
Solana:高性能区块链的新架构
Abstract
บทความนี้นำเสนอสถาปัตยกรรมใหม่สำหรับบล็อกเชนที่มีประสิทธิภาพสูง Solana ใช้กลไกการบอกเวลาแบบใหม่ที่เรียกว่า Proof of History (PoH) ซึ่งเป็นข้อพิสูจน์ในการตรวจสอบลำดับและการผ่านของเวลาระหว่างเหตุการณ์ต่างๆ PoH ใช้เพื่อเข้ารหัสเวลาที่ผ่านไปอย่างไม่ไว้วางใจใน ledger สร้างบันทึกทางประวัติศาสตร์ที่พิสูจน์ว่ามีเหตุการณ์เกิดขึ้นในช่วงเวลาหนึ่งโดยเฉพาะ
นวัตกรรมที่สำคัญคือ PoH ช่วยให้โหนดในเครือข่ายสร้างลำดับเหตุการณ์ชั่วคราวโดยไม่จำเป็นต้องสื่อสารระหว่างกัน ด้วยการใช้ฟังก์ชันหน่วงเวลาที่ตรวจสอบได้ซึ่งนำมาใช้เป็นสายโซ่แฮชตามลำดับ ระบบจะสร้างนาฬิกาเข้ารหัสที่ให้วิธีการตรวจสอบการผ่านของเวลาระหว่างเหตุการณ์ สิ่งนี้ทำให้เครือข่ายสามารถประมวลผลธุรกรรมหลายพันรายการต่อวินาทีในขณะที่ยังคงการกระจายอำนาจและความปลอดภัยไว้
PoH ถูกรวมเข้ากับกลไกฉันทามติ Proof of Stake (PoS) การรวมกันนี้ทำให้เกิดสถาปัตยกรรมบล็อกเชนที่ได้รับการปรับให้เหมาะสมที่สุด โดยที่ validators สามารถตรวจสอบธุรกรรมแบบขนานและบรรลุฉันทามติได้อย่างมีประสิทธิภาพ ระบบได้รับการออกแบบให้ปรับขนาดตามกฎของมัวร์ โดยใช้ประโยชน์จากการเพิ่มประสิทธิภาพฮาร์ดแวร์เพื่อปรับปรุงปริมาณงานโดยไม่กระทบต่อการรับประกันความปลอดภัยของเครือข่ายแบบกระจายอำนาจ
Abstract
本文提出了一种高性能区块链的新架构。Solana实现了一种名为Proof of History(PoH)的新型计时机制——一种用于验证事件之间顺序和时间流逝的证明。PoH用于将无需信任的时间流逝编码到账本中,创建一个历史记录,证明某个事件发生在特定的时间点。
关键创新在于PoH允许网络中的节点在无需相互通信的情况下建立事件的时间顺序。通过使用以顺序哈希链实现的可验证延迟函数,系统生成了一个加密时钟,提供了一种验证事件之间时间流逝的方法。这使得网络能够在保持去中心化和安全性的同时每秒处理数千笔交易。
PoH与Proof of Stake(PoS)共识机制集成。这种组合使得高度优化的区块链架构成为可能,验证者可以并行验证交易并高效地达成共识。该系统被设计为随摩尔定律扩展,利用硬件性能的提升来改善吞吐量,而不牺牲去中心化网络的安全保障。
Introduction
ความท้าทายพื้นฐานในระบบบล็อกเชนคือการบรรลุปริมาณธุรกรรมที่สูงในขณะที่ยังคงรักษาการกระจายอำนาจและความปลอดภัยไว้ การใช้งานบล็อกเชนในปัจจุบันถูกจำกัดด้วยกลไกที่เป็นเอกฉันท์ ซึ่งจำเป็นต้องมีการสื่อสารที่กว้างขวางระหว่างโหนดเพื่อให้ตกลงเรื่องเวลาและการเรียงลำดับของเหตุการณ์ ค่าใช้จ่ายในการประสานงานนี้ทำให้เกิดปัญหาคอขวดที่ป้องกันไม่ให้บล็อกเชนที่มีอยู่ขยายขนาดเพื่อตอบสนองความต้องการของแอปพลิเคชันระดับโลก
ปัญหาหลักคือเวลา ในระบบแบบกระจาย โหนดไม่สามารถพึ่งพานาฬิกาภายนอกได้ เนื่องจากไม่สามารถเชื่อถือได้ว่าการประทับเวลาของโหนดอื่นนั้นแม่นยำ โปรโตคอลฉันทามติบล็อคเชนแบบดั้งเดิมจะแก้ปัญหานี้โดยให้โหนดสื่อสารอย่างกว้างขวางเพื่อตกลงกับสถานะปัจจุบันและลำดับของธุรกรรม ค่าใช้จ่ายในการสื่อสารนี้จำกัดปริมาณงานโดยพื้นฐาน เนื่องจากเครือข่ายสามารถประมวลผลธุรกรรมได้เร็วเท่ากับที่โหนดสามารถบรรลุความเห็นพ้องต้องกันในการสั่งซื้อเท่านั้น
Solana แนะนำ Proof of History เพื่อเป็นแนวทางแก้ไขปัญหาเรื่องเวลานี้ PoH จัดเตรียมวิธีการเข้ารหัสเพื่อพิสูจน์ว่าระยะเวลาหนึ่งผ่านไประหว่างเหตุการณ์ต่างๆ โดยไม่ต้องอาศัยการประทับเวลาจากผู้ที่อาจเป็นอันตราย ด้วยการสร้างบันทึกประวัติที่ตรวจสอบได้ PoH ช่วยให้โหนดสามารถประมวลผลธุรกรรมได้อย่างอิสระ ในขณะที่ยังคงสามารถพิสูจน์ลำดับของเหตุการณ์ที่เกิดขึ้นได้ ความก้าวหน้าครั้งนี้ทำให้เครือข่ายสามารถประมวลผลธุรกรรมแบบขนานและเพิ่มปริมาณงานได้อย่างมาก
ข้อมูลเชิงลึกที่สำคัญคือ ถ้าเราสามารถสร้างแหล่งที่มาของเวลาที่ไม่น่าไว้วางใจ เราก็สามารถขจัดปัญหาคอขวดของการประสานงานออกจากฉันทามติได้ ด้วย PoH ที่มีนาฬิกาเข้ารหัส validators สามารถประมวลผลธุรกรรมแบบขนาน และจำเป็นต้องสื่อสารเพื่อสรุปลำดับตามรูปแบบบัญญัติเท่านั้น การเปลี่ยนแปลงทางสถาปัตยกรรมนี้ช่วยให้ Solana บรรลุระดับประสิทธิภาพที่ก่อนหน้านี้คิดว่าเป็นไปไม่ได้ในบล็อกเชนแบบกระจายอำนาจ
Introduction
区块链系统面临的根本挑战是在保持去中心化和安全性的同时实现高交易吞吐量。当前的区块链实现受限于其共识机制,这些机制需要节点之间进行大量通信来就时间和事件排序达成一致。这种协调开销创建了瓶颈,阻止现有区块链扩展以满足全球规模应用的需求。
核心问题是时间。在分布式系统中,节点不能依赖外部时钟,因为它们无法信任其他节点的时间戳是准确的。传统的区块链共识协议通过让节点进行大量通信来就当前状态和交易顺序达成一致来解决这个问题。这种通信开销从根本上限制了吞吐量,因为网络只能以节点就排序达成共识的速度来处理交易。
