
Stellar 共识协议
초록
국제 결제는 느리고 비용이 많이 듭니다. 부분적으로는 이기종을 통한 멀티홉 결제 라우팅 때문입니다. 은행 시스템. Stellar는 새로운 글로벌 결제 네트워크입니다. 어디서나 디지털 화폐를 직접 전송할 수 있는 몇 초 만에 세계. 핵심 혁신은 안전한 거래입니다 새로운 메커니즘을 사용하여 신뢰할 수 없는 중개자를 통한 메커니즘 SCP라고 불리는 비잔틴 합의 프로토콜. SCP를 사용하면 각각 기관은 남아 있을 다른 기관을 지정합니다. 동의하다; 글로벌 상호 연결을 통해 금융 시스템, 전체 네트워크는 원자에 동의합니다. 중개 자산 발행자의 지급 능력이나 환율 위험 없이 임의의 기관에 걸친 거래 또는 시장 조성자. 우리는 SCP의 모델, 프로토콜 및 공식적인 검증; Stellar 결제 네트워크를 설명하세요. 마지막으로 벤치마크를 통해 경험적으로 Stellar을 평가합니다. 수년간의 생산 사용 경험. CCS 개념 • 보안 및 개인정보 보호 →분산 시스템 보안; • 전산시스템 구성 → 피어 투 피어 아키텍처 • 정보시스템 → 전자 자금 이체. 키워드 blockchain, BFT, 정족수, 지불 ACM 참조 형식: 마르타 로카바, 줄리아노 로사, 데이비드 마지에르, 그레이던 호어, 니콜라스 배리, 엘리 가프니, 조나단 조브, 라파우 말리노프스키, 제드 맥칼렙. 2019. Stellar를 통한 빠르고 안전한 글로벌 결제. SOSP에서는 ’19: 운영 체제 원칙에 관한 심포지엄, 10월 27~30일 2019, 헌츠빌, 온타리오, 캐나다. ACM, 뉴욕, 뉴욕, 미국, 17페이지. https://doi.org/10.1145/3341301.3359636
摘要
国际支付缓慢且昂贵,部分原因是通过异构的多跳支付路由 银行系统。 Stellar 是一个新的全球支付网络 可以直接在世界任何地方转移数字货币 世界在几秒钟内。关键创新是安全交易 跨不受信任的中介机构的机制,使用一种新的 拜占庭协议称为 SCP。通过 SCP,每个 机构指定要留在的其他机构 同意;通过全球互联 金融系统,然后整个网络就原子性达成一致 跨越任意机构的交易,没有中间资产发行人的偿付能力或汇率风险 或做市商。我们介绍 SCP 的模型、协议和 形式验证;描述 Stellar 支付网络; 最后通过基准对 Stellar 进行实证评估 以及我们多年的生产使用经验。 CCS 概念 • 安全和隐私→分布式 系统安全; • 计算机系统组织 → 点对点架构; • 信息系统 → 电子资金转账。 关键词 blockchain、BFT、法定人数、付款 ACM参考格式: 玛塔·洛哈瓦、朱利亚诺·洛萨、大卫·马齐埃、格雷登·霍尔、 尼古拉斯·巴里、伊莱·加夫尼、乔纳森·乔夫、拉斐尔·马利诺夫斯基、杰德·麦卡勒布。 2019 年。使用 Stellar 进行快速、安全的全球支付。在SOSP中 '19:操作系统原理研讨会,10 月 27 日至 30 日, 2019 年,加拿大安大略省亨茨维尔。 ACM,美国纽约州纽约市,17 页。 https://doi.org/10.1145/3341301.3359636
소개
국제 결제는 느리고 비용이 많이 드는 것으로 악명 높습니다 [32]. 미국에서 다음 국가로 0.50달러를 보내는 것은 비실용적입니다. *갈로이스 주식회사 †UCLA 본 저작물의 전부 또는 일부를 디지털 또는 하드 카피로 만들 수 있는 권한 개인 또는 교실 사용은 사본이 아닌 한 무료로 허용됩니다. 영리 또는 상업적 이익을 위해 제작 또는 배포되었으며 그 사본에는 다음과 같은 내용이 포함됩니다. 이 통지문과 첫 페이지에 전체 인용문이 나와 있습니다. 구성 요소에 대한 저작권 ACM이 아닌 타인이 소유한 이 저작물은 존중되어야 합니다. 추상화 신용이 허용됩니다. 다른 방식으로 복사하거나 다시 게시하거나 서버에 게시하거나 목록으로 재배포하려면 사전 특정 허가 및/또는 수수료가 필요합니다. 요청 [email protected]의 권한입니다. SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 © 2019 컴퓨팅 기계 협회. ACM ISBN 978-1-4503-6873-5/19/10...$15.00 https://doi.org/10.1145/3341301.3359636 멕시코, 두 이웃 국가. 최종 사용자는 거의 9달러를 지불합니다. 평균 전송 [32] 및 양자간 합의 국가의 중앙은행이 중개하는 것은 단지 감소할 수 있을 뿐이다. 기본 은행 비용은 항목당 $0.67 [2]입니다. 수수료 외에, 일반적으로 국제 결제 지연 시간이 계산됩니다. 며칠 안에 해외로 빨리 돈을 가져갈 수 없게 만듭니다. 긴급 상황. 은행 시스템이 없는 국가에서는 일하거나 모든 시민에게 서비스를 제공하지 않거나 수수료가 감당할 수 없는 곳에서는 사람들이 버스([38])로 지불금을 보내는 데 의지합니다. 보트 [19], 때로는 지금 Bitcoin [55]까지, 모두 위험, 지연 또는 불편이 발생합니다. 규정 준수 비용은 항상 존재하지만 경쟁 부족으로 인해 상당한 금액의 손실이 발생한다는 증거가 있습니다 [21], 이는 비효율적인 기술로 인해 더욱 악화됩니다. 사람들이 있는 곳 혁신할 수 있고 가격과 지연 시간이 줄어듭니다. 예를 들어, 2019년 2분기 은행 계좌에서 송금하는 데 드는 평균 비용은 6.99%, 모바일 머니 수치는 4.88% [13]에 불과했습니다. 혁신을 불러일으키는 개방형 글로벌 결제 네트워크 비은행 기업과의 경쟁이 위축될 수 있습니다. 규정 준수를 포함한 모든 계층의 비용 및 대기 시간 [83]. 이 백서는 blockchain 기반 결제인 Stellar을 제시합니다. 혁신을 촉진하고 국제 결제 경쟁. Stellar이 첫 번째입니다 다음 세 가지 목표를 모두 충족하는 시스템( 참신하지만 경험적으로 유효한 "인터넷 가설"): 1. 오픈멤버십 – 누구나 통화담보 발행 가능 사용자 간에 교환할 수 있는 디지털 token입니다. 2. 발급자 시행 최종성 – token의 발급자는 이를 방지할 수 있습니다. token의 거래가 취소되거나 실행 취소되지 않습니다. 3. 발행자 간 원자성 – 사용자는 원자적으로 교환할 수 있습니다. 여러 발행자로부터 token을 거래하세요. 처음 두 개를 달성하는 것은 쉽습니다. 어떤 회사라도 Paypal, Venmo, WeChat과 같은 제품을 일방적으로 제공할 수 있습니다. 지불 또는 Alipay를 통해 지불의 최종성을 보장합니다. 그들이 만든 가상 화폐. 불행하게도 이러한 통화 간에 원자적으로 거래하는 것은 불가능합니다. 사실, Paypal이 Venmo의 모회사를 인수했음에도 불구하고 2013년에는 여전히 최종 사용자가 Venmo를 보내는 것이 불가능합니다. PayPal 사용자에게 [78] 달러를 지급합니다. 최근에야 상인들이 단일 통합으로 두 가지를 모두 수용할 수도 있습니다. 목표 2와 3은 폐쇄형 시스템에서 달성할 수 있습니다. 특히 국내결제가 효율적인 국가가 많습니다. 일반적으로 보편적으로 신뢰할 수 있는 규제 기관이 감독하는 네트워크입니다. 단, 회원가입은 비공개로 제한됩니다. 공인 은행 집합과 네트워크는 다음으로 제한됩니다. 국가의 규제 당국에 도달합니다.SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 Lokhavaet al. 목표 1과 3은 채굴된 blockchain에서 달성되었습니다. 특히 Ethereum [3]의 ERC20 tokens 형식입니다. 이 blockchains의 핵심 아이디어는 사람들이 정착에 대해 보상할 수 있는 새로운 암호화폐를 만드는 것입니다. 되돌리기 어려운 거래. 불행하게도 이는 token 발행자가 거래 최종성을 제어하지 않는다는 것을 의미합니다. 소프트웨어인 경우 오류로 인해 거래 내역이 재구성됩니다 [26, 73], 또는 사람들을 속여 얻은 전리품이 그 비용을 초과하는 경우 기록 재구성 [74, 97], 발행자는 tokens에 대해 책임을 질 수 있습니다. 그들은 이미 실제 돈으로 교환했습니다. Stellar blockchain에는 두 가지 구별되는 속성이 있습니다. 첫째, 기본적으로 tokens 간의 효율적인 시장을 지원합니다. 다른 발행자로부터. 특히 누구나 token을 발행할 수 있습니다. blockchain은 token 쌍 간의 거래를 위한 내장 주문서를 제공하며 사용자는 경로 지불을 발행할 수 있습니다. 여러 통화쌍에 걸쳐 원자적으로 거래되는 반면 종단간 한계 가격을 보장합니다. 둘째, Stellar은 새로운 비잔틴 계약을 도입합니다. 프로토콜, SCP(Stellar 합의 프로토콜)를 통해 token 발급자는 시행할 특정 validator 서버를 지정합니다. 거래 최종성. 발행자의 validator(및 기본 디지털 서명 및 암호화 hashes는 안전하게 유지됩니다.) 발행자는 어떤 거래가 발생했는지 정확히 알고 위험을 방지합니다. blockchain 기록 재구성으로 인한 손실. SCP의 핵심 아이디어는 대부분의 자산 발행자가 다음으로부터 이익을 얻는다는 것입니다. 유동적인 시장이며 원자 거래를 촉진하기를 원합니다. 다른 자산과 함께. 따라서 validator 관리자는 해당 서버는 정확한 내용에 대해 다른 validator과 동의합니다. 모든 자산에 대한 모든 거래 내역. validator v1은 다음과 같습니다. v2에 동의하도록 구성하거나 v2에 동의하도록 구성할 수 있습니다. v1을 사용하거나 둘 다 서로 동의하도록 구성할 수 있습니다. 모든 경우에 어느 쪽도 거래 내역을 약속하지 않습니다. 다른 사람이 다른 역사를 맡을 수 없다는 것을 알고 있습니다. 전이성에 따라 v1이 v2에 동의하지 않고 v2가 v3에 동의하지 않으면(또는 그 반대) v1은 v2에 동의하지 않을 수 있습니다. v3, v3이 v1이 들어본 자산을 나타내는지 여부 의. 이러한 합의 관계가 성립한다는 가설 하에 전체 네트워크를 전이적으로 연결, SCP 보장 글로벌 협약, 이를 글로벌 비잔틴 협약으로 만듭니다. 공개 멤버십을 갖춘 프로토콜. 우리는 이 새로운 연결성 가정을 인터넷 가설이라고 부르며, 모두가 이해하는 "인터넷"을 모두 보유하고 있습니다. 전이적으로 연결된 단일 최대 규모의 IP 네트워크를 의미함) 기존 국제 결제(홉별 결제) 비원자적이지만 전이적으로 연결된 글로벌 금융 기관 네트워크). Stellar은 2015년 9월부터 프로덕션에서 사용되었습니다. blockchain 길이를 관리 가능하게 유지하기 위해 시스템이 실행됩니다. 5초 간격의 SCP—blockchain 표준으로는 빠르지만, 비잔틴 계약의 일반적인 적용보다 훨씬 느립니다. 주요 용도는 결제였지만 Stellar은(는) 비화폐 대체 가능 token에 대한 매력이 입증되었습니다. 즉각적인 2차 시장에서 제공됩니다(섹션 7.1 참조). 다음 섹션에서는 관련 작업에 대해 설명합니다. 섹션 3은 다음과 같습니다. SCP. 섹션 4에서는 SCP의 공식 검증을 설명합니다. 섹션 5에서는 Stellar의 결제 계층에 대해 설명합니다. 섹션 6 관련 우리의 배포 경험과 교훈 중 일부. 섹션 7에서는 시스템을 평가합니다. 섹션 8이 마무리됩니다.
介绍
国际支付速度缓慢且成本高昂 [32] 是出了名的。 考虑一下从美国寄 0.50 美元到 *伽罗瓦公司 †加州大学洛杉矶分校 允许将本作品的全部或部分制作为数字或硬拷贝 个人或课堂使用可免费使用,前提是不提供副本 为了利润或商业利益而制作或分发,并且副本具有 本通知以及首页上的完整引文。组件的版权 必须尊重 ACM 以外的其他人所拥有的这项工作。抽象与 信用是允许的。以其他方式复制或重新发布、发布到服务器或 重新分发到列表,需要事先获得特定许可和/或付费。请求 来自[email protected] 的权限。 SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 © 2019 计算机协会。 ACM ISBN 978-1-4503-6873-5/19/10...15.00 美元 https://doi.org/10.1145/3341301.3359636 墨西哥,两个邻国。最终用户支付近 9 美元 平均此类转让 [32],以及双边协议 由各国央行斡旋只能减少 每个项目 [2] 的基础银行成本为 0.67 美元。除了费用之外, 国际支付的延迟一般都算在内 几天之内,就不可能在短时间内快速将钱转移到国外 紧急情况。在没有银行系统的国家 工作或不为所有公民提供服务,或者在费用无法忍受的情况下,人们求助于通过巴士 [38] 发送付款, 乘船[19],现在偶尔乘Bitcoin [55],所有这些 招致风险、延迟或不便。 虽然合规成本始终存在,但有证据表明,由于缺乏竞争而损失了大量成本[21], 低效的技术加剧了这种情况。凡人 可以创新,价格和延迟都会下降。例如,2019 年第二季度的银行账户汇款平均费用为 6.99%,而移动货币仅为4.88%[13]。 吸引创新的开放的全球支付网络 来自非银行实体的竞争可能会压低 所有层的成本和延迟,包括合规性 [83]。 本文提出了 Stellar,一种基于 blockchain 的支付方式 专门为促进创新而设计的网络 国际支付的竞争。 Stellar 是第一个 系统以满足以下所有三个目标(在 新颖但经验有效的“互联网假设”): 1. 开放会员制——任何人都可以发行货币支持 可以在用户之间交换的数字token。 2. 发行人强制的最终性 – token 的发行人可以阻止 token 中的交易被撤销或撤消。 3. 跨发行者原子性——用户可以原子地交换 并交易来自多个发行人的 token。 实现前两个目标很容易。任何公司都可以单方面提供Paypal、Venmo、微信等产品 支付宝或支付宝并确保付款的最终性 他们创造的虚拟货币。不幸的是,跨这些货币进行原子交易是不可能的。事实上, 尽管 Paypal 收购了 Venmo 的母公司 2013年,最终用户仍然无法发送Venmo 美元给 Paypal 用户 [78]。直到最近商家才可以 甚至通过一次集成即可接受两者。 目标2和3可以在封闭系统中实现。特别是一些国家拥有高效的国内支付 网络,通常由普遍信任的监管机构监管。然而,会员资格仅限于封闭的 一组特许银行和网络仅限于 国家监管机构的管辖范围。SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 洛哈瓦等人。 目标 1 和 3 已在 blockchain 矿区实现, 最值得注意的是 Ethereum [3] 上的 ERC20 token 形式。 这些 blockchain 的关键思想是创建一种新的加密货币,用来奖励人们定居下来 交易很难恢复。不幸的是,这意味着 token 发行人无法控制交易的最终性。如果软件 错误导致交易历史记录被重新组织 [26, 73], 或当诈骗者的赃物超过其成本时 重组历史 [74, 97],发行人可能需要承担 tokens 他们已经兑换了现实世界的钱。 Stellar blockchain 有两个显着的属性。 首先,它本身支持 tokens 之间的有效市场 来自不同的发行人。具体来说,任何人都可以发出 token, blockchain 为任意一对 token 之间的交易提供内置订单簿,用户可以发出路径支付 跨多个货币对进行原子交易,同时 保证端到端限价。 二、Stellar引入新的拜占庭协议 协议,SCP(Stellar 共识协议),通过该协议 token 发行人指定特定的 validator 服务器来执行 交易最终性。只要没有人损害发行人的 validator(以及底层数字签名和 加密 hashes 保持安全),发行人确切地知道发生了哪些交易并避免了风险 blockchain 历史重组造成的损失。 SCP 的核心思想是大多数资产发行者受益于 流动市场并希望促进原子交易 与其他资产。因此,validator 管理员配置 他们的服务器与其他 validator 达成一致 所有资产的所有交易历史记录。 validator v1 可以是 配置为同意v2,或者可以配置v2同意 与 v1,或者两者可以配置为彼此一致; 在所有情况下,双方都不会提交交易历史记录,直到 它知道对方不能承诺不同的历史。 根据传递性,如果 v1 不能不同意 v2 并且 v2 不能不同意 v3(反之亦然),则 v1 不能不同意 v3,无论v3是否代表资产v1甚至听说过 的。假设这些协议关系 传递连接整个网络,SCP保证 全球协议,使其成为全球拜占庭协议 具有开放成员资格的协议。我们将这种新的连通性假设称为互联网假设,并注意到它 拥有“互联网”(每个人都理解为 指单个最大的可传递连接的 IP 网络) 以及传统的国际支付(逐跳 非原子的,但利用传递连接的全局 金融机构网络)。 Stellar 自 2015 年 9 月起已投入生产使用。 为了保持 blockchain 长度易于管理,系统运行 SCP 以 5 秒为间隔——按照 blockchain 标准快,但是 比拜占庭协议的典型应用慢得多。 尽管主要用途是支付,但 Stellar 也用于 事实证明对非货币可替代 token 具有吸引力,受益匪浅 来自直接二级市场(见第 7.1 节)。 下一节讨论相关工作。第 3 节介绍 SCP。第 4 节描述了我们对 SCP 的形式验证。第 5 节描述了 Stellar 的支付层。第 6 条涉及 我们的一些部署经验和教训。 第 7 节评估系统。第 8 节总结。
