
CryptoNote v2.0
The paper presented here is the CryptoNote v2.0 whitepaper by Nicolas van Saberhagen (2013), which describes the cryptographic foundations that Monero is built upon. It is not a Monero-specific whitepaper — Monero launched in 2014 as a fork of the CryptoNote reference implementation (Bytecoin) and has since evolved significantly beyond the original protocol.
Introduction
Introduction
"Bitcoin" [1] has been a successful implementation of the concept of p2p electronic cash. Both professionals and the general public have come to appreciate the convenient combination of public transactions and proof-of-work as a trust model. Today, the user base of electronic cash is growing at a steady pace; customers are attracted to low fees and the anonymity provided by electronic cash and merchants value its predicted and decentralized emission. Bitcoin has effectively proved that electronic cash can be as simple as paper money and as convenient as credit cards. Unfortunately, Bitcoin suffers from several deficiencies. For example, the system's distributed nature is inflexible, preventing the implementation of new features until almost all of the network users update their clients. Some critical flaws that cannot be fixed rapidly deter Bitcoin's widespread propagation. In such inflexible models, it is more efficient to roll-out a new project rather than perpetually fix the original project. In this paper, we study and propose solutions to the main deficiencies of Bitcoin. We believe that a system taking into account the solutions we propose will lead to a healthy competition among different electronic cash systems. We also propose our own electronic cash, "CryptoNote", a name emphasizing the next breakthrough in electronic cash.
介绍
“Bitcoin”[1]已经成功实现了p2p电子现金的概念。两者都 专业人士和公众已经开始欣赏这种便捷的组合 公共交易和 proof-of-work 作为信任模型。如今,电子现金的用户群 正在稳步增长;客户被低廉的费用和提供的匿名性所吸引 电子现金和商家对其预测和分散的排放进行评估。 Bitcoin 有 有效证明电子现金可以像纸币一样简单、像纸币一样方便 信用卡。 不幸的是,Bitcoin 有几个缺陷。例如,系统的分布式 本质上是不灵活的,在几乎所有网络用户更新其客户端之前,都会阻止新功能的实现。一些无法快速修复的关键缺陷阻碍了 Bitcoin 广泛传播。在这种不灵活的模式中,推出新项目会更有效率 而不是永久修复原来的项目。 在本文中,我们研究了Bitcoin的主要缺陷并提出了解决方案。我们相信 考虑到我们提出的解决方案的系统将带来良性竞争 不同的电子现金系统之间。我们还提出了我们自己的电子现金“CryptoNote”, 这个名字强调了电子现金的下一个突破。
Bitcoin Drawbacks and Possible Solutions
Bitcoin Drawbacks and Possible Solutions
2 Bitcoin drawbacks and some possible solutions 2.1 Traceability of transactions Privacy and anonymity are the most important aspects of electronic cash. Peer-to-peer payments seek to be concealed from third party’s view, a distinct difference when compared with traditional banking. In particular, T. Okamoto and K. Ohta described six criteria of ideal electronic cash, which included “privacy: relationship between the user and his purchases must be untraceable by anyone” [30]. From their description, we derived two properties which a fully anonymous electronic cash model must satisfy in order to comply with the requirements outlined by Okamoto and Ohta: Untraceability: for each incoming transaction all possible senders are equiprobable. Unlinkability: for any two outgoing transactions it is impossible to prove they were sent to the same person. Unfortunately, Bitcoin does not satisfy the untraceability requirement. Since all the transactions that take place between the network’s participants are public, any transaction can be 1 CryptoNote v 2.0 Nicolas van Saberhagen October 17, 2013 1 Introduction “Bitcoin” [1] has been a successful implementation of the concept of p2p electronic cash. Both professionals and the general public have come to appreciate the convenient combination of public transactions and proof-of-work as a trust model. Today, the user base of electronic cash is growing at a steady pace; customers are attracted to low fees and the anonymity provided by electronic cash and merchants value its predicted and decentralized emission. Bitcoin has effectively proved that electronic cash can be as simple as paper money and as convenient as credit cards. Unfortunately, Bitcoin suffers from several deficiencies. For example, the system’s distributed nature is inflexible, preventing the implementation of new features until almost all of the network users update their clients. Some critical flaws that cannot be fixed rapidly deter Bitcoin’s widespread propagation. In such inflexible models, it is more efficient to roll-out a new project rather than perpetually fix the original project. In this paper, we study and propose solutions to the main deficiencies of Bitcoin. We believe that a system taking into account the solutions we propose will lead to a healthy competition among different electronic cash systems. We also propose our own electronic cash, “CryptoNote”, a name emphasizing the next breakthrough in electronic cash. 2 Bitcoin drawbacks and some possible solutions 2.1 Traceability of transactions Privacy and anonymity are the most important aspects of electronic cash. Peer-to-peer payments seek to be concealed from third party’s view, a distinct difference when compared with traditional banking. In particular, T. Okamoto and K. Ohta described six criteria of ideal electronic cash, which included “privacy: relationship between the user and his purchases must be untraceable by anyone” [30]. From their description, we derived two properties which a fully anonymous electronic cash model must satisfy in order to comply with the requirements outlined by Okamoto and Ohta: Untraceability: for each incoming transaction all possible senders are equiprobable. Unlinkability: for any two outgoing transactions it is impossible to prove they were sent to the same person. Unfortunately, Bitcoin does not satisfy the untraceability requirement. Since all the transactions that take place between the network’s participants are public, any transaction can be 1 3 Bitcoin definitely fails "untraceability." When I send you BTC, the wallet from which it is sent is irrevocably stamped on the blockchain. There is no question about who sent those funds, because only the knower of the private keys can send them.
unambiguously traced to a unique origin and final recipient. Even if two participants exchange funds in an indirect way, a properly engineered path-finding method will reveal the origin and final recipient. It is also suspected that Bitcoin does not satisfy the second property. Some researchers stated ([33, 35, 29, 31]) that a careful blockchain analysis may reveal a connection between the users of the Bitcoin network and their transactions. Although a number of methods are disputed [25], it is suspected that a lot of hidden personal information can be extracted from the public database. Bitcoin’s failure to satisfy the two properties outlined above leads us to conclude that it is not an anonymous but a pseudo-anonymous electronic cash system. Users were quick to develop solutions to circumvent this shortcoming. Two direct solutions were “laundering services” [2] and the development of distributed methods [3, 4]. Both solutions are based on the idea of mixing several public transactions and sending them through some intermediary address; which in turn suffers the drawback of requiring a trusted third party. Recently, a more creative scheme was proposed by I. Miers et al. [28]: “Zerocoin”. Zerocoin utilizes a cryptographic one-way accumulators and zero-knoweldge proofs which permit users to “convert” bitcoins to zerocoins and spend them using anonymous proof of ownership instead of explicit public-key based digital signatures. However, such knowledge proofs have a constant but inconvenient size - about 30kb (based on today’s Bitcoin limits), which makes the proposal impractical. Authors admit that the protocol is unlikely to ever be accepted by the majority of Bitcoin users [5]. 2.2 The proof-of-work function Bitcoin creator Satoshi Nakamoto described the majority decision making algorithm as “oneCPU-one-vote” and used a CPU-bound pricing function (double SHA-256) for his proof-of-work scheme. Since users vote for the single history of transactions order [1], the reasonableness and consistency of this process are critical conditions for the whole system. The security of this model suffers from two drawbacks. First, it requires 51% of the network’s mining power to be under the control of honest users. Secondly, the system’s progress (bug fixes, security fixes, etc...) require the overwhelming majority of users to support and agree to the changes (this occurs when the users update their wallet software) [6].Finally this same voting mechanism is also used for collective polls about implementation of some features [7]. This permits us to conjecture the properties that must be satisfied by the proof-of-work pricing function. Such function must not enable a network participant to have a significant advantage over another participant; it requires a parity between common hardware and high cost of custom devices. From recent examples [8], we can see that the SHA-256 function used in the Bitcoin architecture does not posses this property as mining becomes more efficient on GPUs and ASIC devices when compared to high-end CPUs. Therefore, Bitcoin creates favourable conditions for a large gap between the voting power of participants as it violates the “one-CPU-one-vote” principle since GPU and ASIC owners posses a much larger voting power when compared with CPU owners. It is a classical example of the Pareto principle where 20% of a system’s participants control more than 80% of the votes. One could argue that such inequality is not relevant to the network’s security since it is not the small number of participants controlling the majority of the votes but the honesty of these participants that matters. However, such argument is somewhat flawed since it is rather the possibility of cheap specialized hardware appearing rather than the participants’ honesty which poses a threat. To demonstrate this, let us take the following example. Suppose a malevolent individual gains significant mining power by creating his own mining farm through the cheap 2 unambiguously traced to a unique origin and final recipient. Even if two participants exchange funds in an indirect way, a properly engineered path-finding method will reveal the origin and final recipient. It is also suspected that Bitcoin does not satisfy the second property. Some researchers stated ([33, 35, 29, 31]) that a careful blockchain analysis may reveal a connection between the users of the Bitcoin network and their transactions. Although a number of methods are disputed [25], it is suspected that a lot of hidden personal information can be extracted from the public database. Bitcoin’s failure to satisfy the two properties outlined above leads us to conclude that it is not an anonymous but a pseudo-anonymous electronic cash system. Users were quick to develop solutions to circumvent this shortcoming. Two direct solutions were “laundering services” [2] and the development of distributed methods [3, 4]. Both solutions are based on the idea of mixing several public transactions and sending them through some intermediary address; which in turn suffers the drawback of requiring a trusted third party. Recently, a more creative scheme was proposed by I. Miers et al. [28]: “Zerocoin”. Zerocoin utilizes a cryptographic one-way accumulators and zero-knoweldge proofs which permit users to “convert” bitcoins to zerocoins and spend them using anonymous proof of ownership instead of explicit public-key based digital signatures. However, such knowledge proofs have a constant but inconvenient size - about 30kb (based on today’s Bitcoin limits), which makes the proposal impractical. Authors admit that the protocol is unlikely to ever be accepted by the majority of Bitcoin users [5]. 2.2 The proof-of-work function Bitcoin creator Satoshi Nakamoto described the majority decision making algorithm as “oneCPU-one-vote” and used a CPU-bound pricing function (double SHA-256) for his proof-of-work scheme. Since users vote for the single history of transactions order [1], the reasonableness and consistency of this process are critical conditions for the whole system. The security of this model suffers from two drawbacks. First, it requires 51% of the network’s mining power to be under the control of honest users. Secondly, the system’s progress (bug fixes, security fixes, etc...) require the overwhelming majority of users to support and agree to the changes (this occurs when the users update their wallet software) [6].Finally this same voting mechanism is also used for collective polls about implementation of some features [7]. This permits us to conjecture the properties that must be satisfied by the proof-of-work pricing function. Such function must not enable a network participant to have a significant advantage over another participant; it requires a parity between common hardware and high cost of custom devices. From recent examples [8], we can see that the SHA-256 function used in the Bitcoin architecture does not posses this property as mining becomes more efficient on GPUs and ASIC devices when compared to high-end CPUs. Therefore, Bitcoin creates favourable conditions for a large gap between the voting power of participants as it violates the “one-CPU-one-vote” principle since GPU and ASIC owners posses a much larger voting power when compared with CPU owners. It is a classical example of the Pareto principle where 20% of a system’s participants control more than 80% of the votes. One could argue that such inequality is not relevant to the network’s security since it is not the small number of participants controlling the majority of the votes but the honesty of these participants that matters. However, such argument is somewhat flawed since it is rather the possibility of cheap specialized hardware appearing rather than the participants’ honesty which poses a threat. To demonstrate this, let us take the following example. Suppose a malevolent individual gains significant mining power by creating his own mining farm through the cheap 2 4 Presumably, if every user helps their own anonymity out by always generating a new address for EVERY received payment (which is absurd but technically the "correct" way to do it), and if every user helped out everyone else’s anonymity by insisting that they never send funds to the same BTC address twice, then Bitcoin would still only circumstantially pass the unlinkability test. Why? Consumer data can be used to figure an astonishing amount about people all the time. See, for example http://www.applieddatalabs.com/content/target-knows-it-shows Now, imagine this is 20 years in the future and further imagine that Target didn’t just know about your purchase habits at Target, but they had been mining the blockchain for ALL OF YOUR PERSONAL PURCHASES WITH YOUR COINBASE WALLET FOR THE PAST TWELVE YEARS. They’ll be like "hey buddy you might want to pick up some cough medicine tonight, you won’t feel well tomorrow." This may not be the case if multi-party sorting is exploited correctly. See, for example, this blog post: http://blog.ezyang.com/2012/07/secure-multiparty-bitcoin-anonymization/ I’m not totally convinced of the math on that, but ... one paper at a time, right? Citation needed. Whereas the Zerocoin protocol (standalone) may be insufficient, the Zerocash protocol seems to have implemented a 1kb sized transactions. That project is supported by the US and Israeli militaries, of course, so who knows about it’s robustness. On the other hand, no one wants to be able to spend funds without oversight more than the military. http://zerocash-project.org/ I’m not convinced... see, for example, http://fc14.ifca.ai/bitcoin/papers/bitcoin14_submission_12.pdf Quoting a Cryptonote developer Maurice Planck (presumably a pseudonym) from the cryptonote fora: "Zerocoin, Zerocash. This is the most advanced technology, I must admit. Yes, the quote above is from the analysis of the previous version of the protocol. To my knowledge, it’s not 288, but 384 bytes, but anyway this is good news. They used a brand new technic called SNARK, which has certain downsides: for example, large initial database of public parameters required to create a signature (more than 1 GB) and significant time required to create a transaction (more than a minute). Finally, they’re using a young crypto, which I’ve mentioned to be an arguable idea: https://forum.cryptonote.org/viewtopic.php?f= " - Maurice P. Thu Apr 03, 2014 7:56 pm A function that is performed in the CPU and is not suitable for GPU, FPGA, or ASIC computation. The "puzzle" used in proof-of-work is referred to as the pricing function, cost function, or puzzle function.
unambiguously traced to a unique origin and final recipient. Even if two participants exchange funds in an indirect way, a properly engineered path-finding method will reveal the origin and final recipient. It is also suspected that Bitcoin does not satisfy the second property. Some researchers stated ([33, 35, 29, 31]) that a careful blockchain analysis may reveal a connection between the users of the Bitcoin network and their transactions. Although a number of methods are disputed [25], it is suspected that a lot of hidden personal information can be extracted from the public database. Bitcoin’s failure to satisfy the two properties outlined above leads us to conclude that it is not an anonymous but a pseudo-anonymous electronic cash system. Users were quick to develop solutions to circumvent this shortcoming. Two direct solutions were “laundering services” [2] and the development of distributed methods [3, 4]. Both solutions are based on the idea of mixing several public transactions and sending them through some intermediary address; which in turn suffers the drawback of requiring a trusted third party. Recently, a more creative scheme was proposed by I. Miers et al. [28]: “Zerocoin”. Zerocoin utilizes a cryptographic one-way accumulators and zero-knoweldge proofs which permit users to “convert” bitcoins to zerocoins and spend them using anonymous proof of ownership instead of explicit public-key based digital signatures. However, such knowledge proofs have a constant but inconvenient size - about 30kb (based on today’s Bitcoin limits), which makes the proposal impractical. Authors admit that the protocol is unlikely to ever be accepted by the majority of Bitcoin users [5]. 2.2 The proof-of-work function Bitcoin creator Satoshi Nakamoto described the majority decision making algorithm as “oneCPU-one-vote” and used a CPU-bound pricing function (double SHA-256) for his proof-of-work scheme. Since users vote for the single history of transactions order [1], the reasonableness and consistency of this process are critical conditions for the whole system. The security of this model suffers from two drawbacks. First, it requires 51% of the network’s mining power to be under the control of honest users. Secondly, the system’s progress (bug fixes, security fixes, etc...) require the overwhelming majority of users to support and agree to the changes (this occurs when the users update their wallet software) [6].Finally this same voting mechanism is also used for collective polls about implementation of some features [7]. This permits us to conjecture the properties that must be satisfied by the proof-of-work pricing function. Such function must not enable a network participant to have a significant advantage over another participant; it requires a parity between common hardware and high cost of custom devices. From recent examples [8], we can see that the SHA-256 function used in the Bitcoin architecture does not posses this property as mining becomes more efficient on GPUs and ASIC devices when compared to high-end CPUs. Therefore, Bitcoin creates favourable conditions for a large gap between the voting power of participants as it violates the “one-CPU-one-vote” principle since GPU and ASIC owners posses a much larger voting power when compared with CPU owners. It is a classical example of the Pareto principle where 20% of a system’s participants control more than 80% of the votes. One could argue that such inequality is not relevant to the network’s security since it is not the small number of participants controlling the majority of the votes but the honesty of these participants that matters. However, such argument is somewhat flawed since it is rather the possibility of cheap specialized hardware appearing rather than the participants’ honesty which poses a threat. To demonstrate this, let us take the following example. Suppose a malevolent individual gains significant mining power by creating his own mining farm through the cheap 2 unambiguously traced to a unique origin and final recipient. Even if two participants exchange funds in an indirect way, a properly engineered path-finding method will reveal the origin and final recipient. It is also suspected that Bitcoin does not satisfy the second property. Some researchers stated ([33, 35, 29, 31]) that a careful blockchain analysis may reveal a connection between the users of the Bitcoin network and their transactions. Although a number of methods are disputed [25], it is suspected that a lot of hidden personal information can be extracted from the public database. Bitcoin’s failure to satisfy the two properties outlined above leads us to conclude that it is not an anonymous but a pseudo-anonymous electronic cash system. Users were quick to develop solutions to circumvent this shortcoming. Two direct solutions were “laundering services” [2] and the development of distributed methods [3, 4]. Both solutions are based on the idea of mixing several public transactions and sending them through some intermediary address; which in turn suffers the drawback of requiring a trusted third party. Recently, a more creative scheme was proposed by I. Miers et al. [28]: “Zerocoin”. Zerocoin utilizes a cryptographic one-way accumulators and zero-knoweldge proofs which permit users to “convert” bitcoins to zerocoins and spend them using anonymous proof of ownership instead of explicit public-key based digital signatures. However, such knowledge proofs have a constant but inconvenient size - about 30kb (based on today’s Bitcoin limits), which makes the proposal impractical. Authors admit that the protocol is unlikely to ever be accepted by the majority of Bitcoin users [5]. 2.2 The proof-of-work function Bitcoin creator Satoshi Nakamoto described the majority decision making algorithm as “oneCPU-one-vote” and used a CPU-bound pricing function (double SHA-256) for his proof-of-work scheme. Since users vote for the single history of transactions order [1], the reasonableness and consistency of this process are critical conditions for the whole system. The security of this model suffers from two drawbacks. First, it requires 51% of the network’s mining power to be under the control of honest users. Secondly, the system’s progress (bug fixes, security fixes, etc...) require the overwhelming majority of users to support and agree to the changes (this occurs when the users update their wallet software) [6].Finally this same voting mechanism is also used for collective polls about implementation of some features [7]. This permits us to conjecture the properties that must be satisfied by the proof-of-work pricing function. Such function must not enable a network participant to have a significant advantage over another participant; it requires a parity between common hardware and high cost of custom devices. From recent examples [8], we can see that the SHA-256 function used in the Bitcoin architecture does not posses this property as mining becomes more efficient on GPUs and ASIC devices when compared to high-end CPUs. Therefore, Bitcoin creates favourable conditions for a large gap between the voting power of participants as it violates the “one-CPU-one-vote” principle since GPU and ASIC owners posses a much larger voting power when compared with CPU owners. It is a classical example of the Pareto principle where 20% of a system’s participants control more than 80% of the votes. One could argue that such inequality is not relevant to the network’s security since it is not the small number of participants controlling the majority of the votes but the honesty of these participants that matters. However, such argument is somewhat flawed since it is rather the possibility of cheap specialized hardware appearing rather than the participants’ honesty which poses a threat. To demonstrate this, let us take the following example. Suppose a malevolent individual gains significant mining power by creating his own mining farm through the cheap 2 Comments on page 2
Bitcoin 缺点和可能的解决方案
2 Bitcoin 缺点和一些可能的解决方案 2.1 交易可追溯 隐私和匿名是电子现金最重要的方面。点对点支付 寻求隐藏在第三方的视野之外,与传统的相比有明显的区别 银行业务。特别是,T. Okamoto 和 K. Ohta 描述了理想电子现金的六个标准, 其中包括“隐私:用户及其购买之间的关系必须无法追踪 任何人”[30]。从他们的描述中,我们得出了两个完全匿名的属性 电子现金模型必须满足冈本概述的要求 和太田: 不可追踪性:对于每笔传入交易,所有可能的发件人都是等概率的。 不可链接性:对于任何两个传出交易,无法证明它们被发送到 同一个人。 不幸的是,Bitcoin 不满足不可追踪性要求。由于网络参与者之间发生的所有交易都是公开的,因此任何交易都可以 1 加密笔记 v 2.0 尼古拉斯 \(\cdot\) 范 \(\cdot\) 萨伯哈根 2013 年 10 月 17 日 1 简介 “Bitcoin”[1]已经成功实现了p2p电子现金的概念。两者都 专业人士和公众已经开始欣赏这种便捷的组合 公共交易和 proof-of-work 作为信任模型。如今,电子现金的用户群 正在稳步增长;客户被低廉的费用和提供的匿名性所吸引 电子现金和商家对其预测和分散的排放进行评估。 Bitcoin 有 有效证明电子现金可以像纸币一样简单、像纸币一样方便 信用卡。 不幸的是,Bitcoin 有几个缺陷。例如,系统的分布式 本质上是不灵活的,在几乎所有网络用户更新其客户端之前,都会阻止新功能的实现。一些无法快速修复的关键缺陷阻碍了 Bitcoin 广泛传播。在这种不灵活的模式中,推出新项目会更有效率 而不是永久修复原来的项目。 在本文中,我们研究并提出了针对 Bitcoin 的主要缺陷的解决方案。我们相信 考虑到我们提出的解决方案的系统将带来良性竞争 不同的电子现金系统之间。我们还提出了我们自己的电子现金“CryptoNote”, 这个名字强调了电子现金的下一个突破。 2 Bitcoin 缺点和一些可能的解决方案 2.1 交易可追溯 隐私和匿名是电子现金最重要的方面。点对点支付 寻求隐藏在第三方的视野之外,与传统的相比有明显的区别 银行业务。特别是,T. Okamoto 和 K. Ohta 描述了理想电子现金的六个标准, 其中包括“隐私:用户及其购买之间的关系必须无法追踪 任何人”[30]。从他们的描述中,我们得出了两个完全匿名的属性 电子现金模型必须满足冈本概述的要求 和太田: 不可追踪性:对于每笔传入交易,所有可能的发件人都是等概率的。 不可链接性:对于任何两个传出交易,无法证明它们被发送到 同一个人。 不幸的是,Bitcoin 不满足不可追踪性要求。由于网络参与者之间发生的所有交易都是公开的,因此任何交易都可以 1 3 Bitcoin 绝对无法实现“不可追踪性”。当我向您发送 BTC 时,发送该钱包的钱包 不可撤销地印在 blockchain 上。毫无疑问谁发送了这些资金, 因为只有知道私钥的人才能发送它们。明确追踪到独特的来源和最终接收者。即使两个参与者交换 如果以间接方式筹集资金,适当设计的寻路方法将揭示资金的来源和 最终收件人。 还怀疑Bitcoin不满足第二个性质。 一些研究人员 指出 ([33, 35, 29, 31]) 仔细的 blockchain 分析可能会揭示之间的联系 Bitcoin 网络的用户及其交易。虽然有很多方法 争议[25],疑似可从中提取大量隐藏个人信息 公共数据库。 Bitcoin 未能满足上述两个属性使我们得出结论: 不是匿名的而是伪匿名的电子现金系统。用户发展很快 解决方案来规避这个缺点。两个直接解决方案是“洗钱服务”[2] 和 分布式方法的发展 [3, 4]。两种解决方案都基于混合的想法 一些公共交易并通过某个中间地址发送它们;反过来 存在需要可信第三方的缺点。 最近,I. Miers等人提出了一个更有创意的方案。 [28]:“零币”。零币 利用加密单向累加器和零知识证明,允许用户 将比特币“转换”为零币并使用匿名所有权证明而不是使用它们 基于显式公钥的数字签名。然而,这样的知识证明有一个常数 但大小不方便 - 大约 30kb(基于今天的 Bitcoin 限制),这使得该提案 不切实际的。作者承认该协议不太可能被大多数人接受 Bitcoin 用户 [5]。 2.2 proof-of-work 函数 Bitcoin 的创建者中本聪将多数决策算法描述为“oneCPU-one-vote”,并为他的 proof-of-work 使用了受 CPU 限制的定价函数(双 SHA-256) 计划。由于用户对单笔历史交易订单[1]进行投票,合理性和 这个过程的一致性是整个系统的关键条件。 该模型的安全性有两个缺点。首先,它需要51%的网络资源 挖矿权由诚实用户控制。其次,系统的进展(错误修复, 安全修复等...)需要绝大多数用户支持并同意 更改(当用户更新钱包软件时会发生这种情况)[6]。最后同样的投票 该机制还用于关于某些功能 [7] 的实现的集体民意调查。 这使我们能够推测 proof-of-work 必须满足的属性 定价功能。 此类功能不得使网络参与者拥有重大的 相对于其他参与者的优势;它需要普通硬件和高端硬件之间的平衡 定制设备的成本。从最近的示例 [8] 中,我们可以看到使用了 SHA-256 函数 在 Bitcoin 架构中不具备此属性,因为采矿变得更加高效 GPU 和 ASIC 设备与高端 CPU 相比。 因此,Bitcoin为投票权之间的巨大差距创造了有利条件 参与者,因为它违反了“单 CPU 一票”原则,因为 GPU 和 ASIC 所有者拥有 与 CPU 所有者相比,投票权要大得多。这是一个经典的例子 帕累托原则,即系统中 20% 的参与者控制超过 80% 的选票。 有人可能会争辩说,这种不平等与网络安全无关,因为它不是 少数参与者控制着大多数选票,但这些参与者的诚实性 重要的参与者。然而,这样的论点是有一定缺陷的,因为它实际上是 廉价专用硬件出现的可能性,而不是参与者的诚实度 构成威胁。为了证明这一点,让我们看下面的例子。假设有一个恶意 个人通过廉价的方式创建自己的矿场,从而获得显着的挖矿能力 2 明确追踪到独特的来源和最终接收者。即使两个参与者交换 如果以间接方式筹集资金,适当设计的寻路方法将揭示资金的来源和 最终收件人。 还怀疑Bitcoin不满足第二个性质。 一些研究人员 指出 ([33, 35, 29, 31]) 仔细的 blockchain 分析可能会揭示之间的联系 Bitcoin 网络的用户及其交易。虽然有很多方法 d疑似[25],疑似可提取大量隐藏个人信息 公共数据库。 Bitcoin 未能满足上述两个属性使我们得出结论: 不是匿名的而是伪匿名的电子现金系统。用户发展很快 解决方案来规避这个缺点。两个直接解决方案是“洗钱服务”[2] 和 分布式方法的发展 [3, 4]。两种解决方案都基于混合的想法 一些公共交易并通过某个中间地址发送它们;反过来 存在需要可信第三方的缺点。 最近,I. Miers等人提出了一个更有创意的方案。 [28]:“零币”。零币 利用加密单向累加器和零知识证明,允许用户 将比特币“转换”为零币并使用匿名所有权证明而不是使用它们 基于显式公钥的数字签名。然而,这样的知识证明有一个常数 但大小不方便 - 大约 30kb(基于今天的 Bitcoin 限制),这使得该提案 不切实际的。作者承认该协议不太可能被大多数人接受 Bitcoin 用户 [5]。 2.2 proof-of-work 函数 Bitcoin 的创建者中本聪将多数决策算法描述为“oneCPU-one-vote”,并为他的 proof-of-work 使用了受 CPU 限制的定价函数(双 SHA-256) 计划。由于用户对单笔历史交易订单[1]进行投票,合理性和 这个过程的一致性是整个系统的关键条件。 该模型的安全性有两个缺点。首先,它需要51%的网络资源 挖矿权由诚实用户控制。其次,系统的进展(错误修复, 安全修复等...)需要绝大多数用户支持并同意 更改(当用户更新钱包软件时会发生这种情况)[6]。最后同样的投票 该机制还用于关于某些功能 [7] 的实现的集体民意调查。 这允许我们推测 proof-of-work 必须满足的属性 定价功能。 此类功能不得使网络参与者拥有重大的 相对于其他参与者的优势;它需要普通硬件和高端硬件之间的平衡 定制设备的成本。从最近的示例 [8] 中,我们可以看到使用了 SHA-256 函数 在 Bitcoin 架构中不具备此属性,因为采矿变得更加高效 GPU 和 ASIC 设备与高端 CPU 相比。 因此,Bitcoin为投票权之间的巨大差距创造了有利条件 参与者,因为它违反了“单 CPU 一票”原则,因为 GPU 和 ASIC 所有者拥有 与 CPU 所有者相比,投票权要大得多。这是一个经典的例子 帕累托原则,即系统中 20% 的参与者控制超过 80% 的选票。 有人可能会争辩说,这种不平等与网络安全无关,因为它不是 少数参与者控制着大多数选票,但这些参与者的诚实性 重要的参与者。然而,这样的论点是有一定缺陷的,因为它实际上是 廉价专用硬件出现的可能性,而不是参与者的诚实度 构成威胁。为了证明这一点,让我们看下面的例子。假设有一个恶意 个人通过廉价的方式创建自己的矿场,从而获得显着的挖矿能力 2 4 据推测,如果每个用户总是通过生成新地址来帮助自己匿名 对于每笔收到的付款(这是荒谬的,但从技术上讲是“正确”的方法), 如果每个用户都坚持不发送资金来帮助其他人匿名 两次发送到同一个 BTC 地址,那么 Bitcoin 仍然只能偶尔通过 不可链接性测试。 为什么?消费者数据始终可以用来了解数量惊人的人们。 例如,参见 http://www.applieddatalabs.com/content/target-knows-it-shows 现在,想象一下这是 20 年后的未来,并进一步想象塔吉特不仅知道 关于您在 Target 的购买习惯,但他们一直在挖掘 blockchain 的所有内容 您过去使用 Coinbase 钱包进行的个人购买 十二年。 他们会说“嘿伙计,你今晚可能想买点止咳药,但你不会 明天感觉很好。” 如果正确利用多方排序,情况可能并非如此。例如,参见这个博客文章:http://blog.ezyang.com/2012/07/secure-multiparty-bitcoin-anonymization/ 我并不完全相信这一点的数学原理,但是......一次一篇论文,对吧? 需要引用。尽管 Zerocoin 协议(独立)可能还不够,但 Zerocash 协议似乎已经实现了 1kb 大小的事务。该项目由以下机构支持 当然,美国和以色列军队,所以谁知道它的坚固性。另一方面 另一方面,没有人比军方更希望能够在没有监督的情况下使用资金。 http://zerocash-project.org/ 我不相信......例如,参见 http://fc14.ifca.ai/bitcoin/papers/bitcoin14_submission_12.pdf 引用 Cryptonote 开发者 Maurice Planck(大概是化名)的话 论坛: “零币,零现金。 我必须承认,这是最先进的技术。 是的,报价 以上是对上一版本协议的分析。据我所知,这不是 288,但是384字节,但无论如何这是个好消息。 他们使用了一种名为 SNARK 的全新技术,该技术有一定的缺点:例如, 创建签名所需的公共参数的大型初始数据库(超过 1 GB)以及 创建交易所需的大量时间(超过一分钟)。最后,他们使用的是 年轻的加密货币,我提到这是一个有争议的想法:https://forum.cryptonote.org/viewtopic.php?f= ” - Maurice P. 2014 年 4 月 3 日星期四晚上 7:56 在CPU中执行的功能,不适合GPU、FPGA或ASIC 计算。 proof-of-work 中使用的“难题”被称为定价函数、成本函数或 拼图功能。
明确追踪到独特的来源和最终接收者。即使两个参与者交换 如果以间接方式筹集资金,适当设计的寻路方法将揭示资金的来源和 最终收件人。 还怀疑Bitcoin不满足第二个性质。 一些研究人员 指出 ([33, 35, 29, 31]) 仔细的 blockchain 分析可能会揭示之间的联系 Bitcoin 网络的用户及其交易。虽然有很多方法 争议[25],疑似可从中提取大量隐藏个人信息 公共数据库。 Bitcoin 未能满足上述两个属性使我们得出结论: 不是匿名的而是伪匿名的电子现金系统。用户发展很快 解决方案来规避这个缺点。两个直接解决方案是“洗钱服务”[2] 和 分布式方法的发展 [3, 4]。两种解决方案都基于混合的想法 一些公共交易并通过某个中间地址发送它们;反过来 存在需要可信第三方的缺点。 最近,I. Miers等人提出了一个更有创意的方案。 [28]:“零币”。零币 利用加密单向累加器和零知识证明,允许用户 将比特币“转换”为零币并使用匿名所有权证明而不是使用它们 基于显式公钥的数字签名。然而,这样的知识证明有一个常数 但大小不方便 - 大约 30kb(基于今天的 Bitcoin 限制),这使得该提案 不切实际的。作者承认该协议不太可能被大多数人接受 Bitcoin 用户 [5]。 2.2 proof-of-work 函数 Bitcoin 创建者中本聪将多数决策算法描述为“oneCPU-one-vote”,并为他的 proof-of-work 使用了 CPU 限制的定价函数(双 SHA-256) 计划。由于用户对单笔历史交易订单[1]进行投票,合理性和 这个过程的一致性是整个系统的关键条件。 该模型的安全性有两个缺点。首先,它需要51%的网络资源 挖矿权由诚实用户控制。其次,系统的进展(错误修复, 安全修复等...)需要绝大多数用户支持并同意 更改(当用户更新钱包软件时会发生这种情况)[6]。最后同样的投票 该机制还用于关于某些功能 [7] 的实现的集体民意调查。 这使我们能够推测 proof-of-work 必须满足的属性 定价功能。 此类功能不得使网络参与者拥有重大的 相对于其他参与者的优势;它需要普通硬件和高端硬件之间的平衡 定制设备的成本。从最近的示例 [8] 中,我们可以看到使用了 SHA-256 函数 在 Bitcoin 架构中不具备此属性,因为采矿变得更加高效 GPU 和 ASIC 设备与高端 CPU 相比。 因此,Bitcoin为投票权之间的巨大差距创造了有利条件 参与者,因为它违反了“单 CPU 一票”原则,因为 GPU 和 ASIC 所有者拥有 与 CPU 所有者相比,投票权要大得多。这是一个经典的例子 帕累托原则,即系统中 20% 的参与者控制超过 80% 的选票。 有人可能会争辩说,这种不平等与网络安全无关,因为它不是 少数参与者控制着大多数选票,但这些参与者的诚实性 重要的参与者。然而,这样的论点是有一定缺陷的,因为它实际上是 廉价专用硬件出现的可能性,而不是参与者的诚实度 构成威胁。为了证明这一点,让我们看下面的例子。假设有一个恶意 个人通过廉价的方式创建自己的矿场,从而获得显着的挖矿能力 2 明确追踪到独特的来源和最终接收者。即使两个参与者交换 如果以间接方式筹集资金,适当设计的寻路方法将揭示资金的来源和 最终收件人。 还怀疑Bitcoin不满足第二个性质。 一些研究人员 指出 ([33, 35, 29, 31]) 仔细的 blockchain 分析可能会揭示之间的联系 Bitcoin 网络的用户及其交易。虽然有很多方法 d疑似[25],疑似可提取大量隐藏个人信息 公共数据库。 Bitcoin 未能满足上述两个属性使我们得出结论: 不是匿名的而是伪匿名的电子现金系统。用户发展很快 解决方案来规避这个缺点。两个直接解决方案是“洗钱服务”[2] 和 分布式方法的发展 [3, 4]。两种解决方案都基于混合的想法 一些公共交易并通过某个中间地址发送它们;反过来 存在需要可信第三方的缺点。 最近,I. Miers等人提出了一个更有创意的方案。 [28]:“零币”。零币 利用加密单向累加器和零知识证明,允许用户 将比特币“转换”为零币并使用匿名所有权证明而不是使用它们 基于显式公钥的数字签名。然而,这样的知识证明有一个常数 但大小不便 - 大约 30kb(基于今天的 Bitcoin 限制),这使得该提案 不切实际的。作者承认该协议不太可能被大多数人接受 Bitcoin 用户 [5]。 2.2 proof-of-work 函数 Bitcoin 创建者中本聪将多数决策算法描述为“oneCPU-one-vote”,并为他的 proof-of-work 使用了 CPU 限制的定价函数(双 SHA-256) 计划。由于用户对单笔历史交易订单[1]进行投票,合理性和 这个过程的一致性是整个系统的关键条件。 该模型的安全性有两个缺点。首先,它需要51%的网络资源 挖矿权由诚实用户控制。其次,系统的进展(错误修复, 安全修复等...)需要绝大多数用户支持并同意 更改(当用户更新钱包软件时会发生这种情况)[6]。最后同样的投票 该机制还用于关于某些功能 [7] 的实现的集体民意调查。 这允许我们推测 proof-of-work 必须满足的属性 定价功能。 此类功能不得使网络参与者拥有重大的 相对于其他参与者的优势;它需要普通硬件和高端硬件之间的平衡 定制设备的成本。从最近的示例 [8] 中,我们可以看到使用了 SHA-256 函数 在 Bitcoin 架构中不具备此属性,因为采矿变得更加高效 GPU 和 ASIC 设备与高端 CPU 相比。 因此,Bitcoin为投票权之间的巨大差距创造了有利条件 参与者,因为它违反了“单 CPU 一票”原则,因为 GPU 和 ASIC 所有者拥有 与 CPU 所有者相比,投票权要大得多。这是一个经典的例子 帕累托原则,即系统中 20% 的参与者控制超过 80% 的选票。 有人可能会争辩说,这种不平等与网络安全无关,因为它不是 少数参与者控制着大多数选票,但这些参与者的诚实性 重要的参与者。然而,这样的论点是有一定缺陷的,因为它实际上是 廉价专用硬件出现的可能性,而不是参与者的诚实度 构成威胁。为了证明这一点,让我们看下面的例子。假设有一个恶意 个人通过廉价的方式创建自己的矿场,从而获得显着的挖矿能力 2 第 2 页的评论
The CryptoNote Technology
The CryptoNote Technology
Now that we have covered the limitations of the Bitcoin technology, we will concentrate on presenting the features of CryptoNote.
