
ソラナ:高性能ブロックチェーンのための新しいアーキテクチャ
Abstract
यह पेपर एक उच्च-प्रदर्शन ब्लॉकचेन के लिए एक नई वास्तुकला प्रस्तुत करता है। Solana एक नवीन समय-रखरखाव तंत्र को लागू करता है जिसे Proof of History (PoH) कहा जाता है — घटनाओं के बीच क्रम और समय के बीतने को सत्यापित करने का एक प्रमाण। PoH का उपयोग विश्वासहीन समय के बीतने को एक लेजर में एन्कोड करने के लिए किया जाता है, जो एक ऐतिहासिक रिकॉर्ड बनाता है जो यह साबित करता है कि एक घटना एक विशिष्ट समय पर हुई थी।
मुख्य नवाचार यह है कि PoH नेटवर्क में नोड्स को एक-दूसरे के साथ संवाद किए बिना घटनाओं का कालानुक्रमिक क्रम स्थापित करने की अनुमति देता है। एक अनुक्रमिक हैश चेन के रूप में कार्यान्वित एक सत्यापन योग्य विलंब फ़ंक्शन का उपयोग करके, सिस्टम एक क्रिप्टोग्राफ़िक घड़ी उत्पन्न करता है जो घटनाओं के बीच समय के बीतने को सत्यापित करने का एक तरीका प्रदान करता है। यह नेटवर्क को विकेंद्रीकरण और सुरक्षा बनाए रखते हुए प्रति सेकंड हजारों लेनदेन संसाधित करने में सक्षम बनाता है।
PoH को Proof of Stake (PoS) सहमति तंत्र के साथ एकीकृत किया गया है। यह संयोजन एक अत्यधिक अनुकूलित ब्लॉकचेन वास्तुकला को सक्षम बनाता है जहां सत्यापनकर्ता समानांतर में लेनदेन सत्यापित कर सकते हैं और कुशलतापूर्वक सहमति प्राप्त कर सकते हैं। सिस्टम को मूर के नियम के साथ स्केल करने के लिए डिज़ाइन किया गया है, जो विकेंद्रीकृत नेटवर्क की सुरक्षा गारंटी को त्यागे बिना थ्रूपुट में सुधार के लिए हार्डवेयर प्रदर्शन में वृद्धि का लाभ उठाता है।
Abstract
本論文は、高性能ブロックチェーンのための新しいアーキテクチャを提示する。SolanaはProof of History(PoH)と呼ばれる新しい時間管理メカニズムを実装している。これはイベント間の順序と時間の経過を検証するための証明である。PoHは信頼不要な時間の経過を台帳にエンコードするために使用され、特定の時点でイベントが発生したことを証明する履歴記録を作成する。
重要なイノベーションは、PoHによりネットワーク内のノードが互いに通信することなくイベントの時間的順序を確立できることである。逐次的ハッシュチェーンとして実装された検証可能な遅延関数を使用することで、システムはイベント間の時間の経過を検証する方法を提供する暗号学的時計を生成する。これにより、ネットワークは分散化とセキュリティを維持しながら、毎秒数千のトランザクションを処理できる。
PoHはProof of Stake(PoS)コンセンサスメカニズムと統合されている。この組み合わせにより、バリデータがトランザクションを並列に検証し、効率的にコンセンサスに達することができる高度に最適化されたブロックチェーンアーキテクチャが可能になる。このシステムはムーアの法則に合わせてスケールするように設計されており、分散型ネットワークのセキュリティ保証を犠牲にすることなく、ハードウェア性能の向上を活用してスループットを改善する。
Introduction
ब्लॉकचेन सिस्टम में मौलिक चुनौती विकेंद्रीकरण और सुरक्षा बनाए रखते हुए उच्च लेनदेन थ्रूपुट प्राप्त करना है। वर्तमान ब्लॉकचेन कार्यान्वयन अपने सहमति तंत्रों द्वारा सीमित हैं, जिनके लिए नोड्स के बीच समय और घटनाओं के क्रम पर सहमत होने के लिए व्यापक संचार की आवश्यकता होती है। यह समन्वय ओवरहेड एक अड़चन पैदा करता है जो मौजूदा ब्लॉकचेन को वैश्विक-स्तर के अनुप्रयोगों की मांगों को पूरा करने के लिए स्केल करने से रोकता है।
मूल समस्या समय है। वितरित सिस्टम में, नोड्स बाहरी घड़ियों पर भरोसा नहीं कर सकते क्योंकि वे विश्वास नहीं कर सकते कि अन्य नोड्स के टाइमस्टैम्प सटीक हैं। पारंपरिक ब्लॉकचेन सहमति प्रोटोकॉल इसे नोड्स के वर्तमान स्थिति और लेनदेन के क्रम पर सहमत होने के लिए व्यापक रूप से संवाद करके हल करते हैं। यह संचार ओवरहेड मौलिक रूप से थ्रूपुट को सीमित करता है, क्योंकि नेटवर्क केवल उतनी तेजी से लेनदेन संसाधित कर सकता है जितनी तेजी से नोड्स उनके क्रम पर सहमति प्राप्त कर सकते हैं।
Solana इस समय समस्या के समाधान के रूप में Proof of History पेश करता है। PoH संभावित दुर्भावनापूर्ण अभिकर्ताओं से टाइमस्टैम्प पर निर्भर किए बिना यह साबित करने का एक क्रिप्टोग्राफ़िक तरीका प्रदान करता है कि घटनाओं के बीच एक निश्चित मात्रा में समय बीत चुका है। एक सत्यापन योग्य ऐतिहासिक रिकॉर्ड बनाकर, PoH नोड्स को स्वतंत्र रूप से लेनदेन संसाधित करने में सक्षम बनाता है जबकि वे अभी भी उस क्रम को साबित कर सकते हैं जिसमें घटनाएं हुईं। यह सफलता नेटवर्क को लेनदेन प्रसंस्करण को समानांतर करने और थ्रूपुट को नाटकीय रूप से बढ़ाने की अनुमति देती है।
मुख्य अंतर्दृष्टि यह है कि यदि हम एक विश्वासहीन समय स्रोत बना सकते हैं, तो हम सहमति से समन्वय की अड़चन को हटा सकते हैं। PoH एक क्रिप्टोग्राफ़िक घड़ी प्रदान करने के साथ, सत्यापनकर्ता समानांतर में लेनदेन संसाधित कर सकते हैं और केवल विहित क्रम को अंतिम रूप देने के लिए संवाद करने की आवश्यकता है। यह वास्तुशिल्प परिवर्तन Solana को प्रदर्शन स्तर प्राप्त करने में सक्षम बनाता है जो पहले एक विकेंद्रीकृत ब्लॉकचेन में असंभव माने जाते थे।
Introduction
ブロックチェーンシステムにおける根本的な課題は、分散化とセキュリティを維持しながら高いトランザクションスループットを達成することである。現在のブロックチェーン実装は、時間とイベントの順序付けについて合意するためにノード間の広範な通信を必要とするコンセンサスメカニズムによって制限されている。この調整のオーバーヘッドがボトルネックを生み出し、既存のブロックチェーンがグローバル規模のアプリケーションの需要に対応するためのスケーリングを妨げている。
核心的な問題は時間である。分散システムにおいて、ノードは他のノードのタイムスタンプが正確であることを信頼できないため、外部の時計に依存することができない。従来のブロックチェーンコンセンサスプロトコルは、ノードが現在の状態とトランザクションの順序について合意するために広範に通信することでこの問題を解決している。この通信のオーバーヘッドはスループットを根本的に制限する。ネットワークはノードが順序付けについてコンセンサスに達する速度でしかトランザクションを処理できないからである。