Stellar 합의 프로토콜
Stellar 합의 프로토콜(SCP)은 쿼럼 기반입니다. 공개 멤버십을 갖춘 비잔틴 계약 프로토콜. 쿼럼은 개별 노드의 결합된 로컬 구성 결정에서 나타납니다. 그러나 노드는 오직 자신이 속한 정원회, 그리고 그 이후에만 다른 모든 정원회 구성원의 로컬 구성을 학습합니다. 이 접근 방식의 한 가지 이점은 SCP가 본질적으로 어떤 노드가 존재하는지에 대한 이질적인 관점을 허용합니다. 따라서, 노드는 별도의 작업 없이 일방적으로 합류하고 나갈 수 있습니다. 멤버십을 조정하기 위한 "변경 보기" 프로토콜입니다. 3.1 연합 비잔틴 계약 전통적인 비잔틴 합의 문제는 다음과 같이 구성됩니다. N개 노드로 구성된 폐쇄형 시스템. 그 중 일부는 결함이 있으며 임의로 행동하십시오. 노드는 입력 값을 받고 교환합니다. 입력 중 출력 값을 결정하는 메시지입니다. 비잔틴 합의 프로토콜은 선의로 행동하는 두 노드가 서로 다른 결정과 고유한 결과를 출력하지 않을 때 안전합니다. 결정은 유효한 입력이었습니다(유효한 합의의 일부 정의에 대해).SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 Lokhavaet al. 사전에). 프로토콜은 다음을 보장할 때 활성화됩니다. 모든 정직한 노드는 결국 결정을 내립니다. 일반적으로 프로토콜은 일부 정수에 대해 N = 3f + 1이라고 가정합니다. f > 0이면 안전성과 어떤 형태의 활성도 보장됩니다. 최대 f 노드에 결함이 있는 한. 이들 중 어느 단계에서는 프로토콜, 노드는 제안된 값과 제안에 투표합니다. 투표 정족수라고 불리는 2f + 1 표를 받는 것은 다음과 같습니다. 결정. N = 3f + 1개 노드의 경우 두 쿼럼은 크기 2f + 1은 최소 f + 1개 노드에서 겹칩니다. 만약 이것들이 f개라도 겹치는 노드에 결함이 있는 경우 두 쿼럼은 최소한 결함이 없는 노드 하나를 사용하여 모순된 결정을 방지합니다. 그러나 이 접근 방식은 모든 노드가 동의하는 경우에만 작동합니다. 쿼럼을 구성하는 것은 SCP에서는 불가능합니다. 두 노드는 서로의 존재조차 알지 못할 수도 있습니다. SCP를 사용하면 각 노드 v가 일방적으로 노드 집합을 선언합니다. (a) v는 쿼럼 슬라이스라고 부릅니다. 슬라이스의 구성원이 시스템 상태에 동의하면 그들은 옳고, (b) v는 그 조각 중 적어도 하나가 에 관한 정보를 적시에 제공할 수 있을 것입니다. 시스템 상태. 우리는 결과 시스템을 다음과 같이 부릅니다. 노드와 그 조각, 연합 비잔틴 계약 (FBA) 시스템. 다음에 살펴보겠지만, 정족수 시스템이 등장합니다. 노드의 조각에서. 비공식적으로 FBA 노드의 슬라이스는 누구와 함께 있는지 표현합니다. 노드에는 동의가 필요합니다. 예를 들어, 노드는 각각 3개의 노드를 실행하는 4개의 특정 조직과의 계약이 필요할 수 있습니다. 에 가동 중지 시간을 수용하여 슬라이스를 모든 세트로 설정할 수 있습니다. 각 조직의 2개 노드로 구성됩니다. 이것이 "필요하다면 '합의' 관계는 임의의 두 노드를 전이적으로 관련시킵니다. 우리는 세계적인 합의를 얻었습니다. 그렇지 않으면 우리는 발산을 얻을 수 있습니다. 그러나 어느 쪽도 요구하지 않는 조직 사이에서만 가능합니다. 상대방과의 합의. 오늘의 토폴로지를 고려하면 금융 시스템에서 우리는 광범위한 수렴이 사람들이 부르는 단일 원장 기록을 계속 생성할 것이라고 가정합니다. 우리가 인터넷에 대해 말하는 것과 마찬가지로 "Stellar 네트워크"입니다. 쿼럼은 다음과 같이 조각에서 발생합니다. 모든 노드는 지정합니다 보내는 모든 메시지에서 쿼럼 조각이 삭제됩니다. S를 메시지 집합이 시작된 노드 집합입니다. 에이 노드는 메시지 집합이 쿼럼에 도달한 것으로 간주합니다. S의 모든 구성원이 S에 포함된 슬라이스를 가질 때 임계값입니다. 구성에 따르면, 그러한 집합 S는 만장일치로 다음을 만족합니다. 각 회원의 동의 요구 사항. 결함이 있는 피어는 무엇을 변경하기 위해 제작된 슬라이스를 광고할 수 있습니다. 선의로 행동하는 노드는 쿼럼을 고려합니다. 프로토콜 분석을 위해 FBA의 쿼럼을 비어 있지 않은 것으로 정의합니다. 적어도 하나의 쿼럼 슬라이스를 포함하는 노드 집합 S 결함이 없는 각 멤버. 이 추상화는 어떤 집합과 마찬가지로 건전합니다. 만장일치로 정족수를 대표한다고 주장하는 메시지 실제로 그렇습니다(결함 있는 노드의 메시지가 포함된 경우에도). S가 선의로 행동하는 노드만 포함하면 정확합니다. 에서 이 섹션에서는 노드의 슬라이스가 변경되지 않는다고 가정합니다. 그럼에도 불구하고 우리의 결과는 슬라이스 변경 사례로 이전됩니다. 슬라이스가 변경되는 시스템은 다음과 같이 안전하기 때문입니다. 노드의 슬라이스가 모든 항목으로 구성되는 고정 슬라이스 시스템 슬라이스 변경 사례에서 사용한 슬라이스(정리 참조) [68]의 13). 섹션 4에서 설명했듯이 활성 상태는 다음에 따라 달라집니다. 선량하게 행동하는 노드는 결국 신뢰할 수 없는 노드를 제거합니다. 그들의 조각에서. 노드마다 계약 요구 사항이 다르기 때문에 FBA에서는 안전에 대한 글로벌 정의를 배제합니다. 우리는 말한다 결함이 없는 노드 v1과 v2는 다음과 같은 경우 서로 얽혀 있습니다. v1의 쿼럼은 적어도 하나의 v2의 모든 쿼럼과 교차합니다. 결함이 없는 노드. FBA 프로토콜은 합의를 보장할 수 있습니다. 얽힌 노드 사이에서만; SCP가 그렇게 하기 때문에, 그것의 잘못이다 안전에 대한 내성이 최적입니다. 인터넷 가설, Stellar의 기본 디자인에는 사람들이 관심을 갖는 노드가 명시되어 있습니다. 대략 얽히게 됩니다. I 외부의 모든 노드에 결함이 있더라도 I의 모든 두 구성원이 서로 얽혀 있는 균일하게 결함이 없는 쿼럼인 경우 노드 집합 I는 손상되지 않습니다. 직관적으로, 그러면 나는 손상되지 않은 사람의 행동에 영향을 받지 않는 상태를 유지해야 합니다. 노드. SCP는 비차단 활성 [93]과 노드 자체는 필요하지 않지만 손상되지 않은 세트에 대한 안전성 어떤 세트가 손상되지 않았는지 알 수 있습니다(알지 못할 수도 있음). 게다가, 교차하는 두 개의 온전한 집합의 합집합은 다음과 같습니다. 온전한 세트. 따라서 손상되지 않은 세트는 다음의 파티션을 정의합니다. 각 파티션이 안전하고 활성화되어 있는 잘 동작하는 노드 (일부 조건 하에서)하지만 다른 파티션이 출력될 수 있습니다. 다양한 결정. 3.1.1 FBA의 안전 및 활성 고려 사항 제한된 예외([64])를 제외하고 대부분의 폐쇄형 비잔틴 합의 프로토콜은 균형점에 맞춰 조정됩니다. 안전성과 활성성은 동일한 내결함성을 갖습니다. FBA에서는 이는 장애에 관계없이 모든 것이 가능한 구성을 의미합니다. 얽힌 세트도 그대로 유지됩니다. FBA가 결정한다는 점을 고려하면 분산된 방식으로 쿼럼을 구성하는 경우 개별 슬라이스 선택이 이러한 균형으로 이어질 가능성은 거의 없습니다. 더욱이, 적어도 Stellar에서는 균형이 바람직하지 않습니다. 그 결과 안전 실패(즉, 이중 지출 디지털 화폐)는 활성 실패(즉, 지연)보다 훨씬 더 나쁩니다. 어쨌든 Stellar 전에 며칠이 걸린 지불). 사람 그러므로 큰 쿼럼 조각을 선택해야 하며 그렇게 해야 합니다. 그들의 노드는 손상되지 않은 것보다 서로 얽혀 있을 가능성이 더 높습니다. 저울을 더 기울이면 회복하기가 더 쉽습니다. 기존의 폐쇄형 시스템보다 FBA 시스템의 일반적인 활성 오류입니다. 폐쇄형 시스템에서는 모든 메시지가 다음과 같아야 합니다. 동일한 정원회 집합을 기준으로 해석됩니다. 따라서, 장애 복구를 위해 노드를 추가 및 제거하려면 다음이 필요합니다. 합의가 더 이상 활성화되지 않으면 재구성 이벤트에 대한 합의에 도달하기가 어렵습니다. 이에 반해 FBA의 경우 모든 노드는 언제든지 쿼럼 슬라이스를 일방적으로 조정할 수 있습니다. 시간. 시스템적으로 중요한 서비스의 중단에 대응하여 조직에서 노드 관리자는 슬라이스를 다음과 같이 조정할 수 있습니다. 문제를 해결하세요. 대응을 조정하는 것과 비슷합니다. BGP 재앙 63 물리적 네트워크 링크를 통한 라우팅).
Stellar을 통한 빠르고 안전한 글로벌 결제 SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 3.1.2 캐스케이드 정리 SCP는 기본 원형 모델 [42]의 템플릿을 따릅니다. 노드는 번호가 매겨진 일련의 투표를 통해 진행됩니다. 세 가지 작업 시도: (1) 이전 투표의 결정과 모순되지 않는 "안전한" 값을 식별합니다(종종 투표용지 준비), (2) 안전한 값에 동의하고, (3) 합의가 성공적이었음을 감지합니다. 그러나 FBA는 열려 있습니다. 멤버십은 몇 가지 일반적인 기술을 방해합니다. 기존의 폐쇄형 프로토콜을 FBA로 "포팅"하는 것은 불가능합니다. 단순히 쿼럼의 정의를 변경하여 모델을 만들 수 있습니다. 많은 프로토콜에서 사용되는 기술 중 하나는 회전입니다. 시간 초과 후 라운드 로빈 방식으로 리더 노드를 통과합니다. 폐쇄형 시스템에서는 라운드 로빈 리더 선택이 보장됩니다. 결국 독특하고 정직한 리더는 단일 가치에 대한 합의를 조정하게 됩니다. 아쉽게도 라운드 로빈 멤버십을 알 수 없는 FBA 시스템에서는 작업할 수 없습니다. FBA에서 실패하는 또 다른 일반적인 기술은 특정 쿼럼이 모든 노드를 설득할 수 있다고 가정하는 것입니다. 예를 들어, 모든 사람이 2f + 1 노드를 쿼럼으로 인식하면 2f + 1개의 서명이면 모든 노드에 대한 프로토콜 상태를 증명하는 데 충분합니다. 마찬가지로, 노드가 동일한 메시지의 쿼럼을 수신하는 경우 신뢰할 수 있는 브로드캐스트 [24]을 통해 노드는 결함이 없는 모든 노드도 쿼럼을 볼 것이라고 가정할 수 있습니다. 이와 대조적으로 FBA에서는 쿼럼은 쿼럼 외부의 노드에 아무런 의미가 없습니다. 마지막으로, 비연합 시스템은 종종 "역방향"을 사용합니다. 안전에 대한 추론: f + 1개 노드에 결함이 있는 경우 모든 안전 보증이 손실됩니다. 따라서 노드 v가 f + 1개 노드를 모두 듣는다면 어떤 사실 F를 진술하고, v는 적어도 하나가 F를 말하고 있다고 가정할 수 있습니다. 안전의 손실 없이 진실(따라서 F가 참)입니다. 그러한 안전은 쌍의 속성이기 때문에 FBA에서는 추론이 실패합니다. 따라서 일부 피어에 대한 안전성을 잃은 노드는 항상 나쁜 사실을 가정하여 더 많은 노드에 대한 안전을 잃습니다. 그러나 FBA는 활성에 대해 거꾸로 추론할 수 있습니다. v-차단 세트를 모든 노드와 교차하는 노드 세트로 정의합니다. v의 슬라이스. v-차단 세트 B가 만장일치로 결함이 있는 경우 B 노드 v 쿼럼을 거부하고 활성 상태를 저하할 수 있습니다. 따라서 만약 B가 만장일치로 사실 F를 진술하면, v는 F가 다음 중 하나라는 것을 알게 됩니다. true 또는 v가 손상되지 않았습니다. 그러나 v는 여전히 전체 내용을 확인해야 합니다. 얽힌 노드가 F와 모순되지 않는다는 것을 알기 위한 쿼럼 이는 SCP에서의 마지막 의사소통으로 이어지며 유사하게 필요하지 않은 다른 FBA 프로토콜 [47] 폐쇄형 멤버십 프로토콜. 그 결과 우리는 잠재적인 사실에 대한 세 가지 가능한 신뢰 수준: 불확정, 온전한 노드 사이에서 가정해도 안전함(우리는 이를 용어로 인정된 사실), 서로 얽혀 있는 것으로 가정해도 안전합니다. 노드(확인된 사실이라고 부르겠습니다). 노드 v는 B가 모든 슬라이스와 교차하는지 여부를 확인하여 집합 B가 vblocking인지 여부를 효율적으로 결정할 수 있습니다. 흥미롭게도 노드가 항상 성명을 발표한다면 전체 쿼럼이 성명을 수락하면 성명이 전체에 전파되는 계단식 프로세스가 시작됩니다. 온전한 세트. 우리는 이 전파의 기초가 되는 핵심 사실을 다음과 같이 부릅니다. 캐스케이드 정리는 다음과 같습니다. 만약 내가 온전한 집합, Q는 I의 임의 구성원의 쿼럼이고 S는 임의의 구성원입니다. Q의 상위 집합, S ⊇I 또는 멤버 v ∈I가 있음 v < S이고 I ∩S는 v-차단입니다. 직관적으로 이랬나? 그렇지 않은 경우 S의 보수에는 쿼럼이 포함됩니다. 이는 I와 교차하지만 Q와는 교차하지 않아 쿼럼 교차를 위반합니다. S = Q로 시작하여 S를 반복적으로 확장하면 차단하는 모든 노드를 포함하면 계단식 효과를 얻을 수 있습니다. 결국 S는 I를 모두 포함합니다. 3.2 프로토콜 설명 SCP는 합의에 도달하기 위한 일련의 시도로 구성된 부분 동기식 합의 프로토콜 [42]입니다. 투표용지. 투표용지는 지속 시간이 늘어나는 타임아웃을 사용합니다. 에이 투표 동기화 프로토콜은 노드가 계속 유지되도록 보장합니다. 투표용지가 나올 때까지 동일한 투표용지를 점점 더 오랜 기간 동안 사용함 효과적으로 동기식입니다. 종료가 보장되지 않습니다. 투표용지가 동기식일 때까지는 두 개의 동기식 투표용지가 있습니다. 선의로 행동하는 노드 슬라이스의 결함이 있는 구성원이 수행하는 작업 방해하지 않으면 SCP가 종료되기에 충분합니다. 투표 프로토콜은 각 투표 동안 취해지는 조치를 지정합니다. 투표. 투표는 준비 단계로 시작됩니다. 모순되지 않는 제안 가치를 결정하려고 노력하십시오. 이전 결정. 그런 다음 커밋 단계에서 노드는 다음을 시도합니다. 준비된 가치에 대한 결정을 내립니다. 투표는 연합 투표라는 합의 하위 프로토콜을 사용합니다.n 어떤 노드가 추상 진술에 투표하는지 결국 확인되거나 중단될 수 있습니다. 일부 진술은 모순되는 것으로 지정될 수 있으며 안전성은 연합 투표의 보장은 두 명의 구성원이 참여하지 않는다는 것입니다. 서로 얽힌 세트는 모순되는 진술을 확인합니다. 손상되지 않은 경우를 제외하고 명세서의 확인은 보장되지 않습니다. 구성원이 모두 같은 방식으로 투표하도록 설정합니다. 그러나 만약 온전한 집합의 구성원이 연합된 진술을 확인합니다. 투표는 온전한 세트의 모든 구성원이 결국 해당 진술을 확인하도록 보장합니다. 그러므로 되돌릴 수 없는 조치를 취하는 것은 확인 진술에 대한 응답으로 다음의 활성 상태를 유지합니다. 온전한 노드. 노드는 처음에 추천을 통해 얻은 가치를 제안합니다. 손상되지 않은 모든 구성원의 가능성을 높이는 프로토콜 동일한 가치를 제안하는 세트는 결국 수렴됩니다. (그러나 수렴이 완료되었는지 확인할 방법은 없습니다). 지명은 연합 투표와 리더 선택을 결합합니다. FBA에서는 라운드 로빈이 불가능하기 때문에 지명은 다음을 사용합니다. 확률론적 리더 선택 계획. 캐스케이드 정리는 투표에서 중요한 역할을 합니다. 동기화 및 차단된 상태를 방지하는 데 있어 더 이상 종료가 불가능합니다. 3.2.1 투표 SCP 노드는 일련의 번호가 매겨진 투표를 진행하며 연합 투표를 사용하여 다음 사항에 대한 진술에 동의합니다. 가치는 어느 투표에서 결정되거나 결정되지 않습니다. 비동기인 경우 또는 잘못된 행동으로 인해 투표 n에서 결정을 내리지 못하는 경우, 노드는 시간 초과되고 투표 n + 1에서 다시 시도합니다.
SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 Lokhavaet al. 소환 연합 투표는 종료되지 않을 수 있습니다. 따라서 일부 투표 용지에 대한 진술은 영구적으로 정체될 수 있습니다. 노드가 자신인지 여부를 결코 결정할 수 없는 불확정 상태 아직 진행 중이거나 중단되었습니다. 노드는 배제할 수 없기 때문에 불확실한 진술이 나중에 사실로 판명될 가능성, 새로운 진술에 대해 연합 투표를 시도해서는 안 됩니다. 불확실한 것에 반대되는 것. 각 투표 n에서 노드는 두 가지 유형에 대한 연합 투표를 사용합니다. 성명서 : • prepare ⟨n,x⟩ – x 이외의 값은 없음을 나타냅니다. ≤n 투표에서 결정되었거나 결정될 예정입니다. • commit ⟨n,x⟩ – x가 투표 n에서 결정되었음을 나타냅니다. 중요한 것은 ⟨n,x⟩contradicts 커밋을 준비하는 것입니다. ⟨n′,x ′⟩n ≥n′이고 x , x ′인 경우. 노드는 a에 대한 연합 투표를 시도하여 n 투표를 시작합니다. 명령문은 ⟨n,x⟩를 준비합니다. 이전 준비 문이 있는 경우 연합투표를 통해 성공적으로 확인되었으며, 노드는 확인된 가장 높은 투표 준비에서 x를 선택합니다. 그렇지 않으면 노드는 x를 다음의 출력으로 설정합니다. 다음 하위 섹션에 설명된 지명 프로토콜. 노드가 준비 ⟨n,x⟩를 성공적으로 확인한 경우에만 투표 n에서는 커밋 ⟨n,x⟩에 대해 연합 투표를 시도합니다. 만약에 성공하면 SCP가 결정했음을 의미하므로 노드는 다음을 출력합니다. 확인된 커밋 문의 값입니다. 얽힌 집합 S를 생각해 보세요. 최대 하나의 값이므로 특정 투표에서 S 구성원이 작성한 것을 확인할 수 있지만 두 가지 다른 값이 확인되지는 않습니다. 특정 투표 용지에 S 멤버가 포함됩니다. 게다가 ⟨n,x⟩를 커밋하면 확인되면 준비 ⟨n,x⟩도 확인되었습니다. 이후 prepare ⟨n,x⟩는 연합 투표의 합의 보장에 따라 다른 값에 대한 이전 커밋과 모순됩니다. 우리는 이전에 다른 값이 결정될 수 없다는 것을 알고 있습니다. S회원의 투표. 투표용지 번호 유도를 통해 우리는 그러므로 SCP가 안전하다는 것을 알아내십시오. 활성을 위해서는 온전한 세트 I와 충분히 긴 세트를 고려하세요. 동기식 투표 n. 조각에 결함이 있는 노드가 나타나는 경우 선의로 행동하는 노드 중 n개는 간섭하지 않고 투표를 통해 간섭합니다. n + 1 I의 모든 멤버는 동일한 준비문 세트 P를 확인했습니다. P = ∅이고 투표용지 n이 충분히 길면, 지명 프로토콜은 어떤 값 x에 수렴될 것입니다. 그렇지 않은 경우 x를 P에서 가장 높은 투표로 준비한 값으로 둡니다. 어느 쪽이든 균일하게 페더레이션을 시도합니다. 다음 투표에서 준비 ⟨n + 1,x⟩에 투표하세요. 그러므로 만일 n + 1도 동기식이므로 x에 대한 결정은 필연적으로 따릅니다. 3.2.2 지명 지명에는 다음 진술에 대한 연합 투표가 수반됩니다. • x 지명 – x가 유효한 결정 후보임을 명시합니다. 노드는 여러 가치를 지명하기 위해 투표할 수 있습니다. 지명 진술은 모순되지 않습니다. 그러나 일단 노드는 지명 성명을 확인하고 투표를 중단합니다. 새로운 가치를 지명합니다. 연합 투표는 여전히 노드가 다음을 수행할 수 있도록 허용합니다. 투표하지 않은 새로운 지명 성명을 확인합니다. 투표 또는 수락 정족수에서 받아들이다 정족수에서 a는 유효하다 ~로부터 받다 차단 세트 커밋되지 않은 투표했다 받아들였다 확인했다 ¬a에 투표했습니다 그림 1. 연합 투표 단계 온전한 집합의 구성원이 서로 확인할 수 있도록 허용 새로운 투표를 보류하면서 가치를 지명합니다. 지명의 (진화하는) 결과는 확인된 지명 명세서에 있는 모든 값의 결정론적 조합입니다. 만약에 x는 일련의 거래를 나타내며, 노드는 합집합을 취할 수 있습니다. 세트 중 가장 큰 세트 또는 가장 높은 hash을 가진 세트입니다. 모든 노드가 동일한 작업을 수행하는 한. 노드가 새로운 것을 보류하기 때문에 하나의 지명 성명을 확인한 후 투표합니다. 확인된 문에는 한정된 수의 값만 포함될 수 있습니다. 확인된 진술이 확실하게 전파된다는 사실 손상되지 않은 세트는 손상되지 않은 노드가 결국 다음으로 수렴됨을 의미합니다. 동일한 지정 값 세트 및 그에 따른 지정 결과, 하지만 프로토콜의 임의로 늦은 시점에 알 수 없는 지점이 있습니다. 노드는 연합 리더 선택을 사용하여 지명 진술서의 다양한 값 수. 만 지명 성명서에 아직 투표하지 않은 리더는 새로운 x를 도입할 수 있습니다. 다른 노드는 응답을 기다립니다. 리더의 (유효한) 지명 투표를 복사하면 됩니다. 실패를 수용하기 위해 리더 세트는 다음과 같이 계속 성장합니다. 시간 초과가 발생하지만 실제로는 소수의 노드에서만 새로운 x 값이 도입됩니다. 3.2.3 연합 투표 연합 투표는 다음과 같은 3단계 프로토콜을 사용합니다. 그림 1. 노드는 먼저 추상적 진술에 동의하려고 시도합니다. 투표하고, 수락하고, 최종적으로 진술을 확인합니다. 노드 v는 그렇지 않은 유효한 진술 a에 투표할 수 있습니다. 다른 것과 모순된다미결제 투표 및 수락된 성명서. 이는 서명된 투표 메시지를 방송함으로써 이루어집니다. v 그런 다음 a가 다른 승인된 진술과 일치하고 (사례 1) v가 다음과 같은 쿼럼의 구성원인 경우 a를 승인합니다. 각 노드는 a에 투표하거나 a를 수락합니다. 또는 (케이스 2) v인 경우에도 마찬가지입니다. a에 투표하지 않았으면 v-차단 세트가 a를 수락합니다. 경우 2의 경우, v는 이전에 a에 반대되는 투표를 한 적이 있는데, 지금은 기각되었습니다. v 기각된 투표를 잊어버리는 것이 허용됩니다. v가 손상되지 않은 경우 이를 알고 있기 때문에 결코 캐스팅하지 않은 척합니다. 기각된 투표는 사례 1을 통해 정족수를 완료할 수 없습니다. v는 a를 수락한다고 브로드캐스트한 다음 a가 수신되면 확인합니다. 만장일치로 a를 받아들이는 정족수. 그림 2는 v-차단 세트의 효과와 캐스케이드 정리 연합투표. 서로 얽힌 두 개의 노드는 모순되는 진술을 확인할 수 없습니다. 두 개의 필수 쿼럼이 공유해야 하기 때문입니다.Stellar를 통한 빠르고 안전한 글로벌 결제 SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 3 4 2 1 5 7
Stellar 共识协议
Stellar 共识协议 (SCP) 是一种基于法定人数的协议 具有开放成员资格的拜占庭协议协议。仲裁是由各个节点的本地配置决策组合而成的。然而,节点只识别 他们自己所属的法定人数,并且只有在之后 了解所有其他仲裁成员的本地配置。这种方法的一个好处是 SCP 本质上 容忍节点存在的异构视图。因此, 节点可以单方面加入和离开,无需 协调成员资格的“视图变更”协议。 3.1 联邦拜占庭协议 传统的拜占庭协议问题包括 N 个节点的封闭系统,其中一些节点出现故障,可能会 行为任意。节点接收输入值并交换 消息来决定输入中的输出值。 当没有两个行为良好的节点输出不同的决策并且唯一的决策时,拜占庭协议是安全的。 决定是一个有效的输入(对于有效商定的某些定义SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 洛哈瓦等人。 事先)。当协议保证以下内容时,它就是有效的: 每个诚实节点最终都会输出一个决策。 通常,协议假设某个整数 N = 3f + 1 f > 0,然后保证安全性和某种形式的活性 只要最多 f 个节点出现故障。在这些过程中的某个阶段 协议、节点对提议值和提案进行投票 收到 2f + 1 票,称为投票法定人数,变为 的决定。对于 N = 3f + 1 个节点,任意两个法定人数 大小 2f + 1 在至少 f + 1 个节点中重叠;即使其中 f 重叠节点有故障,两个法定人数至少共享 一个无故障的节点,防止矛盾的决策。 然而,这种方法只有在所有节点都同意的情况下才有效 什么构成了法定人数,这在 SCP 中是不可能的 两个节点甚至可能不知道彼此的存在。 通过 SCP,每个节点 v 单方面声明节点集, 称为它的仲裁切片,使得 (a) v 相信如果所有 切片的成员就系统的状态达成一致,然后 他们是对的,并且 (b) v 相信至少其中一个切片 将能够及时提供有关 系统的状态。我们称由此产生的系统为 节点及其切片,联邦拜占庭协议 (FBA)系统。正如我们接下来将看到的,法定人数系统出现了 来自节点的切片。 非正式地,FBA 节点的切片表示该节点与谁 节点需要同意。例如,一个节点可能需要与 4 个特定组织达成协议,每个组织运行 3 个节点;到 适应停机时间,它可以将其切片设置为全部集合 由每个组织的 2 个节点组成。如果这“需要 同意”关系传递地关联任意两个节点, 我们达成全球协议。否则,我们会得到分歧, 但仅限于双方都不需要的组织之间 与对方达成一致。考虑到当今的拓扑 金融体系中,我们假设广泛的融合将不断产生人们所说的单一分类账历史 “Stellar 网络”,就像我们所说的互联网一样。 法定人数由切片产生,如下所示。每个节点指定 它发送的每条消息中的法定人数切片。设 S 为 一组消息源自的节点集。一个 节点认为消息集已达到法定人数 当 S 的每个成员都有一个切片包含在 S 中时的阈值。 通过构造,这样一个集合 S,如果一致的话,满足 其每个成员的协议要求。 有故障的对等点可能会通告精心设计的切片来改变什么 表现良好的节点会考虑法定人数。为了协议分析的目的,我们将FBA中的法定人数定义为非空 包含至少一个仲裁片的节点集 S 每个非故障成员。这个抽象是合理的,就像任何集合一样 声称代表一致法定人数的消息 实际上确实如此(即使它包含来自故障节点的消息), 当 S 只包含行为良好的节点时,它是精确的。在 在本节中,我们还假设节点的切片不会改变。 尽管如此,我们的结果转移到了改变切片的情况 因为切片变化的系统的安全性不亚于 固定切片系统,其中节点的切片由所有 它在改变切片的情况下使用过的切片(参见定理 13 在 [68])。正如第 4 节中所解释的,活跃度取决于 表现良好的节点最终会删除不可靠的节点 从他们的切片中。 由于不同节点有不同的协议要求,FBA 排除了安全性的全局定义。我们说 当每个节点发生故障时,无故障节点 v1 和 v2 会交织在一起 v1 的仲裁数与 v2 的每个仲裁数至少在一个相交 无故障节点。 FBA 协议可以确保达成一致 仅在交织的节点之间;既然SCP这样做了,那是它的错 安全容忍度是最佳的。互联网假设, Stellar 的设计的底层,指出人们关心的节点 大约会交织在一起。 如果 I 是一致无故障的法定人数,即使 I 之外的每个节点都有故障,I 的每两个成员都交织在一起,我们就说一组节点 I 是完整的。直观地说, 那么,我应该对不完整的人的行为保持不受影响 节点。 SCP 保证非阻塞活性 [93] 和 对完整集合的安全性,尽管节点本身不需要 知道(并且可能无法知道)哪些集合是完整的。 此外,相交的两个完整集合的并集是 完整的一套。因此,完整集定义了一个分区 表现良好的节点,其中每个分区都是安全且活跃的 (在某些条件下),但是不同的分区可能会输出 不同的决定。 3.1.1 FBA 中的安全性与活性考虑因素 除了有限的例外 [64],大多数封闭式拜占庭协议都被调整到平衡点,在该平衡点 安全性和活性具有相同的容错能力。在亚马逊物流中, 这意味着无论发生什么故障,所有的配置 相互缠绕的集合也完好无损。鉴于 FBA 确定 以去中心化的方式组成法定人数,个体切片的选择不太可能导致这种平衡。此外,在 至少在 Stellar 中,均衡是不可取的:后果 安全故障(即双花数字货币)是 比活性失败(即延迟)更糟糕 无论如何,付款都在 Stellar 之前几天完成)。人 因此应该并且确实选择大的法定人数切片,以便 它们的节点更有可能保持交织在一起,而不是完好无损。 进一步倾斜天平,更容易恢复 与传统封闭系统相比,FBA 系统中典型的活性故障。在封闭系统中,所有消息都必须 针对同一组法定人数进行解释。因此, 添加和删除节点以从故障中恢复需要 就重新配置事件达成共识,一旦共识不再有效,就很难达成共识。相比之下,对于FBA, 任何节点都可以随时单方面调整其仲裁切片 时间。响应具有系统重要性的停电 组织,节点管理员可以调整他们的切片 解决问题,有点像协调响应 BGP 灾难 [63] (尽管没有限制 通过物理网络链路进行路由)。
使用 Stellar 进行快速、安全的全球支付 SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 3.1.2 级联定理 SCP遵循基本圆形模型[42]的模板; 节点通过一系列编号的选票取得进展,每个选票 尝试三个任务:(1)确定一个与之前投票中的任何决定不矛盾的“安全”值(通常称为 准备选票),(2) 就安全值达成一致,以及 (3) 检测协议是否成功。不过FBA开放 会员资格阻碍了几种常见的技术,使其 不可能将传统的封闭协议“移植”到FBA 通过简单地改变法定人数的定义来建立模型。 许多协议采用的一项技术是轮换 超时后以循环方式通过领导节点。在封闭系统中,循环领导者选择可确保 最终,一个独特的诚实领导者最终会就单一价值观达成一致。不幸的是,循环赛 无法在成员身份未知的 FBA 系统中工作。 FBA 失败的另一种常见技术是假设特定的法定人数可以说服所有节点。例如, 如果每个人都承认任意 2f + 1 个节点为法定人数,那么 2f + 1 个签名足以向所有节点证明协议状态。 类似地,如果一个节点收到一定数量的相同消息 通过可靠的广播 [24],节点可以假设所有非故障节点也将看到法定人数。相比之下,在 FBA 中, 仲裁对于仲裁之外的节点没有任何意义。 最后,非联邦系统通常采用“向后”方式 安全性推理:如果f+1个节点出现故障,则全部安全 保证消失。因此,如果节点 v 听到 f + 1 个节点全部 陈述一些事实 F, v 可以假设至少有一个事实告诉 真实(因此 F 为真)且不损失安全性。这样的 FBA 推理失败,因为安全是成对的属性 节点,因此对某些对等方失去安全性的节点可以 总是因为假设不好的事实而失去更多节点的安全性。 然而,FBA 可以对活跃度进行反向推理。将 v 阻塞集定义为与每个节点相交的节点集 v 的切片。如果 v 阻塞集 B 一致错误,则 B 可以拒绝节点 v 的仲裁并降低其活跃度。因此,如果 B 一致陈述事实 F,则 v 知道 F 是 true 或 v 不完整。然而,v仍然需要看到完整的 法定人数知道交织的节点不会与 F 相矛盾, 这导致了 SCP 中的最后一轮沟通 类似中不需要的其他 FBA 协议 [47] 封闭式会员协议。结果是我们有 对潜在事实的三种可能的置信水平:不确定,在完整节点中安全地假设(我们将 术语接受的事实),并且可以安全地在交织在一起的情况下进行假设 节点(我们将其称为已确认的事实)。 节点v可以通过检查B是否与其所有切片相交来有效地确定集合B是否是vblocking。有趣的是,如果节点总是宣布它们的声明 接受并且全部法定人数接受一条语句,它会启动一个级联过程,通过该过程语句在整个过程中传播 完好无损的套装。我们称这种传播背后的关键事实为 级联定理,其表述如下:如果 I 是 完整集合,Q 是 I 中任意成员的法定人数,S 是任意 Q 的超集,则要么 S ΣI 要么有一个成员 v ∈I 使得 v < S 且 I ∩S 是 v 阻塞。直观上看,这是 情况并非如此,S 的补集将包含法定人数 与 I 相交但不与 Q 相交,违反了群体交集。 请注意,如果我们从 S = Q 开始并重复将 S 展开为 包括它阻止的所有节点,我们获得级联效果,直到, 最终,S包含了I的全部。 3.2 协议说明 SCP 是一个部分同步共识协议 [42],由一系列达成共识的尝试组成,称为 选票。投票采用越来越长的超时。一个 选票同步协议确保节点保持在线状态 相同的选票持续增加的时间,直到选票 是有效同步的。不保证终止 直到选票同步,但是两个同步选票 其中表现良好的节点切片的错误成员会 不干扰足以使 SCP 终止。 投票协议规定了每次投票期间采取的行动 投票。投票从准备阶段开始,其中节点 尝试确定一个不矛盾的值来提议 任何先前的决定。然后,在提交阶段,节点尝试 对准备值做出决定。 投票采用称为联合投票的协议子协议,我n 哪些节点对抽象语句进行投票 这最终可能会得到证实或陷入困境。有些陈述可能被指定为矛盾的,并且安全性 联合投票的保证是一个组织中没有两个成员 相互交织的集合证实了相互矛盾的陈述。除完好无损外,不保证对声明的确认 设置所有成员都以相同方式投票。然而,如果一个 完整集合的成员确实确认了一个声明,联邦 投票保证完整集的所有成员最终都会确认该声明。因此,采取不可逆转的步骤 响应确认声明保留活性 完整的节点。 节点最初提出从提名中获得的值 增加所有成员完整的机会的协议 集合提出相同的值,最终收敛 (尽管没有办法确定收敛是否完成)。 提名将联合投票与领导人选举结合起来。 由于 FBA 中不可能进行循环赛,因此提名使用 概率领导者选择方案。 级联定理在投票中都起着至关重要的作用 同步并避免阻塞状态 不再可能终止。 3.2.1 投票 SCP 节点进行一系列编号投票,采用联合投票来就哪些声明达成一致 价值观是或不是在哪些选票中决定的。如果异步 或错误行为阻止在投票 n 中做出决定, 节点超时并在选票 n + 1 中重试。
SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 洛哈瓦等人。 回想一下,联合投票可能不会终止。因此,一些 关于选票的陈述可能会永久陷入困境 不确定状态,节点永远无法确定它们是否 仍在进行中或陷入困境。因为节点不能排除 不确定的陈述后来被证明是正确的可能性, 他们绝不能尝试对新声明进行联合投票 与不确定的矛盾。 在每个投票 n 中,节点对两种类型使用联合投票 声明: • 准备⟨n,x⟩– 表示除了x 之外没有其他值 已经或将在任何≤n 的投票中决定。 • 提交⟨n,x⟩– 表明x 在投票n 中决定。 重要的是,请注意准备⟨n,x⟩与提交相矛盾 ⟨n′,x ′⟩当 n ≥n′ 且 x , x ′ 时。 节点通过尝试对 a 进行联合投票来开始投票 n 语句准备⟨n,x⟩。如果之前有任何准备语句 经过联合投票成功确认, 节点从最高选票的确认准备中选择x。否则,节点将 x 设置为 提名协议将在下一小节中描述。 当且仅当节点成功确认准备⟨n,x⟩ 在投票 n 中,它尝试对提交 ⟨n,x⟩ 进行联合投票。如果 成功,说明SCP已经决定,所以节点输出 来自已确认的提交语句的值。 考虑一个交织的集合 S。因为最多有一个值 可以确认由 S 成员在给定选票中准备,不能确认由 S 成员提交的两个不同值 给定选票中的 S 成员。此外,如果提交⟨n,x⟩ 确定了,则准备⟨n,x⟩也确定了;自从 通过联合投票的协议保证,准备⟨n,x⟩与任何早期提交的不同值相矛盾 我们知道在早期可能不会决定不同的值 由 S 成员投票。通过对选票号码的归纳,我们 因此认为SCP是安全的。 对于活性,考虑一个完整的集合 I 和一个足够长的集合 同步投票如果切片中出现故障节点 表现良好的节点不干预n,然后通过投票 I 中的 n+1 个所有成员都已确认相同的 P 组准备语句。如果 P = ∅ 并且选票 n 足够长,则 提名协议将收敛于某个值 x。 否则,令 x 为 P 中具有最高选票的准备中的值。无论哪种方式,我都会统一尝试联合 在下一次投票中对准备⟨n + 1,x⟩进行投票。因此,如果 n + 1 也是同步的,x 的决定不可避免地随之而来。 3.2.2 提名 提名需要对声明进行联合投票: • 提名x – 表明x 是有效的决策候选者。 节点可以投票提名多个不同的值 提名声明并不矛盾。然而,有一次 节点确认任何提名声明后,将停止投票 提名新的价值观。联合投票仍然允许节点 确认其未投票赞成的新提名声明,其中 投票或接受 从法定人数 接受一个 从法定人数 a 有效 接受来自 阻塞集 未承诺的 投票了 接受了一个 确认了一个 投票给 Øa 图 1. 联合投票的阶段 允许完整集合的成员相互确认 提名值,同时仍保留新的选票。 提名的(不断变化的)结果是已确认的提名声明中所有值的确定性组合。如果 x代表一组交易,节点可以取并集 集合中最大的集合,或者具有最高 hash 的集合,所以 只要所有节点都做同样的事情。因为节点保留新的 确认一项提名声明后进行投票,一组 已确认的陈述只能包含有限多个值。 已确认的陈述可靠地传播的事实 完整集意味着完整节点最终收敛于 相同的一组提名值和提名结果, 尽管在协议中任意后期的未知点。 节点采用联邦领导者选择来减少 提名语句中不同值的数量。仅 尚未投票支持提名声明的领导者可以引入新的 x。其他节点等待接收消息 领导人并复制其领导人的(有效)提名票。 为了适应失败,领导者队伍不断壮大 尽管实际上只有少数节点引入了新的 x 值,但还是会发生超时。 3.2.3 联合投票 联合投票采用如图所示的三阶段协议 图 1. 节点首先尝试就抽象语句达成一致 投票,然后接受,最后确认声明。 节点 v 可以投票给任何不支持的有效语句 a 与其他的相矛盾未决投票和已接受的声明。它通过广播签名投票消息来实现这一点。 如果 a 与其他接受的语句一致并且(情况 1)v 是法定人数的成员,则 v 然后接受 a 每个节点要么投票支持 a 要么接受 a,或者(情况 2)即使 v 没有投票给a,v-blocking集合接受a。在情况 2 中,v 可以 之前曾投过与 a 相矛盾的票,现在已 被否决了。 v 可以忘记被否决的选票 假装它从未施放它们,因为 ifv 完好无损,它知道 被否决的投票无法达到案例 1 的法定人数。 v 广播它接受 a,然后在 a 存在时确认它 一致接受 a 的法定人数。图 2 显示了 v-阻塞集和级联定理的影响 联合投票。 两个交织在一起的节点无法确认矛盾的陈述,因为两个所需的法定人数必须共享一个使用 Stellar 进行快速、安全的全球支付 SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 3 4 2 1 5 7
X 투표
Y에 투표하세요 (아) 3 4 2 1 5 7 6 투표 X 투표 X 투표 X 투표 Y 투표 X 투표 Y 투표 Y (비) 3 4 2 1 5 7 6 수락 X 투표 X 수락 X 투표 Y 수락 X 투표 Y 투표 Y (다) 3 4 2 1 5 7 6 수락 X 수락 X 수락 X 투표 Y 수락 X 수락 X 투표 Y (디) 3 4 2 1 5 7 6 수락 X 투표 X 수락 X 수락 X 수락 X 수락 X 수락 X (e) 그림 2. 연합 투표의 계단식 효과. 각 노드에는 슬라이스 구성원에 대한 화살표로 표시된 하나의 쿼럼 슬라이스가 있습니다. (a) 모순되는 진술 X와 Y가 도입됩니다. (b) 노드는 유효한 진술에 투표합니다. (c) 노드 1은 쿼럼 후에 X를 수락합니다. {1, 2, 3, 4}는 만장일치로 X에 투표합니다. (d) 노드 1, 2, 3, 4는 모두 X를 수락합니다. 세트 {1}은 5-차단이므로 노드 5는 X를 허용하여 무시합니다. Y에 대한 이전 투표입니다. (e) 세트 {5}는 6 및 7 차단이므로 6과 7은 모두 X를 허용합니다. 모순되는 진술을 받아들일 수 없는 결함이 없는 노드입니다. 진술 확인은 보장되지 않습니다. 분할 투표의 경우 두 진술 모두 영구적일 수 있습니다. 투표 단계에서 정족수를 기다리지 못했습니다. 그러나 만일 온전한 세트의 노드 나는 진술, 즉 캐스케이드를 확인합니다. 정리와 사례 2를 수락하면 결국 모든 것이 보장됩니다. 그 진술을 확인하십시오. 3.2.4 투표지 동기화 노드가 해당 커밋 문을 확인할 수 없는 경우 현재 투표용지에서 시간 초과 후 포기합니다. 시간 초과가 발생합니다. 임의의 범위에 맞게 조정하기 위해 각 투표 용지의 길이를 늘립니다. 네트워크 지연에. 그러나 시간 초과만으로는 동시에 시작되지 않은 노드의 투표를 동기화하는 데 충분하지 않습니다. 다른 이유로 동기화가 해제되었습니다. 동기화를 달성하기 위해 노드는 노드가 노드의 일부인 경우에만 타이머를 시작합니다. 현재(또는 이후) 투표 n에 모두 참여하는 정족수. 이 일찍 시작된 노드의 속도를 늦추고 온전한 세트의 구성원이 그룹보다 너무 앞서 있습니다. 게다가 노드 v가 나중에 v-blocking 세트를 발견한 경우 즉시 가장 낮은 투표지로 건너뜁니다. 타이머에 관계없이 더 이상 그렇지 않습니다. 캐스케이드 정리는 모든 낙오자들이 따라잡을 수 있도록 보장합니다. 결과 투표용지는 온전한 전체에 걸쳐 대략적으로 동기화된다는 것입니다. 시스템이 동기화되면 설정됩니다. 3.2.5 연합 리더 선택 리더 선택을 통해 각 노드는 다음과 같은 리더를 선택할 수 있습니다. 노드가 일반적으로 하나 또는 작은 숫자만 선택하는 방식 지도자의. 리더 실패를 수용하기 위해 리더 선택 라운드를 통해 진행됩니다. 현재 라운드의 리더인 경우 자신의 책임을 다하지 않는 것처럼 보이다가 나중에 특정 시간 초과 기간 노드는 다음 라운드로 진행됩니다. 그들이 따르는 리더의 집합을 확장합니다. 각 라운드에서는 [0,hmax) 범위의 정수를 출력하는 두 개의 고유한 암호화 hash 함수인 H0 및 H1을 사용합니다. 예를 들어 Stellar은 Hi(m) = SHA256(ib||r||m)을 사용합니다. 여기서 b는 전체 SCP 인스턴스(블록 또는 원장 번호)이고, r은 리더 선택 라운드 번호, hmax = 2256. 내 라운드마다 노드 v의 우선순위를 다음과 같이 정의합니다. 우선순위(v) = H1(v) 각 노드마다 하나의 Stratman이 리더로 선택됩니다. 우선순위가 가장 높은 노드(v). 이 접근 방식은 효과적입니다. 거의 동일한 쿼럼 슬라이스를 사용하지만 제대로 작동하지 않습니다. 불균형 구성에서 노드의 중요성을 포착합니다. 예를 들어 유럽과 중국이 각각 3씩 기여한다면 모든 쿼럼에 노드를 할당하지만 중국은 1,000개의 노드를 실행하고 유럽은 4개를 실행하는 경우 중국이 99.6%의 가장 높은 우선순위 노드를 갖게 됩니다. 시간의. 따라서 우리는 슬라이스 가중치의 개념을 도입합니다. Weight(u,v) ∈[0, 1]은 노드 u의 쿼럼 슬라이스의 비율입니다. 노드 v를 포함합니다. 노드 u가 새로운 리더를 선택할 때, 다음과 같이 정의된 이웃만 고려합니다. 이웃(u) = {v | H0(v) < hmax · 가중치(u,v) } 그런 다음 노드는 빈 리더 세트로 시작하고 각 라운드는 그것에 가장 높은 이웃(u)의 노드 v를 추가합니다. 우선순위(동사). 모든 라운드에서 이웃 세트가 비어 있으면 u는 대신 H0(v)/weight(u,v)의 가장 낮은 값을 가진 nodev를 추가합니다.
投票 X
投票 Y (一) 3 4 2 1 5 7 6 投票 X 投票 X 投票 X 投票 是 投票 X 投票 是 投票 是 (二) 3 4 2 1 5 7 6 接受 X 投票 X 接受 X 投票 是 接受 X 投票 是 投票 是 (三) 3 4 2 1 5 7 6 接受 X 接受 X 接受 X 投票 是 接受 X 接受 X 投票 是 (四) 3 4 2 1 5 7 6 接受 X 投票 X 接受 X 接受 X 接受 X 接受 X 接受 X (五) 图 2. 联合投票中的级联效应。每个节点都有一个仲裁片,用箭头指示该片的成员。 (a) 引入矛盾的陈述 X 和 Y。 (b) 节点投票选出有效的声明。 (c) 节点 1 在达到法定人数后接受 X {1,2,3,4}一致投票支持X。 (d)节点1,2,3,4全部接受X;集合 {1} 是 5 阻塞,因此节点 5 接受 X,推翻 (e) 集合 {5} 是 6 和 7 阻塞,因此 6 和 7 都接受 X。 不能接受矛盾陈述的非故障节点。不保证声明的确认: 如果出现分裂投票,两种声明都可能永久有效 在投票阶段等待法定人数。然而,如果 完整集合中的一个节点我确认了一个陈述,级联 定理并接受案例 2 确保我所有的最终都会 确认该声明。 3.2.4 选票同步 如果节点无法确认提交语句 目前的投票,他们在暂停后放弃。超时时间得到 每次投票的时间更长,以便适应任意范围 关于网络延迟。 然而,仅超时不足以同步不同时启动的节点的选票或 由于其他原因而失去同步。为了实现同步,节点只有在成为某个节点的一部分时才启动计时器。 当前(或以后)投票 n 的法定人数。这个 减慢早期启动的节点并确保没有 完整集合中的成员远远领先于该组。 此外,如果节点 v 注意到稍后设置了 v 阻塞 选票,它立即跳到最低的选票,这样 现在情况不再是这样,无论任何计时器如何。级联 然后定理确保所有掉队者都能赶上。结果 是选票在整个完整的过程中大致同步 一旦系统变得同步就设置。 3.2.5 联邦领导人选举 领导者选择允许每个节点在这样的情况下选择领导者 节点一般只选择一个或少数的方式 的领导者。为了适应领导者失败,领导者选择 分轮进行。如果本轮领先者 似乎没有履行自己的职责,然后经过一段时间 一定的超时时间节点进入下一轮 扩大他们追随的领导者群体。 每轮使用两个独特的加密 hash 函数 H0 和 H1,输出 [0,hmax) 范围内的整数。 例如,Stellar 使用 Hi(m) = SHA256(i∥b∥r ∥m),其中 b 是整个 SCP 实例(区块或账本编号),r 是 领导者选择轮数,hmax = 2256。 一轮中,我们定义节点v的优先级为: 优先级(v) = H1(v) 每个节点将选择一名稻草人作为领导者 具有最高优先级(v)的节点。这种方法有效 具有几乎相同的仲裁切片,但不正确 捕捉不平衡配置中节点的重要性。例如,如果欧洲和中国各贡献 3 每个法定人数都有节点,但中国运行 1,000 个节点,欧洲运行 4 个,那么中国将拥有最高优先级节点 99.6% 的时间。 因此,我们引入切片权重的概念,其中 Weight(u,v) ∈[0, 1] 是节点 u 的仲裁切片的分数 包含节点 v。当节点 u 选择新的领导者时,它 只考虑邻居,定义如下: 邻居(u)= { v | H0(v) < hmax · 权重(u,v) } 然后,nodeu 从一组空的领导者开始,并且在每个 round 将邻居(u) 中具有最高值的节点 v 添加到其中 优先级(v)。如果任何一轮中邻居集为空,则 u 添加具有最低值 H0(v)/weight(u,v) 的节点 v。
SCP의 공식 검증
설계 오류를 없애기 위해 SCP의 안전성을 정식으로 검증했습니다. 및 활성 속성([65] 참조). 구체적으로 우리는 확인했습니다. 서로 얽힌 노드는 결코 동의하지 않으며 아래에 설명된 조건 하에서 온전한 세트의 모든 구성원이 결국 결정합니다. 흥미롭게도 검증 결과 SCP가 활성을 보장하는 조건은 미묘합니다. 처음에 생각했던 것보다 더 강합니다 [68]: 아래에 설명된 대로, 별다른 조치 없이 타이밍을 조작하는 악성 노드 프로토콜에서 벗어나면 수동으로 제거해야 할 수도 있습니다. 쿼럼 조각에서.
SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 Lokhavaet al. 속성이 가능한 모든 측면에서 유지되는지 확인하기 위해 FBA 구성 및 실행은 임의적인 것으로 간주됩니다. 임의의 로컬 구성이 있는 노드 수. 이 분리된 온전한 세트가 있는 시나리오와 잠재적으로 무한히 긴 실행이 포함됩니다. 단점은 우리가 매개변수화된 값을 검증하는 어려운 문제에 직면합니다. 무한 상태 시스템. 검증을 다루기 쉽게 유지하기 위해 우리는 Ivy [69] 및 [82] 방법론을 사용하여 1차 논리(FOL)로 SCP를 모델링했습니다. 검증 프로세스는 수동으로 귀납적 추측을 제공한 다음 자동으로 확인하는 것으로 구성됩니다. 아이비. SCP의 FOL 모델은 다음의 일부 측면을 추상화합니다. FOL에서 다루기 어려운 FBA 시스템(예: 캐스케이드 정리는 공리로 간주되므로) Isabelle/HOL [75]을 사용한 추상화의 건전성. FOL에서 검증 문제를 표현한 후 귀납적 불변량을 제공하여 안전성을 검증합니다. 유도성 불변은 약 12개의 한 줄 추측으로 구성됩니다. 150라인의 프로토콜 사양. 그런 다음 Ivy의 선형 시간 논리에서 SCP의 활성 속성을 지정하고 liveness를 줄이기 위해 [80, 81]의 안전 감소에 대한 liveness 검증 문제에서 귀납적 문제를 찾는 문제 불변. SCP의 안전은 상대적으로 간단하지만 증명하자면, SCP의 생존성 주장은 훨씬 더 복잡하고 약 150개의 단일 행 불변성으로 구성됩니다. 활성을 증명하려면 다음의 정확한 형식화가 필요합니다. SCP가 종료를 보장한다는 가정. 우리는 처음에 온전한 세트가 모두 있는 경우 항상 종료할 것이라고 생각했습니다. 구성원이 슬라이스 [68]에서 결함이 있는 노드를 제거했습니다. 그러나 이것은 불충분한 것으로 판명되었습니다. 손상되지 않음) I can 구성원의 쿼럼에 있는 노드, 결함이 있는 노드의 영향을 완료하여 종료를 방지합니다. 투표가 끝나기 직전에 정족수를 확보하여 I 멤버는 다음 투표에서 다른 x 값을 선택했습니다. 따라서 우리는 비공식적으로 다음을 추가로 가정해야 합니다. I 구성원의 쿼럼에 있는 각 노드는 결국 다음 중 하나를 수행합니다. 적시에 메시지를 보내거나 충분한 기간 동안 메시지를 전혀 보내지 않습니다. 실제로 이는 I의 구성원이 조건이 유지될 때까지 슬라이스를 조정해야 합니다. 이 문제는 FBA 시스템에 고유한 것이 아닙니다: Losa et al. [47] 현재 활성도가 엄격하게 약한 프로토콜에 따라 달라지는 프로토콜 슬라이스에서 결함이 있는 노드를 제거할 필요 없이 최종 동기화 및 최종 리더 선택만 가정합니다.