CryptoNote 技术
现在我们已经涵盖了 Bitcoin 技术的局限性,我们将重点关注 介绍 CryptoNote 的功能。
Untraceable Transactions
Untraceable Transactions
In this section we propose a scheme of fully anonymous transactions satisfying both untraceability
and unlinkability conditions. An important feature of our solution is its autonomy: the sender
is not required to cooperate with other users or a trusted third party to make his transactions;
hence each participant produces a cover traffic independently.
4.1
Literature review
Our scheme relies on the cryptographic primitive called a group signature. First presented by
D. Chaum and E. van Heyst [19], it allows a user to sign his message on behalf of the group.
After signing the message the user provides (for verification purposes) not his own single public
1This is so-called “soft limit” — the reference client restriction for creating new blocks. Hard maximum of
possible blocksize was 1 MB
4
them if necessary that causes the main drawbacks. Unfortunately, it is hard to predict when the
constants may need to be changed and replacing them may lead to terrible consequences.
A good example of a hardcoded limit change leading to disastrous consequences is the block
size limit set to 250kb1. This limit was sufficient to hold about 10000 standard transactions. In
early 2013, this limit had almost been reached and an agreement was reached to increase the
limit. The change was implemented in wallet version 0.8 and ended with a 24-blocks chain split
and a successful double-spend attack [9]. While the bug was not in the Bitcoin protocol, but
rather in the database engine it could have been easily caught by a simple stress test if there was
no artificially introduced block size limit.
Constants also act as a form of centralization point.
Despite the peer-to-peer nature of
Bitcoin, an overwhelming majority of nodes use the official reference client [10] developed by
a small group of people. This group makes the decision to implement changes to the protocol
and most people accept these changes irrespective of their “correctness”. Some decisions caused
heated discussions and even calls for boycott [11], which indicates that the community and the
developers may disagree on some important points. It therefore seems logical to have a protocol
with user-configurable and self-adjusting variables as a possible way to avoid these problems.
2.5
Bulky scripts
The scripting system in Bitcoin is a heavy and complex feature. It potentially allows one to create
sophisticated transactions [12], but some of its features are disabled due to security concerns and
some have never even been used [13]. The script (including both senders’ and receivers’ parts)
for the most popular transaction in Bitcoin looks like this:
key, but the keys of all the users of his group. A verifier is convinced that the real signer is a member of the group, but cannot exclusively identify the signer. The original protocol required a trusted third party (called the Group Manager), and he was the only one who could trace the signer. The next version called a ring signature, introduced by Rivest et al. in [34], was an autonomous scheme without Group Manager and anonymity revocation. Various modifications of this scheme appeared later: linkable ring signature [26, 27, 17] allowed to determine if two signatures were produced by the same group member, traceable ring signature [24, 23] limited excessive anonymity by providing possibility to trace the signer of two messages with respect to the same metainformation (or “tag” in terms of [24]). A similar cryptographic construction is also known as a ad-hoc group signature [16, 38]. It emphasizes the arbitrary group formation, whereas group/ring signature schemes rather imply a fixed set of members. For the most part, our solution is based on the work “Traceable ring signature” by E. Fujisaki and K. Suzuki [24]. In order to distinguish the original algorithm and our modification we will call the latter a one-time ring signature, stressing the user’s capability to produce only one valid signature under his private key. We weakened the traceability property and kept the linkability only to provide one-timeness: the public key may appear in many foreign verifying sets and the private key can be used for generating a unique anonymous signature. In case of a double spend attempt these two signatures will be linked together, but revealing the signer is not necessary for our purposes. 4.2 Definitions 4.2.1 Elliptic curve parameters As our base signature algorithm we chose to use the fast scheme EdDSA, which is developed and implemented by D.J. Bernstein et al. [18]. Like Bitcoin’s ECDSA it is based on the elliptic curve discrete logarithm problem, so our scheme could also be applied to Bitcoin in future. Common parameters are: \(q\): a prime number; \(q = 2^{255} - 19\); \(d\): an element of \(\mathbb{F}_q\); \(d = -121665/121666\); \(E\): an elliptic curve equation; \(-x^2 + y^2 = 1 + dx^2y^2\); \(G\): a base point; \(G = (x, -4/5)\); \(l\): a prime order of the base point; \(l = 2^{252} + 27742317777372353535851937790883648493\); \(H_s\): a cryptographic hash function \(\{0, 1\}^* \to \mathbb{F}_q\); \(H_p\): a deterministic hash function \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\). 4.2.2 Terminology Enhanced privacy requires a new terminology which should not be confused with Bitcoin entities. private ec-key is a standard elliptic curve private key: a number \(a \in [1, l - 1]\); public ec-key is a standard elliptic curve public key: a point \(A = aG\); one-time keypair is a pair of private and public ec-keys; 5 key, but the keys of all the users of his group. A verifier is convinced that the real signer is a member of the group, but cannot exclusively identify the signer. The original protocol required a trusted third party (called the Group Manager), and he was the only one who could trace the signer. The next version called a ring signature, introduced by Rivest et al. in [34], was an autonomous scheme without Group Manager and anonymity revocation. Various modifications of this scheme appeared later: linkable ring signature [26, 27, 17] allowed to determine if two signatures were produced by the same group member, traceable ring signature [24, 23] limited excessive anonymity by providing possibility to trace the signer of two messages with respect to the same metainformation (or “tag” in terms of [24]). A similar cryptographic construction is also known as a ad-hoc group signature [16, 38]. It emphasizes the arbitrary group formation, whereas group/ring signature schemes rather imply a fixed set of members. For the most part, our solution is based on the work “Traceable ring signature” by E. Fujisaki and K. Suzuki [24]. In order to distinguish the original algorithm and our modification we will call the latter a one-time ring signature, stressing the user’s capability to produce only one valid signature under his private key. We weakened the traceability property and kept the linkability only to provide one-timeness: the public key may appear in many foreign verifying sets and the private key can be used for generating a unique anonymous signature. In case of a double spend attempt these two signatures will be linked together, but revealing the signer is not necessary for our purposes. 4.2 Definitions 4.2.1 Elliptic curve parameters As our base signature algorithm we chose to use the fast scheme EdDSA, which is developed and implemented by D.J. Bernstein et al. [18]. Like Bitcoin’s ECDSA it is based on the elliptic curve discrete logarithm problem, so our scheme could also be applied to Bitcoin in future. Common parameters are: \(q\): a prime number; \(q = 2^{255} - 19\); \(d\): an element of \(\mathbb{F}_q\); \(d = -121665/121666\); \(E\): an elliptic curve equation; \(-x^2 + y^2 = 1 + dx^2y^2\); \(G\): a base point; \(G = (x, -4/5)\); \(l\): a prime order of the base point; \(l = 2^{252} + 27742317777372353535851937790883648493\); \(H_s\): a cryptographic hash function \(\{0, 1\}^* \to \mathbb{F}_q\); \(H_p\): a deterministic hash function \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\). 4.2.2 Terminology Enhanced privacy requires a new terminology which should not be confused with Bitcoin entities. private ec-key is a standard elliptic curve private key: a number \(a \in [1, l - 1]\); public ec-key is a standard elliptic curve public key: a point \(A = aG\); one-time keypair is a pair of private and public ec-keys; 5 8 A ring signature works like this: Alex wants to leak a message to WikiLeaks about her employer. Every employee in her Company has a private/public key pair (Ri, Ui). She composes her signature with input set as her message, m, her private key, Ri, and EVERYBODY’s public keys, (Ui;i=1...n). Anyone (without knowing any private keys) can verify easily that some pair (Rj, Uj) must have been used to construct the signature... someone who works for Alex’s employer... but it’s essentially a random guess to figure out which one it could be. http://en.wikipedia.org/wiki/Ring_signature#Crypto-currencies http://link.springer.com/chapter/10.1007/3-540-45682-1_32#page-1 http://link.springer.com/chapter/10.1007/11424826_65 http://link.springer.com/chapter/10.1007/978-3-540-27800-9_28 http://link.springer.com/chapter/10.1007%2F11774716_9 Notice that a linkable ring signature described here is kind of the opposite of "unlinkable" described above. Here, we intercept two messages, and we can determine whether the same party sent them, although we should still be unable to determine who that party is. The definition of "unlinkable" used to construct Cryptonote means we cannot determine whether the same party is receiving them. Hence, what we really have here is FOUR things going on. A system can be linkable or non-linkable, depending on whether or not it’s possible to determine whether the sender of two messages are the same (regardless of whether this requires revoking anonymity). And a system can be unlinkable or non-unlinkable, depending on whether or not it’s possible to determine whether the receiver of two messages are the same (regardless of whether or not this requires revoking anonymity). Please don’t blame me for this terrible terminology. Graph theorists should probably be pleased. Some of you may be more comfortable with "receiver linkable" versus "sender linkable." http://link.springer.com/chapter/10.1007/978-3-540-71677-8_13 When I read this, this seemed like a silly feature. Then I read that it may be a feature for electronic voting, and that seemed to make sense. Kinda cool, from that perspective. But I’m not totally sure about purposely implementing traceable ring signatures. http://search.ieice.org/bin/summary.php?id=e95-a_1_151
key, but the keys of all the users of his group. A verifier is convinced that the real signer is a member of the group, but cannot exclusively identify the signer. The original protocol required a trusted third party (called the Group Manager), and he was the only one who could trace the signer. The next version called a ring signature, introduced by Rivest et al. in [34], was an autonomous scheme without Group Manager and anonymity revocation. Various modifications of this scheme appeared later: linkable ring signature [26, 27, 17] allowed to determine if two signatures were produced by the same group member, traceable ring signature [24, 23] limited excessive anonymity by providing possibility to trace the signer of two messages with respect to the same metainformation (or “tag” in terms of [24]). A similar cryptographic construction is also known as a ad-hoc group signature [16, 38]. It emphasizes the arbitrary group formation, whereas group/ring signature schemes rather imply a fixed set of members. For the most part, our solution is based on the work “Traceable ring signature” by E. Fujisaki and K. Suzuki [24]. In order to distinguish the original algorithm and our modification we will call the latter a one-time ring signature, stressing the user’s capability to produce only one valid signature under his private key. We weakened the traceability property and kept the linkability only to provide one-timeness: the public key may appear in many foreign verifying sets and the private key can be used for generating a unique anonymous signature. In case of a double spend attempt these two signatures will be linked together, but revealing the signer is not necessary for our purposes. 4.2 Definitions 4.2.1 Elliptic curve parameters As our base signature algorithm we chose to use the fast scheme EdDSA, which is developed and implemented by D.J. Bernstein et al. [18]. Like Bitcoin’s ECDSA it is based on the elliptic curve discrete logarithm problem, so our scheme could also be applied to Bitcoin in future. Common parameters are: \(q\): a prime number; \(q = 2^{255} - 19\); \(d\): an element of \(\mathbb{F}_q\); \(d = -121665/121666\); \(E\): an elliptic curve equation; \(-x^2 + y^2 = 1 + dx^2y^2\); \(G\): a base point; \(G = (x, -4/5)\); \(l\): a prime order of the base point; \(l = 2^{252} + 27742317777372353535851937790883648493\); \(H_s\): a cryptographic hash function \(\{0, 1\}^* \to \mathbb{F}_q\); \(H_p\): a deterministic hash function \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\). 4.2.2 Terminology Enhanced privacy requires a new terminology which should not be confused with Bitcoin entities. private ec-key is a standard elliptic curve private key: a number \(a \in [1, l - 1]\); public ec-key is a standard elliptic curve public key: a point \(A = aG\); one-time keypair is a pair of private and public ec-keys; 5 key, but the keys of all the users of his group. A verifier is convinced that the real signer is a member of the group, but cannot exclusively identify the signer. The original protocol required a trusted third party (called the Group Manager), and he was the only one who could trace the signer. The next version called a ring signature, introduced by Rivest et al. in [34], was an autonomous scheme without Group Manager and anonymity revocation. Various modifications of this scheme appeared later: linkable ring signature [26, 27, 17] allowed to determine if two signatures were produced by the same group member, traceable ring signature [24, 23] limited excessive anonymity by providing possibility to trace the signer of two messages with respect to the same metainformation (or “tag” in terms of [24]). A similar cryptographic construction is also known as a ad-hoc group signature [16, 38]. It emphasizes the arbitrary group formation, whereas group/ring signature schemes rather imply a fixed set of members. For the most part, our solution is based on the work “Traceable ring signature” by E. Fujisaki and K. Suzuki [24]. In order to distinguish the original algorithm and our modification we will call the latter a one-time ring signature, stressing the user’s capability to produce only one valid signature under his private key. We weakened the traceability property and kept the linkability only to provide one-timeness: the public key may appear in many foreign verifying sets and the private key can be used for generating a unique anonymous signature. In case of a double spend attempt these two signatures will be linked together, but revealing the signer is not necessary for our purposes. 4.2 Definitions 4.2.1 Elliptic curve parameters As our base signature algorithm we chose to use the fast scheme EdDSA, which is developed and implemented by D.J. Bernstein et al. [18]. Like Bitcoin’s ECDSA it is based on the elliptic curve discrete logarithm problem, so our scheme could also be applied to Bitcoin in future. Common parameters are: \(q\): a prime number; \(q = 2^{255} - 19\); \(d\): an element of \(\mathbb{F}_q\); \(d = -121665/121666\); \(E\): an elliptic curve equation; \(-x^2 + y^2 = 1 + dx^2y^2\); \(G\): a base point; \(G = (x, -4/5)\); \(l\): a prime order of the base point; \(l = 2^{252} + 27742317777372353535851937790883648493\); \(H_s\): a cryptographic hash function \(\{0, 1\}^* \to \mathbb{F}_q\); \(H_p\): a deterministic hash function \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\). 4.2.2 Terminology Enhanced privacy requires a new terminology which should not be confused with Bitcoin entities. private ec-key is a standard elliptic curve private key: a number \(a \in [1, l - 1]\); public ec-key is a standard elliptic curve public key: a point \(A = aG\); one-time keypair is a pair of private and public ec-keys; 5 9 Gosh, the author of this whitepaper sure could have worded this better! Let’s say that an employee-owned company wants to take a vote on whether or not to acquire certain new assets, and Alex and Brenda are both employees. The Company provides each employee a message like "I vote yes on Proposition A!" which has the metainformation "issue" [PROP A] and asks them to sign it with a traceable ring signature if they support the proposition. Using a traditional ring signature, a dishonest employee can sign the message multiple times, presumably with different nonces, in order to vote as many times as they like. On the other hand, in a traceable ring signature scheme, Alex will go to vote, and her private key will have been used on the issue [PROP A]. If Alex tries to sign a message like "I, Brenda, approve of proposition A!" to "frame" Brenda and double vote, this new message will also have the issue [PROP A]. Since Alex’s private key has already tripped the [PROP A] issue, Alex’s identity will be immediately revealed as a fraud. Which, face it, is pretty cool! Cryptography enforced voting equality. http://link.springer.com/chapter/10.1007/978-3-540-71677-8_13 This paper is interesting, essentially creating an ad-hoc ring signature but without any of the other participant’s consent. The structure of the signature may be different; I haven’t dug deep, and I haven’t seen whether it’s secure. https://people.csail.mit.edu/rivest/AdidaHohenbergerRivest-AdHocGroupSignaturesFromHijackedKeypai Ad-hoc group signatures are: ring signatures, which are group signatures with no group managers, no centralization, but allows a member in an ad-hoc group to provably claim that it has (not) issued the anonymous signature on behalf of the group. http://link.springer.com/chapter/10.1007/11908739_9 This isn’t quite correct, from my understanding. And my understanding will likely change as I get deeper into this project. But from my understanding, the hierarchy looks like this. Group sigs: group managers control traceability and the ability of adding or removing members from being signers. Ring sigs: Arbitrary group formation without a group manager. No anonymity revocation. No way to repudiate oneself from a particular signature. With traceable and linkable ring signatures, anonymity is somewhat scaleable. Ad-hoc group signatures: like ring signatures, but members can prove that they did not create a particular signature. This is important when anyone in a group can produce a signature. http://link.springer.com/chapter/10.1007/978-3-540-71677-8_13 Fujisaki and Suzuki’s algorithm is tweaked later by the author to provide one-time-ness. So we will analyze Fujisaki and Suzuki’s algorithm concurrently with the new algorithm rather than going over it here.
key, but the keys of all the users of his group. A verifier is convinced that the real signer is a member of the group, but cannot exclusively identify the signer. The original protocol required a trusted third party (called the Group Manager), and he was the only one who could trace the signer. The next version called a ring signature, introduced by Rivest et al. in [34], was an autonomous scheme without Group Manager and anonymity revocation. Various modifications of this scheme appeared later: linkable ring signature [26, 27, 17] allowed to determine if two signatures were produced by the same group member, traceable ring signature [24, 23] limited excessive anonymity by providing possibility to trace the signer of two messages with respect to the same metainformation (or “tag” in terms of [24]). A similar cryptographic construction is also known as a ad-hoc group signature [16, 38]. It emphasizes the arbitrary group formation, whereas group/ring signature schemes rather imply a fixed set of members. For the most part, our solution is based on the work “Traceable ring signature” by E. Fujisaki and K. Suzuki [24]. In order to distinguish the original algorithm and our modification we will call the latter a one-time ring signature, stressing the user’s capability to produce only one valid signature under his private key. We weakened the traceability property and kept the linkability only to provide one-timeness: the public key may appear in many foreign verifying sets and the private key can be used for generating a unique anonymous signature. In case of a double spend attempt these two signatures will be linked together, but revealing the signer is not necessary for our purposes. 4.2 Definitions 4.2.1 Elliptic curve parameters As our base signature algorithm we chose to use the fast scheme EdDSA, which is developed and implemented by D.J. Bernstein et al. [18]. Like Bitcoin’s ECDSA it is based on the elliptic curve discrete logarithm problem, so our scheme could also be applied to Bitcoin in future. Common parameters are: \(q\): a prime number; \(q = 2^{255} - 19\); \(d\): an element of \(\mathbb{F}_q\); \(d = -121665/121666\); \(E\): an elliptic curve equation; \(-x^2 + y^2 = 1 + dx^2y^2\); \(G\): a base point; \(G = (x, -4/5)\); \(l\): a prime order of the base point; \(l = 2^{252} + 27742317777372353535851937790883648493\); \(H_s\): a cryptographic hash function \(\{0, 1\}^* \to \mathbb{F}_q\); \(H_p\): a deterministic hash function \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\). 4.2.2 Terminology Enhanced privacy requires a new terminology which should not be confused with Bitcoin entities. private ec-key is a standard elliptic curve private key: a number \(a \in [1, l - 1]\); public ec-key is a standard elliptic curve public key: a point \(A = aG\); one-time keypair is a pair of private and public ec-keys; 5 key, but the keys of all the users of his group. A verifier is convinced that the real signer is a member of the group, but cannot exclusively identify the signer. The original protocol required a trusted third party (called the Group Manager), and he was the only one who could trace the signer. The next version called a ring signature, introduced by Rivest et al. in [34], was an autonomous scheme without Group Manager and anonymity revocation. Various modifications of this scheme appeared later: linkable ring signature [26, 27, 17] allowed to determine if two signatures were produced by the same group member, traceable ring signature [24, 23] limited excessive anonymity by providing possibility to trace the signer of two messages with respect to the same metainformation (or “tag” in terms of [24]). A similar cryptographic construction is also known as a ad-hoc group signature [16, 38]. It emphasizes the arbitrary group formation, whereas group/ring signature schemes rather imply a fixed set of members. For the most part, our solution is based on the work “Traceable ring signature” by E. Fujisaki and K. Suzuki [24]. In order to distinguish the original algorithm and our modification we will call the latter a one-time ring signature, stressing the user’s capability to produce only one valid signature under his private key. We weakened the traceability property and kept the linkability only to provide one-timeness: the public key may appear in many foreign verifying sets and the private key can be used for generating a unique anonymous signature. In case of a double spend attempt these two signatures will be linked together, but revealing the signer is not necessary for our purposes. 4.2 Definitions 4.2.1 Elliptic curve parameters As our base signature algorithm we chose to use the fast scheme EdDSA, which is developed and implemented by D.J. Bernstein et al. [18]. Like Bitcoin’s ECDSA it is based on the elliptic curve discrete logarithm problem, so our scheme could also be applied to Bitcoin in future. Common parameters are: \(q\): a prime number; \(q = 2^{255} - 19\); \(d\): an element of \(\mathbb{F}_q\); \(d = -121665/121666\); \(E\): an elliptic curve equation; \(-x^2 + y^2 = 1 + dx^2y^2\); \(G\): a base point; \(G = (x, -4/5)\); \(l\): a prime order of the base point; \(l = 2^{252} + 27742317777372353535851937790883648493\); \(H_s\): a cryptographic hash function \(\{0, 1\}^* \to \mathbb{F}_q\); \(H_p\): a deterministic hash function \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\). 4.2.2 Terminology Enhanced privacy requires a new terminology which should not be confused with Bitcoin entities. private ec-key is a standard elliptic curve private key: a number \(a \in [1, l - 1]\); public ec-key is a standard elliptic curve public key: a point \(A = aG\); one-time keypair is a pair of private and public ec-keys; 5 10 Linkability in the sense of "linkable ring signatures" means we can tell if two outgoing transactions came from the same source without revealing who the source is. The authors weakened linkability so as to (a) preserve privacy, but still (b) spot any transaction using a private key a second time as invalid. Okay, so this is an order-of-events question. Consider the following scenario. My mining computer will have the current blockchain, it will have it’s own block of transactions it calls legitimate, it will be working on that block in a proof-of-work puzzle, and it will have a list of pending transactions to be added to the next block. It will also be sending any new transactions into that pool of pending transactions. If I do not solve the next block, but someone else does, I get an updated copy of the blockchain. The block I was working on and my list of pending transactions both may have some transactions that are now incorporated into the blockchain. Unravel my pending block, combine that with my list of pending transactions, and call that my pool of pending transactions. Remove any that are now officially in the blockchain. Now, what do I do? Should I first go through and "remove all double-spends"? On the other hand, should I search through the list and make sure that each private key has not yet been used, and if it has been used already in my list, then I received the first copy first, and hence any further copy is illegitimate. Thus I proceed to simply delete all instances after the first of the the same private key. Algebraic geometry has never been my strong suit. http://en.wikipedia.org/wiki/EdDSA Such speed, much wow. THIS is algebraic geometry for the win. Not that I’d know anything about that. Problematically, or not, discrete logs are getting very fast. And quantum computers eat them for breakfast. http://link.springer.com/article/10.1007/s13389-012-0027-1 This becomes a really important number, but there is no explanation or citation to how it was chosen. Simply choosing a single known large prime would be fine, but if there are known facts about this large prime, that could influence our choice. Different variants of cryptonote could choose different values of ell, but there is no discussion in this paper about how that choice will affect our choices of other global parameters listed on page 5. This paper needs a section on choosing parameter values.
private user key is a pair \((a, b)\) of two different private ec-keys; tracking key is a pair \((a, B)\) of private and public ec-key (where \(B = bG\) and \(a \neq b\)); public user key is a pair \((A, B)\) of two public ec-keys derived from \((a, b)\); standard address is a representation of a public user key given into human friendly string with error correction; truncated address is a representation of the second half (point \(B\)) of a public user key given into human friendly string with error correction. The transaction structure remains similar to the structure in Bitcoin: every user can choose several independent incoming payments (transactions outputs), sign them with the corresponding private keys and send them to different destinations. Contrary to Bitcoin’s model, where a user possesses unique private and public key, in the proposed model a sender generates a one-time public key based on the recipient’s address and some random data. In this sense, an incoming transaction for the same recipient is sent to a one-time public key (not directly to a unique address) and only the recipient can recover the corresponding private part to redeem his funds (using his unique private key). The recipient can spend the funds using a ring signature, keeping his ownership and actual spending anonymous. The details of the protocol are explained in the next subsections. 4.3 Unlinkable payments Classic Bitcoin addresses, once being published, become unambiguous identifier for incoming payments, linking them together and tying to the recipient’s pseudonyms. If someone wants to receive an “untied” transaction, he should convey his address to the sender by a private channel. If he wants to receive different transactions which cannot be proven to belong to the same owner he should generate all the different addresses and never publish them in his own pseudonym. Public Private Alice Carol Bob’s addr 1 Bob’s addr 2 Bob’s key 1 Bob’s key 2 Bob Fig. 2. Traditional Bitcoin keys/transactions model. We propose a solution allowing a user to publish a single address and receive unconditional unlinkable payments. The destination of each CryptoNote output (by default) is a public key, derived from recipient’s address and sender’s random data. The main advantage against Bitcoin is that every destination key is unique by default (unless the sender uses the same data for each of his transactions to the same recipient). Hence, there is no such issue as “address reuse” by design and no observer can determine if any transactions were sent to a specific address or link two addresses together. 6 private user key is a pair \((a, b)\) of two different private ec-keys; tracking key is a pair \((a, B)\) of private and public ec-key (where \(B = bG\) and \(a \neq b\)); public user key is a pair \((A, B)\) of two public ec-keys derived from \((a, b)\); standard address is a representation of a public user key given into human friendly string with error correction; truncated address is a representation of the second half (point \(B\)) of a public user key given into human friendly string with error correction. The transaction structure remains similar to the structure in Bitcoin: every user can choose several independent incoming payments (transactions outputs), sign them with the corresponding private keys and send them to different destinations. Contrary to Bitcoin’s model, where a user possesses unique private and public key, in the proposed model a sender generates a one-time public key based on the recipient’s address and some random data. In this sense, an incoming transaction for the same recipient is sent to a one-time public key (not directly to a unique address) and only the recipient can recover the corresponding private part to redeem his funds (using his unique private key). The recipient can spend the funds using a ring signature, keeping his ownership and actual spending anonymous. The details of the protocol are explained in the next subsections. 4.3 Unlinkable payments Classic Bitcoin addresses, once being published, become unambiguous identifier for incoming payments, linking them together and tying to the recipient’s pseudonyms. If someone wants to receive an “untied” transaction, he should convey his address to the sender by a private channel. If he wants to receive different transactions which cannot be proven to belong to the same owner he should generate all the different addresses and never publish them in his own pseudonym. Public Private Alice Carol Bob’s addr 1 Bob’s addr 2 Bob’s key 1 Bob’s key 2 Bob Fig. 2. Traditional Bitcoin keys/transactions model. We propose a solution allowing a user to publish a single address and receive unconditional unlinkable payments. The destination of each CryptoNote output (by default) is a public key, derived from recipient’s address and sender’s random data. The main advantage against Bitcoin is that every destination key is unique by default (unless the sender uses the same data for each of his transactions to the same recipient). Hence, there is no such issue as “address reuse” by design and no observer can determine if any transactions were sent to a specific address or link two addresses together. 6 11 So this is like Bitcoin, but with infinite, anonymous PO Boxes, redeemable only by the receiver generating a private key that is as anonymous as a ring signature can be. Bitcoin works this way. If Alex has 0.112 Bitcoin in her wallet she just received from Frank, she really has a signed message "I, [FRANK], send 0.112 Bitcoin to [alex] + H0 + N0" where 1) Frank has signed the message with his private key [FRANK], 2) Frank has signed the message with Alex’s public key, [alex], 3) Frank has included some form of the history of the bitcoin, H0, and 4) Frank includes a random bit of data called the nonce, N0. If Alex then wants to send 0.011 Bitcoin to Charlene, she will take Frank’s message, and she will set that to H1, and sign two messages: one for her transaction, and one for the change. H1= "I, [FRANK], send 0.112 Bitcoin to [alex] + H0 + N" "I, [ALEX], send 0.011 Bitcoin to [charlene] + H1 + N1" "I, [ALEX], send 0.101 Bitcoin as change to [alex] + H1 + N2." where Alex signs both messages with her private key [ALEX], the first message with Charlene’s public key [charlene], the second message with Alex’s public key [alex], and including the histories and some randomly generated nonces N1 and N2 appropriately. Cryptonote works this way: If Alex has 0.112 Cryptonote in her wallet she just received from Frank, she really has a signed message "I, [someone in an ad-hoc group], send 0.112 Cryptonote to [a one-time address] + H0 + N0." Alex discovered that this was her money by checking her private key [ALEX] against [a one-time address] for every passing message, and if she wishes to spend it she does so in the following way. She chooses a recipient of the money, perhaps Charlene has started voting for drone-strikes so Alex wants to send money to Brenda instead. So Alex looks up Brenda’s public key, [brenda], and uses her own private key, [ALEX], to generate a one-time address [ALEX+brenda]. She then chooses an arbitrary collection C from the network of cryptonote users and she constructs a ring signature from this ad-hoc group. We set our history as the previous message, add nonces, and proceed as usual? H1 = "I, [someone in an ad-hoc group], send 0.112 Cryptonote to [a one-time address] + H0 + N0." "I, [someone in the collection C], send 0.011 Cryptonote to [one-time-address-made-fromALEX+brenda] + H1 + N1" "I, [someone in the collection C], send 0.101 Cryptonote as change to [one-time-address-madefrom-ALEX+alex] + H1 + N2" Now, Alex and Brenda both scan all incoming messages for any one-time-addresses that were created using their key. If they find any, then that message is their very own brand new cryptonote! And even then, the transaction will still hit the blockchain. If the coins entering that address are known to be sent from criminals, political contributors, or from committees and accounts with strict budgets (i.e. embezzling), or if the new owner of these coins ever makes a mistake and sends these coins to a common address with coins he is known to own, the anonymity jig is up in bitcoin.
private user key is a pair \((a, b)\) of two different private ec-keys; tracking key is a pair \((a, B)\) of private and public ec-key (where \(B = bG\) and \(a \neq b\)); public user key is a pair \((A, B)\) of two public ec-keys derived from \((a, b)\); standard address is a representation of a public user key given into human friendly string with error correction; truncated address is a representation of the second half (point \(B\)) of a public user key given into human friendly string with error correction. The transaction structure remains similar to the structure in Bitcoin: every user can choose several independent incoming payments (transactions outputs), sign them with the corresponding private keys and send them to different destinations. Contrary to Bitcoin’s model, where a user possesses unique private and public key, in the proposed model a sender generates a one-time public key based on the recipient’s address and some random data. In this sense, an incoming transaction for the same recipient is sent to a one-time public key (not directly to a unique address) and only the recipient can recover the corresponding private part to redeem his funds (using his unique private key). The recipient can spend the funds using a ring signature, keeping his ownership and actual spending anonymous. The details of the protocol are explained in the next subsections. 4.3 Unlinkable payments Classic Bitcoin addresses, once being published, become unambiguous identifier for incoming payments, linking them together and tying to the recipient’s pseudonyms. If someone wants to receive an “untied” transaction, he should convey his address to the sender by a private channel. If he wants to receive different transactions which cannot be proven to belong to the same owner he should generate all the different addresses and never publish them in his own pseudonym. Public Private Alice Carol Bob’s addr 1 Bob’s addr 2 Bob’s key 1 Bob’s key 2 Bob Fig. 2. Traditional Bitcoin keys/transactions model. We propose a solution allowing a user to publish a single address and receive unconditional unlinkable payments. The destination of each CryptoNote output (by default) is a public key, derived from recipient’s address and sender’s random data. The main advantage against Bitcoin is that every destination key is unique by default (unless the sender uses the same data for each of his transactions to the same recipient). Hence, there is no such issue as “address reuse” by design and no observer can determine if any transactions were sent to a specific address or link two addresses together. 6 private user key is a pair \((a, b)\) of two different private ec-keys; tracking key is a pair \((a, B)\) of private and public ec-key (where \(B = bG\) and \(a \neq b\)); public user key is a pair \((A, B)\) of two public ec-keys derived from \((a, b)\); standard address is a representation of a public user key given into human friendly string with error correction; truncated address is a representation of the second half (point \(B\)) of a public user key given into human friendly string with error correction. The transaction structure remains similar to the structure in Bitcoin: every user can choose several independent incoming payments (transactions outputs), sign them with the corresponding private keys and send them to different destinations. Contrary to Bitcoin’s model, where a user possesses unique private and public key, in the proposed model a sender generates a one-time public key based on the recipient’s address and some random data. In this sense, an incoming transaction for the same recipient is sent to a one-time public key (not directly to a unique address) and only the recipient can recover the corresponding private part to redeem his funds (using his unique private key). The recipient can spend the funds using a ring signature, keeping his ownership and actual spending anonymous. The details of the protocol are explained in the next subsections. 4.3 Unlinkable payments Classic Bitcoin addresses, once being published, become unambiguous identifier for incoming payments, linking them together and tying to the recipient’s pseudonyms. If someone wants to receive an “untied” transaction, he should convey his address to the sender by a private channel. If he wants to receive different transactions which cannot be proven to belong to the same owner he should generate all the different addresses and never publish them in his own pseudonym. Public Private Alice Carol Bob’s addr 1 Bob’s addr 2 Bob’s key 1 Bob’s key 2 Bob Fig. 2. Traditional Bitcoin keys/transactions model. We propose a solution allowing a user to publish a single address and receive unconditional unlinkable payments. The destination of each CryptoNote output (by default) is a public key, derived from recipient’s address and sender’s random data. The main advantage against Bitcoin is that every destination key is unique by default (unless the sender uses the same data for each of his transactions to the same recipient). Hence, there is no such issue as “address reuse” by design and no observer can determine if any transactions were sent to a specific address or link two addresses together. 6 12 Hence, rather than users sending coins from address (which is really a public key) to address (another public key) using their private keys, users are sending coins from one-time PO-box (which is generating using your friends public key) to one-time PO-box (similarly) using your own private keys. In a sense, we’re saying "Okay, everyone take your hands offthe money while it’s being transferred around! It’s simply enough to know that our keys can open that box and that we know how much money is in the box. Never put your fingerprints on the PO Box or actually use it, just trade the box filled with cash itself. That way we don’t know who sent what, but the contents of these public addresses are still frictionless, fungible, divisible, and still possess all the other nice qualities of money we desire like bitcoin." An infinite set of PO boxes. You publish an address, I have a private key. I use my private key and your address, and some random data, to generate a public key. The algorithm is designed such that, since your address was used to generate the public key, only YOUR private key works to unlock the message. An observer, Eve, sees you publish your address, and sees the public key I announce. However, she doesn’t know if I announced my public key based on your address or hers, or Brenda’s or Charlene’s, or whoever’s. She checks her private key against the public key I announced and sees it doesn’t work; it isn’t her money. She doens’t know anyone else’s private key, and only the recipient of the message has the private key that can unlock the message. So no one listening in can determine who received the money much less take the money.
Public Private Alice Carol One-time key One-time key One-time key Bob Bob’s Key Bob’s Address Fig. 3. CryptoNote keys/transactions model. First, the sender performs a Diffie-Hellman exchange to get a shared secret from his data and half of the recipient’s address. Then he computes a one-time destination key, using the shared secret and the second half of the address. Two different ec-keys are required from the recipient for these two steps, so a standard CryptoNote address is nearly twice as large as a Bitcoin wallet address. The receiver also performs a Diffie-Hellman exchange to recover the corresponding secret key. A standard transaction sequence goes as follows: 1. Alice wants to send a payment to Bob, who has published his standard address. She unpacks the address and gets Bob’s public key \((A, B)\). 2. Alice generates a random \(r \in [1, l-1]\) and computes a one-time public key \(P = H_s(rA)G + B\). 3. Alice uses \(P\) as a destination key for the output and also packs value \(R = rG\) (as a part of the Diffie-Hellman exchange) somewhere into the transaction. Note that she can create other outputs with unique public keys: different recipients’ keys \((A_i, B_i)\) imply different \(P_i\) even with the same \(r\). Transaction Tx public key Tx output Amount Destination key \(R = rG\) \(P = H_s(rA)G + B\) Receiver’s public key Sender’s random data \(r\) \((A, B)\) Fig. 4. Standard transaction structure. 4. Alice sends the transaction. 5. Bob checks every passing transaction with his private key \((a, b)\), and computes \(P' = H_s(aR)G + B\). If Alice’s transaction for with Bob as the recipient was among them, then \(aR = arG = rA\) and \(P' = P\). 7 Public Private Alice Carol One-time key One-time key One-time key Bob Bob’s Key Bob’s Address Fig. 3. CryptoNote keys/transactions model. First, the sender performs a Diffie-Hellman exchange to get a shared secret from his data and half of the recipient’s address. Then he computes a one-time destination key, using the shared secret and the second half of the address. Two different ec-keys are required from the recipient for these two steps, so a standard CryptoNote address is nearly twice as large as a Bitcoin wallet address. The receiver also performs a Diffie-Hellman exchange to recover the corresponding secret key. A standard transaction sequence goes as follows: 1. Alice wants to send a payment to Bob, who has published his standard address. She unpacks the address and gets Bob’s public key \((A, B)\). 2. Alice generates a random \(r \in [1, l-1]\) and computes a one-time public key \(P = H_s(rA)G + B\). 3. Alice uses \(P\) as a destination key for the output and also packs value \(R = rG\) (as a part of the Diffie-Hellman exchange) somewhere into the transaction. Note that she can create other outputs with unique public keys: different recipients’ keys \((A_i, B_i)\) imply different \(P_i\) even with the same \(r\). Transaction Tx public key Tx output Amount Destination key \(R = rG\) \(P = H_s(rA)G + B\) Receiver’s public key Sender’s random data \(r\) \((A, B)\) Fig. 4. Standard transaction structure. 4. Alice sends the transaction. 5. Bob checks every passing transaction with his private key \((a, b)\), and computes \(P' = H_s(aR)G + B\). If Alice’s transaction for with Bob as the recipient was among them, then \(aR = arG = rA\) and \(P' = P\). 7 13 I wonder how much of a pain in the neck it would be to implement a choice of cryptography scheme. Elliptic or otherwise. So if some scheme is broken in the future, the currency switches without concern. Probably a big pain in the ass. Okay, this is exactly what I just explained in my previous comment. The Diffie-Hellman-type exchanges are neato. Say Alex and Brenda each have a secret number, A and B, and a number they don’t care about keeping secret, a and b. They wish to generate a shared secret without Eva discovering it. Diffie and Hellman came up with a way for Alex and Brenda to share the public numbers a and b, but not the private numbers A and B, and generate a shared secret, K. Using this shared secret, K, without any Eva listening in being able to generate the same K, Alex and Brenda can now use K as a secret encryption key and pass secret messages back and forth. Here’s how it CAN work, although it should work with much larger numbers than 100. We’ll use 100 because working over the integers modulo 100 is equivalent to "throwing out all but the last two digit of a number." Alex and Brenda each choose A, a, B, and b. They keep A and B secret. Alex tells Brenda her value of a modulo 100 (just the last two digits) and Brenda tells Alex her value of b modulo 100. Now Eva knows (a,b) modulo 100. But Alex knows (a,b,A) so she can compute x=abA modulo 100. Alex chops offall but the last digit because we’re working under the integers modulo 100 again. Similarly, Brenda knows (a,b,B) so she can compute y=abB modulo 100. Alex can now publish x and Brenda can publish y. But now Alex can compute yA = abBA modulo 100, and Brenda can compute xB = abBA modulo 100. They both know the same number! But all Eva has heard is (a,b,abA,abB). She has no easy way of computing abA*B. Now, this is the easiest and least secure way of thinking about the Diffie-Hellman exchange. More secure versions exist. But most versions work because integer factorization and discrete logarithms are difficult, and both of those problems are easily solved by quantum computers. I will look into whether any versions that are resistant to quantum exist. http://en.wikipedia.org/wiki/Diffie%E2%80%93Hellman_key_exchange The "standard txn sequence" listed here is missing a whole bunch of steps, like SIGNATURES. They’re just taken for granted in here. Which is really bad, because the order in which we sign stuff, the information included in the signed message, and so on... all of this is extremely important to the protocol. Getting one or two of the steps wrong, even slightly out of order, while implementing "the standard transaction sequence" could throw the security of the whole system into question. Furthermore, the proofs presented later in the paper may not be sufficiently rigorous if the framework under which they work is as loosely defined as in this section.
