
比特币:一种点对点电子现金系统
Abstract
순수한 peer-to-peer 방식의 전자 화폐는 금융 기관을 거치지 않고 한쪽에서 다른 쪽으로 직접 온라인 지불을 가능하게 할 것이다. 전자 서명이 해결책의 일부를 제공하지만, 이중 지불을 방지하기 위해 여전히 신뢰할 수 있는 제3자가 필요하다면 주요 이점은 사라진다. 우리는 peer-to-peer 네트워크를 이용한 이중 지불 문제의 해결책을 제안한다. 이 네트워크는 거래를 hash 기반의 proof-of-work 체인에 hash하여 타임스탬프를 부여하며, proof-of-work를 다시 수행하지 않고는 변경할 수 없는 기록을 형성한다. 가장 긴 체인은 목격된 사건의 순서에 대한 증거일 뿐만 아니라, 그것이 가장 큰 CPU 연산 능력의 풀에서 나왔다는 증거이기도 하다. CPU 연산 능력의 과반수가 네트워크를 공격하려고 협력하지 않는 노드들에 의해 통제되는 한, 그들은 가장 긴 체인을 생성하여 공격자를 앞지를 것이다. 네트워크 자체는 최소한의 구조만을 필요로 한다. 메시지는 최선 노력(best effort) 기반으로 브로드캐스트되며, 노드들은 자유롭게 네트워크를 떠났다가 다시 참여할 수 있고, 부재 중에 일어난 일의 증거로서 가장 긴 proof-of-work 체인을 수용한다.
Abstract
一种完全的点对点电子现金系统将允许在线支付从一方直接发送到另一方,而无需通过金融机构。数字签名提供了部分解决方案,但如果仍然需要一个可信赖的第三方来防止双重支付,那么其主要优势就会丧失。我们提出一种使用点对点网络来解决双重支付问题的方案。该网络通过将交易 hash 到一条基于 hash 的 proof-of-work 的持续增长的链中来为交易打上时间戳,形成一份不重做 proof-of-work 就无法更改的记录。最长的链不仅作为所见证事件序列的证明,而且证明它来自最大的 CPU 算力池。只要大多数 CPU 算力由不合谋攻击网络的节点控制,它们就会生成最长的链并超过攻击者。该网络本身只需要最小化的结构。消息以尽最大努力的方式广播,节点可以随时离开和重新加入网络,并接受最长的 proof-of-work 链作为其离开期间所发生事件的证明。
Introduction
인터넷 상의 상거래는 전자 지불을 처리하는 신뢰할 수 있는 제3자 역할을 하는 금융 기관에 거의 전적으로 의존하게 되었다. 이 시스템은 대부분의 거래에서 충분히 잘 작동하지만, 신뢰 기반 모델의 본질적인 약점으로부터 여전히 벗어나지 못한다. 금융 기관이 분쟁 중재를 피할 수 없기 때문에, 완전히 비가역적인 거래는 사실상 불가능하다. 중재 비용은 거래 비용을 증가시키며, 최소 실용적 거래 규모를 제한하고, 소규모 일상 거래의 가능성을 차단한다. 또한 비가역적 서비스에 대해 비가역적 지불을 할 수 없게 됨으로써 더 광범위한 비용이 발생한다. 취소 가능성이 존재하면 신뢰의 필요성이 확산된다. 상인은 고객을 경계해야 하며, 본래 필요하지 않을 정보까지 요구하게 된다. 일정 비율의 사기는 불가피한 것으로 받아들여진다. 이러한 비용과 지불 불확실성은 물리적 화폐를 사용하여 대면 거래에서는 피할 수 있지만, 신뢰할 수 있는 당사자 없이 통신 채널을 통해 지불하는 메커니즘은 존재하지 않는다.
필요한 것은 신뢰 대신 암호학적 증명에 기반한 전자 지불 시스템으로, 신뢰할 수 있는 제3자 없이도 두 당사자가 직접 거래할 수 있게 하는 것이다. 계산적으로 되돌리기가 실질적으로 불가능한 거래는 판매자를 사기로부터 보호하고, 일상적인 에스크로 메커니즘을 쉽게 구현하여 구매자를 보호할 수 있다. 이 논문에서 우리는 거래의 시간 순서에 대한 계산적 증명을 생성하기 위해 peer-to-peer 분산 타임스탬프 서버를 사용하는 이중 지불 문제의 해결책을 제안한다. 이 시스템은 정직한 노드들이 공격자 노드들의 어떤 협력 그룹보다 더 많은 CPU 연산 능력을 집합적으로 통제하는 한 안전하다.
Introduction
互联网上的商业活动已经几乎完全依赖金融机构作为可信赖的第三方来处理电子支付。虽然该系统对于大多数交易运行得足够好,但它仍然受制于基于信任模型的固有弱点。完全不可逆的交易实际上是不可能的,因为金融机构无法避免调解纠纷。调解成本增加了交易成本,限制了最小实际交易规模,并切断了小额临时交易的可能性,而且在无法为不可逆服务进行不可逆支付方面存在更广泛的成本。由于存在逆转的可能性,对信任的需求就会蔓延。商家必须对客户保持警惕,向他们索要比其他情况下更多的信息。一定比例的欺诈被认为是不可避免的。这些成本和支付的不确定性可以通过使用实物货币进行面对面交易来避免,但不存在一种无需可信赖方就能通过通信渠道进行支付的机制。
所需要的是一种基于密码学证明而非信任的电子支付系统,允许任何两个有意愿的当事方直接进行交易,而无需可信赖的第三方。在计算上不可行的逆转交易将保护卖家免受欺诈,而常规的托管机制可以很容易地实施以保护买家。在本文中,我们提出一种使用点对点分布式时间戳服务器来生成交易时间顺序的计算证明的双重支付问题解决方案。只要诚实节点共同控制的 CPU 算力超过任何合谋的攻击者节点群组,该系统就是安全的。
Transactions
우리는 전자 화폐를 전자 서명의 체인으로 정의한다. 각 소유자는 이전 거래의 hash와 다음 소유자의 공개 키를 전자 서명하고 이를 화폐의 끝에 추가함으로써 화폐를 다음 소유자에게 전달한다. 수취인은 서명을 검증하여 소유권의 체인을 확인할 수 있다.
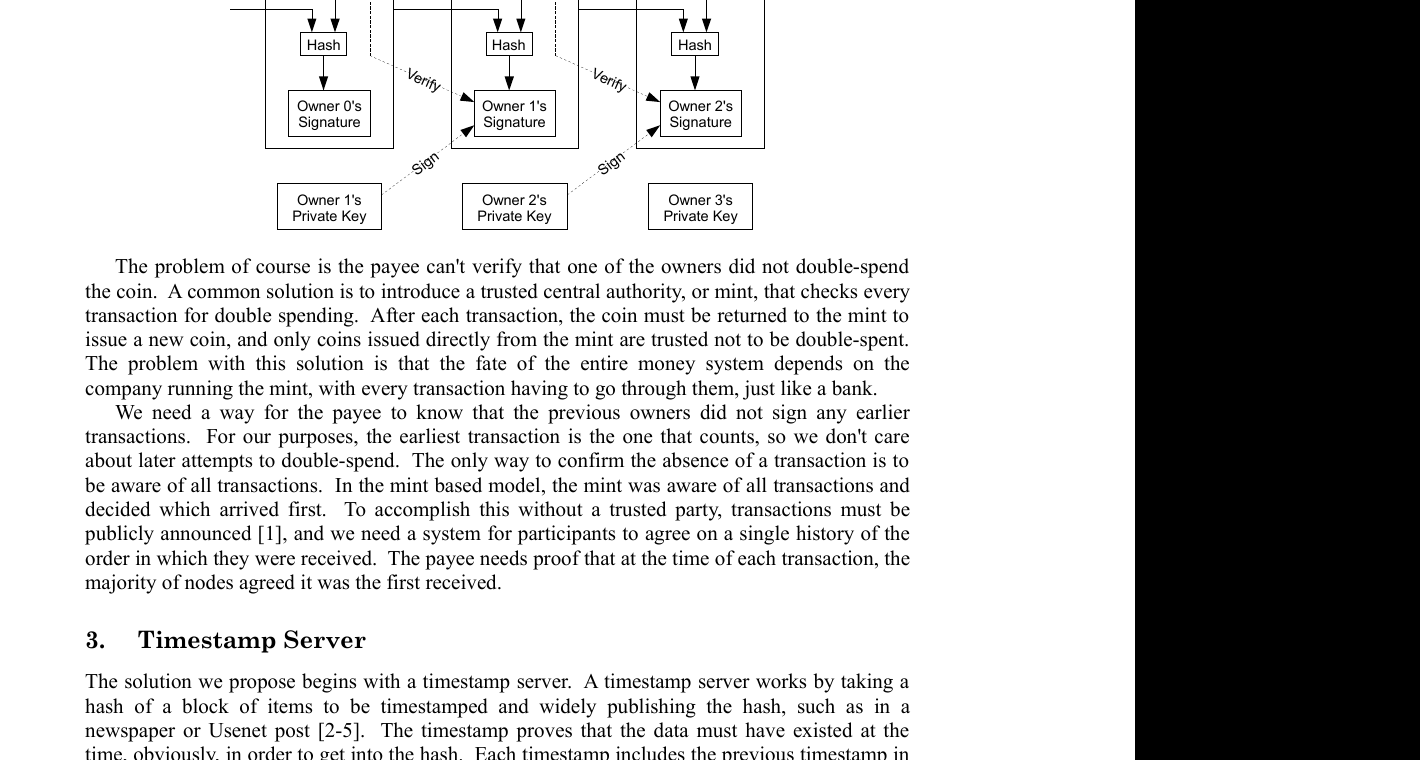
물론 문제는 수취인이 소유자 중 한 명이 화폐를 이중 지불하지 않았는지 검증할 수 없다는 것이다. 일반적인 해결책은 모든 거래의 이중 지불 여부를 확인하는 신뢰할 수 있는 중앙 기관, 즉 조폐국을 도입하는 것이다. 각 거래 후, 화폐는 새로운 화폐를 발행하기 위해 조폐국으로 반환되어야 하며, 조폐국에서 직접 발행된 화폐만이 이중 지불되지 않았다고 신뢰된다. 이 해결책의 문제는 전체 화폐 시스템의 운명이 조폐국을 운영하는 회사에 달려 있으며, 은행처럼 모든 거래가 그들을 거쳐야 한다는 것이다.