SCP的形式验证
为了消除设计错误,我们正式验证了SCP的安全性 和活性属性(参见 [65])。具体来说,我们验证了 相互交织的节点永远不会意见不一致,并且在下面讨论的条件下,完整集合中的每个成员最终都会做出决定。有趣的是,经核查发现, SCP 保证活性的条件很微妙, 并且比最初想象的更强 [68]:如下所述, 恶意节点操纵时间而不用其他方式 违反协议的可能需要手动驱逐 来自法定人数切片。
SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 洛哈瓦等人。 确保属性在所有可能的情况下都被证明成立 FBA配置和执行,我们考虑任意 具有任意本地配置的节点数量。这个 包括具有不相交完整集的场景,以及可能无限长的执行。缺点是我们 面临验证参数化的挑战性问题 无限状态系统。 为了使验证易于处理,我们使用 Ivy [69] 和 [82] 的方法在一阶逻辑 (FOL) 中对 SCP 进行建模。 验证过程包括手动提供归纳猜想,然后由系统自动检查 常春藤。 SCP 的 FOL 模型抽象了 难以在 FOL 中处理的 FBA 系统(例如, 级联定理被视为公理),因此我们验证 使用 Isabelle/HOL [75] 进行抽象的健全性。 在用 FOL 表达验证问题后,我们通过提供归纳不变量来验证安全性。感应式 不变量由十几个单行猜想组成,大约 150行协议规范。然后,我们在 Ivy 的线性时序逻辑中指定 SCP 的活性属性,并使用 活性降低 [80, 81] 的安全性以降低活性 验证问题转化为寻找电感问题 不变的。虽然 SCP 的安全性相对简单 证明,SCP 的活性论证要复杂得多 由大约 150 个单行不变量组成。 证明活性需要精确形式化 SCP 确保终止的假设。我们最初认为是一个完整的集合,如果全部的话我总是会终止 成员从其切片 [68] 中删除了故障节点。然而,事实证明这还不够:一个行为良好的(但 不完整)节点中的法定人数我可以,在 故障节点的影响,通过完成来防止终止 投票结束前达到法定人数,从而导致 I 的成员在下一次投票中选择不同的 x 值。 因此,我们还必须非正式地假设, I 成员的法定人数中的每个节点最终要么 变得及时或在足够长的时间内根本不发送消息。实际上,这意味着 I 的成员可以 需要调整他们的切片,直到条件成立。这个 问题不是 FBA 系统固有的:Losa 等人。 [47] 目前 其活性取决于严格较弱的协议 假设只是最终同步和最终领导者选举,而不需要从切片中删除故障节点。
결제 네트워크
이 섹션에서는 SCP 위에 복제된 상태 머신 [88]으로 구현된 Stellar의 결제 네트워크에 대해 설명합니다. 5.1 원장 모델 Stellar의 원장은 계정 추상화를 중심으로 설계되었습니다( 보다 코인 중심의 사용되지 않은 거래 출력과 대조 또는 UTXO 모델의 Bitcoin). 원장 내용은 다음과 같이 구성됩니다. 계정, 신탁선, 등 네 가지 유형의 원장 항목 집합 제안 및 계정 데이터. 계정은 자산을 소유하고 발행하는 주체입니다. 각각 계정의 이름은 공개 키로 지정됩니다. 기본적으로 해당 개인 키는 계정에 대한 거래에 서명할 수 있습니다. 그러나 다른 서명자를 추가하고 계정 이름을 지정하는 키의 인증을 취소하도록 계정을 재구성할 수 있습니다. 여러 서명자를 요구하는 "다중 서명" 옵션. 각 계정 또한 다음을 포함합니다: 시퀀스 번호(트랜잭션에 포함됨) 재생을 방지하기 위해), 일부 플래그 및 "네이티브"의 균형 XLM이라는 사전 채굴된 암호화폐로, 일부 서비스 거부 공격 및 시장 형성 촉진 중립 통화로. Trustlines는 발행된 자산의 소유권을 추적합니다. 발행 계좌와 숏 계좌로 구성된 쌍으로 명명 자산 코드(예: 'USD' 또는 'EUR'). 각 신뢰선은 다음을 지정합니다. 계정, 자산, 해당 자산의 계정 잔액, 잔고를 초과할 수 없는 한도 및 일부 플래그. 계정은 자산 보유에 명시적으로 동의해야 합니다. 스패머가 안장하는 것을 방지하는 신뢰 라인 생성 원하지 않는 자산이 있는 계정. 고객 파악(KYC) 규정에 따라 많은 금융 기관은 자신이 보유하고 있는 예금이 누구인지 알아야 합니다. 예를 들어 사진이 있는 신분증을 확인하는 것입니다. 이를 준수하기 위해 발급자는 다음을 설정할 수 있습니다. 계정에 선택적인 auth_reqired 플래그를 추가하여 발행한 자산의 소유권을 승인된 계정으로 제한합니다. 그러한 승인을 부여하기 위해 발급자는 승인된 권한을 설정합니다. 고객의 신뢰선에 플래그를 지정합니다. 제안은 계정의 거래 의지에 따라 결정됩니다. 특정 자산의 일정 금액을 다른 자산에 대해 특정 금액으로 주문서의 가격; 자동으로 일치하고 매수/매도 가격이 교차할 때 채워집니다. 마지막으로 계정 데이터는 계정, 키, 값의 세 가지로 구성되어 계정 소유자를 허용합니다. 작은 메타데이터 값을 게시합니다. 원장 스팸을 방지하기 위해 최소 XLM 잔액이 있습니다. 예비라고. 계정의 준비금은 각각 증가합니다. 관련 원장 입력 및 원장 입력 시 감소 사라집니다(예: 주문이 완료되거나 취소되는 경우, 또는 신뢰라인이 삭제되었습니다). 현재 준비금은 0.5 XLM 증가합니다. (~$0.03) 원장 항목당. 보유금액에 상관없이, 삭제를 통해 계정의 전체 가치를 회수 가능 AccountMerge 작업을 사용하여 이를 수행합니다. 그림 3에 표시된 원장 헤더는 전역 속성을 저장합니다. 원장 번호, 예비 잔액과 같은 매개변수 원장 항목, 이전 원장 헤더의 hash(실제로는 여러 hashes가 건너뛰기 목록을 형성함), SCP 출력에는 다음이 포함됩니다. 이 원장에 적용된 새로운 거래의 hash, 의 hash 해당 거래의 결과(예: 성공 또는 실패) 각각) 및 모든 원장 항목의 스냅샷 hash. 스냅샷 hash에는 모든 원장 내용이 포함되어 있으므로, validators는 거래를 검증하기 위해 기록을 보유할 필요가 없습니다. 그러나 예상되는 수억 규모로 확장하려면 계정마다 모든 원장 항목 테이블을 다시hash할 수는 없습니다. 장부를 닫습니다. 또한, 원장을 이전하는 것은 실용적이지 않습니다.Stellar를 통한 빠르고 안전한 글로벌 결제 SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 원장 # = 4 H(이전 hdr) SCP 출력 H(결과) H(스냅샷) ... 헤더 원장 # = 5 H(이전 hdr) SCP 출력 H(결과) H(스냅샷) ... 헤더 . . . 그림 3. 원장 내용. H는 SHA-256이고, H *는 H의 계층적 또는 재귀적 적용을 나타냅니다. SCP 출력 또한 이전 헤더 hash에 따라 달라집니다. 계정 만들기 새 계정 원장 항목 생성 및 자금 조달 계정병합 계정 원장 항목 삭제 옵션 설정 계정 플래그 및 서명자 변경 결제 대상에게 특정 수량의 자산을 지불합니다. 계정 경로지불 결제와 비슷하지만 다른 자산으로 결제(최대 제한하다); 최대 5개의 중개 자산을 지정하세요. 제안 관리 제안 원장 항목 생성/삭제/변경, -패시브 제안 확산을 허용하지 않는 수동적 변형 포함 데이터 관리 계정 생성/삭제/변경 데이터 원장 항목 변화신뢰 신뢰라인 생성/삭제/변경 허용신뢰 트러스트 라인에서 승인된 플래그 설정 또는 지우기 범프 시퀀스 시퀀스를 늘립니다. 계좌번호 그림 4. 원장 운영 노드 연결이 끊어질 때마다 해당 크기 네트워크가 너무 오래 연결되었습니다. 따라서 스냅샷 hash은(는) hashing 및 상태 조정을 모두 최적화하도록 설계되었습니다. 특히 스냅샷은 원장 항목을 시간별로 계층화합니다. 기하급수적으로 크기가 커지는 컨테이너 세트의 마지막 수정 버킷이라고 부릅니다. 버킷 모음을 버킷이라고 합니다. 목록을 작성하며 로그 구조 병합 트리와 일부 유사합니다. (LSM-트리) [77]. 버킷리스트는 트랜잭션 처리 중에는 읽히지 않습니다(섹션 5.4 참조). 그러므로 특정 디자인 LSM 트리의 측면을 완화할 수 있습니다. 특히, 무작위 키로 액세스할 필요가 없으며 버킷은 읽기만 가능합니다. 병합 수준의 일부로 순차적으로. 버킷 해싱 목록은 병합될 때 각 버킷을 hashing하고 버킷 hashes의 새로운 누적 hash을 계산하여 수행됩니다(작은, 각 원장 마감 시 고정 참조 인덱스 hashes). 연결 해제 후 버킷리스트를 조정하려면 다운로드가 필요합니다. 버킷만 다릅니다. 5.2 거래 모델 거래는 원본 계정, 유효성 기준, 메모 및 하나 이상의 작업 목록. 그림 4에는 사용 가능한 작업이 나열되어 있습니다. 각 작업에는 원본 계정이 있습니다. 기본값은 전체 거래의 기본값입니다. 거래는 반드시 모든 소스 계정에 해당하는 키로 서명되어야 합니다. 작업. 다중서명 계정에는 더 높은 서명이 필요할 수 있습니다. 일부 작업(예: SetOptions)의 가중치 이하 다른 경우(예: AllowTrust). 트랜잭션은 원자적입니다. 작업이 실패하면 아무 작업도 수행되지 않습니다. 그들은 실행합니다. 이는 다자간 거래를 단순화합니다. 가정하자 발행자는 토지 증서를 나타내는 자산을 생성하고 사용자 A는 작은 토지 구획과 $10,000를 교환하고 싶습니다. B가 소유한 더 큰 토지 구획. 두 사용자는 모두 서명할 수 있습니다. 세 가지 작업을 포함하는 단일 거래: 두 개의 토지 지불 및 1달러 지불. 트랜잭션의 주요 유효성 기준은 시퀀스 번호이며, 이 시퀀스 번호는 트랜잭션의 시퀀스 번호보다 1 커야 합니다. 원본 계정 원장 항목입니다. 유효한 트랜잭션 실행 (성공 여부에 관계없이) 시퀀스 번호를 증가시켜 재생을 방지합니다. 초기 시퀀스 번호에는 원장이 포함됩니다. 삭제 후에도 재생을 방지하기 위해 상위 비트에 숫자를 넣습니다. 그리고 계정을 다시 만드세요. 다른 타당성 기준은 선택적인 제한입니다. 트랜잭션이 실행될 수 있습니다. 땅과 달러로 돌아가다 위의 스왑에서 A가 B보다 먼저 거래에 서명하면 A는 서명하지 않을 수 있습니다. B가 제출하기 전에 1년 동안 거래를 보류하기를 원합니다. 따라서 거래를 무효화하는 시간 제한을 둘 수 있습니다. 며칠 후. 다중서명 계정도 구성할 수 있습니다 hash 사전 이미지의 공개에 서명 가중치를 부여하기 위해, 이는 시간 제한과 결합되어 원자 크로스체인 거래를 허용합니다 [1]. 거래의 원본 계정은 XLM으로 소소한 수수료를 지불합니다. 정체가 없는 한 10−5 XLM. 혼잡 상황에서는 운영 비용은 네덜란드 경매에 의해 결정됩니다. 검증인은 validators가 유사하기 때문에 수수료로 보상되지 않습니다. 채굴자가 아닌 Bitcoin 전체 노드로. XLM을 파괴하는 대신, 수수료는 투표에 의해 비례적으로 재활용되고 분배됩니다. 기존 XLM 보유자(회고하면 그럴 수도 있고 그럴 수도 있음) 복잡성을 감당할 가치가 없었습니다. 5.3 합의 가치 각 원장에 대해 Stellar은 SCP를 사용하여 데이터 구조에 동의합니다. 세 개의 필드 포함: 트랜잭션 세트 hash(hash 포함) 이전 원장 헤더의), 마감 시간,d 업그레이드. 여러 값이 지명된 것으로 확인되면 Stellar이 가장 많은 작업이 포함된 트랜잭션 세트(연결 끊기) 총 수수료를 기준으로 거래 세트 hash), 모든 항목의 합집합 업그레이드 및 가장 높은 마감 시간. 마감시간은 오직 마지막 원장의 마감 시간과 마감 시간 사이이면 유효합니다. 존재하므로 노드는 잘못된 시간을 지정하지 않습니다. 업그레이드는 준비금 잔액, 최소 운영 비용 및 프로토콜 버전과 같은 글로벌 매개변수를 조정합니다. 언제 지명 중에 결합되면 높은 수수료와 프로토콜 버전 번호가 낮은 번호를 대체합니다. 업그레이드는 연합 투표 난투 공간을 통해 거버넌스에 영향을 미칩니다 [34], 둘 다 평등주의적이지도 중앙집권적이지도 않습니다. 각 validator은(는) 다음과 같이 구성됩니다. 관리 또는 비관리(기본값)에 따라 운영자가 거버넌스에 참여하기를 원하는지 여부. validator을 관리하려면 세 가지 종류의 업그레이드를 고려하세요. 원하는 것, 유효한 것, 유효하지 않은 것(validator이 하지 않는 모든 것)
SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 Lokhavaet al. validator 핵심 지평선 FS DB DB 제출하다 클라이언트 클라이언트 다른 validators 그림 5. Stellar validator 아키텍처 구현 방법을 알고 있습니다). 원하는 업그레이드가 다음과 같이 구성되었습니다. 특정 시간에 트리거되고 서로 조정되도록 의도되었습니다. 연산자. 관리 노드는 항상 원하는 후보를 지명하기 위해 투표합니다. 업그레이드, 수락하지만 유효한 업그레이드를 지명하기 위해 투표하지는 않음 (즉, 차단 정족수를 따르며) 절대로 투표하지 마십시오. 또는 잘못된 업그레이드를 수락합니다. 비정부 validators 에코 유효한 업그레이드에 대해 보는 모든 투표(기본적으로 위임) 선택한 사람들이 원하는 업그레이드에 대한 결정 거버넌스 역할을 위해. 5.4 구현 그림 5는 Stellar의 validator 아키텍처를 보여줍니다. 데몬 stellar-core(~92k 라인의 C++, 타사 라이브러리 제외)라고 불리는 SCP 프로토콜과 복제된 상태 머신을 구현합니다. SCP의 가치를 생성하려면 많은 수의 원장 항목을 작은 암호화로 줄여야 합니다. hashes. 대조적으로, 거래 검증 및 실행 계정 상태 및 주문 일치를 조회해야 합니다. 최고의 가격. 두 기능을 모두 효율적으로 제공하기 위해 stellar-core 원장의 두 가지 표현, 즉 버킷 목록을 포함하는 외부 표현을 유지하며 바이너리 파일로 저장됩니다. 효율적으로 업데이트하고 점진적으로 rehashed할 수 있습니다. SQL 데이터베이스의 내부 표현(PostgreSQL 생산 노드의 경우). Stellar-core는 다음을 포함하는 쓰기 전용 기록 아카이브를 생성합니다. 확인된 각 트랜잭션 세트와 스냅샷 버킷. 아카이브를 통해 새 노드가 스스로 부트스트랩할 수 있습니다. 네트워크에 가입할 때. 장부에 대한 기록도 제공합니다. 역사 - 자료를 찾아볼 수 있는 곳이 있어야 합니다. 2년 전 거래. 기록은 추가 전용이므로 자주 접근하지 않는 정보이므로 저렴한 곳에 보관할 수 있습니다. Amazon Glacier 또는 저장을 허용하는 모든 서비스 등 플랫 파일을 검색합니다. 검증인 호스트는 일반적으로 호스트하지 않습니다. 검증에 영향을 미치지 않도록 자체 아카이브 제공 기록의 실적입니다. 스텔라 코어를 단순하게 유지하기 위해 사용되지 않습니다. 애플리케이션에 의해 직접 제공되며 새로운 트랜잭션 제출을 위해 매우 좁은 인터페이스만 노출합니다. 지원하다 클라이언트, 대부분의 validators는 horizon(~18k)이라는 데몬을 실행합니다. Go 라인) 제출을 위한 HTTP 인터페이스를 제공합니다. 그리고 거래를 학습합니다. horizon에는 읽기 전용 액세스 권한이 있습니다. stellar-core의 SQL 데이터베이스, 지평선의 위험을 최소화 불안정한 항성핵. 지불 경로 찾기와 같은 기능은 완전히 수평으로 구현되며 업그레이드 가능 다른 validator들과 협력하지 않고 일방적으로. 여러 선택적 상위 계층 데몬이 클라이언트가 되어 생태계를 완성합니다. 브릿지 서버는 다음을 용이하게 합니다. Stellar을 기존 시스템과 통합합니다(예: 특정 계정에서 받은 모든 결제에 대한 알림 게시). 에이 규정 준수 서버는 금융 기관에 후크를 제공합니다. 발송인 및 수취인 정보 교환 및 승인 제재 목록 준수를 위해 결제 시. 마지막으로, 페더레이션 서버는 사람이 읽을 수 있는 이름 지정을 구현합니다. 계정 시스템. 6 배포 경험 Stellar은 몇 년 동안 적당한 수준의 상태로 성장했습니다. 합리적으로 신뢰할 수 있는 전체 노드 운영자의 수. 그러나, 노드의 구성은 활성 상태였습니다(물론 그렇지는 않았지만 안전)은 우리 Stellar 개발 재단에 달려 있습니다. (SDF); SDF가 갑자기 사라졌다면, 다른 노드 운영자들은 개입하여 수동으로 우리를 제거해야 했을 것입니다. 네트워크를 계속하려면 쿼럼 슬라이스에서 가져옵니다. 우리와 다른 많은 사람들은 SDF의 시스템적 중요성을 줄이고 싶어하지만 이 목표는 이후에 점점 더 높은 우선순위를 받았습니다. 연구원 [58] 안전 및 위험에 대한 위험을 구분하지 않고 네트워크의 중앙 집중화를 정량화하고 공개했습니다. 활력. 많은 운영자가 적극적인 구성 조정에 반응하여 주로 규모를 늘렸습니다. SDF의 중요성을 희석하기 위한 노력의 일환으로 정족수 분할; 아이러니하게도 이는 생존에 대한 위험만 증가시켰습니다. 두 가지 문제가 상황을 악화시켰습니다. 먼저, 인기 있는 타사 Stellar 모니터링 도구 [5]가 체계적으로 실제로 확인하지 않음으로써 validator 가동 시간을 과대평가함 그 스텔라 코어가 실행 중이었습니다. 이는 사람들이 다음을 포함하도록 유도합니다. 쿼럼 슬라이스에 신뢰할 수 없는 노드가 있습니다. 둘째, 버그 stellar-core는 validator이 다음 원장으로 이동한 것을 의미합니다. 나머지 노드가 사전 준비를 완료하는 데 적절하게 도움이 되지 않았습니다.메시지 분실에 대비한 장부. 그 결과, 네트워크에서 67분의 다운타임이 발생하여 필요 validator 관리자가 수동으로 조정하여 다시 시작합니다. 더 나쁜 것은 네트워크를 다시 시작하려고 시도하는 동안 여러 노드에서 동시에 긴급한 재구성이 발생했다는 것입니다. 일부 노드에서 분기되어 해당 노드를 수동으로 종료해야 하며 분기 동안 승인된 거래를 다시 제출합니다. 다행히도 이러한 차이가 포착되어 수정되었습니다. 신속하고 충돌하는 거래가 포함되지 않았지만 네트워크가 쿼럼 교차를 활용하지 못할 위험 - 잠재적인 충돌을 계속 수용하면서 분열 단순히 구성 오류로 인해 트랜잭션이 발생했습니다. 이번 사건으로 매우 구체적이군요. 이러한 경험을 검토한 결과 두 가지 주요 결론이 도출되었습니다. 그리고 그에 상응하는 시정 조치.Stellar를 통한 빠르고 안전한 글로벌 결제 SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 심각, 100% 51% 51% 높음, 67% 51% 중간, 67% 51% 낮음, 67% 51% 51% ... ... ... 51% ... 51% 그림 6. 유효성 검사기 품질 계층 구조. 최고 품질의 노드 가장 높은 임계값인 100%가 필요한 반면, 낮은 품질은 67% 임계값으로 구성됩니다. 단일 내의 노드 조직은 51%의 과반수를 요구합니다. 6.1 구성의 복잡성과 취약성 Stellar은 쿼럼 슬라이스를 n 항목과 k 항목 집합이 있는 임계값 k로 구성된 중첩된 쿼럼 집합으로 표현합니다. 쿼럼 슬라이스를 구성합니다. n개의 항목 각각은 다음 중 하나입니다. validator 공개 키 또는 재귀적으로 다른 쿼럼 세트. 유연하고 컴팩트하면서도 중첩된 쿼럼을 실현했습니다. 노드 운영자에게 너무 많은 유연성과 너무 적은 지침을 동시에 제공하는 세트: 안전하지 않은 작성이 쉬웠습니다(또는 말도 안되는) 구성. 그룹화 기준 하위 집합을 계층 구조로 구성하기 위해 노드를 집합으로 구성 임계값 선택에 대한 모든 사항이 명확하지 않아 운영 실패의 원인이 되었습니다. 할지 여부가 명확하지 않았습니다. 중첩 집합 계층 구조의 "수준"을 신뢰 수준으로 처리합니다. 또는 조직, 또는 둘 다; 현장의 다양한 구성 위험을 지정하는 것 외에도 이러한 개념을 혼합 또는 의미 없는 임계값. 따라서 우리는 더 간단한 구성 메커니즘을 추가했습니다. 중첩된 쿼럼 집합의 두 가지 측면을 구분하는 것: 그룹화 조직별로 노드를 함께 연결하고 각 조직에 간단한 신뢰 분류(낮음, 중간, 높음 또는 중요). 높은 수준 이상의 조직은 다음을 수행해야 합니다. 역사 기록 보관소를 출판합니다. 새로운 시스템은 각 조직이 다음과 같이 표현되는 중첩된 쿼럼 집합을 통합합니다. 51% 임계값이 설정되고 조직이 세트로 그룹화됩니다. 67% 또는 100% 임계값(그룹 품질에 따라 다름) 각 그룹은 다음(더 높은 품질) 그룹의 단일 항목입니다. 그림 6에 나와 있습니다. 이 단순화된 모델은 구조 측면에서 잘못된 구성 가능성 합성된 중첩 세트와 선택한 임계값 각 세트. 6.2 잘못된 구성을 사전에 감지 둘째, 우리는 부정적인 영향을 관찰하기 위해 기다려서 집합적인 구성 오류를 탐지하는 것은 너무 늦었다는 것을 깨달았습니다. 특히 분기될 수 있는 잘못된 구성과 관련하여 정지보다 더 심각한 장애 모드 - 네트워크 요구 사항 잘못된 구성을 즉시 감지하여 운영자가 실제로 차이가 발생하기 전에 되돌릴 수 있도록 하는 것입니다. 이러한 요구를 해결하기 위해 우리는 노드의 전이적 폐쇄에 있는 모든 피어의 집합적 구성 상태를 지속적으로 수집하고 발산 가능성(예: 분리)을 감지하는 메커니즘을 validator 소프트웨어에 구축했습니다. 쿼럼 - 해당 집단 구성 내에서. 6.2.1 쿼럼 교차 확인 중 쿼럼 조각을 수집하는 것은 쉽지만, 그들 사이에서 연결되지 않은 쿼럼을 찾는 것은 공동 NP가 어렵습니다([62]). 그러나 우리는 채택했습니다. 일련의 알고리즘 휴리스틱 및 사례 제거 규칙 일반적인 사례를 확인하는 Lachowski [62]이 제안한 것 문제보다 몇 배 더 빠르게 문제를 해결합니다. 최악의 비용. 실제로 현재 네트워크의 쿼럼 슬라이스 전이적 폐쇄는 20~30개 정도입니다. 노드를 사용하고 Lachowski의 최적화를 통해 일반적으로 확인합니다. 단일 CPU에서 몇 초 만에 가능합니다. 필요한 경우 성능을 향상시키기 위해 검색을 병렬화할 수 있습니다. 6.2.2 위험한 구성 확인 네트워크가 분리된 쿼럼을 허용하는지 감지하는 것이 한 단계입니다. 올바른 방향으로 가고 있지만 불편할 정도로 늦게 위험을 알립니다. 그런 중요한 문제에 대해. 이상적으로는 네트워크의 집합적 구성이 발생할 때 노드 운영자가 경고를 받기를 원합니다. 위험한 상태에 가까워지고 있을 뿐입니다. 따라서 우리는 쿼럼 교차 검사기를 확장했습니다. 임계성(Criticality)이라고 부르는 조건을 감지하려면: 현재 집합적 구성은 하나의 잘못된 구성입니다. 분리된 정족수를 인정하는 주. 중요도를 탐지하려면, 검사기는 각 조직의 구성을 시뮬레이션된 최악의 구성 오류로 반복적으로 대체합니다. 결과에 대해 내부 쿼럼 교차 검사기를 다시 실행합니다. 그러한 중대한 구성 오류가 한 단계 더 진행된 경우 현재 상태에서 소프트웨어는 경고를 발행하고 잘못된 구성 위험이 있는 조직을 보고합니다. 이러한 변화는 운영자 커뮤니티에 두 가지 계층을 제공합니다. 최악의 형태로부터 보호하기 위한 통지 및 지침 집단적 구성 오류.