Public Private Alice Carol One-time key One-time key One-time key Bob Bob’s Key Bob’s Address Fig. 3. CryptoNote keys/transactions model. First, the sender performs a Diffie-Hellman exchange to get a shared secret from his data and half of the recipient’s address. Then he computes a one-time destination key, using the shared secret and the second half of the address. Two different ec-keys are required from the recipient for these two steps, so a standard CryptoNote address is nearly twice as large as a Bitcoin wallet address. The receiver also performs a Diffie-Hellman exchange to recover the corresponding secret key. A standard transaction sequence goes as follows: 1. Alice wants to send a payment to Bob, who has published his standard address. She unpacks the address and gets Bob’s public key \((A, B)\). 2. Alice generates a random \(r \in [1, l-1]\) and computes a one-time public key \(P = H_s(rA)G + B\). 3. Alice uses \(P\) as a destination key for the output and also packs value \(R = rG\) (as a part of the Diffie-Hellman exchange) somewhere into the transaction. Note that she can create other outputs with unique public keys: different recipients’ keys \((A_i, B_i)\) imply different \(P_i\) even with the same \(r\). Transaction Tx public key Tx output Amount Destination key \(R = rG\) \(P = H_s(rA)G + B\) Receiver’s public key Sender’s random data \(r\) \((A, B)\) Fig. 4. Standard transaction structure. 4. Alice sends the transaction. 5. Bob checks every passing transaction with his private key \((a, b)\), and computes \(P' = H_s(aR)G + B\). If Alice’s transaction for with Bob as the recipient was among them, then \(aR = arG = rA\) and \(P' = P\). 7 Public Private Alice Carol One-time key One-time key One-time key Bob Bob’s Key Bob’s Address Fig. 3. CryptoNote keys/transactions model. First, the sender performs a Diffie-Hellman exchange to get a shared secret from his data and half of the recipient’s address. Then he computes a one-time destination key, using the shared secret and the second half of the address. Two different ec-keys are required from the recipient for these two steps, so a standard CryptoNote address is nearly twice as large as a Bitcoin wallet address. The receiver also performs a Diffie-Hellman exchange to recover the corresponding secret key. A standard transaction sequence goes as follows: 1. Alice wants to send a payment to Bob, who has published his standard address. She unpacks the address and gets Bob’s public key \((A, B)\). 2. Alice generates a random \(r \in [1, l-1]\) and computes a one-time public key \(P = H_s(rA)G + B\). 3. Alice uses \(P\) as a destination key for the output and also packs value \(R = rG\) (as a part of the Diffie-Hellman exchange) somewhere into the transaction. Note that she can create other outputs with unique public keys: different recipients’ keys \((A_i, B_i)\) imply different \(P_i\) even with the same \(r\). Transaction Tx public key Tx output Amount Destination key \(R = rG\) \(P = H_s(rA)G + B\) Receiver’s public key Sender’s random data \(r\) \((A, B)\) Fig. 4. Standard transaction structure. 4. Alice sends the transaction. 5. Bob checks every passing transaction with his private key \((a, b)\), and computes \(P' = H_s(aR)G + B\). If Alice’s transaction for with Bob as the recipient was among them, then \(aR = arG = rA\) and \(P' = P\). 7 14 Note that the author(s?) do a terrible job of keeping their terminology straight throughout the text, but especially in this next bit. Next incarnation of this paper will necessarily be much more rigorous. In the text they refer to P as their one-time public key. In the diagram, they refer to R as their "Tx public key" and P as their "Destination key." If I were going to re-write this, I’d very specifically lay out some terminology before discussing these sections. This ell is massive. See page 5. Who chooses ell? Diagram illustrates that the transaction public key \(R = rG\), which is random and chosen by the sender, is not part of Tx output. This is because it could be the same for multiple transactions to multiple people, and isn’t used LATER to spend. A fresh R is generated every time you want to broadcast a new CryptoNote transaction. Furthermore, R is only used to check if you are the recipient of the transaction. It’s not junk data, but it’s junk to anyone without the private keys associated with (A,B). The Destination key, on the other hand, \(P = H_s(rA)G + B\) is part of Tx output. Everyone rifling through every passing transaction’s data must check their own generated P* against this P to see if they own this passing transaction. Anyone with an unspent transaction output (UTXO) will have a bunch of these Ps laying around with amounts. In order to spend, they sign some new message including P. Alice must sign this transaction with one-time private key(s) associated with the unspent transaction output(s) Destination Key(s). Each destination key owned by Alice comes equipped with a one-time private key also owned (presumably) by Alice. Every time Alice wants to send the contents of a destination key to me, or Bob, or Brenda, or Charlie or Charlene, she uses her private key to sign the transaction. Upon receipt of transaction, I will receive a new Tx public key, a new Destination public key, and I will be able to recover a new one-time private key x. Combining my one-time private key, x, with new transaction’s public Destination key(s) is how we send a new transaction
- Bob can recover the corresponding one-time private key: \(x = H_s(aR) + b\), so as \(P = xG\). He can spend this output at any time by signing a transaction with \(x\). Transaction Tx public key Tx output Amount Destination key \(P' = H_s(aR)G + bG\) one-time public key \(x = H_s(aR) + b\) one-time private key Receiver’s private key \((a, b)\) \(R\) \(P'\) \(\stackrel{?}{=} P\) Fig. 5. Incoming transaction check. As a result Bob gets incoming payments, associated with one-time public keys which are unlinkable for a spectator. Some additional notes: • When Bob “recognizes” his transactions (see step 5) he practically uses only half of his private information: \((a, B)\). This pair, also known as the tracking key, can be passed to a third party (Carol). Bob can delegate her the processing of new transactions. Bob doesn’t need to explicitly trust Carol, because she can’t recover the one-time secret key \(p\) without Bob’s full private key \((a, b)\). This approach is useful when Bob lacks bandwidth or computation power (smartphones, hardware wallets etc.). • In case Alice wants to prove she sent a transaction to Bob’s address she can either disclose \(r\) or use any kind of zero-knowledge protocol to prove she knows \(r\) (for example by signing the transaction with \(r\)). • If Bob wants to have an audit compatible address where all incoming transaction are linkable, he can either publish his tracking key or use a truncated address. That address represent only one public ec-key \(B\), and the remaining part required by the protocol is derived from it as follows: \(a = H_s(B)\) and \(A = H_s(B)G\). In both cases every person is able to “recognize” all of Bob’s incoming transaction, but, of course, none can spend the funds enclosed within them without the secret key \(b\). 4.4 One-time ring signatures A protocol based on one-time ring signatures allows users to achieve unconditional unlinkability. Unfortunately, ordinary types of cryptographic signatures permit to trace transactions to their respective senders and receivers. Our solution to this deficiency lies in using a different signature type than those currently used in electronic cash systems. We will first provide a general description of our algorithm with no explicit reference to electronic cash. A one-time ring signature contains four algorithms: (GEN, SIG, VER, LNK): GEN: takes public parameters and outputs an ec-pair \((P, x)\) and a public key \(I\). SIG: takes a message \(m\), a set \(S'\) of public keys \(\{P_i\}_{i \neq s}\), a pair \((P_s, x_s)\) and outputs a signature \(\sigma\) and a set \(S = S' \cup \{P_s\}\). 8
-
Bob can recover the corresponding one-time private key: \(x = H_s(aR) + b\), so as \(P = xG\). He can spend this output at any time by signing a transaction with \(x\). Transaction Tx public key Tx output Amount Destination key \(P' = H_s(aR)G + bG\) one-time public key \(x = H_s(aR) + b\) one-time private key Receiver’s private key \((a, b)\) \(R\) \(P'\) \(\stackrel{?}{=} P\) Fig. 5. Incoming transaction check. As a result Bob gets incoming payments, associated with one-time public keys which are unlinkable for a spectator. Some additional notes: • When Bob “recognizes” his transactions (see step 5) he practically uses only half of his private information: \((a, B)\). This pair, also known as the tracking key, can be passed to a third party (Carol). Bob can delegate her the processing of new transactions. Bob doesn’t need to explicitly trust Carol, because she can’t recover the one-time secret key \(p\) without Bob’s full private key \((a, b)\). This approach is useful when Bob lacks bandwidth or computation power (smartphones, hardware wallets etc.). • In case Alice wants to prove she sent a transaction to Bob’s address she can either disclose \(r\) or use any kind of zero-knowledge protocol to prove she knows \(r\) (for example by signing the transaction with \(r\)). • If Bob wants to have an audit compatible address where all incoming transaction are linkable, he can either publish his tracking key or use a truncated address. That address represent only one public ec-key \(B\), and the remaining part required by the protocol is derived from it as follows: \(a = H_s(B)\) and \(A = H_s(B)G\). In both cases every person is able to “recognize” all of Bob’s incoming transaction, but, of course, none can spend the funds enclosed within them without the secret key \(b\). 4.4 One-time ring signatures A protocol based on one-time ring signatures allows users to achieve unconditional unlinkability. Unfortunately, ordinary types of cryptographic signatures permit to trace transactions to their respective senders and receivers. Our solution to this deficiency lies in using a different signature type than those currently used in electronic cash systems. We will first provide a general description of our algorithm with no explicit reference to electronic cash. A one-time ring signature contains four algorithms: (GEN, SIG, VER, LNK): GEN: takes public parameters and outputs an ec-pair \((P, x)\) and a public key \(I\). SIG: takes a message \(m\), a set \(S'\) of public keys \(\{P_i\}_{i \neq s}\), a pair \((P_s, x_s)\) and outputs a signature \(\sigma\) and a set \(S = S' \cup \{P_s\}\). 8 15 What does an unspent transaction output look like here? The diagram suggests that transaction output consists only of two data points: amount and destination key. But this isn’t sufficient because when I try to spend this "output" I will still need to know R=rG. Remember, r is chosen by the sender, and R is a) used to recognize incoming cryptonotes as your own and b) used to generate the one-time private key used to "claim" your cryptonote. The part about this that I don’t understand? Taking the theoretical "okay, we have these signatures and transactions, and we pass ’em back and forth" into the world of programming "okay what information specifically makes up an individual UTXO?" Best way to answer that question is to dig into the body of completely uncommented code. Way to go, bytecoin team. Recall: linkability means "did the same person send?" and unlinkability means "did the same person receive?". So a system can be linkable or non-linkable, unlinkable or non-unlinkable. Annoying, I know. So when Nic van Saberhagen here says "...incoming payments [are] associated with one-time public keys which are unlinkable for a spectator," let’s see what he means. First, consider a situation in which Alice sends Bob two separate transactions from the same address to the same address. In the Bitcoin universe, Alice has already made the mistake of sending from the same address and so the transaction has failed our desire for limited linkability. Furthermore, since she sent the money to the same address, she’s failed our desire for unlinkability. This bitcoin transaction was both (totally) linkable and non-unlinkable. On the other hand, in the cryptonote universe, let’s say that Alice sends Bob some cryptonote, using Bob’s public address. She chooses as her obfuscating set of public keys all known public keys in the Washington DC metro area. Alex generates a one-time public key using her own information and Bob’s public information. She sends the money off, and any observer will only be able to glean "Someone from the Washington DC metro area sent 2.3 cryptonotes to the one-time public address XYZ123." We have a probabilistic control over linkability here, so we’ll call this "almost non-linkable." We also only see the one-time public keys money is sent to. Even if we suspected the receiver was Bob, we don’t have his private keys and so we can’t test whether a passing transaction belongs to Bob let alone generate his one-time private key to redeem his cryptonote. So this is, in fact, totally "unlinkable." So, this is the neatest trick of all. Who wants to really trust another MtGox? We may be comfortable storing some amount of BTC on Coinbase, but the ultimate in bitcoin security is a physical wallet. Which is inconvenient. In this case, you can trustlessly give away half of your private key without compromising your own ability to spend money. When doing this, all you are doing is telling someone how to break unlinkability. The other properties of CN acting like a currency are preserved, like proof against double spending and whatnot.
-
Bob can recover the corresponding one-time private key: \(x = H_s(aR) + b\), so as \(P = xG\). He can spend this output at any time by signing a transaction with \(x\). Transaction Tx public key Tx output Amount Destination key \(P' = H_s(aR)G + bG\) one-time public key \(x = H_s(aR) + b\) one-time private key Receiver’s private key \((a, b)\) \(R\) \(P'\) \(\stackrel{?}{=} P\) Fig. 5. Incoming transaction check. As a result Bob gets incoming payments, associated with one-time public keys which are unlinkable for a spectator. Some additional notes: • When Bob “recognizes” his transactions (see step 5) he practically uses only half of his private information: \((a, B)\). This pair, also known as the tracking key, can be passed to a third party (Carol). Bob can delegate her the processing of new transactions. Bob doesn’t need to explicitly trust Carol, because she can’t recover the one-time secret key \(p\) without Bob’s full private key \((a, b)\). This approach is useful when Bob lacks bandwidth or computation power (smartphones, hardware wallets etc.). • In case Alice wants to prove she sent a transaction to Bob’s address she can either disclose \(r\) or use any kind of zero-knowledge protocol to prove she knows \(r\) (for example by signing the transaction with \(r\)). • If Bob wants to have an audit compatible address where all incoming transaction are linkable, he can either publish his tracking key or use a truncated address. That address represent only one public ec-key \(B\), and the remaining part required by the protocol is derived from it as follows: \(a = H_s(B)\) and \(A = H_s(B)G\). In both cases every person is able to “recognize” all of Bob’s incoming transaction, but, of course, none can spend the funds enclosed within them without the secret key \(b\). 4.4 One-time ring signatures A protocol based on one-time ring signatures allows users to achieve unconditional unlinkability. Unfortunately, ordinary types of cryptographic signatures permit to trace transactions to their respective senders and receivers. Our solution to this deficiency lies in using a different signature type than those currently used in electronic cash systems. We will first provide a general description of our algorithm with no explicit reference to electronic cash. A one-time ring signature contains four algorithms: (GEN, SIG, VER, LNK): GEN: takes public parameters and outputs an ec-pair \((P, x)\) and a public key \(I\). SIG: takes a message \(m\), a set \(S'\) of public keys \(\{P_i\}_{i \neq s}\), a pair \((P_s, x_s)\) and outputs a signature \(\sigma\) and a set \(S = S' \cup \{P_s\}\). 8
- Bob can recover the corresponding one-time private key: \(x = H_s(aR) + b\), so as \(P = xG\). He can spend this output at any time by signing a transaction with \(x\). Transaction Tx public key Tx output Amount Destination key \(P' = H_s(aR)G + bG\) one-time public key \(x = H_s(aR) + b\) one-time private key Receiver’s private key \((a, b)\) \(R\) \(P'\) \(\stackrel{?}{=} P\) Fig. 5. Incoming transaction check. As a result Bob gets incoming payments, associated with one-time public keys which are unlinkable for a spectator. Some additional notes: • When Bob “recognizes” his transactions (see step 5) he practically uses only half of his private information: \((a, B)\). This pair, also known as the tracking key, can be passed to a third party (Carol). Bob can delegate her the processing of new transactions. Bob doesn’t need to explicitly trust Carol, because she can’t recover the one-time secret key \(p\) without Bob’s full private key \((a, b)\). This approach is useful when Bob lacks bandwidth or computation power (smartphones, hardware wallets etc.). • In case Alice wants to prove she sent a transaction to Bob’s address she can either disclose \(r\) or use any kind of zero-knowledge protocol to prove she knows \(r\) (for example by signing the transaction with \(r\)). • If Bob wants to have an audit compatible address where all incoming transaction are linkable, he can either publish his tracking key or use a truncated address. That address represent only one public ec-key \(B\), and the remaining part required by the protocol is derived from it as follows: \(a = H_s(B)\) and \(A = H_s(B)G\). In both cases every person is able to “recognize” all of Bob’s incoming transaction, but, of course, none can spend the funds enclosed within them without the secret key \(b\). 4.4 One-time ring signatures A protocol based on one-time ring signatures allows users to achieve unconditional unlinkability. Unfortunately, ordinary types of cryptographic signatures permit to trace transactions to their respective senders and receivers. Our solution to this deficiency lies in using a different signature type than those currently used in electronic cash systems. We will first provide a general description of our algorithm with no explicit reference to electronic cash. A one-time ring signature contains four algorithms: (GEN, SIG, VER, LNK): GEN: takes public parameters and outputs an ec-pair \((P, x)\) and a public key \(I\). SIG: takes a message \(m\), a set \(S'\) of public keys \(\{P_i\}_{i \neq s}\), a pair \((P_s, x_s)\) and outputs a signature \(\sigma\) and a set \(S = S' \cup \{P_s\}\). 8 16 Yes, so now we have a) a payment address and b) a payment ID. A critic could ask "do we really need to do this? After all, if a merchant receives 112.00678952 CN exactly, and that was my order, and I have a screenshot or a receipt or whatever, isn’t that insane degree of precision sufficient?" The answer is "maybe, most of the time, in day-to-day, face-to-face transactions." However, the more common situation (especially in the digial world) is this: a merchant sells a set of objects, each with a fixed price. Say object A is 0.001 CN, object B is 0.01 CN and object C is 0.1 CN. Now, if the merchant receives an order for 1.618 CN, there are many many (many!) ways to arrange an order for a customer. And so without some sort of payment ID, identifying the so-called "unique" order of a customer with the so-called "unique" cost of their order becomes impossible. Even funnier: if everything in my online store costs exactly 1.0 CN, and I get 1000 customers a day? And you want to prove that you bought exactly 3 objects two weeks ago? Without a payment ID? Good luck, buddy. Long story short: When Bob publishes a payment address, he may end up also publishing a payment ID as well (see, e.g. Poloniex XMR deposits). This is different than what is described in the text here where Alice is the one who generates the payment ID. There must be some way for Bob to generate a payment ID as well. \((a, B)\) Recall that the tracking key \((a, B)\) can be published; losing the secrecy of the value for ’a’ will not violate your ability to spend or allow folks to steal from you (I think... that would have to be proven), it will simply allow folks to see all incoming transactions. A truncated address, as described in this paragraph, simply takes the "private" part of the key and generates it from the "public" part. Revealing the value for ’a’ will remove non-linkability but will preserve the rest of the transactions. The author means "not unlinkable" because unlinkable refers to the receiver and linkable refers to the sender. It’s also clear the author didn’t realize that there were two different aspects to linkability. Since, after all, the transaction is a directed object on a graph, there will be two questions: "are these two transactions going to the same person?" and "are these two transactions coming from the same person?" This is a "no-going-back" policy under which the unlinkability property of CryptoNote is conditional. That is to say, Bob can choose his incoming transactions to be not unlinkable using this policy. This is a claim they prove under the Random Oracle Model. We’ll get to that; the Random Oracle has pros and cons.
VER: takes a message \(m\), a set \(S\), a signature \(\sigma\) and outputs "true" or "false". LNK: takes a set \(I = \{I_i\}\), a signature \(\sigma\) and outputs "linked" or "indep". The idea behind the protocol is fairly simple: a user produces a signature which can be checked by a set of public keys rather than a unique public key. The identity of the signer is indistinguishable from the other users whose public keys are in the set until the owner produces a second signature using the same keypair. Private keys \(x_0\) \(\cdots\) \(x_i\) \(\cdots\) \(x_n\) Public keys \(P_0\) \(\cdots\) \(P_i\) \(\cdots\) \(P_n\) Ring Signature sign verify Fig. 6. Ring signature anonymity. GEN: The signer picks a random secret key \(x \in [1, l-1]\) and computes the corresponding public key \(P = xG\). Additionally he computes another public key \(I = xH_p(P)\) which we will call the “key image”. SIG: The signer generates a one-time ring signature with a non-interactive zero-knowledge proof using the techniques from [21]. He selects a random subset \(S'\) of \(n\) from the other users’ public keys \(P_i\), his own keypair \((x, P)\) and key image \(I\). Let \(0 \leq s \leq n\) be signer’s secret index in \(S\) (so that his public key is \(P_s\)). He picks a random \(\{q_i \mid i = 0, \ldots, n\}\) and \(\{w_i \mid i = 0, \ldots, n, i \neq s\}\) from \((1, \ldots, l)\) and applies the following transformations: \[L_i = \begin{cases} q_iG & \text{if } i = s \\ q_iG + w_iP_i & \text{if } i \neq s \end{cases}\] \[R_i = \begin{cases} q_iH_p(P_i) & \text{if } i = s \\ q_iH_p(P_i) + w_iI & \text{if } i \neq s \end{cases}\] The next step is getting the non-interactive challenge: \(c = H_s(m, L_1, \ldots, L_n, R_1, \ldots, R_n)\) Finally the signer computes the response: \(c_i =\) wi, if i ̸= s c − nP i=0 ci mod l, if i = s ri = ( qi, if i ̸= s qs −csx mod l, if i = s The resulting signature is \(\sigma = (I, c_1, \ldots, c_n, r_1, \ldots, r_n)\). 9 VER: takes a message \(m\), a set \(S\), a signature \(\sigma\) and outputs “true” or “false”. LNK: takes a set \(\mathcal{I} = \{I_i\}\), a signature \(\sigma\) and outputs “linked” or “indep”. The idea behind the protocol is fairly simple: a user produces a signature which can be checked by a set of public keys rather than a unique public key. The identity of the signer is indistinguishable from the other users whose public keys are in the set until the owner produces a second signature using the same keypair. Private keys \(x_0\) \(\cdots\) \(x_i\) \(\cdots\) \(x_n\) Public keys \(P_0\) \(\cdots\) \(P_i\) \(\cdots\) \(P_n\) Ring Signature sign verify Fig. 6. Ring signature anonymity. GEN: The signer picks a random secret key \(x \in [1, l - 1]\) and computes the corresponding public key \(P = xG\). Additionally he computes another public key \(I = xH_p(P)\) which we will call the “key image”. SIG: The signer generates a one-time ring signature with a non-interactive zero-knowledge proof using the techniques from [21]. He selects a random subset \(S'\) of \(n\) from the other users’ public keys \(P_i\), his own keypair \((x, P)\) and key image \(I\). Let \(0 \leq s \leq n\) be signer’s secret index in \(S\) (so that his public key is \(P_s\)). He picks a random \(\{q_i \mid i = 0, \ldots, n\}\) and \(\{w_i \mid i = 0, \ldots, n, i \neq s\}\) from \((1, \ldots, l)\) and applies the following transformations: \[L_i = \begin{cases} q_i G, & \text{if } i = s \\\\ q_i G + w_i P_i, & \text{if } i \neq s \end{cases}\] \[R_i = \begin{cases} q_i H_p(P_i), & \text{if } i = s \\\\ q_i H_p(P_i) + w_i I, & \text{if } i \neq s \end{cases}\] The next step is getting the non-interactive challenge:
\[c = H_s(m, L_1, \ldots, L_n, R_1, \ldots, R_n)\] Finally the signer computes the response: \[c_i = \begin{cases} w_i, & \text{if } i \neq s \\\\ c - \sum_{i=0}^{n} c_i \mod l, & \text{if } i = s \end{cases}\] \[r_i = \begin{cases} q_i, & \text{if } i \neq s \\ q_s - c_s x \mod l, & \text{if } i = s \end{cases}\] The resulting signature is \(\sigma = (I, c_1, \ldots, c_n, r_1, \ldots, r_n)\). 9 17 Perhaps this is stupid, but care must be taken when unioning S and P_s. If you just append the last public key to the end, unlinkability is broken because anyone checking passing transactions can just check the last public key listed in each transaction and boom. That’s the public key associated with the sender. So after unioning, a pseudorandom number generator must be used to permute the public keys chosen. "...until the owner produces a second signature using the same keypair." I wish the author(s?) would elaborate on this. I believe this means "make sure that every time you choose a set of public keys to obfuscate yourself with, you pick a completely new set with no two keys alike." Which seems like a pretty strong condition to place upon unlinkability. Perhaps "you pick a new random set from all possible keys" with the assumption that, although nontrivial intersections will inevitably happen, they won’t happen often. Either way, I need to dig deeper into this statement. This is generating the ring signature. Zero-knowledge proofs are awesome: I challenge you to prove to me that you know a secret without revealing the secret. For example, say we are at the entrance of a donut-shaped cave, and at the back of the cave (beyond sight from the entrance) is a one-way door to which you claim you have the key. If you go one direction, it always lets you through, but if you go the other direction, you need a key. But you don’t even want to SHOW me the key, let alone show me that it opens the door. But you want to prove to me that you know how to open the door. In the interactive setting, I flip a coin. Heads is left, tails is right, and you go down the donut-shaped cave whichever way the coin directs you. At the back, beyond my sight, you open the door to come back around the other side. We repeat the coin-flipping experiment until I’m satisfied that you have the key. But that’s clearly the INTERACTIVE zero-knowledge proof. There are non-interactive versions in which you and I never have to communicate; this way, no eavesdroppers can interfere. http://en.wikipedia.org/wiki/Zero-knowledge_proof This is reversed from the previous definition.
VER: takes a message \(m\), a set \(S\), a signature \(\sigma\) and outputs “true” or “false”. LNK: takes a set \(\mathcal{I} = \{I_i\}\), a signature \(\sigma\) and outputs “linked” or “indep”. The idea behind the protocol is fairly simple: a user produces a signature which can be checked by a set of public keys rather than a unique public key. The identity of the signer is indistinguishable from the other users whose public keys are in the set until the owner produces a second signature using the same keypair. Private keys \(x_0\) \(\cdots\) \(x_i\) \(\cdots\) \(x_n\) Public keys \(P_0\) \(\cdots\) \(P_i\) \(\cdots\) \(P_n\) Ring Signature sign verify Fig. 6. Ring signature anonymity. GEN: The signer picks a random secret key \(x \in [1, l - 1]\) and computes the corresponding public key \(P = xG\). Additionally he computes another public key \(I = xH_p(P)\) which we will call the “key image”. SIG: The signer generates a one-time ring signature with a non-interactive zero-knowledge proof using the techniques from [21]. He selects a random subset \(S'\) of \(n\) from the other users’ public keys \(P_i\), his own keypair \((x, P)\) and key image \(I\). Let \(0 \leq s \leq n\) be signer’s secret index in \(S\) (so that his public key is \(P_s\)). He picks a random \(\{q_i \mid i = 0, \ldots, n\}\) and \(\{w_i \mid i = 0, \ldots, n, i \neq s\}\) from \((1, \ldots, l)\) and applies the following transformations: \[L_i = \begin{cases} q_i G, & \text{if } i = s \\\\ q_i G + w_i P_i, & \text{if } i \neq s \end{cases}\] \[R_i = \begin{cases} q_i H_p(P_i), & \text{if } i = s \\\\ q_i H_p(P_i) + w_i I, & \text{if } i \neq s \end{cases}\] The next step is getting the non-interactive challenge:
\[c = H_s(m, L_1, \ldots, L_n, R_1, \ldots, R_n)\] Finally the signer computes the response: \[c_i = \begin{cases} w_i, & \text{if } i \neq s \\\\ c - \sum_{i=0}^{n} c_i \mod l, & \text{if } i = s \end{cases}\] \[r_i = \begin{cases} q_i, & \text{if } i \neq s \\ q_s - c_s x \mod l, & \text{if } i = s \end{cases}\] The resulting signature is \(\sigma = (I, c_1, \ldots, c_n, r_1, \ldots, r_n)\). 9 VER: takes a message \(m\), a set \(S\), a signature \(\sigma\) and outputs “true” or “false”. LNK: takes a set \(\mathcal{I} = \{I_i\}\), a signature \(\sigma\) and outputs “linked” or “indep”. The idea behind the protocol is fairly simple: a user produces a signature which can be checked by a set of public keys rather than a unique public key. The identity of the signer is indistinguishable from the other users whose public keys are in the set until the owner produces a second signature using the same keypair. Private keys \(x_0\) \(\cdots\) \(x_i\) \(\cdots\) \(x_n\) Public keys \(P_0\) \(\cdots\) \(P_i\) \(\cdots\) \(P_n\) Ring Signature sign verify Fig. 6. Ring signature anonymity. GEN: The signer picks a random secret key \(x \in [1, l - 1]\) and computes the corresponding public key \(P = xG\). Additionally he computes another public key \(I = xH_p(P)\) which we will call the “key image”. SIG: The signer generates a one-time ring signature with a non-interactive zero-knowledge proof using the techniques from [21]. He selects a random subset \(S'\) of \(n\) from the other users’ public keys \(P_i\), his own keypair \((x, P)\) and key image \(I\). Let \(0 \leq s \leq n\) be signer’s secret index in \(S\) (so that his public key is \(P_s\)). He picks a random \(\{q_i \mid i = 0, \ldots, n\}\) and \(\{w_i \mid i = 0, \ldots, n, i \neq s\}\) from \((1, \ldots, l)\) and applies the following transformations: \[L_i = \begin{cases} q_i G, & \text{if } i = s \\\\ q_i G + w_i P_i, & \text{if } i \neq s \end{cases}\] \[R_i = \begin{cases} q_i H_p(P_i), & \text{if } i = s \\\\ q_i H_p(P_i) + w_i I, & \text{if } i \neq s \end{cases}\] The next step is getting the non-interactive challenge:
\[c = H_s(m, L_1, \ldots, L_n, R_1, \ldots, R_n)\] Finally the signer computes the response: \[c_i = \begin{cases} w_i, & \text{if } i \neq s \\\\ c - \sum_{i=0}^{n} c_i \mod l, & \text{if } i = s \end{cases}\] \[r_i = \begin{cases} q_i, & \text{if } i \neq s \\ q_s - c_s x \mod l, & \text{if } i = s \end{cases}\] The resulting signature is \(\sigma = (I, c_1, \ldots, c_n, r_1, \ldots, r_n)\). 9 18 This whole area is cryptonote agnostic, simply describing the ring signature algorithm without reference to currencies. I suspect some of the notation is consistent with the rest of the paper, though. For example, x is the "random" secret key chosen in GEN, which gives public key P and public key image I. This value of x is the value Bob computes in part 6 page 8. So this is starting to clear up some of the confusion from the previous description. This is kind of cool; money isn’t being transferred from "Alice’s public address to Bob’s public address." It’s being transferred from one-time address to one-time address. So, in a sense, here’s how stuffis working. If Alex has some cryptonotes because someone sent them to her, this means she has the private keys needed to send them to Bob. She uses a Diffie-Hellman exchange using Bob’s public information to generate a new one-time address and the cryptonotes are transferred to that address. Now, since a (presumably secure) DH exchange was used to generate the new one-time address to which Alex sent her CN, Bob is the only one with the private keys needed to repeat the above. So now, Bob is Alex. http://en.wikipedia.org/wiki/Piecewise#Notation_and_interpretation Summation should be indexed over j not i. Each c_i is random junk (since w_i is random) except for the c_i associated with the actual key involved in this signature. The value of c is a hash of the previous information. I think this may contain a typo worse than re-using the index ’i,’ though, because c_s seems to be implicitly, not explicitly, defined. Indeed, if we take this equation on faith, then we determine that c_s = (1/2)c - (1/2) sum_i neq s c_i. That is, a hash minus a whole bunch of random numbers. On the other hand, if this summation is intended to be read "c_s = (c - sum_j neq s c_j) mod l", then we take the hash of our previous information, generate a bunch of random numbers, subtract all of those random numbers offthe hash, and that gives us c_s. This seems to be what "should" be happening given my intuition, and matches the verification step on page 10. But intuition is not mathematics. I’ll dig deeper into this. Same as before; all of these will be random junk except for the one associated with the actual signer’s public key x. Except this time, this is more what I would expect from the structure: r_i is random for i!=s and r_s is determined only by the secret x and the s-indexed values of q_i and c_i.
VER: The verifier checks the signature by applying the inverse transformations:
\[L'_i = r_i G + c_i P_i\]
\[R'_i = r_i H_p(P_i) + c_i I\] Finally, the verifier checks if
\[\sum_{i=0}^{n} c_i \stackrel{?}{=} H_s(m, L'_0, \ldots, L'_n, R'_0, \ldots, R'_n) \mod l\] If this equality is correct, the verifier runs the algorithm LNK. Otherwise the verifier rejects the signature. LNK: The verifier checks if \(I\) has been used in past signatures (these values are stored in the set \(\mathcal{I}\)). Multiple uses imply that two signatures were produced under the same secret key. The meaning of the protocol: by applying L-transformations the signer proves that he knows such \(x\) that at least one \(P_i = xG\). To make this proof non-repeatable we introduce the key image as \(I = xH_p(P)\). The signer uses the same coefficients \((r_i, c_i)\) to prove almost the same statement: he knows such \(x\) that at least one \(H_p(P_i) = I \cdot x^{-1}\). If the mapping \(x \to I\) is an injection: 1. Nobody can recover the public key from the key image and identify the signer; 2. The signer cannot make two signatures with different \(I\)'s and the same \(x\). A full security analysis is provided in Appendix A. 4.5 Standard CryptoNote transaction By combining both methods (unlinkable public keys and untraceable ring signature) Bob achieves new level of privacy in comparison with the original Bitcoin scheme. It requires him to store only one private key \((a, b)\) and publish \((A, B)\) to start receiving and sending anonymous transactions. While validating each transaction Bob additionally performs only two elliptic curve multiplications and one addition per output to check if a transaction belongs to him. For his every output Bob recovers a one-time keypair \((p_i, P_i)\) and stores it in his wallet. Any inputs can be circumstantially proved to have the same owner only if they appear in a single transaction. In fact this relationship is much harder to establish due to the one-time ring signature. With a ring signature Bob can effectively hide every input among somebody else’s; all possible spenders will be equiprobable, even the previous owner (Alice) has no more information than any observer. When signing his transaction Bob specifies \(n\) foreign outputs with the same amount as his output, mixing all of them without the participation of other users. Bob himself (as well as anybody else) does not know if any of these payments have been spent: an output can be used in thousands of signatures as an ambiguity factor and never as a target of hiding. The double spend check occurs in the LNK phase when checking against the used key images set. Bob can choose the ambiguity degree on his own: \(n = 1\) means that the probability he has spent the output is 50% probability, \(n = 99\) gives 1%. The size of the resulting signature increases linearly as \(O(n+1)\), so the improved anonymity costs to Bob extra transaction fees. He also can set \(n = 0\) and make his ring signature to consist of only one element, however this will instantly reveal him as a spender. 10 VER: The verifier checks the signature by applying the inverse transformations:
\[L'_i = r_i G + c_i P_i\]
\[R'_i = r_i H_p(P_i) + c_i I\] Finally, the verifier checks if
\[\sum_{i=0}^{n} c_i \stackrel{?}{=} H_s(m, L'_0, \ldots, L'_n, R'_0, \ldots, R'_n) \mod l\] If this equality is correct, the verifier runs the algorithm LNK. Otherwise the verifier rejects the signature. LNK: The verifier checks if \(I\) has been used in past signatures (these values are stored in the set \(\mathcal{I}\)). Multiple uses imply that two signatures were produced under the same secret key. The meaning of the protocol: by applying L-transformations the signer proves that he knows such \(x\) that at least one \(P_i = xG\). To make this proof non-repeatable we introduce the key image as \(I = xH_p(P)\). The signer uses the same coefficients \((r_i, c_i)\) to prove almost the same statement: he knows such \(x\) that at least one \(H_p(P_i) = I \cdot x^{-1}\). If the mapping \(x \to I\) is an injection: 1. Nobody can recover the public key from the key image and identify the signer; 2. The signer cannot make two signatures with different \(I\)'s and the same \(x\). A full security analysis is provided in Appendix A. 4.5 Standard CryptoNote transaction By combining both methods (unlinkable public keys and untraceable ring signature) Bob achieves new level of privacy in comparison with the original Bitcoin scheme. It requires him to store only one private key \((a, b)\) and publish \((A, B)\) to start receiving and sending anonymous transactions. While validating each transaction Bob additionally performs only two elliptic curve multiplications and one addition per output to check if a transaction belongs to him. For his every output Bob recovers a one-time keypair \((p_i, P_i)\) and stores it in his wallet. Any inputs can be circumstantially proved to have the same owner only if they appear in a single transaction. In fact this relationship is much harder to establish due to the one-time ring signature. With a ring signature Bob can effectively hide every input among somebody else’s; all possible spenders will be equiprobable, even the previous owner (Alice) has no more information than any observer. When signing his transaction Bob specifies \(n\) foreign outputs with the same amount as his output, mixing all of them without the participation of other users. Bob himself (as well as anybody else) does not know if any of these payments have been spent: an output can be used in thousands of signatures as an ambiguity factor and never as a target of hiding. The double spend check occurs in the LNK phase when checking against the used key images set. Bob can choose the ambiguity degree on his own: \(n = 1\) means that the probability he has spent the output is 50% probability, \(n = 99\) gives 1%. The size of the resulting signature increases linearly as \(O(n+1)\), so the improved anonymity costs to Bob extra transaction fees. He also can set \(n = 0\) and make his ring signature to consist of only one element, however this will instantly reveal him as a spender. 10 19 At this point, I’m terribly confused. Alex receives a message M with signature (I,c_1, ..., c_n, r_1, ..., r_n) and list of public keys S. and she runs VER. This will compute L_i’ and R_i’ This verifies that c_s = c - sum_i neq s c_i on the previous page. At first I was VERy (ha) confused. Anyone can compute L_i’ and R_i’. Indeed, each r_i and c_i have been published in the signature sigma together with the value for I. The set S = P_i of all public keys has also been published. So anyone who has seen sigma and the set of keys S = P_i will get the same values for L_i’ and R_i’ and hence check the signature. But then I remembered this section is simply describing a signature algorithm, not a "check if signed, check if SENT TO ME, and if so, then go spend the money." This is SIMPLY the signature part of the game. I’m interested to read Appendix A when I finally get there. I would like to see a full-scale operation-by-operation comparison of Cryptonote to Bitcoin. Also, electricity/sustainability. What pieces of the algorithms constitute "input" here? Transaction input, I believe, is an Amount and a set of UTXOs that sum to a greater amount than the Amount. This is unclear. "Target of hiding?" I have thought about this for a few minutes now and I still haven’t the foggiest idea of what it could mean. A double-spend attack can be executed only by manipulating a node’s perceived used-key images set \(I\). "Ambiguity degree" = n but the total number of public keys included in the transaction is n+1. That is to say, ambiguity degree would be "how many OTHER people do you want in the crowd?" The answer will probably be, by default "as many as possible."
