 其中一些机制目前驻留在主链上,并且可能会继续存在 即使部署了 DONs,也要这样做。支付机制就是一个例子 对于 oracle 节点提供商(DON 节点)。 DON 主链上的前端合约 包含额外的机制,例如护栏,可能会受到定期检查 修改。 我们预见了两类治理机制:进化机制和紧急机制。 进化治理: 对 Chainlink 生态系统的许多修改是 这样它们的实施就不是一个紧迫的问题:性能改进, 功能增强、(非紧急)安全升级等。随着 Chainlink 逐渐吸引更多参与者参与其治理,我们预计许多或 大多数此类更改均需由受这些影响的特定 DON 社区批准 变化。在此期间,也许最终作为一个并行机制,我们相信 暂时最小特权的概念可以成为实施进化治理的有用手段。很简单,这个想法是逐步部署变革,确保 社区有机会回应他们。例如,迁移到新的 MAINCHAIN 合约可以受到约束,因此必须部署新合约 激活前至少三十天。应急治理: MAINCHAIN 中可利用或被利用的漏洞 合同或其他形式的活动或安全故障可能需要立即干预,以确保避免灾难性后果。我们的目的是支持多重签名 干预机制,以确保防止任何组织的不当行为, 签名者将分散在各个组织中。确保签名者的一致性可用性 并及时联系适当的指挥系统以授权紧急情况 变革显然需要仔细的运营规划和定期审查。这些 挑战与测试其他网络安全事件响应所涉及的挑战类似 能力 [134],具有类似的需要来解决常见问题,例如警惕性降低 [223]。 DONs 的治理不同于许多去中心化系统的治理 潜在的异质性程度。每个 DON 可能具有不同的数据源、可执行文件、服务级别要求(例如正常运行时间)和用户。 Chainlink 网络的 治理机制必须足够灵活,以适应这些变化 运营目标和参数。我们正在积极探索设计思路并计划 将来发表有关该主题的研究。 7.5 公钥基础设施 随着权力下放的逐步推进,将需要对 网络参与者,包括 DON 节点。特别是,Chainlink 需要强大的 公钥基础设施 (PKI)。 PKI 是将密钥与身份绑定的系统。对于 例如,PKI 巩固了互联网的安全连接系统 (TLS): 您通过 HTTPS(例如 https://www.chainlinklabs.com)连接到网站,并且 浏览器中出现锁,这意味着域所有者的公钥已被锁定 已通过权威机构(具体来说,通过数字签名)与该所有者绑定 所谓的证书。证书颁发机构 (CA) 的分层系统,其顶级根颁发机构硬连线到流行的浏览器中,有助于确保证书 仅颁发给域名的合法所有者。 我们预计 Chainlink 最终将使用去中心化的名称服务, 最初是 Ethereum 名称服务 (ENS) [22],作为我们 PKI 的基础。作为 顾名思义,ENS 类似于 DNS,即映射的域名系统 (人类可读的)域名到互联网上的 IP 地址。然而,ENS 将人类可读的 Ethereum 名称映射到 blockchain 地址。因为ENS 在 Ethereum blockchain 上运行,禁止密钥泄露、篡改其 原则上命名空间与篡改管理它的合约一样困难 和/或底层 blockchain。 (相比之下,DNS 历史上一直很脆弱 欺骗、劫持和其他攻击。) 我们已在 Ethereum 主网上向 ENS 注册了 data.eth,并打算 将其建立为根命名空间,在该根命名空间下 oracle 数据服务和 其他 Chainlink 网络实体驻留。 ENS 中的域是分层的,这意味着每个域都可能包含引用 其下的其他名称。 ENS 中的子域名可以作为组织和委托信任。 data.eth 的主要作用是作为链上目录服务 数据馈送。传统上,oracle 的开发者和用户使用链外资源 (例如,docs.chain.link 或 data.chain.link 等网站,或社交网络,例如 Twitter)发布并获取 oracle 数据源地址(例如 ETH-USD 价格 饲料)。使用高度可信的根命名空间(例如 data.eth),可以建立 eth-usd.data.eth 到例如 smart contract 地址的映射 用于 ETH-USD 价格反馈的链上 oracle 网络聚合器。这会 为任何人创建一条安全路径,将 blockchain 作为事实来源 该价格/名称对 (ETH-USD) 的数据源。因此,ENS 的这种使用 实现了链下数据源无法实现的两个好处: • 强大的安全性:对域的所有更改和更新都被永久记录 并以加密方式进行保护,而不是网站上的文本地址,这 不享有这两个安全属性。 • 自动链上传播:更新数据源的 smart contract 的底层地址可以触发传播到依赖智能的通知。 合同,例如可以自动更新相关合同 新地址.13 然而,像 ENS 这样的命名空间不会自动验证合法所有权 断言的名称。因此,例如,如果名称空间包含条目 ⟨“Acme Oracle Node Co.”,addr⟩, 那么用户就可以保证 addr 属于名称为 Acme 的声明者 Oracle Node Co. 没有围绕命名空间管理的额外机制, 然而,她无法保证该名称合法属于某个实体 在现实世界中,我们将其称为 Acme Oracle Node Co.。 我们验证名称的方法,即确保相应的、合法的现实世界实体拥有它们的所有权,依赖于几个组件。今天,Chainlink 实验室 实际上充当 Chainlink 网络的 CA。虽然 Chainlink 实验室将继续 为了验证名称,我们的 PKI 将通过两种方式演变成更加去中心化的模型: • 信任网络模型:分层 PKI 的去中心化版本通常被称为信任网络。14 自 20 世纪 90 年代以来就已经提出了各种变体, 例如,[98],并且许多研究人员观察到 blockchain 可以通过以全局一致的方式记录证书来促进该想法的使用,例如 [227] 分类帐。我们正在探索该模型的变体来验证实体的身份 以更加去中心化的方式存在于 Chainlink 网络中。 13从属合同可以选择包括预定的延迟,以允许手动检查 以及依赖合同管理员的干预。 14 Phil Zimmermann 为 PGP [238] 创造的术语。• 与验证数据的链接:如今,大量oracle 节点性能数据在链上可见,因此存档绑定到节点地址。 此类数据可被视为通过提供其(可靠)参与网络的历史证据来丰富 PKI 中的身份。另外,工具 用于基于 DECO 和 Town Crier [160] 启用节点的去中心化身份 积累来自现实世界数据的凭证。仅举一个例子, 节点操作员可以将凭证附加到其 PKI 身份以证明拥有权 邓白氏评级。这些补充形式的验证可以 补充 staking 以确保网络安全。具有既定现实世界身份的 oracle 节点可能被视为拥有权益 在一个源于其声誉的系统中。 (参见第 4.3 节和第 9.6.3 节。) Chainlink PKI 的最终要求是安全引导,即安全地 发布 Chainlink 网络的根名称,当前为 data.eth (类似地 到浏览器中顶级域的硬连线)。换句话说,Chainlink 用户如何 确定 data.eth 确实是与 Chainlink 关联的顶级域 项目? Chainlink 网络解决这个问题的方法是多管齐下的 可能涉及: • 将 TXT 记录 [224] 添加到指定的 chain.link 域记录中 data.eth 作为 Chainlink 生态系统的根域。 (Chainlink 因此隐式利用互联网域的 PKI 来验证其根 ENS 域。) • 从 Chainlink 的现有网站链接到 data.eth,例如来自 https://docs.chain.link. (另一种隐式使用 PKI 的互联网域。) • 通过各种文档(包括本白皮书)让人们了解 data.eth 的使用。 • 在我们的社交媒体渠道(例如 Twitter)上公开发布 data.eth,以及 Chainlink 博客 [18]。 • 将大量LINK置于同一注册者地址的控制之下 作为 data.eth。
DON Pertimbangan Penerapan
Meskipun bukan bagian dari desain inti kami, ada beberapa pertimbangan teknis yang penting dalam realisasi DONs yang layak mendapat perawatan di sini.
8.1 Pendekatan Peluncuran Makalah ini memaparkan visi ambisius tentang fungsionalitas Chainlink tingkat lanjut realisasinya akan membutuhkan solusi terhadap banyak tantangan yang ada di sepanjang jalan. Buku putih ini mengidentifikasi beberapa tantangan, namun tantangan yang tidak diantisipasi pasti akan muncul. Kami berencana untuk mengimplementasikan elemen-elemen visi ini secara bertahap selama bertahun-tahun jangka waktu yang lama. Harapan kami adalah DONs akan diluncurkan pada awalnya dukungan untuk komponen pra-bangun tertentu yang dibangun secara kolaboratif oleh tim di dalamnya Chainlink komunitas. Tujuannya adalah penggunaan DON yang lebih luas, misalnya kemampuan untuk meluncurkan executable sewenang-wenang, akan melihat dukungan di lain waktu. Salah satu alasan untuk berhati-hati adalah bahwa komposisi smart contract dapat menimbulkan efek samping yang kompleks, tidak diinginkan, dan berbahaya, seperti yang terjadi pada serangan berbasis pinjaman kilat baru-baru ini. misalnya ditunjukkan [127, 189]. Demikian pula komposisi smart contracts, adaptor, dan executable akan membutuhkan kehati-hatian yang ekstrim. Dalam penerapan awal DONs, kami berencana untuk hanya menyertakan sekumpulan executable dan adaptor yang telah dibuat sebelumnya dengan template. Hal ini akan memungkinkan studi tentang keamanan komposisi fungsi ini menggunakan metode formal [46, 170] dan pendekatan lainnya. Itu akan terjadi juga menyederhanakan penetapan harga: Penetapan harga fungsionalitas dapat ditetapkan oleh DON node berdasarkan perfungsionalitas, bukan melalui pengukuran umum, sebuah pendekatan yang diadopsi di, misalnya, [156]. Kami juga mengharapkan komunitas Chainlink untuk mengambil bagian dalam pembuatannya templat tambahan, menggabungkan berbagai adaptor dan executable menjadi lebih banyak layanan terdesentralisasi yang berguna yang dapat dijalankan oleh ratusan, bahkan ribuan orang DONdtk. Selain itu, pendekatan ini dapat membantu mencegah pembengkakan negara, yaitu kebutuhan akan DON node untuk mempertahankan jumlah status yang tidak bisa dijalankan dalam memori kerja. Masalah ini adalah sudah muncul dalam blockchains tanpa izin, yang memotivasi pendekatan seperti “stateless klien” (lihat, misalnya, [206]). Hal ini bisa menjadi lebih akut dalam sistem throughput yang lebih tinggi, sehingga memotivasi sebuah pendekatan di mana DON hanya menyebarkan executable dengan ukuran negara yang dioptimalkan. Seiring dengan berkembang dan matangnya DON serta mencakup pagar pengaman yang kuat, seperti yang dibahas di Bagian 7, mekanisme keamanan berbasis kriptoekonomi dan reputasi seperti yang dibahas di Bagian 9, dan fitur lain yang memberikan jaminan tingkat tinggi bagi pengguna DON, kami juga berharap untuk mengembangkan kerangka kerja dan alat untuk memfasilitasi peluncuran dan penggunaan yang lebih luas DONs oleh komunitas. Idealnya, alat ini akan mengaktifkan kumpulan operator node untuk berkumpul sebagai jaringan oracle dan meluncurkan DON mereka sendiri tanpa izin atau cara swalayan, artinya mereka dapat melakukannya secara sepihak. 8.2 Keanggotaan DON Dinamis Kumpulan node yang menjalankan DON tertentu dapat berubah seiring waktu. Ada dua pendekatan ke manajemen kunci untuk skL dengan keanggotaan dinamis di O. Yang pertama adalah memperbarui bagian skL yang dimiliki oleh node ketika terjadi perubahan keanggotaan, sambil menjaga pkL tidak berubah. Pendekatan ini, yang dieksplorasi dalam [41, 161, 198], mempunyai manfaat karena tidak mengharuskan pihak pengandal memperbarui pkL.Teknik klasik berbagi ulang saham, yang diperkenalkan pada [122], memberikan solusi sederhana dan cara yang efisien untuk mewujudkan pembaruan saham tersebut. Ini memungkinkan rahasia untuk ditransfer antara satu set node O(1) dan satu detik, kemungkinan berpotongan dengan satu O(2). Dalam hal ini pendekatan, setiap node O(1) saya melakukan (k(2), n(2)) pembagian rahasia dari bagian rahasianya node di O(2) untuk n(2) = |O(2)| dan ambang batas yang diinginkan (mungkin baru) k(2). Berbagai skema pembagian rahasia yang dapat diverifikasi (VSS) [108] dapat memberikan keamanan terhadap musuh yang secara aktif merusak node, yaitu memasukkan perilaku jahat ke dalam protokol. Teknik di [161] bertujuan untuk melakukannya sekaligus mengurangi kompleksitas dan penyediaan komunikasi ketahanan terhadap kegagalan dalam asumsi kekerasan kriptografi. Pendekatan kedua adalah memperbarui pkL kunci buku besar. Hal ini mempunyai manfaat ke depan keamanan: Kompromi pada saham lama pkL (yaitu, node komite sebelumnya) tidak akan dilakukan mengakibatkan kompromi pada kunci saat ini. Namun, pembaruan pada pkL memiliki dua kelemahan: (1) Data yang dienkripsi dengan pkL perlu dienkripsi ulang selama penyegaran kunci dan (2) Pembaruan penting perlu disebarkan kepada pihak-pihak yang mengandalkan. Kami bermaksud untuk mengeksplorasi kedua pendekatan tersebut, serta hibridisasi keduanya. 8.3 DON Akuntabilitas Seperti jaringan Chainlink oracle yang ada, DONs akan mencakup mekanisme akuntabilitas, yaitu mencatat, memantau, dan menegakkan perilaku node yang benar. DONs akan memilikinya kapasitas data yang jauh lebih besar dibandingkan banyak blockchain tanpa izin yang ada, terutama mengingat kemampuannya untuk terhubung ke penyimpanan eksternal yang terdesentralisasi. Akibatnya, mereka akan dapat mencatat riwayat kinerja node secara detail, sehingga memungkinkan mekanisme akuntabilitas yang lebih rinci. Misalnya, komputasi off-chain harga aset mungkin melibatkan masukan yang dibuang sebelum hasil median dikirimkan rantai. Dalam DON, hasil antara ini dapat dicatat. Perilaku buruk atau penyimpangan kinerja oleh masing-masing node di DON dapat diperbaiki atau dikenakan sanksi pada DON dengan cara yang halus. Kami juga telah membahas pendekatan untuk membangun pagar pembatas di Bagian 7.3 yang membahas dampak spesifik kontrak dari kegagalan sistemik. Namun, penting juga untuk memiliki mekanisme yang aman dari kegagalan untuk DONs itu sendiri, yaitu, perlindungan terhadap kegagalan DON yang sistemik dan berpotensi menimbulkan bencana, khususnya kegagalan forking / equivocation dan perjanjian tingkat layanan (SLA), seperti yang sekarang kami jelaskan. Forking / dalih: Mengingat cukup banyak node yang salah, DON dapat bercabang atau mengelak, menghasilkan dua blok atau rangkaian blok yang berbeda dan tidak konsisten di L. Namun, karena DON menandatangani isi L secara digital, dimungkinkan untuk memanfaatkan a rantai utama MAINCHAIN untuk mencegah dan/atau menghukum dalih. DON dapat secara berkala menyatakan pos pemeriksaan dari L dalam kontrak audit di MAINCHAIN. Jika keadaan masa depannya menyimpang dari keadaan yang diperiksa, pengguna/auditor dapat memberikan bukti kesalahan perilaku ini terhadap kontrak audit. Bukti tersebut dapat digunakan untuk menghasilkan peringatan atau menghukum DON node melalui pemotongan kontrak. Pendekatan terakhir ini memperkenalkan masalah desain insentif serupa dengan masalah feed oracle tertentu, dan dapat dikembangkan berdasarkan pekerjaan kami diuraikan dalam Bagian 9.Menegakkan perjanjian tingkat layanan: Meskipun DONs belum tentu dimaksudkan demikian berjalan tanpa batas waktu, penting bagi mereka untuk mematuhi perjanjian tingkat layanan (SLA) dengan penggunanya. Penegakan SLA dasar dimungkinkan pada rantai utama. Misalnya, Node DON mungkin berkomitmen untuk mempertahankan DON hingga tanggal tertentu, atau memberikan pemberitahuan terlebih dahulu mengenai penghentian layanan (misalnya, pemberitahuan tiga bulan sebelumnya). Sebuah kontrak aktif MAINCHAIN dapat menyediakan penegakan SLA ekonomi kripto dasar. Misalnya, kontrak SLA dapat memangkas dana yang disetorkan DON jika pos pemeriksaan tidak disediakan pada interval yang diperlukan. Pengguna dapat menyetor dana dan menantang DON untuk membuktikan bahwa pos pemeriksaan dengan benar mewakili urutan blok yang valid (dengan cara tertentu analog dengan, mis. [141]). Tentu saja, produksi blok tidak sama dengan transaksi pemrosesan, namun kontrak SLA juga dapat berfungsi untuk menegakkan yang terakhir. Misalnya, di Jika versi FSS yang kompatibel dengan versi lama di mana transaksi diambil dari mempool (lihat Bagian 5.2), transaksi pada akhirnya ditambang dan ditempatkan dalam rantai. Seorang pengguna dapat membuktikan DON penyimpangan dengan melengkapi kontrak SLA dengan transaksi yang telah ditambang tetapi tidak dikirimkan oleh DON untuk diproses sesuai kontrak target dalam interval waktu yang sesuai.15 Hal ini juga memungkinkan untuk membuktikan keberadaan dan memberikan sanksi pada SLA yang lebih rinci kegagalan, termasuk kesalahan dalam komputasi menggunakan executable (melalui, misalnya, mekanisme untuk membuktikan kebenaran transaksi negara off-chain yang diuraikan dalam Bagian 6.3) atau kegagalan untuk dijalankan executable berdasarkan inisiator yang terlihat di DON, kegagalan menyampaikan data di DON ke RANTAI UTAMA tepat waktu, dan lain sebagainya.