우리는 수취인이 이전 소유자들이 어떤 더 이른 거래에도 서명하지 않았음을 알 수 있는 방법이 필요하다. 우리의 목적상, 가장 이른 거래가 유효한 것이므로 이후의 이중 지불 시도는 신경 쓰지 않는다. 거래의 부재를 확인하는 유일한 방법은 모든 거래를 인지하는 것이다. 조폐국 기반 모델에서, 조폐국은 모든 거래를 인지하고 어떤 것이 먼저 도착했는지 결정했다. 신뢰할 수 있는 당사자 없이 이를 달성하려면, 거래는 공개적으로 발표되어야 하며[^1], 참여자들이 거래가 수신된 순서에 대한 단일한 이력에 동의하는 시스템이 필요하다. 수취인은 각 거래 시점에 노드의 과반수가 그것이 최초로 수신되었다는 데 동의했다는 증거가 필요하다.
Transactions
我们将一枚电子货币定义为一条数字签名链。每个所有者通过对前一笔交易的 hash 和下一个所有者的公钥进行数字签名,并将这些附加到该货币的末尾,从而将货币转移给下一个所有者。收款人可以验证签名以验证所有权链。
当然,问题在于收款人无法验证某个所有者是否对该货币进行了双重支付。一个常见的解决方案是引入一个可信赖的中央权威机构,即铸币厂,来检查每笔交易是否存在双重支付。每次交易后,该货币必须返回铸币厂以发行新的货币,并且只有直接从铸币厂发行的货币才被信任未被双重支付。这个方案的问题是,整个货币系统的命运取决于运营铸币厂的公司,每笔交易都必须经过他们,就像银行一样。
我们需要一种方式让收款人知道前任所有者没有签署任何更早的交易。就我们的目的而言,最早的交易是算数的那个,所以我们不关心后来的双重支付尝试。确认一笔交易不存在的唯一方法是了解所有交易。在基于铸币厂的模型中,铸币厂了解所有交易并决定哪个先到达。为了在没有可信赖方的情况下实现这一点,交易必须被公开宣布 [^1],并且我们需要一个系统让参与者就它们被接收的顺序的单一历史达成一致。收款人需要证明在每笔交易发生时,大多数节点都同意它是第一个被接收的。
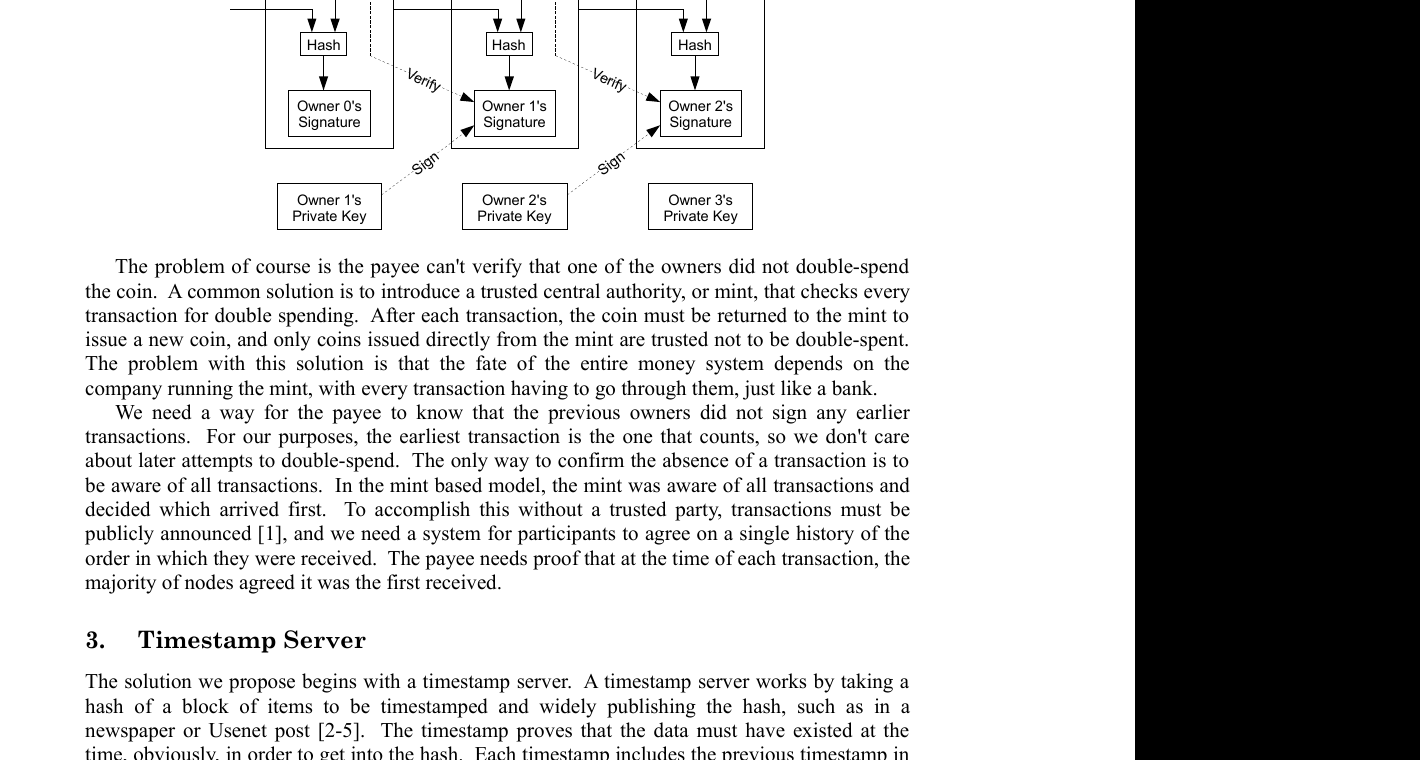
Timestamp Server
우리가 제안하는 해결책은 타임스탬프 서버에서 시작한다. 타임스탬프 서버는 타임스탬프를 부여할 항목 블록의 hash를 취하고, 그 hash를 신문이나 유즈넷 게시물[^2] [^3] [^4] [^5]과 같이 널리 공개하는 방식으로 작동한다. 타임스탬프는 hash에 포함되기 위해서는 당연히 그 시점에 데이터가 존재했어야 함을 증명한다. 각 타임스탬프는 자신의 hash에 이전 타임스탬프를 포함하여 체인을 형성하며, 추가되는 각 타임스탬프는 그 이전의 타임스탬프들을 강화한다.