SolanaはこのタイミングProblemの解決策としてProof of Historyを導入する。PoHは、潜在的に悪意のあるアクターからのタイムスタンプに依存することなく、イベント間に一定の時間が経過したことを証明する暗号学的方法を提供する。検証可能な履歴記録を作成することで、PoHはノードがトランザクションを独立して処理しながら、イベントが発生した順序を証明できるようにする。このブレークスルーにより、ネットワークはトランザクション処理を並列化し、スループットを劇的に向上させることができる。
重要な洞察は、信頼不要な時間源を作成できれば、コンセンサスから調整のボトルネックを除去できるということである。PoHが暗号学的時計を提供することで、バリデータはトランザクションを並列に処理でき、正規の順序付けを確定するためにのみ通信する必要がある。このアーキテクチャの転換により、Solanaは分散型ブロックチェーンでは不可能と考えられていたパフォーマンスレベルを達成できる。
Outline
यह पेपर Solana की तकनीकी वास्तुकला का वर्णन करता है, इस पर ध्यान केंद्रित करते हुए कि Proof of History कैसे उच्च-प्रदर्शन ब्लॉकचेन संचालन को सक्षम बनाता है। दस्तावेज़ पहले PoH तंत्र को स्वयं समझाता है — कैसे एक अनुक्रमिक हैश चेन घटनाओं का सत्यापन योग्य कालानुक्रमिक क्रम बनाती है। हम उन क्रिप्टोग्राफ़िक गुणों का विवरण देते हैं जो PoH को सुरक्षित बनाते हैं और दिखाते हैं कि सत्यापनकर्ता PoH अनुक्रम को कुशलतापूर्वक कैसे सत्यापित कर सकते हैं।
फिर पेपर यह खोजता है कि PoH Proof of Stake सहमति के साथ कैसे एकीकृत होता है। हम Tower BFT का वर्णन करते हैं, एक PoS एल्गोरिथ्म जो विशेष रूप से PoH के कालिक गुणों का लाभ उठाने के लिए डिज़ाइन किया गया है। एकीकरण सत्यापनकर्ताओं को विशिष्ट PoH टाइमस्टैम्प पर लेजर की स्थिति पर वोट करने की अनुमति देता है, एक ऐसा सहमति तंत्र बनाता है जो तेज और सुरक्षित दोनों है। हम उन स्लैशिंग शर्तों को भी समझाते हैं जो दुर्भावनापूर्ण व्यवहार को रोकती हैं।
इसके बाद, हम Solana के नेटवर्क डिज़ाइन और डेटा प्रसार प्रोटोकॉल प्रस्तुत करते हैं। Gulf Stream प्रोटोकॉल मेमपूल की आवश्यकता के बिना लेनदेन अग्रेषण को सक्षम बनाता है, जिससे क्लाइंट आगामी लीडर्स को सीधे लेनदेन भेज सकते हैं। हम वर्णन करते हैं कि लीडर रोटेशन कैसे काम करता है और नेतृत्व बदलने पर भी नेटवर्क उच्च थ्रूपुट कैसे बनाए रखता है।
अंत में, हम Transaction Processing Unit (TPU), Sealevel समानांतर रनटाइम, और डेटा स्टोरेज सत्यापन के लिए Proof of Replication सहित सिस्टम वास्तुकला पर चर्चा करते हैं। प्रदर्शन अनुमान दर्शाते हैं कि Solana एक मानक गीगाबिट नेटवर्क पर प्रति सेकंड 700,000 से अधिक लेनदेन संसाधित कर सकता है, और हार्डवेयर में सुधार के साथ थ्रूपुट स्केल होता है।
Outline
本論文では、Proof of Historyが高性能ブロックチェーン運用をいかに実現するかに焦点を当て、Solanaの技術アーキテクチャを説明する。まず、PoHメカニズム自体について説明する。逐次的ハッシュチェーンがいかにしてイベントの検証可能な時間的順序付けを作成するかを解説する。PoHを安全にする暗号学的特性を詳述し、バリデータがPoHシーケンスを効率的に検証する方法を示す。
次に、PoHがProof of Stakeコンセンサスとどのように統合されるかを探る。PoHの時間的特性を活用するために特別に設計されたPoSアルゴリズムであるTower BFTについて説明する。この統合により、バリデータは特定のPoHタイムスタンプにおける台帳の状態に投票でき、高速かつ安全なコンセンサスメカニズムが実現される。また、悪意ある行動を防止するスラッシング条件についても説明する。
続いて、Solanaのネットワーク設計とデータ伝播プロトコルを提示する。Gulf Streamプロトコルは、mempoolを必要とせずにトランザクション転送を可能にし、クライアントが今後のリーダーに直接トランザクションを送信できるようにする。リーダーローテーションの仕組みと、リーダーシップが変わっても高スループットを維持する方法を説明する。
最後に、Transaction Processing Unit(TPU)、Sealevel並列ランタイム、データストレージ検証のためのProof of Replicationを含むシステムアーキテクチャについて論じる。性能予測は、Solanaが標準的なギガビットネットワーク上で毎秒70万以上のトランザクションを処理でき、ハードウェアの改善に伴いスループットがスケールすることを示している。
Network Design
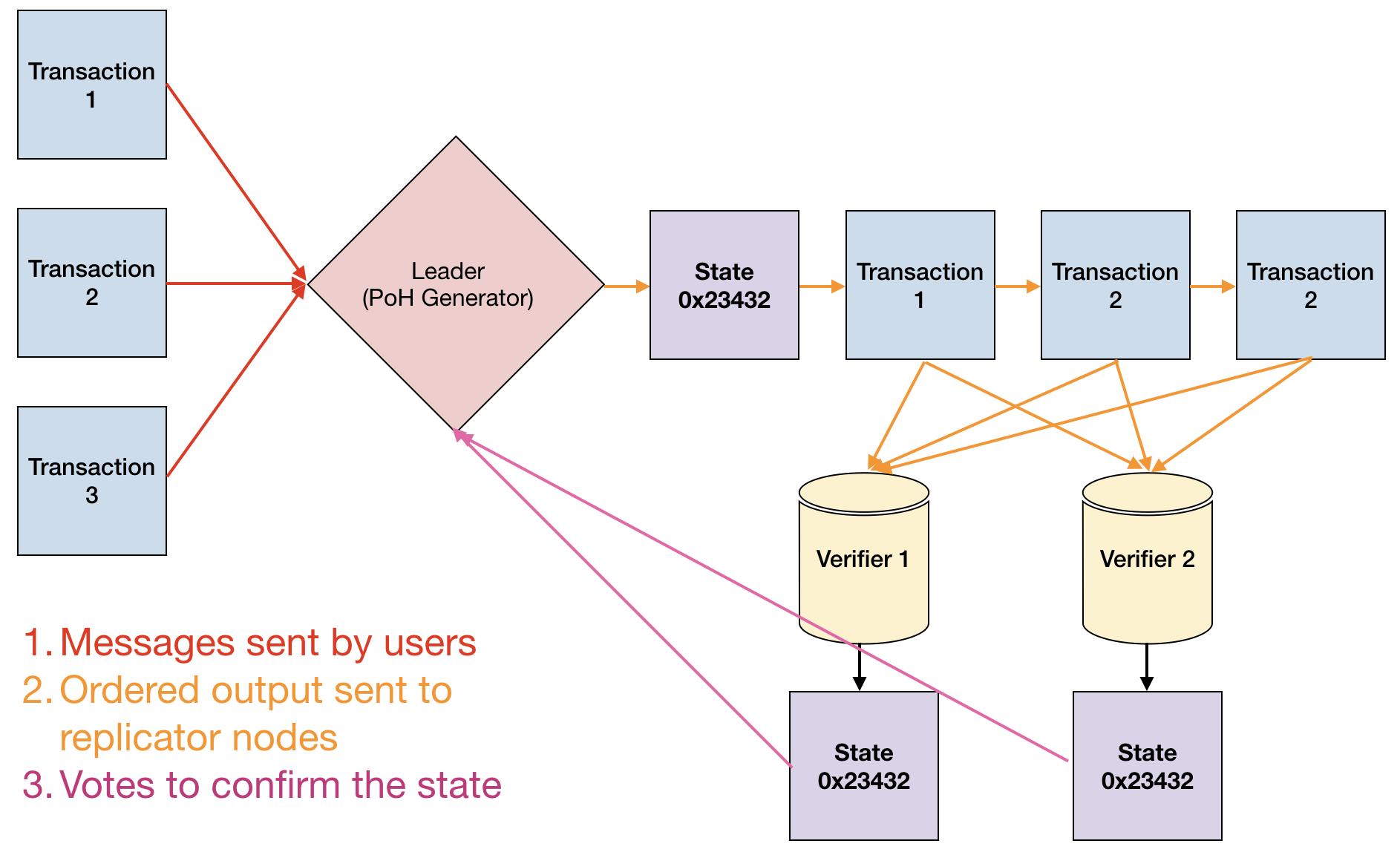
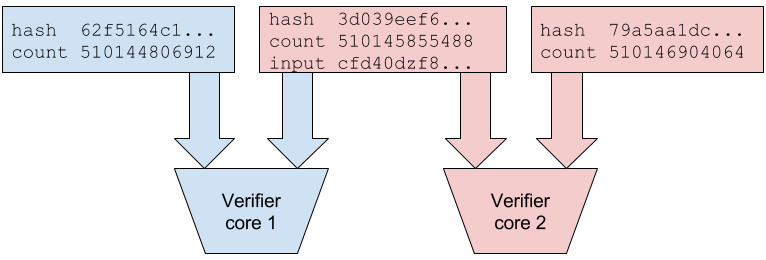
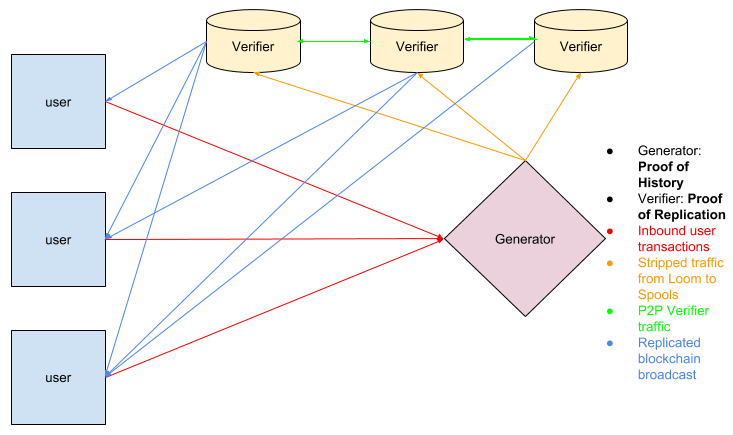
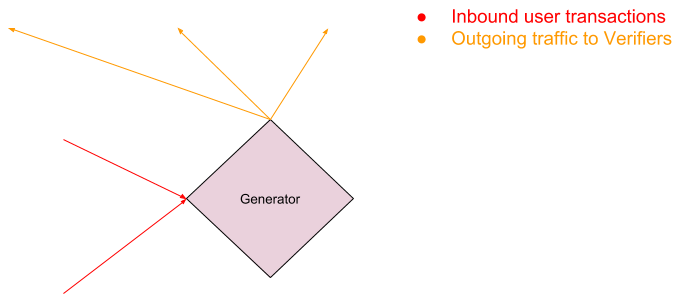
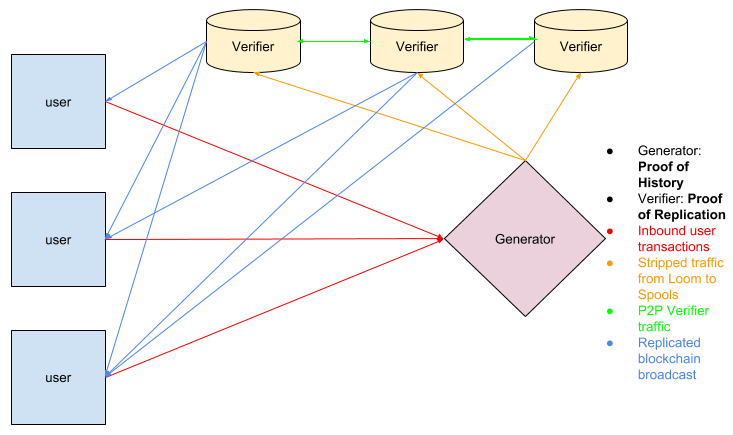
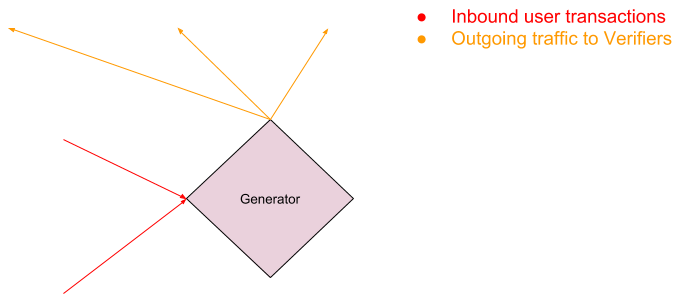
Solana का नेटवर्क डिज़ाइन एक घूर्णन लीडर सिस्टम के इर्द-गिर्द केंद्रित है जहां सत्यापनकर्ता बारी-बारी से ब्लॉक उत्पन्न करते हैं। लीडर आने वाले लेनदेन को PoH स्ट्रीम में अनुक्रमित करने और परिणामी ब्लॉक को नेटवर्क पर प्रकाशित करने के लिए जिम्मेदार है। लीडर्स को स्टेक-भारित एल्गोरिथ्म के माध्यम से चुना जाता है, और रोटेशन शेड्यूल पहले से ज्ञात होता है, जिससे नेटवर्क लेनदेन अग्रेषण को अनुकूलित कर सकता है।
Gulf Stream प्रोटोकॉल क्लाइंट्स को आगामी लीडर्स को सीधे लेनदेन अग्रेषित करने में सक्षम बनाकर पारंपरिक मेमपूल की आवश्यकता को समाप्त करता है। जब कोई क्लाइंट लेनदेन सबमिट करता है, तो इसे रोटेशन शेड्यूल के आधार पर अपेक्षित लीडर को अग्रेषित किया जाता है। यदि वर्तमान लीडर लेनदेन को संसाधित नहीं कर सकता, तो इसे अगले अपेक्षित लीडर को अग्रेषित किया जाता है। यह डिज़ाइन पुष्टि विलंबता को कम करता है और सत्यापनकर्ताओं को समय से पहले लेनदेन निष्पादित करने की अनुमति देता है, जो थ्रूपुट को और अनुकूलित करता है।
लेनदेन प्रसार एक बहु-परत दृष्टिकोण का उपयोग करता है। क्लाइंट सत्यापनकर्ताओं को लेनदेन भेजते हैं, जो उन्हें वर्तमान या आगामी लीडर को अग्रेषित करते हैं। लीडर लेनदेन को PoH स्ट्रीम में अनुक्रमित करता है, एक कुल क्रम बनाता है। अनुक्रमण के बाद, लीडर PoH स्ट्रीम और लेनदेन डेटा को सत्यापनकर्ताओं को प्रेषित करता है, जो PoH अनुक्रम को सत्यापित करते हैं और समानांतर में लेनदेन निष्पादित करते हैं।