DON 部署注意事项
虽然不是我们核心设计的一部分,但有几个重要的技术考虑因素 实现 DON 值得在这里处理。
8.1 推出方法 本文提出了先进 Chainlink 功能的雄心勃勃的愿景,其 实现这一目标需要解决沿途的许多挑战。本白皮书 指出了一些挑战,但肯定会出现意想不到的挑战。 我们计划以渐进的方式实施这一愿景的要素 延长的一段时间。 我们的期望是 DONs 最初将与 支持由内部团队协作构建的特定预构建组件 Chainlink 社区。目的是更广泛地使用 DONs,例如能够 启动任意可执行文件,稍后会看到支持。 如此谨慎的原因之一是 smart contract 的组成可能会产生复杂的、意想不到的和危险的副作用,因为最近基于闪电贷的攻击已经 例如[127, 189]所示。同样,smart contract、适配器和 可执行文件需要格外小心。 在 DONs 的初始部署中,我们计划仅包含一组预构建的模板化可执行文件和适配器。这将使成分安全性的研究成为可能 使用形式化方法 [46, 170] 和其他方法来构建这些功能。它将 还简化了定价:功能定价可以由 DON 节点在功能基础上建立,而不是通过通用计量(采用的一种方法) 例如,[156]。我们还期望 Chainlink 社区参与创建 额外的模板,将各种适配器和可执行文件组合成越来越多的 有用的去中心化服务可以由数百甚至数千个人运行 DONs。 此外,这种方法可以帮助防止状态膨胀,即需要 DON 节点在工作内存中保留无法工作的状态量。这个问题是 已经在无许可的 blockchain 中出现,激励诸如“无状态 客户”(例如,参见 [206])。在吞吐量较高的系统中,它可能会更加严重,从而激励 DON 仅部署状态大小优化的可执行文件的方法。 随着 DON 的发展和成熟,并包括第 7 节中讨论的强大护栏、第 9 节中讨论的加密经济和基于声誉的安全机制,以及为 DON 用户提供高度保证的其他功能,我们 还期望开发一个框架和工具,以促进更广泛的启动和使用 社区的 DONs。理想情况下,这些工具将支持节点运营商的集合 作为一个 oracle 网络聚集在一起,并在未经许可的情况下启动他们自己的 DON 或自助服务方式,这意味着他们可以单方面这样做。 8.2 动态 DON 会员资格 运行给定 DON 的节点集可能会随时间而变化。有两种方法 给定 O 中的动态成员资格的 skL 的密钥管理。 第一个是在成员资格发生变化时更新节点持有的 skL 份额, 同时保持 pkL 不变。 [41,161,198]中探讨的这种方法具有以下优点 不要求依赖方更新 pkL。[122] 中介绍的共享重新共享的经典技术提供了一种简单的方法 以及实现此类共享更新的有效方法。它可以传输秘密 在一组节点 O(1) 和第二组节点之间,可能与一个 O(2) 相交。在这个 方法,每个节点 O(1) 我 执行 (k(2), n(2)) 秘密共享其秘密共享 n(2) = |O(2)| 的 O(2) 中的节点和期望的(可能是新的)阈值 k(2)。各种可验证秘密共享 (VSS) 方案 [108] 可以针对以下对手提供安全保护: 主动破坏节点,即在协议中引入恶意行为。 [161] 中的技术旨在做到这一点,同时降低通信复杂性并提供 针对密码硬度假设失败的弹性。 第二种方法是更新账本密钥 pkL。这样做的好处是可以向前推进 安全性:pkL 的旧份额(即前委员会节点)不会受到损害 导致当前密钥的泄露。然而,pkL 的更新有两个缺点: (1) 在 pkL 下加密的数据需要在密钥刷新期间重新加密,并且 (2) 密钥更新需要传播给依赖方。 我们打算探索这两种方法以及两者的混合。 8.3 DON 责任 与现有的 Chainlink oracle 网络一样,DON 将包括问责机制,即记录、监控和强制执行正确的节点行为。 DONs 将有 比许多现有的无需许可的 blockchain 拥有更多的数据容量, 特别是考虑到它们连接到外部分散存储的能力。因此,他们将能够详细记录节点的性能历史记录,从而允许 更细粒度的问责机制。例如,链外计算 资产价格可能涉及在发送中值结果之前被丢弃的输入 链。在 DON 中,可以记录这些中间结果。因此,DON 中各个节点的不当行为或性能失误可以在 DON 以细粒度的方式。我们还讨论了构建方法 第 7.3 节中的防护栏解决了系统故障的特定于合约的影响。 然而,为 DON 本身提供故障安全机制也很重要, 即针对系统性、潜在灾难性 DON 故障的保护,特别是 正如我们现在所解释的,分叉/模棱两可和服务级别协议 (SLA) 失败。 分叉/模棱两可: 给定足够多的故障节点,DON 可以分叉 或模棱两可,在 L 中产生两个不同的、不一致的块或块序列。 然而,因为 DON 对 L 的内容进行数字签名,所以可以利用 主链 MAINCHAIN 来防止和/或惩罚模棱两可。 DON 可以定期检查主链上审计合约中 L 的状态。 如果其未来状态偏离检查点状态,用户/审计员可以提供证据 审计合同中的这种不当行为。此类证据可用于生成警报 或者通过合约中的削减来惩罚 DON 节点。后一种方法引入了 类似于特定 oracle feed 的激励设计问题,并且可以建立在 我们的工作在第 9 节中概述。执行服务级别协议: 虽然 DONs 并不一定意味着 无限期运行,遵守服务级别协议 (SLA) 非常重要 与他们的用户。在主链上可以执行基本的 SLA。例如, DON 节点可能承诺维护 DON 直到某个日期,或提前提供服务终止通知(例如,提前三个月通知)。合同于 MAINCHAIN 可以提供基本的加密经济 SLA 执行。 例如,如果检查点是,SLA 合约可以削减 DON 存入的资金 未按要求的时间间隔提供。用户可以存入资金并质疑 DON 证明检查点正确地表示一系列有效块(以某种方式 类似于,例如[141])。当然,出块并不等于交易 处理,但 SLA 合同也可以用于执行后者。例如,在 FSS 的传统兼容版本,其中交易从内存池中获取(参见第 5.2 节),交易最终被挖掘并放置在链上。一个用户 可以通过向 SLA 合约提供以下交易来证明 DON 渎职行为: 已开采,但未由 DON 传输以供目标合约处理 在适当的时间间隔内。15 还可以证明更细粒度的 SLA 的存在并对其进行惩罚 失败,包括使用可执行文件的计算错误(例如,通过机制 用于证明第 6.3 节中概述的正确的链下状态交易)或运行失败 基于 DON 上可见的启动器的可执行文件,无法将 DON 上的数据中继到 及时进行MAINCHAIN等等。
Ekonomi dan Kriptoekonomi
Agar jaringan Chainlink dapat mencapai keamanan yang kuat dalam model kepercayaan yang terdesentralisasi, sangat penting bahwa node secara kolektif menunjukkan perilaku yang benar, artinya mereka patuh sebagian besar waktunya tepat untuk protokol DON. Pada bagian ini, kita membahas pendekatan untuk membantu menegakkan perilaku tersebut melalui insentif ekonomi, alias ekonomi kripto insentif. Insentif ini terbagi dalam dua kategori: eksplisit dan implisit, terealisasi masing-masing melalui staking dan peluang biaya masa depan (FFO). Mempertaruhkan: Staking di Chainlink, seperti pada sistem blockchain lainnya, melibatkan peserta jaringan, yaitu node oracle, yang menyetorkan dana terkunci dalam bentuk LINK tokens. Ini dana, yang juga kami sebut sebagai taruhan atau taruhan eksplisit adalah insentif eksplisit. Mereka dapat disita jika node mengalami kegagalan atau penyimpangan. Dalam konteks blockchain, prosedur ini sering disebut pemotongan. Namun, staking sebanyak oracle node di Chainlink, berbeda secara mendasar dari staking oleh validators dalam blockchains tanpa izin. Validator dapat berperilaku buruk dengan mengelak atau memerintahkan transaksi secara berlawanan. Protokol konsensus yang mendasari dalam a 15Karena pengguna dapat mengganti transaksi di mempool, diperlukan kehati-hatian untuk memastikan korespondensi yang benar antara transaksi yang ditambang dan DON yang dikirimkan.Namun, blockchain tanpa izin menggunakan aturan validasi blok yang tegas dan primitif kriptografi untuk mencegah validators menghasilkan blok yang tidak valid. Sebaliknya, perlindungan terprogram tidak dapat mencegah pembuatan jaringan oracle yang curang laporan tidak valid. Alasannya adalah perbedaan utama antara kedua jenis sistem: validasi transaksi di blockchains adalah properti konsistensi internal, sedangkan kebenarannya dari oracle laporan pada blockchain adalah properti eksternal, yaitu data off-chain. Kami telah merancang mekanisme staking awal untuk Chainlink berbasis jaringan pada protokol interaktif di antara oracle node yang mungkin menggunakan data eksternal. Ini Mekanisme ini menciptakan insentif finansial untuk perilaku yang benar dengan menggunakan imbalan yang jelas dan hukuman (tebasan). Karena mekanismenya ekonomis, maka dirancang untuk mencegah node korupsi oleh musuh yang menggunakan sumber daya keuangan untuk merusak node melalui penyuapan. (Musuh seperti itu sangat umum, dan meluas, misalnya, ke node yang bekerja sama mengambil nilai dari perilaku buruk kolektif mereka.) Mekanisme Chainlink staking yang kami rancang memiliki beberapa kekuatan dan novel fitur.16 Fitur utama tersebut adalah dampak staking super-linear (khususnya, kuadrat). Musuh harus memiliki sumber daya yang jauh melebihi dana yang disimpan oleh node untuk menumbangkan mekanisme tersebut. Mekanisme staking kami juga memberikan perlindungan terhadap musuh yang lebih kuat daripada yang dipertimbangkan sebelumnya dalam sistem serupa, yaitu musuh yang dapat memberikan suap yang mengkondisikan perilaku node di masa depan. Selain itu, kami mendiskusikan bagaimana alat Chainlink seperti DECO dapat membantu memperkuat staking kami mekanisme dengan memfasilitasi keputusan yang benar jika terjadi perilaku node yang salah. Peluang biaya masa depan (FFO): blockchains tanpa izin—dari kedua PoW dan variasi PoS—saat ini sangat bergantung pada apa yang kami sebut sebagai insentif implisit. Ini adalah insentif ekonomi untuk perilaku jujur yang tidak berasal dari imbalan yang jelas, namun dari partisipasi platform itu sendiri. Misalnya, komunitas penambang Bitcoin diberi insentif agar tidak melancarkan serangan 51% karena berisiko merusak kepercayaan terhadap perusahaan. Bitcoin, menurunkan nilainya, dan akibatnya mengikis nilai kolektifnya penanaman modal pada infrastruktur pertambangan [150]. Jaringan Chainlink mendapat manfaat dari insentif implisit serupa yang kami rujuk sebagai peluang biaya masa depan (FFO). Node Oracle dengan riwayat kinerja yang kuat atau reputasi menarik biaya dari pengguna. Perilaku buruk oleh node oracle membahayakan masa depan pembayaran biaya dan dengan demikian menghukum node dengan biaya peluang dalam hal potensi pendapatan yang diperoleh melalui partisipasi dalam jaringan. Dengan analogi dengan taruhan eksplisit, FFO dapat dipandang sebagai bentuk pertaruhan implisit, sebuah insentif untuk perilaku jujur berasal dari manfaat bersama dalam menjaga kepercayaan pada platform di mana Bisnis operator node bergantung, misalnya, pada kinerja dan reputasi positif dari node tersebut jaringan. Insentif ini melekat namun tidak secara eksplisit dinyatakan dalam jaringan Chainlink protokol. Pada Bitcoin, mempertahankan nilai operasi penambangan seperti yang disebutkan di atas 16Mekanisme staking yang kami jelaskan di sini saat ini hanya bertujuan untuk menegakkan penyampaian laporan yang benar oleh oracle jaringan. Kami berharap di masa depan pekerjaan dapat memperluasnya untuk memastikan pelaksanaan yang benar dari banyak hal fungsi lain yang akan disediakan oleh DONs.juga dapat dipandang sebagai bentuk kepemilikan implisit. Kami menekankan bahwa FFO sudah ada di Chainlink dan membantu mengamankan jaringan hari ini. Kontribusi utama kami dalam pengembangan lebih lanjut Chainlink adalah pendekatan yang berprinsip dan didorong secara empiris untuk mengevaluasi insentif implisit seperti FFO melalui apa yang kami sebut Kerangka Insentif Implisit (IIF). Untuk memperkirakan jumlah seperti peluang biaya node di masa depan, IIF akan terus memanfaatkan hal ini secara komprehensif data kinerja dan pembayaran yang dikumpulkan oleh jaringan Chainlink. Perkiraan seperti itu akan mengaktifkan parameterisasi sistem staking berbasis IIF yang mencerminkan insentif node dengan akurasi lebih tinggi dibandingkan model heuristik dan/atau statis saat ini. Jadi, untuk meringkas, dua insentif ekonomi utama untuk simpul oracle yang benar perilaku dalam jaringan Chainlink yang sedang berkembang adalah: • Staking (taruhan yang disimpan) o Insentif eksplisit • Peluang biaya masa depan (FFO) o Insentif implisit Kedua bentuk insentif ini saling melengkapi. Node Oracle bisa secara bersamaan berpartisipasi dalam protokol Chainlink staking, nikmati aliran pendapatan berkelanjutan dari pengguna, dan secara kolektif mendapatkan manfaat dari perilaku baik mereka yang berkelanjutan. Demikian kedua insentif tersebut berkontribusi pada keamanan ekonomi kripto yang disediakan oleh jaringan oracle. Selain itu, kedua insentif tersebut dapat saling memperkuat dan/atau saling bertentangan. Misalnya, operator oracle baru tanpa riwayat kinerja dan aliran pendapatan dapat mempertaruhkan a LINK dalam jumlah besar sebagai jaminan perilaku jujur, sehingga menarik pengguna dan biaya. Sebaliknya, operator oracle yang mapan memiliki waktu yang panjang dan relatif bebas kesalahan riwayat kinerja dapat membebankan biaya besar dari basis pengguna yang besar dan karenanya bergantung lebih menekankan pada FFO-nya sebagai bentuk insentif implisit. Secara umum, pendekatan yang kami pertimbangkan di sini bertujuan untuk sejumlah oracle-jaringan sumber daya untuk menciptakan insentif ekonomi sebesar mungkin di Chainlink secara rasional agen—yaitu, node yang memaksimalkan utilitas finansialnya—untuk berperilaku jujur. Letakkan yang lain Dengan cara ini, tujuannya adalah untuk memaksimalkan sumber daya finansial yang dibutuhkan musuh untuk menyerang jaringan berhasil. Dengan merumuskan protokol staking dengan baik secara matematis mendefinisikan keamanan ekonomi dan juga menggunakan IIF, kami bertujuan untuk mengukur kekuatan insentif Chainlink seakurat mungkin. Pembuat kontrak yang mengandalkan akan melakukannya kemudian dapat menentukan dengan keyakinan yang kuat apakah jaringan oracle bertemu tingkat keamanan kriptoekonomi yang diperlukan. Siklus baik keamanan ekonomi: Insentif yang kita bahas di bagian ini, staking dan FFO, mempunyai dampak lebih dari sekadar memperkuat keamanan DONdtk. Mereka berjanji untuk mendorong apa yang kita sebut sebagai siklus keamanan ekonomi yang baik. Dampak staking yang sangat linier (dan skala ekonomi lainnya) mengakibatkan operasional menjadi lebih rendah biaya seiring dengan meningkatnya keamanan DON. Biaya yang lebih rendah menarik pengguna tambahan ke DON,meningkatkan pembayaran biaya. Kenaikan pembayaran biaya terus mendorong pertumbuhan jaringan, yang melanggengkan siklus yang baik. Kami percaya bahwa siklus baik keamanan ekonomi hanyalah salah satu contoh dari skala ekonomi dan efek jaringan antara lain yang akan kita bahas nanti di bagian ini. Organisasi bagian: Staking menghadirkan tantangan teknis dan konseptual yang penting yang mana kami telah merancang mekanisme dengan fitur-fitur baru. Oleh karena itu, staking akan terjadi fokus utama kami di bagian ini. Kami memberikan gambaran umum tentang pendekatan staking yang kami perkenalkan dalam makalah ini di Bagian 9.1, diikuti dengan pembahasan mendetail di Bagian 9.2 hingga 9.5. Kami menyajikan IFF di Bagian 9.6. Kami menyajikan tampilan ringkasan Chainlink insentif jaringan di Bagian 9.7. Di Bagian 9.8, kami membahas siklus baik keamanan ekonomi yang dapat dihasilkan oleh pendekatan staking yang kami usulkan ke jaringan oracle. Terakhir, kami uraikan secara singkat potensi lainnya efek mendorong pertumbuhan jaringan Chainlink di Bagian 9.9. 9.1 Ikhtisar Taruhan Desain mekanisme staking yang kami perkenalkan di sini, seperti disebutkan di atas, melibatkan protokol interaktif di antara oracle node yang memungkinkan penyelesaian ketidakkonsistenan dalam pelaporan data eksternal. Staking bertujuan untuk memastikan perilaku jujur dari node oracle yang rasional. Oleh karena itu kita dapat memodelkan musuh yang menyerang protokol staking sebagai a penyuap: Strategi musuh adalah merusak oracle node dengan menggunakan insentif finansial. Musuh dapat memperoleh sumber daya finansial secara prospektif dari upaya perusakan yang berhasil dengan laporan oracle, misalnya, menawarkan untuk membagi keuntungan yang dihasilkan dengan node yang rusak. Kami menargetkan desain mekanisme staking secara bersamaan pada dua tujuan ambisius: 1. Melawan musuh yang kuat: Mekanisme staking dirancang untuk melindungi oracle jaringan melawan sekelompok besar musuh yang mampu melakukan tindakan yang kompleks, strategi suap bersyarat, termasuk suap prospektif, yang menawarkan suap kepada oracles yang identitasnya ditentukan setelah kejadian tersebut (misalnya, menawarkan suap kepada oracles dipilih secara acak untuk peringatan prioritas tinggi). Sedangkan desain oracle lainnya telah mempertimbangkan serangkaian serangan sempit tanpa kemampuan penuh yang realistis musuh, sepanjang pengetahuan kami mekanisme permusuhan yang kami perkenalkan Inilah yang pertama kali secara eksplisit membahas serangkaian strategi dan pertunjukan suap resistensi dalam model ini. Model kami mengasumsikan bahwa ada node selain penyerang rasional secara ekonomi (bukan jujur), dan kami berasumsi adanya a sumber kebenaran yang sangat mahal untuk penggunaan umum tetapi tersedia jika terjadi perbedaan pendapat (dibahas lebih lanjut di bawah). 2. Mencapai dampak staking super-linier: Tujuan kami adalah memastikan bahwa jaringan oracle terdiri dari laporan agen yang rasional sejujurnya bahkan di hadapan penyerang dengan anggaran yang super-lineardalam total saham yang disimpan oleh seluruh jaringan. Dalam sistem staking yang ada, jika masing-masing dari n node mempertaruhkan $d, penyerang dapat mengeluarkan suap yang kredibel yang diminta bahwa node berperilaku tidak jujur dengan imbalan pembayaran sedikit lebih dari \(d to each node, using a total budget of about \)dn. Ini sudah merupakan standar yang tinggi penyerang harus memiliki anggaran yang likuid berdasarkan urutan simpanan gabungan semua pemangku kepentingan dalam jaringan. Tujuan kami adalah tingkat keamanan ekonomi yang lebih kuat daripada rintangan yang sudah besar ini. Kami bertujuan untuk merancang sistem staking pertama yang dapat mencapai keamanan bagi penyerang umum dengan anggaran super-linear di n. Meskipun pertimbangan praktis mungkin memberikan dampak yang lebih kecil, seperti yang kita bahas di bawah ini, desain awal kami mencapai kebutuhan anggaran yang berlawanan lebih besar dari $dn2/2, yaitu, menskalakan kuadrat dalam n, membuat suap menjadi tidak praktis bahkan ketika node hanya melakukan staking dalam jumlah sedang. Untuk mencapai kedua tujuan ini memerlukan kombinasi desain insentif yang inovatif dan kriptografi. Ide-ide kunci: Pendekatan staking kami bergantung pada gagasan yang kami sebut sebagai prioritas pengawas. Laporan yang dihasilkan oleh jaringan Chainlink oracle dan dikirim ke kontrak yang mengandalkan (misalnya, harga aset) dikumpulkan dari masing-masing laporan yang disumbangkan oleh node yang berpartisipasi (misalnya, dengan mengambil median). Biasanya perjanjian tingkat layanan (SLA) menentukan batas deviasi yang dapat diterima untuk laporan, yaitu seberapa jauh laporan node dapat melakukannya menyimpang dari laporan agregat dan seberapa jauh agregat tersebut diperbolehkan menyimpang dari nilai sebenarnya untuk dianggap benar. Dalam sistem staking kami, untuk putaran pelaporan tertentu, setiap node oracle dapat bertindak sebagai pengawas untuk memberikan peringatan jika mereka yakin bahwa laporan agregat tersebut tidak benar. Di masing-masing putaran pelaporan, setiap node oracle diberi prioritas publik yang menentukan urutan peringatannya (jika ada) akan diproses. Mekanisme kami bertujuan untuk mendapatkan imbalan konsentrasi, yang berarti bahwa pengawas dengan prioritas tertinggi untuk meningkatkan kewaspadaan berhak mendapatkan seluruh imbalan yang dihasilkan dengan menyita simpanan node yang salah. Desain sistem staking kami melibatkan dua tingkatan: yang pertama, tingkat default, dan yang kedua, tingkat penghalang. Tingkat pertama adalah jaringan oracle itu sendiri, yang terdiri dari n node. (Untuk kesederhanaan, kami berasumsi n ganjil.) Jika mayoritas node melaporkan nilai yang salah, pengawas di tingkat pertama diberi insentif yang kuat untuk meningkatkan kewaspadaan. Jika peringatan dimunculkan, pelaporan Keputusan jaringan kemudian ditingkatkan ke tingkat kedua—sistem berbiaya tinggi dan memiliki keandalan maksimum yang dapat ditentukan oleh pengguna dalam perjanjian tingkat layanan jaringan. Ini bisa berupa sistem yang, misalnya, hanya terdiri dari node-node yang kuat skor keandalan historis, atau skor yang memiliki urutan besarnya lebih dari oracles tingkat pertama. Selain itu, sebagaimana dibahas dalam Bagian 9.4.3, DECO atau Town Crier dapat berfungsi sebagai alat yang ampuh untuk membantu memastikan keputusan yang efisien dan konklusif di tingkat kedua. Untuk mempermudah, kami berasumsi bahwa sistem lapis kedua ini menghasilkan laporan yang benar nilai. Meskipun mungkin terlihat menarik jika hanya mengandalkan tingkat kedua untuk menghasilkan semua laporan, manfaat dari desain kami adalah secara konsisten mencapai sifat keamanansistem lapis kedua sambil hanya membayar biaya operasional, dalam kasus tertentu, dari sistem tersebut sistem tingkat pertama. Prioritas pengawas menghasilkan dampak staking super-linear dengan cara berikut: jika jaringan oracle tingkat pertama mengeluarkan hasil yang salah dan sejumlah node pengawas waspada, mekanisme insentif staking memberikan penghargaan kepada pengawas dengan prioritas tertinggi lebih dari $dn/2 diambil dari simpanan node (mayoritas) yang berperilaku buruk. Itu Oleh karena itu, imbalan total terkonsentrasi di tangan pengawas tunggal ini menentukan jumlah minimum yang harus dijanjikan oleh musuh kepada calon pengawas memberi insentif agar tidak memperingatkan. Karena mekanisme kami memastikan bahwa setiap oracle mendapatkan kesempatan untuk bertindak sebagai pengawas jika pengawas dengan prioritas lebih tinggi telah menerima suap (dan memilih untuk tidak waspada), oleh karena itu pihak lawan harus menawarkan suap lebih dari itu $dn/2 ke setiap node untuk mencegah peringatan apa pun dimunculkan. Karena ada n node, maka anggaran yang diperlukan musuh agar suap berhasil berjumlah lebih dari $dn2/2, yang mana adalah kuadrat dalam jumlah n node dalam jaringan. 