Proof-of-Work
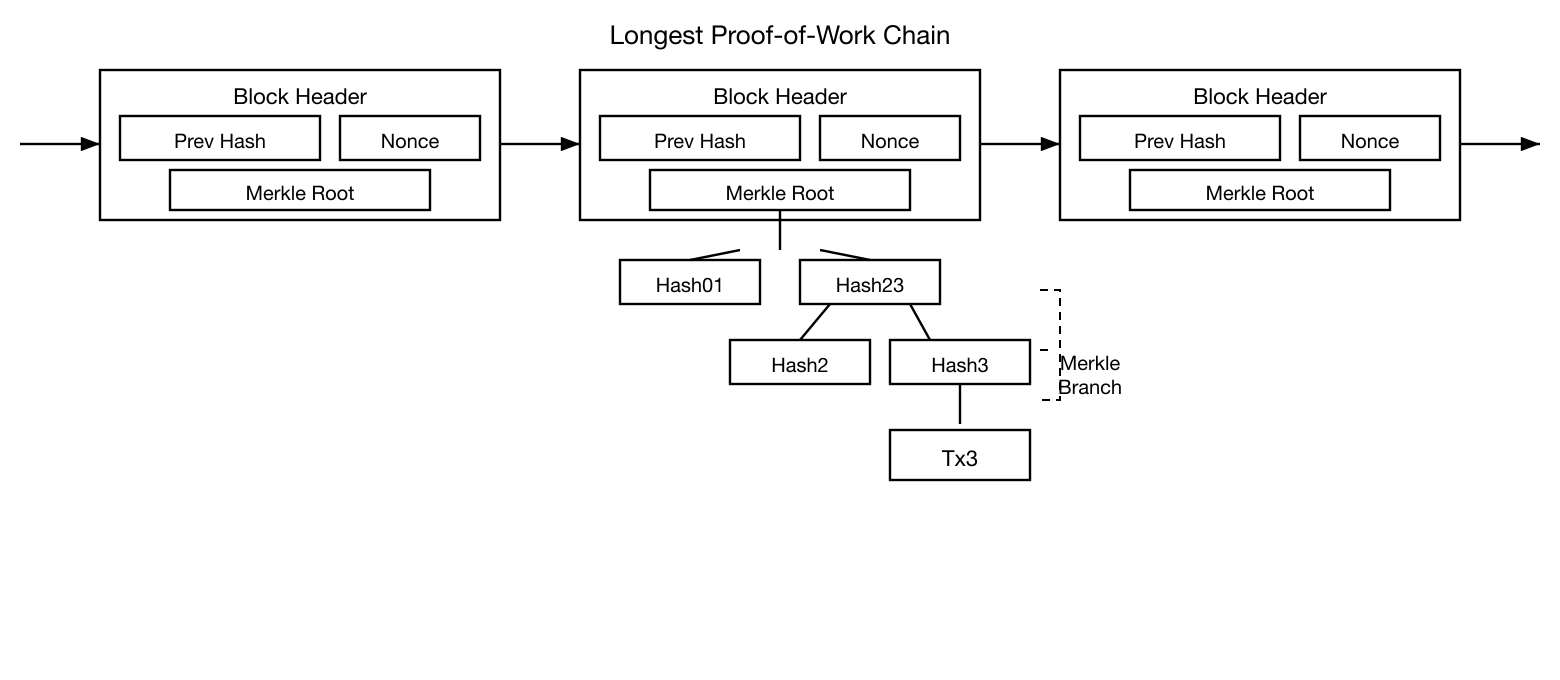
peer-to-peer 기반으로 분산 타임스탬프 서버를 구현하려면, 신문이나 유즈넷 게시물 대신 Adam Back의 Hashcash[^6]와 유사한 proof-of-work 시스템을 사용해야 한다. proof-of-work는 SHA-256과 같은 방식으로 hash했을 때, hash가 일정 수의 0 비트로 시작하는 값을 찾는 것을 포함한다. 필요한 평균 작업량은 요구되는 0 비트 수에 대해 지수적이며, 단일 hash 실행으로 검증할 수 있다.
우리의 타임스탬프 네트워크에서, 블록의 hash가 요구되는 0 비트를 갖는 값이 발견될 때까지 블록 내의 nonce를 증가시키는 방식으로 proof-of-work를 구현한다. CPU 노력이 proof-of-work를 충족하도록 투입되면, 그 작업을 다시 수행하지 않고는 블록을 변경할 수 없다. 이후 블록들이 그 뒤에 체인으로 연결되므로, 해당 블록을 변경하려면 그 이후의 모든 블록을 다시 수행하는 작업이 포함된다.
proof-of-work는 다수결 의사 결정에서 대표성을 결정하는 문제도 해결한다. 만약 다수결이 1-IP-주소-1-투표에 기반한다면, 다수의 IP를 할당할 수 있는 누구라도 이를 전복할 수 있다. proof-of-work는 본질적으로 1-CPU-1-투표이다. 다수결 결정은 가장 큰 proof-of-work 노력이 투입된 가장 긴 체인으로 대표된다. CPU 연산 능력의 과반수가 정직한 노드에 의해 통제되면, 정직한 체인이 가장 빠르게 성장하여 경쟁하는 어떤 체인도 앞지를 것이다. 과거 블록을 수정하려면, 공격자는 해당 블록과 그 이후 모든 블록의 proof-of-work를 다시 수행한 후 정직한 노드들의 작업을 따라잡고 능가해야 한다. 뒤처진 공격자가 따라잡을 확률이 후속 블록이 추가됨에 따라 지수적으로 감소함을 나중에 보일 것이다.
증가하는 하드웨어 속도와 시간에 따라 변동하는 노드 운영에 대한 관심을 보상하기 위해, proof-of-work 난이도는 시간당 평균 블록 수를 목표로 하는 이동 평균에 의해 결정된다. 블록이 너무 빨리 생성되면 난이도가 증가한다.
Proof-of-Work
为了在点对点的基础上实现分布式时间戳服务器,我们需要使用类似于 Adam Back 的 Hashcash [^6] 的 proof-of-work 系统,而不是报纸或 Usenet 帖子。proof-of-work 涉及扫描一个值,使得对该值进行 hash(例如使用 SHA-256)时,hash 以一定数量的零位开头。所需的平均工作量随所需零位数呈指数增长,并且可以通过执行一次 hash 来验证。
对于我们的时间戳网络,我们通过在区块中递增一个 nonce 来实现 proof-of-work,直到找到一个使区块的 hash 满足所需零位数的值。一旦 CPU 花费了足够的努力使其满足 proof-of-work,该区块就无法在不重做工作的情况下被更改。随着后续区块被链接在其后,更改该区块的工作将包括重做其后所有区块的工作。
proof-of-work 还解决了在多数决定中确定代表性的问题。如果多数决定是基于一个 IP 地址一票,那么任何能够分配大量 IP 的人都可以颠覆它。proof-of-work 本质上是一个 CPU 一票。多数决定由最长的链代表,因为它投入了最大的 proof-of-work 努力。如果大多数 CPU 算力由诚实节点控制,诚实链将增长最快并超过任何竞争链。要修改一个过去的区块,攻击者必须重做该区块及其后所有区块的 proof-of-work,然后追上并超过诚实节点的工作。我们将在后面展示,一个较慢的攻击者追上的概率随着后续区块的增加呈指数下降。
为了补偿不断提高的硬件速度和随时间变化的运行节点兴趣,proof-of-work 难度由一个移动平均值确定,目标是每小时平均产出一定数量的区块。如果它们生成得太快,难度就会增加。
Network
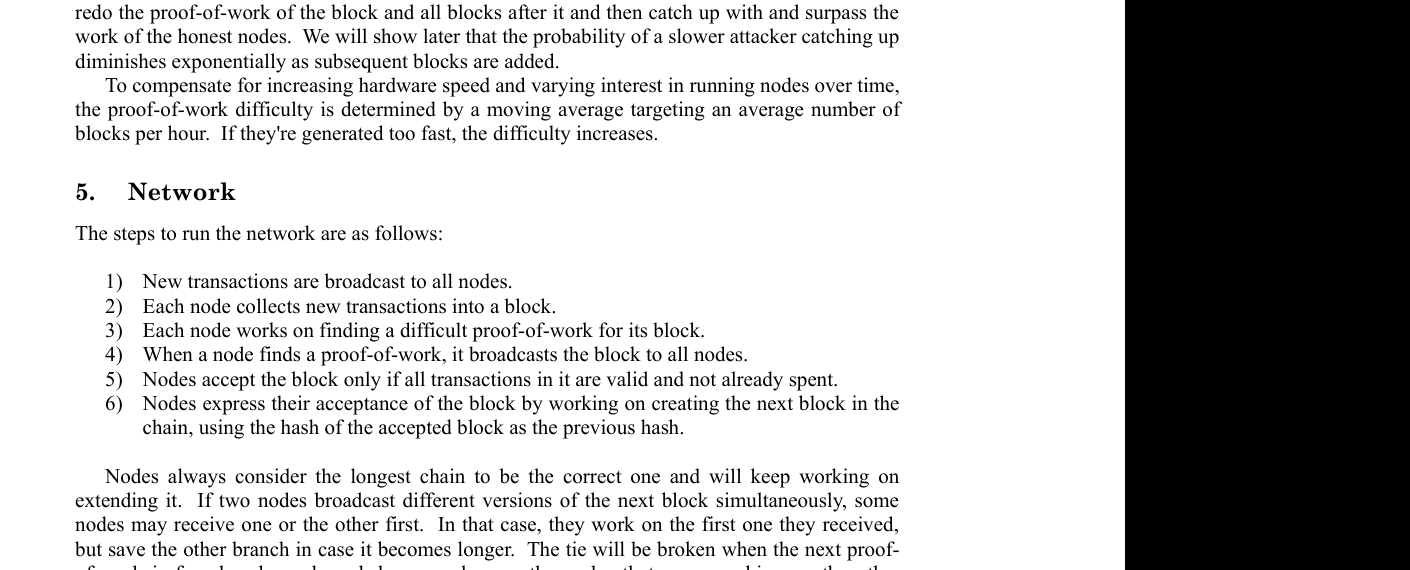
네트워크를 운영하는 단계는 다음과 같다:
- 새로운 거래가 모든 노드에 브로드캐스트된다.