支付网络
本节介绍 Stellar 的支付网络,该网络作为 SCP 之上的复制状态机 [88] 实现。 5.1 账本模型 Stellar 的分类账是围绕帐户抽象设计的(在 与更以币为中心的未花费交易输出形成对比 或 Bitcoin 的 UTXO 型号)。分类账内容包括 四种不同类型的分类账条目集:账户、信任线、 优惠和帐户数据。 账户是拥有和发行资产的主体。每个 帐户由公钥命名。默认情况下,对应的私钥可以为账户签署交易。 但是,可以重新配置帐户以添加其他签名者并取消授权命名该帐户的密钥,并使用 “多重签名”选项需要多个签名者。每个账户 还包含:序列号(包含在交易中 以防止重播),一些标志,以及“native”中的平衡 称为 XLM 的预开采加密货币,旨在缓解 一些拒绝服务攻击并促进做市 作为中性货币。 Trustlines 跟踪已发行资产的所有权,这些资产是 由发行帐户和短帐户组成的一对命名 资产代码(例如“美元”或“欧元”)。每个信任线指定 一个账户、一项资产、该资产的账户余额、 余额不能超过该限制,以及一些标志。 账户必须明确同意持有资产 创建信任线,防止垃圾邮件发送者上当 拥有不需要的资产的账户。 了解你的客户(KYC)法规要求许多金融机构知道他们持有谁的存款, 例如通过检查带照片的身份证件。为了遵守规定,发行人可以设置 他们的账户上有一个可选的 auth_reqired 标志,限制他们向授权账户发行的资产的所有权。 为了授予此类授权,发行人设置了授权 标记客户的信任线。 报价与账户的升级意愿相对应 在给定的时间内将一定数量的特定资产换成另一种资产 订单簿上的价格;它们会自动匹配并且 当买入/卖出价格交叉时填充。最后,账户数据由账户、键、值三元组组成,允许账户持有者 发布小的元数据值。 为了防止账本垃圾邮件,有一个最低的 XLM 余额, 称为储备。账户的准备金随着每次增加而增加 关联的分类账条目和当分类账条目减少时 消失(例如,当订单被执行或取消时,或者当 信任线已删除)。目前储备增长0.5 XLM 每个账本条目 (∼$0.03)。无论储备如何,它都是 可以通过删除来收回帐户的全部价值 它与 AccountMerge 操作。 如图 3 所示,账本标头存储全局属性: 账本编号、每个准备金余额等参数 账本条目,前一个账本标题的 hash (实际上 几个 hashes 形成一个跳过列表),SCP 输出包括 应用于此分类账的 hash 笔新交易, hash 笔 这些交易的结果(例如,成功或失败 每个),以及所有分类帐条目的快照 hash。 因为快照 hash 包含所有账本内容, validators 不需要保留历史记录来验证交易。 然而,要扩展到数亿预期 帐户,我们无法重新hash 每个帐户上的所有分类帐分录表 账本关闭。而且,转移账本也是不切实际的使用 Stellar 进行快速、安全的全球支付 SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 账本# = 4 H(上一个 hdr) SCP输出 H(结果) H(快照) ... 标头 账本# = 5 H(上一个 hdr) SCP输出 H(结果) H(快照) ... 标头 。 。 。 图 3. 分类帐内容。 H 为 SHA-256,而 H * 表示 H 的分层或递归应用。 SCP 输出 还取决于之前的标头 hash。 创建帐户 创建新账户分类账条目并为其提供资金 账户合并 删除账户分类帐条目 设置选项 更改帐户标志和签名者 付款方式 向目的地支付特定数量的资产。帐户。 路径支付 与支付类似,但以不同的资产支付(最多 限制);指定最多 5 个中间资产 管理报价 创建/删除/更改报价分类帐条目, -被动报价 具有被动变体以允许零传播 管理数据 创建/删除/更改帐户。数据分类账录入 改变信任 创建/删除/更改信任线 允许信任 在信任线上设置或清除授权标志 凹凸序列 增加序列账户号码 图 4. 主要账本操作 每次节点断开连接时的大小 网络时间太长。因此,快照 hash 是 旨在优化 hashing 和状态协调。 具体来说,快照按时间对账本条目进行分层 一组指数大小的容器中的最后一次修改 称为桶。桶的集合称为桶 列表,与日志结构的合并树有一些相似之处 (LSM 树)[77]。在事务处理期间不会读取存储桶列表(参见第 5.4 节)。因此,一定的设计 LSM 树的各个方面都可以放宽。特别是随机 不需要通过密钥访问,并且只能读取存储桶 按顺序作为合并级别的一部分。哈希桶 列表是通过在合并每个桶时对每个桶进行 hash 并计算桶 hashes 的新累积 hash 来完成的(一个小的, 每个分类帐关闭时参考的固定索引 hashes)。断开连接后协调存储桶列表需要下载 只有不同的桶。 5.2 交易模式 一笔交易由源账户、有效性标准、 备忘录,以及一个或多个操作的列表。图 4 列出了可用的操作。每个操作都有一个源账户, 默认为整个交易的值。一笔交易必须 由与每个源帐户相对应的密钥进行签名 一次手术。多重签名帐户可能需要更高的签名 某些操作(例如 SetOptions)的权重及更低 对于其他人(例如AllowTrust)。 事务是原子的——如果任何操作失败,则任何操作都失败 他们执行。这简化了多方交易。假设一个 发行人创建资产来代表土地契约,用户A 想要用一块小地块加上 10,000 美元换取一块 B 拥有更大的土地。两个用户都可以签名 一笔交易包含三项操作:两块土地 付款和一美元付款。 交易的主要有效性标准是其序列号,该序列号必须比交易的序列号大1 源帐户分类帐条目。执行有效交易 (成功与否)增加序列号,防止重播。初始序列号包含账本 高位数字以防止删除后重播 并重新创建一个帐户。 另一个有效性标准是对何时的可选限制 交易可以执行。回归土地和美元 上面交换,如果A在B之前签署交易,A可能不会 希望 B 在提交交易之前等待一年 它,因此可以设置使交易无效的时间限制 几天后。还可以配置多重签名帐户 为 hash 原像的揭示赋予签名权重, 它与时间限制相结合,允许原子跨链交易 [1]。 交易的源账户用 XLM 支付少量费用, 10−5 XLM,除非出现拥塞。拥堵情况下, 运营成本通过荷兰式拍卖确定。验证器是 不通过费用补偿,因为 validator 是类似的 到 Bitcoin 全节点,而不是矿工。与其破坏 XLM, 费用通过投票回收并按比例分配 现有的 XLM 持有者,回想起来可能会或可能 不值得这么复杂。 5.3 共识价值观 对于每个账本,Stellar 使用 SCP 就数据结构达成一致 具有三个字段:交易集 hash (包括 hash 前一个分类帐标题的)、关闭时间、d 升级。 当确认指定多个值时,Stellar 取 操作最多的交易集(打破联系 按总费用,然后交易集 hash),所有的并集 升级和最高关闭时间。关闭时间仅 如果在最后一个账本的关闭时间和当前账本的关闭时间之间有效 存在,因此节点不会指定无效时间。 升级调整储备余额、最低操作费、协议版本等全局参数。当 在提名期间,较高的费用和协议版本号会取代较低的费用和协议版本号。通过联合投票的斗争空间 [34] 升级效果治理,两者都不是 平等主义,也不是中央集权主义。每个 validator 配置为 治理或非治理(默认),根据 其运营者是否愿意参与治理。 管理 validators 考虑三种升级: 期望的、有效的和无效的(validator 没有的任何内容)
SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 洛哈瓦等人。 validator 核心 地平线 FS 数据库 数据库 提交 客户 客户 其他 validators 图 5. Stellar validator 架构 知道如何实施)。所需的升级配置为 在特定时间触发,旨在协调 运营商。治理节点总是投票提名所需的 升级,接受但不投票提名有效升级 (即,遵守阻塞法定人数),并且永远不要投票给 或接受无效的升级。非治理 validators 回声 他们看到的任何有效升级的投票,本质上是授权 决定那些选择的人希望进行哪些升级 担任治理角色。 5.4 实施 图 5 显示了 Stellar 的 validator 架构。一个守护进程 称为 stellar-core(约 92k 行 C++,不包括第三方库)实现了 SCP 协议和复制状态机。为 SCP 生成价值需要将大量账本条目减少为小型加密货币 hashes。相比之下,交易验证和执行 需要在以下位置查找帐户状态和订单匹配 最优惠的价格。为了有效地服务这两个功能,stellar-core 保留分类帐的两种表示形式:包含存储桶列表的外部表示形式,存储为二进制文件 可以有效地更新和增量重新hashed,并且 SQL 数据库(PostgreSQL 对于生产节点)。 Stellar-core 创建一个只写历史存档,其中包含 每个已确认的交易集及其快照 桶。该存档让新节点能够自行引导 加入网络时。它还提供分类账记录 历史——需要有一个地方可以让人们查阅 两年前的交易。由于历史只能追加 并且不经常访问,可以将其保存在便宜的地方 例如 Amazon Glacier 或任何允许存储的服务 并检索平面文件。验证者主机通常不托管 他们自己的档案,以避免对验证产生任何影响 服务历史的表现。 为了保持 stellar-core 简单,不打算使用它 直接由应用程序使用,并且仅公开一个非常狭窄的接口用于提交新事务。支持 客户端,大多数 validator 运行一个名为 Horizon 的守护进程(∼18k Go 行)提供了用于提交的 HTTP 接口 以及交易的学习。 Horizon 具有只读访问权限 stellar-core 的 SQL 数据库,最大限度地降低地平线风险 破坏恒星核心的稳定。支付路径查找等功能完全在 Horizon 中实现,并且可以升级 单方面不与其他 validator 协调。 几个可选的高层守护进程是 Horizon 的客户端,完善了生态系统。桥接服务器有助于 将 Stellar 与现有系统集成,例如,发布特定帐户收到的所有付款的通知。一个 合规服务器为金融机构提供挂钩 交换并批准发件人和受益人信息 关于付款,遵守制裁清单。最后, 联合服务器实现人类可读的命名 账户系统。 6 部署经验 Stellar 经过几年发展成为一个中等程度的州 相当可靠的全节点运营商的数量。然而, 节点的配置使得活跃度(尽管不是 安全)取决于我们,Stellar 发展基金会 (自卫队);如果SDF突然消失,其他节点运营商 需要干预并手动删除我们 从仲裁切片中让网络继续。 虽然我们和许多其他人希望降低自卫队的系统重要性,但这一目标在 研究人员 [58] 量化并公开了网络的中心化程度,而没有区分安全风险和 活力。许多运营商积极进行配置调整,主要是增加其规模 削减法定人数,以淡化自卫队的重要性;讽刺的是,这只会增加活性风险。 有两个问题加剧了这种情况。首先,一个流行的 系统地第三方Stellar监控工具[5] 由于没有实际验证而高估了 validator 正常运行时间 那个恒星核心正在运行;这导致人们包括 仲裁切片中的不可靠节点。其次,一个错误 stellar-core 意味着一旦 validator 移动到下一个分类帐, 它没有充分帮助剩余节点完成先前的任务如果丢失消息,我们的分类帐将被删除。结果, 网络出现 67 分钟的停机时间,需要 由 validator 管理员手动协调重新启动。 更糟糕的是,在尝试重新启动网络时,导致多个节点同时仓促重新配置 在集体错误配置中,允许某些节点 分歧,需要手动关闭这些节点并且 重新提交分歧期间接受的交易。幸运的是,这种分歧被发现并纠正了 速度很快并且不包含任何冲突的交易,但是 网络无法享受法定人数交叉的风险—— 分裂,同时继续接受潜在的冲突 交易,仅仅是由于错误配置而进行的 这件事非常具体。 回顾这些经验得出两个主要结论 以及相应的纠正措施。使用 Stellar 进行快速、安全的全球支付 SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 严重,100% 51% 51% 高,67% 51% 中等,67% 51% 低,67% 51% 51% ... ... ... 51% ... 51% 图 6. 验证器质量层次结构。最高质量的节点 要求最高阈值为 100%,而较低质量则配置为 67% 阈值。单个节点内 组织需要简单的 51% 多数。 6.1 配置复杂性和脆弱性 Stellar 将仲裁切片表示为由 n 个条目和阈值 k 组成的嵌套仲裁集,其中 k 个条目的任何集合 构成一个法定人数切片。 n 个条目中的每一个都是 validator 公钥,或者递归地另一个仲裁集。 在灵活和紧凑的同时,我们实现了嵌套仲裁 同时设置为节点操作员提供了太多的灵活性和太少的指导:很容易写出不安全的(或 甚至是无意义的)配置。分组标准 将节点分成集合,用于将子集组织成层次结构,以及 选择阈值的方法都不够明确,导致操作失败。尚不清楚是否要 将嵌套集层次结构中的“级别”视为信任级别, 或一个组织,或两者兼而有之;现场多种配置 除了指定危险之外,还混合了这些概念 或无意义的阈值。 因此我们添加了一个更简单的配置机制 它将嵌套仲裁集的两个方面分开:分组 按组织将节点聚集在一起,并用简单的信任分类(低、中、高或 关键)。高级及以上组织必须 出版历史档案。新系统综合了嵌套仲裁集,其中每个组织都表示为 51%阈值设定,组织分组 67% 或 100% 阈值(取决于群体质量)。 每个组都是下一个(更高质量)组中的一个条目, 如图 6 所示。这个简化的模型减少了 结构错误配置的可能性 合成的嵌套集和选择的阈值 每套。 6.2 主动检测错误配置 其次,我们意识到,通过等待观察其负面影响来发现集体错误配置已经为时已晚。特别是对于可能出现分歧的错误配置——a 比停止更严重的故障模式——网络需要 能够立即检测到错误配置,以便操作员可以在任何分歧实际发生之前恢复它。 为了满足这一需求,我们在 validator 软件中构建了一种机制,该机制不断收集节点传递闭包中所有对等点的集体配置状态,并检测潜在的发散(即不相交) 法定人数——在该集体配置内。 6.2.1 检查仲裁交叉点 虽然收集仲裁切片很容易,但在其中找到不相交的仲裁却是共 NP 难题 [62]。然而,我们采用了 一组算法启发式和案例消除规则 由 Lachowski [62] 提出,检查典型实例 问题的解决速度比问题快几个数量级 最坏情况下的成本。从实际情况来看,目前的网络 仲裁切片传递闭包数量级为 20–30 节点,并且通过 Lachowski 的优化,通常会检查 在单个 CPU 上只需几秒钟。如果有需要的话 为了提高性能,我们可以并行化搜索。 6.2.2 检查有风险的配置 检测网络是否承认不相交的仲裁是一个步骤 方向正确,但危险信号却迟到了 对于如此关键的问题。理想情况下,我们希望节点操作员在网络集体配置时收到警告 只是接近危险状态。 因此,我们扩展了群体交叉检查器 检测我们称之为关键性的条件:当电流 集体配置是一种错误配置 承认不相交法定人数的国家。为了检测关键性, 检查器反复用模拟的最坏情况错误配置替换每个组织的配置,然后 对结果重新运行内部仲裁交集检查器。 如果存在任何此类严重错误配置,只需一步之遥 从当前状态来看,软件会发出警告并 报告该组织存在配置错误风险。 这些变化为运营商社区提供了两个层次 防范最坏形式的通知和指导 集体错误配置。
평가
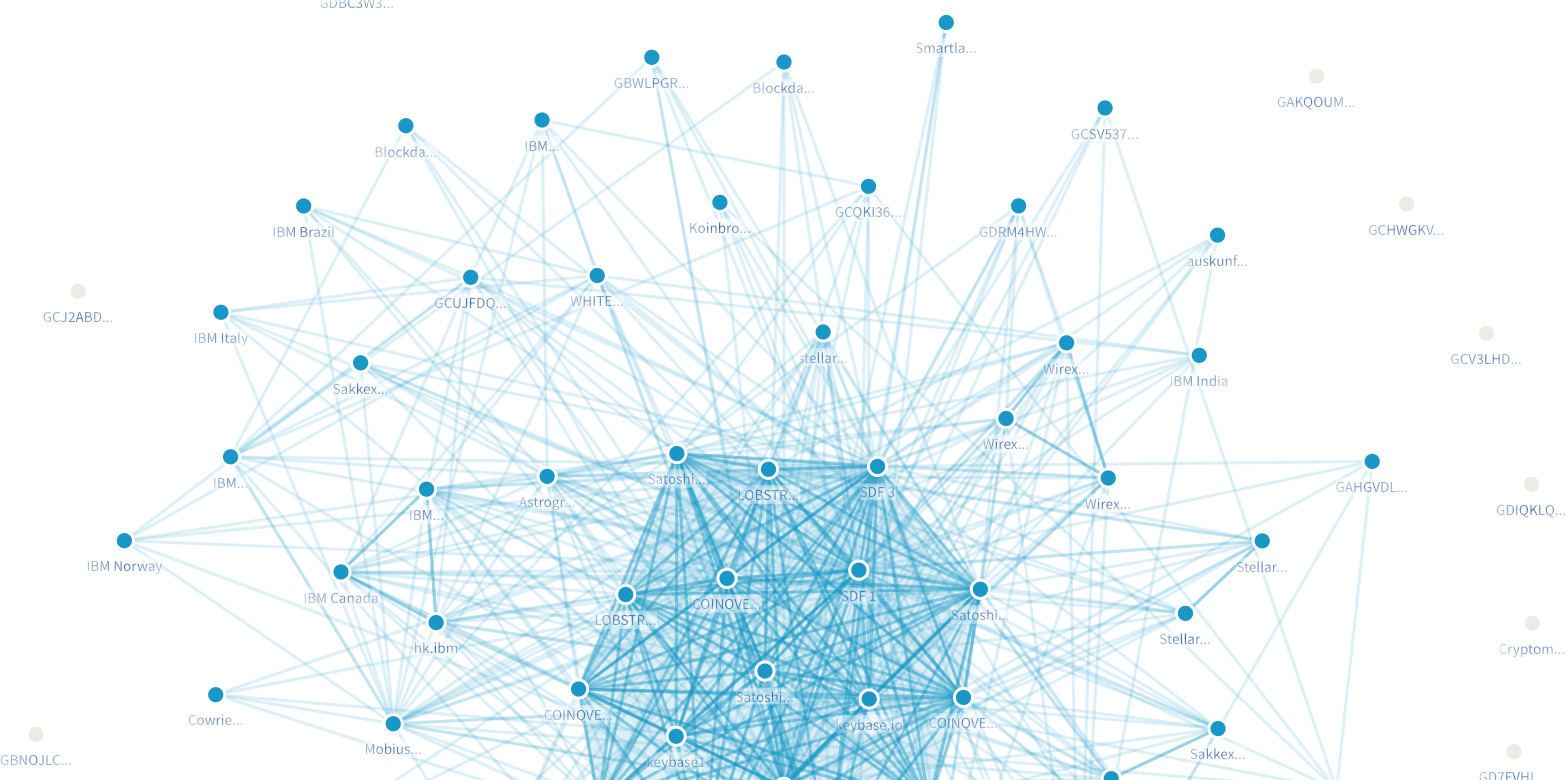