9.2 Latar Belakang Pendekatan kami terhadap staking mengacu pada penelitian di bidang teori dan mekanisme permainan desain (MD) (untuk referensi buku teks, lihat [177]). Teori permainan adalah secara matematis studi formal tentang interaksi strategis. Dalam konteks ini, permainan adalah salah satu contohnya sebuah interaksi, biasanya di dunia nyata, yang mengkodifikasi serangkaian tindakan yang tersedia peserta dalam permainan, yang dikenal sebagai pemain. Sebuah permainan juga menentukan pembayaran yang diperoleh oleh masing-masing pemain—hadiah yang bergantung pada tindakan yang dipilih pemain dan tindakan pemain lain. Mungkin contoh paling terkenal dari permainan yang dipelajari dalam permainan teorinya adalah Dilema Narapidana [178]. Para ahli teori permainan umumnya bertujuan untuk memahami keseimbangan atau keseimbangan (jika ada) yang direpresentasikan dalam permainan tertentu. Keseimbangan adalah serangkaian strategi (satu untuk setiap pemain) sedemikian rupa sehingga tidak ada satu pemain pun yang dapat memperoleh strategi yang lebih tinggi membayar dengan secara sepihak menyimpang dari strateginya. Sedangkan desain mekanisme adalah ilmu merancang insentif sedemikian rupa keseimbangan suatu interaksi (dan permainan terkaitnya) mempunyai beberapa sifat yang diinginkan. MD dapat dipandang sebagai kebalikan dari teori permainan: Pertanyaan kanonik dalam permainan teorinya adalah, “dengan adanya insentif dan model, keseimbangan seperti apa yang akan terjadi?” Di MD, itu Pertanyaannya adalah, “insentif apa yang akan menghasilkan permainan dengan keseimbangan yang diinginkan?” Tujuan umum dari perancang mekanisme adalah untuk menciptakan mekanisme yang ‘kompatibel dengan insentif’, yang berarti bahwa peserta dalam mekanisme tersebut (misalnya, lelang atau informasi lainnya) sistem elisitasi [228]) diberi insentif untuk melaporkan kebenaran mengenai beberapa hal (misalnya, bagaimana seberapa besar mereka menghargai barang tertentu). Lelang Vickrey (harga kedua) mungkin adalah yang terbaik mekanisme yang paling dikenal dan kompatibel dengan insentif, di mana peserta mengajukan penawaran tertutup untuk suatu barang dan penawar tertinggi memenangkan barang tersebut tetapi membayar harga tertinggi kedua [214]. Cryptoeconomics adalah bentuk MD khusus domain yang memanfaatkan kriptografi teknik untuk menciptakan keseimbangan yang diinginkan dalam sistem desentralisasi. Suap dan kolusi menciptakan tantangan yang signifikan di seluruh bidang MD. Hampir semua mekanisme rusak jika terjadi kolusi, yang didefinisikan sebagai kontrak sampingan antaraantara pihak-pihak yang berpartisipasi dalam suatu mekanisme [125, 130]. Penyuapan, dimana pihak eksternal memberikan insentif baru, menghadirkan masalah yang lebih sulit daripada kolusi; kolusi dapat dipandang sebagai kasus khusus suap antar hewan buruan peserta. Sistem Blockchain sering kali dapat dikonseptualisasikan sebagai permainan dengan imbalan moneter (berbasis mata uang kripto). Contoh sederhananya adalah penambangan Proof-of-Work: penambang memiliki ruang tindakan di mana mereka dapat memilih hashrate yang akan digunakan untuk menambang blok. Imbalan penambangan adalah imbalan negatif yang dijamin (biaya listrik dan peralatan) ditambah stokastik imbalan positif (subsidi penambangan) yang bergantung pada jumlah penambang aktif lainnya [106, 172] dan biaya transaksi. oracle crowdsourced seperti SchellingCoin [68] adalah contoh lain: ruang tindakan adalah kumpulan kemungkinan laporan yang dapat dikirim oleh oracle, sementara imbalannya adalah imbalan yang ditentukan oleh mekanisme oracle, misalnya, pembayaran mungkin bergantung tentang seberapa dekat laporan oracle dengan median laporan lainnya [26, 68, 119, 185]. Permainan Blockchain menawarkan peluang besar untuk serangan kolusi dan penyuapan; memang, smart contracts bahkan dapat memfasilitasi serangan tersebut [96, 165]. Mungkin yang paling terkenal serangan suap terhadap crowdsourcing oracles adalah serangan p-plus-epsilon [67]. Serangan ini muncul dalam konteks mekanisme mirip SchellingCoin di mana pemain mengirimkan laporan bernilai boolean (yaitu, salah atau benar) dan diberi hadiah p jika mereka setuju dengan pengajuan mayoritas. Dalam serangan p-plus-epsilon, penyerang secara kredibel berjanji untuk, misalnya, membayar pengguna $p + ϵ untuk memberikan suara salah jika dan hanya jika mayoritas yang diajukan benar. Hasilnya adalah keseimbangan, di mana semua pemain diberi insentif untuk melaporkan kebohongan terlepas dari apa yang dilakukan pemain lain; akibatnya, penyuap dapat menginduksi node melalui janji suap untuk melaporkan kebohongan tanpa benar-benar membayar suap tersebut (!). Namun, eksplorasi strategi penyuap lainnya dalam konteks oracle—dan khususnya oracle yang tidak dilakukan secara crowdsourcing—masih terbatas pada strategi adversarial yang cukup lemah. model. Misalnya, dalam konteks PoW, para peneliti telah mempelajari kontingen hasil suap, yaitu suap yang dibayarkan hanya jika pesan target berhasil disensor dan tidak muncul dalam satu blok, terlepas dari tindakan masing-masing penambang [96, 165]. Dalam kasus ini dari oracles, namun, selain serangan p-plus-epsilon, kami hanya mengetahui pekerjaan di model suap yang sangat terbatas di mana penyuap mengirimkan suap dengan syarat tindakan individu pemain, bukan pada hasil yang dihasilkan. Di sini kami membuat sketsa rancangan mekanisme perolehan informasi yang tetap bersifat insentif kompatibel bahkan dalam model permusuhan yang kuat, seperti yang dijelaskan dalam sub-bagian berikutnya. 9.3 Asumsi Pemodelan Di subbagian ini, kami menjelaskan bagaimana kami memodelkan perilaku dan kemampuan pemain sistem kami, khususnya node oracle tingkat pertama, node di tingkat kedua (penghakiman) lapisan, dan musuh.9.3.1 Model Insentif Tingkat Pertama: Aktor Rasional Banyak sistem blockchain mengandalkan keamanan pada asumsi sejumlah kejujuran node yang berpartisipasi. Node didefinisikan jujur jika mereka mengikuti protokol ketika hal tersebut bukan merupakan kepentingan finansial mereka. Biasanya sistem Proof-of-Work sejujurnya membutuhkan sebagian besar kekuatan hash, sejujurnya sistem Proof-of-Stake biasanya memerlukan 2/3 atau lebih dari seluruh pasak yang berpartisipasi, dan bahkan sistem lapisan-2 seperti Arbitrum [141] memerlukan setidaknya satu peserta yang jujur. Dalam pemodelan mekanisme staking, kami membuat asumsi yang jauh lebih lemah. (Menjadi jelas, asumsi yang lebih lemah berarti properti keamanan yang lebih kuat dan oleh karena itu lebih disukai.) Kami berasumsi bahwa musuh telah melakukan korupsi, yaitu kontrol, beberapa (minoritas) sebagian kecil dari node oracle tingkat pertama. Kami memodelkan node yang tersisa bukan sebagai agen yang jujur, tetapi sebagai pemaksimal utilitas yang diharapkan secara rasional. Node-node ini bertindak sepenuhnya berdasarkan insentif finansial yang mementingkan diri sendiri, memilih tindakan yang menghasilkan finansial yang diharapkan keuntungan. Misalnya, jika sebuah node ditawari suap yang lebih besar daripada imbalan yang dihasilkannya perilaku jujur, ia akan menerima suap. Catatan tentang node musuh: Sesuai dengan model kepercayaan yang umum untuk sistem desentralisasi, kami berasumsi bahwa semua node bersifat rasional, yaitu berupaya untuk memaksimalkan pendapatan bersih, daripada dikendalikan oleh musuh jahat. Namun klaim kami— khususnya dampak staking super-linier atau kuadratik—tetap tanpa gejala bahwa himpunan node yang dikontrol secara musuh paling banyak (1/2 −c)n, untuk beberapa positif konstan c. 9.3.2 Model Ajudikasi Tingkat Kedua: Kebenaran Berdasarkan Asumsi Ingatlah bahwa fitur penting dari mekanisme staking kami yang membantu mencapai keamanan melawan simpul rasional adalah sistem tingkat kedua. Dalam mekanisme staking yang kami usulkan, oracle mana pun dapat memunculkan peringatan yang menunjukkan bahwa ia yakin keluaran dari mekanisme tersebut salah. Peringatan menghasilkan kepercayaan yang tinggi sistem tingkat kedua mengaktifkan dan melaporkan hasil yang benar. Jadi, pemodelan kunci Persyaratan untuk pendekatan kami adalah penilaian yang benar, yaitu pelaporan yang benar oleh sistem lapis kedua. Model staking kami mengasumsikan sistem tingkat kedua yang bertindak sebagai sumber kebenaran yang tidak dapat rusak dan dapat diandalkan secara maksimal. Sistem seperti ini mungkin mahal dan lambat tidak cocok untuk digunakan pada kasus-kasus tertentu. Namun dalam kasus keseimbangan, yaitu kapan jika sistem tingkat pertama berfungsi dengan benar, sistem tingkat kedua tidak akan dijalankan. Sebaliknya, keberadaannya meningkatkan keamanan seluruh sistem oracle dengan menyediakan a penghalang dengan jaminan tinggi. Penggunaan lapisan ajudikasi dengan tingkat kepercayaan tinggi dan berbiaya tinggi mirip dengan proses banding di jantung sebagian besar sistem peradilan. Hal ini juga sudah umum pada desain oracle sistem, misalnya, [119, 185]. Kami secara singkat membahas pendekatan realisasi tingkat kedua dalam mekanisme kami di Bagian 9.4.3.Protokol staking kami menggunakan asumsi penilaian yang benar dari sistem tingkat kedua sebagai ancaman yang dapat dipercaya untuk menegakkan pelaporan yang benar oleh oracle node. Protokol menyita sebagian atau seluruh saham oracle node yang menghasilkan laporan yang diidentifikasi oleh sistem tingkat kedua sebagai salah. Dengan demikian, node Oracle terhindar dari perilaku buruk dengan sanksi finansial yang diakibatkannya. Pendekatan ini memiliki rasa yang mirip dengan yang digunakan dalam rollups yang optimis, misalnya, [141, 10]. 9.3.3 Model Permusuhan Mekanisme staking kami dirancang untuk memperoleh informasi yang benar sekaligus mencapai keamanan terhadap kelompok musuh yang luas dan terdefinisi dengan baik. Ini meningkatkan pekerjaan sebelumnya, yang menghilangkan model permusuhan eksplisit atau fokus pada subkelas musuh yang sempit, misalnya musuh p-plus-epsilon yang dibahas di atas. Tujuan kami adalah merancang staking mekanisme dengan keamanan yang terbukti secara formal terhadap kemungkinan besar seluruh spektrum musuh untuk ditemui dalam praktek. Kita memodelkan musuh kita sebagai musuh yang memiliki anggaran tetap (dapat diparameterisasi), yang dilambangkan dengan $B. Musuh dapat berkomunikasi secara individu dan rahasia dengan masing-masing oracle masuk jaringan, dan secara diam-diam dapat menawarkan jaminan pembayaran suap kepada siapa pun oracle bergantung pada hasil mekanisme yang dapat diobservasi secara publik. Penentu hasil suap dapat mencakup, misalnya, nilai yang dilaporkan oleh oracle, pesan publik apa pun dikirim oleh oracle mana pun ke mekanisme (misalnya, peringatan), nilai yang dilaporkan oleh pihak lain oracles, dan nilai yang dihasilkan oleh mekanisme. Tidak ada mekanisme yang dapat mengamankan serangan dari penyerang dengan kemampuan tak terbatas. Oleh karena itu, kami menganggap beberapa perilaku tidak realistis atau di luar jangkauan. Kami menganggap penyerang kami tidak dapat memecahkan primitif kriptografi standar, dan, seperti disebutkan di atas, memiliki nilai tetap (if berpotensi besar) anggaran $B. Kami selanjutnya berasumsi bahwa musuh tidak mengendalikan komunikasi di jaringan oracle, khususnya yang tidak dapat menunda secara signifikan lalu lintas antara node tingkat pertama dan/atau tingkat kedua. (Apakah musuh dapat mengamati komunikasi tersebut bergantung pada mekanisme tertentu, seperti yang kami jelaskan di bawah.) Namun secara informal, seperti disebutkan di atas, kami berasumsi bahwa pihak yang berlawanan dapat: (1) Korupsi sebagian kecil dari oracle node ((1/2 −c)-fraksi untuk beberapa konstanta c), yaitu, kontrol penuh mereka, dan (2) Menawarkan suap ke node mana pun yang diinginkan, dengan jaminan pembayaran kontinjensi pada hasil yang ditentukan oleh musuh, seperti dijelaskan di atas. Meskipun kami tidak menawarkan model formal atau taksonomi lengkap mengenai musuh secara penuh berbagai kemampuan menyuap dalam whitepaper ini, berikut contoh macamnya penyuap yang tercakup dalam model kami. Untuk mempermudah, kami berasumsi bahwa oracles memancarkan Boolean laporan yang nilai benarnya (w.l.o.g.) benar, dan hasil akhirnya dihitung sebagai kumpulan laporan ini untuk digunakan oleh smart contract konsumen. milik si penyuap tujuannya adalah agar hasil akhirnya salah, yaitu salah. • Penyuap tanpa syarat: Penyuap menawarkan suap $b kepada oracle mana pun yang melaporkan kebohongan. • Penyuap probabilistik: Penyuap menawarkan suap $b dengan beberapa kemungkinan q kepada oracle mana pun yang melaporkan palsu.• hasil palsu yang dikondisikan oleh penyuap: Penyuap menawarkan suap $b kepada oracle mana pun yang melaporkan palsu asalkan hasil akhirnya salah. • Penyuap tanpa syarat: Penyuap menawarkan suap $b kepada oracle mana pun yang melapor salah selama tidak ada peringatan yang dimunculkan. • p-plus-epsilon Penyuap: Penyuap menawarkan suap $b kepada oracle mana pun yang melaporkan palsu sebagai selama mayoritas oracle tidak melaporkan kebohongan. • Calon penyuap: Penyuap menawarkan suap $b terlebih dahulu kepada oracle mana pun yang dipilih untuk peran yang diacak dan melaporkan palsu. Dalam protokol staking yang kami usulkan, semuanya node bertindak sebagai pengawas potensial, dan kami dapat menunjukkan pengacakan itu prioritas pengawas tidak memungkinkan terjadinya suap. Banyak sistem proof-of-work, proof-of-stake, dan berizin yang rentan terhadap prospektif akan tetapi, penyuapan menunjukkan pentingnya mempertimbangkannya dalam persaingan kita membuat model dan memastikan bahwa protokol staking kami tahan terhadapnya. Lihat Lampiran E untuk lebih jelasnya. 9.3.4 Berapa Banyak Keamanan Kriptoekonomi yang Cukup? Musuh yang rasional hanya akan mengeluarkan uang untuk menyerang suatu sistem jika sistem tersebut dapat memperoleh keuntungan lebih besar dari pengeluarannya. Jadi untuk model permusuhan kami dan usulan staking mekanismenya, $B dapat dipandang sebagai ukuran potensi keuntungan yang dapat diperoleh musuh untuk mengekstrak dari mengandalkan smart contracts dengan merusak jaringan oracle dan menyebabkannya untuk menghasilkan laporan atau kumpulan laporan yang salah. Dalam memutuskan apakah jaringan oracle menawarkan tingkat keamanan kriptoekonomi yang memadai untuk tujuan mereka, pengguna harus melakukannya menilai jaringan dari perspektif ini. Untuk musuh yang masuk akal dalam situasi praktis, kami memperkirakan $B secara umum akan terjadi jauh lebih kecil dari total aset pada smart contracts yang diandalkan. Dalam kebanyakan kasus, itu tidak mungkin bagi musuh untuk mengekstraksi aset-aset ini secara keseluruhan. 9.4 Mekanisme Staking: Sketsa Berikut kami sajikan gagasan pokok dan struktur umum dari mekanisme staking kami sedang mempertimbangkan. Untuk kemudahan penyajian, kami uraikan secara sederhana namun lambat (multi-putaran) protokol dalam sub-bagian ini. Namun kami mencatat bahwa skema ini cukup baik praktis. Mengingat jaminan ekonomi yang diberikan oleh mekanisme tersebut, misalnya hukuman dan insentif terhadap node yang salah, banyak pengguna mungkin bersedia untuk melakukan hal tersebut. menerima laporan dengan optimis. Dengan kata lain, pengguna tersebut dapat menerima laporan sebelumnya keputusan potensial oleh tingkat kedua. Pengguna yang tidak mau menerima laporan dengan optimis dapat memilih untuk menunggu hingga protokol selesai eksekusi dihentikan, yaitu hingga terjadi potensi eskalasi ke tingkat kedua. Ini, namun, dapat memperlambat waktu konfirmasi laporan secara signifikan. Oleh karena itu kami secara singkatGambar 15: Skema skema staking dengan peringatan. Dalam contoh ini, 1⃝mayoritas node rusak / disuap dan mengeluarkan nilai ˜r yang salah, bukan nilai yang benar nilai laporan r. Node pengawas 2⃝ mengirimkan peringatan ke komite tingkat kedua, yang 3⃝menentukan dan mengeluarkan nilai laporan yang benar r, mengakibatkan node rusak kehilangan deposit mereka—masing-masing $d ke node pengawas 4⃝. menguraikan beberapa optimasi yang menghasilkan lebih cepat (satu putaran) jika lebih desain kompleks di Bagian 9.5. Ingatlah bahwa tingkat pertama dalam mekanisme staking kita terdiri dari oracle dasar jaringan itu sendiri. Struktur utama mekanisme kami, seperti dijelaskan di atas, adalah di setiap putaran, setiap node dapat bertindak sebagai “anjing penjaga” dengan prioritas tertentu, dan dengan demikian node tersebut mempunyai kemampuan untuk melakukan hal tersebut meningkatkan peringatan jika mekanisme menghasilkan keluaran yang salah, bukan keluaran yang benar satu sungai. Peringatan ini menyebabkan resolusi tingkat kedua, yang kami anggap benar laporan. Node dengan laporan yang salah akan dihukum, dalam artian taruhannya juga demikian dipotong dan diberikan kepada pengawas. Struktur dasar ini umum di sistem oracle, seperti pada, misalnya, [119, 185]. Inovasi utama dalam desain kami, yang disebutkan secara singkat di atas, adalah setiap node diberi prioritas tersendiri dalam mengurutkan calon pengawas. Artinya, anjing penjaga diberi kesempatan untuk waspada dalam urutan prioritas. Ingatlah bahwa jika sebuah node memiliki prioritas tertinggi untuk meningkatkan peringatan, ia menerima pemotongan deposit $d untuk setiap perilaku buruk node, dengan total lebih dari \(dn/2 = \)d × n/2, karena laporan yang salah menyiratkan a mayoritas node buruk. Oleh karena itu, musuh harus membayar setidaknya imbalan ini menyuap node sewenang-wenang. Jadi, untuk menyuap mayoritas node, musuh harus membayar a suap yang besar kepada sebagian besar node, yaitu lebih dari $dn2/2. Kami menunjukkan secara skematis cara kerja peningkatan kewaspadaan dan pengawasan pada Gambar 15.9.4.1 Rincian Mekanisme Lebih Lanjut Sistem tahan suap yang sekarang kami uraikan secara lebih rinci adalah sebuah sketsa sederhana konstruksi dua tingkat yang ingin kami bangun. Sebagian besar fokus kami adalah mendeskripsikan jaringan tingkat pertama (selanjutnya disebut “jaringan” jika jelas dari konteksnya). beserta mekanisme insentifnya dan tata cara eskalasinya ke tingkat kedua. Pertimbangkan jaringan Chainlink yang terdiri dari n oracle node yang bertanggung jawab untuk secara teratur (misalnya, sekali dalam satu menit) melaporkan nilai boolean (misalnya, apakah pasar kapitalisasi BTC melebihi ETH). Sebagai bagian dari mekanisme staking, node harus memberikan dua deposit: deposit $d yang dapat dipotong jika terjadi perselisihan dengan mayoritas dan deposit pengawas $dw dapat dipotong jika terjadi kesalahan eskalasi. Kami berasumsi bahwa node tidak dapat menyalin kiriman dari node lain, misalnya, melalui skema komitmen-pengungkapan seperti yang dibahas dalam Bagian 5.3. Di setiap putaran, node terlebih dahulu berkomitmen pada laporannya, dan setelah semua node telah berkomitmen (atau batas waktu telah habis), node mengungkapkan laporan mereka. Untuk setiap laporan yang akan dihasilkan, setiap node juga diberikan prioritas pengawas antara 1 dan n yang dipilih secara acak, dengan 1 sebagai prioritas utama. Prioritas ini memungkinkan konsentrasi imbalan di tangan satu anjing penjaga. Setelah semua laporan bersifat publik, fase peringatan terjadi. Selama urutan n putaran (sinkron), simpul dengan prioritas i mempunyai kesempatan untuk waspada pada putaran i. Mari