नेटवर्क डिज़ाइन में एक Turbine ब्लॉक प्रसार प्रोटोकॉल भी शामिल है जो ब्लॉक को छोटे पैकेट में विभाजित करता है और उन्हें एक ट्री संरचना में नेटवर्क में वितरित करता है। यह दृष्टिकोण तेज ब्लॉक प्रसार सुनिश्चित करते हुए व्यक्तिगत सत्यापनकर्ताओं के लिए बैंडविड्थ आवश्यकताओं को कम करता है। PoH की लेनदेन क्रम सत्यापित करने की क्षमता के साथ मिलकर, यह वास्तुकला Solana को विकेंद्रीकरण का त्याग किए बिना उच्च थ्रूपुट प्राप्त करने में सक्षम बनाती है।
Network Design
Solanaのネットワーク設計は、バリデータが交代でブロックを生成するローテーションリーダーシステムを中心としている。リーダーは、着信トランザクションをPoHストリームに順序付けし、結果のブロックをネットワークに公開する責任を持つ。リーダーはステーク加重アルゴリズムによって選出され、ローテーションスケジュールは事前に知られているため、ネットワークはトランザクション転送を最適化できる。
Gulf Streamプロトコルは、クライアントが今後のリーダーに直接トランザクションを転送できるようにすることで、従来のmempoolの必要性を排除する。クライアントがトランザクションを送信すると、ローテーションスケジュールに基づいて予想されるリーダーに転送される。現在のリーダーがトランザクションを処理できない場合、次の予想リーダーに転送される。この設計により確認レイテンシが短縮され、バリデータが事前にトランザクションを実行できるため、スループットがさらに最適化される。
トランザクション伝播はマルチレイヤーアプローチを使用する。クライアントはバリデータにトランザクションを送信し、バリデータは現在のリーダーまたは今後のリーダーに転送する。リーダーはトランザクションをPoHストリームに順序付けし、全体の順序付けを作成する。順序付けが完了すると、リーダーはPoHストリームとトランザクションデータをバリデータに送信し、バリデータはPoHシーケンスを検証してトランザクションを並列に実行する。
ネットワーク設計には、ブロックをより小さなパケットに分割し、ツリー構造でネットワーク全体に配布するTurbineブロック伝播プロトコルも含まれている。このアプローチにより、迅速なブロック伝播を確保しながら、個々のバリデータの帯域幅要件を最小化する。PoHのトランザクション順序検証能力と組み合わせることで、このアーキテクチャはSolanaが分散化を犠牲にすることなく高スループットを達成することを可能にする。
Proof of History
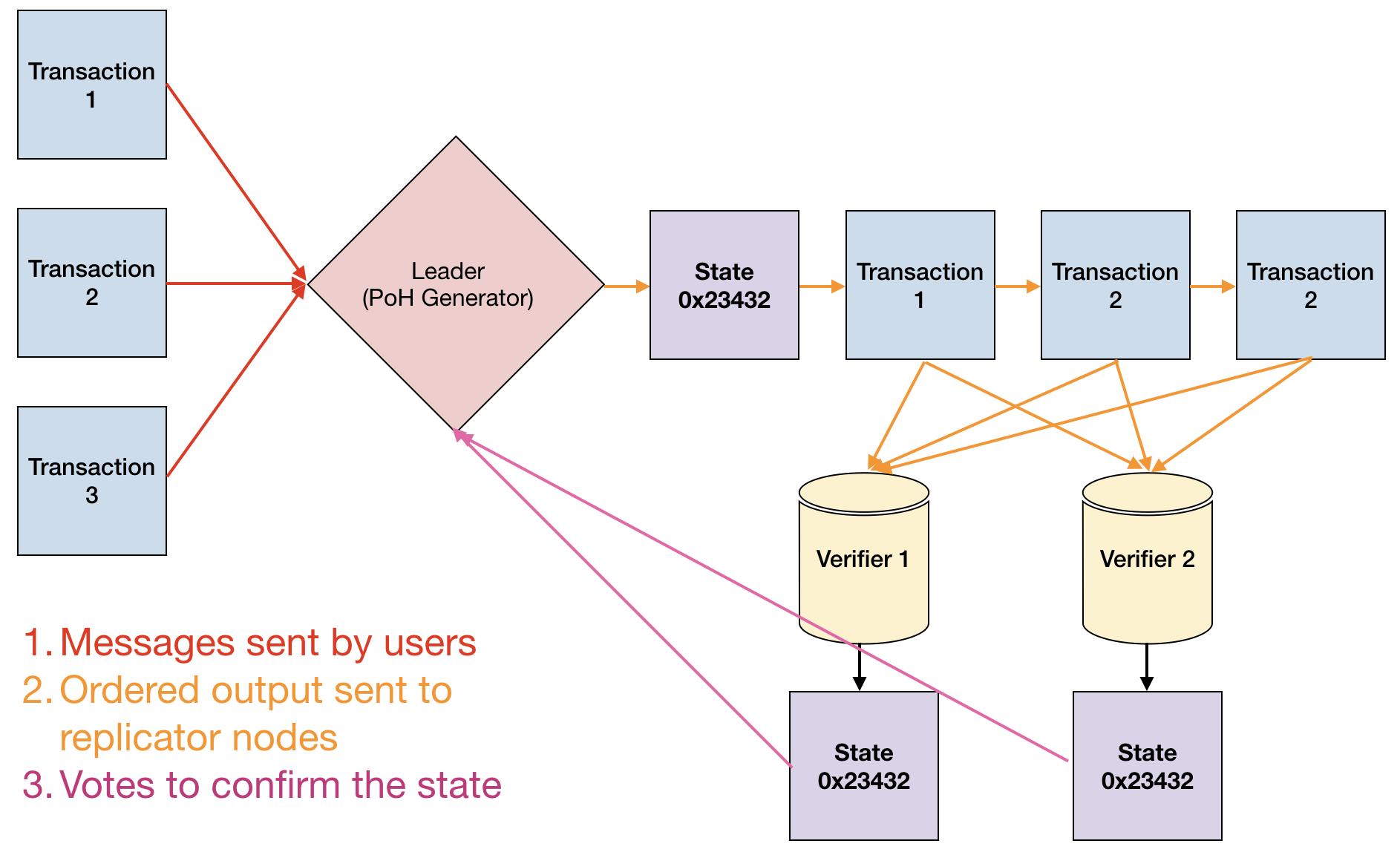
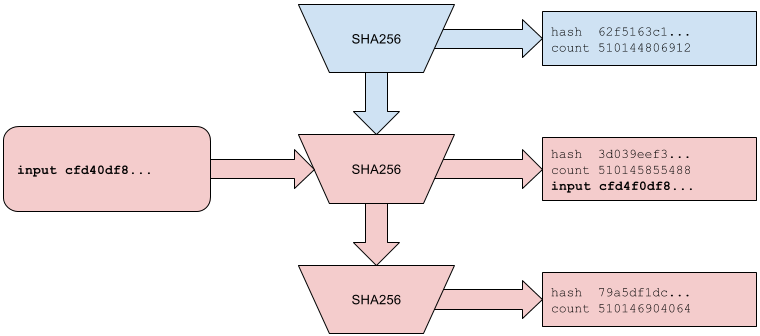
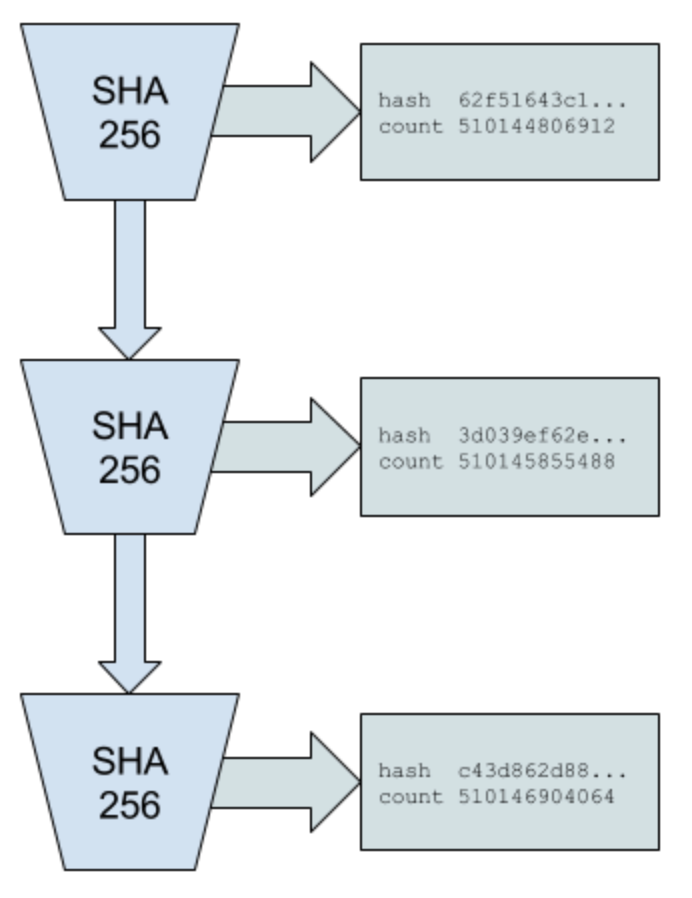
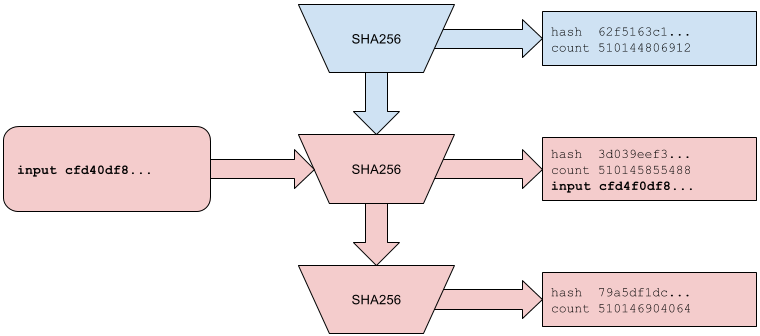
Proof of History SHA-256 का उपयोग करके एक अनुक्रमिक हैश चेन के रूप में कार्यान्वित एक सत्यापन योग्य विलंब फ़ंक्शन है। PoH जनरेटर लगातार SHA-256 हैश की गणना करता है, प्रत्येक आउटपुट को अगले हैश के लिए इनपुट के रूप में उपयोग करता है। यह एक अनुक्रमिक चेन बनाता है जहां प्रत्येक हैश केवल पिछले वाले के बाद ही गणना किया जा सकता है, एक सत्यापन योग्य कालानुक्रमिक क्रम स्थापित करता है। प्रत्येक हैश उत्पन्न करने की गणनात्मक आवश्यकता घटनाओं के बीच न्यूनतम समय विलंब लागू करती है।
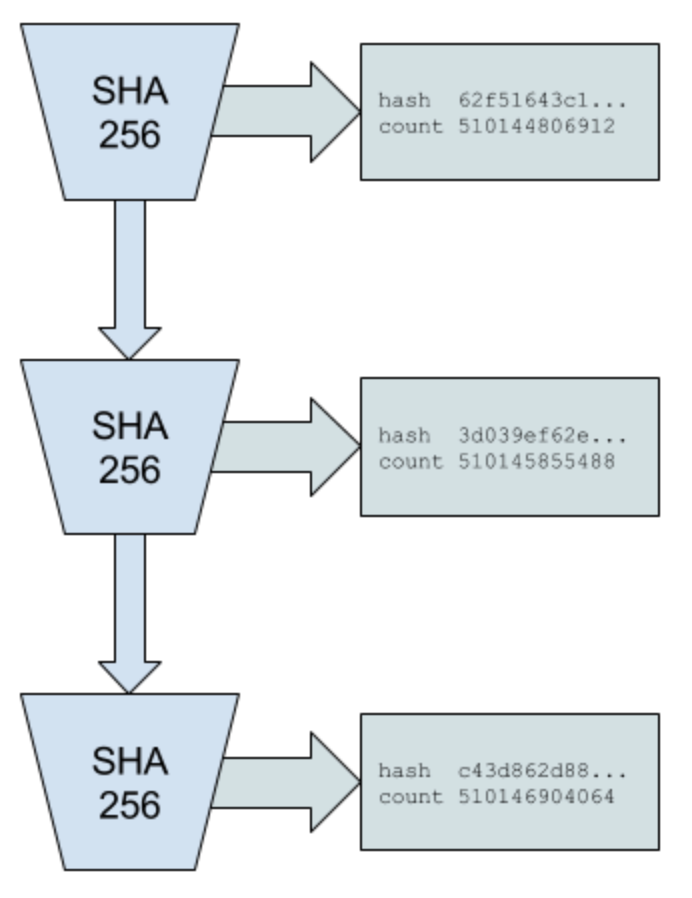
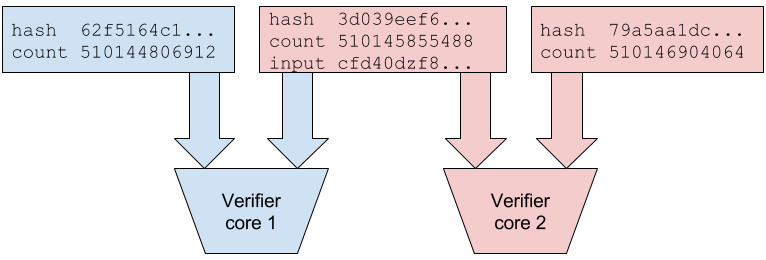
PoH की मुख्य संपत्ति यह है कि इसे सत्यापित करना सस्ता है लेकिन उत्पन्न करना महंगा है। एक सत्यापनकर्ता पूरे हैश अनुक्रम को खंडों में विभाजित करके और प्रत्येक खंड को स्वतंत्र रूप से समानांतर में जांचकर, फिर यह सत्यापित करके कि खंड ठीक से जुड़ते हैं, जांच सकता है। हालांकि, उत्पादन अनुक्रमिक होना चाहिए — वास्तव में हर मध्यवर्ती चरण की गणना किए बिना हैश चेन के आउटपुट की भविष्यवाणी करने का कोई तरीका नहीं है। उत्पादन और सत्यापन के बीच यह विषमता PoH को व्यावहारिक बनाती है।
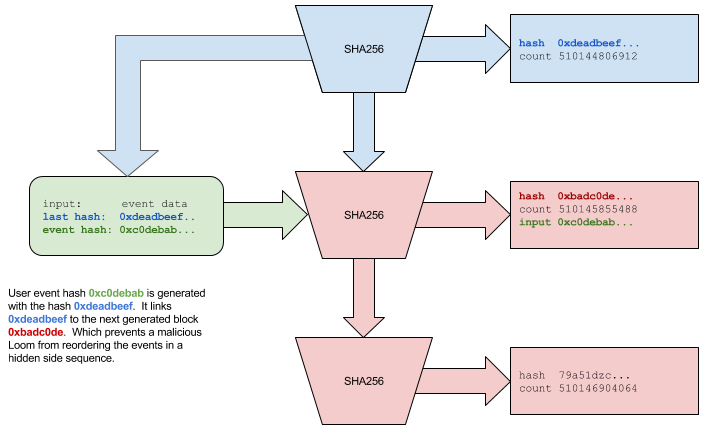
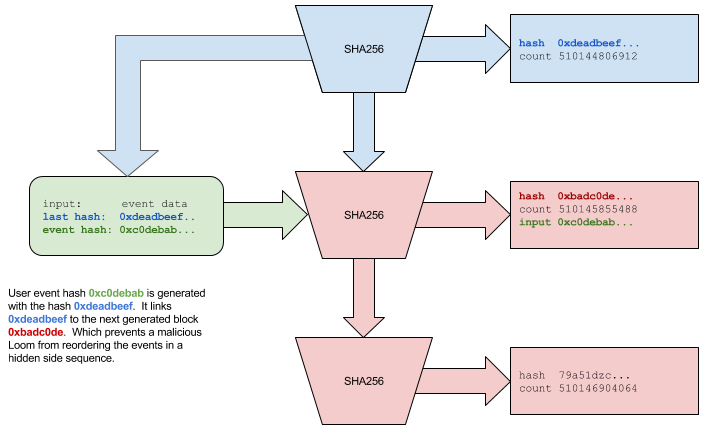
बाहरी घटनाओं और लेनदेन डेटा को हैश चेन में मिलाकर PoH अनुक्रम में डाला जाता है। जब कोई लेनदेन आता है, तो उसका हैश वर्तमान PoH स्थिति के साथ जोड़ दिया जाता है, एक रिकॉर्ड बनाता है जो साबित करता है कि लेनदेन अनुक्रम के उस बिंदु पर मौजूद था। PoH जनरेटर समय-समय पर चेकपॉइंट रिकॉर्ड करता है, अंतिम चेकपॉइंट के बाद से गणना किए गए हैश की संख्या के साथ वर्तमान हैश मान प्रकाशित करता है। ये चेकपॉइंट सत्यापनकर्ताओं को प्रत्येक हैश की पुनर्गणना किए बिना PoH अनुक्रम को कुशलतापूर्वक सत्यापित करने की अनुमति देते हैं।
PoH अनुक्रम पूरे नेटवर्क के लिए एक क्रिप्टोग्राफ़िक घड़ी के रूप में कार्य करता है। क्योंकि हैश चेन अनुक्रमिक और सत्यापन योग्य है, कोई भी नोड बस उस अंतराल के दौरान गणना किए गए हैश दिखाकर साबित कर सकता है कि दो घटनाओं के बीच एक निश्चित मात्रा में समय बीत चुका है। यह नोड्स के लिए बाहरी टाइमस्टैम्प पर भरोसा करने या कालानुक्रमिक क्रम स्थापित करने के लिए एक-दूसरे के साथ समन्वय करने की आवश्यकता को समाप्त करता है, पारंपरिक ब्लॉकचेन सहमति में एक मौलिक अड़चन को हटाता है।
Proof of History
Proof of Historyは、SHA-256を使用した逐次的ハッシュチェーンとして実装された検証可能な遅延関数である。PoHジェネレータは継続的にSHA-256ハッシュを計算し、各出力を次のハッシュの入力として使用する。これにより、各ハッシュは前のものが計算された後にのみ計算できる逐次的なチェーンが作成され、検証可能な時間的順序付けが確立される。各ハッシュを生成するための計算要件により、イベント間の最小時間遅延が強制される。
PoHの重要な特性は、検証は安価だが生成は高コストであることである。検証者はハッシュシーケンス全体をセグメントに分割し、各セグメントを独立して並列にチェックし、セグメントが適切に接続されていることを確認することで検証できる。しかし、生成は逐次的でなければならない。すべての中間ステップを実際に計算せずにハッシュチェーンの出力を予測する方法はない。生成と検証の間のこの非対称性がPoHを実用的にしている。