VER: The verifier checks the signature by applying the inverse transformations:
\[L'_i = r_i G + c_i P_i\]
\[R'_i = r_i H_p(P_i) + c_i I\] Finally, the verifier checks if
\[\sum_{i=0}^{n} c_i \stackrel{?}{=} H_s(m, L'_0, \ldots, L'_n, R'_0, \ldots, R'_n) \mod l\] If this equality is correct, the verifier runs the algorithm LNK. Otherwise the verifier rejects the signature. LNK: The verifier checks if \(I\) has been used in past signatures (these values are stored in the set \(\mathcal{I}\)). Multiple uses imply that two signatures were produced under the same secret key. The meaning of the protocol: by applying L-transformations the signer proves that he knows such \(x\) that at least one \(P_i = xG\). To make this proof non-repeatable we introduce the key image as \(I = xH_p(P)\). The signer uses the same coefficients \((r_i, c_i)\) to prove almost the same statement: he knows such \(x\) that at least one \(H_p(P_i) = I \cdot x^{-1}\). If the mapping \(x \to I\) is an injection: 1. Nobody can recover the public key from the key image and identify the signer; 2. The signer cannot make two signatures with different \(I\)'s and the same \(x\). A full security analysis is provided in Appendix A. 4.5 Standard CryptoNote transaction By combining both methods (unlinkable public keys and untraceable ring signature) Bob achieves new level of privacy in comparison with the original Bitcoin scheme. It requires him to store only one private key \((a, b)\) and publish \((A, B)\) to start receiving and sending anonymous transactions. While validating each transaction Bob additionally performs only two elliptic curve multiplications and one addition per output to check if a transaction belongs to him. For his every output Bob recovers a one-time keypair \((p_i, P_i)\) and stores it in his wallet. Any inputs can be circumstantially proved to have the same owner only if they appear in a single transaction. In fact this relationship is much harder to establish due to the one-time ring signature. With a ring signature Bob can effectively hide every input among somebody else’s; all possible spenders will be equiprobable, even the previous owner (Alice) has no more information than any observer. When signing his transaction Bob specifies \(n\) foreign outputs with the same amount as his output, mixing all of them without the participation of other users. Bob himself (as well as anybody else) does not know if any of these payments have been spent: an output can be used in thousands of signatures as an ambiguity factor and never as a target of hiding. The double spend check occurs in the LNK phase when checking against the used key images set. Bob can choose the ambiguity degree on his own: \(n = 1\) means that the probability he has spent the output is 50% probability, \(n = 99\) gives 1%. The size of the resulting signature increases linearly as \(O(n+1)\), so the improved anonymity costs to Bob extra transaction fees. He also can set \(n = 0\) and make his ring signature to consist of only one element, however this will instantly reveal him as a spender. 10 VER: The verifier checks the signature by applying the inverse transformations:
\[L'_i = r_i G + c_i P_i\]
\[R'_i = r_i H_p(P_i) + c_i I\] Finally, the verifier checks if
\[\sum_{i=0}^{n} c_i \stackrel{?}{=} H_s(m, L'_0, \ldots, L'_n, R'_0, \ldots, R'_n) \mod l\] If this equality is correct, the verifier runs the algorithm LNK. Otherwise the verifier rejects the signature. LNK: The verifier checks if \(I\) has been used in past signatures (these values are stored in the set \(\mathcal{I}\)). Multiple uses imply that two signatures were produced under the same secret key. The meaning of the protocol: by applying L-transformations the signer proves that he knows such \(x\) that at least one \(P_i = xG\). To make this proof non-repeatable we introduce the key image as \(I = xH_p(P)\). The signer uses the same coefficients \((r_i, c_i)\) to prove almost the same statement: he knows such \(x\) that at least one \(H_p(P_i) = I \cdot x^{-1}\). If the mapping \(x \to I\) is an injection: 1. Nobody can recover the public key from the key image and identify the signer; 2. The signer cannot make two signatures with different \(I\)'s and the same \(x\). A full security analysis is provided in Appendix A. 4.5 Standard CryptoNote transaction By combining both methods (unlinkable public keys and untraceable ring signature) Bob achieves new level of privacy in comparison with the original Bitcoin scheme. It requires him to store only one private key \((a, b)\) and publish \((A, B)\) to start receiving and sending anonymous transactions. While validating each transaction Bob additionally performs only two elliptic curve multiplications and one addition per output to check if a transaction belongs to him. For his every output Bob recovers a one-time keypair \((p_i, P_i)\) and stores it in his wallet. Any inputs can be circumstantially proved to have the same owner only if they appear in a single transaction. In fact this relationship is much harder to establish due to the one-time ring signature. With a ring signature Bob can effectively hide every input among somebody else’s; all possible spenders will be equiprobable, even the previous owner (Alice) has no more information than any observer. When signing his transaction Bob specifies \(n\) foreign outputs with the same amount as his output, mixing all of them without the participation of other users. Bob himself (as well as anybody else) does not know if any of these payments have been spent: an output can be used in thousands of signatures as an ambiguity factor and never as a target of hiding. The double spend check occurs in the LNK phase when checking against the used key images set. Bob can choose the ambiguity degree on his own: \(n = 1\) means that the probability he has spent the output is 50% probability, \(n = 99\) gives 1%. The size of the resulting signature increases linearly as \(O(n+1)\), so the improved anonymity costs to Bob extra transaction fees. He also can set \(n = 0\) and make his ring signature to consist of only one element, however this will instantly reveal him as a spender. 10 20 This is interesting; earlier, we provided a way for a receiver, Bob, to make all INCOMING transactions non-unlinkable either by choosing half of his private keys deterministically or by publishing half his private keys as public. This is a no-going-back sort of policy. Here, we see a way of a sender, Alex, to choose a single outgoing transaction as linkable, but in fact this reveals Alex as the sender to the whole network. This is NOT a no-going-back sort of policy. This is transaction-by-transaction. Is there a third policy? Can a receiver, Bob, generate a unique payment ID for Alex that never changes, perhaps using a Diffie-Hellman exchange? If anyone includes that payment ID bundled somewhere in her transaction to Bob’s address, it must have come from Alex. This way, Alex need not reveal herself to the whole network by choosing to link a particular transaction, but she can still identify herself to the person to whom she sends her money. Isn’t this what Poloniex does?
Transaction Tx input \(\text{Output}_0\) \(\ldots\) \(\text{Output}_i\) \(\ldots\) \(\text{Output}_n\) Key image Signatures Ring Signature Destination key Output1 Destination key Outputn Foreign transactions Sender’s output Destination key One-time keypair One-time private key \(I = xH_p(P)\) \(P\), \(x\) Fig. 7. Ring signature generation in a standard transaction. 5 Egalitarian Proof-of-work In this section we propose and ground the new proof-of-work algorithm. Our primary goal is to close the gap between CPU (majority) and GPU/FPGA/ASIC (minority) miners. It is appropriate that some users can have a certain advantage over others, but their investments should grow at least linearly with the power. More generally, producing special-purpose devices has to be as less profitable as possible. 5.1 Related works The original Bitcoin proof-of-work protocol uses the CPU-intensive pricing function SHA-256. It mainly consists of basic logical operators and relies solely on the computational speed of processor, therefore is perfectly suitable for multicore/conveyer implementation. However, modern computers are not limited by the number of operations per second alone, but also by memory size. While some processors can be substantially faster than others [8], memory sizes are less likely to vary between machines. Memory-bound price functions were first introduced by Abadi et al and were defined as “functions whose computation time is dominated by the time spent accessing memory” [15]. The main idea is to construct an algorithm allocating a large block of data (“scratchpad”) within memory that can be accessed relatively slowly (for example, RAM) and “accessing an unpredictable sequence of locations” within it. A block should be large enough to make preserving the data more advantageous than recomputing it for each access. The algorithm also should prevent internal parallelism, hence \(N\) simultaneous threads should require \(N\) times more memory at once. Dwork et al [22] investigated and formalized this approach leading them to suggest another variant of the pricing function: “Mbound”. One more work belongs to F. Coelho [20], who 11 Transaction Tx input \(\text{Output}_0\) \(\ldots\) \(\text{Output}_i\) \(\ldots\) \(\text{Output}_n\) Key image Signatures Ring Signature Destination key Output1 Destination key Outputn Foreign transactions Sender’s output Destination key One-time keypair One-time private key \(I = xH_p(P)\) \(P\), \(x\) Fig. 7. Ring signature generation in a standard transaction. 5 Egalitarian Proof-of-work In this section we propose and ground the new proof-of-work algorithm. Our primary goal is to close the gap between CPU (majority) and GPU/FPGA/ASIC (minority) miners. It is appropriate that some users can have a certain advantage over others, but their investments should grow at least linearly with the power. More generally, producing special-purpose devices has to be as less profitable as possible. 5.1 Related works The original Bitcoin proof-of-work protocol uses the CPU-intensive pricing function SHA-256. It mainly consists of basic logical operators and relies solely on the computational speed of processor, therefore is perfectly suitable for multicore/conveyer implementation. However, modern computers are not limited by the number of operations per second alone, but also by memory size. While some processors can be substantially faster than others [8], memory sizes are less likely to vary between machines. Memory-bound price functions were first introduced by Abadi et al and were defined as “functions whose computation time is dominated by the time spent accessing memory” [15]. The main idea is to construct an algorithm allocating a large block of data (“scratchpad”) within memory that can be accessed relatively slowly (for example, RAM) and “accessing an unpredictable sequence of locations” within it. A block should be large enough to make preserving the data more advantageous than recomputing it for each access. The algorithm also should prevent internal parallelism, hence \(N\) simultaneous threads should require \(N\) times more memory at once. Dwork et al [22] investigated and formalized this approach leading them to suggest another variant of the pricing function: "Mbound". One more work belongs to F. Coelho [20], who 11 21 These are, ostensibly, our UTXO’s: amounts and destination keys. If Alex is the one constructing this standard transaction and is sending to Bob, then Alex also has the private keys to each of these. I like this diagram a whole lot, because it answers some earlier questions. A Txn input consists of a set of Txn outputs and a key image. It is then signed with a ring signature, including all of the private keys Alex owns to all of the foreign transactions wrapped up in the deal. The Txn output consists of an amount and a destination key. The receiver of the transaction may, at will, generate their one-time private key as described earlier in the paper in order to spend the money. It will be delightful to find out how much this matches the actual code... No, Nic van Saberhagen describes loosely some properties of a proof of work algorithm, without actually describing that algorithm. The CryptoNight algorithm itself will REQUIRE a deep analysis. When I read this, I stuttered. Should investment grow at least linearly with power, or should investment grow at most linearly with power? And then I realized; I, as a miner, or an investor, usually think of "how much power can I get for an investment?" not "how much investment is required for a fixed amount of power?" Of course, denote investment by \(I\) and power by \(P\). If \(I(P)\) is investment as a function of power and \(P(I)\) is power as a function of investment, they'll be inverses of each other (wherever inverses can exist). And if \(I(P)\) is faster-than-linear than \(P(I)\) is slower-than-linear. Hence, there will be a reduced rate of returns for investors. That is to say, what the author is saying here is: "sure, as you invest more, you’ll get more power. But we should try to make that a reduced rate of returns thing." CPU investments will cap out sub-linearly, eventually; the question is whether the authors have designed a POW algorithm that will force the ASICs to also do this. Should a hypothetical "future currency" always mine with the slowest/most limited resources? The paper by Abadi et al, (which has some Google and Microsoft engineers as authors) is, essentially, using the fact that for the past few years memory size has had a much smaller variance across machines than processor speed, and with a more-than-linear investment-forpower ratio. In a few years, this may have to be re-assessed! Everything is an arms race... Constructing a hash function is difficult; constructing a hash function satisfying these constraints seems to be more difficult. This paper seems to have no explanation of the actual hashing algorithm CryptoNight. I think it’s a memory-hard implementation of SHA-3, based on forum posts but I have no idea... and that’s the point. It must be explained.
proposed the most effective solution: “Hokkaido”. To our knowledge the last work based on the idea of pseudo-random searches in a big array is the algorithm known as “scrypt” by C. Percival [32]. Unlike the previous functions it focuses on key derivation, and not proof-of-work systems. Despite this fact scrypt can serve our purpose: it works well as a pricing function in the partial hash conversion problem such as SHA-256 in Bitcoin. By now scrypt has already been applied in Litecoin [14] and some other Bitcoin forks. However, its implementation is not really memory-bound: the ratio “memory access time / overall time” is not large enough because each instance uses only 128 KB. This permits GPU miners to be roughly 10 times more effective and continues to leave the possibility of creating relatively cheap but highly-efficient mining devices. Moreover, the scrypt construction itself allows a linear trade-offbetween memory size and CPU speed due to the fact that every block in the scratchpad is derived only from the previous. For example, you can store every second block and recalculate the others in a lazy way, i.e. only when it becomes necessary. The pseudo-random indexes are assumed to be uniformly distributed, hence the expected value of the additional blocks' recalculations is \(\frac{1}{2} \cdot N\), where \(N\) is the number of iterations. The overall computation time increases less than by half because there are also time independent (constant time) operations such as preparing the scratchpad and hashing on every iteration. Saving 2/3 of the memory costs \(\frac{1}{3} \cdot N + \frac{1}{3} \cdot 2 \cdot N = N\) additional recalculations; 9/10 results in \(\frac{1}{10} \cdot N + \ldots + \frac{1}{10} \cdot 9 \cdot N = 4.5N\). It is easy to show that storing only \(\frac{1}{s}\) of all blocks increases the time less than by a factor of \(\frac{s-1}{2}\). This in turn implies that a machine with a CPU 200 times faster than the modern chips can store only 320 bytes of the scratchpad. 5.2 The proposed algorithm We propose a new memory-bound algorithm for the proof-of-work pricing function. It relies on random access to a slow memory and emphasizes latency dependence. As opposed to scrypt every new block (64 bytes in length) depends on all the previous blocks. As a result a hypothetical "memory-saver" should increase his calculation speed exponentially. Our algorithm requires about 2 Mb per instance for the following reasons: 1. It fits in the L3 cache (per core) of modern processors, which should become mainstream in a few years; 2. A megabyte of internal memory is an almost unacceptable size for a modern ASIC pipeline; 3. GPUs may run hundreds of concurrent instances, but they are limited in other ways: GDDR5 memory is slower than the CPU L3 cache and remarkable for its bandwidth, not random access speed. 4. Significant expansion of the scratchpad would require an increase in iterations, which in turn implies an overall time increase. "Heavy" calls in a trust-less p2p network may lead to serious vulnerabilities, because nodes are obliged to check every new block's proof-of-work. If a node spends a considerable amount of time on each hash evaluation, it can be easily DDoSed by a flood of fake objects with arbitrary work data (nonce values). 12 proposed the most effective solution: "Hokkaido". To our knowledge the last work based on the idea of pseudo-random searches in a big array is the algorithm known as “scrypt” by C. Percival [32]. Unlike the previous functions it focuses on key derivation, and not proof-of-work systems. Despite this fact scrypt can serve our purpose: it works well as a pricing function in the partial hash conversion problem such as SHA-256 in Bitcoin. By now scrypt has already been applied in Litecoin [14] and some other Bitcoin forks. However, its implementation is not really memory-bound: the ratio “memory access time / overall time” is not large enough because each instance uses only 128 KB. This permits GPU miners to be roughly 10 times more effective and continues to leave the possibility of creating relatively cheap but highly-efficient mining devices. Moreover, the scrypt construction itself allows a linear trade-offbetween memory size and CPU speed due to the fact that every block in the scratchpad is derived only from the previous. For example, you can store every second block and recalculate the others in a lazy way, i.e. only when it becomes necessary. The pseudo-random indexes are assumed to be uniformly distributed, hence the expected value of the additional blocks’ recalculations is \(\frac{1}{2} \cdot N\), where \(N\) is the number of iterations. The overall computation time increases less than by half because there are also time independent (constant time) operations such as preparing the scratchpad and hashing on every iteration. Saving 2/3 of the memory costs \(\frac{1}{3} \cdot N + \frac{1}{3} \cdot 2 \cdot N = N\) additional recalculations; 9/10 results in \(\frac{1}{10} \cdot N + \ldots + \frac{1}{10} \cdot 9 \cdot N = 4.5N\). It is easy to show that storing only \(\frac{1}{s}\) of all blocks increases the time less than by a factor of \(\frac{s-1}{2}\). This in turn implies that a machine with a CPU 200 times faster than the modern chips can store only 320 bytes of the scratchpad. 5.2 The proposed algorithm We propose a new memory-bound algorithm for the proof-of-work pricing function. It relies on random access to a slow memory and emphasizes latency dependence. As opposed to scrypt every new block (64 bytes in length) depends on all the previous blocks. As a result a hypothetical “memory-saver” should increase his calculation speed exponentially. Our algorithm requires about 2 Mb per instance for the following reasons: 1. It fits in the L3 cache (per core) of modern processors, which should become mainstream in a few years; 2. A megabyte of internal memory is an almost unacceptable size for a modern ASIC pipeline; 3. GPUs may run hundreds of concurrent instances, but they are limited in other ways: GDDR5 memory is slower than the CPU L3 cache and remarkable for its bandwidth, not random access speed. 4. Significant expansion of the scratchpad would require an increase in iterations, which in turn implies an overall time increase. “Heavy” calls in a trust-less p2p network may lead to serious vulnerabilities, because nodes are obliged to check every new block’s proof-of-work. If a node spends a considerable amount of time on each hash evaluation, it can be easily DDoSed by a flood of fake objects with arbitrary work data (nonce values). 12 22 Nevermind, it’s a scrypt coin? Where is the algorithm? All I see is an advertisement. This is where Cryptonote, if their PoW algorithm is worthwhile, will really shine. It’s not really SHA-256, it’s not really scrypt. It’s new, memory bound, and non-recursive.
6 Further advantages 6.1 Smooth emission The upper bound for the overall amount of CryptoNote digital coins is: \(M_{Supply} = 2^{64} - 1\) atomic units. This is a natural restriction based only on implementation limits, not on intuition such as “N coins ought to be enough for anybody”. To ensure the smoothness of the emission process we use the following formula for block rewards: \(BaseReward = (M_{Supply} - A) \gg 18\), where \(A\) is amount of previously generated coins. 6.2 Adjustable parameters 6.2.1 Difficulty CryptoNote contains a targeting algorithm which changes the difficulty of every block. This decreases the system’s reaction time when the network hashrate is intensely growing or shrinking, preserving a constant block rate. The original Bitcoin method calculates the relation of actual and target time-span between the last 2016 blocks and uses it as the multiplier for the current difficulty. Obviously this is unsuitable for rapid recalculations (because of large inertia) and results in oscillations. The general idea behind our algorithm is to sum all the work completed by the nodes and divide it by the time they have spent. The measure of work is the corresponding difficulty values in each block. But due to inaccurate and untrusted timestamps we cannot determine the exact time interval between blocks. A user can shift his timestamp into the future and the next time intervals might be improbably small or even negative. Presumably there will be few incidents of this kind, so we can just sort the timestamps and cut-offthe outliers (i.e. 20%). The range of the rest values is the time which was spent for 80% of the corresponding blocks. 6.2.2 Size limits Users pay for storing the blockchain and shall be entitled to vote for its size. Every miner deals with the trade-offbetween balancing the costs and profit from the fees and sets his own “soft-limit” for creating blocks. Also the core rule for the maximum block size is necessary for preventing the blockchain from being flooded with bogus transaction, however this value should not be hard-coded. Let \(M_N\) be the median value of the last \(N\) blocks sizes. Then the “hard-limit” for the size of accepting blocks is \(2 \cdot M_N\). It averts the blockchain from bloating but still allows the limit to slowly grow with time if necessary. Transaction size does not need to be limited explicitly. It is bounded by the size of a block; and if somebody wants to create a huge transaction with hundreds of inputs/outputs (or with the high ambiguity degree in ring signatures), he can do so by paying sufficient fee. 6.2.3 Excess size penalty A miner still has the ability to stuffa block full of his own zero-fee transactions up to its maximum size \(2 \cdot M_b\). Even though only the majority of miners can shift the median value, there is still a 13 6 Further advantages 6.1 Smooth emission The upper bound for the overall amount of CryptoNote digital coins is: \(M_{Supply} = 2^{64} - 1\) atomic units. This is a natural restriction based only on implementation limits, not on intuition such as “N coins ought to be enough for anybody”. To ensure the smoothness of the emission process we use the following formula for block rewards: \(BaseReward = (M_{Supply} - A) \gg 18\), where \(A\) is amount of previously generated coins. 6.2 Adjustable parameters 6.2.1 Difficulty CryptoNote contains a targeting algorithm which changes the difficulty of every block. This decreases the system’s reaction time when the network hashrate is intensely growing or shrinking, preserving a constant block rate. The original Bitcoin method calculates the relation of actual and target time-span between the last 2016 blocks and uses it as the multiplier for the current difficulty. Obviously this is unsuitable for rapid recalculations (because of large inertia) and results in oscillations. The general idea behind our algorithm is to sum all the work completed by the nodes and divide it by the time they have spent. The measure of work is the corresponding difficulty values in each block. But due to inaccurate and untrusted timestamps we cannot determine the exact time interval between blocks. A user can shift his timestamp into the future and the next time intervals might be improbably small or even negative. Presumably there will be few incidents of this kind, so we can just sort the timestamps and cut-offthe outliers (i.e. 20%). The range of the rest values is the time which was spent for 80% of the corresponding blocks. 6.2.2 Size limits Users pay for storing the blockchain and shall be entitled to vote for its size. Every miner deals with the trade-offbetween balancing the costs and profit from the fees and sets his own “soft-limit” for creating blocks. Also the core rule for the maximum block size is necessary for preventing the blockchain from being flooded with bogus transaction, however this value should not be hard-coded. Let \(M_N\) be the median value of the last \(N\) blocks sizes. Then the “hard-limit” for the size of accepting blocks is \(2 \cdot M_N\). It averts the blockchain from bloating but still allows the limit to slowly grow with time if necessary. Transaction size does not need to be limited explicitly. It is bounded by the size of a block; and if somebody wants to create a huge transaction with hundreds of inputs/outputs (or with the high ambiguity degree in ring signatures), he can do so by paying sufficient fee. 6.2.3 Excess size penalty A miner still has the ability to stuffa block full of his own zero-fee transactions up to its maximum size \(2 \cdot M_b\). Even though only the majority of miners can shift the median value, there is still a 13 23 Atomic units. I like that. Is this the equivalent of Satoshis? If so, then that means there are going to be 185 billion cryptonote. I know this must be, eventually, tweaked in a few pages, or maybe there’s a typo? If the base reward is "all remaining coins" then only one block is sufficient to get all coins. Instamine. On the other hand, if this is supposed to be proportional in some way to the difference in time between now and some coin-production-termination-date? That would make sense. Also, in my world, two greater than signs like this means "much greater than." Did the author possibly mean something else? If adjustment to difficulty occurs every block then an attacker could have a very large farm of machines mine on and offin carefully chosen time intervals. This could cause a chaotic explosion (or crash to zero) in difficulty, if difficulty adjustment formulas aren’t suitably damped. No doubt that Bitcoin’s method is unsuitable for rapid recalculations, but the idea of inertia in these systems would need to be proven, not taken for granted. Furthermore, oscillations in network difficulty isn’t necessarily a problem unless it results in oscillations of ostensible supply of coins - and having a very rapidly changing difficulty could cause "over-correction." Time spent, especially over a short time span like a few minutes, will be proportional to "total number of blocks created on the network." The constant of proportionality will, itself, grow over time, presumably exponentially if CN takes off. It may be a better idea to simply adjust the difficulty to keep "total blocks created on the network since the last block was added to the main chain" within some constant value, or with bounded variation or something like that. If an adaptive algorithm that is computationally easy to implement can be determined, this would seem to solve the problem. But then, if we used that method, someone with a big mining farm could shut their farm down for a few hours, and switch it back on again. For the first few blocks, that farm will make bank. So, actually, this method would bring up an interesting point: mining becomes (on average) a losing game with no ROI, especially as more folks hop on the network. If the mining difficulty very closely tracked network hashrate, I somehow doubt people would mine as much as they currently do. Or, on the other hand, instead of keeping their mining farms going 24/7, they may turn them on for 6 hours, offfor 2, on for 6, offfor 2, or something like that. Just switch to another coin for a few hours, wait for difficulty to drop, then hop back on in order to gain those few extra blocks of profitability as the network adapts. And you know what? This is actually probably one of the better mining scenarios I’ve put my mind into... This could be circular, but if block creation time averages to about a minute, can we just use the number of blocks as a proxy for "time spent?"
6 Further advantages 6.1 Smooth emission The upper bound for the overall amount of CryptoNote digital coins is: \(M_{Supply} = 2^{64} - 1\) atomic units. This is a natural restriction based only on implementation limits, not on intuition such as “N coins ought to be enough for anybody”. To ensure the smoothness of the emission process we use the following formula for block rewards: \(BaseReward = (M_{Supply} - A) \gg 18\), where \(A\) is amount of previously generated coins. 6.2 Adjustable parameters 6.2.1 Difficulty CryptoNote contains a targeting algorithm which changes the difficulty of every block. This decreases the system’s reaction time when the network hashrate is intensely growing or shrinking, preserving a constant block rate. The original Bitcoin method calculates the relation of actual and target time-span between the last 2016 blocks and uses it as the multiplier for the current difficulty. Obviously this is unsuitable for rapid recalculations (because of large inertia) and results in oscillations. The general idea behind our algorithm is to sum all the work completed by the nodes and divide it by the time they have spent. The measure of work is the corresponding difficulty values in each block. But due to inaccurate and untrusted timestamps we cannot determine the exact time interval between blocks. A user can shift his timestamp into the future and the next time intervals might be improbably small or even negative. Presumably there will be few incidents of this kind, so we can just sort the timestamps and cut-offthe outliers (i.e. 20%). The range of the rest values is the time which was spent for 80% of the corresponding blocks. 6.2.2 Size limits Users pay for storing the blockchain and shall be entitled to vote for its size. Every miner deals with the trade-offbetween balancing the costs and profit from the fees and sets his own “soft-limit” for creating blocks. Also the core rule for the maximum block size is necessary for preventing the blockchain from being flooded with bogus transaction, however this value should not be hard-coded. Let \(M_N\) be the median value of the last \(N\) blocks sizes. Then the “hard-limit” for the size of accepting blocks is \(2 \cdot M_N\). It averts the blockchain from bloating but still allows the limit to slowly grow with time if necessary. Transaction size does not need to be limited explicitly. It is bounded by the size of a block; and if somebody wants to create a huge transaction with hundreds of inputs/outputs (or with the high ambiguity degree in ring signatures), he can do so by paying sufficient fee. 6.2.3 Excess size penalty A miner still has the ability to stuffa block full of his own zero-fee transactions up to its maximum size \(2 \cdot M_b\). Even though only the majority of miners can shift the median value, there is still a 13 6 Further advantages 6.1 Smooth emission The upper bound for the overall amount of CryptoNote digital coins is: \(M_{Supply} = 2^{64} - 1\) atomic units. This is a natural restriction based only on implementation limits, not on intuition such as “N coins ought to be enough for anybody”. To ensure the smoothness of the emission process we use the following formula for block rewards: \(BaseReward = (M_{Supply} - A) \gg 18\), where \(A\) is amount of previously generated coins. 6.2 Adjustable parameters 6.2.1 Difficulty CryptoNote contains a targeting algorithm which changes the difficulty of every block. This decreases the system’s reaction time when the network hashrate is intensely growing or shrinking, preserving a constant block rate. The original Bitcoin method calculates the relation of actual and target time-span between the last 2016 blocks and uses it as the multiplier for the current difficulty. Obviously this is unsuitable for rapid recalculations (because of large inertia) and results in oscillations. The general idea behind our algorithm is to sum all the work completed by the nodes and divide it by the time they have spent. The measure of work is the corresponding difficulty values in each block. But due to inaccurate and untrusted timestamps we cannot determine the exact time interval between blocks. A user can shift his timestamp into the future and the next time intervals might be improbably small or even negative. Presumably there will be few incidents of this kind, so we can just sort the timestamps and cut-offthe outliers (i.e. 20%). The range of the rest values is the time which was spent for 80% of the corresponding blocks. 6.2.2 Size limits Users pay for storing the blockchain and shall be entitled to vote for its size. Every miner deals with the trade-offbetween balancing the costs and profit from the fees and sets his own “soft-limit” for creating blocks. Also the core rule for the maximum block size is necessary for preventing the blockchain from being flooded with bogus transaction, however this value should not be hard-coded. Let \(M_N\) be the median value of the last \(N\) blocks sizes. Then the “hard-limit” for the size of accepting blocks is \(2 \cdot M_N\). It averts the blockchain from bloating but still allows the limit to slowly grow with time if necessary. Transaction size does not need to be limited explicitly. It is bounded by the size of a block; and if somebody wants to create a huge transaction with hundreds of inputs/outputs (or with the high ambiguity degree in ring signatures), he can do so by paying sufficient fee. 6.2.3 Excess size penalty A miner still has the ability to stuffa block full of his own zero-fee transactions up to its maximum size \(2 \cdot M_b\). Even though only the majority of miners can shift the median value, there is still a 13 24 Okay, so we have a blockchain, and each block has timestamps IN ADDITION to simply being ordered. This was clearly inserted simply for difficulty adjustment, because timestamps are very unreliable, as mentioned. Are we allowed to have contradicting timestamps in the chain? If Block A comes before Block B in the chain, and everything is consistent in terms of finances, but Block A appears to have been created after Block B? Because, perhaps, someone owned a large part of the network? Is that ok? Probably, because the finances aren’t goofed up. Okay, so I hate this arbitrary "only 80% of the blocks are legitimate for the main blockchain" approach. It was intended to prevent liars from tweaking their timestamps? But now, it adds incentive for everyone to lie about their timestamps and just pick the median. Please define. Meaning "for this block, only include transactions that include fees greater than p%, preferentially with fees greater than 2p%" or something like that? What do they mean by bogus? If the transaction is consistent with past history of the blockchain, and the transaction includes fees that satisfy miners, is that not enough? Well, no, not necessarily. If no maximum block size exists, there is nothing to keep a malicious user from simply uploading a massive block of transactions to himself all at once just to slow down the network. A core rule for maximum block size prevents people from putting enormous amounts of junk data on the blockchain all at once just to slow things down. But such a rule certianly has to be adaptive - during the christmas season, for example, we could expect traffic to spike, and block size to get very big, and immediately afterward, for the block size to subsequently drop again. So we need either a) some sort of adaptive cap or b) a cap large enough so that 99% of reasonable christmas peaks don’t break the cap. Of course, that second one is impossible to estimate - who knows if a currency will catch on? Better to make it adaptive and not worry about it. But then we have a control theory problem: how to make this adaptive without vulnerability to attack or wild & crazy oscillations? Notice an adaptive method doesn’t stop malicious users from accumulating small amounts of junk data over time on the blockchain to cause long-term bloat. This is a different issue altogether and one that cryptonote coins have serious problems with.
6 Further advantages 6.1 Smooth emission The upper bound for the overall amount of CryptoNote digital coins is: \(M_{Supply} = 2^{64} - 1\) atomic units. This is a natural restriction based only on implementation limits, not on intuition such as “N coins ought to be enough for anybody”. To ensure the smoothness of the emission process we use the following formula for block rewards: \(BaseReward = (M_{Supply} - A) \gg 18\), where \(A\) is amount of previously generated coins. 6.2 Adjustable parameters 6.2.1 Difficulty CryptoNote contains a targeting algorithm which changes the difficulty of every block. This decreases the system’s reaction time when the network hashrate is intensely growing or shrinking, preserving a constant block rate. The original Bitcoin method calculates the relation of actual and target time-span between the last 2016 blocks and uses it as the multiplier for the current difficulty. Obviously this is unsuitable for rapid recalculations (because of large inertia) and results in oscillations. The general idea behind our algorithm is to sum all the work completed by the nodes and divide it by the time they have spent. The measure of work is the corresponding difficulty values in each block. But due to inaccurate and untrusted timestamps we cannot determine the exact time interval between blocks. A user can shift his timestamp into the future and the next time intervals might be improbably small or even negative. Presumably there will be few incidents of this kind, so we can just sort the timestamps and cut-offthe outliers (i.e. 20%). The range of the rest values is the time which was spent for 80% of the corresponding blocks. 6.2.2 Size limits Users pay for storing the blockchain and shall be entitled to vote for its size. Every miner deals with the trade-offbetween balancing the costs and profit from the fees and sets his own “soft-limit” for creating blocks. Also the core rule for the maximum block size is necessary for preventing the blockchain from being flooded with bogus transaction, however this value should not be hard-coded. Let \(M_N\) be the median value of the last \(N\) blocks sizes. Then the “hard-limit” for the size of accepting blocks is \(2 \cdot M_N\). It averts the blockchain from bloating but still allows the limit to slowly grow with time if necessary. Transaction size does not need to be limited explicitly. It is bounded by the size of a block; and if somebody wants to create a huge transaction with hundreds of inputs/outputs (or with the high ambiguity degree in ring signatures), he can do so by paying sufficient fee. 6.2.3 Excess size penalty A miner still has the ability to stuffa block full of his own zero-fee transactions up to its maximum size \(2 \cdot M_b\). Even though only the majority of miners can shift the median value, there is still a 13 6 Further advantages 6.1 Smooth emission The upper bound for the overall amount of CryptoNote digital coins is: \(M_{Supply} = 2^{64} - 1\) atomic units. This is a natural restriction based only on implementation limits, not on intuition such as “N coins ought to be enough for anybody”. To ensure the smoothness of the emission process we use the following formula for block rewards: \(BaseReward = (M_{Supply} - A) \gg 18\), where \(A\) is amount of previously generated coins. 6.2 Adjustable parameters 6.2.1 Difficulty CryptoNote contains a targeting algorithm which changes the difficulty of every block. This decreases the system’s reaction time when the network hashrate is intensely growing or shrinking, preserving a constant block rate. The original Bitcoin method calculates the relation of actual and target time-span between the last 2016 blocks and uses it as the multiplier for the current difficulty. Obviously this is unsuitable for rapid recalculations (because of large inertia) and results in oscillations. The general idea behind our algorithm is to sum all the work completed by the nodes and divide it by the time they have spent. The measure of work is the corresponding difficulty values in each block. But due to inaccurate and untrusted timestamps we cannot determine the exact time interval between blocks. A user can shift his timestamp into the future and the next time intervals might be improbably small or even negative. Presumably there will be few incidents of this kind, so we can just sort the timestamps and cut-offthe outliers (i.e. 20%). The range of the rest values is the time which was spent for 80% of the corresponding blocks. 6.2.2 Size limits Users pay for storing the blockchain and shall be entitled to vote for its size. Every miner deals with the trade-offbetween balancing the costs and profit from the fees and sets his own “soft-limit” for creating blocks. Also the core rule for the maximum block size is necessary for preventing the blockchain from being flooded with bogus transaction, however this value should not be hard-coded. Let \(M_N\) be the median value of the last \(N\) blocks sizes. Then the “hard-limit” for the size of accepting blocks is \(2 \cdot M_N\). It averts the blockchain from bloating but still allows the limit to slowly grow with time if necessary. Transaction size does not need to be limited explicitly. It is bounded by the size of a block; and if somebody wants to create a huge transaction with hundreds of inputs/outputs (or with the high ambiguity degree in ring signatures), he can do so by paying sufficient fee. 6.2.3 Excess size penalty A miner still has the ability to stuffa block full of his own zero-fee transactions up to its maximum size \(2 \cdot M_b\). Even though only the majority of miners can shift the median value, there is still a 13 25 Rescaling time so that one unit of time is \(N\) blocks, the average block size could still, theoretically, grow exponentially proportionally to \(2^t\). On the other hand, a more general cap on the next block would be \(M_n \cdot f(M_n)\) for some function \(f\). What properties of \(f\) would we choose in order to guarantee some "reasonable growth" of block size? The progression of block sizes (after rescaling time) would go like this: \(M_n \quad f(M_n) \cdot M_n \quad f(f(M_n) \cdot M_n) \cdot f(M_n) \cdot M_n \quad f(f(f(M_n) \cdot M_n) \cdot f(M_n) \cdot M_n) \cdot f(f(M_n) \cdot M_n) \cdot f(\ldots)\) \(\ldots\) And the goal here is to choose \(f\) such that this sequence grows no faster than, say, linearly, or perhaps even as \(\log(t)\). Of course, if \(f(M_n) = a\) for some constant \(a\), this sequence is actually \(M_n \quad a \cdot M_n \quad a^2 \cdot M_n \quad a^3 \cdot M_n \quad \ldots\) And, of course, the only way this can be limited to at-most linear growth is by choosing \(a = 1\). This is, of course, infeasible. It does not allow growth at all. If, on the other hand, \(f(M_n)\) is a non-constant function, then the situation is much more complicated and may allow for an elegant solution. I’ll think on this for awhile. This fee will have to be large enough to discount the excess size penalty from the next section. Why is a general user assumed male, huh? Huh?