kita pertimbangkan kemungkinan hasil dari mekanisme tersebut setelah node terungkap laporan mereka. Sekali lagi dengan asumsi laporan biner, misalkan nilai yang benar adalah benar dan yang salah adalah salah. Misalkan juga mekanisme tingkat pertama menghasilkan output nilai mayoritas keluaran oleh node sebagai laporan akhir r. Ada tiga kemungkinan hasil dalam mekanisme ini: • Kesepakatan lengkap: Dalam kasus terbaik, node-node sepenuhnya sepakat: semua node tersedia dan telah memberikan laporan tepat waktu dengan nilai r yang sama (baik benar atau salah). Dalam hal ini, jaringan hanya perlu meneruskan r ke kontrak yang diandalkan dan menghadiahi setiap node dengan pembayaran tetap per putaran $p, yang jauh lebih kecil dari $d. • Kesepakatan sebagian: Ada kemungkinan bahwa beberapa node sedang offline atau terdapat perbedaan pendapat mengenai nilai mana yang benar, namun sebagian besar node melaporkan nilai yang benar dan hanya sebagian kecil yang melaporkan nilai yang benar. minoritas melaporkan palsu. Kasus ini juga sangat mudah. Nilai mayoritas (benar) dihitung, menghasilkan laporan yang benar r. Semua node yang melaporkan r adalah diberi hadiah $p sedangkan oracle yang melaporkan salah mendapatkan depositnya dipotong sedikit, misalnya sebesar $10p. • Peringatan: Jika pengawas yakin bahwa keluaran jaringan salah, itu secara publik memicu peringatan, meningkatkan mekanisme ke jaringan tingkat kedua. Ada dua kemungkinan hasil: – Peringatan yang benar: Jika jaringan lapis kedua mengonfirmasi bahwa output dariGambar 16: Memperbesar kerugian bagi penyuap melalui imbalan peringatan yang terkonsentrasi. Sebuah suap Musuh harus menyuap setiap node dengan lebih dari imbalan yang bisa diperoleh dengan memberikan peringatan (ditampilkan sebagai bilah merah). Jika imbalan peringatan dibagikan, maka imbalan ini mungkin relatif kecil. Imbalan peringatan terkonsentrasi meningkatkan imbalan yang mungkin dimiliki oleh node mana pun dapatkan (bilah merah tinggi). Akibatnya, total pembayaran yang dilakukan musuh untuk suap yang layak (wilayah abu-abu) jauh lebih besar dengan imbalan peringatan yang terkonsentrasi dibandingkan dengan imbalan peringatan bersama. jaringan tingkat pertama salah, node pengawas yang memberi peringatan menerima hadiah terdiri dari semua deposit yang dipotong, dan dengan demikian lebih dari $dn/2. – Peringatan salah: Jika oracle tingkat kedua dan tingkat pertama setuju, eskalasinya adalah dianggap salah dan node peringatan kehilangan deposit $dw-nya. Dalam kasus penerimaan laporan yang optimis, peringatan pengawas tidak menimbulkan setiap perubahan dalam pelaksanaan kontrak yang bergantung. Untuk kontrak yang dirancang untuk menunggu potensi arbitrase oleh komite tingkat kedua, peringatan pengawas tertunda namun jangan membekukan pelaksanaan kontrak. Kontrak juga dapat menunjuk a failover DON untuk periode ajudikasi. 9.4.2 Dampak Taruhan Kuadrat Kemampuan setiap node untuk bertindak sebagai pengawas, dikombinasikan dengan prioritas node yang ketat memastikan imbalan terkonsentrasi, memungkinkan mekanisme mencapai staking kuadrat dampak untuk setiap jenis pelaku penyuapan yang dijelaskan dalam Bagian 9.3.3. Ingatlah bahwa ini berarti secara khusus dalam pengaturan kami bahwa, untuk jaringan dengan n node yang masing-masing memiliki deposit $d, penyuap yang sukses (salah satu jenis di atas) harus memiliki anggaran lebih besar dari $dn2/2. Tepatnya, penyuap harus merusak setidaknya (n+1)/2 node, karena penyuap harus melakukannya merusak sebagian besar n node (untuk n ganjil, dengan asumsi). Oleh karena itu, ada pengawas yang berdiri tegak dapatkan hadiah $d(n + 1)/2. Oleh karena itu, penyuap harus membayar jumlah ini kepada setiap orangsimpul untuk memastikan bahwa tidak ada yang bertindak sebagai anjing penjaga. Kami berupaya untuk menunjukkan secara formal bahwa jika penyuap memiliki anggaran paling banyak $d(n2 + n)/2, maka subgame keseimbangan sempurna permainan antara penyuap dan oracles—dengan kata lain, keseimbangan di titik mana pun selama permainan ini berlangsung—adalah agar si penyuap tidak memberikan suapnya dan untuk itu setiap oracle melaporkan nilai sebenarnya dengan jujur. Kami telah menjelaskan di atas bagaimana mungkin seorang penyuap yang berhasil memerlukan a anggarannya jauh lebih besar daripada jumlah simpanan simpul. Untuk menggambarkan hal ini hasil intuitif, Gambar 16 menunjukkan dampak penghargaan peringatan terkonsentrasi secara grafis. Seperti yang kita lihat di sana, kalau imbalannya bagi pengawas waspada—yakni titipan orang yang disuap node yang melaporkan salah)—dibagi di antara semua peringatan potensial, jumlah totalnya setiap node peringatan yang diharapkan akan berukuran relatif kecil $d. Seorang penyuap, yang mengetahui bahwa pembayaran lebih besar dari $d tidak mungkin dilakukan, dapat menggunakannya suap bersyarat hasil palsu untuk menyuap masing-masing n node dengan sedikit lebih dari $d + ϵ. Secara berlawanan, Gambar 16 menunjukkan bahwa suatu sistem yang mendistribusikan imbalan secara luas di antara node yang memberi sinyal peringatan jauh lebih lemah daripada node yang memusatkan hadiahnya tangan seekor anjing penjaga. Contoh parameter: Pertimbangkan jaringan (tingkat pertama) dengan n = 100 node, masing-masing menyetor \(d = \)20K. Jaringan ini akan memiliki total $2 juta yang disetorkan tetapi akan tetap ada dilindungi dari penyuap dengan anggaran \(100M = \)dn2/2. Meningkatkan jumlah oracles tentu saja lebih efektif daripada menaikkan $d, dan dapat memberikan efek yang dramatis: jaringan dengan n = 300 node dan deposit \(d = \)20K akan dilindungi dari a penyuap dengan anggaran hingga $900 juta. Perhatikan bahwa sistem staking dalam banyak kasus dapat melindungi smart contract yang mewakili nilai lebih dari tingkat perlindungan suap yang ditawarkan. Ini karena musuh menyerang kontrak-kontrak ini tidak dapat memperoleh nilai penuh dalam banyak kasus. Misalnya, a Kontrak bertenaga Chainlink yang mendapatkan nilai $1 miliar mungkin hanya memerlukan jaminan terhadap a penyuap dengan sumber daya sebesar $100 juta karena musuh dapat mengambil keuntungan hanya 10% dari nilai kontrak. Catatan: Gagasan bahwa nilai jaringan dapat tumbuh secara kuadratik diungkapkan dalam Hukum Metcalfe yang terkenal [167, 235], yang menyatakan bahwa nilai jaringan tumbuh secara kuadrat dalam jumlah entitas yang terhubung. Namun, Hukum Metcalfe muncul dari pertumbuhan jumlah koneksi jaringan berpasangan potensial, sebuah fenomena yang berbeda dari dampak kuadratik staking dalam insentif kami mekanisme. 9.4.3 Realisasi Tingkat Kedua Dua fitur operasional memfasilitasi realisasi tingkat kedua dengan keandalan tinggi: (1) Keputusan tingkat kedua seharusnya jarang terjadi di jaringan oracle dan oleh karena itu dapat terjadi menjadi jauh lebih mahal daripada operasi normal tingkat pertama dan (2) Dengan asumsilaporan yang diterima secara optimis—atau kontrak yang pelaksanaannya dapat menunggu arbitrase— tingkat kedua tidak perlu dijalankan secara real time. Fitur-fitur ini menghasilkan beragam opsi konfigurasi untuk tingkat kedua untuk memenuhi persyaratan DON tertentu. Sebagai contoh pendekatan, komite tingkat kedua dapat terdiri dari simpul-simpul yang dipilih oleh a DON (yaitu, tingkat pertama) dari node dengan layanan terlama dan paling andal di Chainlink jaringan. Selain pengalaman operasional yang cukup relevan, operator dari node tersebut memiliki insentif implisit yang cukup besar dalam FFO yang memotivasi keinginan untuk memastikan bahwa jaringan Chainlink tetap dapat diandalkan. Mereka juga melakukannya secara terbuka riwayat kinerja yang tersedia yang memberikan transparansi mengenai keandalannya. Node tingkat kedua, perlu dicatat, tidak perlu menjadi peserta dalam jaringan tingkat pertama, dan dapat memutuskan kesalahan di beberapa jaringan tingkat pertama. Node dalam DON tertentu dapat ditunjuk terlebih dahulu dan berkomitmen secara publik ke himpunan n′ tersebut node sebagai komite tingkat kedua untuk DON itu. Selain itu, DON node menerbitkan parameter k′ ≤n′ yang menentukan jumlah suara tingkat kedua diperlukan untuk menghukum node tingkat pertama. Saat peringatan dibuat untuk laporan tertentu, anggota tingkat kedua memberikan suara pada kebenaran nilai yang diberikan masing-masing dari node tingkat pertama. Setiap node tingkat pertama yang menerima k′ suara negatif akan kehilangan node tersebut deposit ke node pengawas. Karena jarangnya proses peradilan dan adanya kesempatan eksekusi yang memakan waktu lama disebutkan di atas, berbeda dengan tingkat pertama, node di tingkat kedua dapat: 1. Mendapatkan kompensasi yang tinggi untuk melakukan ajudikasi. 2. Memanfaatkan sumber data tambahan, bahkan melebihi beragam sumber data yang digunakan oleh data tingkat pertama. 3. Mengandalkan inspeksi dan intervensi manual dan/atau ahli, misalnya untuk mengidentifikasi dan merekonsiliasi kesalahan dalam data sumber dan membedakan antara penyampaian node yang jujur data yang salah dan node yang berperilaku buruk. Kami menekankan bahwa pendekatan yang baru saja kami jelaskan untuk pemilihan simpul tingkat kedua dan keputusan yang mengatur kebijakan hanya mewakili satu titik dalam rentang yang luas. ruang desain kemungkinan realisasi tingkat kedua. Mekanisme insentif kami menawarkan fleksibilitas penuh mengenai bagaimana tingkat kedua diwujudkan. Dengan demikian, individu DON dapat melakukannya menyusun dan menetapkan aturan untuk tingkat kedua yang memenuhi persyaratan tertentu dan harapan node dan pengguna yang berpartisipasi. DECO dan Town Crier sebagai alat penilaian: Ini penting untuk tingkat kedua dalam mekanisme kami untuk dapat membedakan antara node tingkat pertama yang bermusuhan itu sengaja menghasilkan laporan yang salah dan node tingkat pertama yang jujur secara tidak sengaja menyampaikan data yang salah pada sumbernya. Hanya dengan cara inilah tingkat kedua dapat diimplementasikan pemotongan untuk mendisinsentifkan kecurangan, yang merupakan tujuan dari mekanisme kami. DECO dan Town Crier adalah alat canggih yang memungkinkan node tingkat kedua membuat perbedaan penting ini andal.Node tingkat kedua dalam beberapa kasus mungkin dapat langsung menanyakan sumber data yang digunakan oleh node tingkat pertama atau gunakan ADO Bagian 7.1 untuk memeriksa apakah laporan salah disebabkan oleh sumber data yang salah. Namun dalam kasus lain, node tingkat kedua mungkin kurang akses langsung ke sumber data node tingkat pertama. Dalam kasus seperti ini, keputusan yang tepat akan diperlukan tampaknya tidak layak atau memerlukan ketergantungan pada penilaian subjektif. Sebelumnya oracle sistem perselisihan mengandalkan putaran pemungutan suara yang tidak efisien dan meningkat untuk mengatasi hal tersebut tantangan. Namun, dengan menggunakan DECO atau Town Crier, node tingkat pertama dapat membuktikan perilaku yang benar ke node tingkat kedua. (Lihat Bagian 3.6.2 untuk rincian mengenai kedua sistem tersebut.) Khususnya, jika simpul tingkat kedua mengidentifikasi simpul tingkat pertama yang mempunyai keluaran nilai laporan yang salah ˜r, node tingkat pertama dapat menggunakan DECO atau Town Crier untuk menghasilkan bukti anti kerusakan node tingkat kedua yang di-relay dengan benar dari sumber (yang mendukung TLS). diakui sebagai otoritatif oleh DON. Yang terpenting, node tingkat pertama dapat melakukan hal ini tanpa node tingkat kedua yang memerlukan akses langsung ke sumber data.17 Akibatnya, penilaian yang benar dapat dilakukan di Chainlink untuk sumber data apa pun yang diinginkan. 9.4.4 Asuransi yang Salah Pelaporan Kuatnya penolakan terhadap suap yang dicapai oleh mekanisme staking kami sangat bergantung pada hal ini tentang pemotongan dana yang diberikan kepada pemberi peringatan. Tanpa imbalan uang, pemberi peringatan akan melakukannya tidak mempunyai insentif langsung untuk menolak suap. Namun alhasil, dana yang terpangkas tidak jadi tersedia untuk memberi kompensasi kepada pengguna yang dirugikan oleh laporan yang salah, misalnya pengguna yang kehilangan uang ketika data harga yang salah diteruskan ke smart contract. Diasumsikan bahwa laporan yang salah tidak akan menjadi masalah jika laporan tersebut diterima oleh a kontrak hanya setelah kemungkinan pengambilan keputusan, yaitu tindakan oleh tingkat kedua. Seperti yang dijelaskan Namun, untuk mencapai kinerja terbaik, kontrak dapat diandalkan optimis terhadap mekanisme penegakan pelaporan yang benar, artinya mereka menerima laporan sebelum kemungkinan keputusan tingkat kedua. Memang perilaku optimis seperti itu aman dalam model kami dengan asumsi musuh rasional yang anggarannya tidak melebihi staking dampak mekanisme. Pengguna khawatir tentang kemungkinan terjadinya kegagalan mekanisme akibat, misalnya, musuh yang memiliki sumber daya finansial yang besar, mungkin ingin menerapkan lapisan tambahan keamanan ekonomi dalam bentuk asuransi kesalahan pelaporan. Kami tahu banyak perusahaan asuransi yang berniat menawarkan polis yang didukung kontrak cerdas semacam ini untuk protokol yang diamankan Chainlink dalam waktu dekat, termasuk melalui mekanisme inovatif seperti DAOs, misalnya, [7]. Keberadaan riwayat kinerja untuk Chainlink node dan data lain tentang node seperti jumlah taruhannya memberikan dasar yang sangat kuat untuk penilaian risiko aktuaria, sehingga memungkinkan penetapan harga kebijakan dengan cara yang murah bagi pemegang polis namun berkelanjutan bagi perusahaan asuransi. 17Dengan Town Crier, node tingkat pertama juga dapat menghasilkan pengesahan secara lokal kebenaran laporan yang mereka hasilkan dan memberikan pengesahan ini ke node tingkat kedua di suatu dasar sesuai kebutuhan.Bentuk dasar asuransi misreporting dapat diterapkan dengan cara yang dapat dipercaya dan cara yang efisien menggunakan smart contracts. Sebagai contoh sederhana, asuransi parametrik kontrak SCins dapat memberikan kompensasi kepada pemegang polis secara otomatis jika mekanisme insentif kami sesuai tingkat kedua mengidentifikasi kesalahan dalam laporan yang dihasilkan di tingkat pertama. Pengguna U yang ingin membeli polis asuransi, misalnya pembuat target kontrak SC, dapat mengajukan permintaan ke perusahaan asuransi yang terdesentralisasi untuk sejumlah polis $M pada kontrak. Saat menyetujui U, perusahaan asuransi dapat menetapkan jangka waktu yang berkelanjutan (misalnya, bulanan) premi $P dalam SCins. Meskipun U membayar premi, polisnya tetap aktif. Jika terjadi kegagalan pelaporan pada SC, maka hasilnya adalah emisi pasangan (r1, r2) laporan yang bertentangan untuk SC, di mana r1 ditandatangani oleh tingkat pertama dalam mekanisme kami dan r2, laporan koreksi terkait, ditandatangani oleh tingkat kedua. Jika U melengkapi pasangan yang valid (r1, r2) ke SCins, kontrak secara otomatis membayarnya $M, asalkan pembayaran preminya mutakhir. 9.5 Varian Putaran Tunggal Protokol yang dijelaskan dalam sub-bagian sebelumnya mengharuskan komite tingkat kedua menunggu beberapa putaran untuk menentukan apakah lembaga pengawas telah memberikan peringatan. Ini Persyaratan ini berlaku bahkan dalam kasus yang optimis, yaitu ketika tingkat pertama berfungsi dengan benar. Bagi pengguna yang tidak mau menerima laporan secara optimis, yaitu sebelum potensinya keputusan pengadilan, penundaan yang terkait dengan pendekatan itu tidak akan bisa dijalankan. Oleh karena itu, kami juga menjajaki protokol alternatif yang hanya memerlukan satu protokol bulat. Dalam pendekatan ini, semua node oracle mengirimkan bit rahasia yang menunjukkan apakah atau tidak mereka ingin meningkatkan kewaspadaan. Komite tingkat kedua kemudian memeriksa nilai-nilai ini urutan prioritas. Untuk memberikan gambaran kasar, skema tersebut mungkin melibatkan hal berikut langkah-langkah: 1. Pengiriman bit pengawas: Setiap node rahasia Oi berbagi nilai pengawas satu bit wi ∈{no alert, alert} di antara node di tingkat kedua untuk setiap laporan yang dihasilkannya. 2. Tip anonim: Setiap node oracle dapat mengirimkan tip anonim α ke komite tingkat kedua pada putaran yang sama saat bit pengawas dikirimkan. Tip ini α adalah pesan yang menunjukkan bahwa peringatan telah dimunculkan untuk laporan saat ini. 3. Pemeriksaan bit pengawas: Komite tingkat kedua mengungkapkan oracle pengawas node bit dalam urutan prioritas. Perhatikan bahwa node tidak boleh mengirimkan bit pengawas peringatan ketika mereka tidak memberikan peringatan: jika tidak, analisis lalu lintas akan mengungkapkan semua bit node. Protokol memang mengungkapkan tidak ada peringatan bit pengawas dari node dengan prioritas lebih tinggi daripada pengawas peringatan dengan prioritas tertinggi. Perhatikan bahwa apa yang terungkap identik dengan protokol n-round kita. Imbalan juga didistribusikan secara identik dengan skema tersebut, yaitu pengawas yang pertama kali diidentifikasi menerima potongan simpanan dari node yang telah mengirimkan laporan yang salah.Penggunaan tip anonim memungkinkan komite tingkat kedua untuk tetap non-interaktif jika tidak ada peringatan yang disampaikan, sehingga mengurangi kompleksitas komunikasi dalam kasus umum. Perhatikan bahwa pengawas mana pun yang memberikan peringatan mempunyai insentif ekonomi untuk mengirimkan tip anonim: Jika tidak ada tip yang dikirimkan, tidak ada imbalan yang dibayarkan kepada siapa pun. simpul. Untuk memastikan bahwa pengirim Oi dari tip anonim α tidak dapat diidentifikasi oleh musuh berdasarkan data jaringan, tip anonim dapat dikirim melalui anonim saluran, misalnya melalui Tor, atau, lebih praktisnya, diproksi melalui penyedia layanan cloud. Untuk mengautentikasi ujungnya sebagai berasal dari O, Oi dapat menandatangani α menggunakan tanda tangan cincin [39, 192]. Alternatifnya, untuk mencegah serangan penolakan layanan yang tidak dapat diatribusikan terhadap komite tingkat kedua oleh node oracle yang berbahaya, α dapat berupa kredensial anonim dengan anonimitas yang dapat dibatalkan [73]. Protokol ini, meskipun secara praktis dapat dicapai, memiliki rekayasa kelas berat persyaratan (yang sedang kami cari cara untuk menguranginya). Node tingkat pertama, misalnya, harus berkomunikasi langsung dengan node tingkat kedua, yang memerlukan pemeliharaan direktori. Kebutuhan akan saluran anonim dan tanda tangan dering menambah rekayasa kompleksitas skema. Terakhir, ada persyaratan kepercayaan khusus yang dibahas secara singkat dalam catatan di bawah ini. Oleh karena itu, kami juga menjajaki skema yang lebih sederhana yang masih bisa dicapai dampak super-linier staking, namun mungkin kurang dari dampak kuadrat, di mana penyuap membutuhkan sumber daya minimal $n log n, misalnya. Beberapa skema di bawah ini pertimbangan melibatkan pemilihan acak dari subset node yang ketat untuk bertindak sebagai anjing penjaga, dalam hal ini calon suap menjadi serangan yang sangat kuat. Catatan: Keamanan mekanisme staking putaran tunggal ini tidak dapat dimanfaatkan saluran antara oracle dan node tingkat kedua—sebuah persyaratan standar dalam sistem yang tahan terhadap paksaan, misalnya, pemungutan suara [82, 138], dan merupakan persyaratan yang masuk akal dalam praktiknya. Namun, selain itu, simpul Oi yang berupaya bekerja sama dengan penyuap dapat dibangun bagian rahasianya sedemikian rupa untuk menunjukkan kepada penyuap bahwa ia telah mengkodekan suatu hal tertentu nilai. Misalnya, jika Oi tidak mengetahui node mana yang dikontrol oleh penyuap, maka Oi bisa menyerahkan saham bernilai 0 kepada seluruh anggota komite. Penyuap kemudian dapat memverifikasi milik Oi kepatuhan secara probabilistik. Untuk menghindari masalah ini dalam protokol putaran tunggal mana pun, kami mengharuskan Oi mengetahui identitas setidaknya satu node tingkat kedua yang jujur. Dengan protokol interaktif di mana setiap node tingkat kedua menambahkan pengacakan faktor untuk berbagi, hal terbaik yang dapat dilakukan penyuap adalah memaksakan seleksi oleh Oi secara acak sedikit pengawas. 