外部イベントとトランザクションデータは、ハッシュチェーンに混合されることでPoHシーケンスに挿入される。トランザクションが到着すると、そのハッシュは現在のPoH状態と結合され、トランザクションがシーケンスのその時点で存在したことを証明する記録が作成される。PoHジェネレータは定期的にチェックポイントを記録し、最後のチェックポイント以降に計算されたハッシュ数とともに現在のハッシュ値を公開する。これらのチェックポイントにより、バリデータはすべてのハッシュを再計算することなくPoHシーケンスを効率的に検証できる。
PoHシーケンスはネットワーク全体の暗号学的時計として機能する。ハッシュチェーンは逐次的で検証可能であるため、任意のノードは、その間隔中に計算されたハッシュを示すだけで、2つのイベント間に一定の時間が経過したことを証明できる。これにより、ノードが外部のタイムスタンプを信頼したり、時間的順序付けを確立するために互いに調整したりする必要がなくなり、従来のブロックチェーンコンセンサスにおける根本的なボトルネックが除去される。
Proof of History Sequence
Proof of History अनुक्रम SHA-256 हैश की एक निरंतर चेन है जहां प्रत्येक हैश पिछले आउटपुट पर निर्भर करता है। अनुक्रम एक प्रारंभिक बीज मान से शुरू होता है, जिसे पहला आउटपुट उत्पन्न करने के लिए हैश किया जाता है। यह आउटपुट अगले हैश के लिए इनपुट बन जाता है, और प्रक्रिया अनिश्चित काल तक दोहराई जाती है। जनरेटर एक काउंटर भी बनाए रखता है जो गणना किए गए हैश की कुल संख्या को ट्रैक करता है, जो लेजर में घटनाओं के लिए PoH "टाइमस्टैम्प" के रूप में कार्य करता है।
जब डेटा को अनुक्रम में डालने की आवश्यकता होती है (जैसे लेनदेन हैश या सत्यापनकर्ता हस्ताक्षर), तो इसे एक नियतात्मक मिश्रण फ़ंक्शन का उपयोग करके वर्तमान हैश स्थिति के साथ जोड़ा जाता है। उदाहरण के लिए, यदि वर्तमान हैश स्थिति hash_n है और हम डेटा D डालना चाहते हैं, तो हम hash_{n+1} = SHA256(hash_n || D) की गणना करते हैं, जहां || संयोजन को दर्शाता है। सम्मिलन बिंदु काउंटर मान के साथ रिकॉर्ड किया जाता है, यह साबित करता है कि डेटा D अनुक्रम के उस विशिष्ट बिंदु पर मौजूद था।
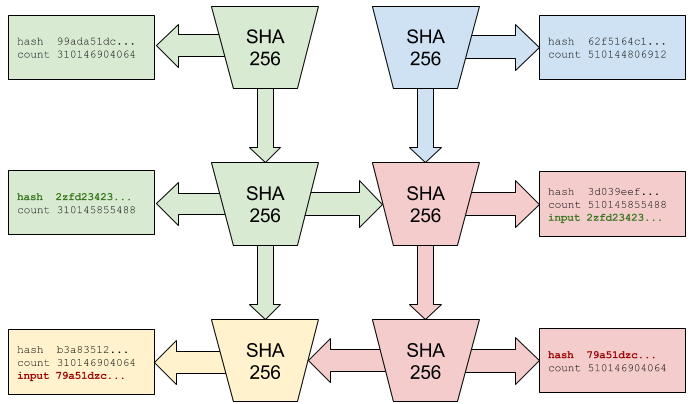
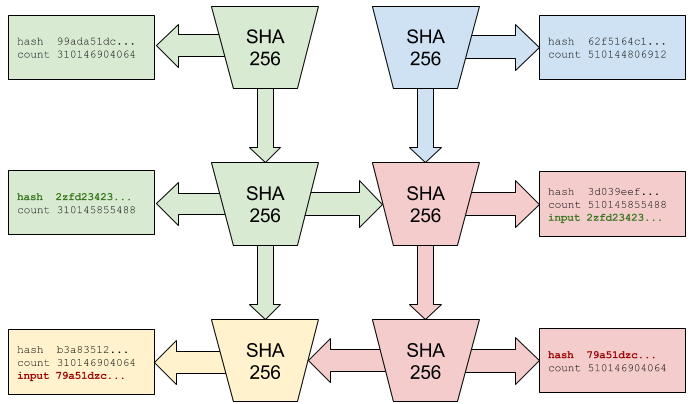
PoH अनुक्रम का सत्यापन चेन को खंडों में विभाजित करके समानांतर किया जा सकता है। उदाहरण के लिए, एक सत्यापनकर्ता हर 10,000 हैश पर PoH चेकपॉइंट प्राप्त कर सकता है। चेकपॉइंट के बीच अनुक्रम को सत्यापित करने के लिए, सत्यापनकर्ता 10,000 हैश को प्रत्येक 100 हैश के 100 खंडों में विभाजित कर सकता है, प्रत्येक खंड को समानांतर में स्वतंत्र रूप से सत्यापित कर सकता है, और फिर यह सत्यापित कर सकता है कि खंड ठीक से जुड़ते हैं। यह सत्यापन को उपलब्ध CPU कोर की संख्या के साथ क्षैतिज रूप से स्केल करने की अनुमति देता है।
अनुक्रम यह भी समर्थन करता है कि दो घटनाएं एक विशिष्ट क्रम में हुईं इसका कुशल प्रमाण। काउंटर मान n और m पर दो डेटा सम्मिलन दिए गए हैं जहां n m, कोई भी उन बिंदुओं के बीच हैश चेन की जांच करके सत्यापित कर सकता है कि n पर घटना m पर घटना से पहले हुई। यह गुण Solana को नोड्स के लगातार ऑनलाइन होने या बाहरी समय स्रोतों पर भरोसा किए बिना नेटवर्क में सभी घटनाओं का सत्यापन योग्य ऐतिहासिक रिकॉर्ड बनाने में सक्षम बनाता है।
Proof of History Sequence
Proof of Historyシーケンスは、各ハッシュが前の出力に依存するSHA-256ハッシュの連続的なチェーンである。シーケンスは初期シード値から始まり、それがハッシュされて最初の出力を生成する。この出力が次のハッシュの入力となり、プロセスは無限に繰り返される。ジェネレータは計算されたハッシュの総数を追跡するカウンタも維持しており、台帳内のイベントのPoH「タイムスタンプ」として機能する。
データをシーケンスに挿入する必要がある場合(トランザクションハッシュやバリデータの署名など)、決定論的な混合関数を使用して現在のハッシュ状態と結合される。例えば、現在のハッシュ状態がhash_nで、データDを挿入する場合、hash_{n+1} = SHA256(hash_n || D)を計算する。ここで||は連結を表す。挿入ポイントはカウンタ値とともに記録され、データDがシーケンスのその特定の時点で存在したことを証明する。
PoHシーケンスの検証は、チェーンをセグメントに分割することで並列化できる。例えば、バリデータは10,000ハッシュごとにPoHチェックポイントを受信する場合がある。チェックポイント間のシーケンスを検証するために、バリデータは10,000ハッシュを100ハッシュの100セグメントに分割し、各セグメントを独立して並列に検証し、セグメントが適切に接続されていることを確認できる。これにより、検証は利用可能なCPUコア数に応じて水平にスケールできる。
シーケンスは、2つのイベントが特定の順序で発生したことの効率的な証明もサポートする。カウンタ値nとm(n m)における2つのデータ挿入がある場合、nのイベントがmのイベントより前に発生したことを、それらの間のハッシュチェーンを確認することで誰でも検証できる。この特性により、Solanaはノードが継続的にオンラインであったり外部の時間源を信頼したりする必要なく、ネットワーク内のすべてのイベントの検証可能な履歴記録を作成できる。
Timestamp
Proof of History एक विकेंद्रीकृत घड़ी के रूप में कार्य करता है जो दीवार-घड़ी समय पर निर्भर किए बिना घटनाओं को टाइमस्टैम्प प्रदान करता है। प्रत्येक PoH हैश क्रिप्टोग्राफ़िक घड़ी का एक असतत "टिक" दर्शाता है, और काउंटर मान टाइमस्टैम्प के रूप में कार्य करता है। क्योंकि हैश चेन अनुक्रमिक और सत्यापन योग्य है, ये टाइमस्टैम्प विश्वासहीन हैं — कोई भी पर्यवेक्षक हैश चेन की जांच करके सत्यापित कर सकता है कि टाइमस्टैम्प वैध है।
Solana में, प्रत्येक सत्यापनकर्ता लीडर के रूप में कार्य करते समय अपना स्वयं का PoH अनुक्रम उत्पन्न कर सकता है। जब सत्यापनकर्ता नेतृत्व का रोटेशन करते हैं, तो वे पिछले लीडर के अंतिम पुष्टि किए गए चेकपॉइंट का उपयोग करके अपने PoH अनुक्रमों को सिंक्रनाइज़ करते हैं। यह सुनिश्चित करता है कि विभिन्न सत्यापनकर्ताओं द्वारा बारी-बारी से ब्लॉक उत्पन्न करने पर भी कालिक रिकॉर्ड की निरंतरता बनी रहे। नेटवर्क यह सहमति प्राप्त करके एक विहित समयरेखा स्थापित करता है कि कौन से PoH अनुक्रमों को आधिकारिक लेजर के भाग के रूप में स्वीकार किया जाए।