possibility to bloat the blockchain and produce an additional load on the nodes. To discourage malevolent participants from creating large blocks we introduce a penalty function: \[NewReward = BaseReward \cdot \left(\frac{BlkSize}{M_N} - 1\right)^2\] This rule is applied only when \(BlkSize\) is greater than minimal free block size which should be close to \(\max(10kb, M_N \cdot 110\%)\). Miners are permitted to create blocks of “usual size” and even exceed it with profit when the overall fees surpass the penalty. But fees are unlikely to grow quadratically unlike the penalty value so there will be an equilibrium. 6.3 Transaction scripts CryptoNote has a very minimalistic scripting subsystem. A sender specifies an expression \(\Phi = f(x_1, x_2, \ldots, x_n)\), where \(n\) is the number of destination public keys \(\{P_i\}_{i=1}^{n}\). Only five binary operators are supported: min, max, sum, mul and cmp. When the receiver spends this payment, he produces \(0 \leq k \leq n\) signatures and passes them to transaction input. The verification process simply evaluates \(\Phi\) with \(x_i = 1\) to check for a valid signature for the public key \(P_i\), and \(x_i = 0\). A verifier accepts the proof iff \(\Phi > 0\). Despite its simplicity this approach covers every possible case: • Multi-/Threshold signature. For the Bitcoin-style “M-out-of-N” multi-signature (i.e. the receiver should provide at least \(0 \leq M \leq N\) valid signatures) \(\Phi = x_1 + x_2 + \ldots + x_N \geq M\) (for clarity we are using common algebraic notation). The weighted threshold signature (some keys can be more important than other) could be expressed as \(\Phi = w_1 \cdot x_1 + w_2 \cdot x_2 + \ldots + w_N \cdot x_N \geq w_M\). And scenario where the master-key corresponds to \(\Phi = \max(M \cdot x, x_1 + x_2 + \ldots + x_N) \geq M\). It is easy to show that any sophisticated case can be expressed with these operators, i.e. they form basis. • Password protection. Possession of a secret password \(s\) is equivalent to the knowledge of a private key, deterministically derived from the password: \(k = KDF(s)\). Hence, a receiver can prove that he knows the password by providing another signature under the key \(k\). The sender simply adds the corresponding public key to his own output. Note that this method is much more secure than the “transaction puzzle” used in Bitcoin [13], where the password is explicitly passed in the inputs. • Degenerate cases. \(\Phi = 1\) means that anybody can spend the money; \(\Phi = 0\) marks the output as not spendable forever. In the case when the output script combined with public keys is too large for a sender, he can use special output type, which indicates that the recipient will put this data in his input while the sender provides only a hash of it. This approach is similar to Bitcoin’s “pay-to-hash” feature, but instead of adding new script commands we handle this case at the data structure level. 7 Conclusion We have investigated the major flaws in Bitcoin and proposed some possible solutions. These advantageous features and our ongoing development make new electronic cash system CryptoNote a serious rival to Bitcoin, outclassing all its forks. 14 possibility to bloat the blockchain and produce an additional load on the nodes. To discourage malevolent participants from creating large blocks we introduce a penalty function: \[NewReward = BaseReward \cdot \left(\frac{BlkSize}{M_N} - 1\right)^2\] This rule is applied only when \(BlkSize\) is greater than minimal free block size which should be close to \(\max(10kb, M_N \cdot 110\%)\). Miners are permitted to create blocks of “usual size” and even exceed it with profit when the overall fees surpass the penalty. But fees are unlikely to grow quadratically unlike the penalty value so there will be an equilibrium. 6.3 Transaction scripts CryptoNote has a very minimalistic scripting subsystem. A sender specifies an expression \(\Phi = f(x_1, x_2, \ldots, x_n)\), where \(n\) is the number of destination public keys \(\{P_i\}_{i=1}^{n}\). Only five binary operators are supported: min, max, sum, mul and cmp. When the receiver spends this payment, he produces \(0 \leq k \leq n\) signatures and passes them to transaction input. The verification process simply evaluates \(\Phi\) with \(x_i = 1\) to check for a valid signature for the public key \(P_i\), and \(x_i = 0\). A verifier accepts the proof iff \(\Phi > 0\). Despite its simplicity this approach covers every possible case: • Multi-/Threshold signature. For the Bitcoin-style “M-out-of-N” multi-signature (i.e. the receiver should provide at least \(0 \leq M \leq N\) valid signatures) \(\Phi = x_1 + x_2 + \ldots + x_N \geq M\) (for clarity we are using common algebraic notation). The weighted threshold signature (some keys can be more important than other) could be expressed as \(\Phi = w_1 \cdot x_1 + w_2 \cdot x_2 + \ldots + w_N \cdot x_N \geq w_M\). And scenario where the master-key corresponds to \(\Phi = \max(M \cdot x, x_1 + x_2 + \ldots + x_N) \geq M\). It is easy to show that any sophisticated case can be expressed with these operators, i.e. they form basis. • Password protection. Possession of a secret password \(s\) is equivalent to the knowledge of a private key, deterministically derived from the password: \(k = KDF(s)\). Hence, a receiver can prove that he knows the password by providing another signature under the key \(k\). The sender simply adds the corresponding public key to his own output. Note that this method is much more secure than the “transaction puzzle” used in Bitcoin [13], where the password is explicitly passed in the inputs. • Degenerate cases. \(\Phi = 1\) means that anybody can spend the money; \(\Phi = 0\) marks the output as not spendable forever. In the case when the output script combined with public keys is too large for a sender, he can use special output type, which indicates that the recipient will put this data in his input while the sender provides only a hash of it. This approach is similar to Bitcoin’s “pay-to-hash” feature, but instead of adding new script commands we handle this case at the data structure level. 7 Conclusion We have investigated the major flaws in Bitcoin and proposed some possible solutions. These advantageous features and our ongoing development make new electronic cash system CryptoNote a serious rival to Bitcoin, outclassing all its forks. 14 26 This may be unnecessary if we can figure out a way to bound block size over time... This also cannot be correct. They just set "NewReward" to an upward-facing parabola where block size is the independent variable. So new reward blows up to infinity. If, on the other hand, the new reward is \(\max(0, BaseReward \cdot (1 - (BlkSize/M_n - 1)^2))\), then the new reward would be a downward facing parabola with peak at \(blocksize = M_n\), and with intercepts at \(Blocksize = 0\) and \(Blocksize = 2 \cdot M_n\). And that seems to be what they are trying to describe. However, this does not
交易无法追踪
在本节中,我们提出了一种完全匿名交易的方案,同时满足不可追溯性
和不可链接条件。我们解决方案的一个重要特点是它的自主性:发送者
不需要与其他用户或受信任的第三方合作进行交易;
因此,每个参与者都独立地产生掩护流量。
4.1
文献综述
我们的方案依赖于称为群签名的加密原语。首先提出者
D. Chaum 和 E. van Heyst [19],它允许用户代表组签署他的消息。
签署消息后,用户提供(出于验证目的)而不是他自己的单一公共信息
1这就是所谓的“软限制”——创建新块的参考客户端限制。硬最大值
可能的块大小为 1 MB
4
如有必要,它们会导致主要缺点。不幸的是,很难预测何时
常量可能需要改变,替换它们可能会导致可怕的后果。
硬编码限制更改导致灾难性后果的一个很好的例子是块
大小限制设置为 250kb1。这个限制足以容纳大约 10000 个标准交易。在
2013 年初,这一限制几乎已达到,并达成协议增加
限制。该更改在钱包版本 0.8 中实施,并以 24 块链分裂结束
以及成功的双花攻击[9]。虽然该错误不在 Bitcoin 协议中,但是
相反,在数据库引擎中,如果有的话,可以通过简单的压力测试轻松捕获它
没有人为引入的块大小限制。
常量也充当集中点的一种形式。
尽管具有点对点的性质
Bitcoin,绝大多数节点使用官方开发的参考客户端[10]
一小群人。该小组决定对协议进行更改
大多数人都会接受这些变化,无论它们的“正确性”如何。一些决定导致
激烈讨论甚至呼吁抵制[11],这表明社区和
开发人员可能在一些重要问题上存在分歧。因此,制定一项协议似乎是合乎逻辑的
使用用户可配置和自我调整的变量作为避免这些问题的可能方法。
2.5
庞大的脚本
Bitcoin 中的脚本系统是一个繁重且复杂的功能。它可能允许人们创建
复杂的交易[12],但由于安全问题和原因,其某些功能被禁用
有些甚至从未使用过[13]。脚本(包括发送者和接收者部分)
Bitcoin 中最受欢迎的交易如下所示:
key,而是他所在组的所有用户的密钥。验证者确信真正的签名者是 该组的成员,但不能唯一地识别签名者。 最初的协议需要一个可信的第三方(称为组经理),而他是 唯一可以追踪签名者的人。引入了称为环签名的下一个版本 作者:Rivest 等人。在 [34] 中,是一个没有组经理和匿名的自治计划 撤销。后来出现了该方案的各种修改:可链接环签名 [26, 27, 17]允许确定两个签名是否由同一组成员产生,可追踪 环签名 [24, 23] 通过提供追踪签名者的可能性来限制过度匿名 两条消息涉及相同的元信息(或 [24] 中的“标签”)。 类似的密码结构也称为临时组签名 [16, 38]。它 强调任意的组形成,而组/环签名方案则意味着 固定的成员集。 在很大程度上,我们的解决方案基于 E. Fujisaki 的作品“可追踪环签名” 和铃木 [24]。为了区分原始算法和我们的修改算法,我们将 将后者称为一次性环签名,强调用户仅产生一个有效的能力 在他的私钥下签名。我们弱化了可追溯性,保留了可链接性 只提供一次性的:公钥可能出现在很多国外的验证集中,并且 私钥可用于生成唯一的匿名签名。如果出现双重支出 尝试将这两个签名链接在一起,但不必透露签名者 为了我们的目的。 4.2 定义 4.2.1 椭圆曲线参数 作为我们的基本签名算法,我们选择使用快速方案 EdDSA,该方案是开发和 由 D.J. 实施伯恩斯坦等人。 [18]。与 Bitcoin 的 ECDSA 一样,它基于椭圆曲线 离散对数问题,因此我们的方案将来也可以应用于 Bitcoin 。 常用参数有: q:素数; q = 2255 -19; d:Fq的一个元素; d = −121665/121666; E:椭圆曲线方程; −x2 + y2 = 1 + dx2y2; G:基点; G = (x,−4/5); l:基点的素数阶; l = 2252 + 27742317777372353535851937790883648493; Hs:加密 hash 函数 \(\{0, 1\}^* \to \mathbb{F}_q\); Hp:确定性 hash 函数 \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\)。 4.2.2 术语 增强隐私需要新的术语,该术语不应与 Bitcoin 实体混淆。 private ec-key 是一个标准的椭圆曲线私钥:一个数字 \(a \in [1, l - 1]\); public ec-key 是标准椭圆曲线公钥:点A = aG; 一次性密钥对是一对私有和公共 ec 密钥; 5 key,而是他所在组的所有用户的密钥。验证者确信真正的签名者是 该组的成员,但不能唯一地识别签名者。 最初的协议需要一个可信的第三方(称为组经理),而他是 唯一可以追踪签名者的人。引入了称为环签名的下一个版本 作者:Rivest 等人。在 [34] 中,是一个没有组经理和匿名的自治计划 撤销。后来出现了该方案的各种修改:可链接环签名 [26, 27, 17]允许确定两个签名是否由同一组成员产生,可追踪 环签名 [24, 23] 通过提供追踪签名者的可能性来限制过度匿名 两条消息涉及相同的元信息(或 [24] 中的“标签”)。 类似的密码结构也称为临时组签名 [16, 38]。它 强调任意的组形成,而组/环签名方案则意味着 固定的成员集。 在很大程度上,我们的解决方案基于 E. Fujisaki 的作品“可追踪环签名” 和铃木 [24]。为了区分原始算法和我们的修改算法,我们将 将后者称为一次性环签名,强调用户仅产生一个有效的能力 在他的私钥下签名。我们弱化了可追溯性,保留了可链接性 仅提供一次性的:公钥可能出现在许多国外验证集中,并且 私钥可用于生成唯一的匿名签名。如果出现双重支出 尝试将这两个签名链接在一起,但不必透露签名者 为了我们的目的。 4.2 定义 4.2.1 椭圆曲线参数 作为我们的基本签名算法,我们选择e 使用快速方案 EdDSA,该方案是开发和 由 D.J. 实施伯恩斯坦等人。 [18]。与 Bitcoin 的 ECDSA 一样,它基于椭圆曲线 离散对数问题,因此我们的方案将来也可以应用于 Bitcoin 。 常用参数有: q:素数; q = 2255 -19; d:Fq的一个元素; d = −121665/121666; E:椭圆曲线方程; −x2 + y2 = 1 + dx2y2; G:基点; G = (x,−4/5); l:基点的素数阶; l = 2252 + 27742317777372353535851937790883648493; Hs:加密 hash 函数 \(\{0, 1\}^* \to \mathbb{F}_q\); Hp:确定性 hash 函数 \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\)。 4.2.2 术语 增强隐私需要新的术语,该术语不应与 Bitcoin 实体混淆。 private ec-key 是一个标准的椭圆曲线私钥:一个数字 \(a \in [1, l - 1]\); public ec-key 是标准椭圆曲线公钥:点A = aG; 一次性密钥对是一对私有和公共 ec 密钥; 5 8 环签名的工作原理如下:亚历克斯想要向维基解密泄露有关她雇主的信息。公司的每位员工都有一个私钥/公钥对(Ri、Ui)。她作曲 她的签名,输入设置为她的消息,m,她的私钥,Ri 和每个人的 公钥,(Ui;i=1...n)。任何人(不知道任何私钥)都可以轻松验证 某些对(Rj,Uj)必须已用于构建签名......工作的人 对于亚历克斯的雇主来说……但这本质上是一种随机猜测,以确定它可能是哪一个。 http://en.wikipedia.org/wiki/Ring_signature#Crypto-currencies http://link.springer.com/chapter/10.1007/3-540-45682-1_32#page-1 http://link.springer.com/chapter/10.1007/11424826_65 http://link.springer.com/chapter/10.1007/978-3-540-27800-9_28 http://link.springer.com/chapter/10.1007%2F11774716_9 请注意,此处描述的可链接环签名与“不可链接”相反 如上所述。这里我们截取两条消息,可以判断是否相同 一方发送了他们,尽管我们仍然无法确定该方是谁。 的 用于构造 Cryptonote 的“不可链接”的定义意味着我们无法确定是否 同一方正在接收它们。 因此,我们这里真正发生的是四件事。 系统可以是可链接的或 不可链接,取决于是否可以确定发送者是否 两条消息是相同的(无论这是否需要撤销匿名)。 并且 系统可以是不可链接的或不可不可链接的,具体取决于是否可以 判断两条消息的接收者是否相同(无论是否相同) 这需要撤销匿名)。 请不要因为这个可怕的术语而责怪我。 图论学家可能应该是 很高兴。你们中的一些人可能更喜欢“接收者可链接”而不是“发送者可链接”。 http://link.springer.com/chapter/10.1007/978-3-540-71677-8_13 当我读到这篇文章时,这似乎是一个愚蠢的功能。然后我读到这可能是一个功能 电子投票,这似乎是有道理的。从这个角度来看,有点酷。但我是 不完全确定是否有意实施可追踪的环签名。 http://search.ieice.org/bin/summary.php?id=e95-a_1_151
key,而是他所在组的所有用户的密钥。验证者确信真正的签名者是 该组的成员,但不能唯一地识别签名者。 最初的协议需要一个可信的第三方(称为组经理),而他是 唯一可以追踪签名者的人。引入了称为环签名的下一个版本 作者:Rivest 等人。在 [34] 中,是一个没有组经理和匿名的自治计划 撤销。后来出现了该方案的各种修改:可链接环签名 [26, 27, 17]允许确定两个签名是否由同一组成员产生,可追踪 环签名 [24, 23] 通过提供追踪签名者的可能性来限制过度匿名 两条消息涉及相同的元信息(或 [24] 中的“标签”)。 类似的密码结构也称为临时组签名 [16, 38]。它 强调任意的组形成,而组/环签名方案则意味着 固定的成员集。 在很大程度上,我们的解决方案基于 E. Fujisaki 的作品“可追踪环签名” 和铃木 [24]。为了区分原始算法和我们的修改算法,我们将 将后者称为一次性环签名,强调用户仅产生一个有效的能力 在他的私钥下签名。我们弱化了可追溯性,保留了可链接性 仅提供一次性的:公钥可能出现在许多国外验证集中,并且 私钥可用于生成唯一的匿名签名。如果出现双重支出 尝试将这两个签名链接在一起,但不必透露签名者 为了我们的目的。 4.2 定义 4.2.1 椭圆曲线参数 作为我们的基本签名算法,我们选择使用快速方案 EdDSA,该方案是开发和 由 D.J. 实施伯恩斯坦等人。 [18]。与 Bitcoin 的 ECDSA 一样,它基于椭圆曲线 离散对数问题,因此我们的方案将来也可以应用于 Bitcoin 。 常用参数有: q:素数; q = 2255 -19; d:Fq的一个元素; d = −121665/121666; E:椭圆曲线方程; −x2 + y2 = 1 + dx2y2; G:基点; G = (x,−4/5); l:基点的素数阶; l = 2252 + 27742317777372353535851937790883648493; Hs:加密 hash 函数 \(\{0, 1\}^* \to \mathbb{F}_q\); Hp:确定性 hash 函数 \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\)。 4.2.2 术语 增强隐私需要新的术语,该术语不应与 Bitcoin 实体混淆。 private ec-key 是一个标准的椭圆曲线私钥:一个数字 \(a \in [1, l - 1]\); public ec-key 是标准椭圆曲线公钥:点A = aG; 一次性密钥对是一对私有和公共 ec 密钥; 5 key,而是他所在组的所有用户的密钥。验证者确信真正的签名者是 该组的成员,但不能唯一地识别签名者。 最初的协议需要一个可信的第三方(称为组经理),而他是 唯一可以追踪签名者的人。引入了称为环签名的下一个版本 作者:Rivest 等人。在 [34] 中,是一个没有组经理和匿名的自治计划 撤销。后来出现了该方案的各种修改:可链接环签名 [26, 27, 17]允许确定两个签名是否由同一组成员产生,可追踪 环签名 [24, 23] 通过提供追踪签名者的可能性来限制过度匿名 两条消息涉及相同的元信息(或 [24] 中的“标签”)。 类似的密码结构也称为临时组签名 [16, 38]。它 强调任意的组形成,而组/环签名方案则意味着 固定的成员集。 在很大程度上,我们的解决方案基于 E. Fujisaki 的作品“可追踪环签名” 和铃木 [24]。为了区分原始算法和我们的修改算法,我们将 将后者称为一次性环签名,强调用户仅产生一个有效的能力 在他的私钥下签名。我们弱化了可追溯性,保留了可链接性 仅提供一次性的:公钥可能出现在许多国外验证集中,并且 私钥可用于生成唯一的匿名签名。如果出现双重支出 尝试将这两个签名链接在一起,但不必透露签名者 为了我们的目的。 4.2 定义 4.2.1 椭圆曲线参数 作为我们的基本签名算法,我们选择e 使用快速方案 EdDSA,该方案是开发和 由 D.J. 实施伯恩斯坦等人。 [18]。与 Bitcoin 的 ECDSA 一样,它基于椭圆曲线 离散对数问题,因此我们的方案将来也可以应用于 Bitcoin 。 常用参数有: q:素数; q = 2255 -19; d:Fq的一个元素; d = −121665/121666; E:椭圆曲线方程; −x2 + y2 = 1 + dx2y2; G:基点; G = (x,−4/5); l:基点的素数阶; l = 2252 + 27742317777372353535851937790883648493; Hs:加密 hash 函数 \(\{0, 1\}^* \to \mathbb{F}_q\); Hp:确定性 hash 函数 \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\)。 4.2.2 术语 增强隐私需要新的术语,该术语不应与 Bitcoin 实体混淆。 private ec-key 是一个标准的椭圆曲线私钥:一个数字 \(a \in [1, l - 1]\); public ec-key 是标准椭圆曲线公钥:点A = aG; 一次性密钥对是一对私有和公共 ec 密钥; 5 9 天哪,本白皮书的作者肯定可以用更好的措辞!假设一个 员工持股的公司想要就是否收购某些新产品进行投票 资产,Alex 和 Brenda 都是雇员。公司为每位员工提供 诸如“我对提案 A 投赞成票!”之类的消息其中存在元信息“问题”[PROP A] 如果他们支持该提议,则要求他们使用可追踪的环签名进行签名。 使用传统的环签名,不诚实的员工可以多次签署消息, 大概有不同的 nonce,以便可以随意投票。另一方面 另一方面,在可追踪的环签名方案中,Alex 将去投票,她的私钥将具有 已用于问题[PROP A]。如果亚历克斯试图签署类似“我,布伦达,同意 提议A!” “陷害”布伦达和双重投票,这条新消息也会有问题 [提案A]。由于 Alex 的私钥已经触发了 [PROP A] 问题,Alex 的身份 将立即被揭露为欺诈行为。 面对现实吧,这真是太酷了!密码学强制投票平等。 http://link.springer.com/chapter/10.1007/978-3-540-71677-8_13 这篇论文很有趣,本质上创建了一个临时环签名,但没有任何 其他参与者的同意。签名的结构可能不同;我没挖过 很深,我还没有看到它是否安全。 https://people.csail.mit.edu/rivest/AdidaHohenbergerRivest-AdHocGroupSignaturesFromHijackedKeypai 临时组签名是: 环签名,即没有组的群签名 经理,没有集中化,但允许特设小组中的成员可以证明地声称 它已(未)代表该团体发布匿名签名。 http://link.springer.com/chapter/10.1007/11908739_9 根据我的理解,这不太正确。我的理解可能会改变 我对这个项目有了更深入的了解。但根据我的理解,层次结构是这样的。 群组签名:群组管理员控制可追溯性以及添加或删除成员的能力 从成为签名者。 Ring sigs:没有组管理员的任意组形成。没有匿名撤销。 没有办法通过特定的签名来否定自己。带有可追踪和可链接的环 签名、匿名在某种程度上是可扩展的。 Ad-hoc 群签名:类似于环签名,但成员可以证明他们没有创建 一个特定的签名。当小组中的任何人都可以生成签名时,这一点很重要。 http://link.springer.com/chapter/10.1007/978-3-540-71677-8_13 藤崎和铃木的算法后来被作者调整以提供一次性性。所以 我们将同时分析 Fujisaki 和 Suzuki 的算法以及新算法 而不是在这里讨论它。
key,而是他所在组的所有用户的密钥。验证者确信真正的签名者是 该组的成员,但不能唯一地识别签名者。 最初的协议需要一个可信的第三方(称为组经理),而他是 唯一可以追踪签名者的人。引入了称为环签名的下一个版本 作者:Rivest 等人。在 [34] 中,是一个没有组经理和匿名的自治计划 撤销。后来出现了该方案的各种修改:可链接环签名 [26, 27, 17]允许确定两个签名是否由同一组成员产生,可追踪 环签名 [24, 23] 通过提供追踪签名者的可能性来限制过度匿名 两条消息涉及相同的元信息(或 [24] 中的“标签”)。 类似的密码结构也称为临时组签名 [16, 38]。它 强调任意的组形成,而组/环签名方案则意味着 固定的成员集。 在很大程度上,我们的解决方案基于 E. Fujisaki 的作品“可追踪环签名” 和铃木 [24]。为了区分原始算法和我们的修改算法,我们将 将后者称为一次性环签名,强调用户仅产生一个有效的能力 在他的私钥下签名。我们弱化了可追溯性,保留了可链接性 仅提供一次性的:公钥可能出现在许多国外验证集中,并且 私钥可用于生成唯一的匿名签名。如果出现双重支出 尝试将这两个签名链接在一起,但不必透露签名者 为了我们的目的。 4.2 定义 4.2.1 椭圆曲线参数 作为我们的基本签名算法,我们选择使用快速方案 EdDSA,该方案是开发和 由 D.J. 实施伯恩斯坦等人。 [18]。与 Bitcoin 的 ECDSA 一样,它基于椭圆曲线 离散对数问题,因此我们的方案将来也可以应用于 Bitcoin 。 常用参数有: q:素数; q = 2255 -19; d:Fq的一个元素; d = −121665/121666; E:椭圆曲线方程; −x2 + y2 = 1 + dx2y2; G:基点; G = (x,−4/5); l:基点的素数阶; l = 2252 + 27742317777372353535851937790883648493; Hs:加密 hash 函数 \(\{0, 1\}^* \to \mathbb{F}_q\); Hp:确定性 hash 函数 \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\)。 4.2.2 术语 增强隐私需要新的术语,该术语不应与 Bitcoin 实体混淆。 private ec-key 是一个标准的椭圆曲线私钥:一个数字 \(a \in [1, l - 1]\); public ec-key 是标准椭圆曲线公钥:点A = aG; 一次性密钥对是一对私有和公共 ec 密钥; 5 key,而是他所在组的所有用户的密钥。验证者确信真正的签名者是 该组的成员,但不能唯一地识别签名者。 最初的协议需要一个可信的第三方(称为组经理),而他是 唯一可以追踪签名者的人。引入了称为环签名的下一个版本 作者:Rivest 等人。在 [34] 中,是一个没有组经理和匿名的自治计划 撤销。后来出现了该方案的各种修改:可链接环签名 [26, 27, 17]允许确定两个签名是否由同一组成员产生,可追踪 环签名 [24, 23] 通过提供追踪签名者的可能性来限制过度匿名 两条消息涉及相同的元信息(或 [24] 中的“标签”)。 类似的密码结构也称为临时组签名 [16, 38]。它 强调任意的组形成,而组/环签名方案则意味着 固定的成员集。 在很大程度上,我们的解决方案基于 E. Fujisaki 的作品“可追踪环签名” 和铃木 [24]。为了区分原始算法和我们的修改算法,我们将 将后者称为一次性环签名,强调用户仅产生一个有效的能力 在他的私钥下签名。我们弱化了可追溯性,保留了可链接性 仅提供一次性的:公钥可能出现在许多国外验证集中,并且 私钥可用于生成唯一的匿名签名。如果出现双重支出 尝试将这两个签名链接在一起,但不必透露签名者 为了我们的目的。 4.2 定义 4.2.1 椭圆曲线参数 作为我们的基本签名算法,我们选择e 使用快速方案 EdDSA,该方案是开发和 由 D.J. 实施伯恩斯坦等人。 [18]。与 Bitcoin 的 ECDSA 一样,它基于椭圆曲线 离散对数问题,因此我们的方案将来也可以应用于 Bitcoin 。 常用参数有: q:素数; q = 2255 -19; d:Fq的一个元素; d = −121665/121666; E:椭圆曲线方程; −x2 + y2 = 1 + dx2y2; G:基点; G = (x,−4/5); l:基点的素数阶; l = 2252 + 27742317777372353535851937790883648493; Hs:加密 hash 函数 \(\{0, 1\}^* \to \mathbb{F}_q\); Hp:确定性 hash 函数 \(E(\mathbb{F}_q) \to E(\mathbb{F}_q)\)。 4.2.2 术语 增强隐私需要新的术语,该术语不应与 Bitcoin 实体混淆。 private ec-key 是一个标准的椭圆曲线私钥:一个数字 \(a \in [1, l - 1]\); public ec-key 是标准椭圆曲线公钥:点A = aG; 一次性密钥对是一对私有和公共 ec 密钥; 5 10 “可链接环签名”意义上的可链接性意味着我们可以判断两个传出交易是否来自同一来源,而无需透露来源是谁。作者削弱了 可链接性,以便 (a) 保护隐私,但仍然 (b) 使用私钥发现任何交易 第二次为无效。 好的,这是一个事件顺序问题。 考虑以下场景。 我的挖矿 计算机将拥有当前的 blockchain,它将拥有自己调用的交易块 合法,它将在 proof-of-work 拼图中的该块上工作,并且它将有一个 要添加到下一个块的待处理交易列表。它还将发送任何新的 交易进入该待处理交易池。 如果我不解决下一个块,但是 其他人这样做了,我得到了 blockchain 的更新副本。我正在研究的区块和 我的待处理交易列表可能包含一些现已合并的交易 进入blockchain。 解开我的待处理块,将其与我的待处理交易列表结合起来,然后调用它 我的待处理交易池。删除现在正式位于 blockchain 中的所有内容。 现在,我该怎么办?我应该首先检查并“消除所有双花”吗?另一方面 另一方面,我是否应该搜索列表并确保每个私钥尚未被 使用过,如果它已经在我的列表中使用过,那么我首先收到第一个副本,因此 任何进一步的复制都是非法的。因此,我继续简单地删除第一个之后的所有实例 同一个私钥。 代数几何从来都不是我的强项。 http://en.wikipedia.org/wiki/EdDSA 这速度,太厉害了。这是代数几何的胜利。并不是说我什么都知道 关于那个。 不管有没有问题,离散日志变得非常快。量子计算机吃掉它们 早餐。 http://link.springer.com/article/10.1007/s13389-012-0027-1 这成为一个非常重要的数字,但没有解释或引用它是如何产生的 被选中了。简单地选择一个已知的大素数就可以了,但是如果有已知的 关于这个大质数的事实可能会影响我们的选择。加密货币的不同变体 可以选择不同的值 嗯,但是本文没有讨论如何做到这一点 选择将影响我们对第 5 页列出的其他全局参数的选择。 本文需要一个关于选择参数值的章节。