9.6 Kerangka Insentif Implisit (IIF) FFO adalah bentuk insentif implisit untuk perilaku yang benar di jaringan Chainlink. Itu berfungsi seperti kepemilikan eksplisit, yaitu simpanan, yang membantu menegakkan keamanan ekonomi jaringan. Dengan kata lain, FFO harus dimasukkan sebagai bagian dari deposit (efektif). $d dari sebuah node di jaringan.Pertanyaannya adalah: Bagaimana kita mengukur FFO dan bentuk insentif implisit lainnya dalam jaringan Chainlink? Kerangka Insentif Implisit (IIF) adalah seperangkat prinsip dan teknik yang kami rencanakan untuk dikembangkan untuk tujuan ini. Sistem blockchain memberikan berbagai bentuk transparansi yang belum pernah terjadi sebelumnya, dan catatan node Kinerja yang mereka hasilkan merupakan batu loncatan bagi visi kami mengenai bagaimana IIF akan bekerja. Di sini kami secara singkat menguraikan ide-ide tentang elemen-elemen kunci IIF. IIF sendiri akan terdiri dari serangkaian faktor yang kami anggap penting dalam evaluasi insentif implisit, serta mekanisme untuk mempublikasikan data yang relevan dalam bentuk jaminan tinggi untuk dikonsumsi oleh algoritma analitik. Chainlink pengguna yang berbeda mungkin ingin menggunakan IIF dengan cara yang berbeda, misalnya memberikan bobot yang berbeda pada faktor yang berbeda. Kami berharap layanan analitik muncul di komunitas yang membantu pengguna menerapkan IIF sesuai dengan preferensi evaluasi risiko masing-masing, dan tujuan kami adalah untuk memfasilitasi layanan tersebut dengan memastikan akses mereka terhadap data pendukung yang terjamin dan tepat waktu, seperti yang kita bahas di bawah (Bagian 9.6.4). 9.6.1 Peluang Biaya di Masa Depan Node berpartisipasi dalam ekosistem Chainlink untuk mendapatkan bagian dari biaya yang dibayarkan jaringan untuk berbagai layanan yang telah kami jelaskan dalam makalah ini, mulai dari umpan data biasa ke layanan tingkat lanjut seperti identitas terdesentralisasi, pengurutan yang adil, dan menjaga kerahasiaan DeFi. Biaya dalam biaya operator node dukungan jaringan Chainlink, misalnya, menjalankan server, memperoleh lisensi data yang diperlukan, dan memelihara staf global untuk memastikan waktu kerja yang tinggi. FFO menunjukkan biaya layanan, setelah dikurangi biaya, yang akan diperoleh node di masa depan—atau rugi jika node tersebut menunjukkan perilaku yang salah. FFO adalah bentuk taruhan yang membantu mengamankan jaringan. Fitur yang berguna dari FFO adalah kenyataan bahwa data on-chain (dilengkapi dengan data off-chain data) membuat catatan sejarah node dengan tingkat kepercayaan tinggi, sehingga memungkinkan penghitungan FFO secara transparan dan didorong oleh empiris. Pengukuran FFO tingkat pertama yang sederhana dapat diperoleh dari pendapatan bersih rata-rata a node selama periode waktu tertentu (yaitu, pendapatan kotor dikurangi biaya operasional). FFO mungkin kemudian dihitung sebagai, misalnya, nilai sekarang bersih [114] dari pendapatan bersih kumulatif di masa depan, dengan kata lain, nilai diskon waktu dari semua pendapatan di masa depan. Namun, pendapatan node bisa berubah-ubah, seperti yang ditunjukkan misalnya pada Gambar 17. Yang lebih penting lagi, pendapatan node mungkin tidak mengikuti distribusi yang stasioner seiring berjalannya waktu. Oleh karena itu, faktor-faktor lain yang kami rencanakan untuk dieksplorasi dalam memperkirakan FFO meliputi: • Riwayat kinerja: Riwayat kinerja operator—termasuk kebenaran dan ketepatan waktu laporannya, serta waktu operasionalnya—memberikan suatu tujuan batu ujian bagi pengguna untuk mengevaluasi keandalannya. Riwayat kinerja akan demikian memberikan faktor penting dalam pemilihan oracle node oleh pengguna (atau, dengan munculnya dari DONs, pilihan mereka DONs). Riwayat kinerja yang kuat kemungkinan besar akan terjadi berkorelasi dengan pendapatan berkelanjutan yang tinggi.18 18Pertanyaan penelitian penting yang ingin kami jawab adalah deteksi volume layanan yang dipalsukan.Gambar 17: Pendapatan yang diperoleh Chainlink node pada satu data feed (ETH-USD) selama minggu perwakilan pada bulan Maret 2021. • Akses data: Meskipun oracle dapat memperoleh berbagai bentuk data dari API terbuka, bentuk data tertentu atau sumber tertentu yang berkualitas tinggi mungkin hanya tersedia di a berdasarkan langganan atau melalui perjanjian kontrak. Akses istimewa ke tertentu sumber data dapat berperan dalam menciptakan aliran pendapatan yang stabil. • Partisipasi DON: Dengan munculnya DONs, komunitas node akan datang bersama-sama untuk memberikan layanan tertentu. Kami berharap banyak DON yang akan disertakan operator secara selektif, menetapkan partisipasi dalam DONs yang memiliki reputasi baik sebagai a posisi pasar istimewa yang membantu memastikan sumber pendapatan yang konsisten. • Aktivitas lintas platform: Beberapa operator node mungkin memiliki rekam jejak kehadiran dan kinerja yang baik dalam konteks lain, misalnya, sebagai PoS validators atau penyedia data dalam konteks non-blockchain. Kinerja mereka dalam sistem lain ini (ketika data tersedia dalam bentuk yang dapat dipercaya) dapat menjadi masukan dalam evaluasi sejarah kinerja mereka. Demikian pula, perilaku salah di jaringan Chainlink dapat membahayakan pendapatan di sistem lain ini dengan mengusir pengguna, misalnya FFO dapat meluas ke seluruh platform. 9.6.2 FFO spekulatif Operator node berpartisipasi dalam jaringan Chainlink bukan hanya untuk menghasilkan pendapatan operasi, tetapi untuk menciptakan dan memposisikan diri untuk memanfaatkan peluang baru dalam menjalankan pekerjaan. Dengan kata lain, pengeluaran sebesar oracle node dalam jaringan juga pernyataan positif tentang masa depan DeFi dan aplikasi kontrak pintar lainnya domain serta aplikasi non-blockchain yang muncul dari jaringan oracle. Operator node saat ini mendapatkan biaya yang tersedia di jaringan Chainlink yang ada dan secara bersamaan Hal ini mirip dengan ulasan palsu di situs internet, hanya saja masalahnya lebih mudah di dalamnya oracle pengaturan karena kami memiliki catatan pasti apakah barang, yaitu laporan, dipesan dan dikirimkan—berbeda dengan, misalnya, barang fisik yang dipesan di toko online. Dengan kata lain, di oracle pengaturan, kinerja dapat divalidasi, meskipun kebenaran pelanggan tidak bisa.membangun reputasi, riwayat kinerja, dan keahlian operasional yang akan diposisikan mereka secara menguntungkan untuk mendapatkan biaya yang tersedia di jaringan masa depan (tentu saja bergantung pada pada perilaku jujur). Node yang beroperasi di ekosistem Chainlink saat ini akan melakukan hal ini sense memiliki keuntungan dibandingkan pendatang baru dalam mendapatkan bayaran sebagai tambahan Chainlink layanan menjadi tersedia. Keuntungan ini berlaku untuk operator baru, serta perusahaan teknologi dengan reputasi yang sudah mapan; misalnya, T-Systems, yang tradisional penyedia teknologi (anak perusahaan Deutsche Telekom), dan Kraken, yang terpusat besar pertukaran, telah hadir sejak awal di ekosistem Chainlink [28, 143]. Partisipasi oracle node dalam peluang masa depan dapat dianggap sebagai hal yang tersendiri sebagai semacam FFO spekulatif, dan dengan demikian merupakan suatu bentuk kepemilikan di Chainlink jaringan. 9.6.3 Reputasi Eksternal IIF seperti yang telah kami jelaskan dapat beroperasi dalam jaringan dengan nama samaran operator, yaitu tanpa pengungkapan orang atau entitas dunia nyata yang terlibat. Namun, salah satu faktor yang berpotensi penting dalam pemilihan penyedia layanan adalah faktor eksternal reputasi. Yang kami maksud dengan reputasi eksternal adalah persepsi mengenai kepercayaan yang melekat pada identitas dunia nyata, bukan nama samaran. Risiko reputasi yang melekat pada identitas dunia nyata dapat dipandang sebagai bentuk insentif implisit. Kami memandang reputasi melalui kacamata IIF, yaitu dalam pengertian ekonomi kripto, sebagai sarana untuk membangun aktivitas lintas platform yang dapat dimasukkan ke dalam estimasi FFO. Sebaliknya, manfaat menggunakan reputasi eksternal sebagai faktor dalam memperkirakan FFO dengan hubungan pseudonim, adalah bahwa reputasi eksternal menghubungkan kinerja tidak hanya dengan suatu aktivitas operator saat ini, namun juga aktivitas di masa depan. Kalau misalnya reputasinya buruk jika melekat pada seseorang, hal ini dapat mencemari usaha orang tersebut di masa depan. Dengan kata lain, reputasi eksternal dapat mencakup FFO yang lebih luas dibandingkan nama samaran catatan kinerja, sebagai dampak penyimpangan yang melekat pada diri seseorang atau ditetapkan perusahaan lebih sulit untuk melarikan diri daripada yang terkait dengan operasi nama samaran. Chainlink kompatibel dengan teknologi identitas terdesentralisasi (Bagian 4.3) itu dapat memberikan dukungan untuk penggunaan reputasi eksternal di IIF. Teknologi seperti itu dapat memvalidasi dan dengan demikian membantu memastikan kebenaran pernyataan operator di dunia nyata identitas.19 9.6.4 Buka IIF Analytics IIF, seperti yang telah kami catat, bertujuan untuk menyediakan data dan alat sumber terbuka yang andal analisis insentif implisit. Tujuannya adalah untuk mengaktifkan penyedia dalam komunitas untuk mengembangkan analisis yang disesuaikan dengan kebutuhan penilaian risiko di berbagai bagian dunia Chainlink basis pengguna. 19Kredensial identitas yang terdesentralisasi juga dapat, jika diinginkan, menghiasi nama samaran dengan nama yang divalidasi informasi tambahan. Misalnya, operator node pada prinsipnya dapat menggunakan kredensial tersebut untuk membuktikan bahwa itu adalah perusahaan Fortune 500, tanpa mengungkapkan yang mana.Sejumlah besar data historis mengenai pendapatan dan kinerja node berada pada rantai dalam bentuk kepercayaan tinggi dan tidak dapat diubah. Namun, tujuan kami adalah menyediakan data selengkap mungkin, termasuk data tentang perilaku yang hanya terlihat di luar rantai, seperti Off-Chain Reporting (OCR) atau aktivitas DON. Data tersebut berpotensi menjadi banyak. Cara terbaik untuk menyimpannya dan memastikan integritasnya, yaitu melindunginya dari kami yakin, gangguan akan dilakukan dengan bantuan DONs, menggunakan teknik yang telah dibahas di Bagian 3.3. Beberapa insentif dapat digunakan dalam bentuk pengukuran langsung, seperti staking deposito dan FFO dasar. Lainnya, seperti FFO spekulatif dan reputasi, lebih sulit dilakukan mengukur secara obyektif, namun kami yakin bahwa bentuk data pendukung, termasuk pertumbuhan historis ekosistem Chainlink, metrik reputasi media sosial, dll., dapat mendukung model analitik IIF bahkan untuk elemen-elemen yang sulit diukur. Kita dapat membayangkan bahwa DON khusus muncul secara khusus untuk memantau, memvalidasi, dan mencatat data yang berkaitan dengan catatan kinerja off-chain node, serta data lainnya digunakan di IIF, seperti informasi identitas yang divalidasi. DON ini dapat memberikan data IIF yang seragam dan memiliki tingkat kepercayaan tinggi untuk setiap penyedia analisis yang melayani komunitas Chainlink. Mereka juga akan memberikan catatan emas yang sesuai dengan klaim penyedia analitik dapat diverifikasi secara independen oleh masyarakat. 9.7 Menyatukan Semuanya: Insentif Operator Node Mensintesis diskusi kami di atas mengenai insentif eksplisit dan implisit untuk operator node memberikan pandangan holistik tentang cara operator node berpartisipasi dan mendapatkan manfaatnya jaringan Chainlink. Sebagai panduan konseptual, kita dapat menyatakan total aset yang dipertaruhkan dengan Chainlink tertentu operator simpul $S dalam bentuk kasar dan bergaya seperti: \(S ≈\)D + \(F + \)FS + $R, dimana: • $D adalah agregat dari seluruh saham yang disimpan secara eksplisit di semua jaringan di mana operator berpartisipasi; • $F adalah nilai sekarang bersih dari agregat seluruh FFO di seluruh jaringan di dimana operator berpartisipasi; • $FS adalah nilai sekarang bersih dari FFO spekulatif operator; dan • $R adalah ekuitas reputasi operator di luar ekosistem Chainlink yang mungkin terancam oleh perilaku buruk yang teridentifikasi di node oracle-nya. Meskipun sebagian besar bersifat konseptual, persamaan kasar ini menunjukkan bahwa terdapat beragam faktor ekonomi yang mendukung kinerja keandalan tinggi pada Chainlink node. Semua faktor ini selain $D terdapat di jaringan Chainlink saat ini.9.8 Siklus Kebajikan Keamanan Ekonomi Kombinasi dampak staking super-linear dengan representasi pembayaran biaya karena peluang biaya masa depan (FFO) di IIF dapat mengarah pada apa yang kita sebut sebagai siklus baik (virtuous cycle). keamanan ekonomi dalam jaringan oracle. Hal ini dapat dilihat sebagai suatu bentuk perekonomian skala. Ketika jumlah total yang dijamin oleh jaringan tertentu meningkat, jumlahnya tambahan saham yang diperlukan untuk menambah jumlah keamanan ekonomi yang tetap akan menurun biaya rata-rata per pengguna. Oleh karena itu, dalam hal biaya, lebih murah bagi pengguna untuk bergabung jaringan yang sudah ada daripada mencapai peningkatan ekonomi jaringan yang sama keamanan dengan membuat jaringan baru. Yang penting, penambahan setiap pengguna baru semakin rendah biaya layanan untuk semua pengguna jaringan tersebut sebelumnya. Mengingat struktur biaya tertentu (misalnya tingkat hasil tertentu pada jumlah yang dipertaruhkan), jika total biaya yang diperoleh suatu jaringan meningkat, hal ini akan memberikan insentif terhadap aliran biaya tambahan mempertaruhkannya ke dalam jaringan untuk mengamankannya pada tingkat yang lebih tinggi. Khususnya jika total taruhan node individu mungkin ditahan dalam sistem dibatasi, kemudian ketika pembayaran biaya baru memasuki sistem, menaikkan FFO-nya, jumlah node n akan bertambah. Terima kasih kepada dampak staking super-linear dari desain sistem insentif kami, keamanan ekonomi sistem akan naik lebih cepat dari n, misalnya, seperti n2 dalam mekanisme yang kita buat sketsa di Bagian 9.4. Akibatnya, biaya rata-rata untuk keamanan ekonomi—yaitu jumlah kontribusi saham satu dolar keamanan ekonomi—akan turun. Oleh karena itu, jaringan dapat membebankan biaya kepada penggunanya biaya yang lebih rendah. Dengan asumsi bahwa permintaan untuk layanan oracle bersifat elastis (lihat, misalnya, [31] untuk gambaran singkatnya penjelasannya), permintaan akan meningkat sehingga menimbulkan biaya tambahan dan FFO. Kami mengilustrasikan hal ini dengan contoh berikut. Contoh 5. Karena keamanan ekonomi jaringan oracle dengan insentif kami skemanya adalah \(dn2 for stake \)dn, keamanan ekonomi disumbangkan oleh satu dolar saham adalah n dan dengan demikian biaya rata-rata per dolar keamanan ekonomi—yaitu, jumlah kepemilikan berkontribusi terhadap satu dolar keamanan ekonomi—adalah 1/n. Pertimbangkan sebuah jaringan yang insentif ekonominya seluruhnya terdiri dari FFO dan dibatasi pada \(d ≤\)10K per node. Misalkan jaringan mempunyai n = 3 node. Lalu biaya rata-rata per dolar keamanan ekonomi adalah sekitar $0,33. Misalkan total FFO jaringan naik di atas \(30K (e.g., to \)31K). Diberikan batas FFO per node, jaringan tumbuh menjadi (setidaknya) n = 4. Sekarang biaya rata-rata per dolar keamanan ekonomi turun menjadi sekitar $0,25. Kami mengilustrasikan seluruh siklus baik keamanan ekonomi di jaringan oracle secara skematis pada Gambar 18. Kami menekankan bahwa siklus baik keamanan ekonomi berasal dari dampaknya pengguna mengumpulkan biaya mereka. FFO kolektif merekalah yang menguntungkan perusahaan yang lebih besar ukuran jaringan dan dengan demikian keamanan kolektif yang lebih besar. Kami juga mencatat bahwa siklus yang baik keamanan ekonomi mendukung DON mencapai keberlanjutan finansial. Sekali dibuat, DON yang memenuhi kebutuhan pengguna harus berkembang hingga melampaui titik di mana pendapatan dari biaya melebihi biaya operasional untuk oracle node.
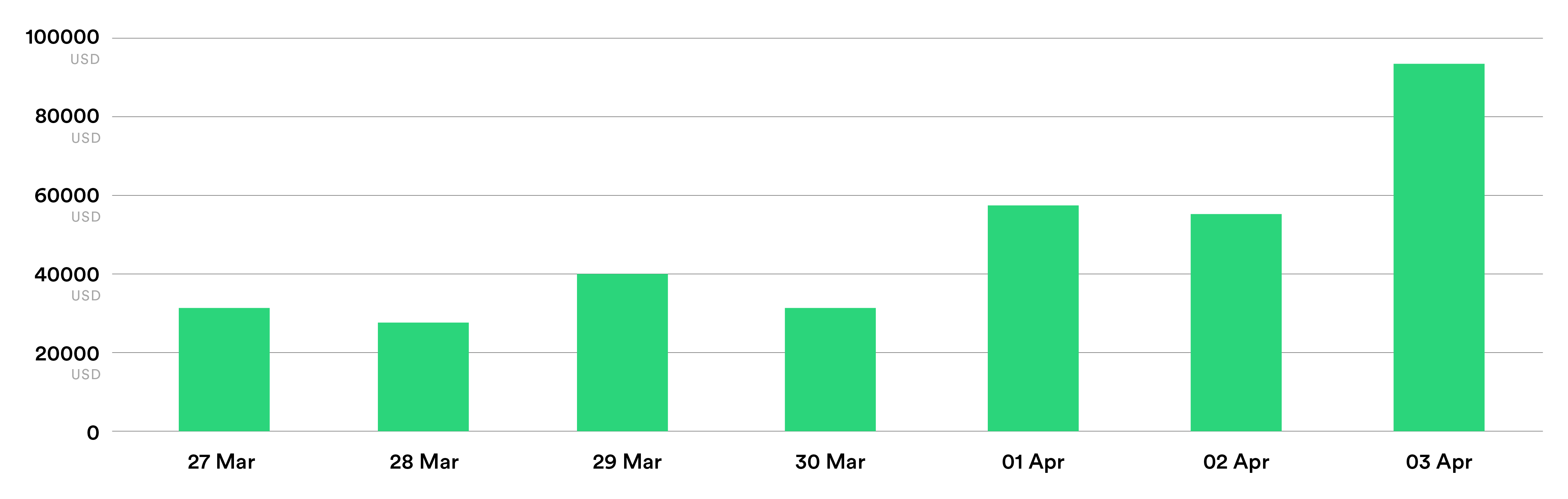
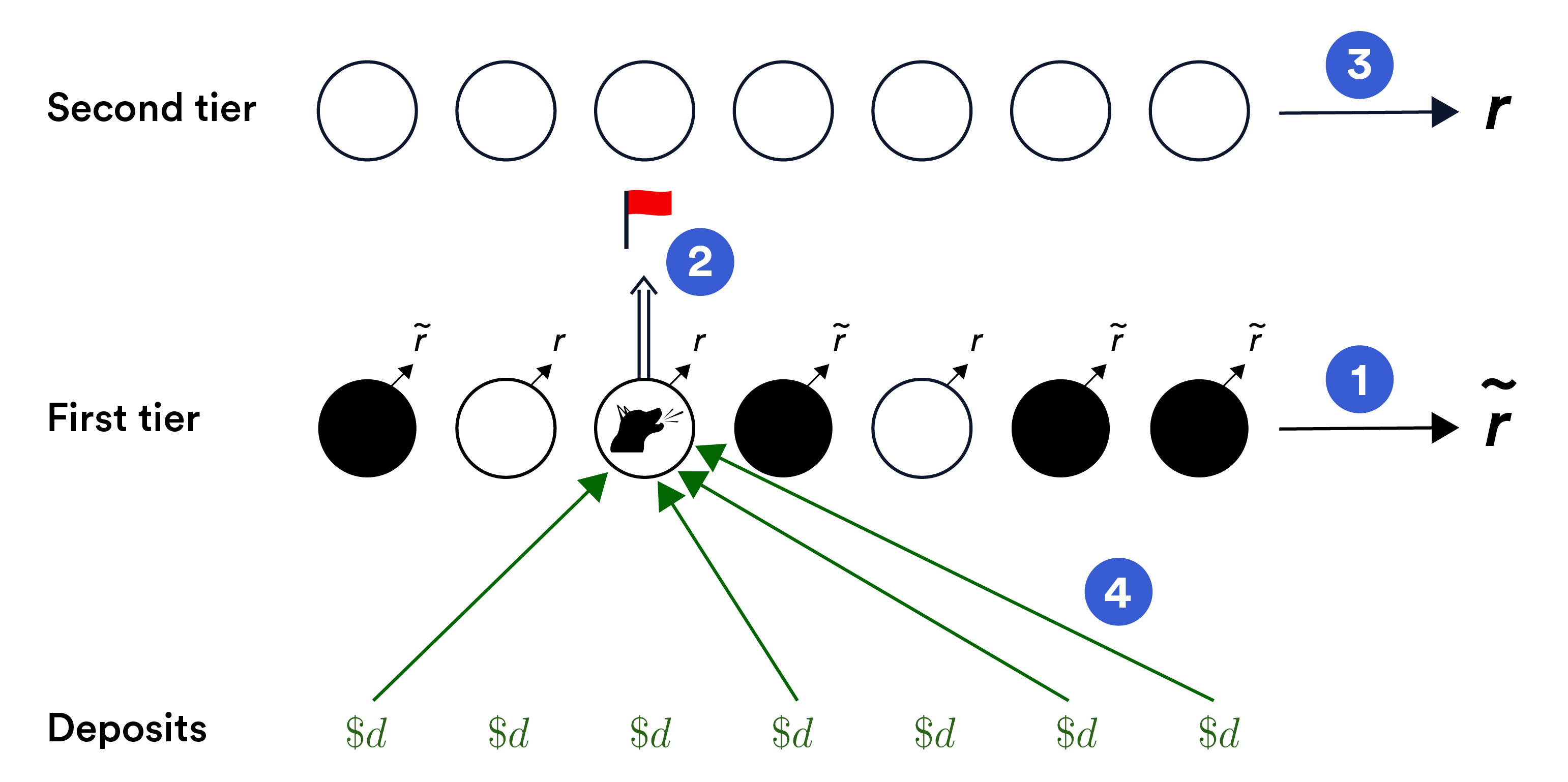
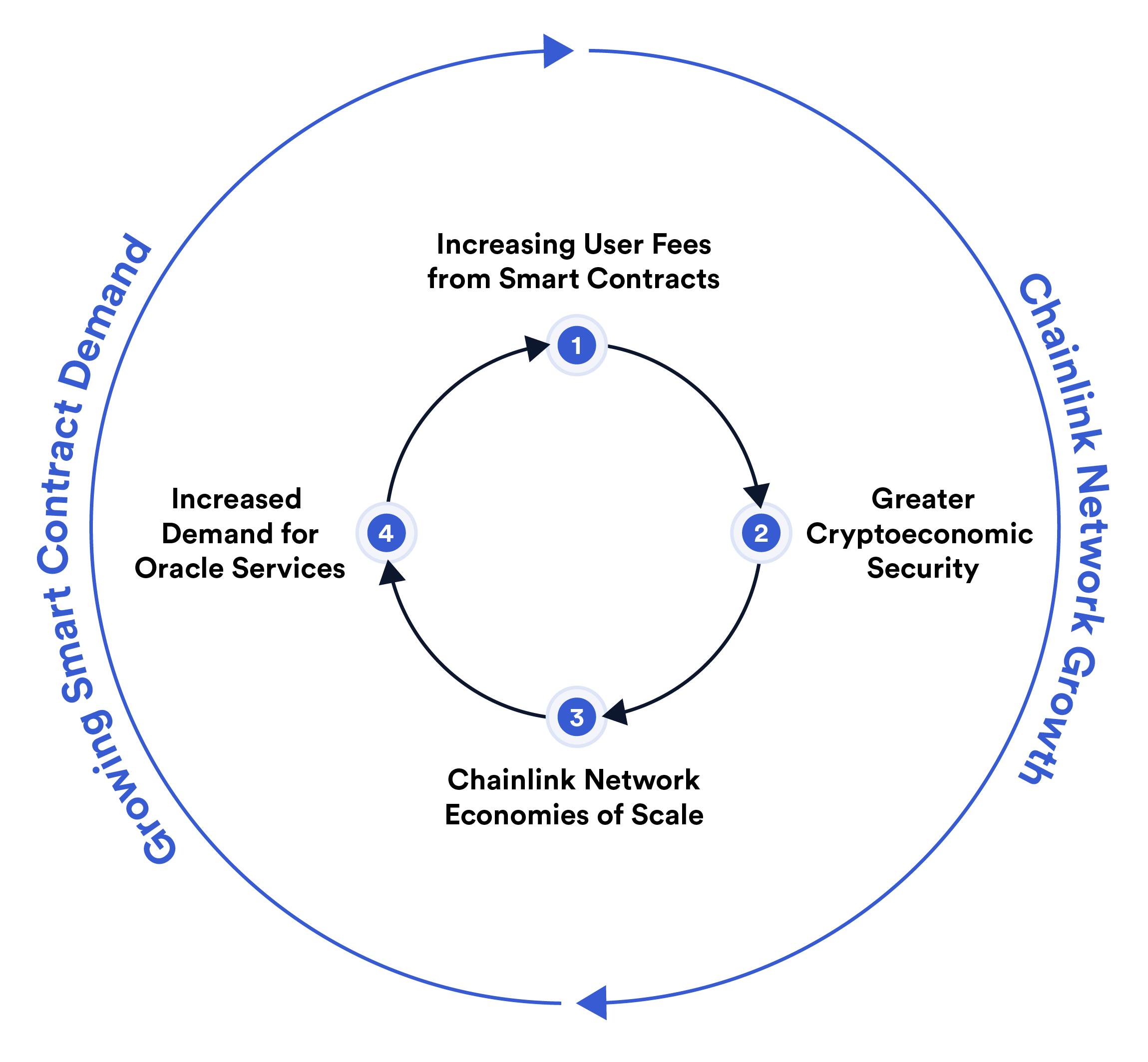
Gambar 18: Skema siklus kebajikan Chainlink staking. Kenaikan biaya pengguna pembayaran ke jaringan oracle 1⃝menyebabkannya tumbuh, sehingga menyebabkan pertumbuhan ekonominya keamanan 2⃝. Pertumbuhan super linier ini mewujudkan skala ekonomi di Chainlink jaringan 3⃝. Secara khusus, hal ini berarti pengurangan biaya rata-rata keamanan ekonomi, yaitu, keamanan ekonomi per dolar yang timbul dari pembayaran biaya atau sumber kepemilikan lainnya meningkat. Biaya yang lebih rendah, yang dibebankan kepada pengguna, merangsang peningkatan permintaan untuk oracle layanan 4⃝. 9.9 Faktor Tambahan yang Mendorong Pertumbuhan Jaringan Seiring dengan berkembangnya ekosistem Chainlink, kami yakin akan daya tariknya bagi pengguna dan pentingnya infrastruktur bagi perekonomian blockchain akan meningkat. Nilai yang diberikan oleh jaringan oracle bersifat super-linear, artinya ia berkembang lebih cepatdaripada ukuran jaringan itu sendiri. Pertumbuhan nilai ini berasal dari keduanya skala ekonomi—efisiensi biaya per pengguna yang lebih besar seiring dengan peningkatan volume layanan—dan efek jaringan—peningkatan utilitas jaringan seiring pengguna mengadopsi DON secara lebih luas. Karena smart contract yang ada terus mendapatkan lebih banyak nilai yang terjamin dan sepenuhnya baru smart contract aplikasi dimungkinkan oleh layanan yang lebih terdesentralisasi, secara total penggunaan dan biaya agregat yang dibayarkan ke DONs akan bertambah. Meningkatkan kumpulan biaya masuk menerjemahkannya menjadi sarana dan insentif untuk menciptakan layanan yang lebih terdesentralisasi, menghasilkan siklus yang baik. Siklus yang baik ini memecahkan masalah ayam-dan-telur yang kritis masalah dalam ekosistem hibrida smart contract: Fitur smart contract yang inovatif seringkali memerlukan layanan terdesentralisasi yang belum ada (misalnya, pasar DeFi baru sering kali memerlukan sumber data baru) namun memerlukan permintaan ekonomi yang memadai agar dapat terwujud. Penggabungan biaya berdasarkan berbagai smart contract untuk DON yang ada akan menandakan permintaan akan layanan terdesentralisasi tambahan dari basis pengguna yang terus bertambah, sehingga memunculkan penciptaannya sebesar DONs dan pemberdayaan berkelanjutan terhadap smart contracts hybrid yang baru dan bervariasi. Singkatnya, kami percaya bahwa pertumbuhan keamanan jaringan didorong oleh kebajikan siklus dalam mekanisme Chainlink staking menunjukkan pola pertumbuhan yang lebih besar yang jaringan Chainlink dapat membantu mewujudkan perekonomian on-chain untuk desentralisasi layanan.