Solana引入Proof of History作为这个时间问题的解决方案。PoH提供了一种加密方法来证明事件之间已经过了一定的时间,而无需依赖来自潜在恶意行为者的时间戳。通过创建可验证的历史记录,PoH使节点能够独立处理交易,同时仍然能够证明事件发生的顺序。这一突破使网络能够并行化交易处理并大幅提高吞吐量。
关键洞察是,如果我们能创建一个无需信任的时间源,就可以从共识中消除协调瓶颈。通过PoH提供加密时钟,验证者可以并行处理交易,只需在确定规范排序时进行通信。这种架构转变使Solana能够实现之前在去中心化区块链中被认为不可能的性能水平。
Outline
เอกสารนี้จะอธิบายสถาปัตยกรรมทางเทคนิคของ Solana โดยเน้นไปที่วิธีที่ Proof of History ช่วยให้การดำเนินงานบล็อกเชนมีประสิทธิภาพสูงได้อย่างไร ในขั้นแรกเอกสารจะอธิบายกลไก PoH เองว่า hash chain แบบต่อเนื่องสร้างการเรียงลำดับเหตุการณ์ชั่วคราวที่ตรวจสอบได้อย่างไร เราให้รายละเอียดเกี่ยวกับคุณสมบัติการเข้ารหัสที่ทำให้ PoH ปลอดภัย และสาธิตวิธีที่ validators สามารถตรวจสอบลำดับ PoH ได้อย่างมีประสิทธิภาพ
จากนั้น บทความนี้จะสำรวจว่า PoH ผสานรวมกับฉันทามติ Proof of Stake ได้อย่างไร เราอธิบาย Tower BFT ซึ่งเป็นอัลกอริทึม PoS ที่ออกแบบมาโดยเฉพาะเพื่อใช้ประโยชน์จากคุณสมบัติชั่วคราวของ PoH การผสานรวมช่วยให้ validators ลงคะแนนสถานะของ ledger ณ เวลาประทับ PoH ที่เฉพาะเจาะจง สร้างกลไกที่เป็นเอกฉันท์ที่ทั้งรวดเร็วและปลอดภัย นอกจากนี้เรายังอธิบายเงื่อนไขการตัดเฉือนที่ป้องกันพฤติกรรมที่เป็นอันตรายด้วย
ต่อไป เราจะนำเสนอการออกแบบเครือข่ายและโปรโตคอลการเผยแพร่ข้อมูลของ Solana โปรโตคอล Gulf Stream ช่วยให้สามารถส่งต่อธุรกรรมได้โดยไม่จำเป็นต้องใช้ mempool ช่วยให้ลูกค้าส่งธุรกรรมโดยตรงไปยังผู้นำที่กำลังจะมาถึง เราอธิบายวิธีการทำงานของการหมุนเวียนผู้นำ และวิธีที่เครือข่ายรักษาปริมาณงานที่สูง แม้ว่าผู้นำจะเปลี่ยนไปก็ตาม
สุดท้ายนี้ เราจะพูดถึงสถาปัตยกรรมระบบ รวมถึงหน่วยประมวลผลธุรกรรม (TPU), รันไทม์แบบขนาน Sealevel และ Proof of Replication สำหรับการตรวจสอบการจัดเก็บข้อมูล การคาดการณ์ประสิทธิภาพแสดงให้เห็นว่า Solana สามารถประมวลผลธุรกรรมได้มากกว่า 700,000 รายการต่อวินาทีบนเครือข่ายกิกะบิตมาตรฐาน โดยมีการปรับขนาดปริมาณงานเมื่อฮาร์ดแวร์ได้รับการปรับปรุง
Outline
本文描述了Solana的技术架构,重点介绍Proof of History如何实现高性能区块链运行。文档首先解释PoH机制本身——顺序哈希链如何创建可验证的事件时间排序。我们详细说明使PoH安全的加密属性,并演示验证者如何高效地验证PoH序列。
然后,本文探讨PoH如何与Proof of Stake共识集成。我们描述Tower BFT,这是一种专门设计用于利用PoH时间属性的PoS算法。该集成允许验证者在特定的PoH时间戳上对账本状态进行投票,创建一个既快速又安全的共识机制。我们还解释了防止恶意行为的惩罚条件。
接下来,我们介绍Solana的网络设计和数据传播协议。Gulf Stream协议实现了无需内存池的交易转发,允许客户端直接向即将到来的领导者发送交易。我们描述领导者轮换如何工作以及网络如何在领导权更替时保持高吞吐量。
最后,我们讨论系统架构,包括Transaction Processing Unit(TPU)、Sealevel并行运行时和用于数据存储验证的Proof of Replication。性能预测表明,Solana可以在标准千兆网络上每秒处理超过700,000笔交易,并且吞吐量会随硬件改进而扩展。
Network Design
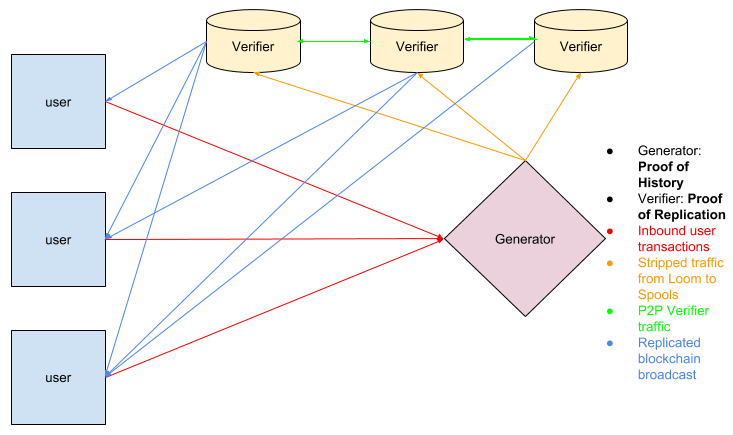
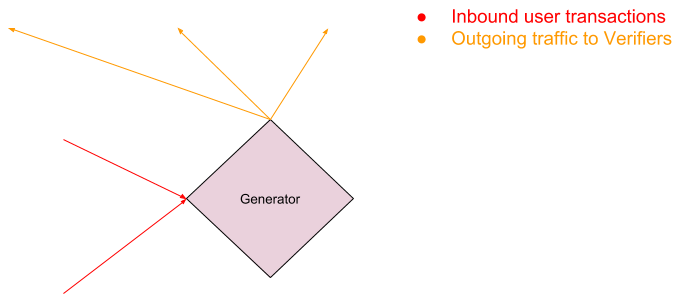
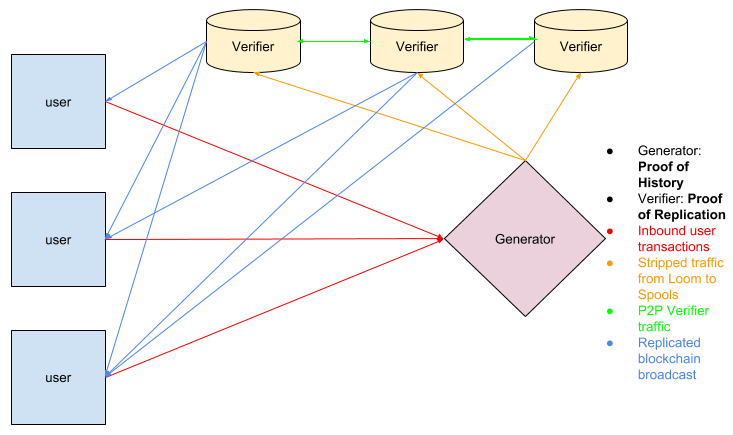
การออกแบบเครือข่ายของ Solana มีศูนย์กลางอยู่ที่ระบบผู้นำแบบหมุนเวียน โดยที่ validators ผลัดกันสร้างบล็อก ผู้นำมีหน้าที่รับผิดชอบในการจัดลำดับธุรกรรมขาเข้าลงในสตรีม PoH และเผยแพร่บล็อกผลลัพธ์ไปยังเครือข่าย ผู้นำจะถูกเลือกผ่านอัลกอริธึมแบบถ่วงน้ำหนักเดิมพัน และทราบกำหนดการหมุนเวียนล่วงหน้า ช่วยให้เครือข่ายเพิ่มประสิทธิภาพการส่งต่อธุรกรรมได้
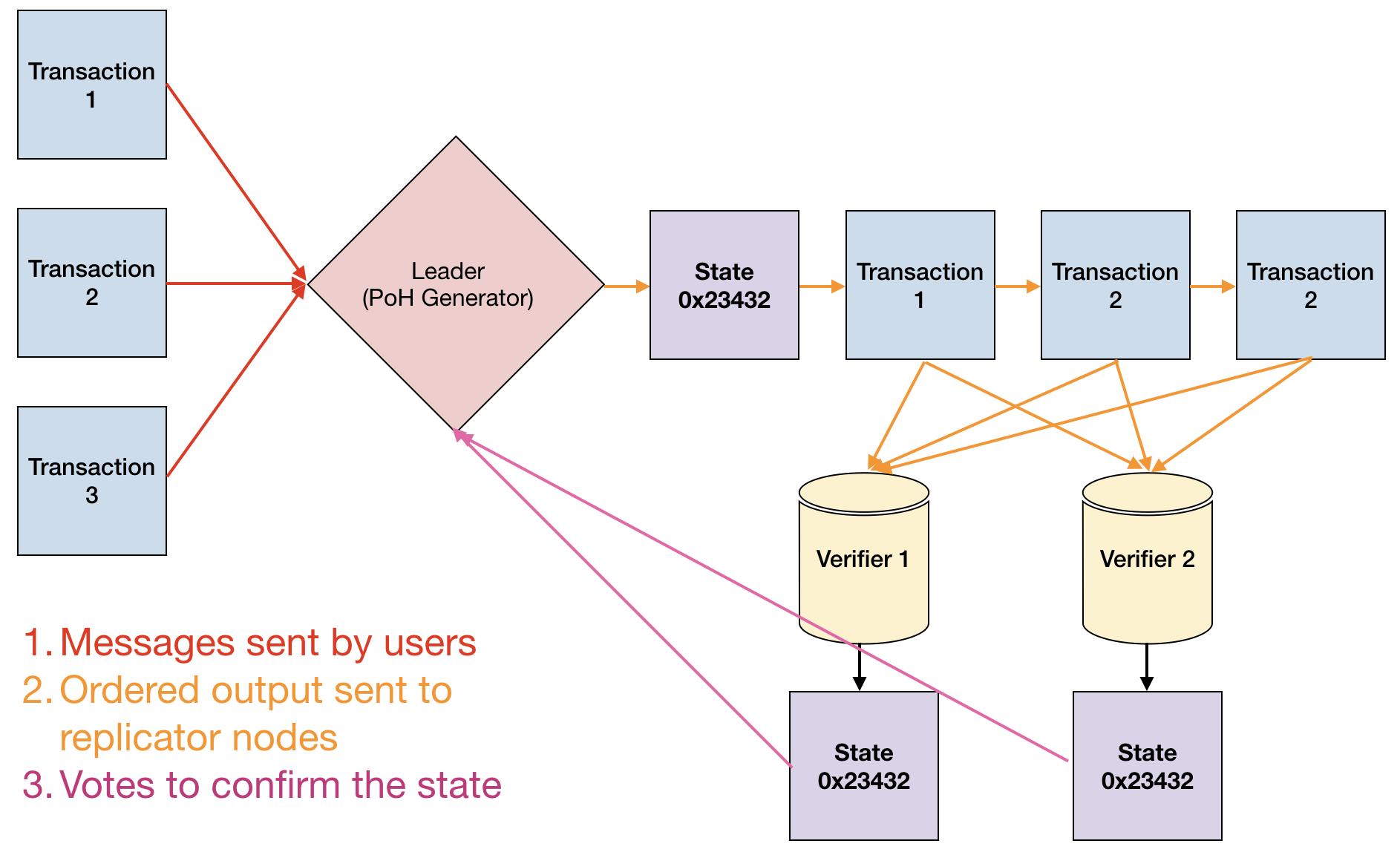
โปรโตคอลกัลฟ์สตรีมช่วยลดความจำเป็นในการใช้ mempool แบบเดิม โดยช่วยให้ลูกค้าสามารถส่งต่อธุรกรรมโดยตรงไปยังผู้นำที่กำลังจะมาถึงได้ เมื่อลูกค้าส่งธุรกรรม มันจะถูกส่งต่อไปยังผู้นำที่คาดหวังตามกำหนดการหมุนเวียน หากผู้นำปัจจุบันไม่สามารถประมวลผลธุรกรรมได้ ก็จะส่งต่อไปยังผู้นำที่คาดหวังคนถัดไป การออกแบบนี้ช่วยลดเวลาแฝงในการยืนยัน และอนุญาตให้ validators ดำเนินธุรกรรมล่วงหน้า เพิ่มประสิทธิภาพปริมาณงานให้ดียิ่งขึ้น
การเผยแพร่ธุรกรรมใช้วิธีการแบบหลายชั้น ลูกค้าส่งธุรกรรมไปที่ validators ซึ่งส่งต่อไปยังผู้นำปัจจุบันหรือที่กำลังจะมาถึง ผู้นำจัดลำดับธุรกรรมลงในสตรีม PoH สร้างการเรียงลำดับทั้งหมด เมื่อจัดลำดับแล้ว ผู้นำจะส่งสตรีม PoH และข้อมูลธุรกรรมไปยัง validators ซึ่งจะตรวจสอบลำดับ PoH และดำเนินธุรกรรมแบบขนาน