- 각 노드는 새로운 거래를 블록에 수집한다.
- 각 노드는 자신의 블록에 대한 어려운 proof-of-work를 찾기 위해 작업한다.
- 노드가 proof-of-work를 찾으면, 해당 블록을 모든 노드에 브로드캐스트한다.
- 노드들은 블록 내의 모든 거래가 유효하고 아직 지출되지 않은 경우에만 블록을 수락한다.
- 노드들은 수락된 블록의 hash를 이전 hash로 사용하여 체인의 다음 블록을 생성하는 작업을 함으로써 블록 수락을 표현한다.
노드들은 항상 가장 긴 체인을 올바른 것으로 간주하고 이를 연장하는 작업을 계속한다. 만약 두 노드가 다음 블록의 서로 다른 버전을 동시에 브로드캐스트하면, 일부 노드는 한쪽을, 다른 노드는 다른 쪽을 먼저 수신할 수 있다. 이 경우, 먼저 수신한 것에 대해 작업하되, 더 길어질 경우를 대비하여 다른 분기를 저장한다. 다음 proof-of-work가 발견되어 한 분기가 더 길어지면 동률은 깨지며, 다른 분기에서 작업하던 노드들은 더 긴 분기로 전환한다.
새로운 거래 브로드캐스트가 반드시 모든 노드에 도달할 필요는 없다. 많은 노드에 도달하는 한, 머지않아 블록에 포함될 것이다. 블록 브로드캐스트 역시 누락된 메시지에 대해 관대하다. 만약 노드가 블록을 수신하지 못하면, 다음 블록을 수신할 때 하나를 놓쳤음을 인지하고 해당 블록을 요청할 것이다.
Network
运行该网络的步骤如下:
- 新交易被广播到所有节点。
- 每个节点将新交易收集到一个区块中。
- 每个节点为其区块寻找一个困难的 proof-of-work。
- 当一个节点找到一个 proof-of-work 时,它将该区块广播到所有节点。
- 节点只有在区块中所有交易都是有效的且未被花费过的情况下才接受该区块。
- 节点通过在链中创建下一个区块来表示对该区块的接受,使用被接受区块的 hash 作为前一个 hash。
节点始终将最长的链视为正确的链,并将继续在其上扩展。如果两个节点同时广播了下一个区块的不同版本,一些节点可能先接收到其中一个或另一个。在这种情况下,它们在先接收到的版本上工作,但保留另一个分支以防它变得更长。当下一个 proof-of-work 被找到且其中一个分支变得更长时,平局将被打破;在另一个分支上工作的节点将切换到更长的那个。
新交易广播不一定需要到达所有节点。只要它们到达足够多的节点,它们不久就会进入一个区块。区块广播也容忍丢失的消息。如果一个节点没有收到一个区块,它会在收到下一个区块并意识到它遗漏了一个时请求该区块。
Incentive
관례적으로, 블록의 첫 번째 거래는 블록 생성자가 소유하는 새로운 화폐를 시작하는 특별한 거래이다. 이는 노드들이 네트워크를 지원할 인센티브를 추가하며, 화폐를 발행할 중앙 기관이 없으므로 화폐를 유통에 최초로 배분하는 방법을 제공한다. 일정량의 새로운 화폐가 꾸준히 추가되는 것은 금 채굴자들이 자원을 투입하여 금을 유통에 추가하는 것과 유사하다. 우리의 경우, 투입되는 것은 CPU 시간과 전기이다.
인센티브는 거래 수수료로도 충당될 수 있다. 거래의 출력 값이 입력 값보다 작으면, 그 차이는 해당 거래를 포함하는 블록의 인센티브 값에 추가되는 거래 수수료이다. 사전에 정해진 수의 화폐가 유통에 들어가면, 인센티브는 완전히 거래 수수료로 전환될 수 있으며, 완전히 인플레이션이 없게 된다.