सिस्टम लीडर रोटेशन और सहमति के संयोजन के माध्यम से क्लॉक ड्रिफ्ट और हार्डवेयर प्रदर्शन में भिन्नता को संभालता है। यदि कोई दुर्भावनापूर्ण या दोषपूर्ण लीडर गलत दर (बहुत तेज या बहुत धीमी) पर PoH टाइमस्टैम्प उत्पन्न करने का प्रयास करता है, तो सत्यापनकर्ता अपने स्वयं के स्थानीय PoH जनरेटर के साथ PoH टिक दर की तुलना करके इसका पता लगा सकते हैं। अपेक्षित दर से महत्वपूर्ण विचलन एक समस्या का संकेत देते हैं, और सत्यापनकर्ता उन लीडर्स के ब्लॉक को अस्वीकार कर सकते हैं जिनके PoH अनुक्रम नेटवर्क माध्यिका से बहुत दूर विचलित होते हैं।
यह टाइमस्टैम्पिंग तंत्र वितरित सिस्टम में मौलिक समस्याओं में से एक को हल करता है: एक विश्वसनीय केंद्रीय प्राधिकरण के बिना समय की एक सामान्य धारणा स्थापित करना। PoH को एक विकेंद्रीकृत घड़ी के रूप में उपयोग करके, Solana सत्यापनकर्ताओं को वैश्विक रूप से सुसंगत क्रम बनाए रखते हुए समानांतर में लेनदेन संसाधित करने में सक्षम बनाता है। टाइमस्टैम्प लेनदेन समाप्ति, अनुसूचित संचालन और प्रदर्शन मापन जैसी समय-आधारित सुविधाओं के लिए भी एक आधार प्रदान करते हैं।
Timestamp
Proof of Historyは、壁時計時間に依存せずにイベントにタイムスタンプを割り当てる分散型時計として機能する。各PoHハッシュは暗号学的時計の離散的な「ティック」を表し、カウンタ値がタイムスタンプとして機能する。ハッシュチェーンは逐次的で検証可能であるため、これらのタイムスタンプは信頼不要である。任意の観察者がハッシュチェーンを確認することでタイムスタンプの正当性を検証できる。
Solanaでは、各バリデータがリーダーとして行動する際に独自のPoHシーケンスを生成できる。バリデータがリーダーシップをローテーションする際、前のリーダーからの最後の確認済みチェックポイントを使用してPoHシーケンスを同期する。これにより、異なるバリデータが交代でブロックを生成しても、時間記録の連続性が確保される。ネットワークは、どのPoHシーケンスを公式台帳の一部として受け入れるかについてコンセンサスに達することで、正規のタイムラインを確立する。
システムはクロックドリフトとハードウェア性能のばらつきを、リーダーローテーションとコンセンサスの組み合わせで処理する。悪意のあるまたは故障したリーダーが不正な速度(速すぎるまたは遅すぎる)でPoHタイムスタンプを生成しようとした場合、バリデータは自身のローカルPoHジェネレータとPoHティックレートを比較することでこれを検出できる。予想レートからの大幅な逸脱は問題を示し、バリデータはPoHシーケンスがネットワーク中央値から大きく逸脱するリーダーからのブロックを拒否できる。
このタイムスタンプメカニズムは、分散システムにおける根本的な問題の1つを解決する。信頼できる中央機関なしに共通の時間概念を確立することである。PoHを分散型時計として使用することで、Solanaはバリデータがグローバルに一貫した順序付けを維持しながらトランザクションを並列に処理できるようにする。タイムスタンプはまた、トランザクションの有効期限、スケジュールされた操作、パフォーマンス測定などの時間ベースの機能の基盤も提供する。
Proof of Stake Consensus
Solana का सहमति तंत्र, जिसे Tower BFT कहा जाता है, एक Proof of Stake एल्गोरिथ्म है जो विशेष रूप से Proof of History के कालिक गुणों का लाभ उठाने के लिए डिज़ाइन किया गया है। सत्यापनकर्ता सहमति में भाग लेने के लिए SOL टोकन स्टेक करते हैं और ब्लॉक को सही ढंग से सत्यापित करने के लिए पुरस्कार अर्जित करते हैं। स्टेक-भारित मतदान प्रणाली सुनिश्चित करती है कि नेटवर्क में अधिक आर्थिक हित रखने वाले सत्यापनकर्ताओं का सहमति निर्णयों पर आनुपातिक रूप से अधिक प्रभाव हो।
Tower BFT में मुख्य नवाचार लॉकआउट अवधि का उपयोग है जो प्रत्येक लगातार वोट के साथ तेजी से बढ़ती है। जब कोई सत्यापनकर्ता PoH हैश पर वोट करता है, तो वह एक निश्चित संख्या में PoH टिक के लिए लेजर के उस फोर्क के प्रति प्रतिबद्ध होता है। यदि वे उस फोर्क के अगले ब्लॉक पर वोट करते हैं, तो लॉकआउट अवधि दोगुनी हो जाती है। यह सत्यापनकर्ताओं के लिए एक ही फोर्क पर वोट करते रहने का एक मजबूत आर्थिक प्रोत्साहन बनाता है, क्योंकि फोर्क बदलने के लिए पहले के लॉकआउट की समाप्ति का इंतजार करना आवश्यक होगा।
विशेष रूप से, यदि कोई सत्यापनकर्ता PoH टाइमस्टैम्प t पर किसी ब्लॉक पर वोट करता है, तो वे 2^n टिक बीतने तक किसी विरोधी फोर्क पर वोट नहीं कर सकते, जहां n वर्तमान फोर्क पर किए गए लगातार वोटों की संख्या है। यह घातांकीय लॉकआउट तंत्र सिस्टम को तेज अंतिमता की अनुमति देते हुए दीर्घकालिक हमलों के खिलाफ सुरक्षित बनाता है। एक बार पर्याप्त गहराई के साथ स्टेक के अत्यधिक बहुमत ने किसी ब्लॉक पर वोट कर दिया, तो वह ब्लॉक प्रभावी रूप से अंतिम हो जाता है।
स्लैशिंग शर्तें ईमानदार व्यवहार लागू करती हैं। यदि कोई सत्यापनकर्ता उस अवधि के दौरान दो विरोधी फोर्क पर वोट करता है जब उन्हें लॉक आउट होना चाहिए, तो उन्हें स्लैश किया जाता है — उनके स्टेक किए गए टोकन आंशिक रूप से नष्ट हो जाते हैं और उन्हें सत्यापनकर्ता सेट से हटा दिया जाता है। यह दोहरे मतदान या अन्य बीजान्टिन व्यवहार का प्रयास करना आर्थिक रूप से अतार्किक बनाता है। PoH के सत्यापन योग्य टाइमस्टैम्प और Tower BFT के घातांकीय लॉकआउट का संयोजन एक ऐसा सहमति तंत्र बनाता है जो तेज और सुरक्षित दोनों है, पारंपरिक BFT सिस्टम की सुरक्षा गारंटी बनाए रखते हुए सेकंडों में अंतिमता प्राप्त करता है।
Proof of Stake Consensus
SolanaのコンセンサスメカニズムはTower BFTと呼ばれ、Proof of Historyの時間的特性を活用するために特別に設計されたProof of Stakeアルゴリズムである。バリデータはSOLトークンをステークしてコンセンサスに参加し、ブロックの正確な検証に対して報酬を得る。ステーク加重投票システムにより、ネットワークにより多くの経済的利害関係を持つバリデータがコンセンサス決定に比例してより多くの影響力を持つことが保証される。
Tower BFTの核心的なイノベーションは、連続投票ごとに指数関数的に増加するロックアウト期間の使用である。バリデータがPoHハッシュに投票すると、一定数のPoHティックの間、台帳のそのフォークにコミットする。そのフォークの次のブロックに投票すると、ロックアウト期間は倍増する。これにより、バリデータが同じフォークで投票を続ける強い経済的インセンティブが生まれる。フォークの切り替えには以前のロックアウトの期限切れを待つ必要があるからである。