Stellar의 글로벌 결제로서의 적합성을 이해하고 거래 네트워크, 우리는 공용 네트워크의 상태를 평가했습니다. 개인 실험에 대해 통제된 실험을 실행했습니다. 네트워크. 우리는 다음 질문에 중점을 두었습니다. • 프로덕션 네트워크 토폴로지는 어떤 모습입니까? 평균적으로 얼마나 많은 메시지가 방송되는지, 그리고 SCP는 어떻게 시간 초과를 경험합니까? • 합의 및 원장 업데이트 지연 시간이 계정 수와 독립적으로 유지됩니까?SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 Lokhavaet al. • (a) 초당 트랜잭션 증가(결과적으로 초당 트랜잭션 증가)가 지연 시간에 어떤 영향을 미칩니까? 원장) 및 (b) validator 노드 수는 무엇입니까? • CPU 측면에서 노드를 실행하는 데 드는 비용은 얼마입니까? 메모리 및 네트워크 대역폭? 결제 네트워크에 비해 거래율이 낮습니다. 다른 유형의 분산 시스템에 적용됩니다. 주요 blockchain, Bitcoin 및 Ethereum, 초당 최대 15개의 트랜잭션을 확인합니다. Stellar 미만. 게다가 이러한 시스템은 작업 증명을 위해서는 여러 블록이 채굴될 때까지 기다려야 하기 때문에 거래를 안전하게 확인하는 데 한 시간이 걸립니다. 는 non-blockchain SWIFT 네트워크는 최대 피크일인 [14]에 초당 평균 420건의 트랜잭션만 처리했습니다. 그러므로 우리는 선택했습니다 측정값을 5초 목표와 비교하기 위해 원장 간격, 더 공격적인 목표입니다. 우리의 결과는 다음과 같습니다 대기 시간은 다음과 같은 경우에도 이 한도보다 훨씬 낮습니다. 아직 구현되지 않은 몇 가지 최적화가 파이프라인에 있습니다. 7.1 앵커 거래량 기준으로 가장 많이 거래되는 자산에는 통화가 포함됩니다(예: 3 USD 앵커, 2 CNY), Bitcoin 앵커, 부동산 담보 증권 token [92] 및 인앱 통화 [8]. 앵커마다 정책이 다릅니다. 예를 들어 USD 앵커 하나는 Stronghold는 auth_reqired를 설정하고 보유하고 있는 모든 계정에 대해 고객 파악(KYC) 프로세스를 요구합니다. 자산. 또 다른 AnchorUSD, 누구나 받고 거래하자 USD(문자 그대로 $0.50를 멕시코로 보내는 것이 가능함) $0.000001의 수수료로 5초 안에 완료됩니다. 그러나 AnchorUSD는 USD를 구매하거나 상환하려면 KYC 및 수수료가 필요합니다. 기존 송금 방식으로. 필리핀에서는 입금에 대한 은행 규정이 완화되었습니다, coin.ph 모든 ATM 기계 [36]에서 PHP 현금화를 지원합니다. 앞서 언급한 보안 token 및 인앱 통화 외에도 다음과 같은 다양한 비통화 token이 있습니다. 상업 채권 [22] 및 탄소 배출권 [85, 96] 더보기 token 협업을 장려하는 난해한 자산 자동차 압수 [35]. 7.2 공용 네트워크 이 글을 쓰는 시점에서 126개의 활성 풀 노드가 있으며 그 중 66개는 투표 메시지에 서명하여 합의에 참여합니다. 그림 7 ([5]에 의해 생성됨)은 사이에 선을 사용하여 네트워크를 시각화합니다. 하나가 다른 노드의 쿼럼 조각에 나타나는 경우 두 개의 노드 진한 파란색 선은 양방향 의존성을 나타냅니다. 에서 센터는 17개의 사실상 "계층 1 validators"로 구성된 클러스터입니다. SDF, SatoshiPay, LOBSTR, COINQVEST 및 Keybase. 4개월 전, 섹션 6의 사건이 일어나기 전, 시스템적으로 중요한 노드는 15개였습니다. 겉보기에는 3개였습니다. Tier 1 조직과 여러 개의 무작위 싱글톤. 는 그래프도 훨씬 덜 규칙적으로 보였습니다. 따라서 새로운 구성 메커니즘 및/또는 더 나은 운영자 결정이 필요한 것 같습니다. 더 건강한 네트워크 토폴로지에 기여합니다. 없이 훌륭한 재정 자원(및 해당 주주) 그림 7. 쿼럼 슬라이스 맵 의무), 5급 1인 채용은 어려웠을 것 그러나 처음부터 조직. 이는 정족수를 제안합니다. 슬라이스는 네트워크 부트스트래핑에서 유용한 역할을 합니다. 누구나 할 수 있습니다. 중요한 플레이어가 되겠다는 목표를 가지고 참여하세요. 쌍으로 합의할 수 있는 문지기가 없습니다. 현재 원장에는 330만 개 이상의 계정이 있습니다. 오버 최근 24시간 동안 Stellar은 평균 4.5건의 거래를 기록했으며 초당 15.7 작업. 최근 원장을 검토하면 대부분 트랜잭션은 단일 작업을 수행하는 것처럼 보이지만 몇 번의 작업마다 원장에는 다음과 같은 많은 작업이 포함된 트랜잭션이 표시됩니다. 제안을 관리하는 시장 조성자로부터 오는 것으로 보입니다. 는 합의를 달성하고 원장을 업데이트하는 데 걸리는 시간은 다음과 같습니다. 각각 1061ms와 46ms입니다. 99번째 백분위수는 2252ms 및 142ms(전자는 1초 시간 초과를 반영함) 지명 지도자 선정에서). 참고 SCP의 성능은 SCP 이후 대부분 초당 트랜잭션과 독립적입니다. 임의의 많은 거래 중 hash에 동의합니다. 병목 현상은 후보 전파로 인해 발생할 가능성이 더 높습니다. 지명, 실행 및 검증 중 거래 트랜잭션 및 버킷 병합. 우리는 아직 필요하지 않았습니다 여러 CPU 코어 또는 디스크 드라이브를 통해 stellar-core의 트랜잭션 처리를 병렬화합니다. 우리는 또한 방송된 SCP 메시지의 수를 평가했습니다. 생산 네트워크에서. 일반적인 경우에는 단일 리더가 가치를 지명하기 위해 선출되면 우리는 7가지 논리적인 가치를 기대합니다. 브로드캐스트할 메시지: 투표하고 수락할 메시지 2개 노미nate 성명, 수락 및 확인을 위한 두 개의 메시지 준비문, 승인 및 확인을 위한 두 개의 메시지 커밋 문, 마지막으로 외부화 메시지 (낙오자를 돕기 위해 새 원장을 디스크에 커밋한 후 전송됨) 따라잡으세요). 구현은 커밋 확인을 결합합니다. 메시지를 최적화로 외부화합니다. 커밋된 후에 값을 외부화하는 것이 안전합니다. 그런 다음 프로덕션 Stellar validator에서 수집된 측정항목을 분석합니다. 오버 68시간 동안 초당 1.3개의 메시지가 방출되었습니다. 원장당 평균 6-7개의 메시지. 우리는 총
Stellar을 통한 빠르고 안전한 글로벌 결제 SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 백분위수 시간 초과 횟수 지명 투표 75% 0 0 99% 1 0 맥스 4 1 그림 8. 68시간이 넘는 원장당 시간 초과 validators가 브로드캐스트한 메시지 수가 더 많습니다. 연합 투표 메시지 외에도 노드도 브로드캐스트합니다. 그들이 배우는 모든 거래. 그림 8은 프로덕션에서 발생한 시간 초과를 보여줍니다. validator 68시간 동안. 추천 시간 제한은 다음과 같습니다. 리더 선출 기능의 효율성(비)을 측정하는 반면, 투표 시간 초과는 네트워크에 크게 의존합니다. 잠재적인 메시지 지연. 시간 초과가 일관되게 발생합니다. 방출된 메시지 수: 최선의 시나리오, 추가 지명 라운드가 필요한 경우 최소 7개의 메시지. 7.3 통제된 실험 우리는 포장된 용기에서 통제된 실험을 실시했습니다. 72GiB RAM을 갖춘 Amazon EC2 c5d.9xlarge 인스턴스, 900GB의 NVMe SSD 및 36개의 vCPU. 각 인스턴스는 동일한 EC2 지역이고 고정 대역폭이 10Gbps였습니다. 우리는 SQLite를 저장소로 사용했습니다. (Stellar은 PostgreSQL도 지원합니다. 하지만 측정에 노이즈를 주입하는 비동기 작업이 있습니다.) Stellar은 내장된 런타임 쿼리, 생성 로드, 특정 대상에서 합성 부하를 생성할 수 있는 기능 거래/두 번째 요율. Stellar은 다양한 기능을 지원하지만 주문장 및 자산 간 경로와 같은 거래 기능 결제 방식으로는 간편결제에 중점을 두었습니다. 거래 확인은 여러 단계로 구성되어 있으므로 다음 각각에 대한 측정값을 기록했습니다. • 추천: 추천부터 첫 준비까지의 시간 • 투표: 처음 준비부터 확인까지의 시간 투표용지가 확정됨 • 원장 업데이트: 합의 가치를 적용하는 시간 • 거래수: 원장별 확인된 거래 각 실험은 세 가지 매개변수로 정의되었습니다. 원장의 계정 항목 수, 금액 초당 제출된 로드(XLM 결제 형식), 그리고 validator의 수. 우리는 validator마다 구성했습니다. 다른 모든 validator에 대해 알고 싶습니다(최악의 시나리오) SCP의 경우) 쿼럼 슬라이스는 단순 과반수로 설정됩니다. 노드(다양한 쿼럼 수를 최대화하기 위해). 기준선 기본 실험에서는 Stellar을(를) 측정했습니다. 100,000개의 계정, 4개의 validator 및 로드 생성 초당 100건의 트랜잭션 속도. 우리는 원장당 평균 507건의 거래를 관찰했으며 표준편차는 49입니다. (9.7%). 삭제된 트랜잭션은 없습니다. 경미한 105 106 107 0 500 1,000 1,500 2,000 계정 지연 시간 [ms] 원장 업데이트 투표 지명 그림 9. 계정 수 증가에 따른 지연 시간 변동은 부하 생성기의 일정 제한으로 인해 발생합니다. 우리는 원장당 거래 수를 관찰했습니다. 원장을 고려하면 로드 생성 속도와 일치했습니다. 5초마다 닫힙니다. 지명, 투표 및 장부 업데이트에서는 평균 대기 시간이 82.53ms, 95.96ms로 나타났습니다. 각각 174.08ms입니다. 우리는 지명 지연 시간을 관찰했습니다. 99번째 백분위수는 지속적으로 61ms 미만입니다. 첫 번째 단계에 해당하는 약 1초의 스파이크 리더 선택의 타임아웃 기능. 기본 성능을 고려하여 효과를 살펴보았습니다. 각 테스트 설정 매개변수를 변경하는 것입니다. 계정 그림 9의 데이터는 Stellar이 확장됨을 시사합니다. 그리고 계정수도 늘어납니다. 테스트 생성 버킷 생성 및 병합으로 인해 단순히 데이터베이스를 채우는 것이 불가능해졌습니다. SQL을 통해 직접 계정을 사용합니다. 따라서 우리는 최대 50,000,000개의 계정에 대한 실험을 수행할 수 있습니다. 있는 동안 합의 및 원장 업데이트 지연 시간에 미치는 영향을 최소화합니다. 계정을 늘리면 다음과 같은 오버헤드가 발생합니다. 버킷을 병합하면 더 커집니다. 거래율 거래율은 금액에 영향을 미칩니다. validator 간의 트래픽 멀티캐스트, 각 원장에 포함된 트랜잭션 수, 최상위 수준의 크기 버킷. 거래 증가의 효과를 이해하려면 로드 후 100,000개의 계정과 4개의 validator을 사용하여 실험을 실행했습니다. 그림 10은 합의 지연 시간의 느린 증가를 보여줍니다. 대부분의 시간은 원장을 업데이트하는 데 소비되었습니다. 당연히 트랜잭션 세트의 크기가 증가함에 따라 데이터베이스에 커밋하는 데 시간이 더 걸립니다. 우리는 또한 원장 업데이트 지연 시간은 구현에 따라 크게 달라집니다. 데이터베이스 선택에 영향을 받습니다. 검증인 노드 Tierone validators의 수가 어떻게 증가하는지 확인하려면성능에 영향을 미치므로 실험을 진행했습니다. 100,000개의 계정, 100개의 트랜잭션/초 및 4에서 43까지 다양한 수의 validator이 있습니다. 모든 validator이 나타났습니다. 모든 validators의 쿼럼 슬라이스에서; 더 작은 쿼럼 슬라이스는 성능에 미치는 영향이 적습니다.SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌 Lokhavaet al. 100 150 200 250 300 350 0 500 1,000 1,500 2,000 로드 [트랜잭션/초] 지연 시간 [ms] 원장 업데이트 투표 지명 그림 10. 트랜잭션 로드 증가에 따른 지연 시간 10 20 30 40 0 500 1,000 1,500 2,000 검증인 지연 시간 [ms] 원장 업데이트 투표 지명 그림 11. 노드 수가 증가함에 따른 지연 시간 네트워크의 검증 노드 수 변경 교환된 SCP 메시지 수에도 영향을 미칩니다. 지명 중 잠재적 가치의 수. 그림 11 지명 시간이 상대적으로 작은 비율로 증가하는 것을 보여줍니다. 데이터에 따르면 투표가 병목 현상을 일으키는 것으로 나타났습니다. 개선을 통해 많은 확장 문제를 해결할 수 있다고 믿습니다. Stellar의 오버레이 네트워크는 네트워크 트래픽을 최적화합니다. 다음과 같이 예상대로 원장 업데이트 지연 시간은 노드 수. 마감율 마지막으로 원장이 확인되는 빈도와 Stellar이 5초 목표를 달성하는지 여부를 측정하여 Stellar의 엔드투엔드 성능을 측정하고 싶었습니다. 모든 거래를 삭제합니다. 우리는 평균 원장 마감을 관찰했습니다. 계정을 늘리면 5.03초, 5.10초, 5.15초가 됩니다. 각각 항목, 트랜잭션 속도 및 노드 수입니다. 결과는 Stellar이 지속적으로 원장을 마감할 수 있음을 시사합니다. 높은 부하에서. 7.4 validator 실행 Stellar의 중요한 특징 중 하나는 저렴한 비용입니다. 앵커가 실행(또는 계약)되어야 하므로 validator을 실행합니다. validators를 사용하여 최종성을 강화합니다. SDF는 2개의 코어가 있는 c5.large AWS 인스턴스에서 3개의 프로덕션 validator을 실행합니다. 4GiB RAM 및 Intel(R) Xeon(R) Platinum 8124M CPU @ 3.00GHz 프로세서. 하나의 리소스 사용량 검사 이 기계 중 우리는 다음을 사용하여 Stellar 프로세스를 관찰했습니다. CPU는 약 7%, 메모리는 300MiB입니다. 네트워크 트래픽 측면에서 피어에 대한 연결이 28개이고 쿼럼 크기가 있습니다. 34개 중 수신 및 발신 속도는 2.78Mbit/s였으며 각각 2.56Mbit/s입니다. 이러한 실행에 필요한 하드웨어 프로세스가 저렴합니다. 우리의 경우 비용은 $0.054/시간입니다. 또는 월 $40 정도입니다. 7.5 미래의 일 이러한 실험은 Stellar이 쉽게 1~2개 주문을 확장할 수 있음을 시사합니다. 오늘날의 네트워크 사용량을 넘어서는 규모입니다. 왜냐하면 현재까지 성능 요구 사항은 너무 적었습니다. Stellar 다음을 사용하여 많은 간단한 최적화를 위한 여지를 남겨둡니다. 잘 알려진 기술. 예를 들어 트랜잭션과 SCP 메시지는 순진한 플러딩을 사용하여 validators에 의해 방송됩니다. 하지만 이상적으로는 보다 효율적이고 구조화된 프로토콜을 사용해야 합니다. 피어 투 피어 멀티캐스트 [30]. 또한, 데이터베이스가 많이 사용되는 원장 업데이트 시간은 표준 일괄 처리 및 프리페치 기술을 통해 향상될 수 있습니다.