인센티브는 노드들이 정직하게 유지되도록 장려하는 데 도움이 될 수 있다. 탐욕스러운 공격자가 모든 정직한 노드보다 더 많은 CPU 연산 능력을 모을 수 있다면, 자신의 지불을 되돌려 훔치는 사기에 사용하거나, 새로운 화폐를 생성하는 데 사용하는 것 중에서 선택해야 한다. 그는 다른 모든 사람을 합친 것보다 더 많은 새로운 화폐를 자신에게 유리하게 하는 규칙대로 행동하는 것이, 시스템과 자신의 부의 유효성을 훼손하는 것보다 더 수익성이 높다고 판단해야 할 것이다.
Incentive
按照惯例,区块中的第一笔交易是一笔特殊交易,它创建一枚由区块创建者拥有的新货币。这为节点支持网络增加了激励,并提供了一种将货币最初分配到流通中的方式,因为没有中央权威机构来发行它们。稳定地增加固定数量的新货币类似于金矿矿工消耗资源将黄金加入流通。在我们的案例中,消耗的是 CPU 时间和电力。
激励也可以通过交易费来资助。如果一笔交易的输出值小于其输入值,差额就是交易费,它被加到包含该交易的区块的激励值中。一旦预定数量的货币进入流通,激励就可以完全过渡到交易费,并且完全没有通货膨胀。
激励可能有助于鼓励节点保持诚实。如果一个贪婪的攻击者能够集结比所有诚实节点更多的 CPU 算力,他将不得不在使用它来通过偷回自己的付款来欺骗人们,或使用它来生成新货币之间做出选择。他应该发现按照规则行事更有利可图,因为这些规则使他获得比所有其他人加起来还多的新货币,而不是破坏系统和他自身财富的有效性。
Reclaiming Disk Space
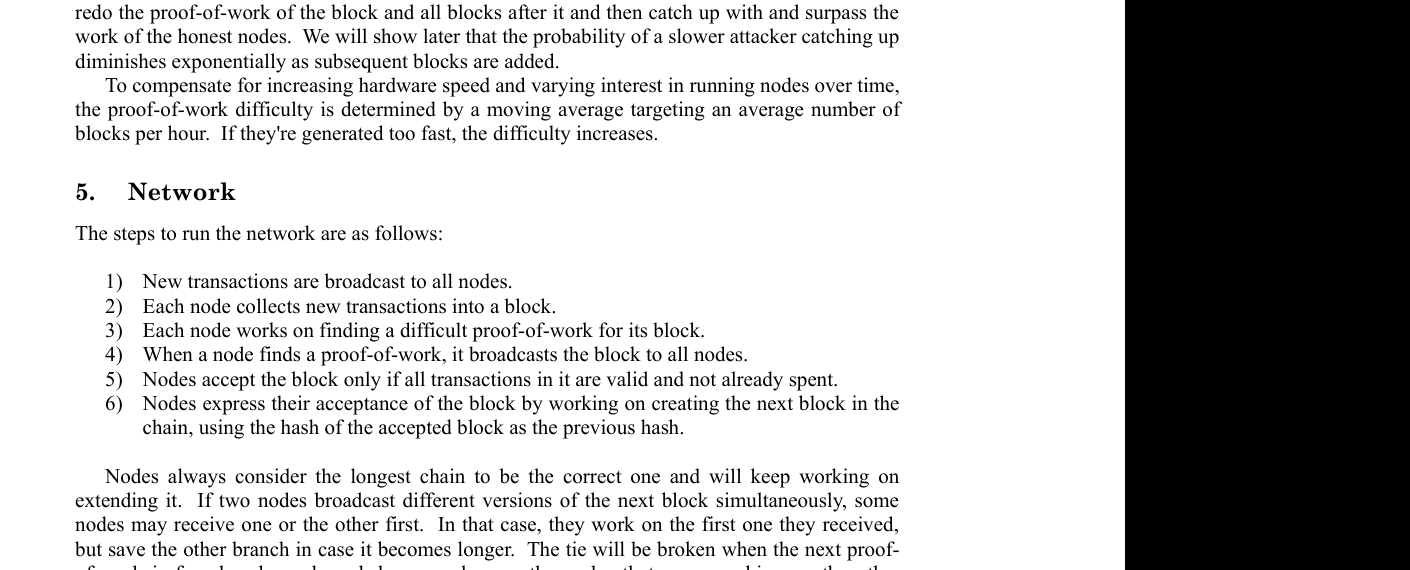
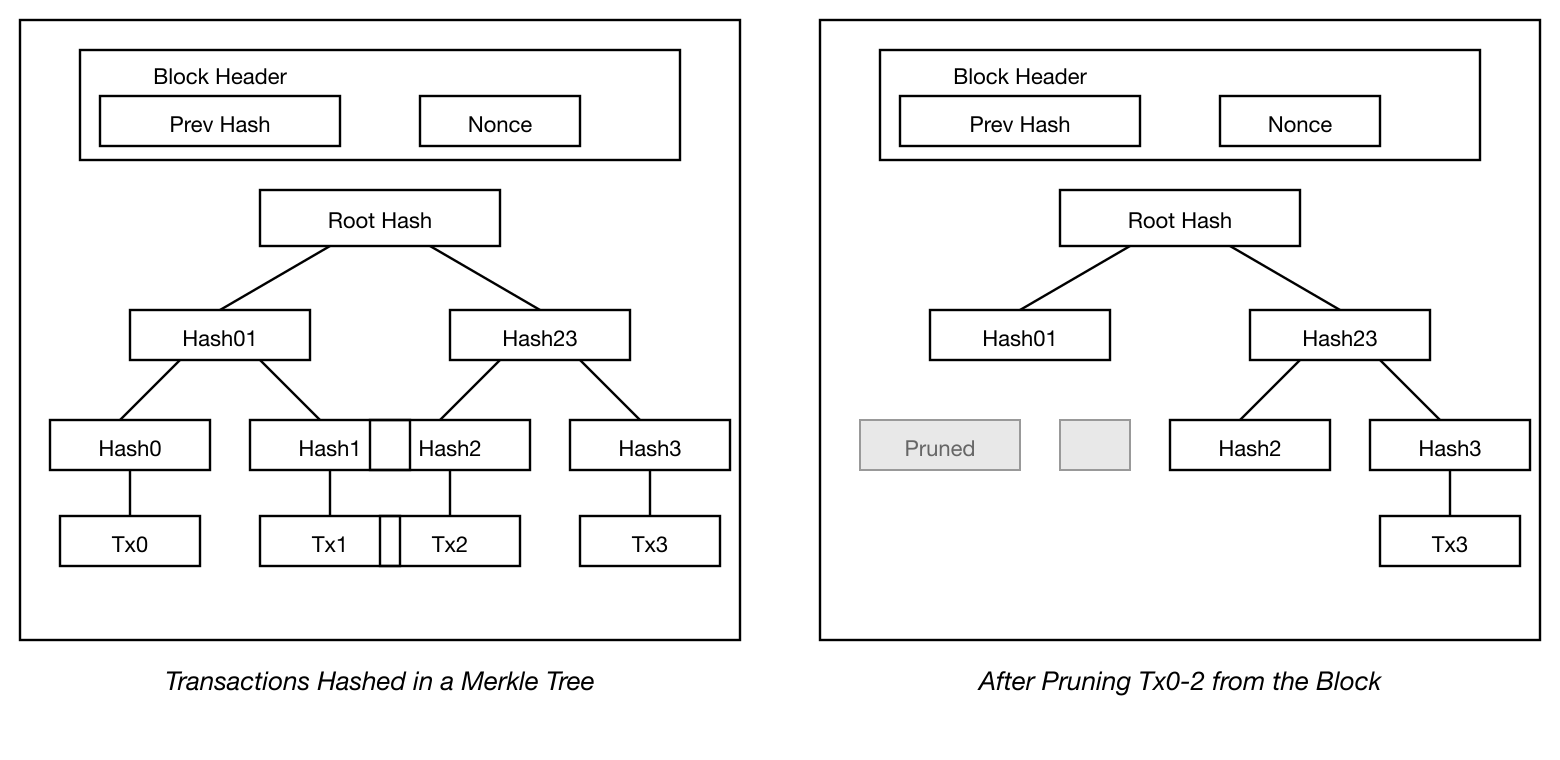
화폐의 최신 거래가 충분한 블록 아래에 묻히면, 그 이전의 지출된 거래들은 디스크 공간을 절약하기 위해 폐기할 수 있다. 블록의 hash를 깨뜨리지 않으면서 이를 용이하게 하기 위해, 거래들은 Merkle Tree[^7] [^2] [^5]로 hash되며, 루트만 블록의 hash에 포함된다. 오래된 블록은 트리의 가지를 잘라내어 압축할 수 있다. 내부 hash는 저장할 필요가 없다.
거래가 없는 블록 헤더는 약 80바이트이다. 블록이 10분마다 생성된다고 가정하면, 80바이트 * 6 * 24 * 365 = 연간 4.2MB이다. 2008년 기준으로 컴퓨터 시스템이 일반적으로 2GB RAM과 함께 판매되고, 무어의 법칙이 연간 1.2GB의 현재 성장률을 예측하고 있으므로, 블록 헤더가 메모리에 유지되어야 하더라도 저장 공간은 문제가 되지 않을 것이다.
Reclaiming Disk Space
一旦一枚货币中的最新交易被埋在足够多的区块之下,之前已花费的交易就可以被丢弃以节省磁盘空间。为了在不破坏区块 hash 的情况下实现这一点,交易被 hash 到一棵 Merkle Tree [^7] [^2] [^5] 中,只有根节点包含在区块的 hash 中。旧区块随后可以通过裁剪树的分支来压缩。内部 hash 不需要被存储。
一个没有交易的区块头大约是 80 字节。如果我们假设区块每 10 分钟生成一次,80 字节 * 6 * 24 * 365 = 每年 4.2MB。截至 2008 年,计算机系统通常配备 2GB 的 RAM,而摩尔定律预测当前每年增长 1.2GB,即使区块头必须保存在内存中,存储也不应该成为问题。
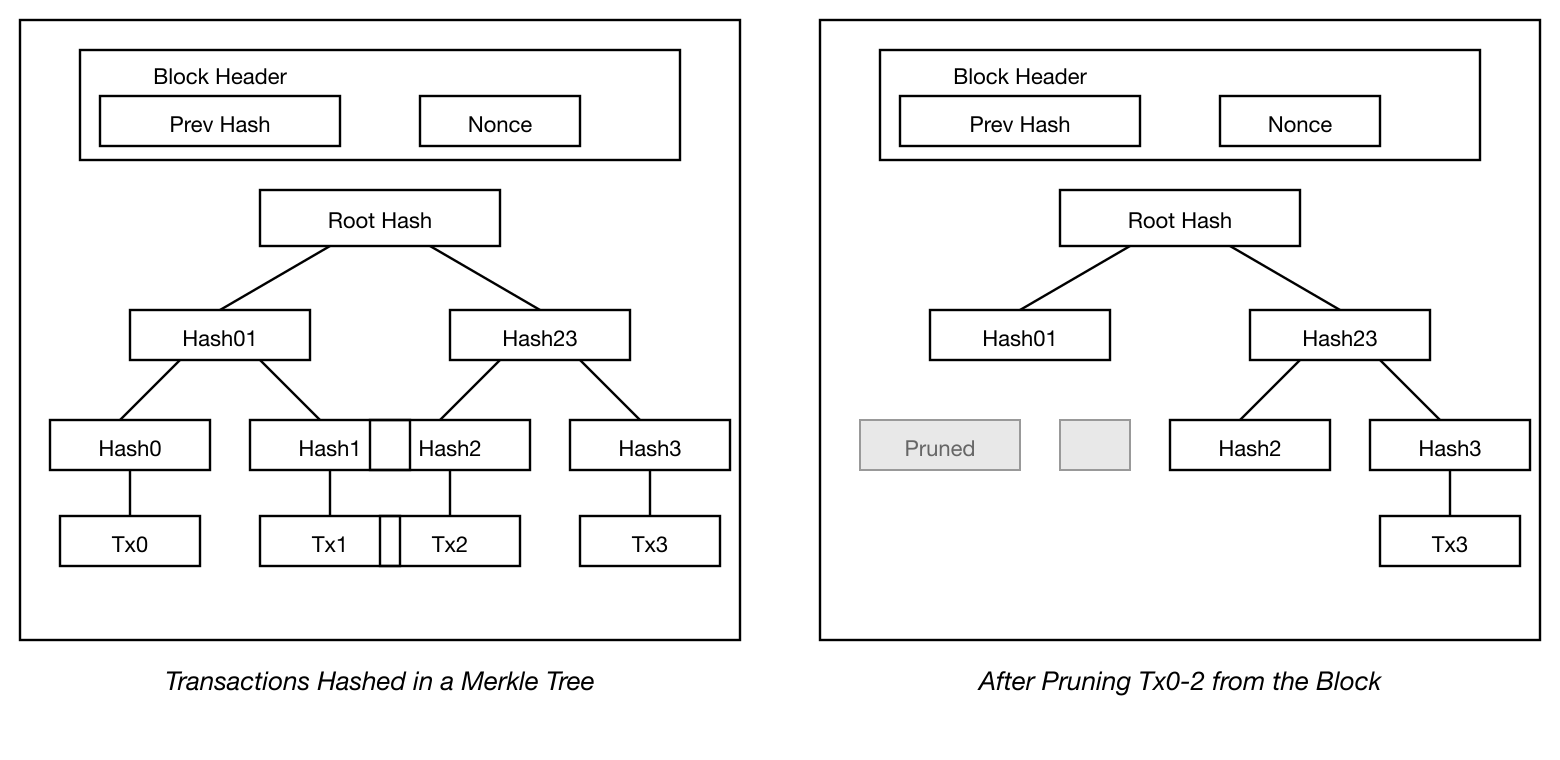
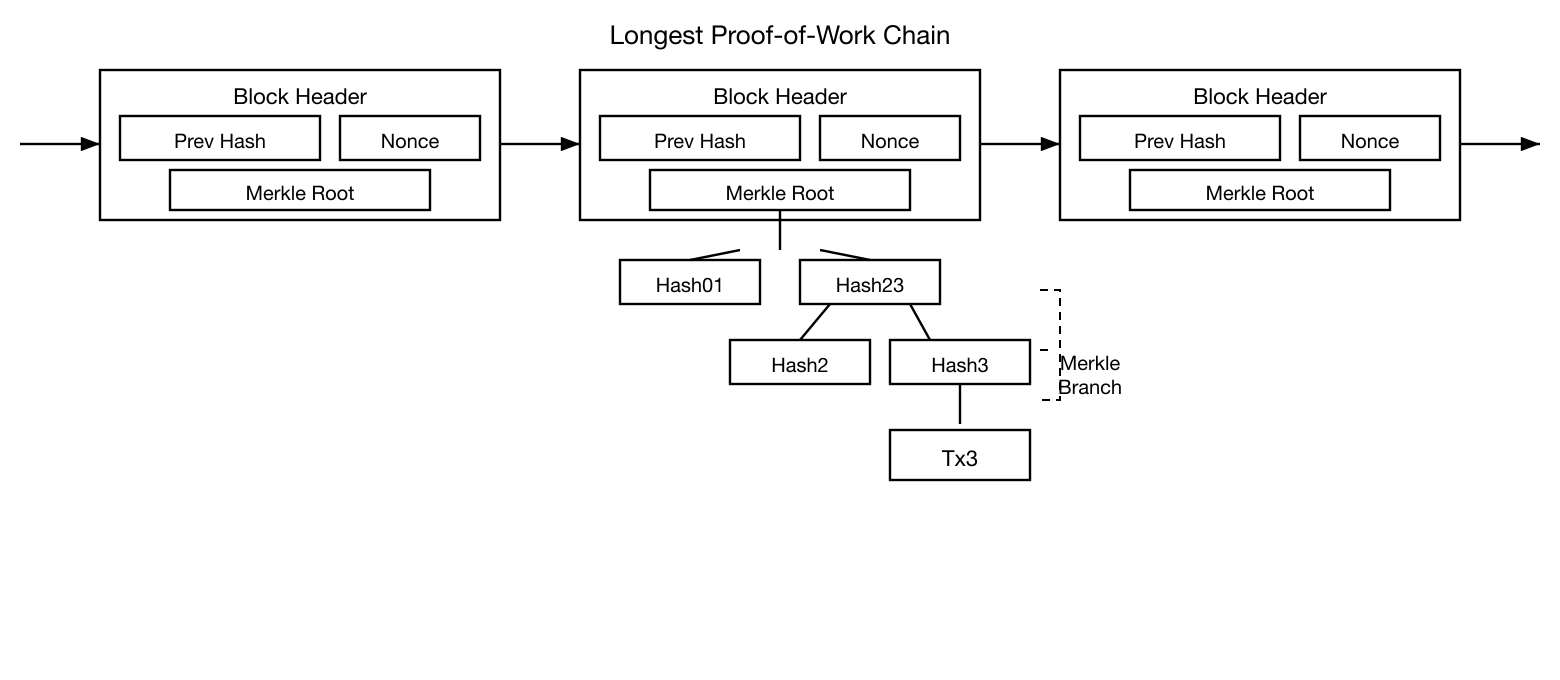
Simplified Payment Verification