具体的には、バリデータがPoHタイムスタンプtでブロックに投票した場合、2^nティックが経過するまで競合するフォークに投票できない。ここでnは現在のフォークで行った連続投票の数である。この指数関数的ロックアウトメカニズムにより、システムは高速なファイナリティを可能にしながら、長距離攻撃に対して安全になる。ステークの超過半数が十分な深さでブロックに投票すると、そのブロックは事実上確定される。
スラッシング条件は正直な行動を強制する。バリデータがロックアウトされているはずの期間中に2つの競合するフォークに投票した場合、スラッシングされる。ステークされたトークンは部分的に破壊され、バリデータセットから除外される。これにより、二重投票やその他のビザンチン行動を試みることが経済的に非合理的になる。PoHの検証可能なタイムスタンプとTower BFTの指数関数的ロックアウトの組み合わせにより、従来のBFTシステムのセキュリティ保証を維持しながら、数秒でファイナリティを達成する高速かつ安全なコンセンサスメカニズムが実現される。
Streaming Proof of Replication
Proof of Replication (PoRep) एक ऐसा तंत्र है जो सत्यापनकर्ताओं को डेटा स्वयं प्रकट किए बिना या गहन गणना की आवश्यकता के बिना यह साबित करने की अनुमति देता है कि वे लेजर डेटा संग्रहीत कर रहे हैं। Solana PoRep का एक स्ट्रीमिंग संस्करण लागू करता है जहां सत्यापनकर्ता लगातार प्रदर्शित करते हैं कि वे ब्लॉकचेन स्थिति की प्रतिलिपि बना रहे हैं। यह नेटवर्क सुरक्षा के लिए आवश्यक है, क्योंकि यह सुनिश्चित करता है कि लेजर डेटा सत्यापनकर्ताओं के बीच उचित रूप से वितरित है और कुछ स्थानों पर केंद्रित नहीं है।
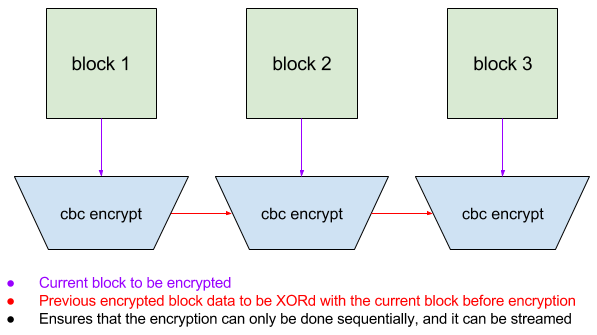
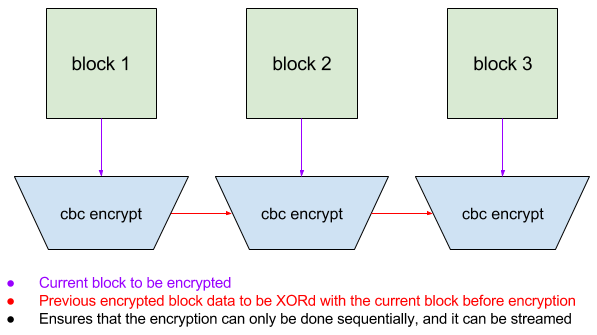
PoRep तंत्र सत्यापनकर्ताओं द्वारा उनकी पहचान से प्राप्त सत्यापनकर्ता-विशिष्ट कुंजी का उपयोग करके CBC (Cipher Block Chaining) मोड एन्क्रिप्शन के साथ लेजर के खंडों को एन्क्रिप्ट करके काम करता है। एन्क्रिप्शन प्रक्रिया ऐसी है कि प्रत्येक एन्क्रिप्टेड ब्लॉक पिछले ब्लॉक पर निर्भर करता है, प्रत्येक सत्यापनकर्ता के लिए अद्वितीय एक चेन बनाता है। यह सत्यापनकर्ताओं को एक-दूसरे से एन्क्रिप्टेड डेटा कॉपी करने से रोकता है — प्रत्येक सत्यापनकर्ता को अपना अद्वितीय एन्क्रिप्टेड संस्करण उत्पन्न करने के लिए मूल लेजर डेटा संग्रहीत और संसाधित करना होगा।
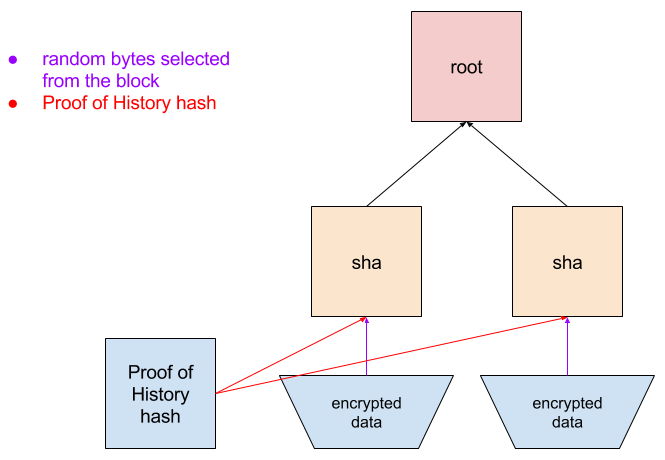
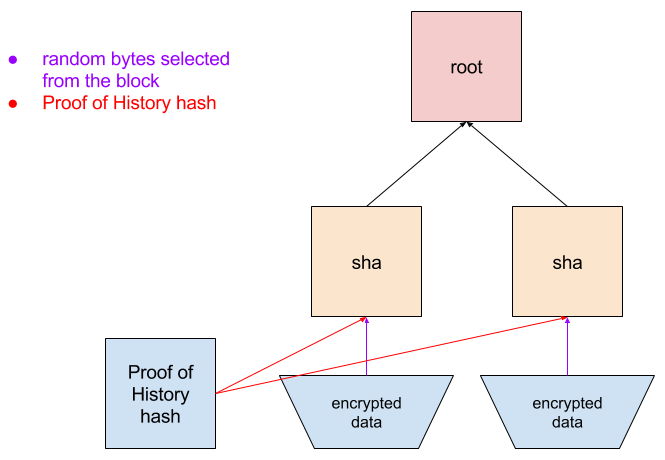
समय-समय पर, नेटवर्क सत्यापनकर्ताओं को विशिष्ट एन्क्रिप्टेड ब्लॉक प्रदान करने के लिए चुनौतियां जारी करता है। क्योंकि एन्क्रिप्शन चेन किया गया है, सत्यापनकर्ता को सही प्रतिक्रिया उत्पन्न करने के लिए सभी पूर्ववर्ती ब्लॉक संग्रहीत होने चाहिए। सत्यापनकर्ता अपने एन्क्रिप्टेड ब्लॉक को अपने एन्क्रिप्टेड लेजर में इसकी स्थिति दिखाने वाले Merkle प्रमाण के साथ जमा करता है। नेटवर्क डेटा को डिक्रिप्ट या पुनः एन्क्रिप्ट किए बिना इस प्रमाण को तुरंत सत्यापित कर सकता है।
PoRep के लिए यह स्ट्रीमिंग दृष्टिकोण पारंपरिक proof-of-storage सिस्टम की तुलना में कम ओवरहेड रखता है। सत्यापनकर्ता डेटा आने पर एन्क्रिप्ट कर सकते हैं और न्यूनतम विलंबता के साथ चुनौतियों का जवाब दे सकते हैं। सिस्टम डेटा हानि के मामले में पुनर्प्राप्ति को भी सक्षम बनाता है — यदि कोई सत्यापनकर्ता लेजर का कुछ भाग खो देता है, तो वे इसे अन्य सत्यापनकर्ताओं से पुनः डाउनलोड कर सकते हैं और पुनः एन्क्रिप्ट कर सकते हैं। PoRep और PoH टाइमस्टैम्प का संयोजन एक पूर्ण जवाबदेही प्रणाली बनाता है जहां नेटवर्क यह सत्यापित कर सकता है कि डेटा कब बनाया गया था और यह सत्यापनकर्ता नेटवर्क में उचित रूप से संग्रहीत है।
Streaming Proof of Replication
Proof of Replication(PoRep)は、バリデータがデータ自体を明かしたり計算集約的な処理を必要としたりすることなく、台帳データを保存していることを証明できるメカニズムである。SolanaはPoRepのストリーミングバージョンを実装しており、バリデータはブロックチェーンの状態を複製していることを継続的に実証する。これはネットワークセキュリティにとって不可欠であり、台帳データがバリデータ間で適切に分散され、少数の場所に集中していないことを保証する。
PoRepメカニズムは、バリデータがそのIDから派生したバリデータ固有のキーを使用して、CBC(Cipher Block Chaining)モード暗号化で台帳のセグメントを暗号化することで機能する。暗号化プロセスは、各暗号化ブロックが前のブロックに依存するようになっており、各バリデータに固有のチェーンを作成する。これにより、バリデータが互いの暗号化データを単にコピーすることが防止される。各バリデータは、固有の暗号化バージョンを生成するために、元の台帳データを保存して処理しなければならない。
定期的に、ネットワークはバリデータに特定の暗号化ブロックの提供を要求するチャレンジを発行する。暗号化はチェーンされているため、バリデータは正しい応答を生成するためにすべての先行ブロックを保存していなければならない。バリデータは暗号化ブロックとともに、暗号化台帳内のその位置を示すMerkle証明を提出する。ネットワークはデータを復号化または再暗号化する必要なく、この証明を迅速に検証できる。
このPoRepへのストリーミングアプローチは、従来のproof-of-storageシステムと比較して低いオーバーヘッドを持つ。バリデータはデータの到着時に暗号化でき、最小限のレイテンシでチャレンジに応答できる。システムはデータ損失の場合のリカバリも可能にする。バリデータが台帳の一部を失った場合、他のバリデータからダウンロードして再暗号化できる。PoRepとPoHタイムスタンプの組み合わせにより、ネットワークがデータの作成時期とバリデータネットワーク全体に適切に保存されていることの両方を検証できる完全な説明責任システムが作成される。
System Architecture
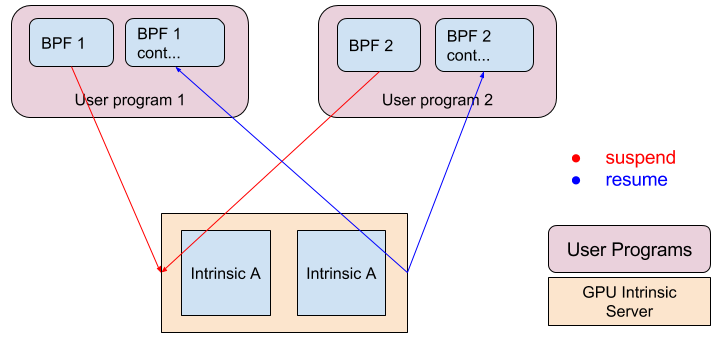
Solana की सिस्टम वास्तुकला एक पाइपलाइन के रूप में डिज़ाइन की गई है जहां लेनदेन प्रसंस्करण के विभिन्न चरण समानांतर में होते हैं। Transaction Processing Unit (TPU) आने वाले लेनदेन को संभालने के लिए जिम्मेदार मुख्य घटक है। TPU में कई चरण शामिल हैं: fetch (लेनदेन का संग्रह), हस्ताक्षर सत्यापन, banking (लेनदेन निष्पादन), और write (स्टोरेज में लिखना)। प्रत्येक चरण विभिन्न लेनदेन पर समानांतर में संचालित होता है, CPU पाइपलाइनिंग के समान।