评估
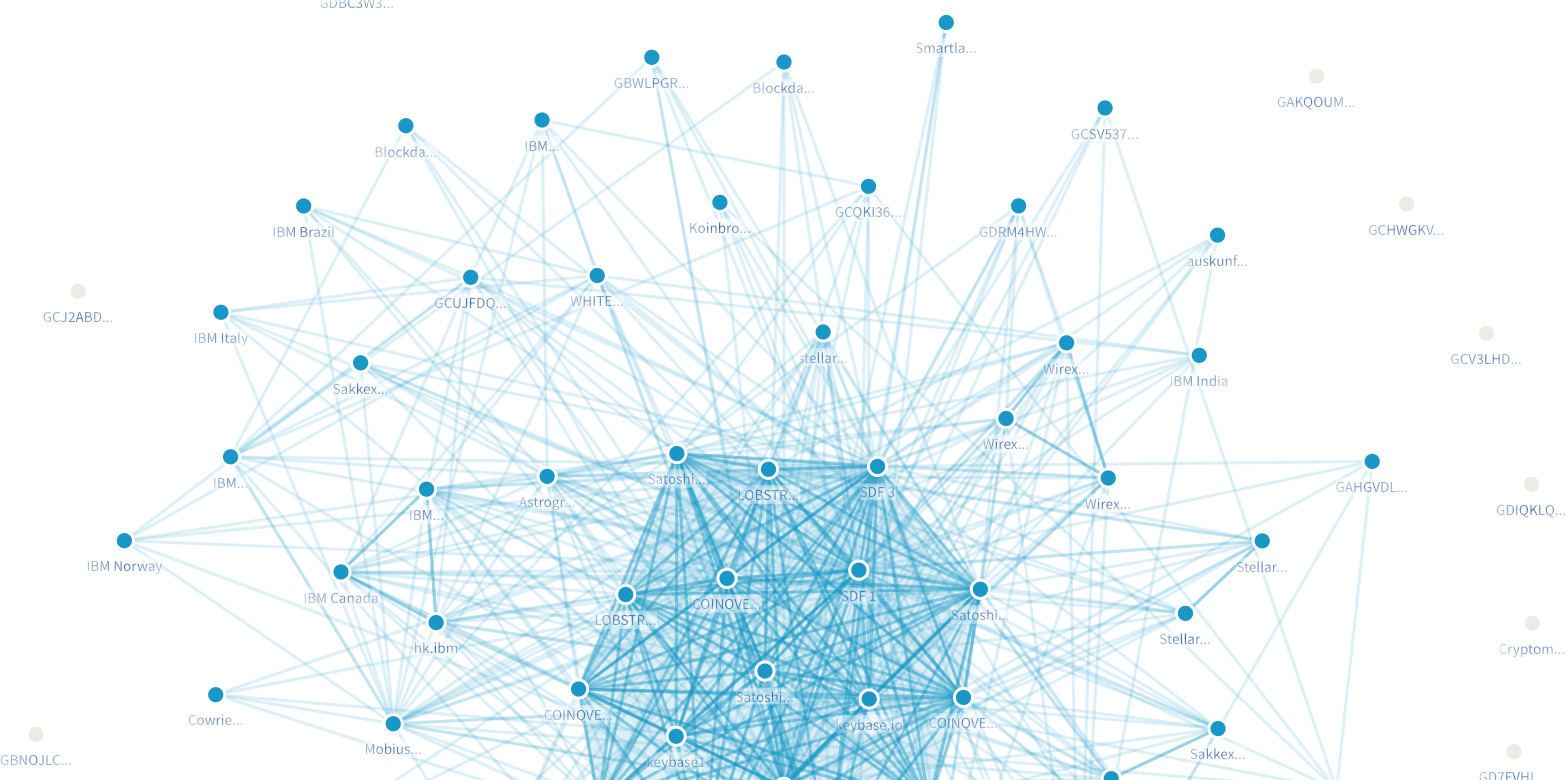
了解 Stellar 作为全球支付的适用性和 交易网络,我们评估了公共网络的状态 并在私人实验上进行了对照实验 网络。我们重点关注以下问题: • 生产网络拓扑是什么样的? 平均广播多少条消息,以及 SCP 如何经历超时? • 共识和账本更新延迟是否独立于账户数量?SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 洛哈瓦等人。 • 增加 (a) 每秒事务数(以及因此增加的每秒事务数)对延迟有何影响? (b) validator 节点的数量? • 运行一个节点的CPU 成本是多少? 内存和网络带宽? 相比之下,支付网络的交易率较低 到其他类型的分布式系统。领先的 blockchains, Bitcoin 和 Ethereum,确认每秒最多 15 笔交易, 小于 Stellar。此外,这些系统需要几分钟的时间 安全确认交易需要一个小时,因为工作量证明需要等待几个区块被开采。的 非blockchain SWIFT 网络在高峰日[14] 平均每秒仅处理420 笔交易。因此我们选择了 将我们的测量值与 5 秒目标进行比较 账本间隔,一个更激进的目标。我们的结果显示 即使在以下情况下,延迟也完全低于此限制 一些尚未实施的优化仍在进行中。 7.1 锚 按交易量排名前列的资产包括货币(例如 3 美元 锚点,2 元人民币)、一个 Bitcoin 锚点、一个房地产支持的证券 token [92] 和一个应用内货币 [8]。不同的主播有不同的政策。例如,一个美元锚, Stronghold,设置 auth_reqired 并要求每个持有其账户的账户都有一个了解你的客户 (KYC) 流程 资产。另一个,AnchorUSD,让任何人都可以接收和交易 他们的美元(实际上可以向墨西哥发送 0.50 美元) 5 秒内,费用为 0.000001 美元)。然而,AnchorUSD 购买或赎回美元确实需要 KYC 和费用 与传统的电汇。在菲律宾,哪里 银行对收款的监管较为宽松,coins.ph 支持在任何 ATM 机 [36] 上提取 PHP 现金。除了前面提到的安全 token 和应用内货币之外,还有一系列非货币 token,范围从 商业债券 [22] 和碳信用额 [85, 96] 等等 深奥的资产,例如 token 激励协作 汽车收回[35]。 7.2 公网 截至撰写本文时,有 126 个活动全节点,其中 66 个 通过签署投票消息参与共识。图7 (由 [5] 生成)可视化网络,中间有一条线 两个节点,如果一个出现在另一个节点的仲裁切片中,并且 深蓝色线表示双向依赖性。在 该中心是由 17 个事实上的“一级 validator”组成的集群,由 SDF、SatoshiPay、LOBSTR、COINQVEST 和 Keybase。 四个月前,在第六节事件发生之前,有 共有 15 个具有系统重要性的节点:3 个看似 一级组织和几个随机的单身人士。的 图表看起来也不太规则。因此,新的配置机制和/或更好的操作员决策似乎 为更健康的网络拓扑做出贡献。没有 雄厚的财力(及相应股东 图 7. 仲裁切片图 义务),招募 5 名一级人员是很困难的 然而,从一开始就组织。这表明法定人数 切片在网络引导中发挥着有用的作用:任何人都可以 加入的目标是成为重要的参与者,因为 成对协议没有看门人。 目前账本上有超过 330 万个账户。结束 最近 24 小时内,Stellar 平均有 4.5 笔交易, 每秒 15.7 次操作。回顾最近的账本,大多数 交易似乎只有一个操作,而每隔几个 在分类账中,我们看到包含许多操作的交易 似乎来自管理报价的做市商。的 达成共识和更新账本的平均时间是 分别为 1061 毫秒和 46 毫秒。第 99 个百分位数是 2252 毫秒和 142 毫秒(前者反映 1 秒超时 提名领导者的选择)。注意 SCP 的性能是 基本上与每秒交易无关,因为 SCP 就任意多笔交易的 hash 达成一致。瓶颈更有可能来自宣传候选人 提名、执行和验证期间的交易 事务和合并桶。我们还没有需要 在多个 CPU 核心或磁盘驱动器上并行 stellar-core 的事务处理。 我们还评估了 SCP 消息广播的数量 在生产网络上。在正常情况下,有一个 领导者选出提名一个值,我们期望七个逻辑 要广播的消息:两个要投票和接受的消息 阿诺米nate声明,两条消息接受和确认 一个准备声明,两条接受和确认消息 提交语句,最后是外部化消息 (在将新账本提交到磁盘后发送,以帮助落后者 赶上)。该实现结合了确认提交 并将消息外部化作为优化,因为它是 提交值后可以安全地将其外部化。然后,我们分析在生产 Stellar validator 上收集的指标。结束 在 68 小时的过程中,每秒发出 1.3 条消息, 每个分类账平均有 6-7 条消息。我们注意到,总计
使用 Stellar 进行快速、安全的全球支付 SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 百分位数 超时次数 提名 投票 75% 0 0 99% 1 0 最大 4 1 图 8. 68 小时内每个账本的超时 validators 广播的消息数量更大,因为 除了联合投票消息外,节点还广播 他们了解到的任何交易。 图 8 显示了生产环境所经历的超时 validator 超过 68 小时。提名超时是 衡量领导者选举功能有效性(无效)的指标,而投票超时在很大程度上取决于网络 以及潜在的消息延迟。超时是一致的 发出的消息数量: 6 条消息 最好的情况,以及如果需要额外的提名轮至少七条消息。 7.3 对照实验 我们在装满的容器中进行了对照实验 具有 72 GiB RAM 的 Amazon EC2 c5d.9xlarge 实例, 900 GB NVMe SSD 和 36 个 vCPU。每个实例都位于 相同的 EC2 区域并具有 10 Gbps 的固定带宽。 我们使用 SQLite 作为存储。 (Stellar 还支持 PostgreSQL, 但它有异步任务,会向测量中注入噪声。) Stellar 提供内置的运行时查询、generateload、 允许在特定目标处生成合成负载 交易/二流。虽然 Stellar 支持各种 交易功能,例如订单簿和跨资产路径 支付方面,我们专注于简单支付。 确认交易由多个步骤组成,因此我们 记录以下各项的测量值: • 提名:从提名到第一次准备的时间 • 投票:从最初准备到确认的时间 已提交选票 • 账本更新:应用共识值的时间 • 交易计数:每个分类账已确认的交易 我们的每个实验都由三个参数定义: 分类账中的账户条目数、金额 每秒提交的负载(以 XLM 付款的形式), 以及 validator 的数量。我们配置了每个 validator 了解所有其他 validator (最坏的情况 对于 SCP),法定人数切片设置为任何简单多数 节点(以便最大化不同仲裁的数量)。 基线 我们的基线实验测量了 Stellar 100,000 个帐户、四个 validator 和负载生成 每秒 100 笔交易的速率。我们观察到每个账本平均有 507 笔交易,标准差为 49 (9.7%)。请注意,没有交易被丢弃;轻微的 105 106 107 0 500 1,000 1,500 人 2,000 账户 延迟[毫秒] 账本更新 投票 提名 图 9. 帐户数量增加时的延迟 差异是由于负载生成器的调度限制造成的。我们观察到每个分类账的交易数量 与我们的负载生成率一致,给定分类帐 每 5 秒关闭一次。提名、投票和分类账 更新显示平均延迟分别为 82.53 毫秒、95.96 毫秒和 分别为 174.08 毫秒。我们观察到提名延迟 第 99 个百分位数始终低于 61 毫秒,偶尔有 大约 1 秒的峰值,对应于第一步 在leader选择的超时函数中。 考虑到基准性能,我们研究了效果 改变每个测试设置参数。 账户 图 9 中的数据表明 Stellar 具有扩展性 以及账户数量的增加。测试生成 帐户成为一个漫长的过程,因为存储桶创建和 合并阻止我们简单地填充数据库 直接通过 SQL 处理帐户。因此,我们进行了 最多可对 50,000,000 个帐户进行实验。虽然有 对共识和账本更新延迟的影响最小, 我们注意到,增加帐户会产生以下开销 合并桶,变得更大。 交易率 交易率影响金额 validator之间的流量多播,每个账本包含的交易数量,以及顶层的大小 桶。了解增加交易的影响 负载,我们用 100,000 个帐户和 4 个 validator 进行了实验。 图 10 显示了共识延迟的缓慢增长, 而大部分时间都花在更新账本上。 毫不奇怪,随着交易集规模的增加, 将其提交到数据库需要更长的时间。我们还注意到 账本更新延迟在很大程度上取决于实现, 并且受到数据库选择的影响。 验证节点 查看如何增加 tierone validator 的数量影响性能,我们进行了实验 有 100,000 个账户,每秒 100 笔交易,validator 的数量从 4 到 43 不等。所有 validator 都出现了 在所有 validators 的仲裁切片中;较小的仲裁片会 对性能的影响较小。SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔 洛哈瓦等人。 100 150 200 250 300 350 0 500 1,000 1,500 人 2,000 负载[事务/秒] 延迟[毫秒] 账本更新 投票 提名 图 10. 事务负载增加时的延迟 10 20 30 40 0 500 1,000 1,500 人 2,000 验证者 延迟[毫秒] 账本更新 投票 提名 图 11. 节点数量增加时的延迟 更改网络上验证节点的数量 影响交换的 SCP 消息的数量以及 提名期间潜在值的数量。图11 显示提名时间以相对较小的速度增长。 虽然数据表明投票是瓶颈,但我们 相信许多扩展问题可以通过改进来解决 Stellar 的覆盖网络以优化网络流量。作为 预计,账本更新延迟仍然独立于 节点数量。 成交率 最后,我们希望通过测量账本的确认频率以及 Stellar 是否达到其 5 秒目标来衡量 Stellar 的端到端性能。 放弃任何交易。我们观察到平均账本关闭 当我们增加账户时,时间为 5.03 s、5.10 s 和 5.15 s 分别是条目数、交易率和节点数。 结果表明 Stellar 可以持续关闭账本 高负载下。 7.4 运行 validator Stellar 的重要特征之一是低成本 运行 validator,因为锚应该运行(或与之签约) validators 强制确定性。 SDF 运行 3 个生产 validator,全部在 c5.large AWS 实例上,该实例有两个核心, 4 GiB RAM 和 Intel(R) Xeon(R) Platinum 8124M CPU @ 3.00GHz 处理器。检查其中一台的资源使用情况 在这些机器中,我们使用以下命令观察了 Stellar 进程 大约 7% 的 CPU 和 300 MiB 内存。就网络流量而言,与对等点的连接数为 28 个,法定人数大小 34条中,进出速率为2.78Mbit/s, 分别为 2.56 Mbit/s。运行此类程序所需的硬件 过程成本低廉。在我们的例子中,成本为 0.054 美元/小时 或约 40 美元/月。 7.5 未来的工作 这些实验表明 Stellar 可以轻松扩展 1-2 个订单 其规模超出了当今的网络使用量。因为 迄今为止,性能要求非常有限,Stellar 为许多直接优化留下了空间 众所周知的技术。例如,交易和 SCP validators 使用简单的洪泛方式广播消息 协议,但理想情况下应该使用更高效、结构化的 点对点多播 [30]。此外,数据库密集型 可以通过标准批处理和预取技术来缩短账本更新时间。
결론
국제 결제는 비용이 많이 들고 며칠이 걸립니다. 기금 보관은 환은행 및 송금 서비스를 포함한 여러 금융 기관을 통해 이루어집니다. 각 홉은 완전히 신뢰되어야 하기 때문에 새로운 홉은 어렵습니다. 시장점유율을 확보하고 경쟁하기 위한 진입자. Stellar 쇼 단 몇 초 만에 전 세계로 저렴하게 송금하는 방법. 는 핵심 혁신은 P2P 구조를 활용하는 새로운 개방형 멤버십 비잔틴 계약 프로토콜인 SCP입니다. 금융 네트워크의 글로벌 합의를 달성하기 위해 새로운 인터넷 가설. SCP는 Stellar을 원자적으로 커밋하도록 허용합니다. 임의 참가자 간의 되돌릴 수 없는 거래 서로에 대해 모르거나 신뢰하지 않습니다. 이는 결과적으로 신규 진입자가 기존 시장과 동일한 시장에 접근할 수 있도록 보장합니다. 플레이어는 최상의 교환을 안전하게 받을 수 있습니다. 신뢰할 수 없는 시장 조성자로부터도 가격이 하락하고 극적으로 결제 지연 시간을 줄입니다. 감사의 말 Stellar는 이른 시간이 없었다면 지금의 모습은 없었을 것입니다. 조이스 김의 리더십이나 Scott Fleckenstein과 Bartek Nowotarski가 건물을 짓고 지평선 유지, Stellar SDK 및 기타 핵심 부분 Stellar 생태계의. Kolten Bergeron에게도 감사드립니다. 헨리 코리건-깁스, 캔디스 켈리, 카필 K. 제인, 보리스 레즈니코프, 제레미 루빈, 크리스티안 러더, 에릭 손더스, Torsten Stüber, Tomer Weller, 익명의 심사위원, 그리고 우리 목자 저스틴 셰리(Justine Sherry)가 도움이 되는 의견을 주었습니다. 이전 초안. 면책조항 이 출판물에 대한 Mazières 교수의 기여는 유급 컨설턴트로서 이루어졌으며 그의 일부는 아닙니다. 스탠포드 대학의 의무 또는 책임.
Stellar를 통한 빠르고 안전한 글로벌 결제 SOSP ’19, 2019년 10월 27~30일, 캐나다 온타리오주 헌츠빌
结论
国际付款费用昂贵且需要数天时间。基金 托管通过多个金融机构,包括代理银行和汇款服务机构。 因为每一跳都必须完全可信,所以新的很难 进入者获得市场份额并参与竞争。 Stellar 显示 如何在几秒钟内以低廉的价格向世界各地汇款。的 关键创新是新的开放成员拜占庭协议 SCP,它利用点对点结构 金融网络的融合,以达成全球共识 新颖的互联网假设。 SCP 让 Stellar 原子提交 任意参与者之间的不可逆交易 彼此不了解或不信任。这反过来又保证了新进入者能够进入与已建立的市场相同的市场 玩家,可以安全地获得最佳的可用交换 甚至来自不受信任的做市商的利率,并且戏剧性地 减少支付延迟。 致谢 如果没有早期的努力,Stellar 就不会成为今天的样子 乔伊斯·金 (Joyce Kim) 的领导或巨大贡献 斯科特·弗莱肯斯坦 (Scott Fleckenstein) 和巴特克·诺沃塔斯基 (Bartek Nowotarski) 在建筑和 维护地平线、Stellar SDK 和其他关键部分 Stellar 生态系统的一部分。我们还要感谢 Kolten Bergeron, 亨利·科里根-吉布斯、坎迪斯·凯利、卡皮尔·贾恩、鲍里斯 雷兹尼科夫、杰里米·鲁宾、克里斯蒂安·鲁德、埃里克·桑德斯、 Torsten Stüber、Tomer Weller、匿名审稿人以及 我们的牧羊人贾斯汀雪莉对 早期的草稿。 免责声明 Mazières 教授对本出版物的贡献是作为付费顾问,而不是他的工作的一部分 斯坦福大学的职责或责任。
使用 Stellar 进行快速、安全的全球支付 SOSP '19,2019 年 10 月 27-30 日,加拿大安大略省亨茨维尔