私有用户密钥是一对 (a, b) 两个不同的私有 ec-key; 跟踪密钥是一对 (a, B) 私有和公共 ec-key(其中 B = bG 且 a̸= b); 公共用户密钥是从 (a, b) 派生的两个公共 ec-key 的一对 (A, B); 标准地址是提供给人类友好字符串的公共用户密钥的表示 具有纠错功能; 截断的地址是给定的公共用户密钥的后半部分(B点)的表示 转换为人类友好的字符串并进行纠错。 交易结构仍然与Bitcoin中的结构类似:每个用户都可以选择 几个独立的收款(交易输出),用相应的签名 私钥并将它们发送到不同的目的地。 与 Bitcoin 的模型相反,用户拥有唯一的私钥和公钥,在 提出的模型发送者根据接收者的地址生成一次性公钥 一些随机数据。从这个意义上说,同一接收者的传入交易被发送到 一次性公钥(不直接发送到唯一地址)并且只有接收者才能恢复 相应的私人部分来赎回他的资金(使用他唯一的私钥)。收件人可以 使用环签名来支出资金,使他的所有权和实际支出保持匿名。 协议的详细信息将在接下来的小节中解释。 4.3 无法关联的付款 经典的 Bitcoin 地址一旦发布,就成为传入的明确标识符 付款,将它们链接在一起并与接收者的假名绑定。如果有人想要 收到“解绑”交易时,他应该通过私人渠道将其地址传达给发送者。 如果他想收到不同的交易,而这些交易不能被证明属于同一所有者 他应该生成所有不同的地址,并且永远不要以自己的笔名发布它们。 公共 私人 爱丽丝 卡罗尔 鲍勃的地址 1 鲍勃的地址 2 鲍勃的钥匙 1 鲍勃的钥匙 2 鲍勃 图 2. 传统的 Bitcoin 密钥/交易模型。 我们提出了一个解决方案,允许用户发布单个地址并无条件接收 无法链接的付款。每个 CryptoNote 输出的目的地(默认情况下)是一个公钥, 来自收件人的地址和发件人的随机数据。相对 Bitcoin 的主要优势 默认情况下,每个目标密钥都是唯一的(除非发送者对每个目标密钥使用相同的数据) 他的交易给同一个接收者)。因此,不存在“地址重用”的问题 设计,没有观察者可以确定是否有任何交易被发送到特定地址或链接 两个地址在一起。 6 私有用户密钥是一对 (a, b) 两个不同的私有 ec-key; 跟踪密钥是一对 (a, B) 私有和公共 ec-key(其中 B = bG 且 a̸= b); 公共用户密钥是从 (a, b) 派生的两个公共 ec-key 的一对 (A, B); 标准地址是提供给人类友好字符串的公共用户密钥的表示 具有纠错功能; 截断的地址是给定的公共用户密钥的后半部分(B点)的表示 转换为人类友好的字符串并进行纠错。 交易结构仍然与Bitcoin中的结构类似:每个用户都可以选择 几个独立的收款(交易输出),用相应的签名 私钥并将它们发送到不同的目的地。 与 Bitcoin 的模型相反,用户拥有唯一的私钥和公钥,在 提出的模型发送者根据接收者的地址生成一次性公钥 一些随机数据。从这个意义上说,同一接收者的传入交易被发送到 一次性公钥(不直接发送到唯一地址)并且只有接收者才能恢复 相应的私人部分来赎回他的资金(使用他唯一的私钥)。收件人可以 使用环签名来支出资金,使他的所有权和实际支出保持匿名。 协议的详细信息将在接下来的小节中解释。 4.3 无法关联的付款 经典的 Bitcoin 地址一旦发布,就成为传入的明确标识符 付款,将它们链接在一起并与接收者的假名绑定。如果有人想要 收到“解绑”交易时,他应该通过私人渠道将其地址传达给发送者。 如果他想收到不同的交易,而这些交易不能被证明属于同一所有者 他应该生成所有不同的地址,并且永远不要以自己的笔名发布它们。 公共 私人 爱丽丝 卡罗尔 鲍勃的地址 1 鲍勃的地址 2 鲍勃的钥匙 1 鲍勃的钥匙 2 鲍勃 图 2. 传统的 Bitcoin 密钥/交易模式埃尔。 我们提出了一个解决方案,允许用户发布单个地址并无条件接收 无法链接的付款。每个 CryptoNote 输出的目的地(默认情况下)是一个公钥, 来自收件人的地址和发件人的随机数据。相对 Bitcoin 的主要优势 默认情况下,每个目标密钥都是唯一的(除非发送者对每个目标密钥使用相同的数据) 他的交易给同一个接收者)。因此,不存在“地址重用”的问题 设计,没有观察者可以确定是否有任何交易被发送到特定地址或链接 两个地址在一起。 6 11 所以这就像 Bitcoin,但具有无限的匿名邮政信箱,只能由收件人兑换 生成与环签名一样匿名的私钥。 Bitcoin 就是这样工作的。 如果 Alex 刚刚从 Frank 收到的钱包里有 0.112 Bitcoin,那么她确实有一个签名 消息“我,[FRANK],发送 0.112 Bitcoin 至 [alex] + H0 + N0”,其中 1) Frank 已签署 用他的私钥 [FRANK] 发送消息,2) Frank 已用 Alex 的公钥签署了该消息 key,[alex],3) Frank 包含了某种形式的比特币历史,H0,以及 4) Frank 包括称为 nonce, N0 的随机数据位。 如果 Alex 然后想要发送 0.011 Bitcoin 给 Charlene,她会接受 Frank 的消息,并且她 将其设置为 H1,并签署两条消息:一条用于她的交易,一条用于更改。 H1=“我,[FRANK],发送 0.112 Bitcoin 至 [alex] + H0 + N” “我,[ALEX],发送 0.011 Bitcoin 至 [charlene] + H1 + N1" “我,[ALEX],发送 0.101 Bitcoin 作为对 [alex] + H1 + N2 的更改。” Alex 用她的私钥 [ALEX] 签署了两条消息,第一条消息是用 Charlene 的 公钥 [charlene],带有 Alex 公钥 [alex] 的第二条消息,包括 历史和一些随机生成的 nonces N1 和 N2 适当。 Cryptonote 的工作原理如下: 如果 Alex 在她刚刚从 Frank 收到的钱包里有 0.112 Cryptonote,那么她确实有一个签名的 消息“我,[临时组中的某个人],将 0.112 Cryptonote 发送到 [一次性地址] + H0 + N0。” Alex 通过检查她的私钥 [ALEX] 发现这是她的钱 每一条传递的消息的[一次性地址],如果她想花掉它,她会在 以下方式。 她选择了这笔钱的接收者,也许夏琳已经开始投票支持无人机袭击,所以 亚历克斯想汇款给布伦达。因此 Alex 查找 Brenda 的公钥 [brenda], 并使用她自己的私钥 [ALEX] 生成一次性地址 [ALEX+brenda]。她 然后从加密货币用户网络中选择一个任意集合 C 并构造 来自该临时组的环签名。 我们将历史记录设置为上一条消息,添加 nonces,然后照常进行吗? H1 =“我,[临时组中的某人],将 0.112 Cryptonote 发送到 [一次性地址] + H0 + N0。” “我,[集合 C 中的某个人],将 0.011 Cryptonote 发送至 [one-time-address-made-fromALEX+brenda] + H1 + N1” “我,[集合 C 中的某个人],将 0.101 Cryptonote 作为找零发送给 [one-time-address-madefrom-ALEX+alex] + H1 + N2” 现在,Alex 和 Brenda 都扫描所有传入消息,以查找曾经存在过的一次性地址。 使用他们的密钥创建。 如果他们找到任何消息,那么该消息就是他们自己的全新消息 加密货币! 即便如此,交易仍将达到 blockchain。如果硬币进入该地址 已知是由犯罪分子、政治捐助者或委员会和账户发送的 预算严格(即贪污),或者这些代币的新所有者犯了错误 并将这些硬币发送到一个与他已知拥有的硬币相同的地址,即匿名夹具 比特币上涨了。
私有用户密钥是一对 (a, b) 两个不同的私有 ec-key; 跟踪密钥是一对 (a, B) 私有和公共 ec-key(其中 B = bG 且 a̸= b); 公共用户密钥是从 (a, b) 派生的两个公共 ec-key 的一对 (A, B); 标准地址是提供给人类友好字符串的公共用户密钥的表示 具有纠错功能; 截断的地址是给定的公共用户密钥的后半部分(B点)的表示 转换为人类友好的字符串并进行纠错。 交易结构仍然与Bitcoin中的结构类似:每个用户都可以选择 几个独立的收款(交易输出),用相应的签名 私钥并将它们发送到不同的目的地。 与 Bitcoin 的模型相反,用户拥有唯一的私钥和公钥,在 提出的模型发送者根据接收者的地址生成一次性公钥 一些随机数据。从这个意义上说,同一接收者的传入交易被发送到 一次性公钥(不直接发送到唯一地址)并且只有接收者才能恢复 相应的私人部分来赎回他的资金(使用他唯一的私钥)。收件人可以 使用环签名来支出资金,使他的所有权和实际支出保持匿名。 协议的详细信息将在接下来的小节中解释。 4.3 无法关联的付款 经典的 Bitcoin 地址一旦发布,就成为传入的明确标识符 付款,将它们链接在一起并与接收者的假名绑定。如果有人想要 收到“解绑”交易时,他应该通过私人渠道将其地址传达给发送者。 如果他想收到不同的交易,而这些交易不能被证明属于同一所有者 他应该生成所有不同的地址,并且永远不要以自己的笔名发布它们。 公共 私人 爱丽丝 卡罗尔 鲍勃的地址 1 鲍勃的地址 2 鲍勃的钥匙 1 鲍勃的钥匙 2 鲍勃 图 2. 传统的 Bitcoin 密钥/交易模型。 我们提出了一个解决方案,允许用户发布单个地址并无条件接收 无法链接的付款。每个 CryptoNote 输出的目的地(默认情况下)是一个公钥, 来自收件人的地址和发件人的随机数据。对抗 Bitcoin 的主要优势 默认情况下,每个目标密钥都是唯一的(除非发送者对每个目标密钥使用相同的数据) 他的交易给同一个接收者)。因此,不存在“地址重用”的问题 设计,没有观察者可以确定是否有任何交易被发送到特定地址或链接 两个地址在一起。 6 私有用户密钥是一对 (a, b) 两个不同的私有 ec-key; 跟踪密钥是一对 (a, B) 私有和公共 ec-key(其中 B = bG 且 a̸= b); 公共用户密钥是从 (a, b) 派生的两个公共 ec-key 的一对 (A, B); 标准地址是提供给人类友好字符串的公共用户密钥的表示 具有纠错功能; 截断的地址是给定的公共用户密钥的后半部分(B点)的表示 转换为人类友好的字符串并进行纠错。 交易结构仍然与Bitcoin中的结构类似:每个用户都可以选择 几个独立的收款(交易输出),用相应的签名 私钥并将它们发送到不同的目的地。 与 Bitcoin 的模型相反,用户拥有唯一的私钥和公钥,在 提出的模型发送者根据接收者的地址生成一次性公钥 一些随机数据。从这个意义上说,同一接收者的传入交易被发送到 一次性公钥(不直接发送到唯一地址)并且只有接收者才能恢复 相应的私人部分来赎回他的资金(使用他唯一的私钥)。收件人可以 使用环签名来支出资金,使他的所有权和实际支出保持匿名。 协议的详细信息将在接下来的小节中解释。 4.3 无法关联的付款 经典的 Bitcoin 地址一旦发布,就成为传入的明确标识符 付款,将它们链接在一起并与接收者的假名绑定。如果有人想要 收到“解绑”交易时,他应该通过私人渠道将其地址传达给发送者。 如果他想收到不同的交易,而这些交易不能被证明属于同一所有者 他应该生成所有不同的地址,并且永远不要以自己的笔名发布它们。 公共 私人 爱丽丝 卡罗尔 鲍勃的地址 1 鲍勃的地址 2 鲍勃的钥匙 1 鲍勃的钥匙 2 鲍勃 图 2. 传统的 Bitcoin 密钥/交易模式埃尔。 我们提出了一个解决方案,允许用户发布单个地址并无条件接收 无法链接的付款。每个 CryptoNote 输出的目的地(默认情况下)是一个公钥, 来自收件人的地址和发件人的随机数据。相对 Bitcoin 的主要优势 默认情况下,每个目标密钥都是唯一的(除非发送者对每个目标密钥使用相同的数据) 他的交易给同一个接收者)。因此,不存在“地址重用”的问题 设计,没有观察者可以确定是否有任何交易被发送到特定地址或链接 两个地址在一起。 6 12 因此,用户不是从地址(实际上是公钥)发送硬币到地址 (另一个公钥)使用他们的私钥,用户从一次性邮政信箱发送硬币 (使用您朋友的公钥生成)到一次性邮政信箱(类似地)使用您的 自己的私钥。 从某种意义上说,我们是在说“好吧,每个人在钱被使用的时候把手拿开” 转来转去!只要知道我们的钥匙可以打开那个盒子就足够了 我们知道盒子里有多少钱。 切勿将指纹放在邮政信箱或 实际使用时,只需交易装满现金的盒子即可。这样我们就不知道是谁发的 什么,但是这些公共地址的内容仍然是无摩擦的、可替代的、可分割的,并且 仍然拥有我们想要的所有其他良好的货币品质,比如比特币。” 无限组邮政信箱。 你公布地址,我有私钥。我使用我的私钥和您的地址,并且 一些随机数据,以生成公钥。该算法的设计使得,由于您 地址用于生成公钥,只有您的私钥才能解锁 消息。 观察者 Eve 看到您发布了您的地址,并看到了我宣布的公钥。然而, 她不知道我是否根据你的地址或她的地址或布伦达的地址公布了我的公钥 或夏琳的,或任何人的。她根据我宣布的公钥检查她的私钥 并发现它不起作用;这不是她的钱。她不知道其他人的私钥,并且 只有消息的接收者才拥有可以解锁消息的私钥。所以没有人 倾听可以确定谁收到了钱,更不用说拿走了钱。
公共 私人 爱丽丝 卡罗尔 一次性钥匙 一次性钥匙 一次性钥匙 鲍勃 鲍勃的钥匙 鲍勃的地址 图 3. CryptoNote 密钥/交易模型。 首先,发送者执行 Diffie-Hellman 交换,从他的数据中获取共享秘密,并 收件人地址的一半。然后,他使用共享的密钥计算一次性目标密钥 秘密和地址的后半部分。收件人需要两个不同的 ec-key 对于这两个步骤,因此标准 CryptoNote 地址几乎是 Bitcoin 钱包的两倍 地址。 接收方还执行 Diffie-Hellman 交换以恢复相应的 秘密密钥。 标准交易顺序如下: 1. Alice 想要向 Bob 发送一笔付款,Bob 已经发布了他的标准地址。 她 解压地址并获取 Bob 的公钥 (A, B)。 2. Alice 生成一个随机 \(r \in [1, l - 1]\) 并计算一次性公钥 \(P = H_s(rA)G +\) B. 3. Alice 使用 P 作为输出的目标密钥,并且还打包值 R = rG(作为一部分) Dffie-Hellman 交换的一部分)进入交易的某个地方。请注意,她可以创建 具有唯一公钥的其他输出:不同接收者的密钥(Ai,Bi)意味着不同的 Pi 即使使用相同的 r。 交易 发送方公钥 发射输出 金额 目的地键 R=rG P = Hs(rA)G + B 接收者的 公钥 发送者的随机数据 r (甲、乙) 图 4. 标准交易结构。 4. Alice 发送交易。 5. Bob 用他的私钥 (a, b) 检查每笔通过的交易,并计算 P ′ = Hs(aR)G + B。 如果Alice与Bob作为接收者的交易也在其中, 则 aR = arG = rA 且 P ′ = P。 7 公共 私人 爱丽丝 卡罗尔 一次性钥匙 一次性钥匙 一次性钥匙 鲍勃 鲍勃的钥匙 鲍勃的地址 图 3. CryptoNote 密钥/交易模型。 首先,发送者执行 Diffie-Hellman 交换,从他的数据中获取共享秘密,并 收件人地址的一半。然后,他使用共享的密钥计算一次性目标密钥 秘密和地址的后半部分。收件人需要两个不同的 ec-key 对于这两个步骤,因此标准 CryptoNote 地址几乎是 Bitcoin 钱包的两倍 地址。 接收方还执行 Diffie-Hellman 交换以恢复相应的 秘密密钥。 标准交易顺序如下: 1. Alice 想要向 Bob 发送一笔付款,Bob 已经发布了他的标准地址。 她 解压地址并获取 Bob 的公钥 (A, B)。 2. Alice 生成一个随机 \(r \in [1, l - 1]\) 并计算一次性公钥 \(P = H_s(rA)G +\) B. 3. Alice 使用 P 作为输出的目标密钥,并且还打包值 R = rG(作为一部分) Dffie-Hellman 交换的一部分)进入交易的某个地方。请注意,她可以创建 具有唯一公钥的其他输出:不同接收者的密钥(Ai,Bi)意味着不同的 Pi 即使使用相同的 r。 交易 发送方公钥 发射输出 金额 目的地键 R=rG P = Hs(rA)G + B 接收者的 公钥 发送者的随机数据 r (甲、乙) 图 4. 标准交易结构。 4. Alice 发送交易。 5. Bob 用他的私钥 (a, b) 检查每笔通过的交易,并计算 P ′ = Hs(aR)G + B。 如果Alice与Bob作为接收者的交易也在其中, 则 aR = arG = rA 且 P ′ = P。 7 13 我想知道实施密码学的“选择”会带来多大的痛苦 计划。椭圆形或其他形状。因此,如果将来某个计划被破坏,货币就会转换 无需担心。可能是一个很大的痛苦。 好的,这正是我在之前的评论中所解释的。迪-赫尔曼型 交流很简单。假设 Alex 和 Brenda 各有一个秘密号码 A 和 B,以及一个号码 他们不关心保守秘密,a和b。他们希望生成一个共享秘密而无需 伊娃发现了它。迪耶和赫尔曼想出了一个方法,让亚历克斯和布伦达分享 公开号码a和b,但不是私人号码A和B,并生成共享秘密, K. 使用这个共享秘密 K,无需任何 Eva 监听即可生成相同的秘密 K、Alex 和 Brenda 现在可以使用 K 作为秘密加密密钥并传回秘密消息 等等。 以下是它 CAN 的工作原理,尽管它应该适用于比 100 大得多的数字。 我们将使用 100,因为对整数取模 100 相当于“扔掉所有 但数字的最后两位。” Alex 和 Brenda 各自选择 A、a、B 和 b。他们对 A 和 B 保密。 Alex 告诉 Brenda 她的模 100 的值(仅最后两位数字),Brenda 告诉 Alex 她的 b 值模 100。现在 Eva 知道 (a,b) 模 100。但是 Alex 知道 (a,b,A),所以她 可以计算 x=abA 模 100。亚历克斯砍掉了所有的东西,只留下最后一个数字,因为我们正在工作 再次以 100 为模的整数。同样,布伦达知道 (a,b,B),因此她可以计算 y=abB 模 100。Alex 现在可以发布 x,Brenda 可以发布 y。 但现在 Alex 可以计算 yA = abBA modulo 100,而 Brenda 可以计算 xB = abBA 模 100。 他们都知道同一个号码! 但伊娃听到的只是 (a,b,abA,abB)。她没有简单的方法来计算 abA*B。 现在,这是考虑 Diffie-Hellman 交换的最简单且最不安全的方式。 存在更安全的版本。但大多数版本都可以工作,因为整数分解和离散 对数很难,而这两个问题都可以通过量子计算机轻松解决。 我将研究是否存在任何抵抗量子的版本。 http://en.wikipedia.org/wiki/Diffie%E2%80%93Hellman_key_exchange 此处列出的“标准 txn 序列”缺少一大堆步骤,例如签名。 他们在这里被视为理所当然。这真的很糟糕,因为我们的顺序 签名内容、签名消息中包含的信息等等……所有这些都非常重要 对协议很重要。 在实施“ 标准交易序列”可能会使整个系统的安全性受到质疑。 此外,如果 它们工作的框架与本节一样松散地定义。
公共 私人 爱丽丝 卡罗尔 一次性钥匙 一次性钥匙 一次性钥匙 鲍勃 鲍勃的钥匙 鲍勃的地址 图 3. CryptoNote 密钥/交易模型。 首先,发送者执行 Diffie-Hellman 交换,从他的数据中获取共享秘密,并 收件人地址的一半。然后,他使用共享的密钥计算一次性目标密钥 秘密和地址的后半部分。收件人需要两个不同的 ec-key 对于这两个步骤,因此标准 CryptoNote 地址几乎是 Bitcoin 钱包的两倍 地址。 接收方还执行 Diffie-Hellman 交换以恢复相应的 秘密密钥。 标准交易顺序如下: 1. Alice 想要向 Bob 发送一笔付款,Bob 已经发布了他的标准地址。 她 解压地址并获取 Bob 的公钥 (A, B)。 2. Alice 生成一个随机 \(r \in [1, l - 1]\) 并计算一次性公钥 \(P = H_s(rA)G +\) B. 3. Alice 使用 P 作为输出的目标密钥,并且还打包值 R = rG(作为一部分) Dffie-Hellman 交换的一部分)进入交易的某个地方。请注意,她可以创建 具有唯一公钥的其他输出:不同接收者的密钥(Ai,Bi)意味着不同的 Pi 即使使用相同的 r。 交易 发送方公钥 发射输出 金额 目的地键 R=rG P = Hs(rA)G + B 接收者的 公钥 发送者的随机数据 r (甲、乙) 图 4. 标准交易结构。 4. Alice 发送交易。 5. Bob 用他的私钥 (a, b) 检查每笔通过的交易,并计算 P ′ = Hs(aR)G + B。 如果Alice与Bob作为接收者的交易也在其中, 则 aR = arG = rA 且 P ′ = P。 7 公共 私人 爱丽丝 卡罗尔 一次性钥匙 一次性钥匙 一次性钥匙 鲍勃 鲍勃的钥匙 鲍勃的地址 图 3. CryptoNote 密钥/交易模型。 首先,发送者执行 Diffie-Hellman 交换,从他的数据中获取共享秘密,并 收件人地址的一半。然后,他使用共享的密钥计算一次性目标密钥 秘密和地址的后半部分。收件人需要两个不同的 ec-key 对于这两个步骤,因此标准 CryptoNote 地址几乎是 Bitcoin 钱包的两倍 地址。 接收方还执行 Diffie-Hellman 交换以恢复相应的 秘密密钥。 标准交易顺序如下: 1. Alice 想要向 Bob 发送一笔付款,Bob 已经发布了他的标准地址。 她 解压地址并获取 Bob 的公钥 (A, B)。 2. Alice 生成一个随机 \(r \in [1, l - 1]\) 并计算一次性公钥 \(P = H_s(rA)G +\) B. 3. Alice 使用 P 作为输出的目标密钥,并且还打包值 R = rG(作为一部分) Dffie-Hellman 交换的一部分)进入交易的某个地方。请注意,她可以创建 具有唯一公钥的其他输出:不同接收者的密钥(Ai,Bi)意味着不同的 Pi 即使使用相同的 r。 交易 发送方公钥 发射输出 金额 目的地键 R=rG P = Hs(rA)G + B 接收者的 公钥 发送者的随机数据 r (甲、乙) 图 4. 标准交易结构。 4. Alice 发送交易。 5. Bob 用他的私钥 (a, b) 检查每笔通过的交易,并计算 P ′ = Hs(aR)G + B。 如果Alice与Bob作为接收者的交易也在其中, 则 aR = arG = rA 且 P ′ = P。 7 14 请注意,作者在保持术语简洁方面做得很糟糕 文本,但尤其是在接下来的部分。本文的下一个版本必然是 更加严格。 在文本中,他们将 P 称为他们的一次性公钥。在图中,他们将 R 称为 他们的“Tx 公钥”和 P 作为他们的“目标密钥”。如果我要重写这个,我会 在讨论这些部分之前,非常具体地列出一些术语。 这个井很大。参见第 5 页。 谁选择艾尔? 该图说明交易公钥 R = rG,它是随机选择的 由发送方发送,不是 Tx 输出的一部分。这是因为对于多个来说它可能是相同的 交易给多人,并且 稍后 不会用于支出。生成一个新的R 每次您想要广播新的 CryptoNote 交易时。此外,R仅用于 检查您是否是交易的接收者。这不是垃圾数据,但对任何人来说都是垃圾 没有与 (A,B) 关联的私钥。 另一方面,目的地密钥 P = Hs(rA)G + B 是 Tx 输出的一部分。大家 翻阅每笔经过的交易数据必须检查自己生成的 P* 这个 P 看看他们是否拥有这个传递的交易。任何拥有未使用交易输出的人 (UTXO) 将会有一堆这样的 P 并带有数量。为了度过d、他们 签署一些新消息,包括 P。 Alice 必须使用与未使用的交易输出目标密钥关联的一次性私钥来签署此交易。 Alice 拥有的每把目的地钥匙都配备有 具有(大概)爱丽丝也拥有的一次性私钥。每次爱丽丝想要的时候 将目标密钥的内容发送给我、鲍勃、布伦达、查理或夏琳,她 使用她的私钥来签署交易。收到交易后,我将收到新的 Tx 公钥,一个新的目标公钥,我将能够恢复一个新的一次性私钥 x。将我的一次性私钥 x 与新交易的公共目的地相结合 key(s) 是我们发送新交易的方式
- Bob 可以恢复相应的一次性私钥:x = Hs(aR) + b,因此 P = xG。 他可以随时通过与 x 签署交易来花费此输出。 交易 发送方公钥 发射输出 金额 目的地键 P ′ = Hs(aR)G + bG 一次性公钥 x = Hs(aR) + b 一次性私钥 接收者的 私钥 (一、二) 右 P′ ? = P 图 5. 传入交易检查。 结果,鲍勃收到了与一次性公钥相关的收款,该公钥是 对于观众来说是不可链接的。一些附加说明: • 当鲍勃“识别”他的交易时(参见步骤 5),他实际上只使用了他的一半交易 私人信息:(a,B)。这对也称为跟踪密钥,可以通过 给第三方(卡罗尔)。鲍勃可以委托她处理新交易。鲍勃 不需要明确信任 Carol,因为她无法恢复一次性密钥 p 没有 Bob 的完整私钥 (a, b)。当 Bob 缺乏带宽时,此方法很有用 或计算能力(智能手机、硬件钱包等)。 • 如果爱丽丝想证明她向鲍勃的地址发送了一笔交易,她可以披露 r 或使用任何类型的零知识协议来证明她知道 r (例如通过签名 与 r 的交易。 • 如果 Bob 希望拥有一个审计兼容地址,其中所有传入交易都在 可链接,他可以发布他的跟踪密钥或使用截断的地址。那个地址 只代表一个公共ec-key B,协议所需的剩余部分为 由此导出如下:a = Hs(B) 且 A = Hs(B)G。在这两种情况下,每个人都是 能够“识别”Bob 的所有传入交易,但是,当然,没有人可以花费 其中包含的资金没有密钥 b. 4.4 一次性环签名 一种基于一次性环签名的协议允许用户实现无条件的不可链接性。 不幸的是,普通类型的加密签名允许追踪交易到他们的 各自的发送者和接收者。我们解决这个缺陷的方法是使用不同的签名 类型不同于当前电子现金系统中使用的类型。 我们将首先提供我们算法的一般描述,没有明确引用 电子现金。 一次性环签名包含四种算法:(GEN、SIG、VER、LNK): GEN:采用公共参数并输出 ec 对 (P, x) 和公钥 I。 SIG:接受消息 m、一组公钥 {Pi}i̸=s、一对 (Ps, xs) \(S'\),并输出签名 \(\sigma\) 以及集合 \(S = \)S'\( \cup \{P_s\}\)。 8
-
Bob 可以恢复相应的一次性私钥:x = Hs(aR) + b,因此 P = xG。 他可以随时通过与 x 签署交易来花费此输出。 交易 发送方公钥 发射输出 金额 目的地键 P ′ = Hs(aR)G + bG 一次性公钥 x = Hs(aR) + b 一次性私钥 接收者的 私钥 (一、二) 右 P′ ? = P 图 5. 传入交易检查。 结果,鲍勃收到了与一次性公钥相关的收款,该公钥是 对于观众来说是不可链接的。一些附加说明: • 当鲍勃“识别”他的交易时(参见步骤 5),他实际上只使用了他的一半交易 私人信息:(a,B)。这对也称为跟踪密钥,可以通过 给第三方(卡罗尔)。鲍勃可以委托她处理新交易。鲍勃 不需要明确信任 Carol,因为她无法恢复一次性密钥 p 没有 Bob 的完整私钥 (a, b)。当 Bob 缺乏带宽时,此方法很有用 或计算能力(智能手机、硬件钱包等)。 • 如果爱丽丝想证明她向鲍勃的地址发送了一笔交易,她可以披露 r 或使用任何类型的零知识协议来证明她知道 r (例如通过签名 与 r 的交易。 • 如果 Bob 希望拥有一个审计兼容地址,其中所有传入交易都在 可链接,他可以发布他的跟踪密钥或使用截断的地址。那个地址 只代表一个公共ec-key B,协议所需的剩余部分为 由此导出如下:a = Hs(B) 且 A = Hs(B)G。在这两种情况下,每个人都是 能够“识别”Bob 的所有传入交易,但是,当然,没有人可以花费 其中包含的资金没有密钥 b. 4.4 一次性环签名 一种基于一次性环签名的协议允许用户实现无条件的不可链接性。 不幸的是,普通类型的加密签名允许追踪交易到他们的 各自的发送者和接收者。我们解决这个缺陷的方法是使用不同的签名 类型不同于当前电子现金系统中使用的类型。 我们首先提供一个gener我们算法的所有描述,没有明确引用 电子现金。 一次性环签名包含四种算法:(GEN、SIG、VER、LNK): GEN:采用公共参数并输出 ec 对 (P, x) 和公钥 I。 SIG:接受消息 m、一组公钥 {Pi}i̸=s、一对 (Ps, xs) \(S'\),并输出签名 \(\sigma\) 以及集合 \(S = \)S'\( \cup \{P_s\}\)。 8 15 这里未使用的交易输出是什么样的?该图表明交易输出仅包含两个数据点:金额和目的地键。但这不是 足够了,因为当我尝试使用这个“输出”时,我仍然需要知道 R=rG。请记住,r 由发送者选择,并且 R a) 用于将传入的加密货币识别为您的 拥有和 b) 用于生成用于“认领”您的加密货币的一次性私钥。 我不明白的部分是什么? 采取理论上的“好吧,我们有这些 签名和交易,我们将它们来回传递”到编程世界 “好吧,具体什么信息构成了个体UTXO?” 回答这个问题的最佳方法是深入研究完全未注释的代码主体。 一路走好,比特币团队。 回想一下:可链接性意味着“是同一个人发送的吗?”不可链接性意味着“做了同样的事情” 人收到吗?”。因此,系统可以是可链接的或不可链接的、不可链接的或不可不可链接的。 很烦人,我知道。 因此,当 Nic van Saberhagen 在这里说“……收到的付款[与]一次性相关” 观众无法链接的公钥”,让我们看看他的意思。 首先,考虑这样一种情况:Alice 向 Bob 发送来自同一交易的两个单独的交易。 地址到同一个地址。 在Bitcoin宇宙中,爱丽丝已经犯了错误 从同一地址发送,因此交易未能满足我们对有限的愿望 可链接性。而且,既然她把钱寄到了同一个地址,她就辜负了我们的愿望 为不可链接性。该比特币交易既是(完全)可链接又是不可链接的。 另一方面,在加密货币世界中,假设爱丽丝向鲍勃发送了一些加密货币, 使用鲍勃的公共地址。她选择所有已知的公共密钥作为她的混淆公共密钥集 华盛顿特区都会区的钥匙。 Alex 使用自己的公钥生成一次性公钥 信息和鲍勃的公开信息。她把钱寄出去,任何观察者都会 只能收集“来自华盛顿特区都会区的某人发送了 2.3 个加密货币到 一次性公共地址 XYZ123。” 我们在这里对可链接性进行概率控制,因此我们将其称为“几乎不可链接”。 我们也只看到一次性公钥资金被发送到的地方。即使我们怀疑接收者 是鲍勃,我们没有他的私钥,所以我们无法测试是否通过交易 属于鲍勃,更不用说生成他的一次性私钥来兑换他的加密货币了。所以这个 事实上,完全“无法链接”。 所以,这是所有技巧中最巧妙的。谁愿意真正信任另一个 MtGox?我们可能是 在 Coinbase 上存储一定数量的 BTC 很舒服,但比特币安全的终极目标是 实体钱包。这很不方便。 在这种情况下,您可以放心地泄露一半的私钥,而不会损害您的 自己花钱的能力。 执行此操作时,您所做的就是告诉某人如何打破不可链接性。另一个 CN 像货币一样的属性被保留,例如防止双重支出和 诸如此类的。
-
Bob 可以恢复相应的一次性私钥:x = Hs(aR) + b,因此 P = xG。 他可以随时通过与 x 签署交易来花费此输出。 交易 发送方公钥 发射输出 金额 目的地键 P ′ = Hs(aR)G + bG 一次性公钥 x = Hs(aR) + b 一次性私钥 接收者的 私钥 (一、二) 右 P′ ? = P 图 5. 传入交易检查。 结果,鲍勃收到了与一次性公钥相关的收款,该公钥是 对于观众来说是不可链接的。一些附加说明: • 当鲍勃“识别”他的交易时(参见步骤 5),他实际上只使用了他的一半交易 私人信息:(a,B)。这对也称为跟踪密钥,可以通过 给第三方(卡罗尔)。鲍勃可以委托她处理新交易。鲍勃 不需要明确信任 Carol,因为她无法恢复一次性密钥 p 没有 Bob 的完整私钥 (a, b)。当 Bob 缺乏带宽时,此方法很有用 或计算能力(智能手机、硬件钱包等)。 • 如果爱丽丝想证明她向鲍勃的地址发送了一笔交易,她可以披露 r 或使用任何类型的零知识协议来证明她知道 r (例如通过签名 与 r 的交易。 • 如果 Bob 希望拥有一个审计兼容地址,其中所有传入交易都在 可链接,他可以发布他的跟踪密钥或使用截断的地址。那个地址 只代表一个公共ec-key B,协议所需的剩余部分为 由此导出如下:a = Hs(B) 且 A = Hs(B)G。在这两种情况下,每个人都是 能够“识别”Bob 的所有传入交易,但是,当然,没有人可以花费 其中包含的资金没有密钥 b. 4.4 一次性环签名 一种基于一次性环签名的协议允许用户实现无条件的不可链接性。 不幸的是,普通类型的加密签名允许追踪交易到他们的 各自的发送者和接收者。我们解决这个缺陷的方法是使用不同的签名 类型不同于当前电子现金系统中使用的类型。 我们将首先提供我们算法的一般描述,没有明确引用 电子现金。 一次性环签名包含四种算法:(GEN、SIG、VER、LNK): GEN:采用公共参数并输出 ec 对 (P, x) 和公钥 I。 SIG:接受消息 m、一组公钥 {Pi}i̸=s、一对 (Ps, xs) \(S'\),并输出签名 \(\sigma\) 以及集合 \(S = \)S'\( \cup \{P_s\}\)。 8
- Bob 可以恢复相应的一次性私钥:x = Hs(aR) + b,因此 P = xG。 他可以随时通过与 x 签署交易来花费此输出。 交易 发送方公钥 发射输出 金额 目的地键 P ′ = Hs(aR)G + bG 一次性公钥 x = Hs(aR) + b 一次性私钥 接收者的 私钥 (一、二) 右 P′ ? = P 图 5. 传入交易检查。 结果,鲍勃收到了与一次性公钥相关的收款,该公钥是 对于观众来说是不可链接的。一些附加说明: • 当鲍勃“识别”他的交易时(参见步骤 5),他实际上只使用了他的一半交易 私人信息:(a,B)。这对也称为跟踪密钥,可以通过 给第三方(卡罗尔)。鲍勃可以委托她处理新交易。鲍勃 不需要明确信任 Carol,因为她无法恢复一次性密钥 p 没有 Bob 的完整私钥 (a, b)。当 Bob 缺乏带宽时,此方法很有用 或计算能力(智能手机、硬件钱包等)。 • 如果爱丽丝想证明她向鲍勃的地址发送了一笔交易,她可以披露 r 或使用任何类型的零知识协议来证明她知道 r (例如通过签名 与 r 的交易。 • 如果 Bob 希望拥有一个审计兼容地址,其中所有传入交易都在 可链接,他可以发布他的跟踪密钥或使用截断的地址。那个地址 只代表一个公共ec-key B,协议所需的剩余部分为 由此导出如下:a = Hs(B) 且 A = Hs(B)G。在这两种情况下,每个人都是 能够“识别”Bob 的所有传入交易,但是,当然,没有人可以花费 其中包含的资金没有密钥 b. 4.4 一次性环签名 一种基于一次性环签名的协议允许用户实现无条件的不可链接性。 不幸的是,普通类型的加密签名允许追踪交易到他们的 各自的发送者和接收者。我们解决这个缺陷的方法是使用不同的签名 类型不同于当前电子现金系统中使用的类型。 我们首先提供一个gener我们算法的所有描述,没有明确引用 电子现金。 一次性环签名包含四种算法:(GEN、SIG、VER、LNK): GEN:采用公共参数并输出 ec 对 (P, x) 和公钥 I。 SIG:接受消息 m、一组公钥 {Pi}i̸=s、一对 (Ps, xs) \(S'\),并输出签名 \(\sigma\) 以及集合 \(S = \)S'\( \cup \{P_s\}\)。 8 16 是的,现在我们有 a) 付款地址和 b) 付款 ID。 批评者可能会问“我们真的需要这样做吗?毕竟,如果商家收到 112.00678952 CN 完全正确,那是我的订单,我有屏幕截图或收据或其他什么,不是吗 疯狂的精确度足够了吗?”答案是“也许,大多数时候,在日常生活中, 面对面交易。” 然而,更常见的情况(尤其是在数字世界中)是这样的:商家出售 一组物品,每个物品都有固定的价格。假设对象 A 为 0.001 CN,对象 B 为 0.01 CN, 物体C是0.1 CN。现在,如果商家收到一个1.618 CN的订单,有很多很多 (很多!)为客户安排订单的方式。因此,如果没有某种付款 ID, 识别客户所谓的“独特”订单及其所谓的“独特”成本 秩序变得不可能。更有趣的是:如果我在线商店中的所有商品的价格都是 1.0 CN,我每天有 1000 个客户?并且您想证明您恰好购买了 3 件物品 两周前?没有付款ID?祝你好运,伙计。 长话短说:当鲍勃发布一个付款地址时,他最终可能还会发布一个 以及付款 ID(例如 Poloniex XMR 存款)。这与描述的不同 在此处的文本中,Alice 是生成付款 ID 的人。 Bob 也必须有某种方式来生成支付 ID。 (一、乙) 回想一下,跟踪密钥 (a,B) 可以被发布;失去“a”意志价值的秘密 不侵犯您的消费能力或允许人们从您那里偷窃(我认为......这会 有待证明),它只会让人们看到所有传入的交易。 如本段所述,截断的地址仅采用密钥的“私有”部分 并从“公共”部分生成它。显示“a”的值将消除不可链接性 但将保留其余交易。 作者的意思是“not unlinkable”,因为unlinkable指的是接收者而linkable 指发件人。 很明显,作者没有意识到可链接性有两个不同的方面。 毕竟,交易是图上的有向对象,因此会出现两个问题: “这两笔交易是同一个人进行的吗?”以及“这两笔交易即将到来吗? 来自同一个人?” 这是一个“不回头”的政策,在该政策下,CryptoNote 的不可链接性属性是 有条件的。也就是说,Bob 可以选择他传入的交易不是不可链接的 使用该政策。 这是他们在随机预言模型下证明的主张。我们会谈到这一点;随机的 甲骨文有优点也有缺点。