전체 네트워크 노드를 운영하지 않고도 지불을 검증하는 것이 가능하다. 사용자는 가장 긴 proof-of-work 체인의 블록 헤더 사본만 유지하면 되며, 이는 가장 긴 체인을 확보했다고 확신할 때까지 네트워크 노드에 질의하여 얻을 수 있고, 거래를 타임스탬프된 블록에 연결하는 Merkle 분기를 확보하면 된다. 거래를 직접 확인할 수는 없지만, 체인의 한 위치에 연결함으로써 네트워크 노드가 이를 수락했음을 알 수 있고, 그 이후에 추가된 블록들은 네트워크가 이를 수락했음을 추가로 확인해 준다.
이와 같이, 정직한 노드들이 네트워크를 통제하는 한 검증은 신뢰할 수 있지만, 네트워크가 공격자에 의해 압도되면 더 취약해진다. 네트워크 노드가 거래를 스스로 검증할 수 있는 반면, 간소화된 방법은 공격자가 네트워크를 계속 압도할 수 있는 한 공격자의 조작된 거래에 속을 수 있다. 이에 대한 한 가지 보호 전략은 네트워크 노드가 유효하지 않은 블록을 감지했을 때 경고를 수락하여, 사용자의 소프트웨어가 전체 블록과 경고된 거래를 다운로드하여 불일치를 확인하도록 하는 것이다. 빈번한 지불을 수신하는 사업체는 보다 독립적인 보안과 빠른 검증을 위해 자체 노드를 운영하기를 원할 것이다.
Simplified Payment Verification
在不运行完整网络节点的情况下验证支付是可能的。用户只需要保留一份最长 proof-of-work 链的区块头副本,他可以通过查询网络节点直到确信自己拥有最长的链来获取它,并获取将交易链接到其被打上时间戳的区块的 Merkle 分支。他无法自己检查交易,但通过将其链接到链中的某个位置,他可以看到网络节点已经接受了它,而在其后添加的区块进一步确认了网络已经接受了它。
因此,只要诚实节点控制着网络,验证就是可靠的,但如果网络被攻击者制服则更加脆弱。虽然网络节点可以自己验证交易,但只要攻击者能够继续制服网络,简化方法就可能被攻击者伪造的交易所欺骗。一种防御策略是接受来自网络节点的警报,当它们检测到无效区块时,提示用户的软件下载完整区块和被警报的交易以确认不一致性。频繁接收支付的企业可能仍然希望运行自己的节点以获得更独立的安全性和更快的验证。
Combining and Splitting Value
화폐를 개별적으로 다루는 것이 가능하겠지만, 이체에서 매 센트마다 별도의 거래를 만드는 것은 다루기 어려울 것이다. 가치의 분할과 결합을 허용하기 위해, 거래는 다수의 입력과 출력을 포함한다. 일반적으로 더 큰 이전 거래로부터의 단일 입력 또는 더 작은 금액을 결합하는 다수의 입력이 있으며, 최대 두 개의 출력이 있다: 하나는 지불을 위한 것이고, 하나는 잔돈이 있는 경우 발신자에게 돌려주는 것이다.
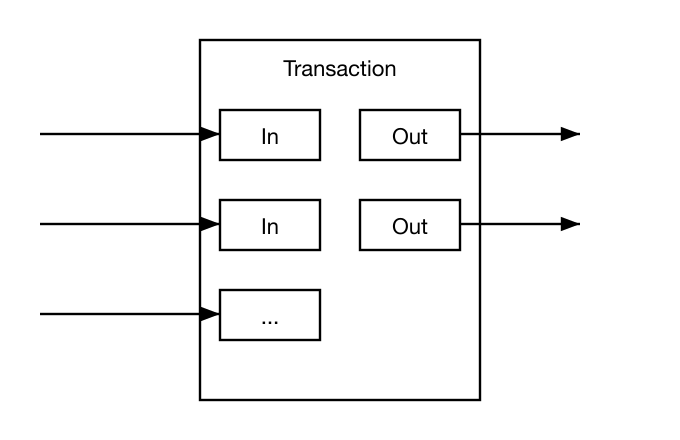
하나의 거래가 여러 거래에 의존하고, 그 거래들이 다시 더 많은 거래에 의존하는 팬아웃(fan-out)은 여기서 문제가 되지 않음에 유의해야 한다. 거래 이력의 완전한 독립 사본을 추출할 필요는 결코 없다.
Privacy
전통적인 은행 모델은 관련 당사자와 신뢰할 수 있는 제3자에게만 정보 접근을 제한함으로써 일정 수준의 개인정보 보호를 달성한다. 모든 거래를 공개적으로 발표해야 하는 필요성은 이 방법을 배제하지만, 정보의 흐름을 다른 곳에서 끊음으로써 개인정보 보호는 여전히 유지될 수 있다: 공개 키를 익명으로 유지하는 것이다. 대중은 누군가가 다른 누군가에게 금액을 보내고 있음을 볼 수 있지만, 거래를 누구에게도 연결하는 정보가 없다. 이는 증권 거래소가 공개하는 정보 수준과 유사하며, 개별 거래의 시간과 규모, 즉 "시세 테이프"는 공개되지만 당사자가 누구인지는 알리지 않는다.