การออกแบบเครือข่ายยังรวมถึงโปรโตคอลการแพร่กระจายบล็อกกังหันที่แบ่งบล็อกออกเป็นแพ็คเก็ตขนาดเล็กและกระจายไปทั่วเครือข่ายในโครงสร้างแบบต้นไม้ วิธีการนี้จะช่วยลดความต้องการแบนด์วิธสำหรับ validators แต่ละรายการให้เหลือน้อยที่สุด ในขณะเดียวกันก็รับประกันการแพร่กระจายของบล็อกอย่างรวดเร็ว เมื่อรวมกับความสามารถของ PoH ในการตรวจสอบลำดับของธุรกรรม สถาปัตยกรรมนี้ช่วยให้ Solana บรรลุปริมาณงานสูงโดยไม่ต้องเสียสละการกระจายอำนาจ
Network Design
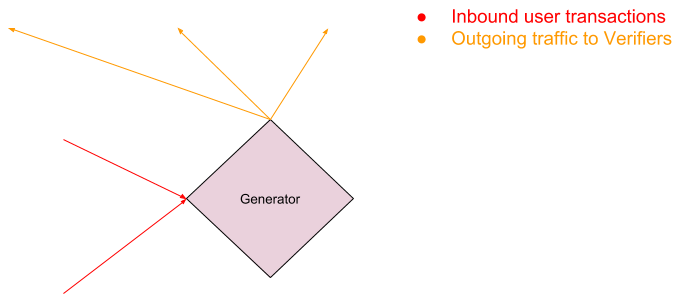
Solana的网络设计以轮换领导者系统为中心,验证者轮流产生区块。领导者负责将传入的交易排序到PoH流中,并将产生的区块发布到网络。领导者通过权益加权算法选出,轮换时间表提前已知,使网络能够优化交易转发。
Gulf Stream协议通过使客户端能够直接将交易转发给即将到来的领导者,消除了对传统内存池的需求。当客户端提交交易时,它会根据轮换时间表转发给预期的领导者。如果当前领导者无法处理该交易,则将其转发给下一个预期领导者。这种设计减少了确认延迟,并允许验证者提前执行交易,进一步优化吞吐量。
交易传播使用多层方法。客户端将交易发送给验证者,验证者将其转发给当前或即将到来的领导者。领导者将交易排序到PoH流中,创建总排序。排序完成后,领导者将PoH流和交易数据传输给验证者,验证者验证PoH序列并并行执行交易。
网络设计还包括Turbine区块传播协议,该协议将区块分解为更小的数据包,并以树形结构在网络中分发。这种方法在确保快速区块传播的同时最小化了单个验证者的带宽需求。结合PoH验证交易排序的能力,这种架构使Solana能够在不牺牲去中心化的情况下实现高吞吐量。
Proof of History
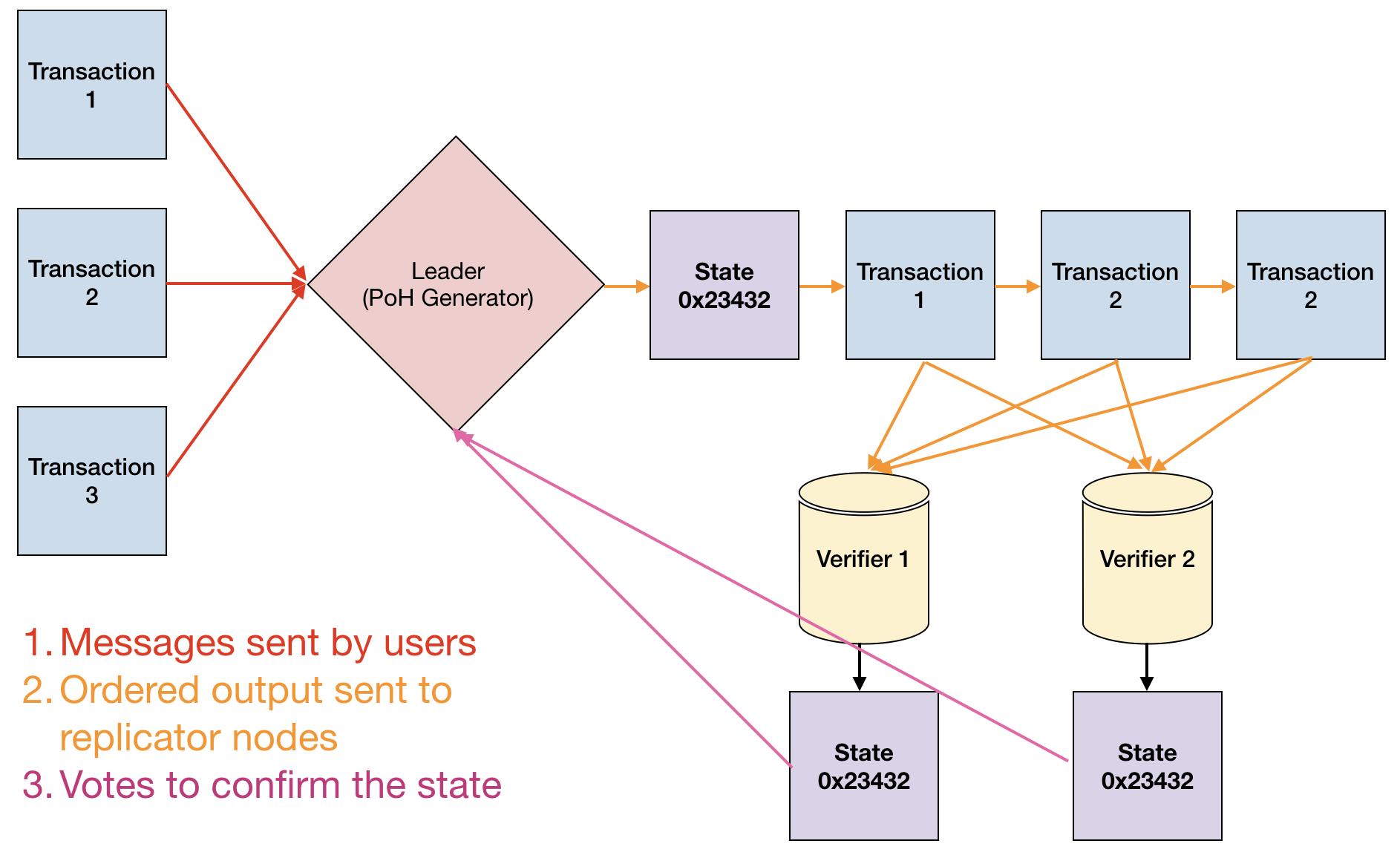
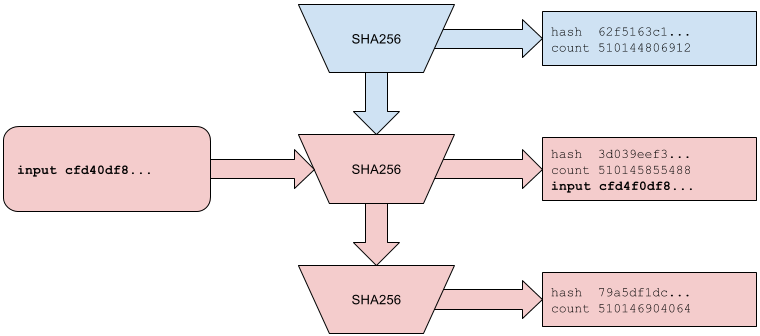
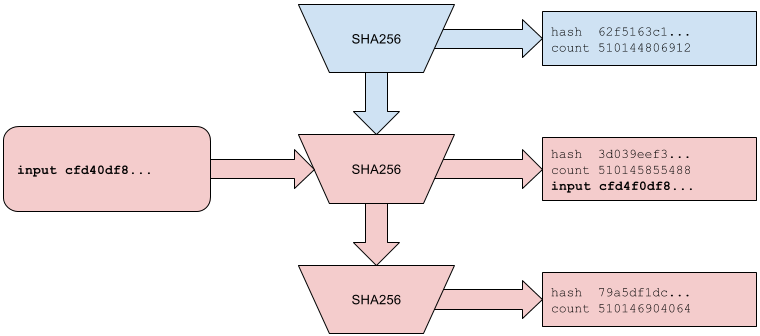
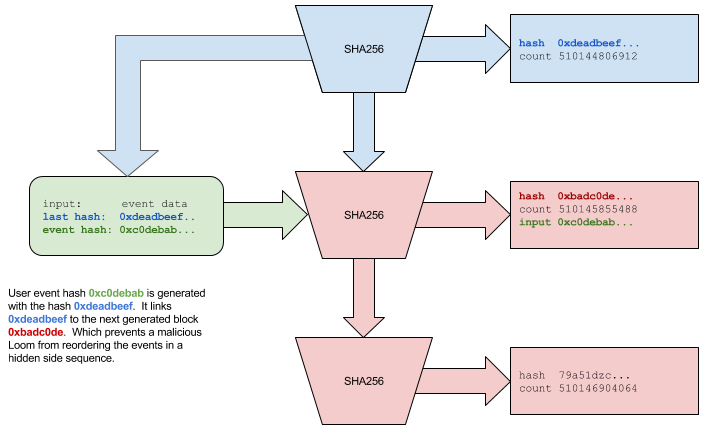
Proof of History เป็นฟังก์ชันหน่วงเวลาที่ตรวจสอบได้ซึ่งใช้งานเป็นห่วงโซ่แฮชตามลำดับโดยใช้ SHA-256 ตัวสร้าง PoH คำนวณแฮช SHA-256 อย่างต่อเนื่อง โดยใช้แต่ละเอาต์พุตเป็นอินพุตสำหรับแฮชถัดไป สิ่งนี้จะสร้างลำดับลูกโซ่โดยที่แต่ละแฮชสามารถคำนวณได้หลังจากแฮชก่อนหน้าเท่านั้น สร้างการเรียงลำดับชั่วคราวที่ตรวจสอบได้ ข้อกำหนดในการคำนวณเพื่อสร้างแต่ละแฮชบังคับให้มีการหน่วงเวลาขั้นต่ำระหว่างเหตุการณ์
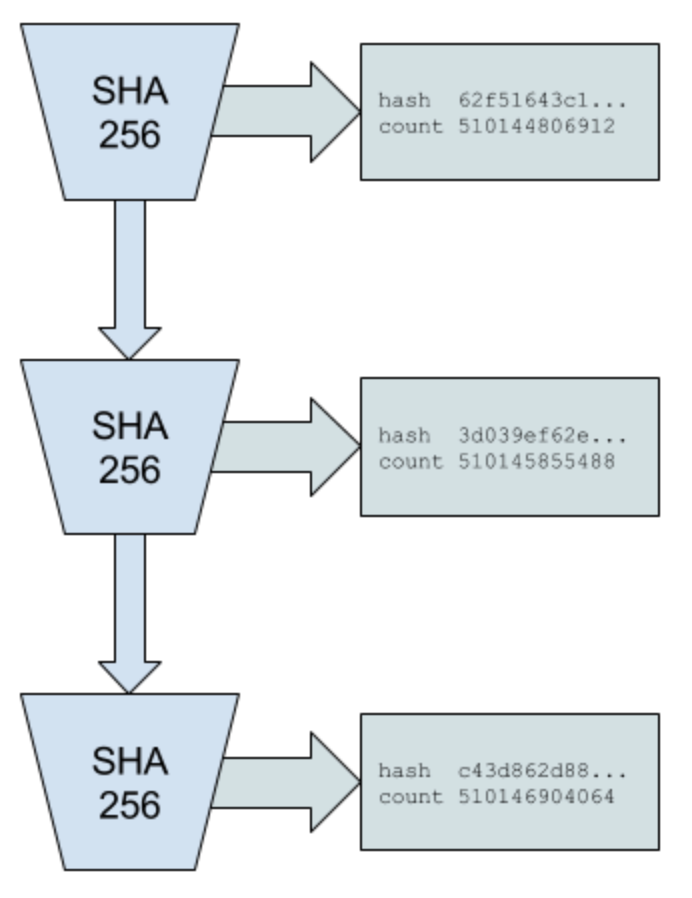
คุณสมบัติหลักของ PoH คือ มีราคาถูกในการตรวจสอบแต่มีราคาแพงในการผลิต ผู้ตรวจสอบสามารถตรวจสอบลำดับแฮชทั้งหมดแบบขนานโดยแยกออกเป็นส่วนๆ และตรวจสอบแต่ละส่วนแยกจากกัน จากนั้นตรวจสอบว่าส่วนต่างๆ เชื่อมต่อกันอย่างถูกต้อง อย่างไรก็ตาม การสร้างจะต้องเป็นไปตามลำดับ — ไม่มีวิธีใดที่จะคาดเดาผลลัพธ์ของห่วงโซ่แฮชได้โดยไม่ต้องคำนวณทุกขั้นตอนระหว่างกลางจริงๆ ความไม่สมดุลระหว่างการสร้างและการตรวจสอบนี้คือสิ่งที่ทำให้ PoH ใช้งานได้จริง
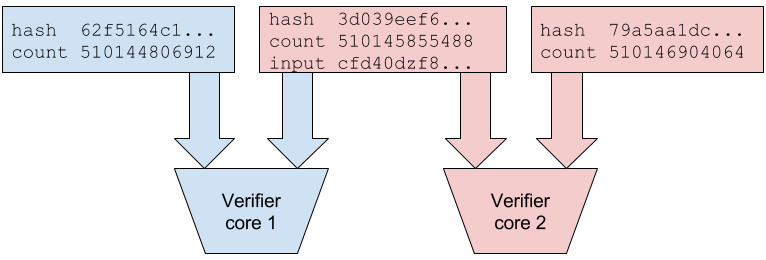
เหตุการณ์ภายนอกและข้อมูลธุรกรรมจะถูกแทรกลงในลำดับ PoH โดยการผสมเหตุการณ์เหล่านั้นลงในห่วงโซ่แฮช เมื่อธุรกรรมมาถึง แฮชของธุรกรรมจะถูกรวมเข้ากับสถานะ PoH ปัจจุบัน สร้างบันทึกที่พิสูจน์ว่ามีธุรกรรมอยู่ที่จุดนั้นในลำดับ ตัวสร้าง PoH จะบันทึกจุดตรวจสอบเป็นระยะ โดยเผยแพร่ค่าแฮชปัจจุบันพร้อมกับจำนวนแฮชที่คำนวณตั้งแต่จุดตรวจสอบครั้งล่าสุด จุดตรวจสอบเหล่านี้อนุญาตให้ validators ตรวจสอบลำดับ PoH ได้อย่างมีประสิทธิภาพโดยไม่ต้องคำนวณทุกแฮชใหม่
ลำดับ PoH ทำหน้าที่เป็นนาฬิกาเข้ารหัสสำหรับทั้งเครือข่าย เนื่องจากห่วงโซ่แฮชเป็นแบบต่อเนื่องและตรวจสอบได้ โหนดใดๆ จึงสามารถพิสูจน์ได้ว่าระยะเวลาหนึ่งผ่านไประหว่างสองเหตุการณ์ เพียงแค่แสดงแฮชที่ถูกคำนวณในช่วงเวลานั้น ซึ่งช่วยลดความจำเป็นที่โหนดจะต้องเชื่อถือการประทับเวลาภายนอกหรือประสานงานซึ่งกันและกันเพื่อสร้างลำดับชั่วคราว ซึ่งช่วยขจัดปัญหาคอขวดพื้นฐานในฉันทามติบล็อกเชนแบบดั้งเดิม
Proof of History
Proof of History是一种使用SHA-256实现的顺序哈希链形式的可验证延迟函数。PoH生成器持续计算SHA-256哈希,使用每个输出作为下一个哈希的输入。这创建了一个顺序链,其中每个哈希只能在前一个哈希计算完成后才能计算,从而建立可验证的时间排序。生成每个哈希的计算要求强制了事件之间的最小时间延迟。
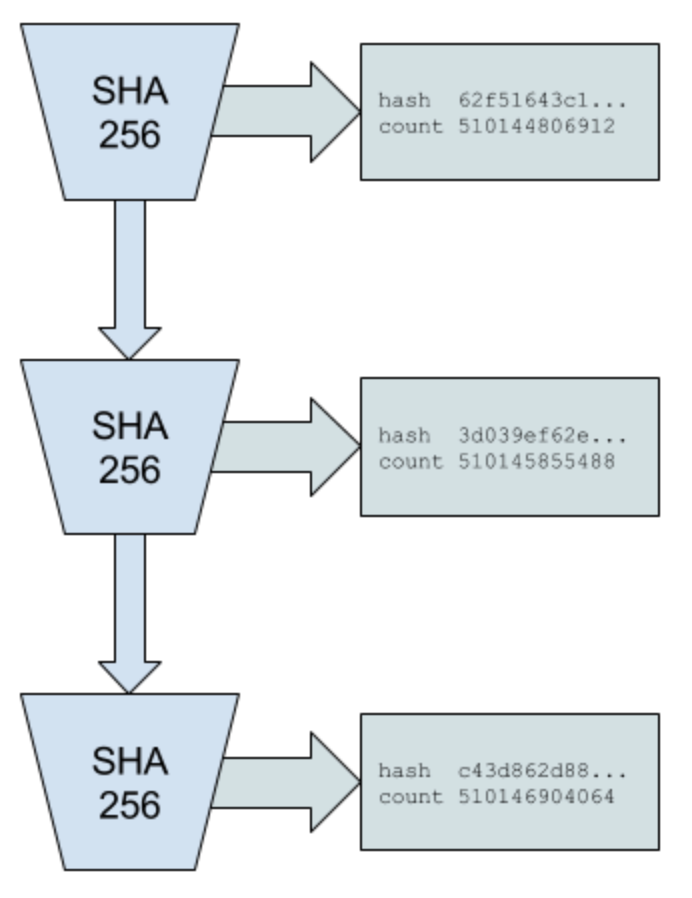
PoH的关键属性是验证成本低但生成成本高。验证者可以通过将哈希序列分成段,独立并行检查每个段,然后验证各段正确连接来检查整个哈希序列。然而,生成必须是顺序的——不实际计算每个中间步骤就无法预测哈希链的输出。生成和验证之间的这种不对称性使PoH变得实用。
外部事件和交易数据通过混合到哈希链中插入PoH序列。当交易到达时,其哈希与当前PoH状态结合,创建一条记录证明该交易在序列的该点存在。PoH生成器定期记录检查点,发布当前哈希值以及自上次检查点以来计算的哈希数量。这些检查点使验证者能够高效地验证PoH序列,而无需重新计算每个哈希。