VER:接受消息 m、集合 S、签名 \(\sigma\) 并输出“真”或“假”。 LNK:采用集合 I = {Ii}、签名 \(\sigma\) 并输出“linked”或“indep”。 该协议背后的想法相当简单:用户生成一个签名,该签名可以是 通过一组公钥而不是唯一的公钥进行检查。签名者的身份是 与公钥在集合中的其他用户无法区分,直到所有者生成 使用相同密钥对的第二个签名。 私钥 x0 \(\cdots\) 希 \(\cdots\) xn 公钥 P0 \(\cdots\) 圆周率 \(\cdots\) PN 戒指 签名 标志 验证 图 6. 环签名匿名性。 GEN:签名者选择一个随机密钥 \(x \in [1, l - 1]\) 并计算相应的密钥 公钥 P = xG。此外,他还计算了另一个公钥 I = xHp(P),我们将其 称之为“关键图像”。 SIG:签名者生成具有非交互式零知识的一次性环签名 使用 [21] 中的技术进行证明。他从其他用户的 n 中随机选择子集 \(S'\) 公钥 Pi、他自己的密钥对 (x, P) 和密钥图像 I。令 \(0 \leq s \leq n\) 为签名者的秘密索引 在 S 中(因此他的公钥是 Ps)。 他随机选择一个{qi |我= 0 。 。 。 n} 和 {wi |我= 0 。 。 。 n, i ̸= s} 从 (1 . . . l) 并应用 以下转换: 李= ( qiG, 如果我=s qiG + wiPi, 如果 i ̸= s 里= ( qiHp(Pi), 如果我=s qiHp(Pi) + wiI, 如果 i ̸= s 下一步是接受非交互式挑战: c = Hs(m, L1, ..., Ln, R1, ..., Rn) 最后签名者计算响应: ci = 无线, 如果 i ̸= s c - 正压 我=0 词 模l, 如果我=s 里= ( 气, 如果 i ̸= s qs-csx 模l, 如果我=s 所得签名为 \(\sigma = (I, c_1, \ldots, c_n, r_1, \ldots, r_n)\)。 9 VER:接受消息 m、集合 S、签名 \(\sigma\) 并输出“真”或“假”。 LNK:采用集合 I = {Ii}、签名 \(\sigma\) 并输出“linked”或“indep”。 该协议背后的想法相当简单:用户生成一个签名,该签名可以是 通过一组公钥而不是唯一的公钥进行检查。签名者的身份是 与公钥在集合中的其他用户无法区分,直到所有者生成 使用相同密钥对的第二个签名。 私钥 x0 \(\cdots\) 希 \(\cdots\) xn 公钥 P0 \(\cdots\) 圆周率 \(\cdots\) PN 戒指 签名 标志 验证 图 6. 环签名匿名性。 GEN:签名者选择一个随机密钥 \(x \in [1, l - 1]\) 并计算相应的密钥 公钥 P = xG。此外,他还计算了另一个公钥 I = xHp(P),我们将其 称之为“关键图像”。 SIG:签名者生成具有非交互式零知识的一次性环签名 使用 [21] 中的技术进行证明。他从其他用户的 n 中随机选择子集 \(S'\) 公钥 Pi、他自己的密钥对 (x, P) 和密钥图像 I。令 \(0 \leq s \leq n\) 为签名者的秘密索引 在 S 中(因此他的公钥是 Ps)。 他随机选择一个{qi |我= 0 。 。 。 n} 和 {wi |我= 0 。 。 。 n, i ̸= s} 从 (1 . . . l) 并应用 以下转换: 李= ( qiG, 如果我=s qiG + wiPi, 如果 i ̸= s 里= ( qiHp(Pi), 如果我=s qiHp(Pi) + wiI, 如果 i ̸= s 下一步是接受非交互式挑战: c = Hs(m, L1, ..., Ln, R1, ..., Rn) 最后签名者计算响应: ci = 无线, 如果 i ̸= s c - 正压 我=0 词 模l, 如果我=s 里= ( 气, 如果 i ̸= s qs-csx 模l, 如果我=s 所得签名为 \(\sigma = (I, c_1, \ldots, c_n, r_1, \ldots, r_n)\)。 9 17 号 也许这很愚蠢,但是在联合 S 和 P_s 时必须小心。如果您只是附加 最后一个公钥,不可链接性被破坏,因为任何人都检查传递的交易 可以只检查每笔交易和繁荣中列出的最后一个公钥。这就是公钥 与发件人相关联。因此,联合后,伪随机数生成器必须是 用于排列所选的公钥。 “......直到所有者使用相同的密钥对生成第二个签名。”我希望作者(?) 将对此进行详细说明。 我相信这意味着“确保每次选择一组公钥来混淆 你自己选择一套全新的钥匙,没有两把钥匙是一样的。” 对不可链接性施加相当强的条件。也许“你从其中选择一个新的随机集 所有可能的键”的假设是,虽然非平凡的交叉点将不可避免地 发生,它们不会经常发生。 不管怎样,我需要更深入地研究这个陈述。 这正在生成环签名。 零知识证明太棒了:我挑战你向我证明你知道一个秘密 而不泄露秘密。例如,假设我们在一个甜甜圈形状的洞穴的入口处, 在洞穴的后面(从入口处看不到)有一个o你通往的新门 声称你有钥匙。如果你朝一个方向走,它总是会让你通过,但如果你朝另一方向走 其他方向,你需要一把钥匙。但你甚至不想给我看钥匙,更不用说 让我看看它能打开门。但你想向我证明你知道如何打开 门。 在互动环境中,我抛硬币。 左边是头,右边是尾,然后你沿着 甜甜圈形状的洞穴,无论硬币指向你的方向。在我的视线之外的后面,你 打开门绕到另一边回来。我们重复抛硬币实验 直到我确信你有钥匙为止。 但这显然是交互式零知识证明。有一些非交互式版本,您和我永远不需要交流;这样,窃听者就无法干扰。 http://en.wikipedia.org/wiki/Zero-knowledge_proof 这与之前的定义相反。
VER:接受消息 m、集合 S、签名 \(\sigma\) 并输出“真”或“假”。 LNK:采用集合 I = {Ii}、签名 \(\sigma\) 并输出“linked”或“indep”。 该协议背后的想法相当简单:用户生成一个签名,该签名可以是 通过一组公钥而不是唯一的公钥进行检查。签名者的身份是 与公钥在集合中的其他用户无法区分,直到所有者生成 使用相同密钥对的第二个签名。 私钥 x0 \(\cdots\) 希 \(\cdots\) xn 公钥 P0 \(\cdots\) 圆周率 \(\cdots\) PN 戒指 签名 标志 验证 图 6. 环签名匿名性。 GEN:签名者选择一个随机密钥 \(x \in [1, l - 1]\) 并计算相应的密钥 公钥 P = xG。此外,他还计算了另一个公钥 I = xHp(P),我们将其 称之为“关键图像”。 SIG:签名者生成具有非交互式零知识的一次性环签名 使用 [21] 中的技术进行证明。他从其他用户的 n 中随机选择子集 \(S'\) 公钥 Pi、他自己的密钥对 (x, P) 和密钥图像 I。令 \(0 \leq s \leq n\) 为签名者的秘密索引 在 S 中(因此他的公钥是 Ps)。 他随机选择一个{qi |我= 0 。 。 。 n} 和 {wi |我= 0 。 。 。 n, i ̸= s} 从 (1 . . . l) 并应用 以下转换: 李= ( qiG, 如果我=s qiG + wiPi, 如果 i ̸= s 里= ( qiHp(Pi), 如果我=s qiHp(Pi) + wiI, 如果 i ̸= s 下一步是接受非交互式挑战: c = Hs(m, L1, ..., Ln, R1, ..., Rn) 最后签名者计算响应: ci = 无线, 如果 i ̸= s c - 正压 我=0 词 模l, 如果我=s 里= ( 气, 如果 i ̸= s qs-csx 模l, 如果我=s 所得签名为 \(\sigma = (I, c_1, \ldots, c_n, r_1, \ldots, r_n)\)。 9 VER:接受消息 m、集合 S、签名 \(\sigma\) 并输出“真”或“假”。 LNK:采用集合 I = {Ii}、签名 \(\sigma\) 并输出“linked”或“indep”。 该协议背后的想法相当简单:用户生成一个签名,该签名可以是 通过一组公钥而不是唯一的公钥进行检查。签名者的身份是 与公钥在集合中的其他用户无法区分,直到所有者生成 使用相同密钥对的第二个签名。 私钥 x0 \(\cdots\) 希 \(\cdots\) xn 公钥 P0 \(\cdots\) 圆周率 \(\cdots\) PN 戒指 签名 标志 验证 图 6. 环签名匿名性。 GEN:签名者选择一个随机密钥 \(x \in [1, l - 1]\) 并计算相应的密钥 公钥 P = xG。此外,他还计算了另一个公钥 I = xHp(P),我们将其 称之为“关键图像”。 SIG:签名者生成具有非交互式零知识的一次性环签名 使用 [21] 中的技术进行证明。他从其他用户的 n 中随机选择子集 \(S'\) 公钥 Pi、他自己的密钥对 (x, P) 和密钥图像 I。令 \(0 \leq s \leq n\) 为签名者的秘密索引 在 S 中(因此他的公钥是 Ps)。 他随机选择一个{qi |我= 0 。 。 。 n} 和 {wi |我= 0 。 。 。 n, i ̸= s} 从 (1 . . . l) 并应用 以下转换: 李= ( qiG, 如果我=s qiG + wiPi, 如果 i ̸= s 里= ( qiHp(Pi), 如果我=s qiHp(Pi) + wiI, 如果 i ̸= s 下一步是接受非交互式挑战: c = Hs(m, L1, ..., Ln, R1, ..., Rn) 最后签名者计算响应: ci = 无线, 如果 i ̸= s c - 正压 我=0 词 模l, 如果我=s 里= ( 气, 如果 i ̸= s qs-csx 模l, 如果我=s 所得签名为 \(\sigma = (I, c_1, \ldots, c_n, r_1, \ldots, r_n)\)。 9 18 整个区域与加密货币无关,只是简单地描述环签名算法,而无需 参考货币。我怀疑某些符号与论文的其余部分一致, 不过。例如,x 是 GEN 中选择的“随机”密钥,它给出公钥 P 和公钥图像 I。x 的值是 Bob 在第 6 部分第 8 页中计算的值。所以这是 开始澄清之前描述中的一些混乱。 这有点酷;钱没有从“爱丽丝的公共地址转移到鲍勃的公共地址” 地址。”它正在从一次性地址转移到一次性地址。 所以,从某种意义上说,这就是这些东西的工作原理。如果亚历克斯有一些加密货币,因为有人 将它们发送给她,这意味着她拥有将它们发送给鲍勃所需的私钥。她用 使用 Bob 的公开信息生成新的一次性地址的 Diffie-Hellman 交换 并且加密货币将被转移到该地址。 现在,由于使用(大概是安全的)DH 交换来生成新的一次性地址 Alex 向其发送了 CN,Bob 是唯一拥有重复该操作所需私钥的人 上面。所以现在,鲍勃是亚历克斯。 http://en.wikipedia.org/wiki/Piecewise#Notation_and_interpretation 求和应该在 j 而不是 i 上索引。每个 c_i 都是随机垃圾(因为 w_i 是随机的) 除了 c_i 屁股与此签名中涉及的实际密钥相关联。 c 的值为 先前信息的 hash。 我认为这可能包含比重新使用索引“i”更糟糕的拼写错误,因为 c_s 似乎 是隐含的,而不是明确的定义。 事实上,如果我们相信这个方程,那么我们可以确定 c_s = (1/2)c - (1/2) sum_i neq s c_i。也就是说,hash 减去一大堆随机数。 另一方面,如果要读取此求和“c_s = (c - sum_j neq s c_j) mod l”,然后我们取之前信息的hash,生成一堆随机数, 减去 hash 中的所有随机数,得到 c_s。这似乎是 根据我的直觉,“应该”发生什么,并且与第 10 页的验证步骤相匹配。 但直觉不是数学。我会更深入地探讨这一点。 和以前一样;除了与实际相关的之外,所有这些都将是随机垃圾 签名者的公钥 x。除了这一次,这更符合我对结构的期望: r_i 对于 i!=s 是随机的,并且 r_s 仅由秘密 x 和 s 索引值确定 q_i 和 c_i。
VER:验证者通过应用逆变换来检查签名: ( L′ i = riG + ciPi R′ i = riHp(Pi) + ciI 最后,验证者检查是否 正压 我=0 词 ? = Hs(m, L′ 0,. 。 。 , L′ n,R′ 0,. 。 。 ,R′ n) 模 l 如果这个等式正确,验证器将运行 LNK 算法。否则验证者拒绝 签名。 LNK:验证器检查 I 是否已在过去的签名中使用过(这些值存储在 集 I)。多次使用意味着两个签名是在同一密钥下生成的。 协议的含义:通过应用 L 变换,签名者证明他知道 这样 x 至少有一个 Pi = xG。为了使这个证明不可重复,我们引入了关键图像 因为 I = xHp(P)。签名者使用相同的系数 (ri, ci) 来证明几乎相同的陈述: 他知道 x 至少有一个 \(H_p(P_i) = I \cdot x^{-1}\)。 如果映射 \(x \to I\) 是一个注入: 1. 任何人都无法从密钥图像中恢复公钥并识别签名者; 2. 签名者不能使用不同的 I 和相同的 x 进行两个签名。 附录 A 提供了完整的安全分析。 4.5 标准 CryptoNote 交易 通过结合这两种方法(不可链接的公钥和不可追踪的环签名),Bob 实现了 与原始 Bitcoin 方案相比,新的隐私级别。它只需要他存储 一个私钥(a,b)并发布(A,B)以开始接收和发送匿名交易。 在验证每笔交易时,Bob 仅对每个输出执行两次椭圆曲线乘法和一次加法,以检查交易是否属于他。为了他的每一个 输出 Bob 恢复一次性密钥对 (pi, Pi) 并将其存储在他的钱包中。任何输入都可以 仅当它们出现在一次交易中时,才能间接证明它们具有相同的所有者。在 事实上,由于一次性环签名,这种关系更难建立。 通过环签名,鲍勃可以有效地隐藏其他人的每个输入;一切皆有可能 消费者将是等概率的,即使是前任所有者(爱丽丝)也没有比 任何观察者。 当鲍勃签署他的交易时,指定了n个与他的金额相同的外国输出 输出,在没有其他用户参与的情况下混合所有这些。鲍勃本人(以及 其他人)不知道这些付款是否已被花费:可以使用输出 数以千计的签名作为一个模糊因素,而不是作为隐藏的目标。双 支出检查发生在 LNK 阶段,检查已使用的关键映像集。 Bob可以自己选择模糊度:n=1表示他有的概率 花费输出的概率为 50%,n = 99 给出 1%。生成的签名的大小增加 线性为 O(n+1),因此改进的匿名性会让 Bob 付出额外的交易费用。他也可以 设置 n = 0 并使他的环签名仅包含一个元素,但这将立即 揭露他是一个花钱的人。 10 VER:验证者通过应用逆变换来检查签名: ( L′ i = riG + ciPi R′ i = riHp(Pi) + ciI 最后,验证者检查是否 正压 我=0 词 ? = Hs(m, L′ 0,. 。 。 , L′ n,R′ 0,. 。 。 ,R′ n) 模 l 如果这个等式正确,验证器将运行 LNK 算法。否则验证者拒绝 签名。 LNK:验证器检查 I 是否已在过去的签名中使用过(这些值存储在 集 I)。多次使用意味着两个签名是在同一密钥下生成的。 协议的含义:通过应用 L 变换,签名者证明他知道 这样 x 至少有一个 Pi = xG。为了使这个证明不可重复,我们引入了关键图像 因为 I = xHp(P)。签名者使用相同的系数 (ri, ci) 来证明几乎相同的陈述: 他知道 x 至少有一个 \(H_p(P_i) = I \cdot x^{-1}\)。 如果映射 \(x \to I\) 是一个注入: 1. 任何人都无法从密钥图像中恢复公钥并识别签名者; 2. 签名者不能使用不同的 I 和相同的 x 进行两个签名。 附录 A 提供了完整的安全分析。 4.5 标准 CryptoNote 交易 通过结合这两种方法(不可链接的公钥和不可追踪的环签名),Bob 实现了 与原始 Bitcoin 方案相比,新的隐私级别。它只需要他存储 一个私钥(a,b)并发布(A,B)以开始接收和发送匿名交易。 在验证每笔交易时,Bob 仅对每个输出执行两次椭圆曲线乘法和一次加法,以检查交易是否属于他。为了他的每一个 输出 Bob 恢复一次性密钥对 (pi, Pi) 和 st把它放在他的钱包里。任何输入都可以 仅当它们出现在一次交易中时,才能间接证明它们具有相同的所有者。在 事实上,由于一次性环签名,这种关系更难建立。 通过环签名,鲍勃可以有效地隐藏其他人的每个输入;一切皆有可能 消费者将是等概率的,即使是前任所有者(爱丽丝)也没有比 任何观察者。 当鲍勃签署他的交易时,指定了n个与他的金额相同的外国输出 输出,在没有其他用户参与的情况下混合所有这些。鲍勃本人(以及 其他人)不知道这些付款是否已被花费:可以使用输出 数以千计的签名作为一个模糊因素,而不是作为隐藏的目标。双 支出检查发生在 LNK 阶段,检查已使用的关键映像集。 Bob可以自己选择模糊度:n=1表示他有的概率 花费输出的概率为 50%,n = 99 给出 1%。生成的签名的大小增加 线性为 O(n+1),因此改进的匿名性会让 Bob 付出额外的交易费用。他也可以 设置 n = 0 并使他的环签名仅包含一个元素,但这将立即 揭露他是一个花钱的人。 10 19 此时,我非常困惑。 Alex 收到带有签名 (I,c_1, ..., c_n, r_1, ..., r_n) 和公共列表的消息 M 键 S.,她运行 VER。这将计算 L_i' 和 R_i' 这验证了上一页上的 c_s = c - sum_ineq s c_i。 一开始我很困惑。任何人都可以计算 L_i' 和 R_i'。事实上,每个 r_i 和 c_i 已在签名中发布 sigma 与 I 的值一起。集合 S = 所有公钥的 P_i 也已发布。所以任何看过 sigma 和集合的人 键 S = P_i 将获得相同的 L_i’ 和 R_i’ 值,从而检查签名。 但后来我想起这部分只是描述签名算法,而不是“检查” 如果签名了,请检查是否已发送给我,如果是,则去花钱。”这就是 游戏的签名部分。 当我最终到达那里时,我有兴趣阅读附录 A。 我希望看到 Cryptonote 与 Bitcoin 的全面逐个操作比较。 此外,还有电力/可持续性。 算法的哪些部分构成了这里的“输入”? 我相信,交易输入是一个金额和一组 UTXO,其总和大于 金额。 这还不清楚。 “隐藏的目标?”我已经想了几分钟了,但我仍然没有想到 最模糊的想法是它可能意味着什么。 双花攻击只能通过操纵节点感知的使用密钥来执行 图像集 \(I\)。 “模糊度” = n 但交易中包含的公钥总数为 n+1。也就是说,模糊度是“你想要多少其他人” 人群?” 默认情况下,答案可能是“尽可能多”。
VER:验证者通过应用逆变换来检查签名: ( L′ i = riG + ciPi R′ i = riHp(Pi) + ciI 最后,验证者检查是否 正压 我=0 词 ? = Hs(m, L′ 0,. 。 。 , L′ n,R′ 0,. 。 。 ,R′ n) 模 l 如果这个等式正确,验证器将运行 LNK 算法。否则验证者拒绝 签名。 LNK:验证器检查 I 是否已在过去的签名中使用过(这些值存储在 集 I)。多次使用意味着两个签名是在同一密钥下生成的。 协议的含义:通过应用 L 变换,签名者证明他知道 这样 x 至少有一个 Pi = xG。为了使这个证明不可重复,我们引入了关键图像 因为 I = xHp(P)。签名者使用相同的系数 (ri, ci) 来证明几乎相同的陈述: 他知道 x 至少有一个 \(H_p(P_i) = I \cdot x^{-1}\)。 如果映射 \(x \to I\) 是一个注入: 1. 任何人都无法从密钥图像中恢复公钥并识别签名者; 2. 签名者不能使用不同的 I 和相同的 x 进行两个签名。 附录 A 提供了完整的安全分析。 4.5 标准 CryptoNote 交易 通过结合这两种方法(不可链接的公钥和不可追踪的环签名),Bob 实现了 与原始 Bitcoin 方案相比,新的隐私级别。它只需要他存储 一个私钥(a,b)并发布(A,B)以开始接收和发送匿名交易。 在验证每笔交易时,Bob 仅对每个输出执行两次椭圆曲线乘法和一次加法,以检查交易是否属于他。为了他的每一个 输出 Bob 恢复一次性密钥对 (pi, Pi) 并将其存储在他的钱包中。任何输入都可以 仅当它们出现在一次交易中时,才能间接证明它们具有相同的所有者。在 事实上,由于一次性环签名,这种关系更难建立。 通过环签名,鲍勃可以有效地隐藏其他人的每个输入;一切皆有可能 消费者将是等概率的,即使是前任所有者(爱丽丝)也没有比 任何观察者。 当鲍勃签署他的交易时,指定了n个与他的金额相同的外国输出 输出,在没有其他用户参与的情况下混合所有这些。鲍勃本人(以及 其他人)不知道这些付款是否已被花费:可以使用输出 数以千计的签名作为一个模糊因素,而不是作为隐藏的目标。双 支出检查发生在 LNK 阶段,检查已使用的关键映像集。 Bob可以自己选择模糊度:n=1表示他有的概率 花费输出的概率为 50%,n = 99 给出 1%。生成的签名的大小增加 线性为 O(n+1),因此改进的匿名性会让 Bob 付出额外的交易费用。他也可以 设置 n = 0 并使他的环签名仅包含一个元素,但这将立即 揭露他是一个花钱的人。 10 VER:验证者通过应用逆变换来检查签名: ( L′ i = riG + ciPi R′ i = riHp(Pi) + ciI 最后,验证者检查是否 正压 我=0 词 ? = Hs(m, L′ 0,. 。 。 , L′ n,R′ 0,. 。 。 ,R′ n) 模 l 如果这个等式正确,验证器将运行 LNK 算法。否则验证者拒绝 签名。 LNK:验证器检查 I 是否已在过去的签名中使用过(这些值存储在 集 I)。多次使用意味着两个签名是在同一密钥下生成的。 协议的含义:通过应用 L 变换,签名者证明他知道 这样 x 至少有一个 Pi = xG。为了使这个证明不可重复,我们引入了关键图像 因为 I = xHp(P)。签名者使用相同的系数 (ri, ci) 来证明几乎相同的陈述: 他知道 x 至少有一个 \(H_p(P_i) = I \cdot x^{-1}\)。 如果映射 \(x \to I\) 是一个注入: 1. 任何人都无法从密钥图像中恢复公钥并识别签名者; 2. 签名者不能使用不同的 I 和相同的 x 进行两个签名。 附录 A 提供了完整的安全分析。 4.5 标准 CryptoNote 交易 通过结合这两种方法(不可链接的公钥和不可追踪的环签名),Bob 实现了 与原始 Bitcoin 方案相比,新的隐私级别。它只需要他存储 一个私钥(a,b)并发布(A,B)以开始接收和发送匿名交易。 在验证每笔交易时,Bob 仅对每个输出执行两次椭圆曲线乘法和一次加法,以检查交易是否属于他。为了他的每一个 输出 Bob 恢复一次性密钥对 (pi, Pi) 和 st把它放在他的钱包里。任何输入都可以 仅当它们出现在一次交易中时,才能间接证明它们具有相同的所有者。在 事实上,由于一次性环签名,这种关系更难建立。 通过环签名,鲍勃可以有效地隐藏其他人的每个输入;一切皆有可能 消费者将是等概率的,即使是前任所有者(爱丽丝)也没有比 任何观察者。 当鲍勃签署他的交易时,指定了n个与他的金额相同的外国输出 输出,在没有其他用户参与的情况下混合所有这些。鲍勃本人(以及 其他人)不知道这些付款是否已被花费:可以使用输出 数以千计的签名作为一个模糊因素,而不是作为隐藏的目标。双 支出检查发生在 LNK 阶段,检查已使用的关键映像集。 Bob可以自己选择模糊度:n=1表示他有的概率 花费输出的概率为 50%,n = 99 给出 1%。生成的签名的大小增加 线性为 O(n+1),因此改进的匿名性会让 Bob 付出额外的交易费用。他也可以 设置 n = 0 并使他的环签名仅包含一个元素,但这将立即 揭露他是一个花钱的人。 10 20 这很有趣;早些时候,我们为接收者 Bob 提供了一种方法来使所有 INCOMING 通过确定性地选择一半的私钥或通过 将他一半的私钥公开。这是一种不走回头路的政策。在这里,我们看到 发送者 Alex 选择单个传出交易作为可链接的一种方式,但实际上这是 向整个网络显示 Alex 是发件人。这不是一种不走回头路的政策。 这是逐笔交易。 还有第三个政策吗?接收方 Bob 能否为 Alex 生成一个唯一的付款 ID? 永远不会改变,也许使用 Dffie-Hellman 交换? 如果有人包含该付款 ID 绑定在她的交易中的某个位置到 Bob 的地址,它一定来自 Alex。 这样,亚历克斯就不需要通过选择链接特定的网络来向整个网络暴露自己。 交易,但她仍然可以向收款人表明自己的身份。 这不是 Poloniex 所做的吗?
交易 发射输入 输出0 。 。 。 输出i 。 。 。 输出n 关键图像 签名 环签名 目的地键 输出1 目的地键 输出n 国外交易 发送者的输出 目的地键 一次性密钥对 一次性 私钥 I = xHp(P) , x 图 7. 标准交易中的环签名生成。 5 平等的工作量证明 在本节中,我们提出并基础了新的 proof-of-work 算法。 我们的首要目标 是缩小 CPU(多数)和 GPU/FPGA/ASIC(少数)矿工之间的差距。它是 适当的是,某些用户可以比其他用户拥有一定的优势,但他们的投资 应至少随功率线性增长。更一般地说,生产专用设备 必须尽可能降低利润。 5.1 相关作品 原始 Bitcoin proof-of-work 协议使用 CPU 密集型定价函数 SHA-256。 它主要由基本逻辑运算符组成,完全依赖于计算速度 因此,处理器非常适合多核/传送器实现。 然而,现代计算机并不仅限于每秒的操作次数, 还受内存大小的影响。虽然某些处理器可能比其他处理器快得多 [8], 机器之间的内存大小不太可能有所不同。 内存限制价格函数首先由 Abadi 等人提出,定义为 “计算时间主要由访问内存所花费的时间决定的函数”[15]。 主要思想是构建一个分配大数据块的算法(“scratchpad”) 在访问速度相对较慢的内存(例如 RAM)中并且“访问 其中不可预测的位置顺序”。一个块应该足够大以保存 数据比每次访问重新计算数据更有利。该算法还应该 防止内部并行,因此 N 个并发线程应该需要 N 倍的内存 立刻。 Dwork 等人 [22] 研究了这种方法并将其形式化,导致他们提出了另一种方法 定价函数的变体:“Mbound”。 另一件作品属于 F. Coelho [20],他 11 交易 发射输入 输出0 。 。 。 输出i 。 。 。 输出n 关键图像 签名 环签名 目的地键 输出1 目的地键 输出n 国外交易 发送者的输出 目的地键 一次性密钥对 一次性 私钥 I = xHp(P) , x 图 7. 标准交易中的环签名生成。 5 平等的工作量证明 在本节中,我们提出并基础了新的 proof-of-work 算法。 我们的首要目标 是缩小 CPU(多数)和 GPU/FPGA/ASIC(少数)矿工之间的差距。它是 适当的是,某些用户可以比其他用户拥有一定的优势,但他们的投资 应至少随功率线性增长。更一般地说,生产专用设备 必须尽可能降低利润。 5.1 相关作品 原始 Bitcoin proof-of-work 协议使用 CPU 密集型定价函数 SHA-256。 它主要由基本逻辑运算符组成,完全依赖于计算速度 因此,处理器非常适合多核/传送器实现。 然而,现代计算机并不仅限于每秒的操作次数, 还受内存大小的影响。虽然某些处理器可能比其他处理器快得多 [8], 机器之间的内存大小不太可能有所不同。 内存限制价格函数首先由 Abadi 等人提出,定义为 “计算时间主要由访问内存所花费的时间决定的函数”[15]。 主要思想是构建一个分配大数据块的算法(“scratchpad”) 在访问速度相对较慢的内存(例如 RAM)中并且“访问 其中不可预测的位置顺序”。一个块应该足够大以保存 数据比每次访问重新计算数据更有利。该算法还应该 防止内部并行,因此 N 个并发线程应该需要 N 倍的内存 立刻。 Dwork 等人 [22] 研究了这种方法并将其形式化,导致他们提出了另一种方法 定价函数的变体:“Mbound”。 另一件作品属于 F. Coelho [20],他 11 21 表面上,这些是我们的 UTXO:金额和目的地键。如果 Alex 是构建此标准交易并将其发送给 Bob 的人,那么 Alex 也拥有私钥 对于每一个。 我非常喜欢这张图,因为它回答了一些之前的问题。 Txn 输入包括 一组 Txn 输出和一个 key 图像。然后用环签名对其进行签名,包括所有 Alex 拥有该交易中所有外国交易的私钥。的 Txn 输出由金额和目标密钥组成。交易的接收者可以, 随意生成他们的一次性私钥,如本文前面所述,以便花费 钱。 很高兴知道这与实际代码有多少匹配...... 不,Nic van Saberhagen 松散地描述了工作量证明算法的一些属性, 没有实际描述该算法。 CryptoNight 算法本身需要深入分析。 当我读到这里时,我结巴了。投资是否应该至少与电力呈线性增长,或者应该 投资增长最多与功率呈线性关系? 然后我意识到;我作为一个矿工,或者一个投资者,通常会想到“我能得到多少算力” 为了投资?”不是“固定电量需要多少投资?” 当然,用 I 表示投资,用 P 表示功率。如果 I(P) 是作为功率函数的投资 P(I) 是作为投资函数的权力,它们将彼此相反(无论何时 逆可以存在)。如果 I(P) 比线性快,那么 P(I) 比线性慢。因此, 投资者的回报率将会降低。 也就是说,作者在这里所说的是:“当然,当你投入更多时,你会得到更多 权力。但我们应该努力降低回报率。” CPU 投资最终将呈次线性上限;问题是作者是否 我们设计了一种 POW 算法,迫使 ASIC 也这样做。 假设的“未来货币”是否应该总是用最慢/最有限的资源来开采? Abadi 等人(作者是一些 Google 和 Microsoft 工程师)的论文是: 本质上,利用在过去几年内存大小已经小得多的事实 机器之间的差异大于处理器速度,并且具有超过线性的投资功率比。 几年后,这可能需要重新评估!一切都是军备竞赛...... 构造 hash 函数很困难;构建满足这些约束的 hash 函数似乎更困难。这篇文章似乎没有解释实际情况 hashing 算法 CryptoNight。我认为这是 SHA-3 的内存困难实现,基于 在论坛帖子上,但我不知道......这就是重点。必须加以解释。
提出了最有效的解决方案:“北海道”。 据我们所知,基于大数组中伪随机搜索思想的最后一项工作是 C. Percival [32] 称为“scrypt”的算法。与之前的功能不同,它专注于 密钥派生,而不是 proof-of-work 系统。尽管如此,scrypt 仍然可以满足我们的目的: 它在部分 hash 转换问题中作为定价函数效果很好,例如 SHA-256 Bitcoin。 到目前为止,scrypt 已经应用于 Litecoin [14] 和其他一些 Bitcoin 分叉中。然而,它的实现并不是真正受内存限制:比率“内存访问时间/总体时间” time”不够大,因为每个实例仅使用 128 KB。这允许 GPU 矿工 大约提高 10 倍,并且继续留下相对创造的可能性 廉价但高效的采矿设备。 此外,scrypt 结构本身允许在内存大小和 CPU 速度是因为暂存器中的每个块都仅源自前一个块。 例如,您可以存储每隔一个块并以惰性方式重新计算其他块,即仅 当有必要时。假设伪随机索引是均匀分布的, 因此额外块重新计算的期望值为1 \(2 \cdot N\),其中N是数字 迭代次数。总体计算时间增加不到一半,因为还有 与时间无关(恒定时间)的操作,例如准备暂存器和 hashing 每次迭代。节省 2/3 的内存成本 1 \(3 \cdot N\)+1 3 \(\cdot\) \(2 \cdot N\)=N次额外重新计算; 9/10 结果 1 \(10 \cdot N\)+。 。 。 + 1 \(10 \cdot 9 \cdot N\)=4.5N。很容易证明只存储 1 所有块的 s 增加时间小于 s−1 倍 2.这反过来又意味着具有 CPU 的机器 比现代芯片快200倍,只能存储320字节的暂存器。 5.2 提出的算法 我们为 proof-of-work 定价函数提出了一种新的内存限制算法。它依赖于 随机访问慢速内存并强调延迟依赖性。与 scrypt every 相反 新块(长度为 64 字节)取决于所有先前的块。结果是一个假设的 “内存节省者”应该成倍地提高他的计算速度。 我们的算法每个实例大约需要 2 Mb,原因如下: 1.它适合现代处理器的L3缓存(每个核心),这应该成为主流 几年后; 2. 对于现代 ASIC 流水线来说,1MB 的内部存储器几乎是不可接受的大小; 3. GPU 可以运行数百个并发实例,但它们在其他方面受到限制: GDDR5 内存比 CPU L3 缓存慢,但带宽显着,而不是 随机访问速度。 4. 暂存器的显着扩展将需要增加迭代次数,这在 转向意味着总体时间增加。不信任的 p2p 网络中的“大量”调用可能会导致 严重漏洞,因为节点有义务检查每个新块的 proof-of-work。 如果节点在每次 hash 评估上花费大量时间,则可以轻松地 通过大量具有任意工作数据(nonce 值)的虚假对象进行 DDoS 攻击。 12 提出了最有效的解决方案:“北海道”。 据我们所知,基于大数组中伪随机搜索思想的最后一项工作是 C. Percival [32] 称为“scrypt”的算法。与之前的功能不同,它专注于 密钥派生,而不是 proof-of-work 系统。尽管如此,scrypt 仍然可以满足我们的目的: 它在部分 hash 转换问题中作为定价函数效果很好,例如 SHA-256 Bitcoin。 到目前为止,scrypt 已经应用于 Litecoin [14] 和其他一些 Bitcoin 分叉中。然而,它的实现并不是真正受内存限制:比率“内存访问时间/总体时间” time”不够大,因为每个实例仅使用 128 KB。这允许 GPU 矿工 大约提高 10 倍,并且继续留下相对创造的可能性 廉价但高效的采矿设备。 此外,scrypt 结构本身允许在内存大小和 CPU 速度是因为暂存器中的每个块都仅源自前一个块。 例如,您可以存储每隔一个块并以惰性方式重新计算其他块,即仅 当有必要时。假设伪随机索引是均匀分布的, 因此额外块重新计算的期望值为1 \(2 \cdot N\),其中N 是数字 迭代次数。总体计算时间增加不到一半,因为还有 与时间无关(恒定时间)的操作,例如准备暂存器和 hashing 每次迭代。节省 2/3 的内存成本 1 \(3 \cdot N\)+1 3 \(\cdot\) \(2 \cdot N\)=N次额外重新计算; 9/10 结果 1 \(10 \cdot N\)+。 。 。 + 1 \(10 \cdot 9 \cdot N\)=4.5N。很容易证明只存储 1 所有块的 s 增加时间小于 s−1 倍 2.这反过来又意味着具有 CPU 的机器 比现代芯片快200倍,只能存储320字节的暂存器。 5.2 提出的算法 我们为 proof-of-work 定价函数提出了一种新的内存限制算法。它依赖于 随机访问慢速内存并强调延迟依赖性。与 scrypt every 相反 新块(长度为 64 字节)取决于所有先前的块。结果是一个假设的 “内存节省者”应该成倍地提高他的计算速度。 我们的算法每个实例大约需要 2 Mb,原因如下: 1.它适合现代处理器的L3缓存(每个核心),这应该成为主流 几年后; 2. 对于现代 ASIC 流水线来说,1MB 的内部存储器几乎是不可接受的大小; 3. GPU 可以运行数百个并发实例,但它们在其他方面受到限制: GDDR5 内存比 CPU L3 缓存慢,但带宽显着,而不是 随机访问速度。 4. 暂存器的显着扩展将需要增加迭代次数,这在 转向意味着总体时间增加。不信任的 p2p 网络中的“大量”调用可能会导致 严重漏洞,因为节点有义务检查每个新块的 proof-of-work。 如果节点在每次 hash 评估上花费大量时间,则可以轻松地 通过大量具有任意工作数据(nonce 值)的虚假对象进行 DDoS 攻击。 12 22 没关系,这是一个加密货币? 算法在哪里?我看到的都是广告。 如果 Cryptonote 的 PoW 算法值得的话,这就是 Cryptonote 真正大放异彩的地方。这不是 真的SHA-256,它并不是真正的scrypt。它是新的、受内存限制且非递归的。
6 更多优点 6.1 平稳发射 CryptoNote 数字货币总量的上限为:MSupply = 264 −1 原子单位。这是仅基于实现限制而不是直觉的自然限制 比如“N个币对任何人来说都应该足够了”。 为了保证发射过程的顺利,我们对块使用以下公式 奖励: 基础奖励 = (MSupply −A) ≫18, 其中 A 是先前生成的硬币数量。 6.2 可调参数 6.2.1 难度 CryptoNote 包含一个目标算法,可以改变每个块的难度。这个 当网络 hashrate 急剧增长或收缩时,减少系统的反应时间, 保持恒定的块率。原始的 Bitcoin 方法计算实际的关系 和最后 2016 个区块之间的目标时间跨度,并将其用作当前区块的乘数 困难。显然这不适合快速重新计算(因为惯性大)并且 导致振荡。 我们算法背后的总体思想是将节点完成的所有工作相加 除以他们花费的时间。工作量的衡量标准是相应的难度值 在每个块中。但由于时间戳不准确且不受信任,我们无法确定确切的时间 块之间的时间间隔。用户可以将他的时间戳转移到未来和下一个时间 间隔可能很小甚至是负值。估计会出现很少的情况 这种情况下,我们可以对时间戳进行排序并剔除异常值(即 20%)。范围为 其余值是 80% 的相应块所花费的时间。 6.2.2 尺寸限制 用户支付存储 blockchain 的费用,并有权对其大小进行投票。 每个矿工 处理平衡成本和费用利润之间的权衡,并设定自己的 用于创建块的“软限制”。最大块大小的核心规则对于 防止 blockchain 被虚假交易淹没,但是该值应该 不要硬编码。 令 MN 为最后 N 个块大小的中值。然后是大小的“硬限制” 接受块的数量是2 \(\cdot\) MN。它可以避免 blockchain 膨胀,但仍然允许限制 如果有必要的话,会随着时间慢慢增长。 交易大小不需要明确限制。它受块大小的限制; 如果有人想创建一个具有数百个输入/输出(或具有 环签名的高度模糊性),他可以通过支付足够的费用来做到这一点。 6.2.3 尺寸过大的处罚 矿工仍然有能力将自己的零费用交易塞满区块,直至达到最大值 大小 \(2 \cdot M_b\)。尽管只有大多数矿工可以改变中值,但仍然存在 13 6 更多优点 6.1 平稳发射 CryptoNote 数字货币总量的上限为:MSupply = 264 −1 原子单位。这是仅基于实现限制而不是直觉的自然限制 比如“N个币对任何人来说都应该足够了”。 为了保证发射过程的顺利,我们对块使用以下公式 奖励: 基础奖励 = (MSupply −A) ≫18, 其中 A 是先前生成的硬币数量。 6.2 可调参数 6.2.1 难度 CryptoNote 包含一个目标算法,可以改变每个块的难度。这个 当网络 hashrate 急剧增长或收缩时,减少系统的反应时间, 保持恒定的块率。原始的 Bitcoin 方法计算实际的关系 和最后 2016 个区块之间的目标时间跨度,并将其用作当前区块的乘数 困难。显然这不适合快速重新计算(因为惯性大)并且 导致振荡。 我们算法背后的总体思想是将节点完成的所有工作相加 除以他们花费的时间。工作量的衡量标准是相应的难度值 在每个块中。但由于时间戳不准确且不受信任,我们无法确定确切的时间 块之间的时间间隔。用户可以将他的时间戳转移到未来和下一个时间 间隔可能很小甚至是负值。估计会出现很少的情况 这种情况下,我们可以对时间戳进行排序并剔除异常值(即 20%)。范围为 其余值是 80% 的相应块所花费的时间。 6.2.2 尺寸限制 用户支付存储 blockchain 的费用,并有权对其大小进行投票。 每个矿工 处理平衡之间的权衡e 费用和利润,并自行设定 用于创建块的“软限制”。最大块大小的核心规则对于 防止 blockchain 被虚假交易淹没,但是该值应该 不要硬编码。 令 MN 为最后 N 个块大小的中值。然后是大小的“硬限制” 接受块的数量是2 \(\cdot\) MN。它可以避免 blockchain 膨胀,但仍然允许限制 如果有必要的话,会随着时间慢慢增长。 交易大小不需要明确限制。它受块大小的限制; 如果有人想创建一个具有数百个输入/输出(或具有 环签名的高度模糊性),他可以通过支付足够的费用来做到这一点。 6.2.3 尺寸过大的处罚 矿工仍然有能力将自己的零费用交易塞满区块,直至达到最大值 大小 \(2 \cdot M_b\)。尽管只有大多数矿工可以改变中值,但仍然存在 13 23 原子单位。我喜欢这样。这相当于中本聪吗? 如果是这样,那就意味着将有 1850 亿枚加密货币。 我知道这最终必须在几页中进行调整,或者可能存在拼写错误? 如果基本奖励是“所有剩余的硬币”,那么只有一个区块就足以获得所有硬币。 即时。 另一方面,如果这应该以某种方式与 现在与某个硬币生产终止日期之间的时间差? 那会 有道理。 另外,在我的世界里,像这样的两个大于符号意味着“远大于”。作者有没有 可能意味着别的什么? 如果每个区块都进行难度调整,那么攻击者可能会拥有一个非常大的农场 机器在精心选择的时间间隔内断断续续地挖矿。如果难度调整公式没有得到适当的抑制,这可能会导致难度的混乱爆炸(或崩溃到零)。 毫无疑问,Bitcoin的方法不适合快速重新计算,但惯性的思想 这些系统中的功能需要得到证明,而不是想当然。此外,振荡 网络困难不一定是问题,除非它导致表面上的振荡 硬币的供应 - 以及快速变化的难度可能会导致“过度修正”。 所花费的时间,特别是在几分钟之类的短时间内,将与“总时间”成正比。 网络上创建的块数。”比例常数本身会增长 随着时间的推移,如果 CN 起飞的话,可能会呈指数级增长。 简单地调整难度以保持“在网络上创建的总块数”可能是一个更好的主意。 自最后一个区块被添加到主链以来的网络”在某个恒定值内,或者 有界变化或类似的东西。如果自适应算法在计算上 可以确定容易实施,这样看来问题就解决了。 但是,如果我们使用这种方法,拥有大型矿场的人可能会关闭他们的矿场 几个小时,然后再次打开它。对于前几个街区,该农场将生产 银行。 所以,实际上,这种方法会提出一个有趣的观点:挖矿(平均而言)变成了 在没有投资回报的情况下输掉比赛,尤其是随着越来越多的人跳上网络。如果挖矿难度 非常密切跟踪的网络 hashrate,我以某种方式怀疑人们会像他们一样开采 目前正在做。 或者,另一方面,他们可能不会让矿场 24/7 持续运转,而是将其转变为 开启 6 小时,关闭 2 小时,开启 6 小时,关闭 2 小时,或类似的时间。只需换成另一种硬币即可 几个小时,等待难度下降,然后重新开始以获得额外的难度 随着网络的适应,盈利能力受到阻碍。你知道吗?这其实大概是 我全心投入的更好的采矿场景之一...... 这可能是循环的,但如果块创建时间平均约为一分钟,我们可以 使用块数作为“花费时间”的代理?