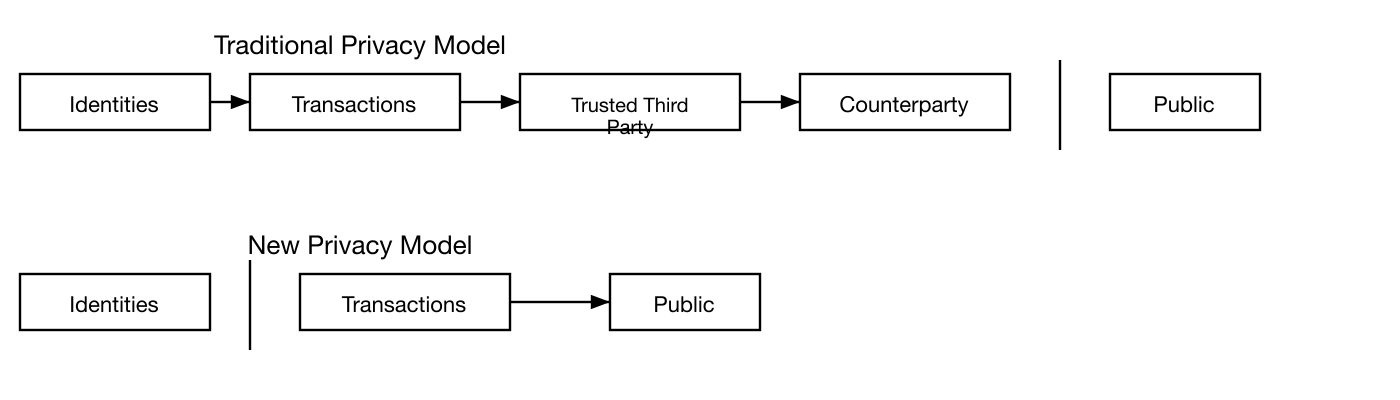
추가적인 방화벽으로, 각 거래마다 새로운 키 쌍을 사용하여 공통 소유자에게 연결되는 것을 방지해야 한다. 다중 입력 거래에서는 일부 연결이 여전히 불가피한데, 이는 그 입력들이 동일한 소유자의 것이었음을 필연적으로 드러내기 때문이다. 위험은 키의 소유자가 밝혀지면 연결을 통해 동일한 소유자에게 속한 다른 거래들이 드러날 수 있다는 것이다.
Privacy
传统的银行模型通过限制相关方和可信赖第三方对信息的访问来实现一定程度的隐私。公开宣布所有交易的必要性排除了这种方法,但隐私仍然可以通过在另一个地方打断信息流来维持:保持公钥匿名。公众可以看到某人正在向其他人发送一笔金额,但没有将交易与任何人关联的信息。这类似于证券交易所发布的信息级别,个别交易的时间和规模,即"行情",是公开的,但不会透露当事方是谁。
作为额外的防火墙,每笔交易应使用一对新的密钥,以防止它们被关联到一个共同的所有者。对于多输入交易,某些关联仍然是不可避免的,因为它们必然揭示其输入属于同一所有者。风险在于,如果密钥的所有者被揭露,关联可能会揭示属于同一所有者的其他交易。
Calculations
우리는 공격자가 정직한 체인보다 더 빠르게 대안 체인을 생성하려고 시도하는 시나리오를 고려한다. 이것이 달성되더라도, 무에서 가치를 만들거나 공격자에게 속하지 않은 돈을 빼앗는 것과 같은 임의적인 변경에 시스템을 개방하지는 않는다. 노드들은 유효하지 않은 거래를 지불로 수락하지 않을 것이며, 정직한 노드들은 그러한 거래를 포함하는 블록을 절대 수락하지 않을 것이다. 공격자는 오직 자신의 거래 중 하나를 변경하여 최근에 지출한 돈을 되돌리려고 시도할 수 있을 뿐이다.
정직한 체인과 공격자 체인 간의 경쟁은 이항 랜덤 워크(Binomial Random Walk)로 특성화할 수 있다. 성공 사건은 정직한 체인이 한 블록 연장되어 리드를 +1만큼 증가시키는 것이고, 실패 사건은 공격자의 체인이 한 블록 연장되어 격차를 -1만큼 줄이는 것이다.
주어진 격차에서 공격자가 따라잡을 확률은 도박사의 파산 문제(Gambler's Ruin problem)에 비유된다. 무한한 신용을 가진 도박사가 적자에서 시작하여 손익분기점에 도달하기 위해 잠재적으로 무한한 횟수의 시도를 한다고 가정하자. 그가 손익분기점에 도달하는 확률, 또는 공격자가 정직한 체인을 따라잡는 확률은 다음과 같이 계산할 수 있다[^8]:
p = probability an honest node finds the next block
q = probability the attacker finds the next block
q = probability the attacker will ever catch up from z blocks behind
``````
\[
qz =
\begin{cases}
1 & \text{if } p \leq q \\
\left(\frac{q}{p}\right) z & \text{if } p > q
\end{cases}
\]
p q라는 가정하에, 공격자가 따라잡아야 하는 블록 수가 증가함에 따라 확률은 지수적으로 감소한다. 불리한 상황에서, 초반에 운 좋게 앞서 나가지 못하면, 뒤처질수록 그의 가능성은 극히 작아진다.
이제 새로운 거래의 수신자가 발신자가 거래를 변경할 수 없다고 충분히 확신하기 전에 얼마나 기다려야 하는지 고려한다. 발신자는 수신자에게 자신이 지불했다고 한동안 믿게 만든 후, 일정 시간이 지난 후 자신에게 되돌려 지불하도록 전환하려는 공격자라고 가정한다. 그런 일이 발생하면 수신자에게 경고가 가지만, 발신자는 그때쯤이면 너무 늦기를 바란다.
수신자는 새로운 키 쌍을 생성하고 서명 직전에 발신자에게 공개 키를 제공한다. 이는 발신자가 충분히 앞서 나갈 만큼 운이 좋을 때까지 블록 체인을 미리 연속적으로 작업하여 준비한 후 그 시점에 거래를 실행하는 것을 방지한다. 거래가 전송되면, 부정직한 발신자는 자신의 거래의 대안 버전을 포함하는 병렬 체인을 비밀리에 작업하기 시작한다.
수신자는 거래가 블록에 추가되고 z개의 블록이 그 뒤에 연결될 때까지 기다린다. 공격자가 이룬 정확한 진행 정도를 알 수 없지만, 정직한 블록이 블록당 평균 예상 시간이 걸렸다고 가정하면, 공격자의 잠재적 진행은 기대값이 다음과 같은 포아송 분포가 될 것이다:
\[
\lambda = z\frac{q}{p}
\]
공격자가 지금이라도 따라잡을 수 있는 확률을 구하기 위해, 그가 이룰 수 있었던 각 진행 정도에 대한 포아송 밀도에 그 지점에서 따라잡을 수 있는 확률을 곱한다:
\[
\sum_{k=0}^{\infty} \frac{\lambda^k e^{-\lambda}}{k!} \cdot \left\{
\begin{array}{cl}
\left(\frac{q}{p}\right)^{(z-k)} & \text{if } k \leq z \\
1 & \text{if } k > z
\end{array}
\right.
\]
분포의 무한 꼬리를 합산하는 것을 피하기 위해 재배열하면...
\[
1 - \sum_{k=0}^{z} \frac{\lambda^k e^{-\lambda}}{k!} \left(1-\left(\frac{q}{p}\right)^{(z-k)}\right)
\]
C 코드로 변환하면...
```c
#include math.h
double AttackerSuccessProbability(double q, int z)
{
double p = 1.0 - q;
double lambda = z * (q / p);
double sum = 1.0;
int i, k;
for (k = 0; k = z; k++)
{
double poisson = exp(-lambda);
for (i = 1; i = k; i++)
poisson *= lambda / i;
sum -= poisson * (1 - pow(q / p, z - k));
}
return sum;
}
몇 가지 결과를 실행하면, z에 따라 확률이 지수적으로 감소하는 것을 볼 수 있다.
q=0.1
z=0 P=1.0000000
z=1 P=0.2045873
z=2 P=0.0509779
z=3 P=0.0131722
z=4 P=0.0034552
z=5 P=0.0009137
z=6 P=0.0002428
z=7 P=0.0000647
z=8 P=0.0000173
z=9 P=0.0000046
z=10 P=0.0000012
q=0.3
z=0 P=1.0000000
z=5 P=0.1773523
z=10 P=0.0416605
z=15 P=0.0101008
z=20 P=0.0024804
z=25 P=0.0006132
z=30 P=0.0001522
z=35 P=0.0000379
z=40 P=0.0000095
z=45 P=0.0000024
z=50 P=0.0000006
P가 0.1% 미만인 경우를 풀면...