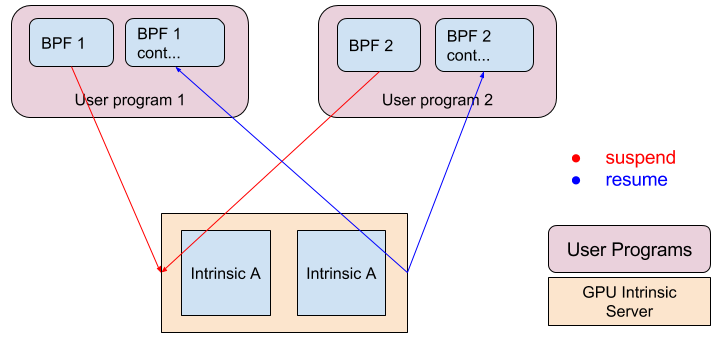
हस्ताक्षर सत्यापन GPU का उपयोग करके त्वरित किया जाता है, जो लेनदेन हस्ताक्षरों को सत्यापित करने के लिए आवश्यक अण्डाकार वक्र क्रिप्टोग्राफी संचालन में अत्यधिक कुशल हैं। इस गणनात्मक रूप से गहन कार्य को GPU पर ऑफलोड करके, Solana कमोडिटी हार्डवेयर पर प्रति सेकंड 900,000 से अधिक की दर पर हस्ताक्षर सत्यापित कर सकता है। यह समानांतर हस्ताक्षर सत्यापन बहुत उच्च लेनदेन दरों पर भी क्रिप्टोग्राफ़िक सत्यापन को अड़चन बनने से रोकता है।
Sealevel रनटाइम Solana का समानांतर स्मार्ट कॉन्ट्रैक्ट निष्पादन इंजन है। पारंपरिक ब्लॉकचेन जो लेनदेन को क्रमिक रूप से निष्पादित करते हैं, उसके विपरीत, Sealevel लेनदेन का विश्लेषण करता है कि वे कौन से खातों तक पहुंचते हैं और गैर-विरोधी लेनदेन को कई CPU कोर पर समानांतर में निष्पादित करता है। समान खातों तक पहुंचने वाले लेनदेन सुसंगतता बनाए रखने के लिए क्रमिक रूप से निष्पादित किए जाते हैं, लेकिन विभिन्न खातों तक पहुंचने वाले लेनदेन एक साथ चल सकते हैं। यह समानांतरता संभव है क्योंकि PoH एक वैश्विक क्रम स्थापित करता है — सत्यापनकर्ता किसी भी क्रम में लेनदेन निष्पादित कर सकते हैं जब तक वे PoH-निर्दिष्ट अनुक्रम में उन्हें स्थिति पर लागू करते हैं।
वास्तुकला में ब्लॉक प्रसार और स्टोरेज के लिए अनुकूलित घटक भी शामिल हैं। Turbine ब्लॉक प्रसार प्रोटोकॉल इरेजर कोडिंग का उपयोग करके ब्लॉक को छोटे पैकेट में विभाजित करता है जो ट्री संरचना में नेटवर्क में वितरित किए जाते हैं, बैंडविड्थ आवश्यकताओं को न्यूनतम करता है। Archivers नेटवर्क PoRep का उपयोग करके डेटा उपलब्धता सुनिश्चित करते हुए ऐतिहासिक लेजर डेटा के लिए विकेंद्रीकृत स्टोरेज प्रदान करता है। ये घटक मिलकर एक ऐसा सिस्टम बनाते हैं जो ब्लॉकचेन के विकेंद्रीकरण और सुरक्षा गुणों को बनाए रखते हुए प्रति सेकंड सैकड़ों हजारों लेनदेन संसाधित कर सकता है।
System Architecture
Solanaのシステムアーキテクチャは、トランザクション処理の異なる段階が並列に行われるパイプラインとして設計されている。Transaction Processing Unit(TPU)は、着信トランザクションの処理を担当する中核コンポーネントである。TPUはいくつかの段階で構成される:fetch(トランザクションの収集)、署名検証、banking(トランザクション実行)、write(ストレージへのコミット)。各段階は異なるトランザクションに対して並列に動作し、CPUパイプラインと同様の仕組みである。
署名検証はGPUを使用して加速される。GPUはトランザクション署名の検証に必要な楕円曲線暗号演算において非常に効率的である。この計算集約的なタスクをGPUにオフロードすることで、Solanaはコモディティハードウェア上で毎秒900,000を超える速度で署名を検証できる。この並列署名検証により、非常に高いトランザクションレートでも暗号学的検証がボトルネックになることが防止される。
Sealevelランタイムは、Solanaの並列スマートコントラクト実行エンジンである。トランザクションを逐次的に実行する従来のブロックチェーンとは異なり、Sealevelはトランザクションを分析してアクセスするアカウントを特定し、競合しないトランザクションを複数のCPUコアで並列に実行する。同じアカウントにアクセスするトランザクションは一貫性を維持するために逐次的に実行されるが、異なるアカウントにアクセスするトランザクションは同時に実行できる。この並列処理はPoHがグローバルな順序付けを確立するため可能である。バリデータは、PoHで指定されたシーケンスで状態に適用する限り、任意の順序でトランザクションを実行できる。
アーキテクチャには、ブロック伝播とストレージのための最適化されたコンポーネントも含まれている。Turbineブロック伝播プロトコルは、イレイジャーコーディングを使用してブロックをより小さなパケットに分割し、ツリー構造でネットワーク全体に配布することで帯域幅要件を最小化する。Archiversネットワークは、PoRepを使用してデータの可用性を確保しながら、履歴台帳データの分散ストレージを提供する。これらのコンポーネントが一体となり、ブロックチェーンの分散化とセキュリティ特性を維持しながら毎秒数十万のトランザクションを処理できるシステムを構築する。
Performance
Solana की वास्तुकला मूर के नियम का पालन करते हुए हार्डवेयर सुधारों के साथ स्केल करने वाले प्रदर्शन स्तर प्राप्त करने के लिए डिज़ाइन की गई है। एक मानक 1 गीगाबिट नेटवर्क कनेक्शन पर, सैद्धांतिक अधिकतम थ्रूपुट प्रति लेनदेन 176 बाइट (हस्ताक्षर और मेटाडेटा सहित) मानते हुए प्रति सेकंड लगभग 710,000 लेनदेन है। यह गणना प्राथमिक अड़चन के रूप में नेटवर्क बैंडविड्थ पर आधारित है, जिसमें गणनात्मक अड़चनों को समानांतरीकरण के माध्यम से हटा दिया गया है।
हस्ताक्षर सत्यापन, जो अक्सर ब्लॉकचेन प्रदर्शन में एक सीमित कारक होता है, GPU समानांतरीकरण का उपयोग करके त्वरित किया जाता है। एक एकल GPU प्रति सेकंड 900,000 से अधिक ed25519 हस्ताक्षर सत्यापित कर सकता है, जो नेटवर्क थ्रूपुट सीमा से अधिक है। इसका मतलब है कि हस्ताक्षर सत्यापन सिस्टम के प्रदर्शन को बाधित नहीं करता — अड़चन नेटवर्क बैंडविड्थ और लेनदेन निष्पादन में स्थानांतरित हो जाती है। जटिल स्मार्ट कॉन्ट्रैक्ट लॉजिक के बिना केवल मूल्य हस्तांतरित करने वाले सरल लेनदेन के लिए, banking चरण नेटवर्क इनपुट दर से मेल खाने वाली दर पर लेनदेन संसाधित कर सकता है।
PoH जनरेटर एक समर्पित CPU कोर पर चलता है, 4GHz प्रोसेसर पर प्रति मिलीसेकंड लगभग 4,000 हैश उत्पन्न करता है। इस दर पर, PoH अनुक्रम 0.25 माइक्रोसेकंड ग्रैन्युलैरिटी वाले टाइमस्टैम्प प्रदान करता है, जो प्रति सेकंड लाखों लेनदेन के क्रम के लिए पर्याप्त है। PoH उत्पादन की अनुक्रमिक प्रकृति का अर्थ है कि इस घटक को समानांतर नहीं किया जा सकता, लेकिन थ्रूपुट इतना अधिक है कि यह समग्र सिस्टम प्रदर्शन को सीमित नहीं करता।