PoH序列作为整个网络的加密时钟。因为哈希链是顺序的且可验证的,任何节点都可以通过展示在该时间间隔内计算的哈希来证明两个事件之间经过了一定的时间。这消除了节点信任外部时间戳或相互协调以建立时间排序的需要,消除了传统区块链共识中的根本瓶颈。
Proof of History Sequence
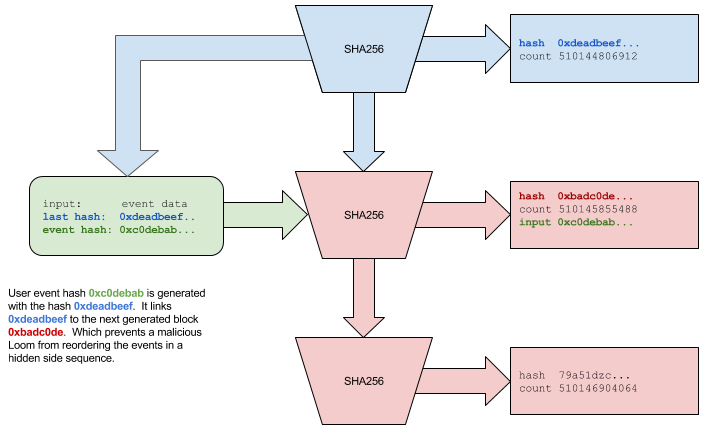
ลำดับ Proof of History คือสายโซ่ต่อเนื่องของแฮช SHA-256 โดยแต่ละแฮชขึ้นอยู่กับเอาต์พุตก่อนหน้า ลำดับเริ่มต้นด้วยค่าเริ่มต้น ซึ่งถูกแฮชเพื่อสร้างเอาต์พุตแรก เอาต์พุตนี้จะกลายเป็นอินพุตสำหรับแฮชถัดไป และกระบวนการจะทำซ้ำอย่างไม่มีกำหนด ตัวสร้างยังรักษาตัวนับที่ติดตามจำนวนแฮชทั้งหมดที่คำนวณ ซึ่งทำหน้าที่เป็น "การประทับเวลา" ของ PoH สำหรับเหตุการณ์ใน ledger
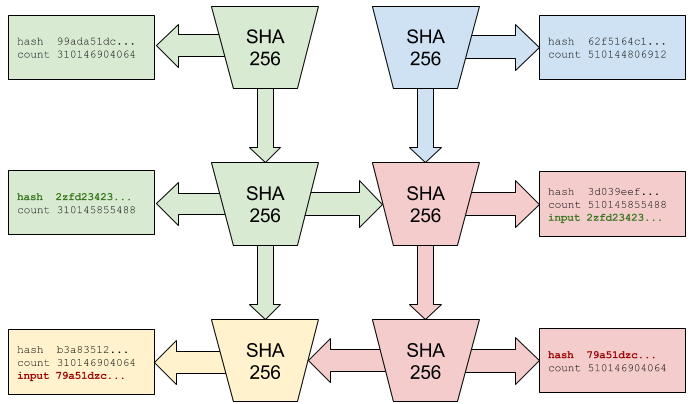
เมื่อจำเป็นต้องแทรกข้อมูลลงในลำดับ (เช่น แฮชของธุรกรรมหรือลายเซ็น validator) ข้อมูลจะรวมกับสถานะแฮชปัจจุบันโดยใช้ฟังก์ชันผสมที่กำหนดขึ้น ตัวอย่างเช่น หากสถานะแฮชปัจจุบันคือ hash_n และเราต้องการแทรกข้อมูล D เราจะคำนวณ hash_{n+1} = SHA256(hash_n || D) โดยที่ || หมายถึงการต่อข้อมูลเข้าด้วยกัน จุดแทรกจะถูกบันทึกพร้อมกับค่าตัวนับ เพื่อพิสูจน์ว่ามีข้อมูล D อยู่ที่จุดเฉพาะนั้นในลำดับ
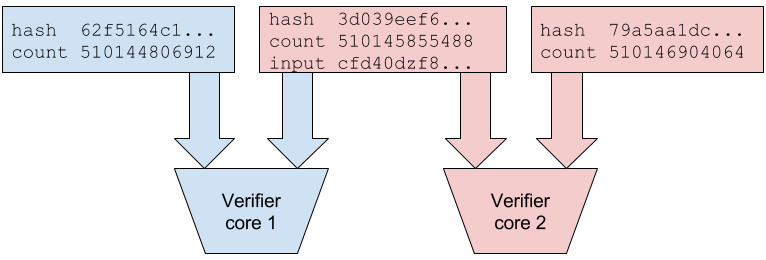
การตรวจสอบลำดับ PoH สามารถดำเนินการแบบขนานได้โดยการแยกสายโซ่ออกเป็นส่วนต่างๆ ตัวอย่างเช่น validator อาจได้รับจุดตรวจสอบ PoH ทุกๆ 10,000 แฮช ในการตรวจสอบลำดับระหว่างจุดตรวจสอบ validator สามารถแบ่งแฮช 10,000 รายการออกเป็น 100 ส่วน ส่วนละ 100 แฮช ตรวจสอบแต่ละส่วนแยกจากกันในแบบคู่ขนาน จากนั้นตรวจสอบว่าส่วนต่างๆ เชื่อมต่อกันอย่างถูกต้อง ซึ่งช่วยให้การตรวจสอบขยายขนาดในแนวนอนตามจำนวนคอร์ CPU ที่มีอยู่ได้
ลำดับยังสนับสนุนการพิสูจน์ที่มีประสิทธิภาพว่าเหตุการณ์สองเหตุการณ์เกิดขึ้นในลำดับเฉพาะ ด้วยการแทรกข้อมูลสองครั้งที่ค่าตัวนับ n และ m โดยที่ n m ใครๆ ก็สามารถตรวจสอบได้ว่าเหตุการณ์ที่ n เกิดขึ้นก่อนเหตุการณ์ที่ m โดยการตรวจสอบสายโซ่แฮชระหว่างจุดเหล่านั้น คุณสมบัตินี้ช่วยให้ Solana สร้างบันทึกประวัติที่ตรวจสอบได้ของเหตุการณ์ทั้งหมดในเครือข่าย โดยไม่ต้องกำหนดให้โหนดออนไลน์อย่างต่อเนื่องหรือเชื่อถือแหล่งเวลาภายนอก
Proof of History Sequence
Proof of History序列是一个连续的SHA-256哈希链,其中每个哈希依赖于前一个输出。序列从初始种子值开始,该值被哈希以产生第一个输出。此输出成为下一个哈希的输入,过程无限重复。生成器还维护一个计数器,跟踪计算的哈希总数,作为账本中事件的PoH"时间戳"。
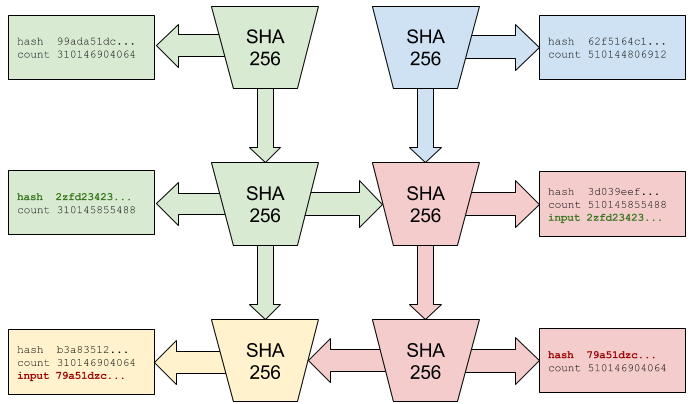
当需要将数据插入序列时(如交易哈希或验证者签名),使用确定性混合函数将其与当前哈希状态结合。例如,如果当前哈希状态是hash_n,我们想插入数据D,则计算hash_{n+1} = SHA256(hash_n || D),其中||表示连接。插入点与计数器值一起记录,证明数据D在序列的该特定点存在。
PoH序列的验证可以通过将链分成段来并行化。例如,验证者可能每10,000个哈希接收一次PoH检查点。要验证检查点之间的序列,验证者可以将10,000个哈希分成100个段,每段100个哈希,独立并行验证每个段,然后验证各段正确连接。这允许验证随可用CPU核心数水平扩展。
序列还支持高效证明两个事件以特定顺序发生。给定在计数器值n和m(其中n m)处的两个数据插入,任何人都可以通过检查这些点之间的哈希链来验证n处的事件发生在m处的事件之前。此属性使Solana能够创建网络中所有事件的可验证历史记录,而无需节点持续在线或信任外部时间源。
Timestamp
Proof of History ทำหน้าที่เป็นนาฬิกากระจายอำนาจที่กำหนดเวลาให้กับเหตุการณ์โดยไม่ต้องอาศัยเวลาของนาฬิกาแขวน แฮช PoH แต่ละรายการแสดงถึง "เครื่องหมายถูก" ที่ไม่ต่อเนื่องของนาฬิกาเข้ารหัส และค่าตัวนับจะทำหน้าที่เป็นการประทับเวลา เนื่องจากสายแฮชเป็นแบบต่อเนื่องและตรวจสอบได้ การประทับเวลาเหล่านี้จึงไม่น่าเชื่อถือ ผู้สังเกตการณ์ทุกคนสามารถตรวจสอบได้ว่าการประทับเวลานั้นถูกต้องโดยการตรวจสอบสายแฮช
ใน Solana แต่ละ validator สามารถสร้างลำดับ PoH ของตัวเองได้เมื่อทำหน้าที่เป็นผู้นำ เมื่อ validators หมุนเวียนผู้นำ พวกเขาจะซิงโครไนซ์ลำดับ PoH ของตนโดยใช้จุดตรวจสอบที่ยืนยันล่าสุดจากผู้นำคนก่อน สิ่งนี้ทำให้มั่นใจถึงความต่อเนื่องของบันทึกชั่วคราว แม้ว่า validators ที่แตกต่างกันจะผลัดกันสร้างบล็อกก็ตาม เครือข่ายสร้างไทม์ไลน์ตามรูปแบบบัญญัติโดยบรรลุข้อตกลงร่วมกันว่าลำดับ PoH ใดที่จะยอมรับเป็นส่วนหนึ่งของ ledger อย่างเป็นทางการ
ระบบจะจัดการกับการเลื่อนของสัญญาณนาฬิกาและความแปรปรวนในประสิทธิภาพของฮาร์ดแวร์ผ่านการผสมผสานระหว่างการหมุนเวียนผู้นำและความเห็นพ้องต้องกัน หากผู้นำที่เป็นอันตรายหรือผิดพลาดพยายามสร้างการประทับเวลา PoH ในอัตราที่ไม่ถูกต้อง (เร็วเกินไปหรือช้าเกินไป) validators สามารถตรวจจับสิ่งนี้ได้โดยการเปรียบเทียบอัตราเห็บ PoH กับตัวสร้าง PoH ในพื้นที่ของตนเอง การเบี่ยงเบนอย่างมีนัยสำคัญจากอัตราที่คาดไว้บ่งบอกถึงปัญหา และ validators สามารถปฏิเสธบล็อกจากผู้นำที่มีลำดับ PoH แตกต่างจากค่ามัธยฐานของเครือข่ายมากเกินไป
กลไกการประทับเวลานี้แก้ปัญหาพื้นฐานประการหนึ่งในระบบแบบกระจาย: การสร้างแนวคิดทั่วไปเกี่ยวกับเวลาโดยไม่มีหน่วยงานกลางที่เชื่อถือได้ ด้วยการใช้ PoH เป็นนาฬิกากระจายอำนาจ Solana ช่วยให้ validators ประมวลผลธุรกรรมแบบขนานในขณะที่ยังคงรักษาลำดับที่สอดคล้องกันทั่วโลก การประทับเวลายังจัดเตรียมรากฐานสำหรับฟีเจอร์ตามเวลา เช่น การหมดอายุของธุรกรรม การดำเนินการตามกำหนดการ และการวัดประสิทธิภาพ
Timestamp
Proof of History作为去中心化时钟运行,在不依赖墙钟时间的情况下为事件分配时间戳。每个PoH哈希代表加密时钟的一个离散"滴答",计数器值作为时间戳。因为哈希链是顺序的且可验证的,这些时间戳是无需信任的——任何观察者都可以通过检查哈希链来验证时间戳的合法性。
在Solana中,每个验证者在充当领导者时可以生成自己的PoH序列。当验证者轮换领导权时,他们使用前一个领导者的最后确认检查点来同步其PoH序列。这确保了即使不同的验证者轮流产生区块,时间记录的连续性也得到保持。网络通过就接受哪些PoH序列作为官方账本的一部分达成共识来建立规范时间线。
系统通过领导者轮换和共识的组合来处理时钟漂移和硬件性能差异。如果恶意或故障的领导者试图以不正确的速率(过快或过慢)生成PoH时间戳,验证者可以通过将PoH滴答率与自己的本地PoH生成器进行比较来检测这一点。与预期速率的显著偏差表明存在问题,验证者可以拒绝PoH序列偏离网络中位数太远的领导者的区块。
这种时间戳机制解决了分布式系统中的一个基本问题:在没有受信任的中央机构的情况下建立共同的时间概念。通过使用PoH作为去中心化时钟,Solana使验证者能够在保持全局一致排序的同时并行处理交易。时间戳还为基于时间的功能提供了基础,如交易过期、定时操作和性能测量。
Proof of Stake Consensus
กลไกฉันทามติของ Solana ที่เรียกว่า Tower BFT เป็นอัลกอริธึม Proof of Stake ที่ออกแบบมาโดยเฉพาะเพื่อใช้ประโยชน์จากคุณสมบัติชั่วคราวของ Proof of History ผู้ตรวจสอบจะเดิมพันโทเค็น SOL เพื่อเข้าร่วมฉันทามติและรับรางวัลจากการตรวจสอบความถูกต้องของบล็อก ระบบการลงคะแนนแบบถ่วงน้ำหนักหุ้นทำให้มั่นใจได้ว่า validators ที่มีผลประโยชน์ทางเศรษฐกิจมากกว่าในเครือข่ายจะมีอิทธิพลเหนือการตัดสินใจที่เป็นเอกฉันท์ตามสัดส่วนมากกว่า
นวัตกรรมหลักใน Tower BFT คือการใช้ระยะเวลาล็อคที่เพิ่มขึ้นแบบทวีคูณเมื่อมีการโหวตแต่ละครั้งติดต่อกัน เมื่อ validator โหวตให้กับแฮช PoH พวกเขายอมรับการแยกของ ledger สำหรับขีด PoH จำนวนหนึ่ง หากพวกเขาโหวตบล็อกถัดไปในทางแยกนั้น ระยะเวลาการล็อคจะเพิ่มเป็นสองเท่า สิ่งนี้สร้างแรงจูงใจทางเศรษฐกิจที่แข็งแกร่งสำหรับ validators ที่จะลงคะแนนเสียงบนส้อมเดิมต่อไป เนื่องจากการสลับส้อมจะต้องรอให้การล็อคก่อนหน้านี้หมดอายุ
โดยเฉพาะอย่างยิ่ง หาก validator โหวตบนบล็อกที่ประทับเวลา PoH t พวกเขาจะไม่สามารถลงคะแนนใน fork ที่ขัดแย้งกันจนกว่าเครื่องหมาย 2^n จะผ่านไป โดยที่ n คือจำนวนการโหวตติดต่อกันที่พวกเขาได้ทำบน fork ปัจจุบัน กลไกการล็อคแบบเอกซ์โปเนนเชียลนี้ทำให้ระบบปลอดภัยจากการโจมตีระยะไกล ในขณะเดียวกันก็ทำให้สามารถสรุปผลได้อย่างรวดเร็ว เมื่อเสียงข้างมากของเดิมพันได้ลงคะแนนในบล็อกที่มีความลึกเพียงพอ บล็อกนั้นก็จะได้รับการสรุปผลอย่างมีประสิทธิภาพ
เงื่อนไขที่รุนแรงบังคับใช้พฤติกรรมที่ซื่อสัตย์ หาก validator โหวตให้กับส้อมสองอันที่ขัดแย้งกันในช่วงเวลาที่ควรถูกล็อค โทเค็นเหล่านั้นจะถูกเฉือน — โทเค็นที่เดิมพันจะถูกทำลายบางส่วนและจะถูกลบออกจากชุด validator ซึ่งทำให้ไม่สมเหตุสมผลในเชิงเศรษฐกิจที่จะพยายามคลุมเครือหรือพฤติกรรม Byzantine อื่นๆ การผสมผสานระหว่างการประทับเวลาที่ตรวจสอบได้ของ PoH และการล็อกเอาท์แบบเอ็กซ์โปเนนเชียลของ Tower BFT ทำให้เกิดกลไกที่เป็นเอกฉันท์ที่ทั้งรวดเร็วและปลอดภัย โดยบรรลุผลขั้นสุดท้ายในไม่กี่วินาที ขณะเดียวกันก็รักษาการรับประกันความปลอดภัยของระบบ BFT แบบดั้งเดิม
Proof of Stake Consensus
Solana的共识机制称为Tower BFT,是一种专门设计用于利用Proof of History时间属性的Proof of Stake算法。验证者质押SOL代币参与共识,并因正确验证区块而获得奖励。权益加权投票系统确保在网络中拥有更多经济利益的验证者在共识决策中拥有相应更大的影响力。
Tower BFT的核心创新是使用随每次连续投票呈指数增长的锁定期。当验证者对PoH哈希投票时,他们承诺在一定数量的PoH滴答内留在账本的该分叉上。如果他们对该分叉的下一个区块投票,锁定期翻倍。这为验证者继续在同一分叉上投票创造了强烈的经济激励,因为切换分叉需要等待早期锁定期到期。
具体来说,如果验证者在PoH时间戳t处对区块投票,则在2^n个滴答过去之前不能对冲突的分叉投票,其中n是他们在当前分叉上进行的连续投票次数。这种指数锁定机制使系统在允许快速最终性的同时抵御远程攻击。一旦绝对多数的权益在足够深度上对区块投票,该区块就被有效地最终确定。
惩罚条件强制执行诚实行为。如果验证者在应该被锁定的期间对两个冲突的分叉投票,他们将被惩罚——质押的代币被部分销毁,并从验证者集合中移除。这使得尝试模棱两可或其他拜占庭行为在经济上不合理。PoH的可验证时间戳与Tower BFT的指数锁定的结合创造了一个既快速又安全的共识机制,在保持传统BFT系统安全保障的同时,在几秒内实现最终性。
Streaming Proof of Replication
Proof of Replication (PoRep) เป็นกลไกที่ช่วยให้ validators พิสูจน์ได้ว่ากำลังจัดเก็บข้อมูล ledger โดยไม่ต้องเปิดเผยข้อมูลหรือต้องใช้การคำนวณอย่างเข้มข้น Solana ใช้ PoRep เวอร์ชันสตรีมมิ่ง โดยที่ validators แสดงให้เห็นอย่างต่อเนื่องว่ากำลังจำลองสถานะบล็อกเชน นี่เป็นสิ่งสำคัญสำหรับการรักษาความปลอดภัยเครือข่าย เนื่องจากช่วยให้แน่ใจว่าข้อมูล ledger มีการกระจายอย่างเหมาะสมทั่วทั้ง validators และไม่กระจุกตัวอยู่ในตำแหน่งบางแห่ง
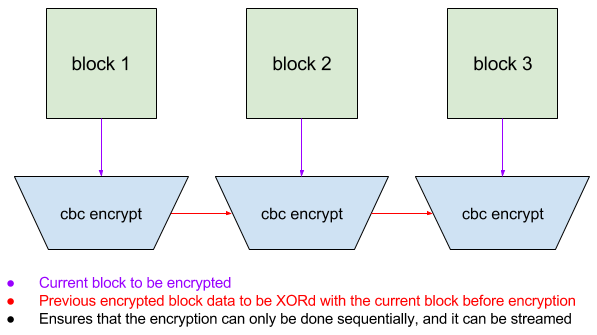
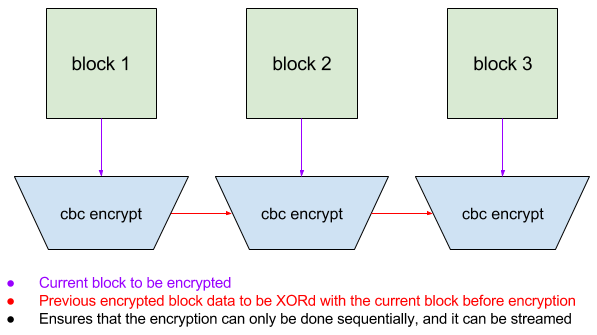
กลไก PoRep ทำงานโดยให้ validators เข้ารหัสเซ็กเมนต์ของ ledger โดยใช้การเข้ารหัสโหมด CBC (Cipher Block Chaining) พร้อมด้วยคีย์เฉพาะ validator ที่ได้มาจากข้อมูลระบุตัวตน กระบวนการเข้ารหัสนั้นทำให้แต่ละบล็อกที่เข้ารหัสนั้นขึ้นอยู่กับบล็อกก่อนหน้า สร้างสายโซ่ที่ไม่ซ้ำกันสำหรับแต่ละ validator การทำเช่นนี้จะป้องกันไม่ให้ validators คัดลอกข้อมูลที่เข้ารหัสจากกัน โดย validator แต่ละตัวจะต้องจัดเก็บและประมวลผลข้อมูล ledger ดั้งเดิมเพื่อสร้างเวอร์ชันที่เข้ารหัสที่ไม่ซ้ำกัน
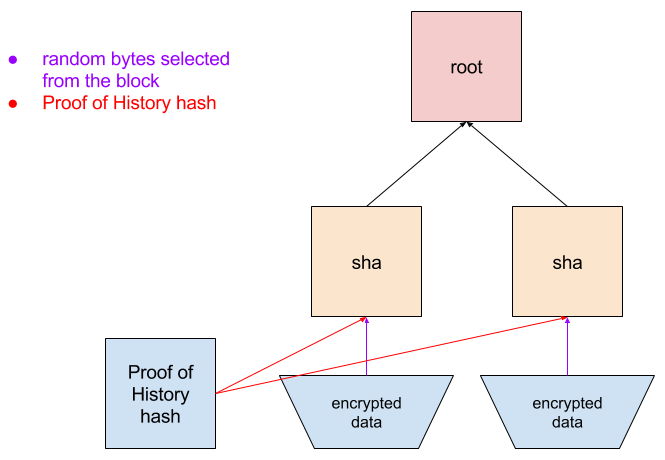
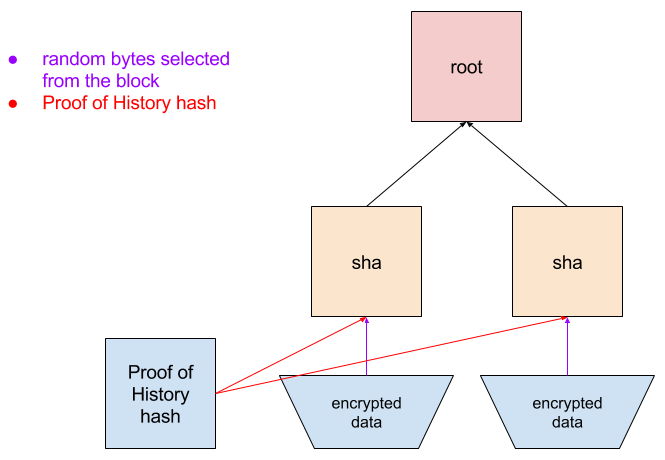
เครือข่ายจะออกคำถามท้าทาย validators เป็นระยะ โดยขอให้จัดเตรียมบล็อกที่เข้ารหัสเฉพาะ เนื่องจากการเข้ารหัสเป็นแบบลูกโซ่ validator จะต้องจัดเก็บบล็อกก่อนหน้าทั้งหมดเพื่อสร้างการตอบสนองที่ถูกต้อง validator ส่งบล็อกที่เข้ารหัสพร้อมกับหลักฐาน Merkle ที่แสดงตำแหน่งใน ledger ที่เข้ารหัส เครือข่ายสามารถตรวจสอบหลักฐานนี้ได้อย่างรวดเร็วโดยไม่จำเป็นต้องถอดรหัสหรือเข้ารหัสข้อมูลอีกครั้ง
วิธีการสตรีมไปยัง PoRep นี้มีค่าใช้จ่ายต่ำเมื่อเทียบกับระบบพิสูจน์การจัดเก็บแบบดั้งเดิม เครื่องมือตรวจสอบสามารถเข้ารหัสข้อมูลเมื่อมาถึงและตอบสนองต่อความท้าทายโดยมีเวลาแฝงน้อยที่สุด ระบบยังเปิดใช้งานการกู้คืนในกรณีที่ข้อมูลสูญหาย หาก validator สูญเสียส่วนหนึ่งของ ledger ก็สามารถดาวน์โหลดใหม่จาก validators อื่นและเข้ารหัสอีกครั้งได้ การผสมผสานระหว่าง PoRep กับการประทับเวลา PoH จะสร้างระบบความรับผิดชอบที่สมบูรณ์ ซึ่งเครือข่ายสามารถตรวจสอบทั้งเมื่อมีการสร้างข้อมูลและจัดเก็บอย่างเหมาะสมผ่านเครือข่าย validator
Streaming Proof of Replication
Proof of Replication(PoRep)是一种允许验证者证明他们正在存储账本数据而无需揭示数据本身或需要密集计算的机制。Solana实现了PoRep的流式版本,验证者持续证明他们正在复制区块链状态。这对网络安全至关重要,因为它确保账本数据在验证者之间适当分布,而不是集中在少数位置。
PoRep机制通过让验证者使用从其身份派生的验证者特定密钥,以CBC(Cipher Block Chaining)模式加密账本段来工作。加密过程使每个加密块依赖于前一个块,创建一个对每个验证者唯一的链。这防止验证者简单地从彼此复制加密数据——每个验证者必须存储和处理原始账本数据才能生成其唯一的加密版本。
网络定期向验证者发出挑战,要求他们提供特定的加密块。因为加密是链式的,验证者必须存储所有前面的块才能生成正确的响应。验证者提交其加密块以及显示其在加密账本中位置的Merkle证明。网络可以快速验证此证明,而无需解密或重新加密数据。
这种流式PoRep方法与传统的存储证明系统相比开销较低。验证者可以在数据到达时进行加密,并以最小延迟响应挑战。系统还支持数据丢失时的恢复——如果验证者丢失了部分账本,可以从其他验证者重新下载并重新加密。PoRep与PoH时间戳的结合创建了一个完整的问责系统,网络可以验证数据的创建时间以及它在验证者网络中被正确存储。
System Architecture
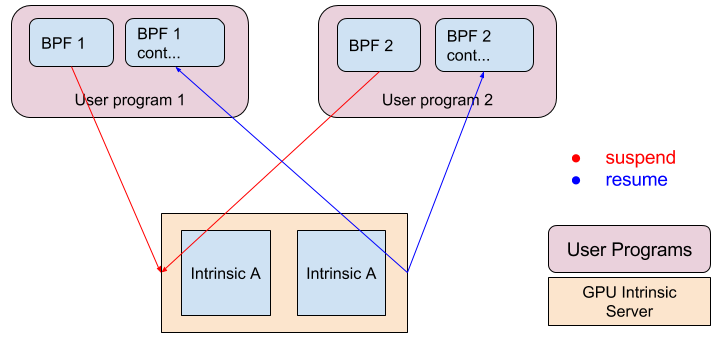
สถาปัตยกรรมระบบของ Solana ได้รับการออกแบบให้เป็นไปป์ไลน์ที่ขั้นตอนต่างๆ ของการประมวลผลธุรกรรมเกิดขึ้นพร้อมกัน หน่วยประมวลผลธุรกรรม (TPU) เป็นองค์ประกอบหลักที่รับผิดชอบในการจัดการธุรกรรมที่เข้ามา TPU ประกอบด้วยหลายขั้นตอน: ดึงข้อมูล (รวบรวมธุรกรรม) การตรวจสอบลายเซ็น การธนาคาร (การดำเนินการธุรกรรม) และการเขียน (ยินยอมที่จะจัดเก็บข้อมูล) แต่ละขั้นตอนดำเนินการแบบขนานในธุรกรรมที่แตกต่างกัน คล้ายกับการวางท่อ CPU
การตรวจสอบลายเซ็นจะถูกเร่งให้เร็วขึ้นโดยใช้ GPU ซึ่งมีประสิทธิภาพสูงในการดำเนินการเข้ารหัสแบบเส้นโค้งวงรี ซึ่งจำเป็นในการตรวจสอบลายเซ็นของธุรกรรม ด้วยการถ่ายงานที่ต้องใช้การคำนวณสูงนี้ไปยัง GPU ทำให้ Solana สามารถตรวจสอบลายเซ็นในอัตราที่เกิน 900,000 ต่อวินาทีบนฮาร์ดแวร์สินค้าโภคภัณฑ์ การตรวจสอบลายเซ็นแบบขนานนี้ช่วยป้องกันการตรวจสอบการเข้ารหัสไม่ให้กลายเป็นคอขวด แม้จะมีอัตราการทำธุรกรรมที่สูงมากก็ตาม
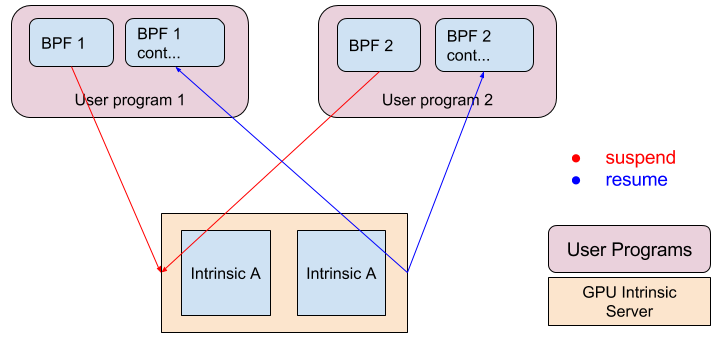
รันไทม์ Sealevel คือกลไกการดำเนินการสัญญาอัจฉริยะแบบขนานของ Solana ต่างจากบล็อกเชนแบบดั้งเดิมที่ดำเนินธุรกรรมตามลำดับ Sealevel วิเคราะห์ธุรกรรมเพื่อระบุบัญชีที่พวกเขาเข้าถึง และดำเนินธุรกรรมที่ไม่ขัดแย้งในแบบคู่ขนานบนแกน CPU หลายตัว ธุรกรรมที่เข้าถึงบัญชีเดียวกันจะได้รับการดำเนินการตามลำดับเพื่อรักษาความสอดคล้อง แต่ธุรกรรมที่เข้าถึงบัญชีที่แตกต่างกันสามารถดำเนินการพร้อมกันได้ ความขนานนี้เป็นไปได้เนื่องจาก PoH สร้างการเรียงลำดับทั่วโลก — validators สามารถทำธุรกรรมในลำดับใดก็ได้ ตราบใดที่ธุรกรรมเหล่านั้นใช้กับสถานะในลำดับที่ระบุ PoH
สถาปัตยกรรมยังรวมถึงส่วนประกอบที่ได้รับการปรับปรุงสำหรับการแพร่กระจายและการจัดเก็บข้อมูลแบบบล็อก โปรโตคอลการแพร่กระจายบล็อกกังหันใช้การเข้ารหัสการลบข้อมูลเพื่อแบ่งบล็อกออกเป็นแพ็กเก็ตขนาดเล็กที่กระจายไปทั่วเครือข่ายในโครงสร้างแบบต้นไม้ ช่วยลดความต้องการแบนด์วิดท์ให้เหลือน้อยที่สุด เครือข่าย Archivers มอบพื้นที่จัดเก็บข้อมูลแบบกระจายอำนาจสำหรับข้อมูลประวัติ ledger โดยใช้ PoRep เพื่อรับรองความพร้อมใช้งานของข้อมูล ส่วนประกอบเหล่านี้ร่วมกันสร้างระบบที่สามารถประมวลผลธุรกรรมนับแสนรายการต่อวินาที ในขณะที่ยังคงรักษาคุณสมบัติการกระจายอำนาจและความปลอดภัยของบล็อกเชน
System Architecture
Solana的系统架构被设计为流水线,交易处理的不同阶段并行进行。Transaction Processing Unit(TPU)是负责处理传入交易的核心组件。TPU由几个阶段组成:fetch(收集交易)、签名验证、banking(交易执行)和write(提交到存储)。每个阶段对不同的交易并行操作,类似于CPU流水线。
签名验证使用GPU加速,GPU在验证交易签名所需的椭圆曲线加密操作方面效率很高。通过将这个计算密集型任务卸载到GPU,Solana可以在商用硬件上以每秒超过900,000次的速率验证签名。这种并行签名验证防止了即使在非常高的交易速率下加密验证成为瓶颈。
Sealevel运行时是Solana的并行智能合约执行引擎。与顺序执行交易的传统区块链不同,Sealevel分析交易以识别它们访问哪些账户,并在多个CPU核心上并行执行不冲突的交易。访问相同账户的交易为保持一致性而顺序执行,但访问不同账户的交易可以同时运行。这种并行性之所以可能,是因为PoH建立了全局排序——验证者可以按任何顺序执行交易,只要按PoH指定的序列将其应用于状态。
架构还包括用于区块传播和存储的优化组件。Turbine区块传播协议使用纠删码将区块分解为更小的数据包,并以树形结构在网络中分发,最小化带宽需求。Archivers网络使用PoRep确保数据可用性,为历史账本数据提供去中心化存储。这些组件共同创建了一个系统,能够在保持区块链去中心化和安全属性的同时每秒处理数十万笔交易。
Performance
สถาปัตยกรรมของ Solana ได้รับการออกแบบมาเพื่อให้บรรลุระดับประสิทธิภาพที่ปรับขนาดได้ด้วยการปรับปรุงฮาร์ดแวร์ตามกฎของมัวร์ สำหรับการเชื่อมต่อเครือข่ายมาตรฐาน 1 กิกะบิต ปริมาณงานสูงสุดตามทฤษฎีจะอยู่ที่ประมาณ 710,000 ธุรกรรมต่อวินาที โดยถือว่า 176 ไบต์ต่อธุรกรรม (รวมลายเซ็นและข้อมูลเมตา) การคำนวณนี้อิงตามแบนด์วิดท์เครือข่ายที่เป็นคอขวดหลัก โดยที่คอขวดในการคำนวณจะถูกลบออกผ่านการทำขนาน
การตรวจสอบลายเซ็นซึ่งมักเป็นปัจจัยจำกัดในประสิทธิภาพของบล็อกเชน จะถูกเร่งให้เร็วขึ้นโดยใช้ GPU แบบขนาน GPU ตัวเดียวสามารถตรวจสอบลายเซ็น ed25519 ได้มากกว่า 900,000 รายการต่อวินาที ซึ่งเกินขีดจำกัดปริมาณงานของเครือข่าย ซึ่งหมายความว่าการตรวจสอบลายเซ็นไม่ได้จำกัดประสิทธิภาพของระบบ — คอขวดจะเปลี่ยนไปที่แบนด์วิดท์เครือข่ายและการดำเนินการธุรกรรม สำหรับธุรกรรมง่ายๆ ที่โอนเฉพาะมูลค่าโดยไม่มีตรรกะของสัญญาอัจฉริยะที่ซับซ้อน ขั้นตอนการธนาคารสามารถประมวลผลธุรกรรมในอัตราที่ตรงกับอัตราอินพุตของเครือข่าย
ตัวสร้าง PoH ทำงานบนแกน CPU เฉพาะ ซึ่งสร้างแฮชประมาณ 4,000 ต่อมิลลิวินาทีบนโปรเซสเซอร์ 4GHz ในอัตรานี้ ลำดับ PoH จะให้การประทับเวลาที่มีความละเอียด 0.25 ไมโครวินาที ซึ่งเพียงพอสำหรับการสั่งซื้อธุรกรรมหลายล้านรายการต่อวินาที ลักษณะตามลำดับของการสร้าง PoH หมายความว่าส่วนประกอบนี้ไม่สามารถขนานกันได้ แต่ปริมาณงานสูงพอที่จะไม่จำกัดประสิทธิภาพโดยรวมของระบบ
เมื่อฮาร์ดแวร์ได้รับการปรับปรุง ปริมาณงานของ Solana ก็จะปรับขนาดตามไปด้วย เครือข่ายที่เร็วขึ้น GPU ที่ทรงพลังยิ่งขึ้น และ CPU ที่ได้รับการปรับปรุง ล้วนส่งผลให้อัตราการทำธุรกรรมสูงขึ้น ระบบได้รับการออกแบบมาเพื่อใช้ประโยชน์จากการปรับปรุงเหล่านี้โดยไม่ต้องเปลี่ยนโปรโตคอล วิธีการขยายขนาดนี้แตกต่างกับบล็อกเชนที่ถูกจำกัดโดยพื้นฐานโดยกลไกฉันทามติตามลำดับ ซึ่งช่วยให้ Solana บรรลุระดับประสิทธิภาพที่ก่อนหน้านี้คิดว่าเป็นไปไม่ได้ในระบบกระจายอำนาจ ในขณะที่ยังคงรักษาความปลอดภัยและการรับประกันการกระจายอำนาจ
Performance
Solana的架构旨在实现随硬件改进而扩展的性能水平,遵循摩尔定律。在标准1千兆网络连接上,理论最大吞吐量约为每秒710,000笔交易,假设每笔交易176字节(包括签名和元数据)。此计算基于网络带宽作为主要瓶颈,计算瓶颈已通过并行化消除。
签名验证通常是区块链性能的限制因素,通过GPU并行化加速。单个GPU每秒可以验证超过900,000个ed25519签名,超过网络吞吐量限制。这意味着签名验证不会限制系统性能——瓶颈转移到网络带宽和交易执行。对于只转移价值而不涉及复杂智能合约逻辑的简单交易,banking阶段可以以匹配网络输入速率的速率处理交易。
PoH生成器在专用CPU核心上运行,在4GHz处理器上每毫秒产生约4,000个哈希。在此速率下,PoH序列提供0.25微秒粒度的时间戳,足以每秒排序数百万笔交易。PoH生成的顺序性质意味着此组件不能并行化,但吞吐量足够高,不会限制整体系统性能。
随着硬件改进,Solana的吞吐量相应扩展。更快的网络、更强大的GPU和改进的CPU都有助于更高的交易速率。系统被设计为无需协议更改即可利用这些改进。这种可扩展性方法与受顺序共识机制根本限制的区块链形成对比,使Solana能够在保持安全性和去中心化保障的同时,实现之前在去中心化系统中被认为不可能的性能水平。
Conclusion
Proof of History แสดงถึงความก้าวหน้าขั้นพื้นฐานในสถาปัตยกรรมบล็อกเชนโดยการแก้ปัญหาเรื่องเวลาที่จำกัดความสามารถในการปรับขนาดของ ledgers แบบกระจาย ด้วยการสร้างนาฬิกาเข้ารหัสลับที่ตรวจสอบได้ PoH ช่วยให้ validators สร้างการเรียงลำดับเหตุการณ์ชั่วคราวโดยไม่มีค่าใช้จ่ายด้านการสื่อสารที่ครอบคลุมซึ่งกำหนดโดยกลไกฉันทามติแบบดั้งเดิม นวัตกรรมนี้ช่วยขจัดปัญหาคอขวดที่สำคัญและช่วยให้การประมวลผลธุรกรรมสามารถขนานกันทั่วทั้งเครือข่ายได้
การบูรณาการ PoH เข้ากับส่วนประกอบของระบบที่ได้รับการปรับปรุง - การตรวจสอบลายเซ็นที่เร่งด้วย GPU การดำเนินการธุรกรรมแบบขนานผ่าน Sealevel และโปรโตคอลการแพร่กระจายบล็อกที่มีประสิทธิภาพ - สร้างบล็อกเชนที่สามารถประมวลผลธุรกรรมนับแสนรายการต่อวินาทีบนฮาร์ดแวร์สินค้าโภคภัณฑ์ ที่สำคัญกว่านั้น สถาปัตยกรรมได้รับการออกแบบให้ปรับขนาดได้ด้วยการปรับปรุงฮาร์ดแวร์ ซึ่งหมายความว่าประสิทธิภาพจะเพิ่มขึ้นอย่างต่อเนื่องเมื่อโปรเซสเซอร์เร็วขึ้นและเครือข่ายมีความสามารถมากขึ้น
การออกแบบของ Solana แสดงให้เห็นว่าประสิทธิภาพสูงและการกระจายอำนาจไม่ได้แยกจากกัน ด้วยการใช้ประโยชน์จาก PoH เป็นรากฐานสำหรับความเห็นพ้องต้องกันและการประสานงานของระบบ เครือข่ายบรรลุระดับการรับส่งข้อมูลที่เทียบได้กับฐานข้อมูลแบบรวมศูนย์ ในขณะที่ยังคงรักษาคุณสมบัติด้านความปลอดภัยและการต้านทานการเซ็นเซอร์ของบล็อกเชนแบบกระจายอำนาจ กลไกฉันทามติ Tower BFT แบบถ่วงน้ำหนักเดิมพันช่วยให้แน่ใจว่าเครือข่ายยังคงปลอดภัยจากนักแสดง Byzantine ในขณะที่บรรลุผลขั้นสุดท้ายอย่างรวดเร็ว
การนำสถาปัตยกรรมนี้ไปใช้ถือเป็นแนวทางปฏิบัติสำหรับเทคโนโลยีบล็อกเชนเพื่อขยายไปสู่การนำไปใช้ทั่วโลก แอปพลิเคชันที่ต้องการทรูพุตธุรกรรมสูง เช่น การแลกเปลี่ยนแบบกระจายอำนาจ แพลตฟอร์มเกม และระบบทางการเงิน สามารถสร้างบนโครงสร้างพื้นฐานแบบกระจายอำนาจอย่างแท้จริง โดยไม่กระทบต่อประสิทธิภาพการทำงาน Proof of History เปิดประตูสู่แอปพลิเคชันบล็อกเชนรุ่นใหม่ที่ก่อนหน้านี้ไม่สามารถทำได้เนื่องจากข้อจำกัดด้านความสามารถในการขยาย
Conclusion
Proof of History通过解决限制分布式账本可扩展性的时间问题,代表了区块链架构的根本性突破。通过创建可验证的加密时钟,PoH使验证者能够在不需要传统共识机制所需的大量通信开销的情况下建立事件的时间排序。这项创新消除了关键瓶颈,允许交易处理在网络中并行化。
PoH与优化的系统组件的集成——GPU加速签名验证、通过Sealevel的并行交易执行和高效的区块传播协议——创建了一个能够在商用硬件上每秒处理数十万笔交易的区块链。更重要的是,该架构被设计为随硬件改进而扩展,这意味着随着处理器变得更快、网络变得更强大,性能将持续提高。
Solana的设计证明了高性能和去中心化并非相互排斥。通过利用PoH作为共识和系统协调的基础,网络在保持去中心化区块链的安全性和抗审查属性的同时,实现了与中心化数据库相当的吞吐量水平。权益加权Tower BFT共识机制确保网络在实现快速最终性的同时抵御拜占庭行为者。
该架构的实现为区块链技术扩展到全球采用提供了实际路径。需要高交易吞吐量的应用——如去中心化交易所、游戏平台和金融系统——现在可以在不牺牲性能的情况下构建在真正去中心化的基础设施上。Proof of History为之前因可扩展性限制而不可行的新一代区块链应用打开了大门。