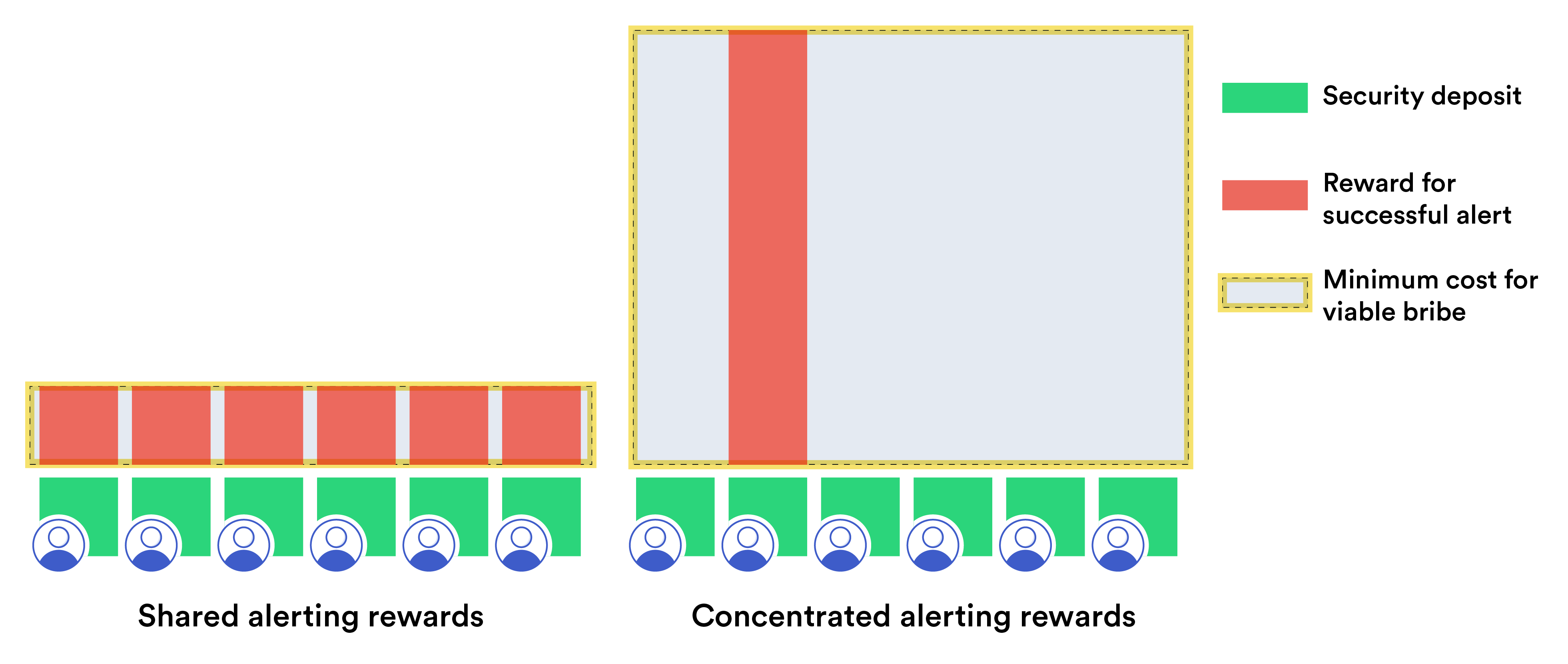
经济学和加密经济学
为了让 Chainlink 网络在去中心化信任模型中实现强大的安全性, 节点共同表现出正确的行为至关重要,这意味着它们遵守 大多数时候完全符合 DON 协议。在本节中,我们讨论方法 通过经济激励(又名加密经济)来帮助实施这种行为 激励措施。 这些激励分为两类:显性激励和隐性激励 分别通过 staking 和未来费用机会 (FFO)。 质押: 与其他 blockchain 系统一样,在 Chainlink 中进行质押涉及网络参与者,即 oracle 节点,以 LINK token 的形式存入锁定资金。这些 资金,我们也称为股权或显性股权,是一种显性激励。他们 因节点故障或不当行为而被没收。在 blockchain 上下文中, 这个过程通常被称为削减。 然而,Chainlink 中 oracle 节点的质押与 staking 有根本不同 由 validators 在未经许可的 blockchains 中编写。验证者可能会通过模棱两可或对抗性地排序交易来做出不当行为。 底层共识协议 15由于用户可以替换内存池中的交易,因此需要注意确保挖掘的交易和 DON 提交的交易之间的正确对应。不过,无需许可的 blockchain 使用严格快速的块验证规则和加密原语来防止 validator 生成无效块。相比之下, 程序保护无法阻止作弊 oracle 网络生成 无效报告。原因是两种类型的系统之间的一个关键区别:blockchains 中的事务验证是内部一致性的属性,而正确性 关于 blockchain 的 oracle 报告是外部数据(即链下数据)的属性。 我们为基于 Chainlink 的网络设计了初步的 staking 机制 基于可能使用外部数据的 oracle 节点之间的交互协议。这个 机制使用明确的奖励和措施为正确的行为创造经济激励 处罚(削减)。由于该机制是经济的,因此旨在防止节点 对手使用金融资源通过以下方式腐败节点: 贿赂。 (这样的对手是非常普遍的,并且可以扩展到例如与 从他们的集体不当行为中获取价值。) 我们设计的Chainlink staking机制具有一些强大且新颖的功能 16 主要的此类特征是超线性 staking 影响(具体来说,二次影响)。 对手所拥有的资源必须远远超过节点存入的资金 从而达到颠覆机制的目的。我们的 staking 机制还提供了针对比之前在类似系统中考虑的更强大对手的保护,即 一个可以根据节点未来行为进行贿赂的对手。此外,我们还讨论了 Chainlink 工具(例如 DECO)如何帮助加强我们的 staking 通过在节点行为出现故障的情况下促进正确裁决的机制。 未来费用机会(FFO): 两个 PoW 的未经许可的 blockchains 和 PoS 多样性——如今严重依赖我们所说的隐性激励。这些是 对诚实行为的经济激励不是来自明确的奖励,而是来自 从平台参与本身来看。例如,Bitcoin 矿工社区受到激励,不会发起 51% 攻击,因为这可能会破坏人们对比特币的信心。 Bitcoin,压低其价值,从而侵蚀其集体的价值 采矿基础设施资本投资[150]。 Chainlink 网络受益于我们提到的类似隐性激励 作为未来费用机会(FFO)。具有良好性能历史记录的 Oracle 节点或 声誉会吸引用户付费。 oracle 节点的不当行为会危及未来 费用支付,从而以潜在的机会成本来惩罚节点 通过参与网络获得的收入。与显性权益类比, FFO 可以被视为一种隐性股权形式,是对诚实行为的激励, 源于对平台保持信心的共同利益 节点运营商的业务取决于节点运营商的积极绩效和声誉 网络。这种激励是 Chainlink 网络所固有的,但没有明确表达 协议。在 Bitcoin 中,维持上述采矿作业的价值 16我们在此描述的 staking 机制目前仅旨在强制提供正确的报告 由 oracle 网络提供。我们希望在未来的工作中对其进行扩展,以确保许多任务的正确执行 DONs 将提供的其他功能。同样可以被视为隐性股权的一种形式。 我们强调 FFO 已存在于 Chainlink 中并有助于保护网络 今天。我们对 Chainlink 进一步发展的主要贡献将是一种有原则的、经验驱动的方法,通过以下方式评估 FFO 等隐性激励: 我们称之为隐性激励框架(IIF)。估计数量,例如 节点未来的收费机会,IIF将持续借鉴综合 Chainlink 网络收集的绩效和付款数据。这样的估计 将启用反映节点激励的 staking 系统基于 IIF 的参数化 比当前的启发式和/或静态模型具有更高的准确性。 总结一下,正确的 oracle 节点的两个主要经济激励措施 正在发展的 Chainlink 网络中的行为将是: • 质押(存入的质押) 哦 明确的激励 • 未来收费机会 (FFO) 哦 隐性激励 这两种形式的激励是相辅相成的。 Oracle节点可以同时 参与 Chainlink staking 协议,享受持续的收入来源 用户,并从他们持续的良好行为中集体受益。因此这两种激励措施 为 oracle 网络提供的加密经济安全做出贡献。另外, 这两种激励措施可以相互加强和/或相互抵消。例如, 没有业绩历史记录和收入来源的新 oracle 运营商可以抵押 大量的LINK作为诚实行为的保证,从而吸引用户 和费用。相反,一个已建立的 oracle 运算符具有长且相对无故障的 性能历史记录可能会向大量用户收取大量费用,因此依赖 更重视 FFO 作为隐性激励的一种形式。 一般来说,我们在这里考虑的方法旨在实现给定量的 oracle-网络 资源以在 Chainlink 中创造最大可能的经济激励 代理——即最大化其财务效用的节点——诚实行事。再放一个 方式,目标是最大化对手攻击所需的金融资源 网络成功。通过数学上良好地制定 staking 协议 定义经济安全并使用 IIF,我们的目标是衡量经济实力 Chainlink 的激励措施尽可能准确。依赖合约的创建者将 然后能够充满信心地确定 oracle 网络是否满足 他们所需的加密经济安全级别。 经济安全的良性循环: 我们在本节中讨论的激励措施 staking 和 FFO 的影响超出了其增强安全性的范围 DONs。它们承诺会引发我们所说的经济安全的良性循环。 超线性 staking 影响(和其他规模经济)导致运营成本降低 随着 DON 安全性的增长而增加成本。较低的成本吸引更多用户使用 DON,增加费用支付。费用支付的增加继续刺激行业的增长 网络,形成良性循环。 我们认为,经济安全的良性循环只是一个例子 规模经济和网络效应等,我们将在本节后面讨论。 部门组织:质押给以下组织带来了显着的技术和概念挑战 我们设计了一种具有新颖功能的机制。因此,质押将是 我们本节的主要重点。 我们在第 9.1 节中概述了本文中介绍的 staking 方法,然后在第 9.2 节到第 9.5 节中进行了详细讨论。我们介绍 IFF 在第 9.6 节中。我们在第 9.7 节中总结了 Chainlink 网络激励措施。 在第 9.8 节中,我们讨论了我们提出的 staking 方法可以给 oracle 网络带来的经济安全的良性循环。最后,我们简单描述一下其他的潜力 影响第 9.9 节中 Chainlink 网络的增长。 9.1 质押概览 如上所述,我们在这里介绍的 staking 机制设计涉及 oracle 节点之间的交互协议,允许解决 外部数据报告。质押旨在确保理性 oracle 节点的诚实行为。因此,我们可以将攻击 staking 协议的对手建模为 行贿者:对手的策略是利用经济激励来腐蚀 oracle 节点。 对手可能会通过成功篡改来获取未来的金融资源 带有 oracle 报告,例如,提出与损坏的节点分享由此产生的利润。 我们的 staking 机制设计同时致力于实现两个雄心勃勃的目标: 1. 抵御强大的对手:staking机制旨在保护 oracle 网络针对广泛的对手,这些对手能够进行复杂的、 有条件的贿赂策略,包括提供贿赂的预期贿赂 至 oracle ,其身份是在事后确定的(例如,向 随机选择 oracles 进行高优先级警报)。而其他 oracle 设计 考虑了一组狭窄的攻击,但没有实际的全部功能 对手,据我们所知,我们引入的对抗机制 这是第一个明确阐述一系列广泛的贿赂策略并表明 该模型中的电阻。我们的模型假设除了攻击者之外的节点 经济上理性的(相对于诚实的),我们假设存在一个 对于典型使用来说价格昂贵但可用的事实来源 如有分歧(下文进一步讨论)。 2. 实现超线性staking影响: 我们的目标是确保由理性代理组成的 oracle 网络报告 即使存在预算超线性的攻击者,也能如实进行整个网络存入的总权益。在现有的 staking 系统中,如果 每个 n 个节点都持有 $d,攻击者可以发出可信的贿赂请求 节点以不诚实的行为换取略高于 \(d to each node, using a total budget of about \)dn。这已经是一个很高的标准了 攻击者必须拥有相当于存款总和的流动预算 网络中的所有利益相关者。我们的目标是更强的经济安全 这已经是一个很大的障碍了。我们的目标是设计第一个 staking 系统 可以通过 n 的预算超线性实现一般攻击者的安全性。 虽然实际考虑可能会产生较小的影响,但正如我们下面讨论的, 我们的初步设计达到了对抗性预算要求大于 $dn2/2,即以 n 为单位进行二次缩放,即使行贿行为在很大程度上也是不切实际的 当节点仅抵押适量时。 实现这两个目标需要激励设计的创新组合 和密码学。 主要想法: 我们的 staking 方法取决于我们称之为“看门狗优先”的想法。 由 Chainlink oracle 网络生成并发送到依赖合约的报告 (例如,资产价格)是从参与节点贡献的各个报告中汇总的(例如,通过取中位数)。通常是服务级别协议 (SLA) 指定报告偏差的可接受范围,即节点的报告可以走多远 与汇总报告的偏差以及应允许汇总报告的偏差程度 偏离真实值才被认为是正确的。 在我们的 staking 系统中,对于给定的报告轮次,每个 oracle 节点可以充当 如果监管机构认为汇总报告不正确,则会发出警报。在每个 在报告轮中,每个 oracle 节点都被分配一个公共优先级,该优先级决定了 其警报(如果有)的处理顺序。我们的机制旨在奖励 集中度,这意味着发出警报的最高优先级的看门狗将获得 没收故障节点的存款所产生的全部奖励。 我们的 staking 系统设计涉及两层:第一层,默认层,第二层, 后挡板层。第一层是 oracle 网络本身,一组 n 个节点。 (为简单起见, 我们假设 n 是奇数。)如果大多数节点报告不正确的值,则 第一层有强烈的动机发出警报。如果发出警报,则报告 然后网络的决策被升级到第二层——一个高成本、最大可靠性的系统,可以由用户在网络服务级别协议中指定。 例如,这可能是一个仅由具有强大功能的节点组成的系统 历史可靠性分数,或者其数量级大于 oracles 第一层。此外,如第 9.4.3 节中所述,DECO 或 Town Crier 可以服务 作为强大的工具,帮助确保第二层的高效和结论性裁决。 为了简单起见,我们假设第二层系统得出了正确的报告 值。 虽然仅依靠第二层来生成所有报告似乎很有吸引力, 我们设计的好处是它始终如一地实现了在典型情况下,只需支付第二层系统的运营成本 第一层系统。 看门狗优先级会通过以下方式产生超线性 staking 影响:如果 第一层 oracle 网络输出错误结果和多个看门狗节点 警报,staking 激励机制奖励最高优先级的看门狗 从(大多数)行为不当节点的存款中提取的金额超过 $dn/2。的 因此,总奖励集中在这个单一看门狗手中,因此 确定对手必须承诺潜在看门狗的最低限度 激励它不发出警报。由于我们的机制确保每个 oracle 都获得 如果更高优先级的监管机构接受了贿赂,则有机会担任监管机构 (并且选择不发出警报),因此对手必须提供超过 $dn/2 到每个节点以防止引发任何警报。由于有n个节点, 对手成功行贿所需的预算超过 dn2/2 美元,其中 是网络中节点数量 n 的二次方。 9.2 背景 我们对 staking 的方法借鉴了博弈论和机制领域的研究 设计 (MD)(有关教科书参考,请参阅 [177])。博弈论是数学上的 战略互动的正式研究。在这种情况下,游戏就是这样的模型 一种交互,通常是在现实世界中,将可用的操作集编纂成 游戏的参与者,称为玩家。博弈还指定了所获得的收益 由个别玩家决定——奖励取决于玩家选择的行动和 其他玩家的行动。也许是游戏中研究的最著名的游戏例子 理论是囚徒困境[178]。博弈论学家通常旨在理解 给定博弈中所代表的均衡或均衡(如果有)。平衡是 一组策略(每个玩家一个),这样没有一个玩家可以获得更高的分数 单方面偏离其战略所带来的回报。 与此同时,机制设计是设计激励措施的科学,使得 交互(及其相关博弈)的平衡具有一些理想的特性。 MD 可以被视为博弈论的逆:博弈中的典型问题 理论是,“给定激励和模型,均衡将会是什么?”在马里兰州, 相反,问题是“什么激励措施会导致博弈达到理想的均衡?” 机制设计者的一个典型目标是创建一个“激励兼容”机制,这意味着该机制的参与者(例如,拍卖或其他信息) 启发系统[228])被激励去报告某些事情的真相(例如,如何 他们非常看重某个特定的物品)。维克里(第二价)拍卖也许是 最著名的激励兼容机制,其中参与者提交密封投标 对于某件商品,出价最高者赢得该商品,但支付第二高的价格 [214]。加密经济学是 MD 的一种特定领域形式,它利用密码学 在去中心化系统中创造理想平衡的技术。 贿赂和共谋给整个医学博士领域带来了重大挑战。几乎所有的机制都会在共谋的存在下崩溃,共谋被定义为附带合同。参与机制的各方之间 [125, 130]。贿赂是指外部一方在游戏中引入新颖的激励措施,这提出了一个更棘手的问题 比串通更重要;串通可以被视为游戏行贿的特例 参与者。 区块链系统通常可以被概念化为具有货币(基于加密货币)回报的游戏。一个简单的例子是工作量证明挖矿:矿工有一个行动空间 他们可以选择 hash 速率来开采区块。挖矿的回报是有保证的负奖励(电力和设备成本)加上随机 正奖励(挖矿补贴)取决于其他活跃矿工的数量 [106, 172] 和交易费用。像 SchellingCoin [68] 这样的众包 oracle 是另一个例子:操作空间是 oracle 可能发送的一组可能的报告,而 收益是 oracle 机制指定的奖励,例如,付款可能取决于 oracle 的报告与其他报告的中位数有多接近 [26, 68, 119, 185]。 区块链游戏为串通和贿赂攻击提供了成熟的机会;确实, smart contracts 甚至可以促进此类攻击 [96, 165]。也许最有名的 对众包 oracle 的贿赂攻击是 p-plus-epsilon 攻击 [67]。这次攻击 出现在类似 SchellingCoin 的机制中,在该机制中,玩家提交布尔值报告(即假或真),如果他们同意,则获得 p 奖励 多数提交。 在 p-plus-epsilon 攻击中,攻击者可信地承诺: 例如,当且仅当多数提交为真时,才向投票错误的用户支付 $p + ϵ 费用。 结果是一种均衡,其中所有参与者都被激励报告虚假信息 无论其他玩家做什么;因此,行贿者可以诱导节点 通过其承诺的贿赂举报虚假信息,而无需实际支付贿赂(!)。 然而,在 oracle 背景下(特别是非众包的 oracle )对其他贿赂策略的探索仅限于相当弱的对抗性 模型。例如,在 PoW 环境中,研究人员研究了结果偶然性 贿赂,即只有在目标消息被成功审查并且没有被审查的情况下才行贿。 出现在一个区块中,无论单个矿工的行为如何[96, 165]。在这种情况下 然而,除了 p-plus-epsilon 攻击之外,我们只知道 oracles 中的工作 一种严格限制的贿赂模式,其中行贿者以以下条件进行贿赂: 个人玩家的行动,而不是最终的结果。 在这里,我们概述了保持激励的信息获取机制的设计 即使在强对抗模型中也是兼容的,如下一小节所述。 9.3 建模假设 在本小节中,我们将解释如何对玩家的行为和能力进行建模 我们的系统,特别是第一层 oracle 节点,第二层节点(裁决) 层和对手。9.3.1 第一层激励模型:理性参与者 许多 blockchain 系统的安全性依赖于一定数量诚实的假设 参与节点。如果节点遵循协议,则被定义为诚实的 当这样做不符合他们的经济利益时。通常是工作量证明系统 需要大多数 hash 权力才能诚实,权益证明系统通常需要所有参与权益的 2/3 或更多才能诚实,甚至像这样的第 2 层系统 仲裁 [141] 需要至少一个诚实的参与者。 在我们的 staking 机制建模中,我们做出了一个更弱的假设。 (成为 清晰、较弱的假设意味着更强的安全属性,因此更可取。)我们假设对手已经腐败,即控制了一些(少数) 第一层 oracle 节点的一部分。我们将其余节点建模为不诚实的代理, 而是作为理性预期效用最大化者。这些节点完全根据自利的财务激励措施行事,选择导致预期财务的行动 增益。例如,如果一个节点收到的贿赂金额大于其所获得的奖励 行为诚实,就会收受贿赂。 关于对抗节点的注意事项: 根据常见的信任建模 去中心化系统中,我们假设所有节点都是理性的,即寻求最大化 净收入,而不是被恶意对手控制。然而我们的主张—— 特别是超线性或二次 staking 影响——渐近地保持 对于某些正的情况,对抗性控制的节点集至多为 (1/2 −c)n 常数 c. 9.3.2 第二层裁决模型:假设的正确性 回想一下,我们的 staking 机制的一个关键功能有助于实现安全性 对抗理性节点的是它的第二层系统。 在我们提出的 staking 机制中,任何 oracle 都可能发出警报,表明 它认为该机制的输出是不正确的。警报会带来高度信任 第二层系统激活并报告正确的结果。因此,关键建模 我们的方法的要求是正确的裁决,即正确的报告 第二层系统。 我们的 staking 模型假设第二层系统充当廉洁、最可靠的事实来源。这样的系统可能既昂贵又缓慢,因此 不适合用于典型情况。然而,在平衡情况下,即当 第一层系统正常工作,第二层系统不会被调用。 相反,它的存在通过提供一个增强了整个 oracle 系统的安全性 高保证的后盾。 使用高信任度、高成本的裁决层类似于上诉流程 大多数司法系统的核心。它在 oracle 的设计中也很常见 系统,例如[119, 185]。我们简要讨论第二层的实现方法 在我们第 9.4.3 节的机制中。我们的 staking 协议使用第二层系统的假设正确裁决作为可信威胁,强制执行 oracle 节点的正确报告。协议 没收 oracle 节点的部分或全部权益,这些节点生成由 第二层系统不正确。从而阻止 Oracle 节点出现不当行为 由此产生的经济处罚。这种方法在风格上类似于 乐观的 rollups,例如 [141, 10]。 9.3.3 对抗模型 我们的 staking 机制旨在获取真实信息,同时实现针对广泛、明确类别的对手的安全。它改进了以前的作品, 它要么省略明确的对抗模型,要么专注于对手的狭窄子类,例如上面讨论的 p+epsilon 对手。我们的目标是设计一个 staking 具有正式证明的安全机制,可以抵御各种对手 实践中会遇到。 我们将对手建模为具有固定(可参数化)预算,表示为 $B。对手可以与每个 oracle 进行单独且保密的通信 网络,并可以秘密向任何个人 oracle 提供贿赂保证 取决于该机制的可公开观察的结果。结果决定 例如,贿赂可以包括 oracle 报告的价值、任何公共消息 由任何 oracle 发送到该机制(例如,警报),其他报告的值 oracles,以及机制输出的值。 没有任何机制可以抵御具有无限能力的攻击者。因此,我们认为某些行为不切实际或超出范围。我们假设我们的攻击者 不能破坏标准加密原语,并且如上所述,有一个固定的(如果 可能很大)预算$B。我们进一步假设对手无法控制 oracle 网络中的通信,特别是它不能大幅延迟 第一层和/或第二层节点之间的流量。 (对手是否可以观察到这种通信取决于特定的机制,我们将在下面解释。) 然而,非正式地,如上所述,我们假设对手可以: (1) 腐败 oracle 节点的一部分((1/2 −c)-某个常数 c 的分数),即完全控制 (2) 向任何想要的节点提供贿赂,并保证付款 如上所述,取决于对手指定的结果。 虽然我们没有提供对手完整的正式模型或完整分类 本白皮书中列出了一系列贿赂能力,以下是各种类型的示例 我们的模型涵盖了行贿者。为了简单起见,我们假设 oracles 发出布尔值 报告其正确值 (w.l.o.g.) 为 true,并且最终结果计算为 消费 smart contract 使用的这些报告的汇总。行贿者的 目标是最终结果不正确,即错误。 • 无条件贿赂者:贿赂者向任何报告虚假信息的oracle 提供贿赂$b。 • 概率贿赂者:贿赂者以某种概率 q 向任何 oracle 提供贿赂 $b 报告错误。• 以虚假结果为条件的行贿者:行贿者向任何报告虚假信息的oracle 行贿$b,只要最终结果是虚假的。 • 无警报条件的行贿者:行贿者向任何举报的oracle 提供贿赂$b 只要没有发出警报,就为 false。 • p-plus-epsilon 贿赂者:贿赂者向任何报告错误的 oracle 提供贿赂 $b 只要大多数 oracle 不报告虚假信息即可。 • 潜在行贿者:行贿者提前向选定的 oracle 行贿 $b 对于随机角色并报告错误。在我们提出的 staking 协议中,所有 节点充当潜在的看门狗,我们能够证明随机化 监管机构的优先事项并不适合潜在的贿赂。许多工作量证明、proof-of-stake 和许可系统都容易受到预期影响 然而,贿赂表明了在我们的对手中考虑这一问题的重要性 模型并确保我们的 staking 协议能够适应它。参见附录E 了解更多详情。 9.3.4 多少加密经济安全才足够? 理性的对手只有在能够获取利润的情况下才会花钱攻击系统 大于其支出。 因此,对于我们的对抗模型和提议的 staking 机制中,$B 可以被视为对手能够获得的潜在利润的衡量标准 通过破坏 oracle 网络并导致其从依赖 smart contract 中提取 生成不正确的报告或一组报告。在决定是否存在 oracle 网络时 为其目的提供足够程度的加密经济安全性,用户应该 从这个角度来评估网络。 对于实际环境中看似合理的对手,我们预计 $B 通常会是 远小于依赖 smart contract 的总资产。在大多数情况下,它 对手不可能全部提取这些资产。 9.4 质押机制:草图 在这里,我们介绍了staking机制的主要思想和总体结构。 目前正在考虑。 为了便于演示,我们描述了一个简单但缓慢的 本小节中的(多轮)协议。但我们注意到,这个方案相当 实用。鉴于该机制提供的经济保证,即对故障节点的惩罚和随之而来的激励,许多用户可能愿意 乐观地接受报告。换句话说,此类用户可以在之前接受报告 可能由第二层进行裁决。 不愿意乐观接受报告的用户可以选择等待协议 执行终止,即直到发生任何潜在的升级到第二层的情况。这个, 然而,这会大大减慢报告的确认时间。因此我们简单地图 15:带警报的 staking 方案示意图。在这个例子中,1⃝多数 的节点被损坏/贿赂并发出不正确的值〜r,而不是正确的值 报告值河看门狗节点2⃝向二级委员会发送警报, 3⃝确定并发出正确的报告值r,导致节点损坏 没收他们的存款——每 d 美元交给看门狗节点 4⃝。 概述一些优化,这些优化会导致更快(单轮)(如果更多的话) 第 9.5 节中的复杂设计。 回想一下,我们的 staking 机制中的第一层由基本的 oracle 组成。 网络本身。 如上所述,我们机制的主要结构是在每一轮中, 每个节点都可以充当具有一定优先级的“看门狗”,因此它有能力 如果该机制得到不正确的输出,而不是正确的输出,则发出警报 奥恩河此警报会导致第二层解决方案,我们假设达到了正确的结果 报告。报告不正确的节点会受到惩罚,因为他们的权益 削减并奖励给监管机构。这种基本结构在 oracle 系统中很常见, 例如,[119, 185]。 我们设计中的关键创新,如上面简要提到的,是每个节点都是 在潜在看门狗的排序中分配了不同的优先级。也就是看门狗 有机会按优先顺序发出警报。回想一下,如果一个节点有 发出警报的最高优先级,每次不当行为都会收到减少的押金 $d 节点,总共超过 \(dn/2 = \)d × n/2,因为不正确的报告意味着 大多数坏节点。因此,对手必须至少支付这个奖励 贿赂任意节点。因此,要贿赂大多数节点,对手必须支付 对大多数节点进行大额贿赂,即严格超过 $dn2/2。 我们在图 15 中示意性地展示了警报和看门狗升级的工作原理。9.4.1 进一步的机制细节 我们现在更详细描述的反贿赂系统是一个简化的草图 我们打算建造的两层建筑。我们的大部分重点将放在描述 第一层网络(以下简称“网络”,从上下文中可以清楚地看出) 及其激励机制和升级到第二层的程序。 考虑一个由 n 个 oracle 节点组成的 Chainlink 网络,这些节点负责 定期(例如,每分钟一次)报告布尔值(例如,市场是否 BTC 的市值超过了 ETH)。作为 staking 机制的一部分,节点 必须提供两笔押金:押金 $d 如有分歧,将被削减 多数和看门狗押金 $dw 会在出现故障时被削减 升级。我们假设节点无法复制其他节点的提交,例如, 通过第 5.3 节中讨论的提交-显示方案。每轮中,节点优先 提交他们的报告,一旦所有节点都已提交(或超时已过期), 节点公布他们的报告。 对于要生成的每个报告,每个节点还被赋予随机选择的 1 到 n 之间的看门狗优先级,其中 1 为最高优先级。该优先级使 奖励集中在一个看门狗手中。所有报告公开后, 随后进入警报阶段。在一系列 n(同步)轮中,节点 优先级 i 有机会在第一轮中发出警报。 让我们考虑一下节点揭示后该机制可能产生的结果 他们的报告。再次假设二进制报告,假设正确的值为 true 并且 不正确的是假的。还假设第一层机制输出 节点输出的多数值作为最终报告r。 该机制可能产生三种结果: • 完全一致:在最好的情况下,节点完全一致:所有节点 可用并已提供相同值 r 的及时报告(无论是真实的 或假)。在这种情况下,网络只需将 r 转发给依赖合约 并用固定的每轮支付 $p 奖励每个节点,该支付要小得多 比 $d。 • 部分一致:有可能某些节点处于离线状态,或者对于哪个值正确存在分歧,但大多数节点报告真实,并且只有一个 少数报告虚假。这个案例也很简单。多数值 (true) 被计算,产生正确的报告 r。所有报告 r 的节点都是 奖励 $p,而报告错误的 oracle 则拥有存款 适度削减,例如削减 10 美元。 • 警报:如果看门狗认为网络输出不正确, 它公开触发警报,将该机制升级到第二层网络。 那么就有两种可能的结果: – 正确警报:如果第二层网络确认图 16:通过集中警报奖励放大行贿者的成本。行贿 对手必须用超过其通过警报获得的奖励来贿赂每个节点 (显示为红色条)。如果警报奖励是共享的,那么这个奖励可能会相对 小。集中的警报奖励增加了任何单个节点可能获得的奖励 获得(高红色条)。因此,对手为可行的贿赂支付的总金额 (灰色区域)集中的警报奖励比共享的警报奖励大得多。 第一层网络错误,报警看门狗节点获得奖励 包括所有削减的存款,因此超过 $dn/2。 – 错误警报:如果第二层和第一层 oracle 一致,则升级 被认为有故障,并且警报节点失去 $dw 押金。 在乐观接受报告的情况下,看门狗警报不会导致 依赖合同执行的任何变化。对于旨在等待的合同 第二层委员会可能进行仲裁,监管机构发出延迟警报,但 不要冻结合同执行。合同也可以指定一个 裁决期间的故障转移 DON。 9.4.2 二次质押影响 每个节点都可以充当看门狗,并结合严格的节点优先级 确保集中奖励,使该机制实现二次staking 第 9.3.3 节中描述的每种贿赂攻击者的影响。回想一下,这个 具体来说,在我们的设置中,对于具有 n 个节点的网络,每个节点都有存款 $d,成功的贿赂者(上述任何一种)的预算必须大于 $dn2/2。 准确地说,行贿者必须至少破坏 (n+1)/2 个节点,因为行贿者必须 损坏大多数 n 个节点(对于奇数 n,根据假设)。因此,看门狗代表 获得 $d(n + 1)/2 的奖励。因此,行贿者必须向每个人支付这笔金额节点以确保没有人充当看门狗。我们正在努力正式证明,如果 行贿者的预算至多为 $d(n2 + n)/2,则子博弈完美均衡 行贿者和 oracle 之间的博弈——换句话说,平衡点为 游戏进行期间的任何一点——行贿者不得行贿,并且 每个 oracle 诚实地报告其真实值。 我们在上面已经解释了成功的行贿者如何可能需要 预算明显大于节点存款总和。为了说明这一点 直观的结果,图 16 以图形方式显示了集中警报奖励的影响。 正如我们所看到的,如果监管机构警报的奖励——即受贿的存款 报告错误的节点)—分为所有潜在警报,即警报的总量 任何单独的警报节点预计都会相对较小,大约为 $d。 行贿者知道不可能支付超过 d 美元的款项,因此可以使用 一个虚假结果的有条件贿赂,贿赂 n 个节点中的每一个节点,其金额略高于 $d + ϵ。 与直觉相反,图 16 显示了一个广泛分配奖励的系统 发出警报的节点之间的强度远弱于集中奖励的节点 单一看门狗的手中。 参数示例: 考虑一个(第一层)网络,其中 n = 100 个节点,每个节点 存入 \(d = \)20K。该网络将总共存入 200 万美元,但 免受预算为 \(100M = \)dn2/2 的贿赂。增加数量 当然,oracles 比增加 $d 更有效,并且可以产生戏剧性的效果: 具有 n = 300 个节点和存款 \(d = \)20K 的网络将受到保护 预算高达 9 亿美元的行贿者。 请注意,staking 系统在许多情况下可以保护代表 smart contract 的 比提供的贿赂保护水平更有价值。这是因为对手 在许多情况下,攻击这些合约并不能获取全部价值。例如,一个 Chainlink 支持价值 10 亿美元的合约可能只需要针对 拥有 1 亿美元资源的贿赂者,因为这样的对手可以切实地获取利润 仅占合同价值的10%。 注意: 网络的价值可以呈二次方增长的想法表达为 众所周知的梅特卡夫定律 [167, 235],该定律指出网络的价值 连接实体的数量呈二次方增长。然而,梅特卡夫定律 来自潜在成对网络连接数量的增长,这是与我们激励中潜在的二次 staking 影响不同的现象 机制。 9.4.3 第二层的实现 两个操作特性有助于实现高可靠性第二层:(1) 二级裁决在 oracle 网络中应该是罕见的事件,因此可以 比第一层正常运行的成本要高得多,并且 (2) 假设乐观地接受的报告——或可以等待仲裁执行的合同—— 第二层不需要实时执行。 这些功能导致了一系列 第二层的配置选项以满足特定 DONs 的要求。 作为示例方法,第二层委员会可以由由 DON(即第一层)来自 Chainlink 中服务时间最长且最可靠的节点 网络。运营商除了拥有丰富的相关运营经验外, 的此类节点在 FFO 中具有相当大的隐性激励,从而激发了欲望 确保 Chainlink 网络保持高度可靠。他们还公开 可用的性能历史记录可提供其可靠性的透明度。值得注意的是,第二层节点不必是第一层网络的参与者,并且 可以裁决多个第一层网络的故障。 给定 DON 中的节点可以预先指定并公开提交一组 n' 这样的 节点构成该 DON 的第二级委员会。此外,DON 节点发布一个参数k′≤n′,该参数决定第二层投票的数量 需要惩罚第一层节点。当针对给定报告生成警报时, 第二层成员对每个人提供的值的正确性进行投票 第一层节点。任何收到 k′ 反对票的第一层节点将丧失其地位 存款到看门狗节点。 由于审判和延长执行时间的机会很少 如上所述,与第一层相比,第二层中的节点可以: 1. 因审判而获得高额报酬。 2. 利用额外的数据源,甚至超出第一层使用的各种数据源。 3. 依靠人工和/或专家检查和干预,例如识别和 协调源数据中的错误并区分诚实节点中继 错误的数据和行为不当的节点。 我们强调,我们刚才描述的选择第二层节点和政策管理裁决的方法仅代表了一个大问题中的一个点。 第二层可能实现的设计空间。我们的激励机制提供 关于如何实现第二层的完全灵活性。因此,各个 DON 可以 为满足特定要求的第二层制定并制定规则 以及参与节点和用户的期望。 DECO 和 Town Crier 作为裁决工具: 对于第二层来说这是必不可少的 在我们的机制中能够区分敌对的第一层节点 故意产生不正确的报告和无意中诚实的第一层节点 中继源处不正确的数据。只有这样第二层才能实现 削减是为了抑制作弊行为,这是我们机制的目标。德科和城市公告员 是强大的工具,可以使第二层节点做出这一关键区分 可靠。第二层节点在某些情况下可能能够直接查询所使用的数据源 由第一层节点或使用ADO第7.1节来检查是否有错误的报告 由错误的数据源导致。然而,在其他情况下,第二层节点可能缺乏 直接访问第一层节点的数据源。在这种情况下,正确的判决将 似乎不可行或需要依赖主观判断。上一页 oracle 争议系统依赖于低效且不断升级的投票来解决此类问题 挑战。 然而,使用 DECO 或 Town Crier,第一层节点可以证明正确的行为 到第二层节点。 (有关这两个系统的详细信息,请参见第 3.6.2 节。)具体来说,如果 第二层节点将第一层节点识别为输出了错误的报告值~r, 第一层节点可以使用DECO或Town Crier来生成防篡改证据 第二层节点正确地从(启用 TLS 的)源正确中继 〜r 被 DON 认可为权威。至关重要的是,第一层节点可以做到这一点 无需需要直接访问数据源的第二层节点。 17 因此, 对于任何所需的数据源,正确的裁决在 Chainlink 中都是可行的。 9.4.4 误报保险 我们的staking机制实现的强大反贿赂从根本上依赖于 削减奖励给警报者的资金。如果没有金钱奖励,警报者就会 没有拒绝贿赂的直接动机。然而,其结果是,削减的资金并没有 可用于补偿因错误报告而受到伤害的用户,例如损失金钱的用户 当错误的价格数据转发到 smart contract 时。 根据假设,如果报告被接受,不正确的报告不会造成问题。 仅在可能的裁决(即第二层采取行动)之后签订合同。正如所解释的 不过,为了实现最佳性能,合约可能会依赖 对执行正确报告的机制持乐观态度,这意味着他们接受 在潜在的二级裁决之前进行报告。 确实如此乐观的行为 在我们的模型中假设理性对手的预算不超过预算是安全的 staking 该机制的影响。 用户担心由于以下原因而导致的不太可能发生的机制故障: 例如,拥有压倒性金融资源的对手可能希望以误报保险的形式采用额外的经济安全层。我们知道 多家保险公司已经打算提供此类智能合约支持的保单 在不久的将来,针对 Chainlink 安全协议,包括通过 DAOs 等创新机制,例如 [7]。 Chainlink 的性能历史记录是否存在 节点和有关节点的其他数据(例如其权益金额)为风险精算评估提供了异常坚实的基础,从而可以为政策定价 以对投保人来说成本低廉但对保险公司来说可持续的方式。 17借助 Town Crier,第一层节点还可以在本地生成证明 他们输出的报告的正确性,并向网络上的第二层节点提供这些证明 按需基础上。误报保险的基本形式可以在值得信赖和 使用 smart contracts 的有效方式。举个简单的例子,参数保险 如果我们的激励机制有效,合同 SCins 可以自动补偿保单持有人 第二层标识第一层生成的报告中的错误。 希望购买保险的用户U,例如目标的创建者 SC 合约,可以向去中心化保险公司提交保单金额请求 合同金额为 M 美元。在批准 U 后,保险公司可以设置持续的(例如每月) SCins 中 $P 的溢价。当 U 支付保费时,她的保单仍然有效。 如果 SC 发生报告失败,结果将是一对 (r1, r2) 的发射 SC 的冲突报告,其中 r1 由我们机制中的第一层签名, r2,相应的更正报告,由第二层签署。如果U提供 这样一个有效的 SCins 对 (r1, r2),合约会自动向她支付 M 美元,前提是 她的保费是最新的。 9.5 单轮变体 上一小节中描述的协议要求第二层委员会等待 n 轮以确定看门狗是否发出警报。 这个 即使在乐观的情况下,即当第一层运行时,要求也成立 正确。对于不愿意乐观地接受报告的用户,即在潜在的 裁决,与该方法相关的拖延是行不通的。 出于这个原因,我们也在探索只需要一个的替代协议 圆形。在这种方法中,所有 oracle 节点提交秘密位,指示是否 他们希望发出警报。然后,第二层委员会检查这些值 优先顺序。为了提供一个粗略的草图,这样的方案可能涉及以下内容 步骤: 1.看门狗位提交:每个节点Oi秘密共享一位看门狗值 对于它生成的每个报告,第二层中的节点之间 wi 属于{无警报,警报}。 2. 匿名提示:任何oracle节点都可以在提交看门狗位的同一轮中向二级委员会提交匿名提示α。这个提示α 是一条消息,指示已针对当前报告发出警报。 3. 看门狗位检查:第二层委员会揭示oracle节点的看门狗 按优先级顺序排列的位。 请注意,节点在不发出警报时不得发送警报看门狗位:否则,流量分析会显示所有节点的位。该协议确实显示无警报 优先级高于最高优先级警报看门狗的节点的看门狗位。 观察到所揭示的内容与我们的 n 轮协议相同。奖励的分配也与该方案相同,即第一个识别的看门狗 收到提交错误报告的节点的被削减的存款。使用匿名提示使二级委员会能够在没有发出警报的情况下保持非互动,从而降低沟通复杂性 在常见情况下。请注意,任何提出警报的监管机构都有提交匿名举报的经济动机:如果没有提交举报,则不会向任何人支付任何奖励 节点。 确保匿名提示 α 的发送者 Oi 不能被 根据网络数据,攻击者可以通过匿名方式发送匿名提示 通道,例如通过 Tor,或者更实际地,通过云服务提供商代理。至 验证 Tip 源自 O,Oi 可以使用环签名对 α 进行签名 [39, 192]。 或者,为了防止恶意 oracle 节点对第二层委员会进行不可归因的拒绝服务攻击,α 可以是一个匿名凭证, 可撤销的匿名[73]。 该协议虽然实际上是可以实现的,但具有一定的重量级工程 要求(我们正在探索减少的方法)。以第一层节点为例, 必须直接与第二层节点通信,需要维护目录。对匿名通道和环签名的需求增加了工程量 方案的复杂性。最后,简要讨论了一个特殊的信任要求 在下面的注释中。因此,我们也在探索更简单的方案,但仍能实现 超线性 staking 影响,但可能小于二次影响,例如,行贿者渐近需要至少 $n log n 的资源。以下的一些计划 考虑因素涉及随机选择节点的严格子集作为看门狗, 在这种情况下,潜在的贿赂就成为一种特别有力的攻击。 备注: 这种单轮 staking 机制的安全性需要不可攻克 oracle 和第二层节点之间的通道——这是抗强制系统的标准要求,例如投票 [82, 138],并且在实践中是合理的。 然而,此外,寻求与行贿者合作的节点 Oi 可以构建 其秘密共享的方式是向行贿者表明它已对特定的内容进行了编码 值。例如,如果 Oi 不知道行贿者控制哪些节点,那么 Oi 可以 向所有委员会成员提交 0 值股票。然后行贿者可以验证 Oi 的 概率上的合规性。为了避免在任何单轮协议中出现这个问题,我们 要求 Oi 知道至少一个诚实的第二层节点的身份。 使用交互式协议,其中每个第二层节点添加随机化 股份的因素,行贿者能做的最好的事情就是强制 Oi 随机选择 看门狗位。 9.6 隐性激励框架(IIF) FFO 是对 Chainlink 网络中正确行为的隐性激励的一种形式。它 其功能类似于显性权益(即存款),因为它有助于加强经济安全 网络。换句话说,FFO 应包含在(有效)存款中 网络中节点的$d。问题是:我们如何衡量 FFO 和其他形式的隐性激励 在 Chainlink 网络内? 隐性激励框架(IIF)是一套 我们计划为此目的开发的原则和技术。区块链系统 提供多种形式前所未有的透明度,以及节点的高信任记录 他们创造的业绩是我们实现 IIF 如何运作的愿景的跳板。 在这里,我们非常简要地概述了 IIF 关键要素的想法。 IIF 本身将包含一系列我们认为在评估中重要的因素 隐性激励,以及以高保证形式发布相关数据以供分析算法使用的机制。不同的 Chainlink 用户可能 希望以不同的方式使用 IIF,例如,对不同的因素给予不同的权重。 我们期望社区中出现分析服务,帮助用户应用 IIF 根据他们个人的风险评估偏好,我们的目标是促进 通过确保他们获得高可信度和及时的支持数据来提供此类服务, 正如我们下面讨论的(第 9.6.4 节)。 9.6.1 未来的收费机会 节点参与 Chainlink 生态系统,以赚取网络为我们在本文中描述的任何各种服务支付的费用的一部分,从 将普通数据馈送到高级服务,例如去中心化身份、公平排序、 和保密DeFi。 Chainlink 网络中的费用支持节点运营商的成本,例如运行服务器、获取必要的数据许可证和维护 全球员工确保高正常运行时间。 FFO 表示扣除费用后的服务费, 节点在未来会获得收益,或者如果表现出错误行为则会损失。 FFO 是一种有助于保护网络安全的权益形式。 FFO 的一个有用功能是链上数据(由链下数据补充) 数据)建立节点历史的高信任记录,从而实现 FFO 的计算 以透明的、经验驱动的方式。 FFO 的一个简单的一阶度量可以从一个企业的平均净收入中得出 一段时间内的节点(即总收入减去运营费用)。 FFO 可能 然后计算为,例如,累计未来净收入的净现值[114], 换句话说,所有未来收益的时间贴现值。 然而,节点收入可能会波动,如图 17 所示。 更重要的是,节点收入可能不会遵循平稳的分布 随着时间的推移。因此,我们计划在估算 FFO 时探索的其他因素包括: • 绩效历史记录:操作员的绩效历史记录(包括其报告的正确性和及时性以及正常运行时间)提供了一个目标 为用户评价其可靠性的试金石。 因此,性能历史将 为用户选择 oracle 节点提供一个关键因素(或者,随着出现 DONs,他们选择的 DONs)。强劲的业绩历史可能会 与高额持续收入相关。18 18我们打算解决的一个重要研究问题是伪造服务量的检测。图 17:Chainlink 节点在单个数据源 (ETH-USD) 期间赚取的收入 2021 年 3 月具有代表性的一周。 • 数据访问:虽然oracles 可以从开放API 获取多种形式的数据, 某些形式的数据或某些高质量来源可能仅在 认购基础上或通过合同协议。对某些内容的特权访问 数据源可以在创造稳定的收入流方面发挥作用。 • DON 参与:随着 DON 的出现,节点社区将会出现 共同提供特定服务。我们预计许多 DON 将包括 选择性地运营商,参与信誉良好的 DONs 作为 优越的市场地位有助于确保稳定的收入来源。 • 跨平台活动:一些节点运营商可能在其他环境中拥有良好的存在和绩效跟踪记录,例如 PoS validators 或 非 blockchain 上下文中的数据提供者。它们在这些其他系统中的表现(当其数据以可信形式提供时)可以为评估提供信息 他们的表演历史。同样,Chainlink 网络中的错误行为 可能会通过赶走用户(即 FFO)来危及这些其他系统的收入 可以跨平台扩展。 9.6.2 投机性 FFO 节点运营商参与 Chainlink 网络不仅仅是为了从中获得收入 运营,而是创造并定位自己,以利用新的机会来开展工作。换句话说,网络中 oracle 节点的支出也是 关于 DeFi 和其他智能合约应用的未来的积极声明 域以及 oracle 网络的新兴非 blockchain 应用。如今,节点运营商赚取现有 Chainlink 网络上可用的费用,同时 这些与互联网网站上的虚假评论大致相似,只不过问题在 oracle 设置,因为我们有关于货物(即报告)是否已订购和是否已订购的最终记录。 交付——与在网上商店订购的实物商品不同。换句话说,在 oracle 中 即使无法验证客户的真实性,也可以验证性能。建立声誉、业绩历史和运营专业知识,以定位 他们有利于赚取未来网络中可用的费用(当然, 诚实行为)。今天在 Chainlink 生态系统中运行的节点将在此 感觉比新人在赚取额外 Chainlink 费用方面有优势 服务变得可用。这一优势适用于新运营商,以及享有盛誉的科技公司;例如,T-Systems,一个传统的 技术提供商(德国电信的子公司)和 Kraken(一家大型中心化公司) 交换,已在 Chainlink 生态系统中建立了早期存在 [28, 143]。 oracle 节点对未来机会的这种参与可能被视为本身 作为一种投机性 FFO,因此构成 Chainlink 的一种股权形式 网络。 9.6.3 外部声誉 正如我们所描述的,IIF 可以在严格假名的网络中运行 运营商,即不披露所涉及的人员或现实世界实体。 然而,用户选择提供商的一个潜在重要因素是外部因素。 声誉。外部声誉是指对现实世界身份而非假名的可信度的感知。声誉风险 现实世界的身份可以被视为隐性激励的一种形式。我们看信誉 通过 IIF 的视角,即在加密经济学意义上,作为建立 可能会纳入 FFO 估算的跨平台活动。 使用外部声誉作为 FFO 估计因素的好处,而不是 与假名链接相比,外部声誉不仅与绩效相关 运营商现有的活动,也包括未来的活动。例如,如果声誉不好 依附于一个人,它可能会污染这个人未来的企业。换句话说,与假名相比,外部声誉可以捕获更广泛的 FFO 绩效记录,作为个人或既定的不当行为的影响 与假名操作相比,公司更难逃脱。 Chainlink 与去中心化身份技术(第 4.3 节)兼容, 可以为 IIF 中外部声誉的使用提供支持。此类技术 可以验证并从而帮助确保运营商声称的现实世界的准确性 身份.19 9.6.4 开放 IIF 分析 正如我们所指出的,IIF 旨在为以下领域提供可靠的开源数据和工具: 隐性激励分析。 目标是使社区内的提供者能够 开发适合不同部门风险评估需求的分析 Chainlink 用户群。 19如果需要的话,去中心化的身份凭证还可以用经过验证的假名来修饰假名。 补充信息。例如,节点运营商原则上可以使用此类凭证来 证明它是一家财富 500 强公司,但没有透露是哪一家。大量关于节点收益和性能的历史数据 以高度信任、不可变的形式驻留在链上。然而,我们的目标是提供 最全面的可能数据,包括仅在外部可见的行为数据 链,例如链外报告 (OCR) 或 DON 活动。此类数据有可能 内容要丰富。存储它并确保其完整性的最佳方法,即保护它免受 我们相信,篡改将在 DONs 的帮助下,使用所讨论的技术 在第 3.3 节中。 有些激励措施适合直接的衡量形式,例如 staking 存款和基本 FFO。其他的,例如投机性 FFO 和声誉,则更难 以客观的方式进行衡量,但我们认为支持数据的形式,包括 Chainlink 生态系统的历史增长、社交媒体声誉指标等, 即使对于这些难以量化的元素,也可以支持 IIF 分析模型。 我们可以想象专门的 DON 专门用于监视、验证和 记录与节点的链外性能记录相关的数据,以及其他数据 在 IIF 中使用,例如经过验证的身份信息。这些 DON 可以为任何为 Chainlink 社区提供服务的分析提供商提供统一、高信任度的 IIF 数据。 他们还将提供黄金记录,让分析提供商声称 由社区独立验证。 9.7 综合起来:节点运营商激励 综合我们上面关于节点运营商的显性和隐性激励的讨论 提供节点运营商参与并从中受益的方式的整体视图 Chainlink 网络。 作为概念指南,我们可以通过给定的 Chainlink 来表示所涉及的总资产 节点运算符 $S 的粗略、程式化形式如下: \(S ≈\)D + \(F + \)FS + $R, 其中: • $D 是所有网络中所有明确存入的权益的总和,其中 经营者参与; • $F 是所有网络中所有 FFO 总和的净现值 运营商参与的; • $FS 是运营商的投机FFO 的净现值;和 • $R 是Chainlink 生态系统之外的运营商的声誉资产 其 oracle 节点中发现的不当行为可能会危及这一点。 虽然主要是概念性的,但这种粗略的等式有助于表明存在有多种经济因素有利于 Chainlink 节点的高可靠性性能。 除 $D 之外的所有这些因素都存在于当今的 Chainlink 网络中。9.8 经济安全的良性循环 超线性 staking 影响与费用支付表示的结合 因为 IIF 中的未来费用机会 (FFO) 可以带来我们所说的良性循环 oracle 网络中的经济安全。这可以看作是一种经济 规模。随着特定网络保护的总量增加, 增加固定数量的经济安全所需的额外股份会随着增加而减少 每个用户的平均成本。因此,就费用而言,用户加入更便宜 一个已经存在的网络比实现同样的网络经济增长 通过创建新网络来确保安全。重要的是,每个新用户的添加都会降低 该网络所有先前用户的服务成本。 给定特定的费用结构(例如,质押金额的特定收益率), 如果网络赚取的总费用增加,就会刺激额外的流量 投入网络以更高的速度保护网络。具体来说,如果总权益 单个节点在系统中的持有量是有上限的,那么当新的费用支付时 进入系统,提高其FFO,节点数n将增加。感谢 超线性 staking 我们激励制度设计的影响,经济安全 系统将比 n 上升得更快,例如,我们在第 9.4 节中概述的机制中为 n2。 因此,经济安全的平均成本,即贡献的股份数量 一美元的经济安全——将会下降。因此,网络可以向用户收费 较低的费用。假设对 oracle 服务的需求是有弹性的(例如,参见 [31] 了解简要信息) 解释),需求将会上升,产生额外费用和 FFO。 我们用下面的例子来说明这一点。 示例 5. 由于 oracle 网络在我们的激励下具有经济安全性 方案为\(dn2 for stake \)dn,一美元的权益所贡献的经济安全 是 n,因此每美元经济安全的平均成本——即股权数量 对一美元经济安全的贡献是 1/n。 考虑一个网络,其中经济激励完全由 FFO 组成,上限为 每个节点 \(d ≤\)10K。假设网络有 n = 3 个节点。那么平均成本 每美元的经济安全约为 0.33 美元。 假设网络的总 FFO 上升到 \(30K (e.g., to \)31K 以上。给定 每个节点 FFO 的上限,网络增长到(至少)n = 4。现在平均成本 每美元的经济安全下降至约 0.25 美元。 我们在图 18 中示意性地说明了 oracle 网络中经济安全的完整良性循环。 我们强调经济安全的良性循环源于 用户汇集费用。 正是他们的集体 FFO 有利于更大的 网络规模,从而提高集体安全性。我们还注意到,良性循环 经济安全有利于 DON 实现财务可持续性。曾经 创建的、满足用户需求的 DON 应该增长到并超过 oracle 节点的费用收入超过运营成本。
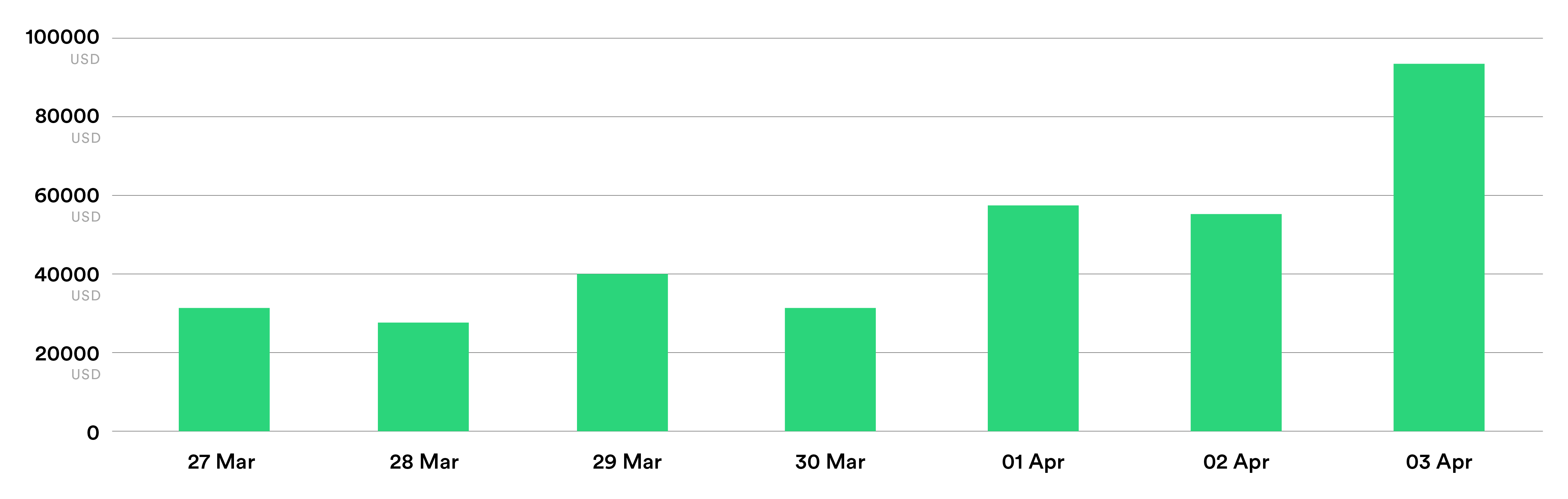
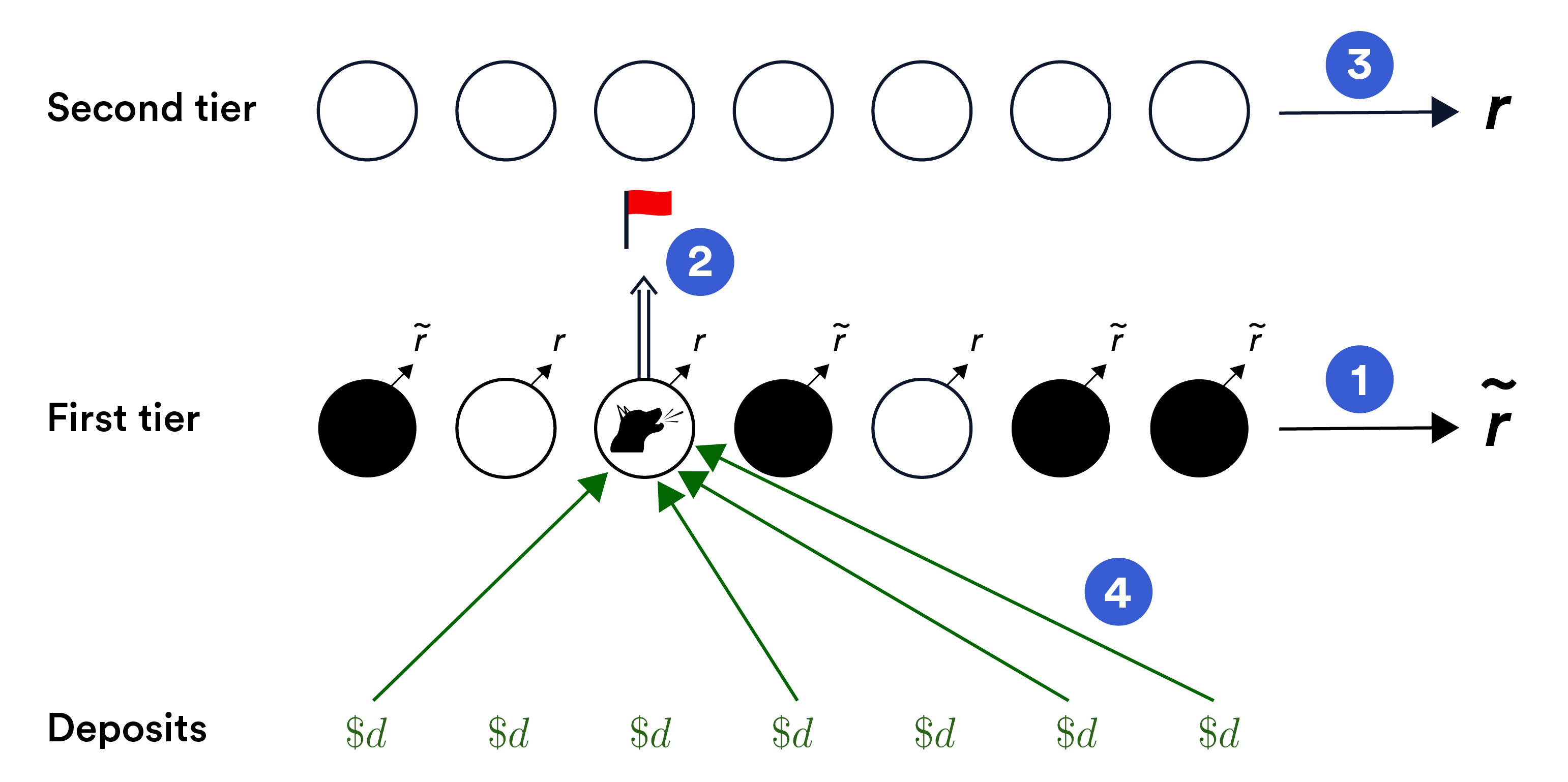
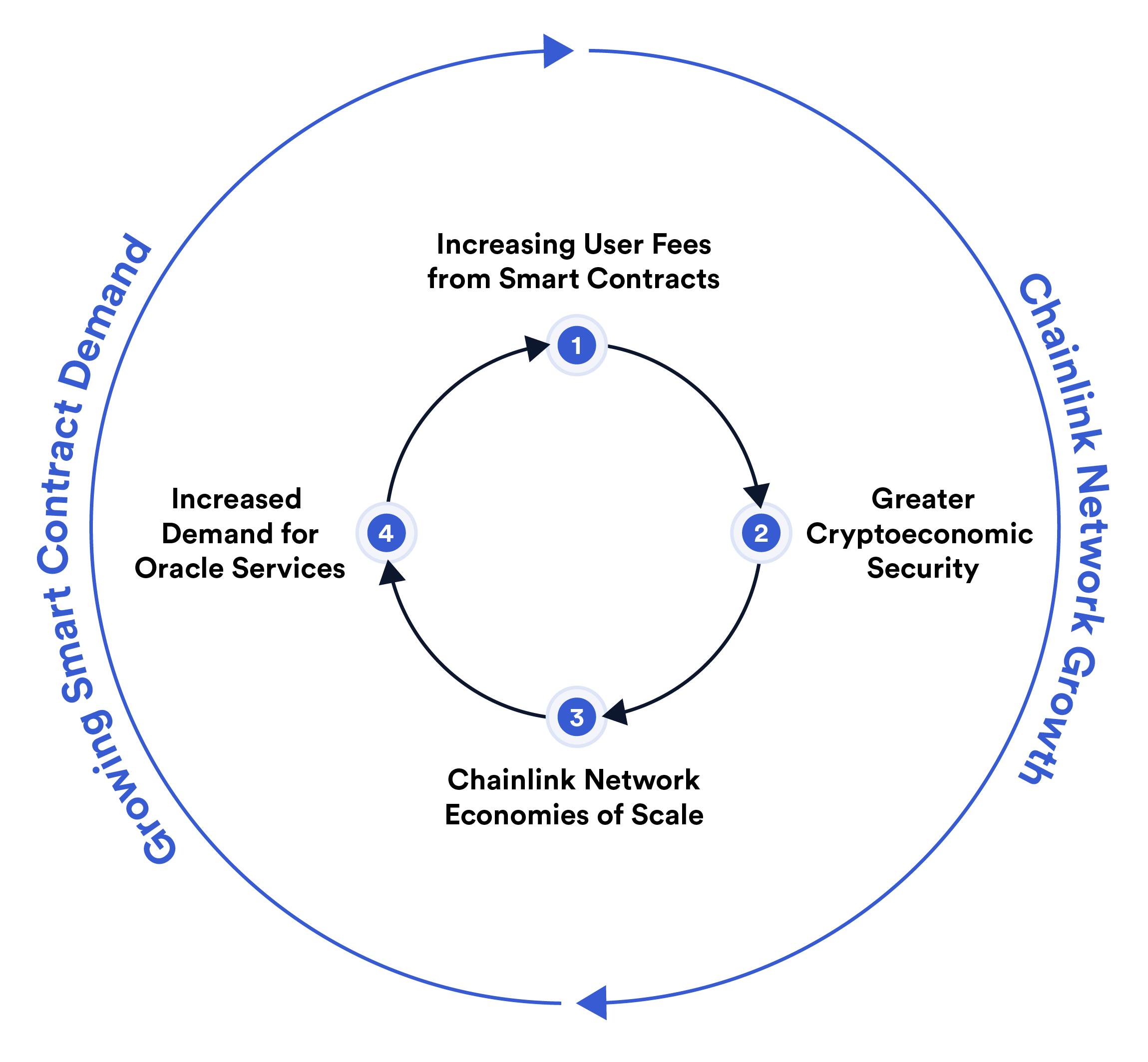
图 18:Chainlink staking 的良性循环示意图。使用费上涨 向 oracle 网络支付 1⃝ 使其增长,从而导致其经济增长 安全2⃝。这种超线性增长在 Chainlink 网络中实现了规模经济 3⃝。具体来说,它意味着经济安全平均成本的降低,即 由费用支付或其他股权来源产生的每美元经济安全 增加。降低成本,转嫁给用户,刺激对 oracle 的需求增加 服务4⃝。 9.9 推动网络增长的其他因素 随着 Chainlink 生态系统的不断扩大,我们相信它的吸引力 对用户的重要性以及作为 blockchain 经济基础设施的重要性将会加速。 oracle 网络提供的值是超线性的,这意味着它增长得更快比网络本身的规模更大。 这种价值的增长来自于 规模经济——随着服务量的增加,每个用户的成本效率更高——以及 网络效应——随着用户更广泛地采用 DON,网络效用增加。 随着现有的 smart contract 继续获得更多价值和全新价值 smart contract 应用程序通过更加去中心化的服务而成为可能, DON 的使用和支付的总费用应该会增加。 增加收费池 转变为创造更加去中心化服务的手段和激励, 从而形成良性循环。 这种良性循环解决了关键的先有鸡还是先有蛋的问题 混合 smart contract 生态系统中的问题:创新 smart contract 功能 通常需要尚不存在的去中心化服务(例如,新的 DeFi 市场通常 需要新的数据源)但需要足够的经济需求才能存在。 各个 smart contract 对现有 DON 的费用汇集将表明对 来自不断增长的用户群的额外去中心化服务,从而催生了它们的诞生 由 DONs 和不断启用新的和多样化的混合 smart contracts。 综上所述,我们认为网络安全的增长是由良性的驱动的 Chainlink staking 机制中的循环体现了更大的增长模式 Chainlink 网络可以帮助实现去中心化的链上经济 服务。
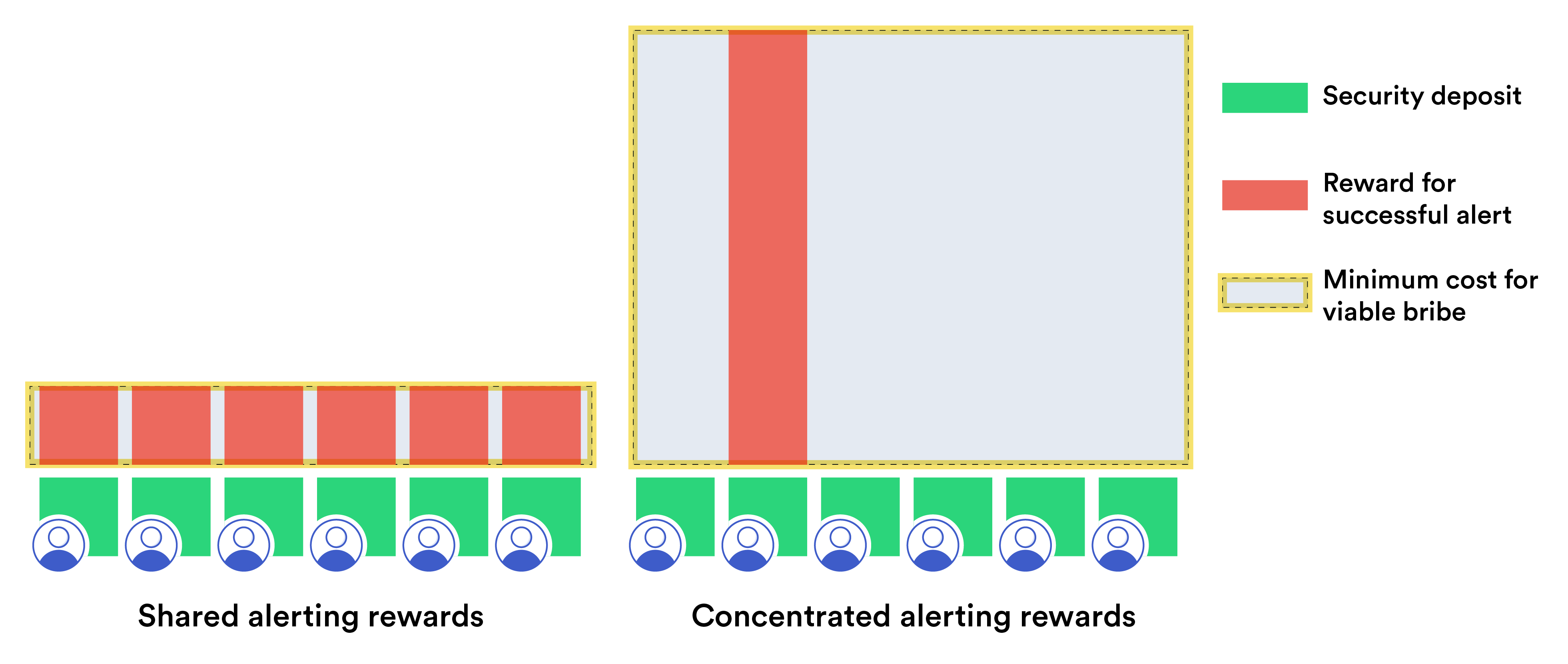
Kesimpulan
Dalam makalah ini, kami telah menetapkan visi evolusi Chainlink. Tema utama dalam visi ini adalah kemampuan jaringan oracle untuk menyediakan layanan yang lebih luas smart contracts dari sekedar pengiriman data. Menggunakan DONs sebagai fondasi untuk layanan terdesentralisasi di masa depan, Chainlink bertujuan untuk menyediakan fungsionalitas oracle yang berkinerja tinggi dan meningkatkan kerahasiaan. Jaringan oracle-nya akan menawarkan minimalisasi kepercayaan yang kuat melalui kombinasi mekanisme ekonomi kripto yang berprinsip seperti staking dan pagar pengaman yang disusun dengan cermat dan penegakan tingkat layanan pada rantai utama yang mengandalkan. DONs juga akan membantu sistem lapisan-2 menerapkan kebijakan pemesanan transaksi yang fleksibel dan adil, serta mengurangi biaya bahan bakar untuk transaksi yang dialihkan mempool. Secara bersama-sama, Semua kemampuan ini mengarah ke teknologi hybrid cerdas yang aman dan kaya fungsi kontrak. Fleksibilitas DON akan meningkatkan layanan Chainlink yang ada dan meningkatkan banyak fitur dan aplikasi tambahan smart contract. Di antaranya mulus koneksi ke berbagai sistem off-chain, pembuatan identitas terdesentralisasi dari data yang ada, saluran prioritas untuk membantu memastikan pengiriman infrastruktur penting secara tepat waktu transaksi, dan instrumen DeFi yang menjaga kerahasiaan. Visi yang kami kemukakan di sini adalah visi yang ambisius. Dalam jangka pendek, kami berupaya memberdayakan kontrak hibrida untuk mencapai tujuan di luar jangkauan smart contracts saat ini dalam jangka panjang kami bertujuan untuk mewujudkan lapisan meta yang terdesentralisasi. Untunglah kita bisa menggambar pada alat dan ide baru—mulai dari algoritma konsensus hingga bukti tanpa pengetahuan sistem—yang dikembangkan komunitas sebagai hasil penelitian yang berkembang pesat.
Demikian pula, kami berharap untuk memprioritaskan implementasi ide-ide dalam makalah ini sebagai tanggapannya dengan kebutuhan komunitas pengguna Chainlink. Kita nantikan tahap berikutnya dalam upaya kami untuk memberdayakan smart contracts melalui konektivitas universal dan membangun teknologi terdesentralisasi sebagai tulang punggung generasi keuangan dunia berikutnya dan sistem hukum. Ucapan Terima Kasih Terima kasih kepada Julian Alterini dan Shawn Lee yang telah menyajikan angka-angka dalam makalah ini.
结论
在本文中,我们提出了 Chainlink 的演变愿景。主题 在这一愿景中,oracle 网络有能力为以下用户提供更广泛的服务: smart contracts 比单纯的数据传输。使用 DON 作为未来去中心化服务的基础,Chainlink 将致力于提供高性能、保密性增强的 oracle 功能。其 oracle 网络将提供强大的信任最小化 通过结合原则性的加密经济机制,例如 staking 和 精心设计的护栏和依赖主链的服务水平执行。 DONs 还将帮助第 2 层系统对交易执行灵活、公平的排序策略,并降低内存池路由交易的 Gas 成本。综合起来, 这些功能都朝着安全且功能丰富的混合智能方向发展 合同。 DON 的灵活性将增强现有的 Chainlink 服务并带来 许多附加的 smart contract 功能和应用程序。其中,无缝衔接 连接到各种链下系统,去中心化身份创建 现有数据、优先渠道有助于确保及时交付关键基础设施 交易和保密 DeFi 工具。 我们在这里提出的愿景是雄心勃勃的。在短期内,我们寻求增强能力 混合合同来实现目前 smart contract 无法实现的目标,同时 从长远来看,我们的目标是实现去中心化的元层。庆幸的是我们可以画画 新工具和想法——从共识算法到零知识证明 系统——社区正在开发该系统,作为快速发展的研究的成果。
同样,我们希望优先实施本文中的想法作为回应 满足 Chainlink 用户社区的需求。我们期待下一阶段 我们寻求通过通用连接来增强 smart contract 的能力并建立 去中心化技术是世界下一代金融的支柱 和法律制度。 致谢 感谢 Julian Alterini 和 Shawn Lee 绘制了本文中的数据。