जैसे-जैसे हार्डवेयर में सुधार होता है, Solana का थ्रूपुट तदनुसार स्केल होता है। तेज नेटवर्क, अधिक शक्तिशाली GPU, और बेहतर CPU सभी उच्च लेनदेन दरों में योगदान करते हैं। सिस्टम को प्रोटोकॉल परिवर्तनों की आवश्यकता के बिना इन सुधारों का लाभ उठाने के लिए डिज़ाइन किया गया है। यह स्केलेबिलिटी दृष्टिकोण उन ब्लॉकचेन से विपरीत है जो अनुक्रमिक सहमति तंत्रों द्वारा मौलिक रूप से सीमित हैं, जो Solana को सुरक्षा और विकेंद्रीकरण गारंटी बनाए रखते हुए विकेंद्रीकृत सिस्टम में पहले असंभव माने जाने वाले प्रदर्शन स्तर प्राप्त करने की अनुमति देता है।
Performance
Solanaのアーキテクチャは、ムーアの法則に従ってハードウェアの改善とともにスケールするパフォーマンスレベルを達成するように設計されている。標準的な1ギガビットネットワーク接続では、理論上の最大スループットは1トランザクションあたり176バイト(署名とメタデータを含む)を想定すると、毎秒約710,000トランザクションである。この計算はネットワーク帯域幅を主要なボトルネックとし、計算上のボトルネックは並列化によって除去されている。
署名検証はブロックチェーンパフォーマンスの制限要因となることが多いが、GPUの並列化を使用して加速される。単一のGPUは毎秒900,000以上のed25519署名を検証でき、これはネットワークスループット制限を超えている。これは署名検証がシステムのパフォーマンスを制約しないことを意味する。ボトルネックはネットワーク帯域幅とトランザクション実行に移行する。複雑なスマートコントラクトロジックを含まない単純な価値移転トランザクションの場合、bankingステージはネットワーク入力レートに匹敵するレートでトランザクションを処理できる。
PoHジェネレータは専用のCPUコア上で動作し、4GHzプロセッサ上でミリ秒あたり約4,000ハッシュを生成する。このレートで、PoHシーケンスは0.25マイクロ秒の粒度のタイムスタンプを提供し、毎秒数百万のトランザクションの順序付けに十分である。PoH生成の逐次的な性質はこのコンポーネントを並列化できないことを意味するが、スループットは十分に高く、全体的なシステムパフォーマンスを制限しない。
ハードウェアが改善されるにつれて、Solanaのスループットはそれに応じてスケールする。より高速なネットワーク、より強力なGPU、改善されたCPUはすべてより高いトランザクションレートに貢献する。システムはプロトコルの変更を必要とせずにこれらの改善を活用するように設計されている。このスケーラビリティアプローチは、逐次的コンセンサスメカニズムによって根本的に制限されるブロックチェーンとは対照的であり、Solanaがセキュリティと分散化の保証を維持しながら、分散型システムでは不可能と考えられていたパフォーマンスレベルを達成することを可能にする。
Conclusion
Proof of History वितरित लेजर की स्केलेबिलिटी को सीमित करने वाली समय समस्या को हल करके ब्लॉकचेन वास्तुकला में एक मौलिक सफलता का प्रतिनिधित्व करता है। एक सत्यापन योग्य क्रिप्टोग्राफ़िक घड़ी बनाकर, PoH सत्यापनकर्ताओं को पारंपरिक सहमति तंत्रों द्वारा आवश्यक व्यापक संचार ओवरहेड के बिना घटनाओं का कालानुक्रमिक क्रम स्थापित करने में सक्षम बनाता है। यह नवाचार एक महत्वपूर्ण अड़चन को दूर करता है और लेनदेन प्रसंस्करण को नेटवर्क में समानांतर करने की अनुमति देता है।
PoH का अनुकूलित सिस्टम घटकों के साथ एकीकरण — GPU-त्वरित हस्ताक्षर सत्यापन, Sealevel के माध्यम से समानांतर लेनदेन निष्पादन, और कुशल ब्लॉक प्रसार प्रोटोकॉल — कमोडिटी हार्डवेयर पर प्रति सेकंड सैकड़ों हजारों लेनदेन संसाधित करने में सक्षम एक ब्लॉकचेन बनाता है। इससे भी महत्वपूर्ण बात यह है कि वास्तुकला हार्डवेयर सुधारों के साथ स्केल करने के लिए डिज़ाइन की गई है, जिसका अर्थ है कि प्रोसेसर तेज होने और नेटवर्क अधिक सक्षम होने पर प्रदर्शन बढ़ता रहेगा।
Solana का डिज़ाइन दर्शाता है कि उच्च प्रदर्शन और विकेंद्रीकरण परस्पर अनन्य नहीं हैं। PoH को सहमति और सिस्टम समन्वय के लिए आधार के रूप में लाभ उठाकर, नेटवर्क विकेंद्रीकृत ब्लॉकचेन की सुरक्षा और सेंसरशिप-प्रतिरोध गुणों को बनाए रखते हुए केंद्रीकृत डेटाबेस के समान थ्रूपुट स्तर प्राप्त करता है। स्टेक-भारित Tower BFT सहमति तंत्र सुनिश्चित करता है कि तेज अंतिमता प्राप्त करते हुए नेटवर्क बीजान्टिन अभिकर्ताओं के खिलाफ सुरक्षित रहे।
इस वास्तुकला का कार्यान्वयन ब्लॉकचेन प्रौद्योगिकी के वैश्विक अपनाने तक स्केल करने के लिए एक व्यावहारिक मार्ग प्रदान करता है। उच्च लेनदेन थ्रूपुट की आवश्यकता वाले अनुप्रयोग — जैसे विकेंद्रीकृत एक्सचेंज, गेमिंग प्लेटफॉर्म, और वित्तीय प्रणालियां — अब प्रदर्शन से समझौता किए बिना वास्तव में विकेंद्रीकृत बुनियादी ढांचे पर बनाए जा सकते हैं। Proof of History ब्लॉकचेन अनुप्रयोगों की एक नई पीढ़ी का द्वार खोलता है जो पहले स्केलेबिलिटी बाधाओं के कारण अव्यावहारिक थे।
Conclusion
Proof of Historyは、分散型台帳のスケーラビリティを制限してきたタイミング問題を解決することで、ブロックチェーンアーキテクチャにおける根本的なブレークスルーを表している。検証可能な暗号学的時計を作成することで、PoHはバリデータが従来のコンセンサスメカニズムで必要とされる広範な通信オーバーヘッドなしにイベントの時間的順序付けを確立できるようにする。このイノベーションにより重要なボトルネックが除去され、トランザクション処理をネットワーク全体で並列化できるようになる。
PoHと最適化されたシステムコンポーネント(GPU加速署名検証、Sealevelによる並列トランザクション実行、効率的なブロック伝播プロトコル)の統合により、コモディティハードウェア上で毎秒数十万のトランザクションを処理できるブロックチェーンが実現される。さらに重要なのは、アーキテクチャがハードウェアの改善とともにスケールするように設計されており、プロセッサが高速化しネットワークがより高性能になるにつれてパフォーマンスが向上し続けることである。
Solanaの設計は、高性能と分散化が相互に排他的ではないことを実証している。PoHをコンセンサスとシステム調整の基盤として活用することで、ネットワークは分散型ブロックチェーンのセキュリティと検閲耐性の特性を維持しながら、中央集権型データベースに匹敵するスループットレベルを達成する。ステーク加重Tower BFTコンセンサスメカニズムにより、高速なファイナリティを達成しながら、ビザンチンアクターに対するネットワークの安全性が確保される。
このアーキテクチャの実装は、ブロックチェーン技術がグローバルな採用へとスケールするための実用的な道筋を提供する。高いトランザクションスループットを必要とするアプリケーション(分散型取引所、ゲームプラットフォーム、金融システムなど)は、パフォーマンスを犠牲にすることなく、真に分散化されたインフラストラクチャ上に構築できるようになった。Proof of Historyは、スケーラビリティの制約のために以前は実現不可能であった新世代のブロックチェーンアプリケーションへの扉を開く。