P 0.001
q=0.10 z=5
q=0.15 z=8
q=0.20 z=11
q=0.25 z=15
q=0.30 z=24
q=0.35 z=41
q=0.40 z=89
q=0.45 z=340
Calculations
我们考虑一个攻击者试图比诚实链更快地生成替代链的场景。即使这一目标达成,也不会使系统面临任意更改的风险,例如凭空创造价值或夺取从不属于攻击者的资金。节点不会接受无效交易作为支付,诚实节点永远不会接受包含无效交易的区块。攻击者只能尝试更改自己的一笔交易,以收回他最近花费的资金。
诚实链与攻击者链之间的竞赛可以被描述为一个二项随机游走。成功事件是诚实链被延长一个区块,使其领先优势增加 +1,失败事件是攻击者的链被延长一个区块,使差距缩小 -1。
攻击者从给定落后距离追上的概率类似于赌徒破产问题。假设一个拥有无限信用的赌徒从亏损开始,进行潜在的无限次尝试以达到盈亏平衡。我们可以计算他最终达到盈亏平衡的概率,即攻击者追上诚实链的概率,如下 [^8]:
p = probability an honest node finds the next block
q = probability the attacker finds the next block
q = probability the attacker will ever catch up from z blocks behind
``````
\[
qz =
\begin{cases}
1 & \text{if } p \leq q \\
\left(\frac{q}{p}\right) z & \text{if } p > q
\end{cases}
\]
假设 p q,概率随着攻击者需要追赶的区块数量的增加而呈指数下降。如果他没有在早期幸运地向前冲刺,随着他进一步落后,他的机会变得微乎其微。
我们现在考虑新交易的接收者需要等待多长时间才能充分确定发送者无法更改交易。我们假设发送者是一个攻击者,他想让接收者相信他已经付款了一段时间,然后在一段时间后将其改为支付给自己。接收者在那时会收到警报,但发送者希望那时已经太晚了。
接收者生成一对新密钥,并在签名前不久将公钥提供给发送者。这防止了发送者通过持续在其上工作来提前准备一条区块链,直到他足够幸运地取得足够的领先,然后在那个时刻执行交易。一旦交易发送,不诚实的发送者开始秘密地在一条包含其交易替代版本的并行链上工作。
接收者等待交易被添加到一个区块中,并且在其后链接了 z 个区块。他不知道攻击者已经取得的确切进展,但假设诚实区块按照每个区块的平均预期时间产出,攻击者的潜在进展将是一个期望值为以下值的泊松分布:
\[
\lambda = z\frac{q}{p}
\]
为了获得攻击者现在仍然能够追上的概率,我们将他可能取得的每个进展量的泊松密度乘以他从该点追上的概率:
\[
\sum_{k=0}^{\infty} \frac{\lambda^k e^{-\lambda}}{k!} \cdot \left\{
\begin{array}{cl}
\left(\frac{q}{p}\right)^{(z-k)} & \text{if } k \leq z \\
1 & \text{if } k > z
\end{array}
\right.
\]
重新整理以避免对分布的无穷尾部求和......
\[
1 - \sum_{k=0}^{z} \frac{\lambda^k e^{-\lambda}}{k!} \left(1-\left(\frac{q}{p}\right)^{(z-k)}\right)
\]
转换为 C 代码......
```c
#include math.h
double AttackerSuccessProbability(double q, int z)
{
double p = 1.0 - q;
double lambda = z * (q / p);
double sum = 1.0;
int i, k;
for (k = 0; k = z; k++)
{
double poisson = exp(-lambda);
for (i = 1; i = k; i++)
poisson *= lambda / i;
sum -= poisson * (1 - pow(q / p, z - k));
}
return sum;
}
运行一些结果,我们可以看到概率随 z 呈指数下降。
q=0.1
z=0 P=1.0000000
z=1 P=0.2045873
z=2 P=0.0509779
z=3 P=0.0131722
z=4 P=0.0034552
z=5 P=0.0009137
z=6 P=0.0002428
z=7 P=0.0000647
z=8 P=0.0000173
z=9 P=0.0000046
z=10 P=0.0000012
q=0.3
z=0 P=1.0000000
z=5 P=0.1773523
z=10 P=0.0416605
z=15 P=0.0101008
z=20 P=0.0024804
z=25 P=0.0006132
z=30 P=0.0001522
z=35 P=0.0000379
z=40 P=0.0000095
z=45 P=0.0000024
z=50 P=0.0000006
求解 P 小于 0.1%......
P 0.001
q=0.10 z=5
q=0.15 z=8
q=0.20 z=11
q=0.25 z=15
q=0.30 z=24
q=0.35 z=41
q=0.40 z=89
q=0.45 z=340
Conclusion
우리는 신뢰에 의존하지 않는 전자 거래 시스템을 제안했다. 전자 서명으로 만들어진 화폐의 일반적인 프레임워크에서 출발했는데, 이는 소유권의 강력한 통제를 제공하지만 이중 지불을 방지할 방법 없이는 불완전하다. 이를 해결하기 위해, 거래의 공개 이력을 기록하는 proof-of-work를 사용하는 peer-to-peer 네트워크를 제안했으며, 정직한 노드가 CPU 연산 능력의 과반수를 통제하는 한 공격자가 변경하는 것이 계산적으로 빠르게 실질적으로 불가능해진다. 네트워크는 비구조적 단순성에서 강건하다. 노드들은 거의 조율 없이 모두 동시에 작업한다. 메시지가 특정 장소로 라우팅되지 않고 최선 노력(best effort) 기반으로만 전달되면 되므로, 노드를 식별할 필요가 없다. 노드들은 자유롭게 네트워크를 떠났다가 다시 참여할 수 있으며, 부재 중에 일어난 일의 증거로서 proof-of-work 체인을 수용한다. 그들은 CPU 연산 능력으로 투표하며, 유효한 블록을 연장하는 작업을 통해 수락을 표현하고, 유효하지 않은 블록에 대한 작업을 거부함으로써 이를 거부한다. 필요한 규칙과 인센티브는 이 합의 메커니즘으로 시행될 수 있다.
Conclusion
我们提出了一种不依赖信任的电子交易系统。我们从由数字签名构成的货币的通常框架开始,这提供了对所有权的强有力控制,但如果没有防止双重支付的方法则是不完整的。为了解决这个问题,我们提出了一种使用 proof-of-work 的点对点网络来记录交易的公共历史,如果诚实节点控制了大多数 CPU 算力,对攻击者来说更改记录在计算上很快就变得不可行。该网络在其非结构化的简单性中是健壮的。节点同时工作,几乎不需要协调。它们不需要被识别,因为消息不会被路由到任何特定的地方,只需要以尽最大努力的方式传递。节点可以随时离开和重新加入网络,接受 proof-of-work 链作为其离开期间所发生事件的证明。它们用自己的 CPU 算力投票,通过在有效区块上扩展来表示接受,通过拒绝在无效区块上工作来表示拒绝。任何需要的规则和激励都可以通过这种共识机制来执行。
References
-
H. Massias, X.S. Avila, and J.-J. Quisquater, "Design of a secure timestamping service with minimal trust requirements," In 20th Symposium on Information Theory in the Benelux, May 1999.
-
S. Haber, W.S. Stornetta, "How to time-stamp a digital document," In Journal of Cryptology, vol 3, no 2, pages 99-111, 1991.
-
D. Bayer, S. Haber, W.S. Stornetta, "Improving the efficiency and reliability of digital time-stamping," In Sequences II: Methods in Communication, Security and Computer Science, pages 329-334, 1993.
-
S. Haber, W.S. Stornetta, "Secure names for bit-strings," In Proceedings of the 4th ACM Conference on Computer and Communications Security, pages 28-35, April 1997.
-
A. Back, "Hashcash - a denial of service counter-measure," http://www.hashcash.org/papers/hashcash.pdf, 2002.
-
R.C. Merkle, "Protocols for public key cryptosystems," In Proc. 1980 Symposium on Security and Privacy, IEEE Computer Society, pages 122-133, April 1980.
-
W. Feller, "An introduction to probability theory and its applications," 1957.
References
-
H. Massias, X.S. Avila, and J.-J. Quisquater, "Design of a secure timestamping service with minimal trust requirements," In 20th Symposium on Information Theory in the Benelux, May 1999.
-
S. Haber, W.S. Stornetta, "How to time-stamp a digital document," In Journal of Cryptology, vol 3, no 2, pages 99-111, 1991.
-
D. Bayer, S. Haber, W.S. Stornetta, "Improving the efficiency and reliability of digital time-stamping," In Sequences II: Methods in Communication, Security and Computer Science, pages 329-334, 1993.
-
S. Haber, W.S. Stornetta, "Secure names for bit-strings," In Proceedings of the 4th ACM Conference on Computer and Communications Security, pages 28-35, April 1997.
-
A. Back, "Hashcash - a denial of service counter-measure," http://www.hashcash.org/papers/hashcash.pdf, 2002.
-
R.C. Merkle, "Protocols for public key cryptosystems," In Proc. 1980 Symposium on Security and Privacy, IEEE Computer Society, pages 122-133, April 1980.
-
W. Feller, "An introduction to probability theory and its applications," 1957.