6 更多优点 6.1 平稳发射 CryptoNote 数字货币总量的上限为:MSupply = 264 −1 原子单位。这是仅基于实现限制而不是直觉的自然限制 比如“N个币对任何人来说都应该足够了”。 为了保证发射过程的顺利,我们对块使用以下公式 奖励: 基础奖励 = (MSupply −A) ≫18, 其中 A 是先前生成的硬币数量。 6.2 可调参数 6.2.1 难度 CryptoNote 包含一个目标算法,可以改变每个块的难度。这个 当网络 hashrate 急剧增长或收缩时,减少系统的反应时间, 保持恒定的块率。原始的 Bitcoin 方法计算实际的关系 和最后 2016 个区块之间的目标时间跨度,并将其用作当前区块的乘数 困难。显然这不适合快速重新计算(因为惯性大)并且 导致振荡。 我们算法背后的总体思想是将节点完成的所有工作相加 除以他们花费的时间。工作量的衡量标准是相应的难度值 在每个块中。但由于时间戳不准确且不受信任,我们无法确定确切的时间 块之间的时间间隔。用户可以将他的时间戳转移到未来和下一个时间 间隔可能很小甚至是负值。估计会出现很少的情况 这种情况下,我们可以对时间戳进行排序并剔除异常值(即 20%)。范围为 其余值是 80% 的相应块所花费的时间。 6.2.2 尺寸限制 用户支付存储 blockchain 的费用,并有权对其大小进行投票。 每个矿工 处理平衡成本和费用利润之间的权衡,并设定自己的 用于创建块的“软限制”。最大块大小的核心规则对于 防止 blockchain 被虚假交易淹没,但是该值应该 不要硬编码。 令 MN 为最后 N 个块大小的中值。然后是大小的“硬限制” 接受块的数量是2 \(\cdot\) MN。它可以避免 blockchain 膨胀,但仍然允许限制 如果有必要的话,会随着时间慢慢增长。 交易大小不需要明确限制。它受块大小的限制; 如果有人想创建一个具有数百个输入/输出(或具有 环签名的高度模糊性),他可以通过支付足够的费用来做到这一点。 6.2.3 尺寸过大的处罚 矿工仍然有能力将自己的零费用交易塞满区块,直至达到最大值 大小 \(2 \cdot M_b\)。尽管只有大多数矿工可以改变中值,但仍然存在 13 6 更多优点 6.1 平稳发射 CryptoNote 数字货币总量的上限为:MSupply = 264 −1 原子单位。这是仅基于实现限制而不是直觉的自然限制 比如“N个币对任何人来说都应该足够了”。 为了保证发射过程的顺利,我们对块使用以下公式 奖励: 基础奖励 = (MSupply −A) ≫18, 其中 A 是先前生成的硬币数量。 6.2 可调参数 6.2.1 难度 CryptoNote 包含一个目标算法,可以改变每个块的难度。这个 当网络 hashrate 急剧增长或收缩时,减少系统的反应时间, 保持恒定的块率。原始的 Bitcoin 方法计算实际的关系 和最后 2016 个区块之间的目标时间跨度,并将其用作当前区块的乘数 困难。显然这不适合快速重新计算(因为惯性大)并且 导致振荡。 我们算法背后的总体思想是将节点完成的所有工作相加 除以他们花费的时间。工作量的衡量标准是相应的难度值 在每个块中。但由于时间戳不准确且不受信任,我们无法确定确切的时间 块之间的时间间隔。用户可以将他的时间戳转移到未来和下一个时间 间隔可能很小甚至是负值。估计会出现很少的情况 这种情况下,我们可以对时间戳进行排序并剔除异常值(即 20%)。范围为 其余值是 80% 的相应块所花费的时间。 6.2.2 尺寸限制 用户支付存储 blockchain 的费用,并有权对其大小进行投票。 每个矿工 处理平衡之间的权衡e 费用和利润,并自行设定 用于创建块的“软限制”。最大块大小的核心规则对于 防止 blockchain 被虚假交易淹没,但是该值应该 不要硬编码。 令 MN 为最后 N 个块大小的中值。然后是大小的“硬限制” 接受块的数量是2 \(\cdot\) MN。它可以避免 blockchain 膨胀,但仍然允许限制 如果有必要的话,会随着时间慢慢增长。 交易大小不需要明确限制。它受块大小的限制; 如果有人想创建一个具有数百个输入/输出(或具有 环签名的高度模糊性),他可以通过支付足够的费用来做到这一点。 6.2.3 尺寸过大的处罚 矿工仍然有能力将自己的零费用交易塞满区块,直至达到最大值 大小 \(2 \cdot M_b\)。尽管只有大多数矿工可以改变中值,但仍然存在 13 24 好的,我们有一个 blockchain,每个块都有时间戳 订购了。这显然是为了调整难度而插入的,因为时间戳是 如前所述,非常不可靠。我们是否允许链中存在相互矛盾的时间戳? 如果区块 A 在链中出现在区块 B 之前,并且在财务方面一切都是一致的, 但 A 区似乎是在 B 区之后创建的?因为,也许有人拥有 网络的很大一部分?可以吗? 可能是因为财务状况没有出现问题。 好吧,所以我讨厌这种任意的“只有 80% 的块对于主 blockchain 是合法的” 方法。它的目的是防止骗子调整他们的时间戳?但现在,它增加了 激励每个人谎报自己的时间戳并只选择中位数。 请定义。 意思是“对于这个区块,只包括费用更大的交易” 高于 p%,优先收取高于 2p% 的费用”或类似的费用? 他们说的假货是什么意思? 如果交易与过去的历史一致 blockchain,并且交易包含了让矿工满意的费用,这还不够吗?嗯, 不,不一定。如果不存在最大块大小,则没有什么可以阻止恶意用户 从简单地一次性上传大量交易给自己只是为了放慢速度 网络。 最大块大小的核心规则可以防止人们放入大量垃圾 一次性将 blockchain 上的数据全部删除,只是为了减慢速度。但这样的规则当然必须 具有适应性 - 例如,在圣诞节期间,我们预计流量会激增,并且 块大小变得非常大,然后立即块大小随后下降 再次。因此,我们需要 a) 某种自适应上限或 b) 足够大的上限,以便 99% 合理的圣诞节高峰不会突破上限。当然,第二个是不可能的 估计——谁知道某种货币是否会流行?最好让它适应而不用担心 关于它。但接下来我们有一个控制理论问题:如何在没有 容易受到攻击或疯狂的振荡? 请注意,自适应方法并不能阻止恶意用户积累少量资金 随着时间的推移,blockchain 上的垃圾数据会导致长期膨胀。这是一个不同的问题 总的来说,加密货币存在严重的问题。
6 更多优点 6.1 平稳发射 CryptoNote 数字货币总量的上限为:MSupply = 264 −1 原子单位。这是仅基于实现限制而不是直觉的自然限制 比如“N个币对任何人来说都应该足够了”。 为了保证发射过程的顺利,我们对块使用以下公式 奖励: 基础奖励 = (MSupply −A) ≫18, 其中 A 是先前生成的硬币数量。 6.2 可调参数 6.2.1 难度 CryptoNote 包含一个目标算法,可以改变每个块的难度。这个 当网络 hashrate 急剧增长或收缩时,减少系统的反应时间, 保持恒定的块率。原始的 Bitcoin 方法计算实际的关系 和最后 2016 个区块之间的目标时间跨度,并将其用作当前区块的乘数 困难。显然这不适合快速重新计算(因为惯性大)并且 导致振荡。 我们算法背后的总体思想是将节点完成的所有工作相加 除以他们花费的时间。工作量的衡量标准是相应的难度值 在每个块中。但由于时间戳不准确且不受信任,我们无法确定确切的时间 块之间的时间间隔。用户可以将他的时间戳转移到未来和下一个时间 间隔可能很小甚至是负值。估计会出现很少的情况 这种情况下,我们可以对时间戳进行排序并剔除异常值(即 20%)。范围为 其余值是 80% 的相应块所花费的时间。 6.2.2 尺寸限制 用户支付存储 blockchain 的费用,并有权对其大小进行投票。 每个矿工 处理平衡成本和费用利润之间的权衡,并设定自己的 用于创建块的“软限制”。最大块大小的核心规则对于 防止 blockchain 被虚假交易淹没,但是该值应该 不要硬编码。 令 MN 为最后 N 个块大小的中值。然后是大小的“硬限制” 接受块的数量是2 \(\cdot\) MN。它可以避免 blockchain 膨胀,但仍然允许限制 如果有必要的话,会随着时间慢慢增长。 交易大小不需要明确限制。它受块大小的限制; 如果有人想创建一个具有数百个输入/输出(或具有 环签名的高度模糊性),他可以通过支付足够的费用来做到这一点。 6.2.3 尺寸过大的处罚 矿工仍然有能力将自己的零费用交易塞满区块,直至达到最大值 大小 \(2 \cdot M_b\)。尽管只有大多数矿工可以改变中值,但仍然存在 13 6 更多优点 6.1 平稳发射 CryptoNote 数字货币总量的上限为:MSupply = 264 −1 原子单位。这是仅基于实现限制而不是直觉的自然限制 比如“N个币对任何人来说都应该足够了”。 为了保证发射过程的顺利,我们对块使用以下公式 奖励: 基础奖励 = (MSupply −A) ≫18, 其中 A 是先前生成的硬币数量。 6.2 可调参数 6.2.1 难度 CryptoNote 包含一个目标算法,可以改变每个块的难度。这个 当网络 hashrate 急剧增长或收缩时,减少系统的反应时间, 保持恒定的块率。原始的 Bitcoin 方法计算实际的关系 和最后 2016 个区块之间的目标时间跨度,并将其用作当前区块的乘数 困难。显然这不适合快速重新计算(因为惯性大)并且 导致振荡。 我们算法背后的总体思想是将节点完成的所有工作相加 除以他们花费的时间。工作量的衡量标准是相应的难度值 在每个块中。但由于时间戳不准确且不受信任,我们无法确定确切的时间 块之间的时间间隔。用户可以将他的时间戳转移到未来和下一个时间 间隔可能很小甚至是负值。估计会出现很少的情况 这种情况下,我们可以对时间戳进行排序并剔除异常值(即 20%)。范围为 其余值是 80% 的相应块所花费的时间。 6.2.2 尺寸限制 用户支付存储 blockchain 的费用,并有权对其大小进行投票。 每个矿工 处理平衡之间的权衡e 费用和利润,并自行设定 用于创建块的“软限制”。最大块大小的核心规则对于 防止 blockchain 被虚假交易淹没,但是该值应该 不要硬编码。 令 MN 为最后 N 个块大小的中值。然后是大小的“硬限制” 接受块的数量是2 \(\cdot\) MN。它可以避免 blockchain 膨胀,但仍然允许限制 如果有必要的话,会随着时间慢慢增长。 交易大小不需要明确限制。它受块大小的限制; 如果有人想创建一个具有数百个输入/输出(或具有 环签名的高度模糊性),他可以通过支付足够的费用来做到这一点。 6.2.3 尺寸过大的处罚 矿工仍然有能力将自己的零费用交易塞满区块,直至达到最大值 大小 \(2 \cdot M_b\)。尽管只有大多数矿工可以改变中值,但仍然存在 13 25 重新调整时间,使一个时间单位为 N 个块,理论上,平均块大小仍然可以按指数比例增长到 2ˆt。另一方面,更通用的上限 对于某个函数 f,下一个块将是 M_nf(M_n)。 f 有哪些性质 我们选择是为了保证区块大小的“合理增长”?的进展 块大小(重新调整时间后)将如下所示: M_n f(M_n)M_n f(f(M_n)M_n)f(M_n)M_n f(f(f(M_n)M_n)f(M_n)M_n)f(f(M_n)M_n)f( ... 这里的目标是选择 f 使得该序列的增长速度不超过线性增长速度, 或者甚至可以作为 Log(t)。当然,如果 f(M_n) = a 对于某个常数 a,则该序列为 实际上 M_n aM_n a^2M_n a^3M_n ... 当然,限制至多线性增长的唯一方法是选择 a=1。 这当然是不可行的。它根本不允许生长。 另一方面,如果 f(M_n) 是一个非常数函数,那么情况就更复杂了 复杂,并且可以提供优雅的解决方案。我会考虑一下这个问题。 该费用必须足够大,才能抵消下一部分的超额罚款。 为什么一般用户被假定为男性,嗯?啊?
可能会使 blockchain 膨胀并在节点上产生额外的负载。劝阻 对于创建大区块的恶意参与者,我们引入了惩罚函数: 新奖励=基础奖励 \(\cdot\) 块大小 明尼苏达州 −1 2 仅当 BlkSize 大于最小空闲块大小时才应用此规则,而最小空闲块大小应 接近max(10kb, \(M_N \cdot 110\%\))。矿工可以创建“正常大小”的区块,甚至 当总费用超过罚款时,利润就超过了罚款。但费用不太可能增长 与惩罚值不同,是二次方,因此会存在平衡。 6.3 交易脚本 CryptoNote 有一个非常简约的脚本子系统。发送者指定一个表达式 Φ = f (x1, x2, ..., xn),其中 n 是目标公钥 {Pi}n 的数量 我=1。只有五个二进制 支持运算符:min、max、sum、mul 和 cmp。当收款人花掉这笔款项时, 他产生 \(0 \leq k \leq n\) 签名并将它们传递到交易输入。验证过程 只需使用 xi = 1 计算 Φ,以检查公钥 Pi 的有效签名,并且 xi = 0。 验证者在 iffΦ > 0 时接受该证明。 尽管很简单,但这种方法涵盖了所有可能的情况: • 多重/阈值签名。对于 Bitcoin 风格的“M-out-of-N”多重签名(即 接收方应提供至少 \(0 \leq M \leq N\) 个有效签名) Φ = x1+x2+。 。 .+xN\(\geq M\) (为了清楚起见,我们使用常见的代数符号)。加权阈值签名 (某些键可能比其他键更重要)可以表示为 Φ = \(w_1 \cdot x_1\) + \(w_2 \cdot x_2\)+ . 。 。 + \(w_N \cdot x_N\) \(\geq wM\)。主密钥对应的场景 Φ = max(\(M \cdot x\), x1 + x2 + ... + xN) \(\geq M\)。很容易证明任何复杂的情况都可以 用这些运算符表示,即它们构成基础。 • 密码保护。拥有秘密密码 s 相当于知道 私钥,确定性地从密码导出:k = KDF(s)。因此,接收器 可以通过在密钥 k 下提供另一个签名来证明他知道密码。 发送者只需将相应的公钥添加到他自己的输出中即可。请注意,这 方法比 Bitcoin [13] 中使用的“交易谜题”安全得多,其中 密码在输入中显式传递。 • 退化的情况。 Φ = 1 意味着任何人都可以花这笔钱; Φ = 0 标志着 产出不能永远使用。 如果与公钥结合的输出脚本对于发送者来说太大,他 可以使用特殊的输出类型,这表明接收者会将这些数据放入他的输入中 而发件人仅提供其中的 hash 。这种方法类似于 Bitcoin 的“pay-to-hash” 功能,但我们没有添加新的脚本命令,而是在数据结构中处理这种情况 水平。 7 结论 我们调查了 Bitcoin 中的主要缺陷并提出了一些可能的解决方案。这些有利的功能和我们不断的开发使得新的电子现金系统 CryptoNote Bitcoin 的有力竞争对手,超越了它的所有叉子。 14 可能会使 blockchain 膨胀并在节点上产生额外的负载。劝阻 对于创建大区块的恶意参与者,我们引入了惩罚函数: 新奖励=基础奖励 \(\cdot\) 块大小 明尼苏达州 −1 2 仅当 BlkSize 大于最小空闲块大小时才应用此规则,而最小空闲块大小应 接近max(10kb, \(M_N \cdot 110\%\))。矿工可以创建“正常大小”的区块,甚至 当总费用超过罚款时,利润就超过了罚款。但费用不太可能增长 与惩罚值不同,是二次方,因此会存在平衡。 6.3 交易脚本 CryptoNote 有一个非常简约的脚本子系统。发送者指定一个表达式 Φ = f (x1, x2, ..., xn),其中 n 是目标公钥 {Pi}n 的数量 我=1。只有五个二进制 支持运算符:min、max、sum、mul 和 cmp。当收款人花掉这笔款项时, 他产生 \(0 \leq k \leq n\) 签名并将它们传递到交易输入。验证过程 只需使用 xi = 1 计算 Φ,以检查公钥 Pi 的有效签名,并且 xi = 0。 验证者在 iffΦ > 0 时接受该证明。 尽管很简单,但这种方法涵盖了所有可能的情况: • 多重/阈值签名。对于 Bitcoin 风格的“M-out-of-N”多重签名(即 接收方应提供至少 \(0 \leq M \leq N\) 个有效签名) Φ = x1+x2+。 。 .+xN\(\geq M\) (为了清楚起见,我们使用常见的代数符号)。加权阈值签名 (某些键可能比其他键更重要)可以表示为 Φ = \(w_1 \cdot x_1\) + \(w_2 \cdot x_2\)+ . 。 。 + \(w_N \cdot x_N\) \(\geq wM\)。和场景io 其中主密钥对应于 Φ = max(\(M \cdot x\), x1 + x2 + ... + xN) \(\geq M\)。很容易证明任何复杂的情况都可以 用这些运算符表示,即它们构成基础。 • 密码保护。拥有秘密密码 s 相当于知道 私钥,确定性地从密码导出:k = KDF(s)。因此,接收器 可以通过在密钥 k 下提供另一个签名来证明他知道密码。 发送者只需将相应的公钥添加到他自己的输出中即可。请注意,这 方法比 Bitcoin [13] 中使用的“交易难题”安全得多,其中 密码在输入中显式传递。 • 退化的情况。 Φ = 1 意味着任何人都可以花这笔钱; Φ = 0 标志着 产出不能永远使用。 如果与公钥结合的输出脚本对于发送者来说太大,他 可以使用特殊的输出类型,这表明接收者会将这些数据放入他的输入中 而发件人仅提供其中的 hash 。这种方法类似于 Bitcoin 的“pay-to-hash” 功能,但我们没有添加新的脚本命令,而是在数据结构中处理这种情况 水平。 7 结论 我们调查了 Bitcoin 中的主要缺陷并提出了一些可能的解决方案。这些有利的功能和我们不断的开发使得新的电子现金系统 CryptoNote Bitcoin 的有力竞争对手,超越了它的所有叉子。 14 26 如果我们能找到一种随着时间的推移限制块大小的方法,这可能是不必要的...... 这也不可能是正确的。他们只是将“NewReward”设置为向上的抛物线,其中 块大小是自变量。所以新的奖励会增加到无穷大。如果,另一方面 手,新的奖励是Max(0,Base Reward(1-(BlkSize/Mn - 1)ˆ2)),那么新的奖励 将是一个向下的抛物线,其峰值位于块大小 = Mn,截距为 块大小 = 0 且块大小 = 2Mn。这似乎就是他们想要描述的。 然而,这并不
Analysis
Analysis
5 Not that it matters too much when a billion people in the world live on less than a dollar a day and have no hope in ever participating in any sort of mining network... but an economic world driven by a p2p currency system with one-cpu-one-vote would be, presumably, more fair than a system driven by fractional reserve banking. But Cryptonote’s protocol still requires 51% honest users... see, for example, the Cryptonote forums where one of the developers, Pliskov, says that a traditional replace-the-data-on-theblockchain 51% attack can still work. https://forum.cryptonote.org/viewtopic.php?f=2&t=198 Note that you don’t really need 51% honest users. You just really need "no single dishonest faction with more than 51% of the hashing power of the network." Let’s call this so-called problem of bitcoin "adaptive rigidity." Cryptonote’s solution to adaptive rigidity is adaptive flexibility in the protocol parameter values. If you need block sizes bigger, no problem, the network will have been gently adjusting the whole time. That is to say, the way that Bitcoin adjusts difficulty over time can be replicated across all of our protocol parameters so that network consensus need not be obtained for updating the protocol. On the surface this seems like a good idea, but without careful forethought, a self-adjusting system can become quite unpredictable and chaotic. We’ll look further into this later as the opportunities arise. "Good" systems are somewhere between adaptively rigid and adaptively flexible, and perhaps even the rigidity itself are adaptive. If we truly had "one-CPU-one-vote," then collaborating and developing pools to get to 51% would be more difficult. We would expect every CPU in the world to be mining, from phones to the on-board CPU in your Tesla while it’s charging. http://en.wikipedia.org/wiki/Pareto_principle I claim that the Pareto equilibrium is somewhat unavoidable. Either 20% of the system will own 80% of the CPUs, or 20% of the system will own 80% of the ASICs. I hypothesize this because the underlying distribution of wealth in society already exhibits the Pareto distribution, and as new miners join up, they are drawn from that underlying distribution. However, I argue that protocols with one-cpu-one-vote will see ROI on hardware. Block reward per node will be more closely proportional to number of nodes in the network because distribution of performance across the nodes will be much more tight. Bitcoin, on the other hand, sees a block reward (per node) more proportional to the computational capacity of that node. That is to say, only the "big boys" are still in the mining game. On the other hand, even though the Pareto principle will still be in play, in a one-cpu-one-vote world, everyone participates in network security and gains a bit of mining income. In an ASIC world, it’s not sensible to rig every XBox and cell phone to mine. In a onecpu-one-vote world, it’s very sensible in terms of mining reward. As a delightful consequence, gaining 51% of the vote is more difficult when there are more and more votes, yielding a lovely benefit to network security..
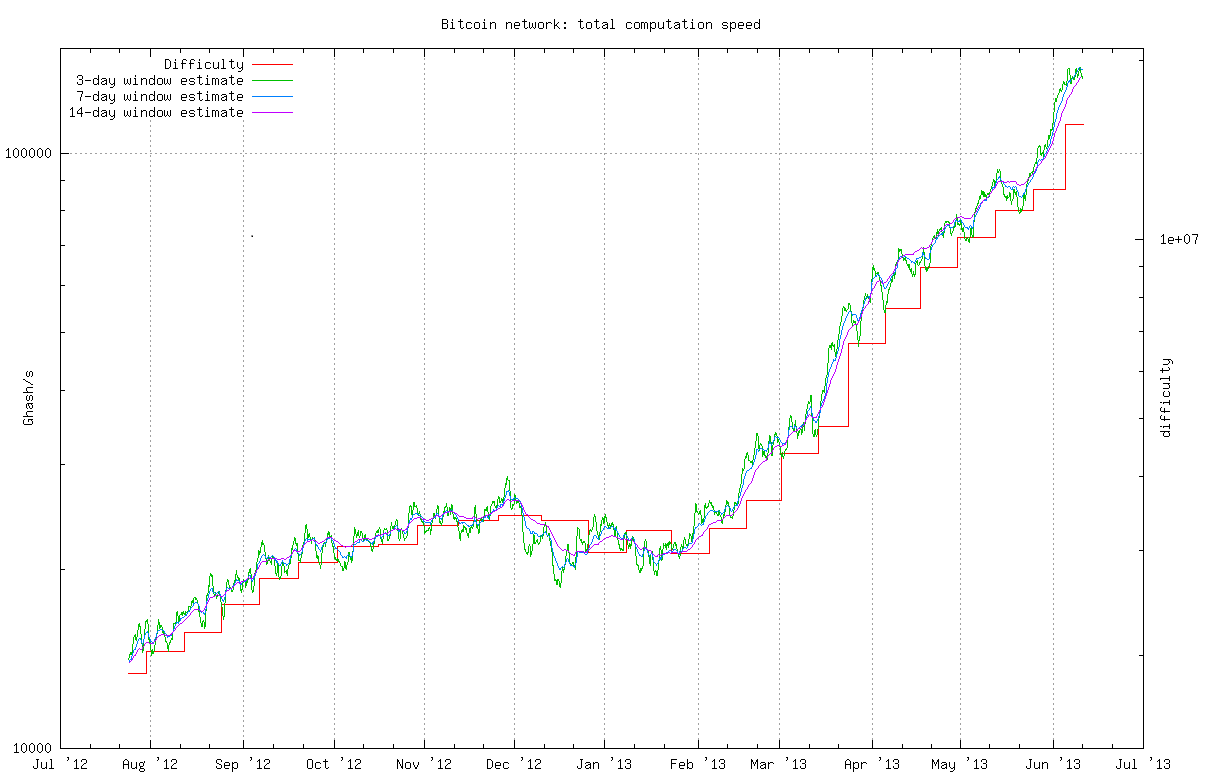
hardware described previously. Suppose that the global hashrate decreases significantly, even for a moment, he can now use his mining power to fork the chain and double-spend. As we shall see later in this article, it is not unlikely for the previously described event to take place. 2.3 Irregular emission Bitcoin has a predetermined emission rate: each solved block produces a fixed amount of coins. Approximately every four years this reward is halved. The original intention was to create a limited smooth emission with exponential decay, but in fact we have a piecewise linear emission function whose breakpoints may cause problems to the Bitcoin infrastructure. When the breakpoint occurs, miners start to receive only half of the value of their previous reward. The absolute difference between 12.5 and 6.25 BTC (projected for the year 2020) may seem tolerable. However, when examining the 50 to 25 BTC drop that took place on November 28 2012, felt inappropriate for a significant number of members of the mining community. Figure 1 shows a dramatic decrease in the network’s hashrate in the end of November, exactly when the halving took place. This event could have been the perfect moment for the malevolent individual described in the proof-of-work function section to carry-out a double spending attack [36]. Fig. 1. Bitcoin hashrate chart (source: http://bitcoin.sipa.be) 2.4 Hardcoded constants Bitcoin has many hard-coded limits, where some are natural elements of the original design (e.g. block frequency, maximum amount of money supply, number of confirmations) whereas other seem to be artificial constraints. It is not so much the limits, as the inability of quickly changing 3 hardware described previously. Suppose that the global hashrate decreases significantly, even for a moment, he can now use his mining power to fork the chain and double-spend. As we shall see later in this article, it is not unlikely for the previously described event to take place. 2.3 Irregular emission Bitcoin has a predetermined emission rate: each solved block produces a fixed amount of coins. Approximately every four years this reward is halved. The original intention was to create a limited smooth emission with exponential decay, but in fact we have a piecewise linear emission function whose breakpoints may cause problems to the Bitcoin infrastructure. When the breakpoint occurs, miners start to receive only half of the value of their previous reward. The absolute difference between 12.5 and 6.25 BTC (projected for the year 2020) may seem tolerable. However, when examining the 50 to 25 BTC drop that took place on November 28 2012, felt inappropriate for a significant number of members of the mining community. Figure 1 shows a dramatic decrease in the network’s hashrate in the end of November, exactly when the halving took place. This event could have been the perfect moment for the malevolent individual described in the proof-of-work function section to carry-out a double spending attack [36]. Fig. 1. Bitcoin hashrate chart (source: http://bitcoin.sipa.be) 2.4 Hardcoded constants Bitcoin has many hard-coded limits, where some are natural elements of the original design (e.g. block frequency, maximum amount of money supply, number of confirmations) whereas other seem to be artificial constraints. It is not so much the limits, as the inability of quickly changing 3 6 Let’s call this what it is, a zombie attack. Let’s discuss how continuous emission may be related to one-cpu-one-vote in a zombie attack scenario. In a one-cpu-one-vote world, every cell phone and car, whenever idle, would be mining. Collecting heaps of cheap hardware to create a mining farm would be very very easy, because just about everything has a CPU in it. On the other hand, at that point, the number of CPUs required to launch a 51% attack would be quite astonishing, I would think. Furthermore, precisely because it would be easy to collect cheap hardware, we can reasonably expect a lot of folks to start hoarding anything with a CPU. The arms race in a one-cpu-one-vote world is necessarily more egalitarian than in an ASIC world. Hence, a discontinuity in network security due to emission rates should be LESS of a problem in a one-cpu-one-vote world. However, two facts remain: 1) discontinuity in emission rate can lead to a stuttering effect in the economy and in network security both, which is bad, and 2) even though a 51% attack performed by someone collecting cheap hardware can still occur in a one-cpu-one-vote world, it seems like it should be harder. Presumably, the safeguard against this is that all the dishonest actors will be trying this simultaneously, and we fall back to Bitcoin’s previous security notion: "we require no dishonest faction to control more than 51% of the network." The author is claiming here that one problem with bitcoin is that discontinuity in coin emission rate could lead to sudden drops in network participation, and hence network security. Thus, a continuous, differentiable, smooth coin emission rate is preferable. The author ain’t wrong, necessarily. Any sort of sudden decrease in network participation can lead to such a problem, and if we can remove one source of it, we should. Having said that, it’s possible that long periods of "relatively constant" coin emission punctuated by sudden changes is the ideal way to go from an economics point of view. I’m not an economist. So, perhaps we must decide if we are going to trade network security for economic something-whatsit here? http://arxiv.org/abs/1402.2009
them if necessary that causes the main drawbacks. Unfortunately, it is hard to predict when the
constants may need to be changed and replacing them may lead to terrible consequences.
A good example of a hardcoded limit change leading to disastrous consequences is the block
size limit set to 250kb1. This limit was sufficient to hold about 10000 standard transactions. In
early 2013, this limit had almost been reached and an agreement was reached to increase the
limit. The change was implemented in wallet version 0.8 and ended with a 24-blocks chain split
and a successful double-spend attack [9]. While the bug was not in the Bitcoin protocol, but
rather in the database engine it could have been easily caught by a simple stress test if there was
no artificially introduced block size limit.
Constants also act as a form of centralization point.
Despite the peer-to-peer nature of
Bitcoin, an overwhelming majority of nodes use the official reference client [10] developed by
a small group of people. This group makes the decision to implement changes to the protocol
and most people accept these changes irrespective of their “correctness”. Some decisions caused
heated discussions and even calls for boycott [11], which indicates that the community and the
developers may disagree on some important points. It therefore seems logical to have a protocol
with user-configurable and self-adjusting variables as a possible way to avoid these problems.
2.5
Bulky scripts
The scripting system in Bitcoin is a heavy and complex feature. It potentially allows one to create
sophisticated transactions [12], but some of its features are disabled due to security concerns and
some have never even been used [13]. The script (including both senders’ and receivers’ parts)
for the most popular transaction in Bitcoin looks like this:
分析
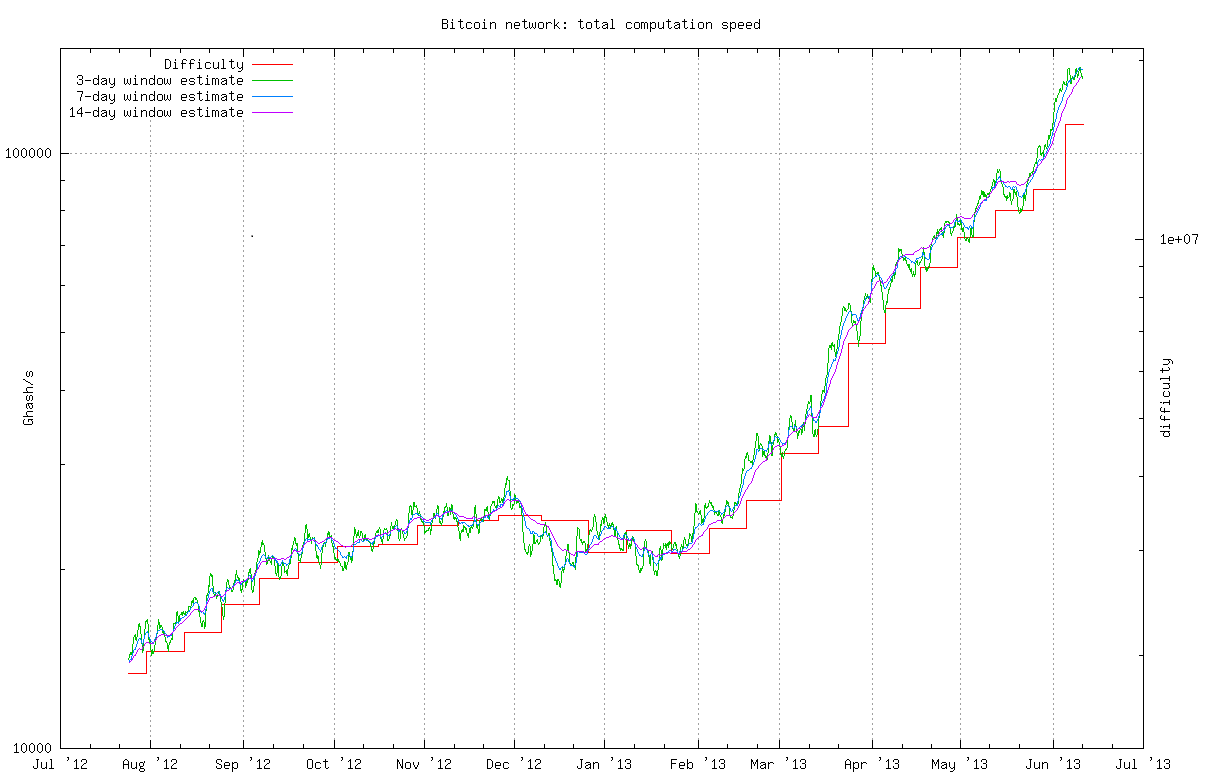
5
当世界上十亿人的生活费低于一美元时,这并不重要。
一天,不希望参与任何类型的采矿网络......但经济
由一个 CPU 一票的 P2P 货币系统驱动的世界大概会更
比由部分准备金银行驱动的系统公平。
但 Cryptonote 的协议仍然需要 51% 的诚实用户……例如,参见 Cryptonote
开发人员之一 Pliskov 表示,传统的替换 blockchain 51% 上的数据的攻击仍然有效。 https://forum.cryptonote.org/viewtopic.php?f=2&t=198
请注意,您实际上并不需要 51% 的诚实用户。你真的需要“没有一个不诚实的人
拥有网络 hashing 力量 51% 以上的派系。”
我们将这种所谓的比特币问题称为“适应性刚性”。 Cryptonote 的自适应解决方案
刚性是协议参数值的自适应灵活性。如果您需要更大的块大小,
没问题,网络将一直在轻轻调整。
也就是说,
Bitcoin 随着时间的推移调整难度的方式可以在我们的所有协议中复制
参数,以便更新协议时不需要获得网络共识。
从表面上看,这似乎是个好主意,但如果没有仔细考虑,就会出现自我调整的情况。
系统可能变得相当不可预测和混乱。稍后我们将进一步研究这一点
机会出现。 “好”系统介于自适应刚性和自适应之间
灵活,也许甚至刚性本身也是适应性的。
如果我们真的拥有“一 CPU 一票”,那么就通过协作和开发池来达到 51%
会更困难。我们预计世界上的每个 CPU 都会从手机开始挖矿
充电时连接到 Tesla 的板载 CPU。
http://en.wikipedia.org/wiki/Pareto_principle
我认为帕累托均衡在某种程度上是不可避免的。系统的 20% 将
拥有 80% 的 CPU,或者 20% 的系统将拥有 80% 的 ASIC。我做出这样的假设是因为社会财富的基本分配已经呈现出帕累托分布,
随着新矿工的加入,他们是从底层分布中抽取的。
然而,我认为采用一 CPU 一投票的协议将会在硬件上带来投资回报。
块
每个节点的奖励将与网络中的节点数量更成正比,因为
节点之间的性能分布将更加紧密。另一方面,Bitcoin
另一方面,看到区块奖励(每个节点)与该节点的计算能力成正比
节点。也就是说,只有“大佬”还在挖矿游戏中。另一方面,
尽管帕累托原则仍然有效,但在一个 CPU 一票的世界中,每个人
参与网络安全并获得一点挖矿收益。
在 ASIC 世界中,让每台 Xbox 和手机都用于挖矿是不明智的。
在一个CPU一票的世界里,就挖矿奖励而言,这是非常明智的。作为一个令人高兴的结果,
当选票越来越多时,获得 51% 的选票会变得更加困难,从而产生可爱的结果
有利于网络安全..前面描述过的硬件。假设全局 hash 率显着下降,即使对于
一会儿,他现在可以利用自己的挖矿能力来分叉链条并进行双花。正如我们将看到的
在本文后面,前面描述的事件发生的可能性也不是很大。
2.3
不规则发射
Bitcoin 具有预定的排放率:每个解决的块都会产生固定数量的硬币。
大约每四年这一奖励就会减半。最初的目的是创建一个
具有指数衰减的有限平滑发射,但实际上我们有分段线性发射
其断点可能会导致 Bitcoin 基础设施出现问题的函数。
当断点发生时,矿工开始只收到先前价值的一半
奖励。 12.5 和 6.25 BTC 之间的绝对差异(预计 2020 年)可能会
看起来还可以忍受。然而,当检查 11 月份发生的 50 至 25 BTC 下跌时
2012 年 2 月 28 日,对于采矿界的相当一部分成员来说,这感觉不合适。图
图 1 显示了 11 月底网络的 hash 速率急剧下降,此时正是
减半发生了。对于恶意者来说,这一事件可能是完美的时刻
proof-of-work 函数部分中描述了执行双花攻击 [36] 的方法。
图 1. Bitcoin hash 费率图表
(来源:http://bitcoin.sipa.be)
2.4
硬编码常量
Bitcoin 有许多硬编码限制,其中一些是原始设计的自然元素(例如
区块频率、最大货币供应量、确认数量),而其他
似乎是人为的限制。与其说是限制,不如说是无法快速改变
3
前面描述过的硬件。假设全局 hash 率显着下降,即使对于
一会儿,他现在可以利用自己的挖矿能力来分叉链条并进行双花。正如我们将看到的
在本文后面,前面描述的事件发生的可能性也不是很大。
2.3
不规则发射
Bitcoin 具有预定的排放率:每个解决的块都会产生固定数量的硬币。
大约每四年这一奖励就会减半。最初的目的是创建一个
具有指数衰减的有限平滑发射,但实际上我们有分段线性发射
其断点可能会导致 Bitcoin 基础设施出现问题的函数。
当断点发生时,矿工开始只收到先前价值的一半
奖励。 12.5 和 6.25 BTC 之间的绝对差异(预计 2020 年)可能会
看起来还可以忍受。然而,当检查 11 月份发生的 50 至 25 BTC 下跌时
2012 年 2 月 28 日,对于采矿界的相当一部分成员来说,这感觉不合适。图
图 1 显示了 11 月底网络的 hash 速率急剧下降,此时正是
减半发生了。对于恶意者来说,这一事件可能是完美的时刻
proof-of-work 函数部分中描述了执行双花攻击 [36] 的方法。
图 1. Bitcoin hash 费率图表
(来源:http://bitcoin.sipa.be)
2.4
硬编码常量
Bitcoin 有许多硬编码限制,其中一些是原始设计的自然元素(例如
区块频率、最大货币供应量、确认数量),而其他
似乎是人为的限制。与其说是限制,不如说是无法快速改变
3
6
让我们称其为僵尸攻击。
让我们讨论一下如何连续发射
与僵尸攻击场景中的一CPU一票相关。
在一个CPU一票的世界里,每部手机和汽车只要闲置,就会进行挖矿。收集大量廉价硬件来创建矿场将非常非常容易,因为只需
几乎所有东西都有一个CPU。另一方面,此时 CPU 的数量
我认为发动 51% 攻击所需的时间是相当惊人的。
此外,
正是因为很容易收集廉价的硬件,我们可以合理地预期
很多人开始囤积任何带有 CPU 的东西。一CPU一票世界中的军备竞赛
必然比 ASIC 世界更加平等。
因此,网络不连续
在一个 CPU 一票的世界中,排放率带来的安全问题应该不是什么问题。
然而,有两个事实仍然存在:1)发射率的不连续性可能会导致口吃效应
经济和网络安全都不好,而且 2) 即使发生 51% 攻击
由收集廉价硬件的人执行的操作仍然可能发生在单 CPU 中-投票世界,
看来应该更难了。
据推测,防止这种情况发生的措施是“所有”不诚实的行为者都会尝试这样做
同时,我们又回到了 Bitcoin 之前的安全概念:“我们不需要不诚实的人
派别控制了超过 51% 的网络。”
作者在这里声称比特币的一个问题是硬币发行的不连续性
速率可能会导致网络参与度突然下降,从而导致网络安全性下降。因此,
连续的、可微的、平滑的硬币发行率是优选的。
作者没有错,一定是这样。网络参与度的任何形式的突然减少都可能导致
导致这样一个问题,如果我们能够消除它的一个根源,我们就应该这样做。话虽如此,这是
长期“相对稳定”的代币发行可能会被突然的变化所打断
从经济学的角度来看,这是理想的方法。我不是经济学家。所以,也许我们
我们必须决定是否要用网络安全来换取经济利益——这是什么?
http://arxiv.org/abs/1402.2009如有必要,它们会导致主要缺点。不幸的是,很难预测何时
常量可能需要改变,替换它们可能会导致可怕的后果。
硬编码限制更改导致灾难性后果的一个很好的例子是块
大小限制设置为 250kb1。这个限制足以容纳大约 10000 个标准交易。在
2013 年初,这一限制几乎已达到,并达成协议增加
限制。该更改在钱包版本 0.8 中实施,并以 24 块链分裂结束
以及成功的双花攻击[9]。虽然该错误不在 Bitcoin 协议中,但是
相反,在数据库引擎中,如果有的话,可以通过简单的压力测试轻松捕获它
没有人为引入的块大小限制。
常量也充当集中点的一种形式。
尽管具有点对点的性质
Bitcoin,绝大多数节点使用官方开发的参考客户端[10]
一小群人。该小组决定对协议进行更改
大多数人都会接受这些变化,无论它们的“正确性”如何。一些决定导致
激烈讨论甚至呼吁抵制[11],这表明社区和
开发人员可能在一些重要问题上存在分歧。因此,制定一项协议似乎是合乎逻辑的
使用用户可配置和自我调整的变量作为避免这些问题的可能方法。
2.5
庞大的脚本
Bitcoin 中的脚本系统是一个繁重且复杂的功能。它可能允许人们创建
复杂的交易[12],但由于安全问题和原因,其某些功能被禁用
有些甚至从未使用过[13]。脚本(包括发送者和接收者部分)
Bitcoin 中最受欢迎的交易如下所示: